System Security on Cloud
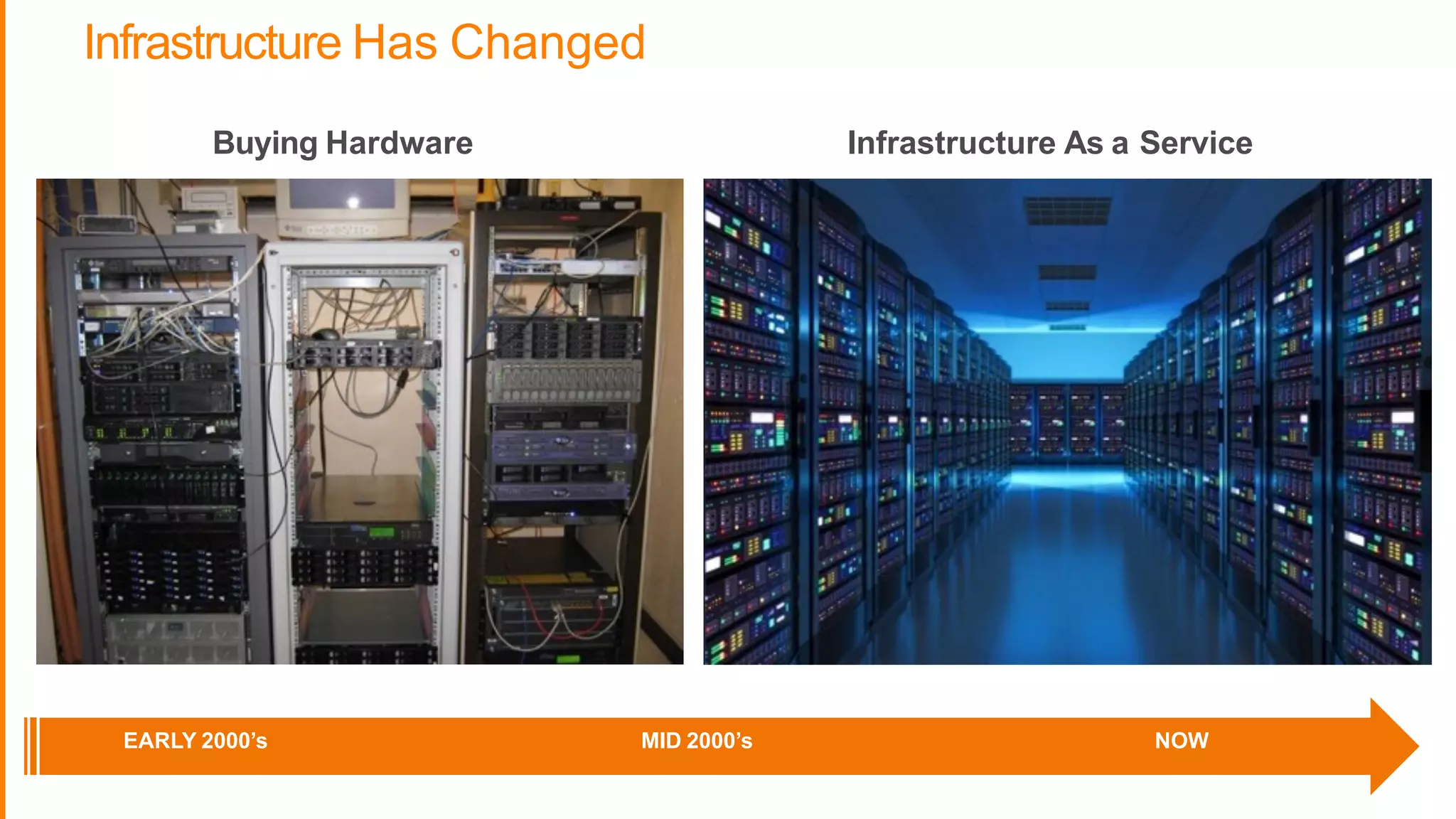
