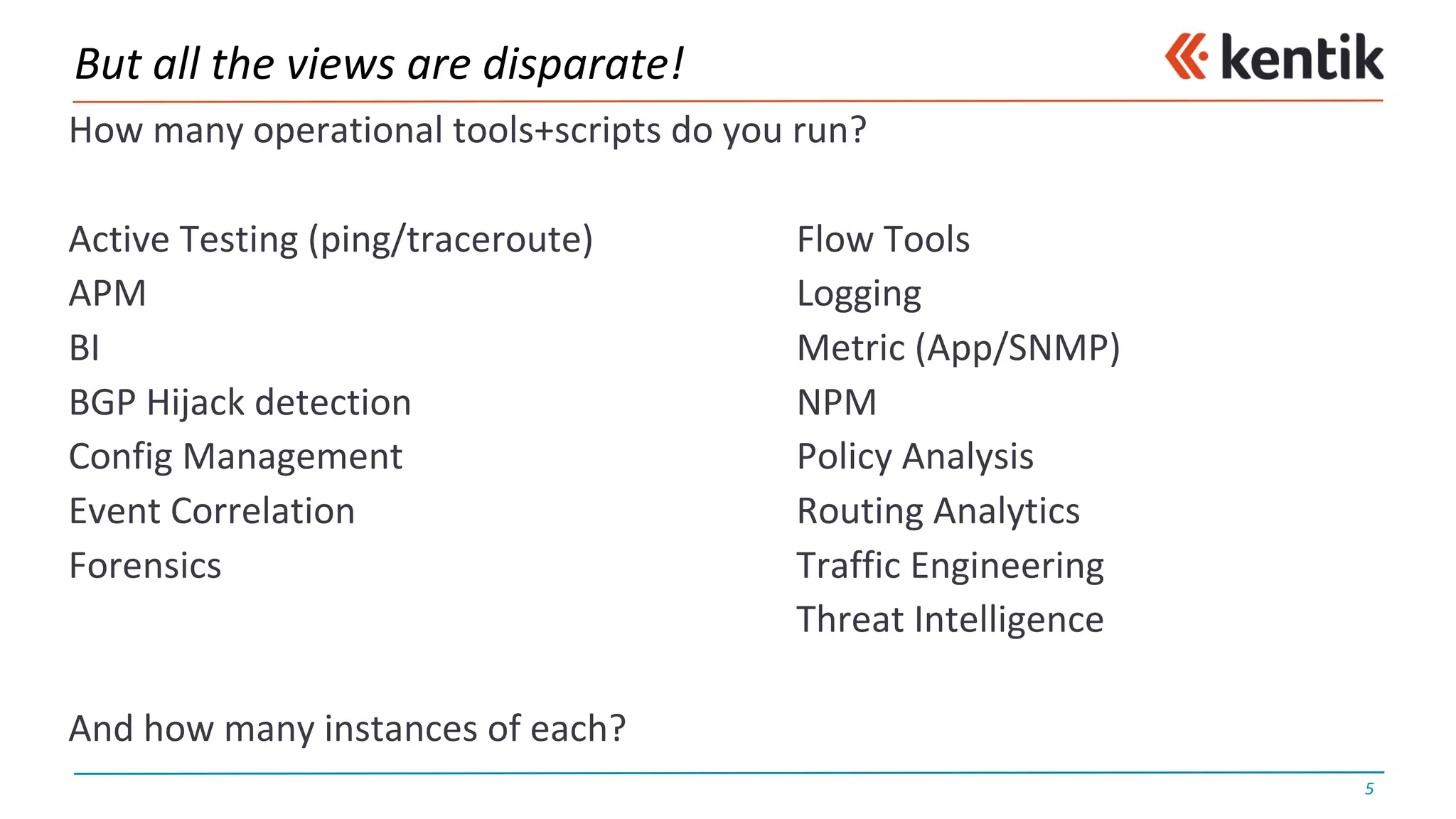
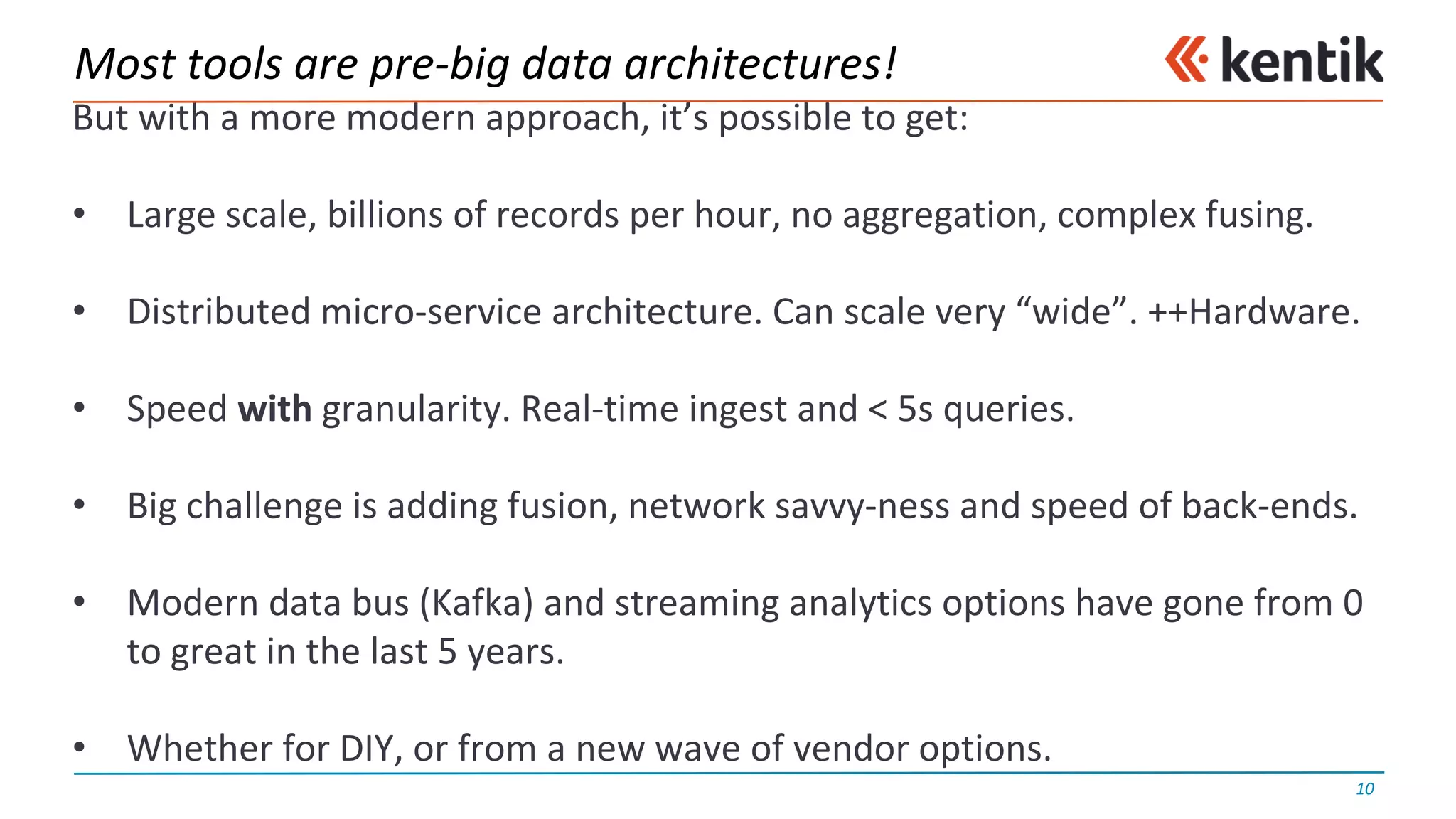
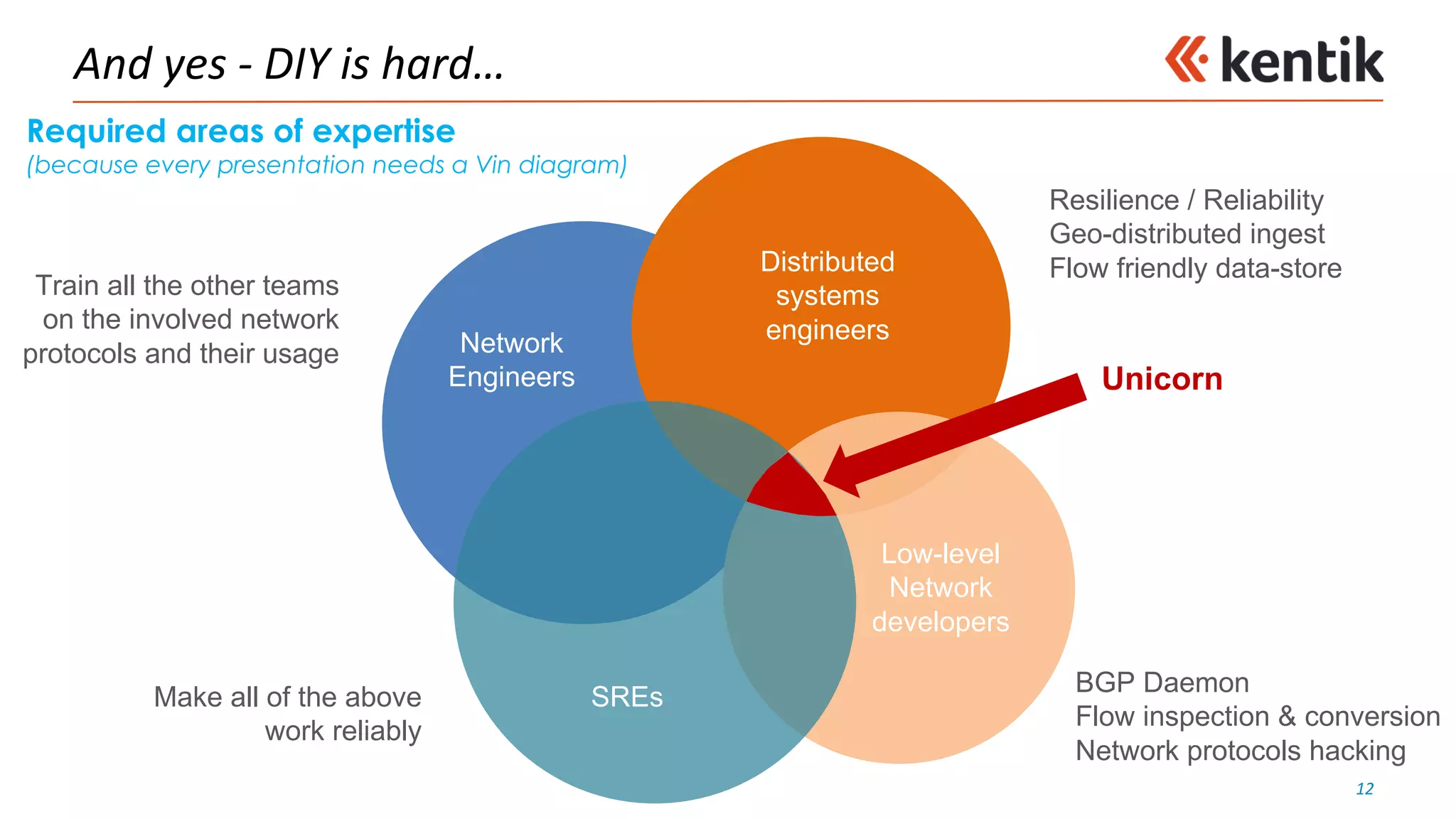
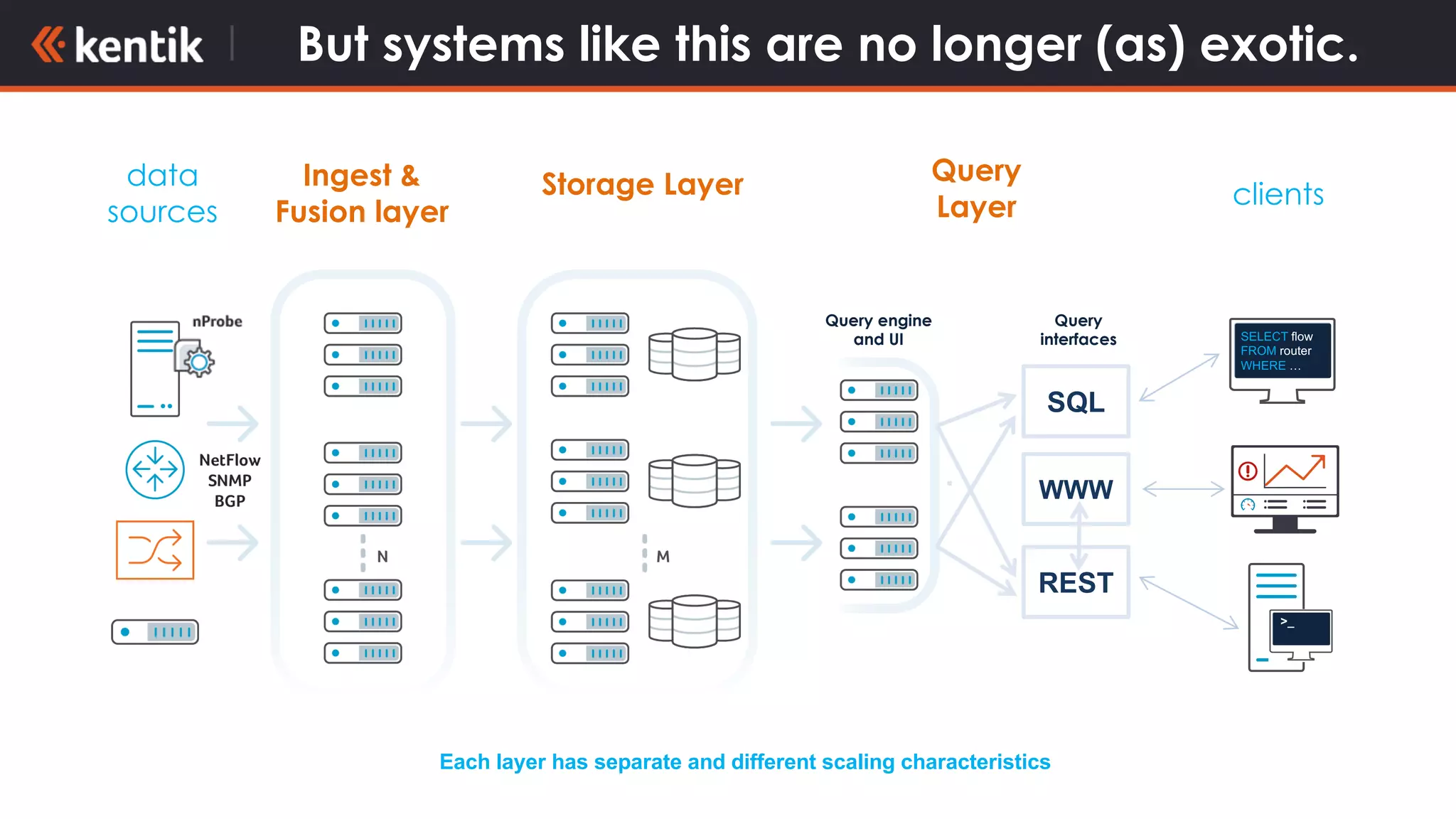