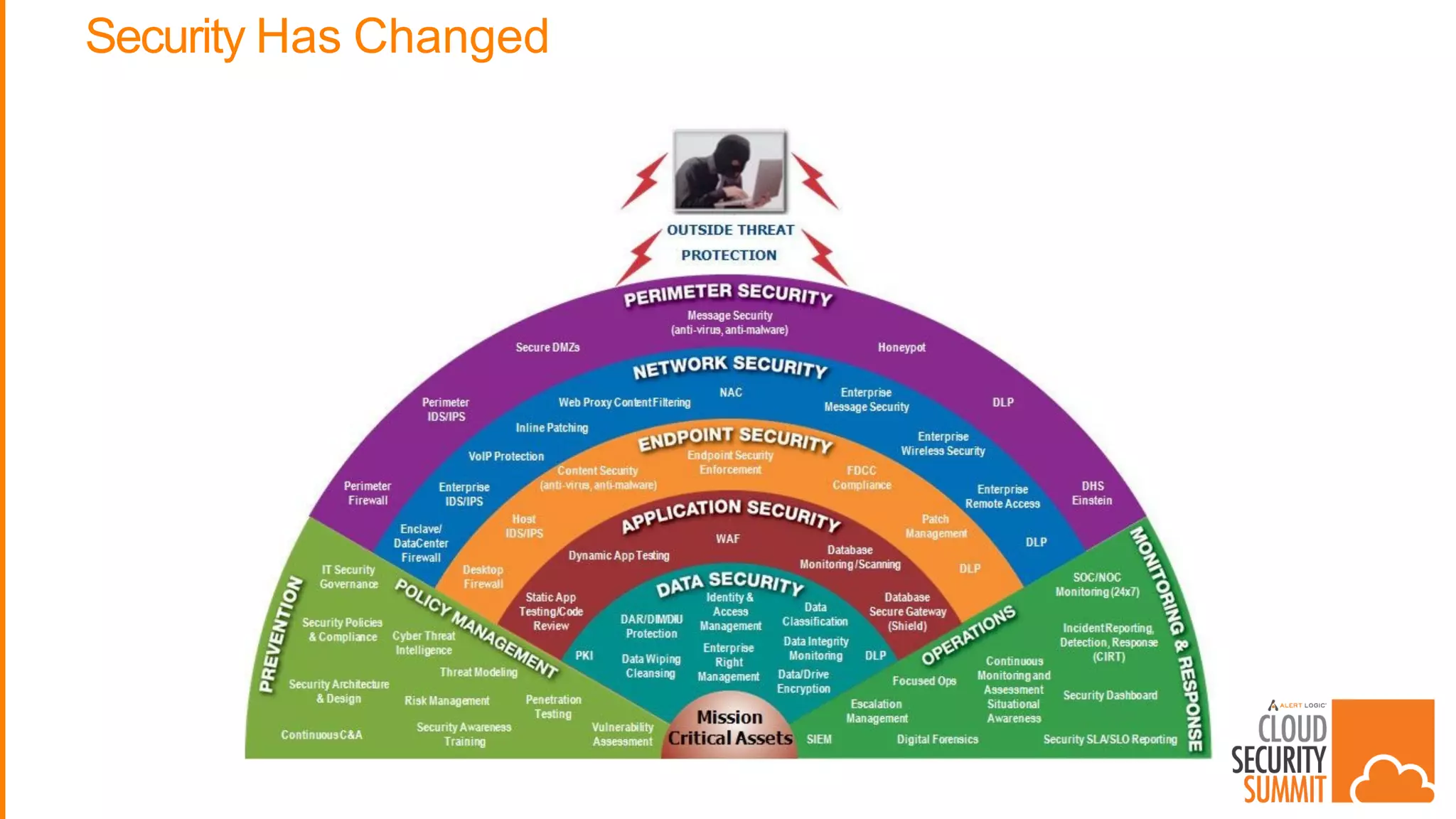
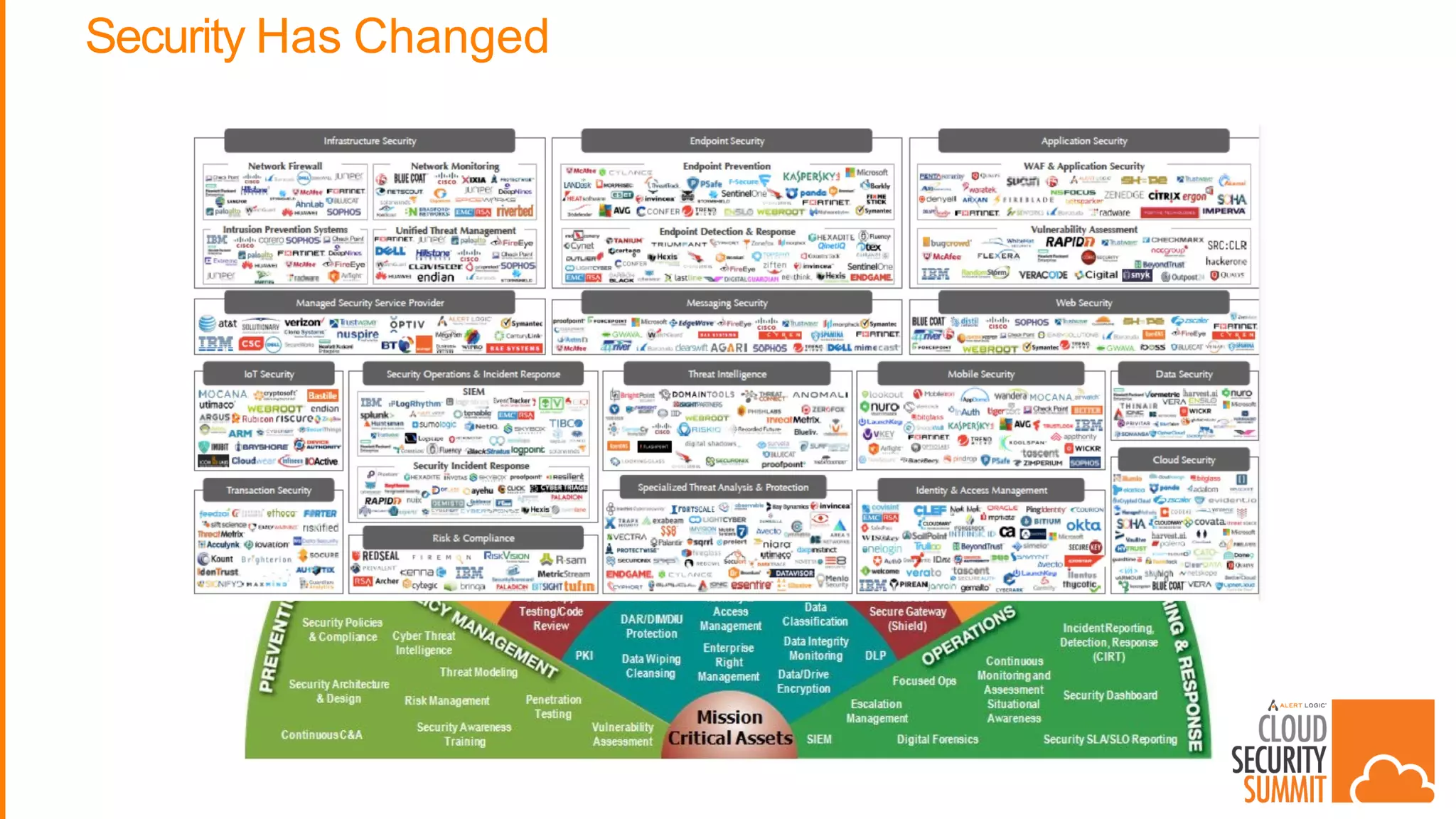