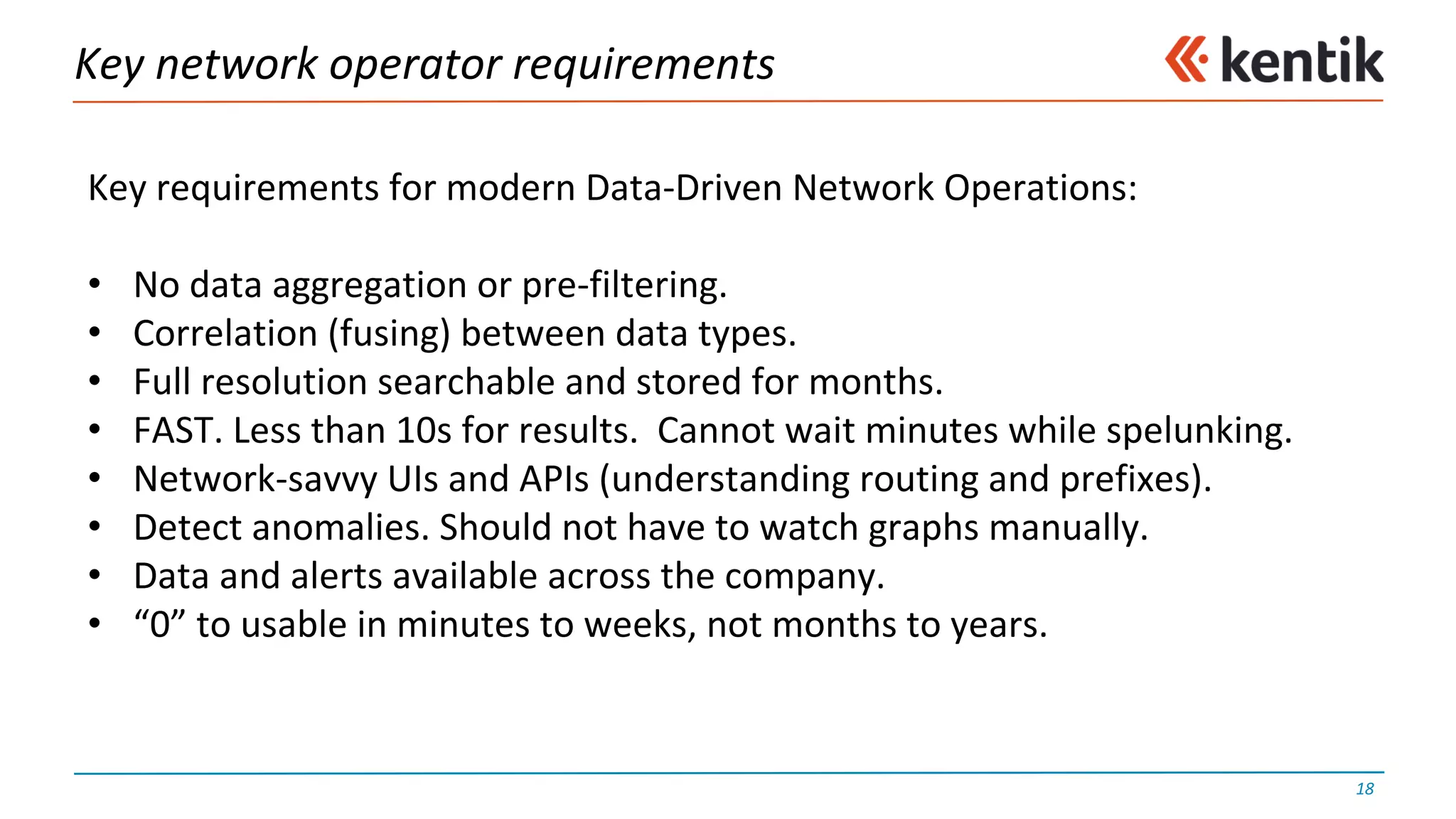
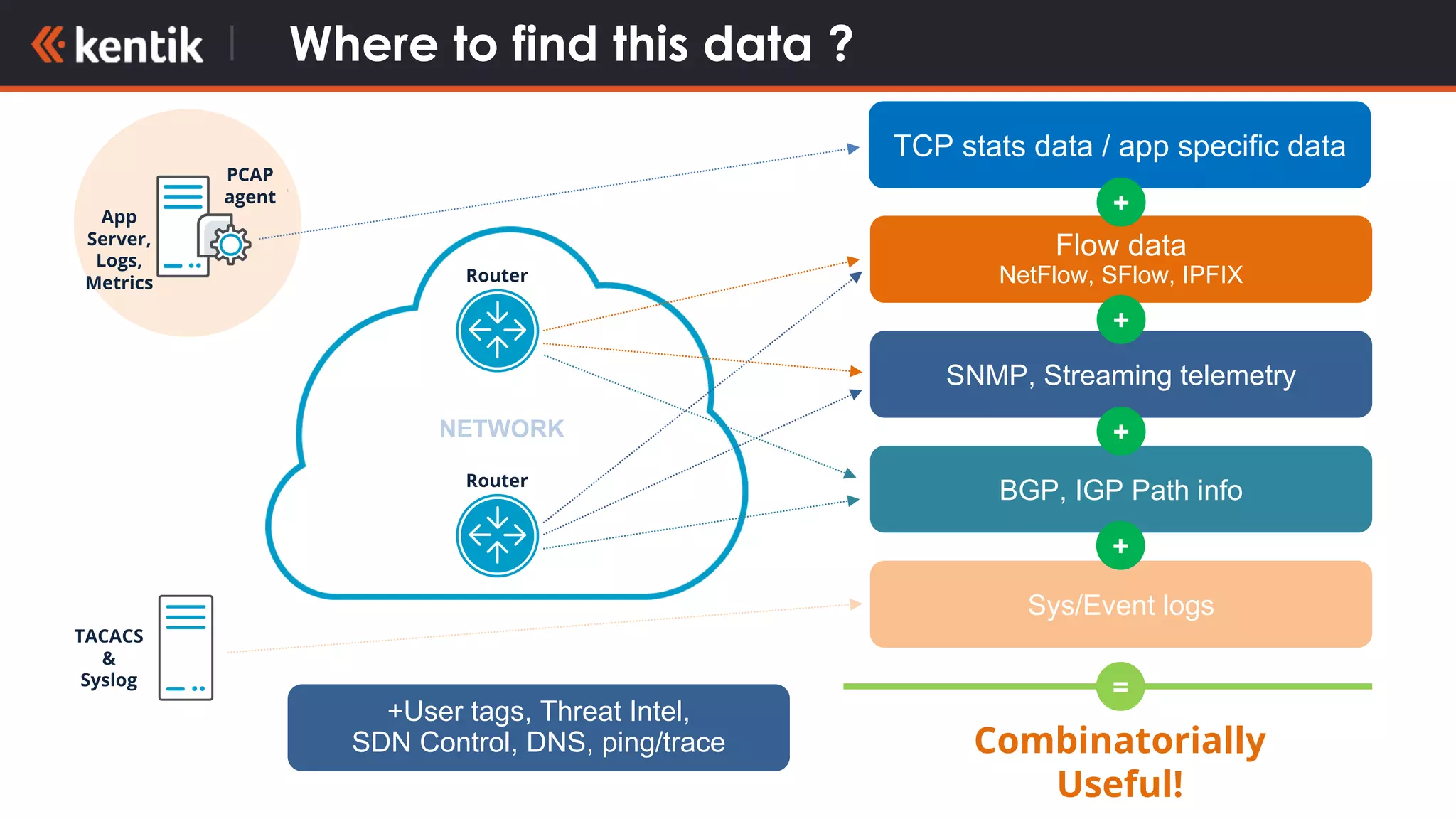
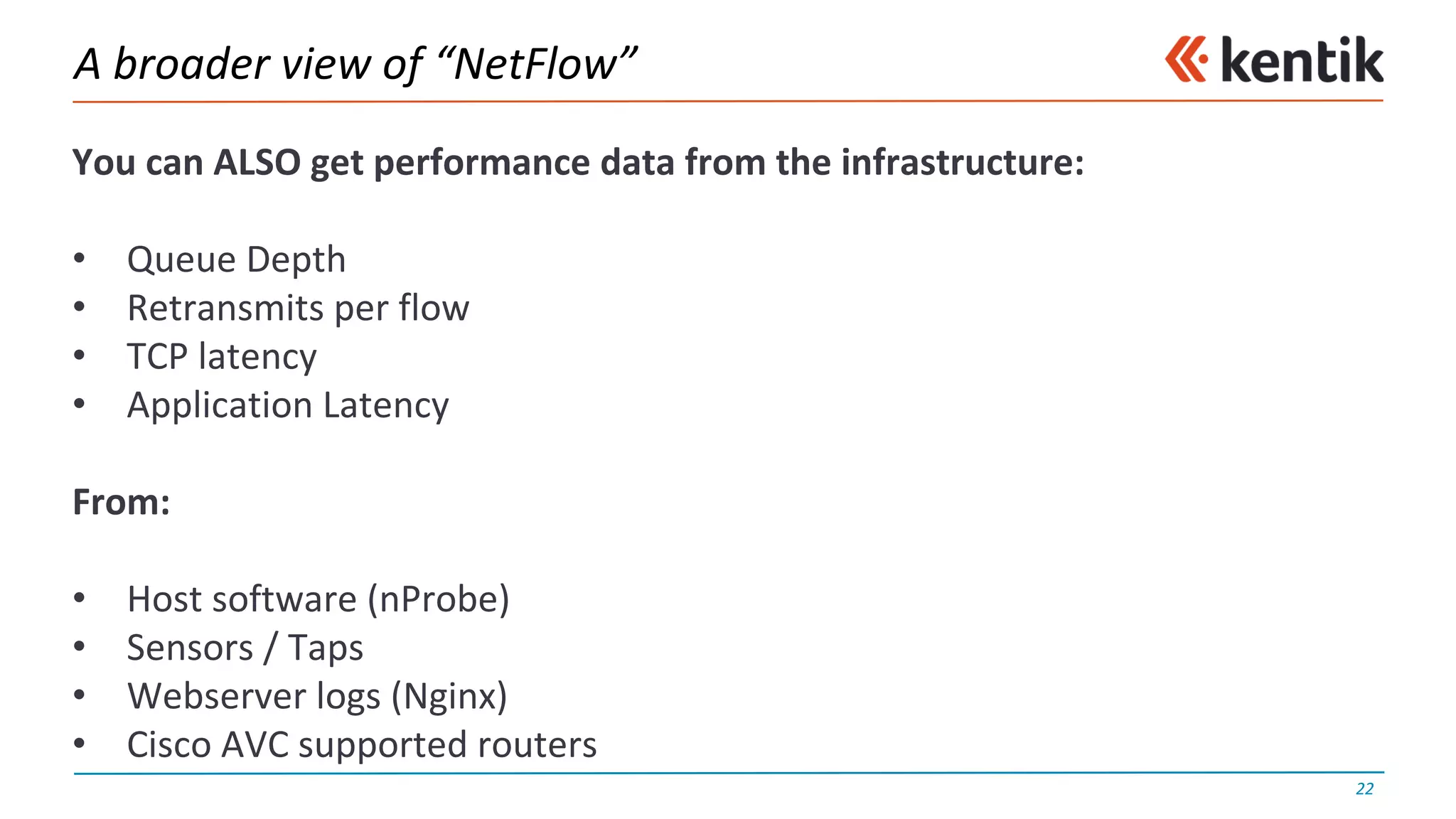
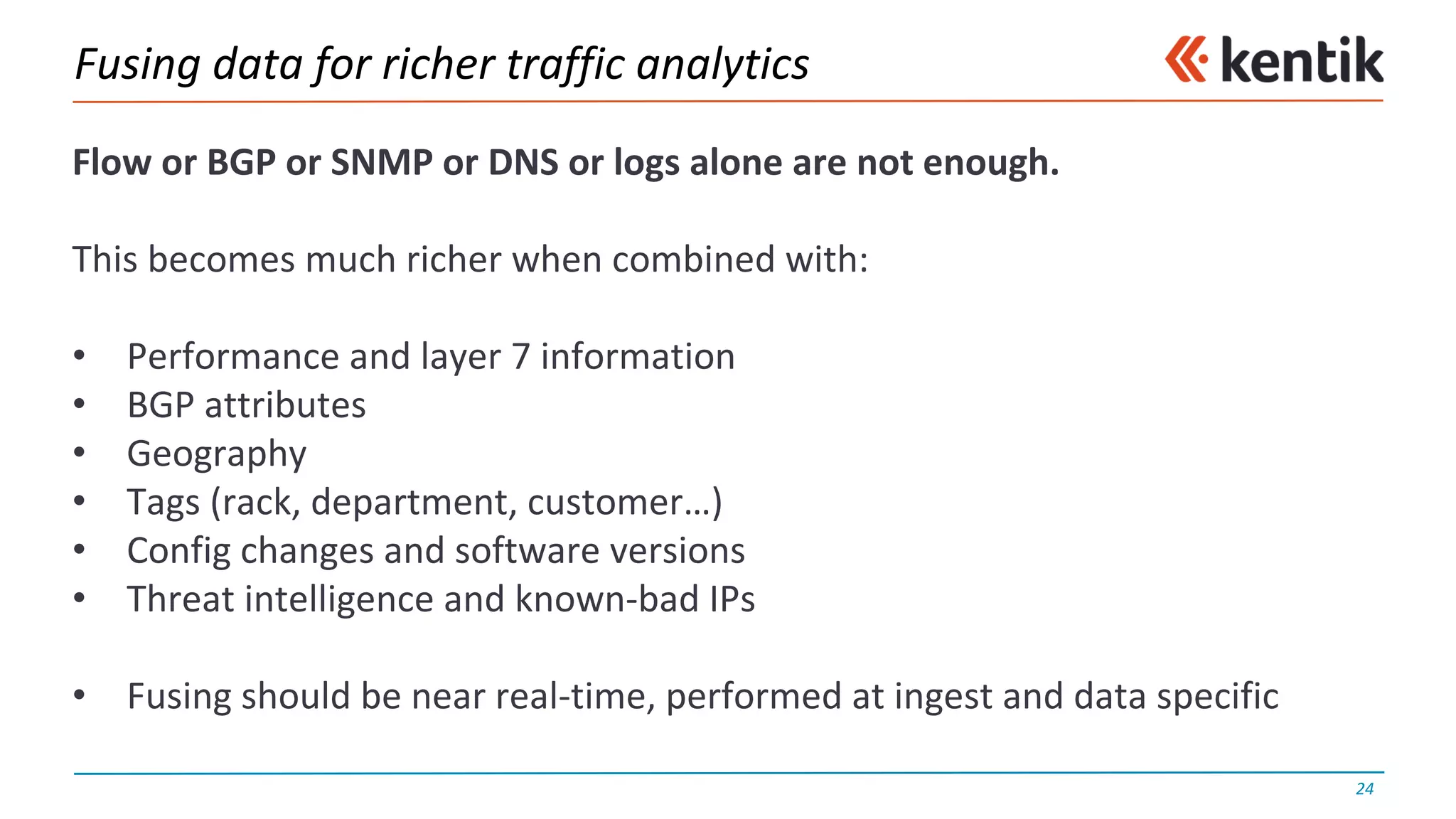