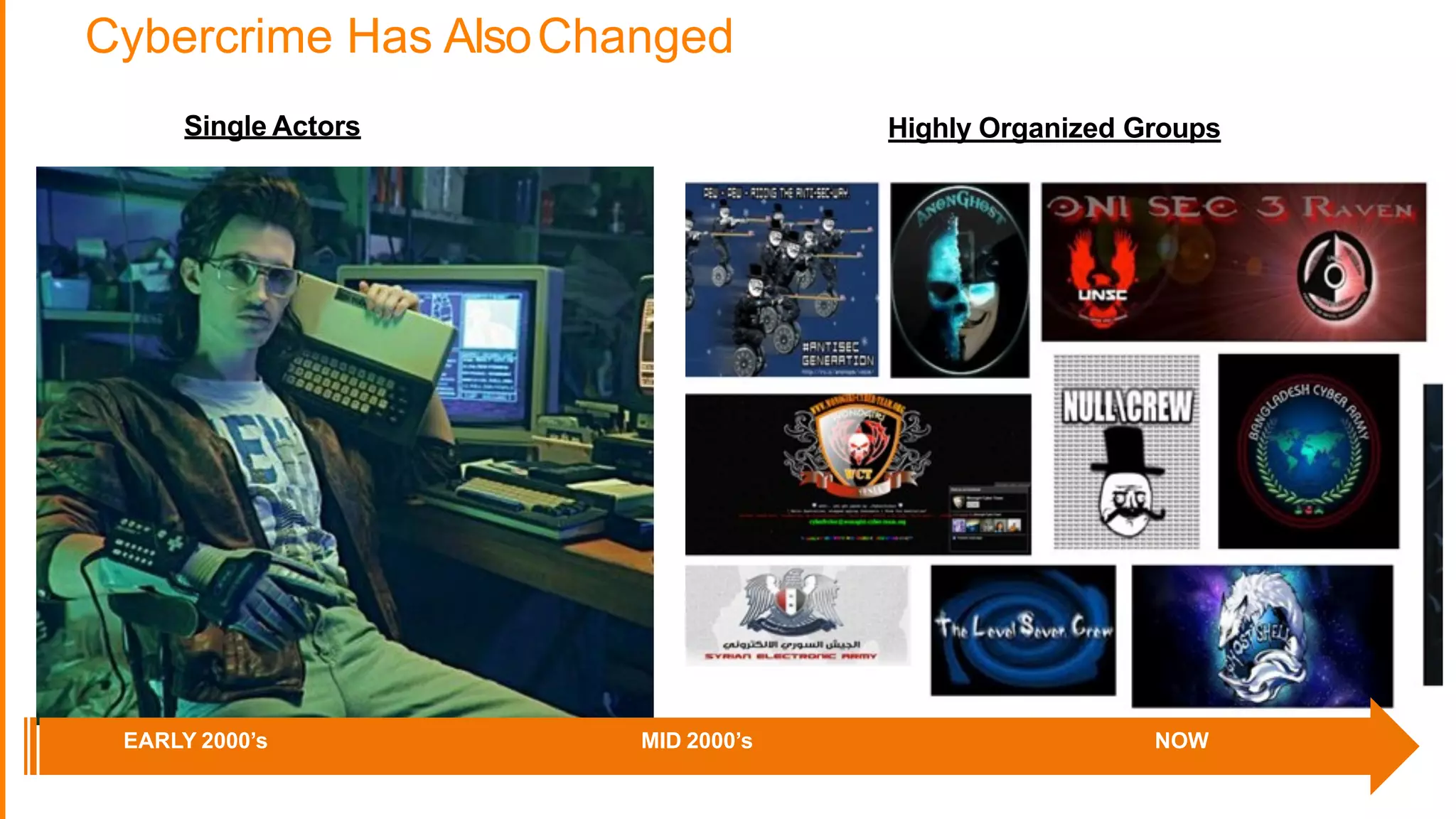
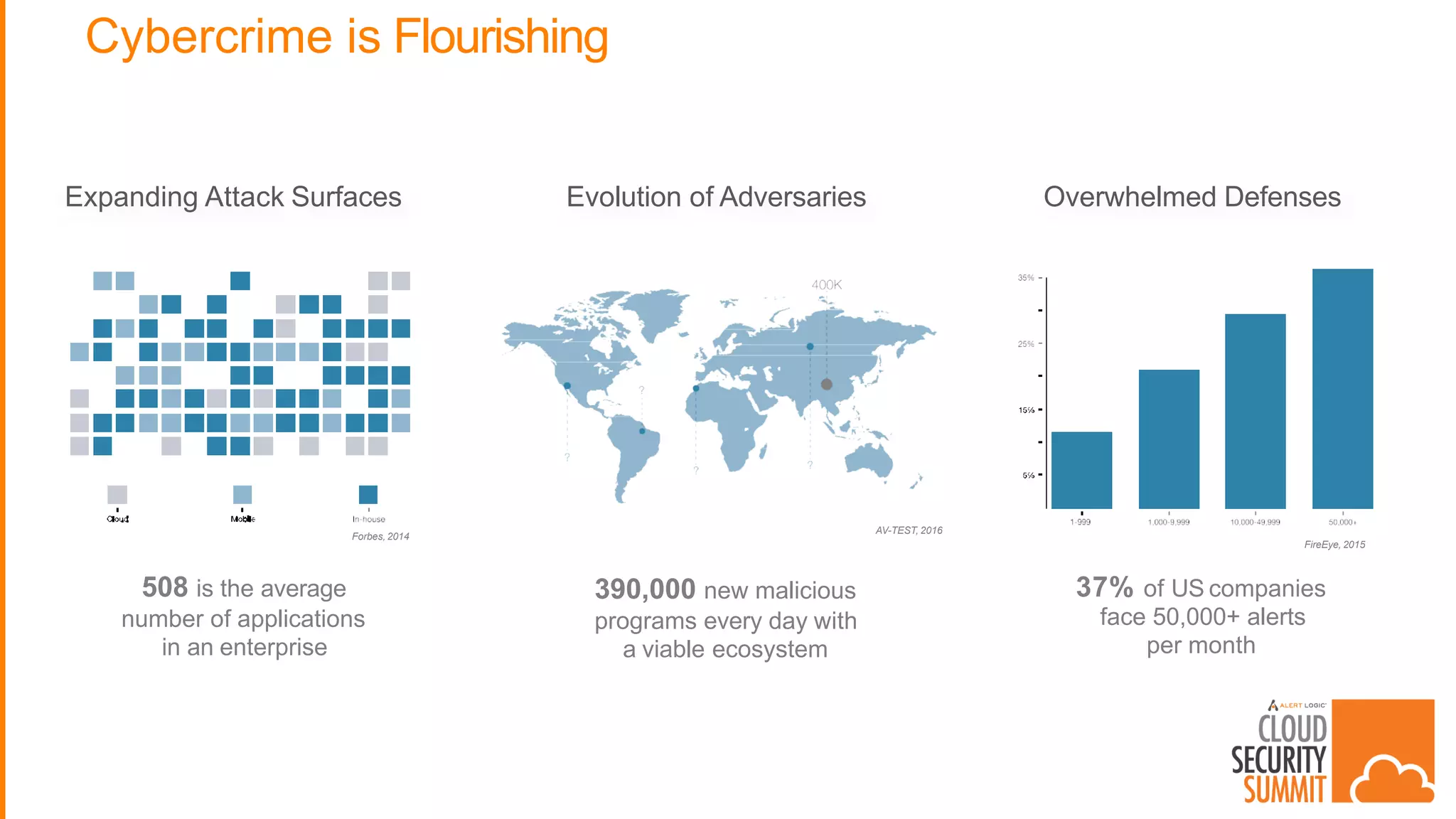
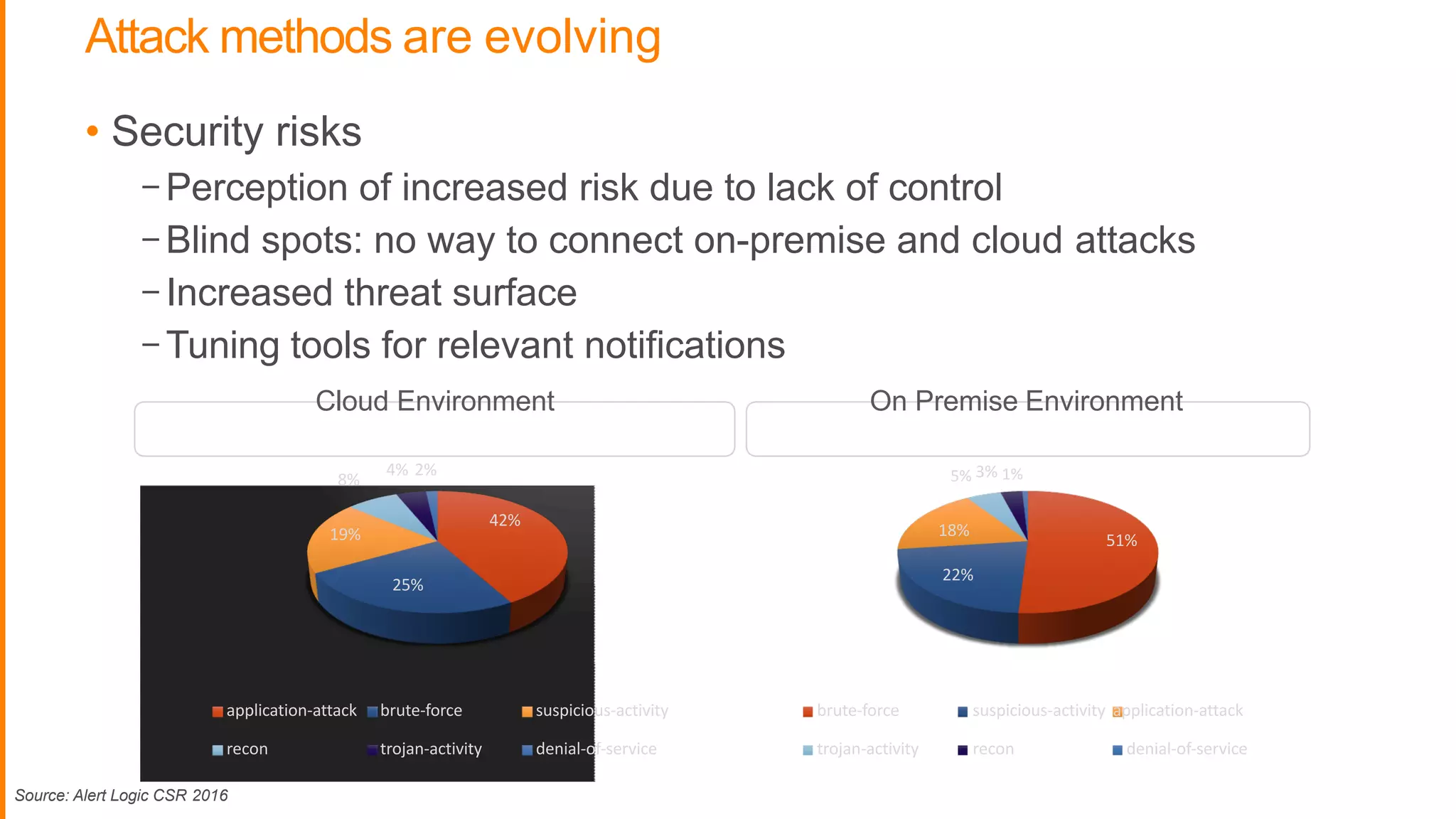