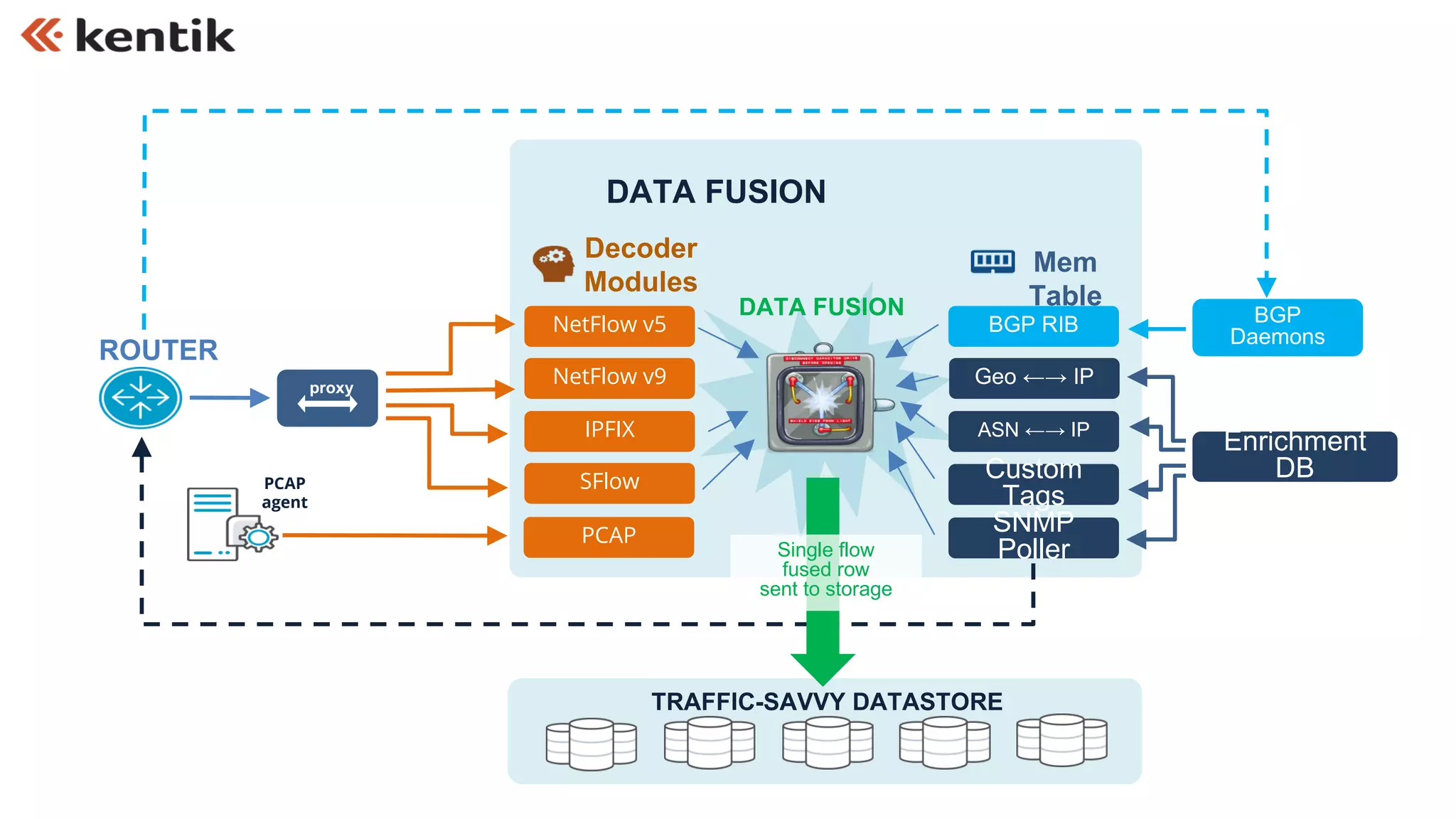
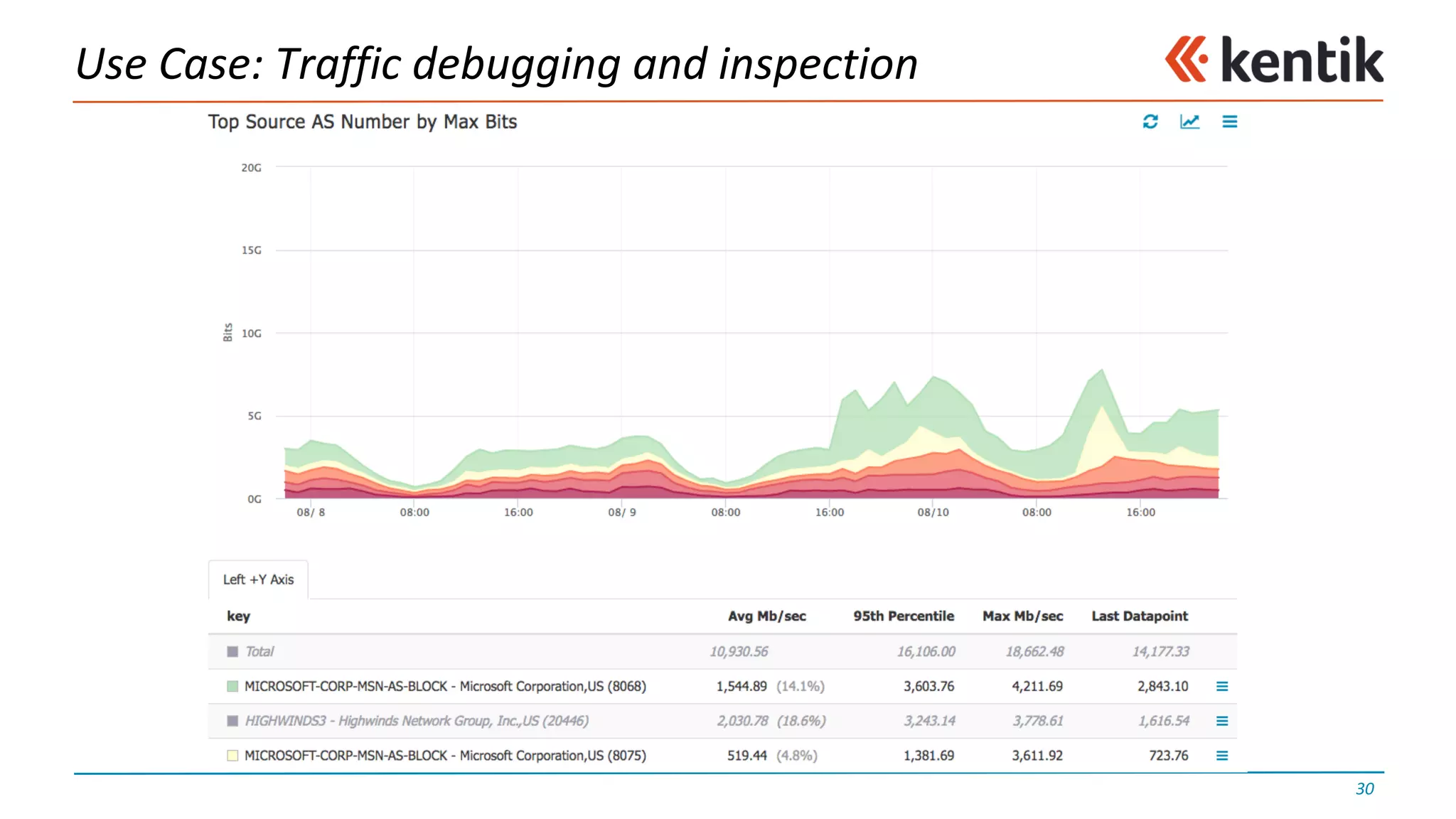
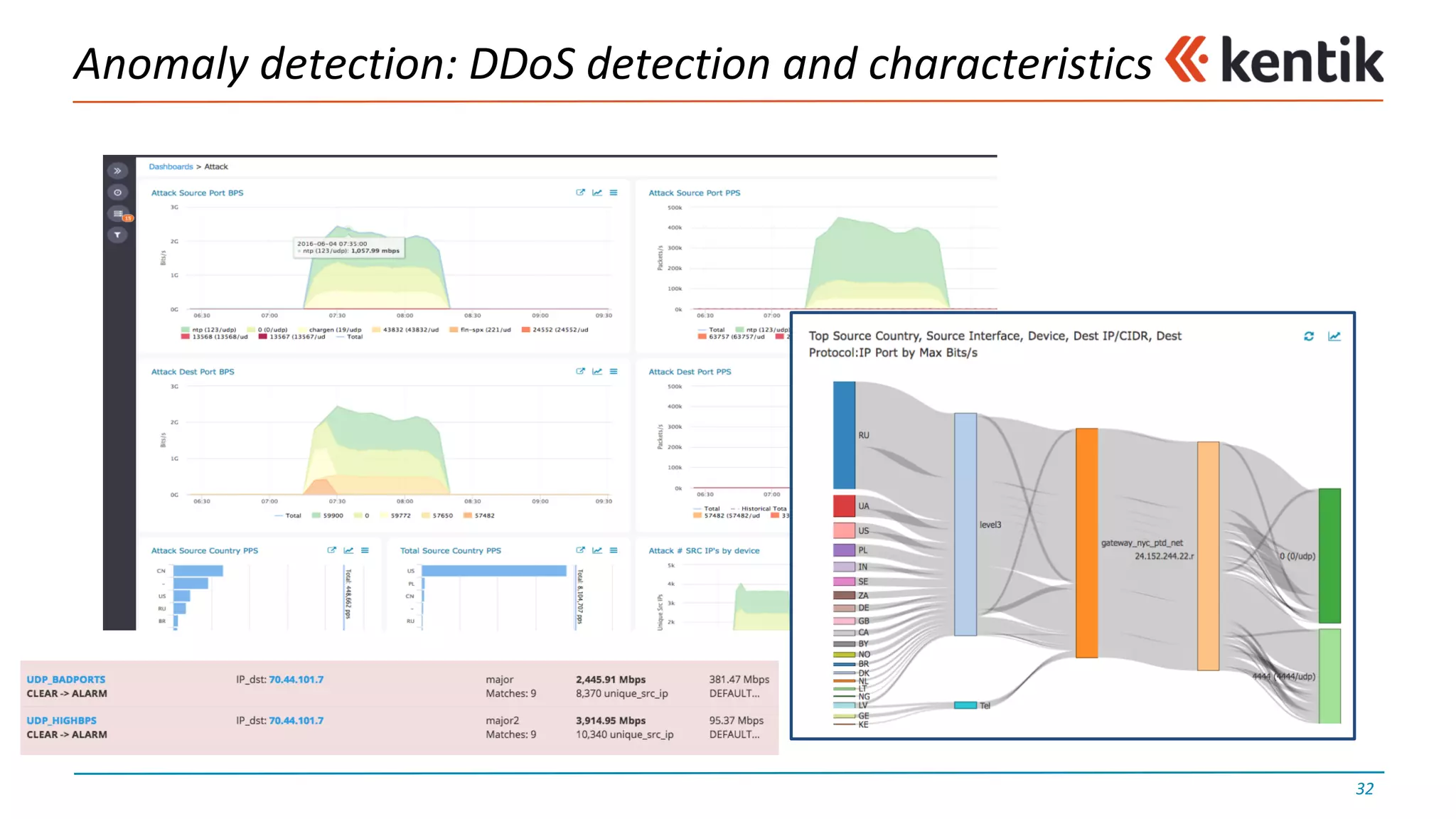
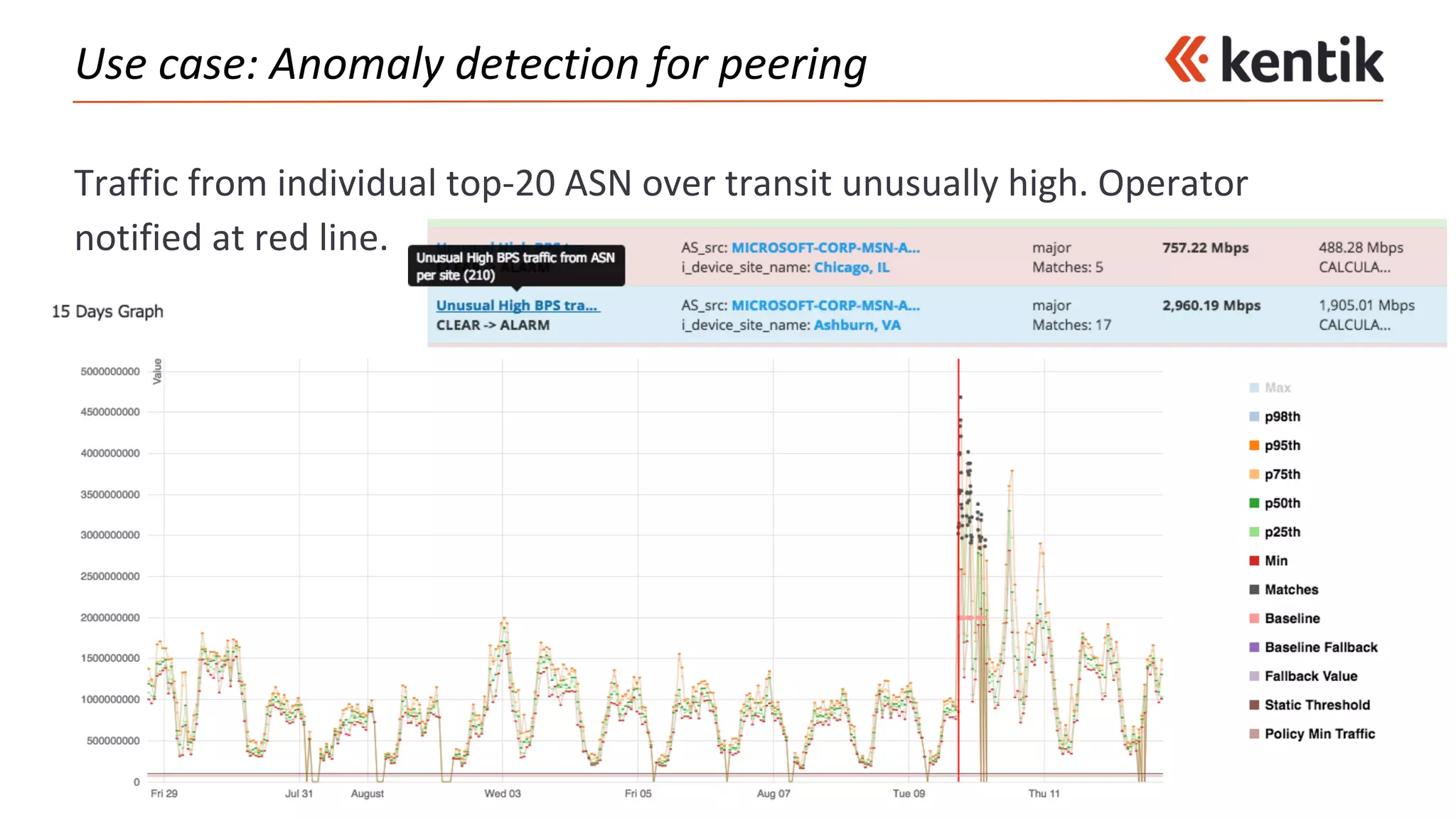