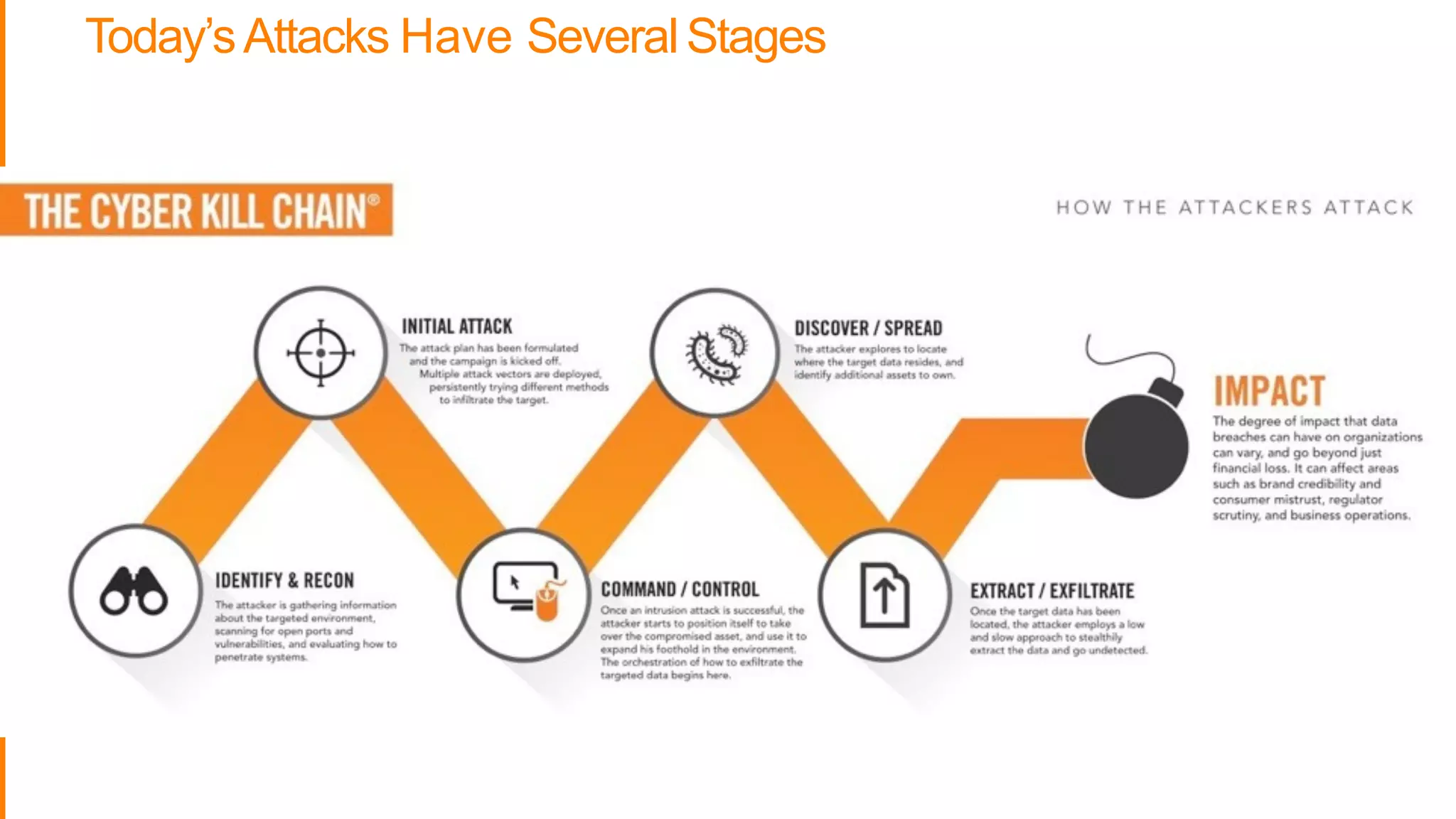
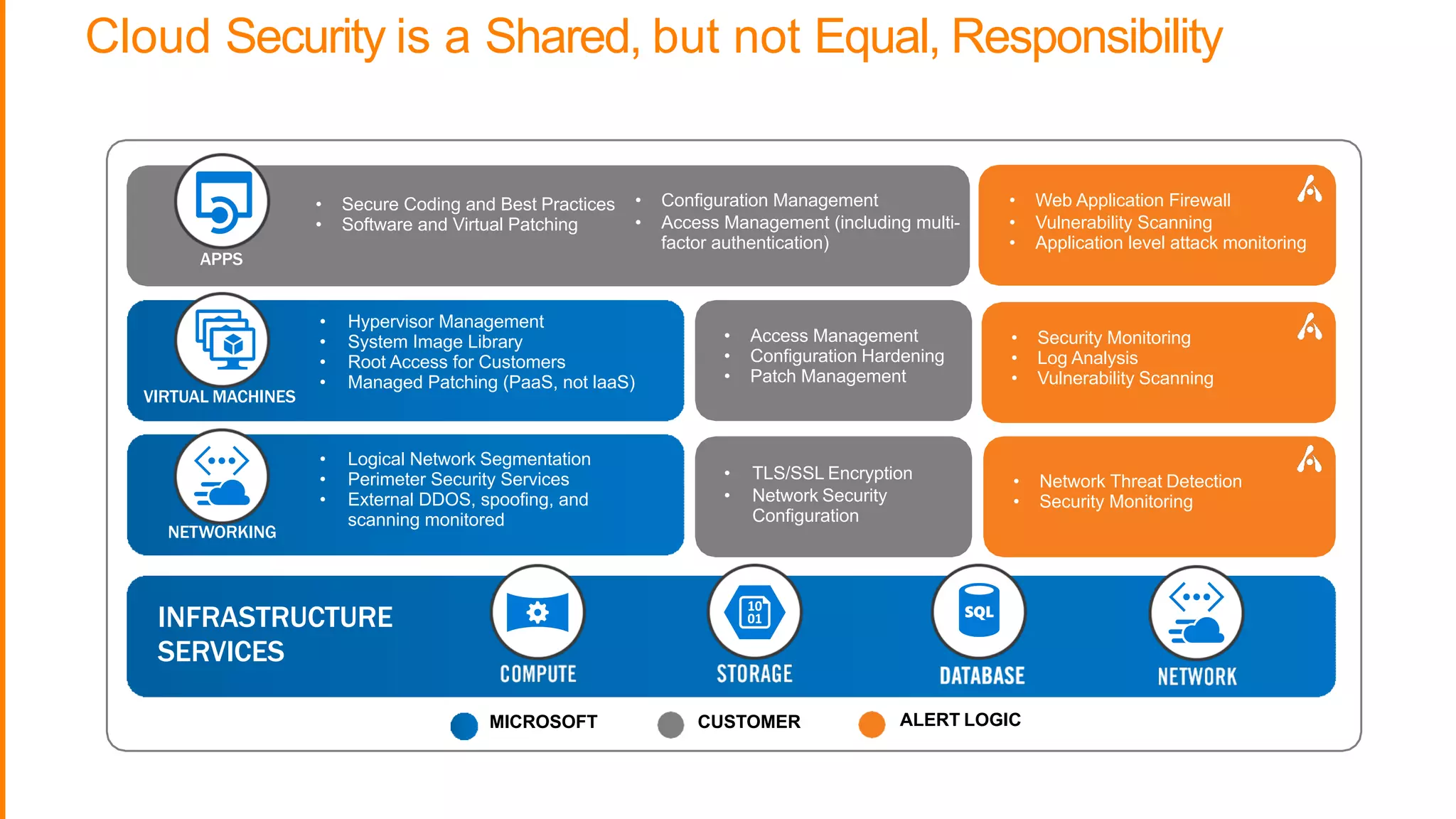
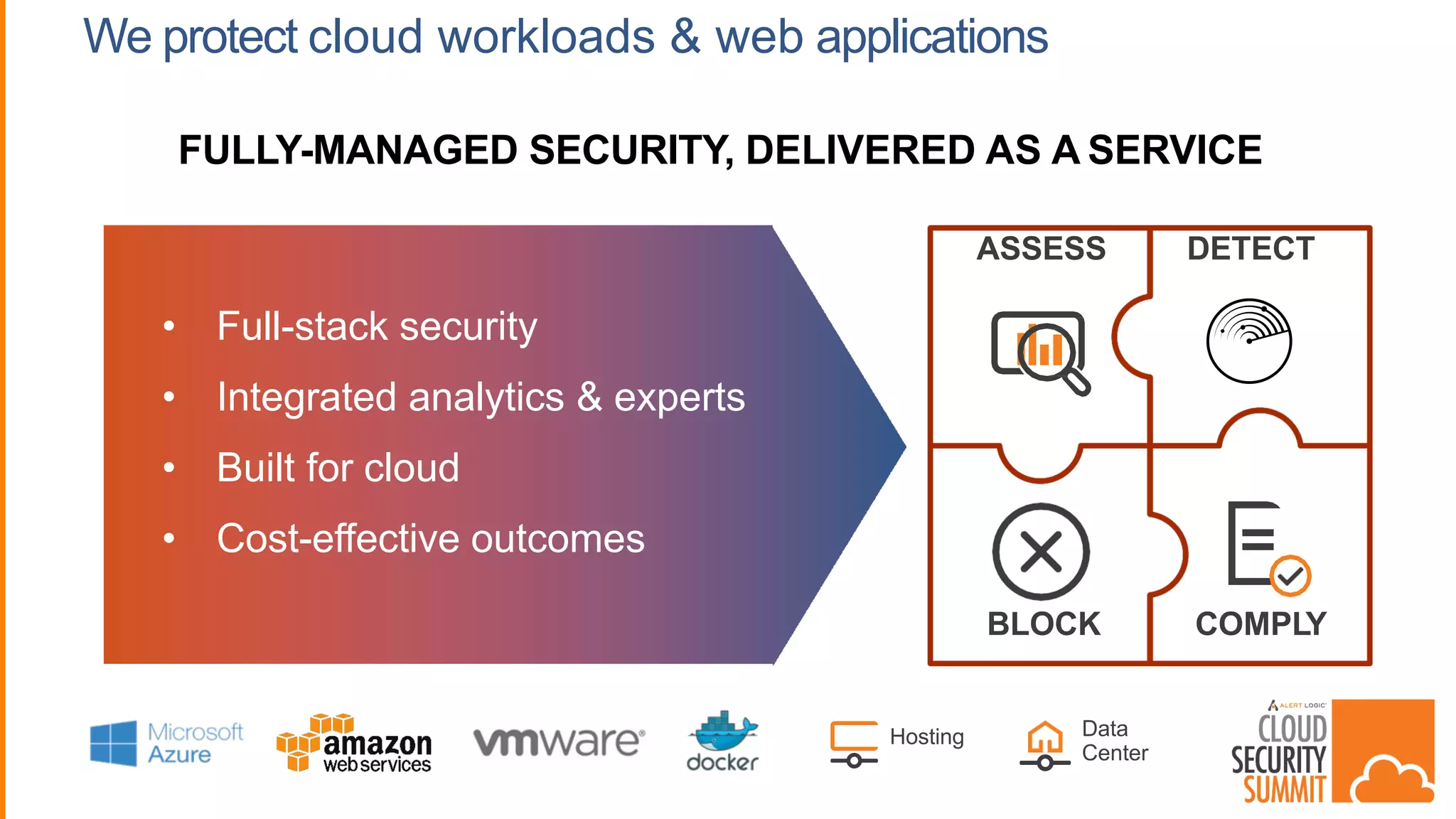