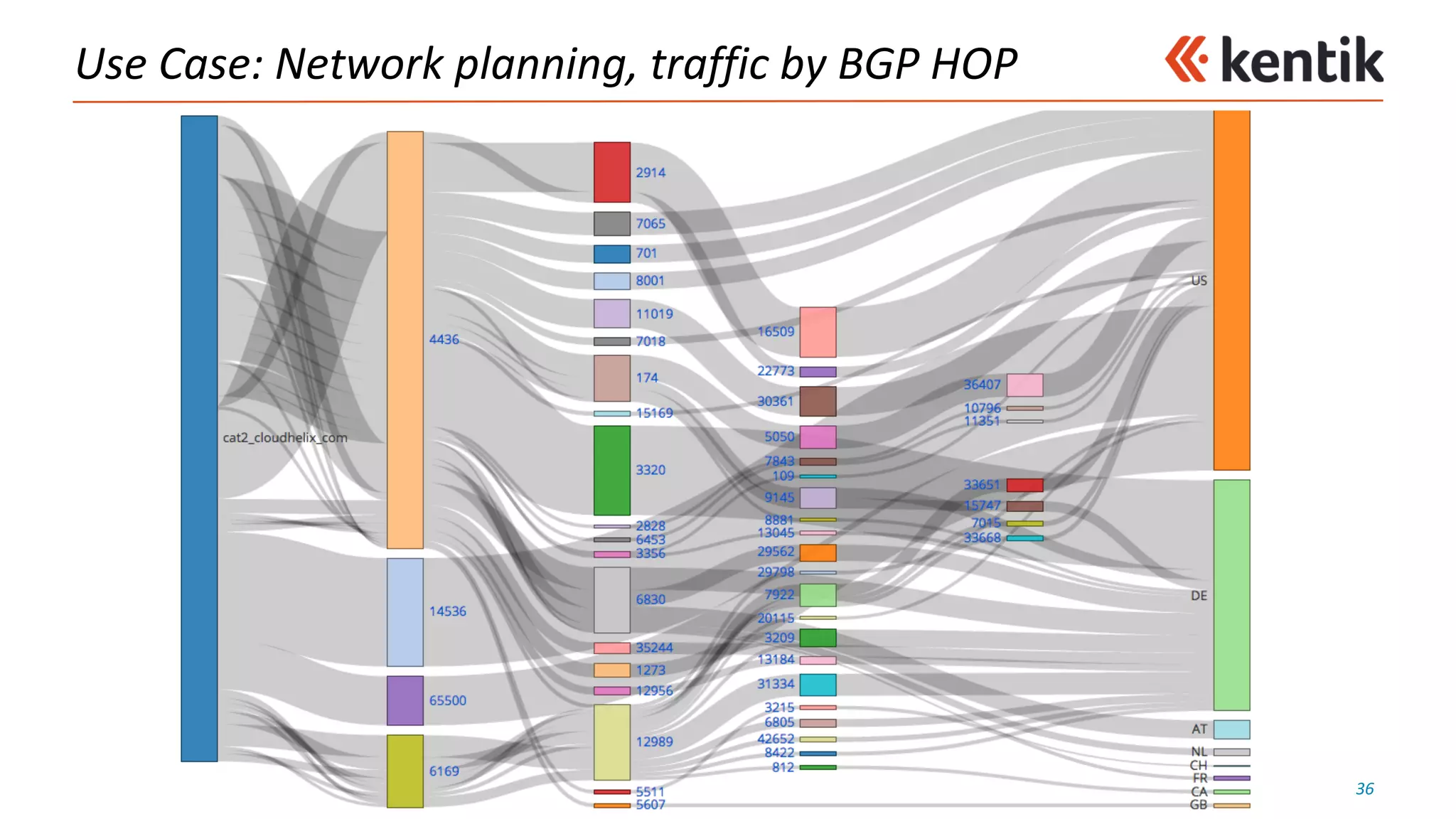
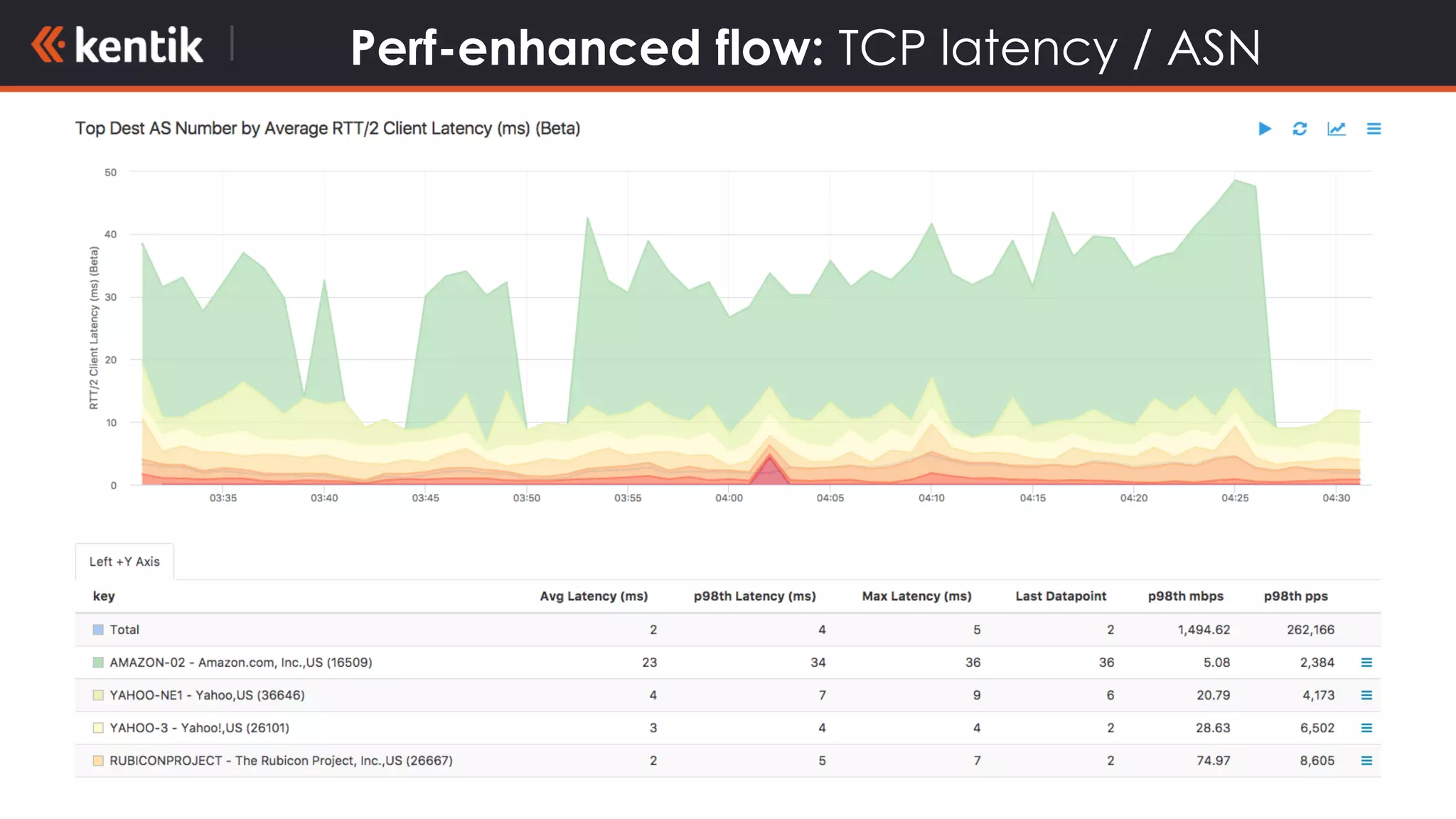
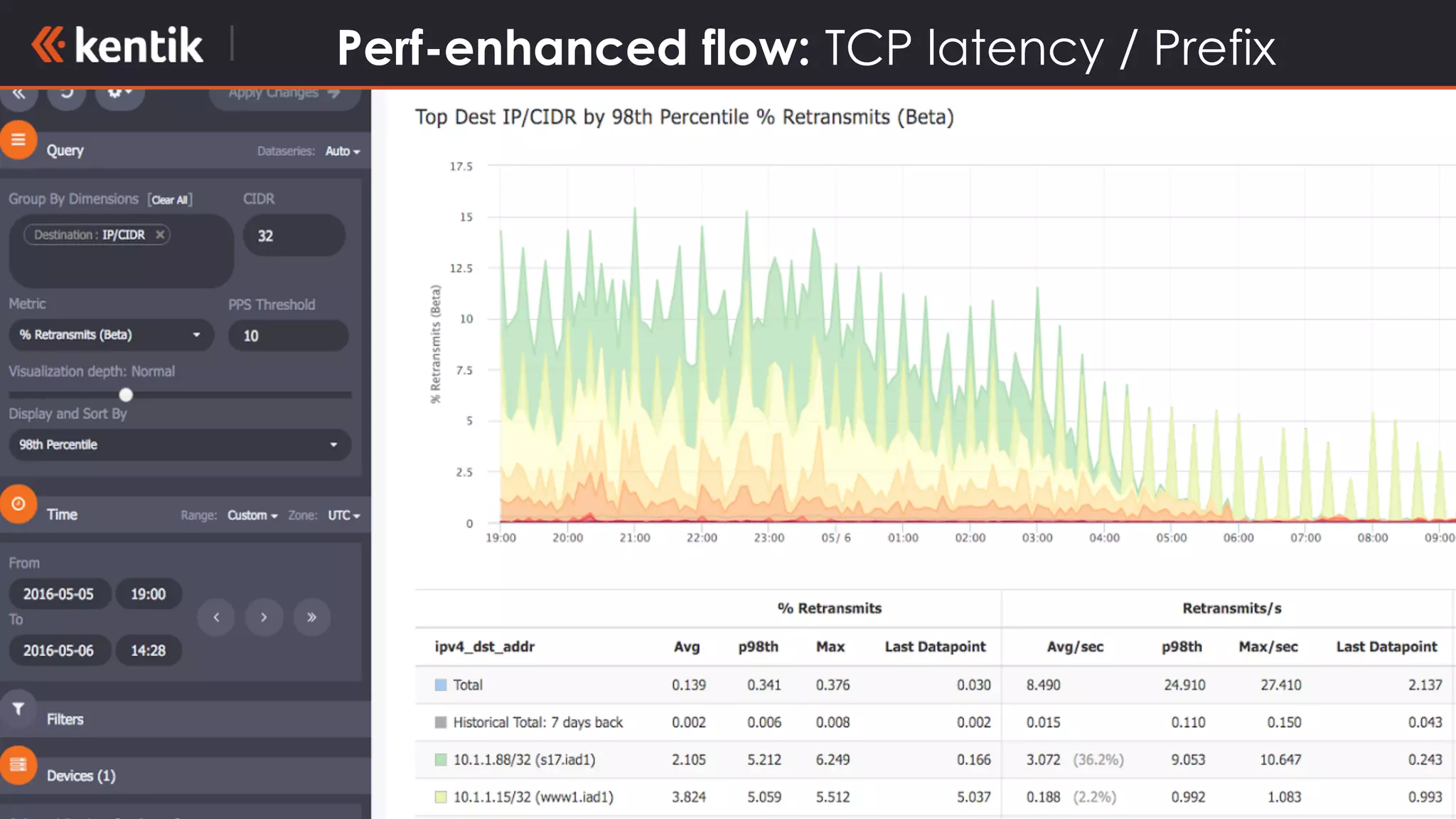
This document discusses the need for data-driven network operations. It begins by noting how difficult it can be to manage infrastructure using the many disparate operational tools currently available. It then argues that taking a data-driven approach by collecting, fusing, storing and analyzing network data can help network operators better understand issues, plan infrastructure changes, and provide insights for both technical and business stakeholders. Specific use cases mentioned include traffic debugging, anomaly detection, network planning, security analytics and performance analysis. The challenges of obtaining and working with network data at scale are also addressed.