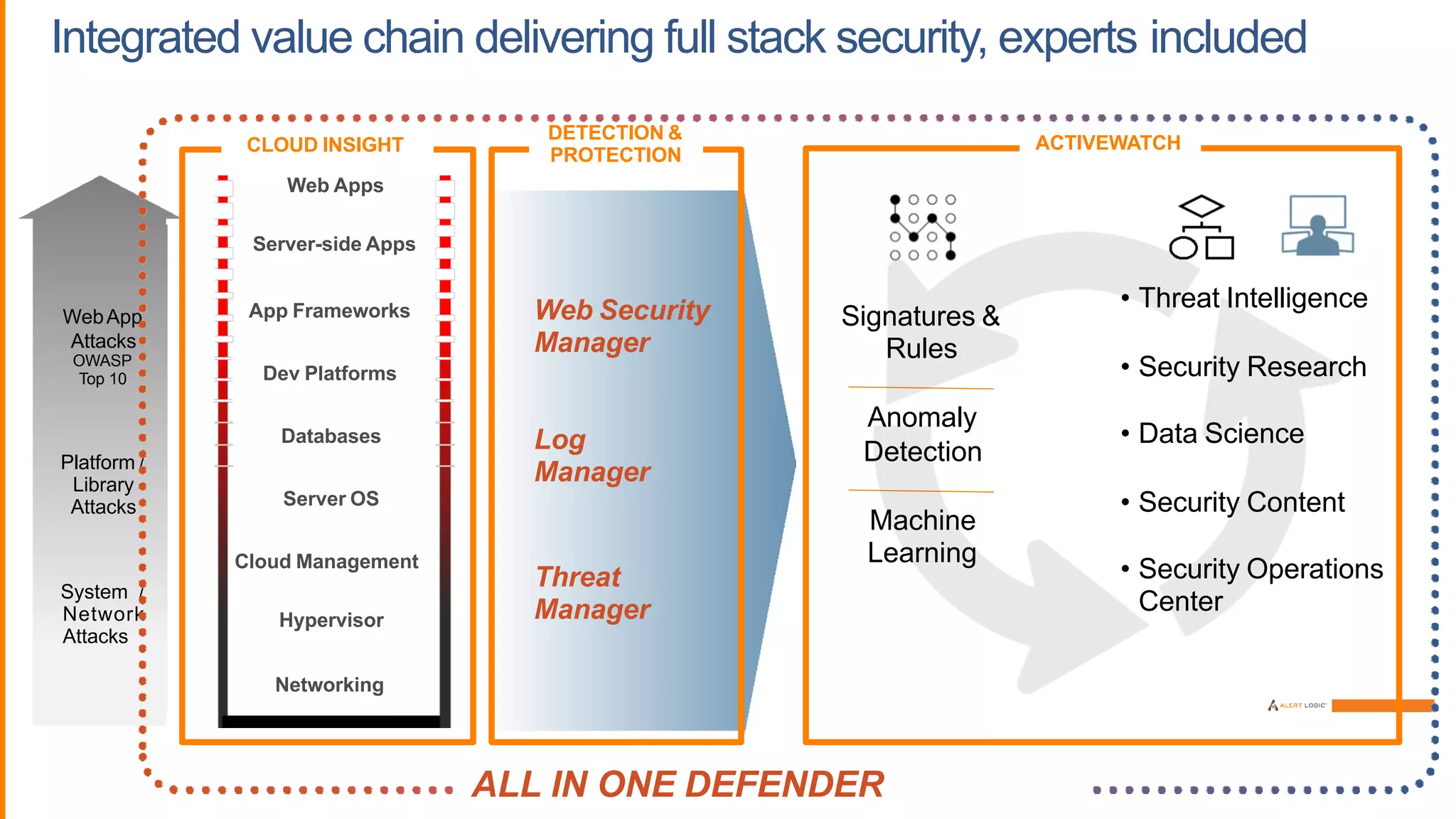
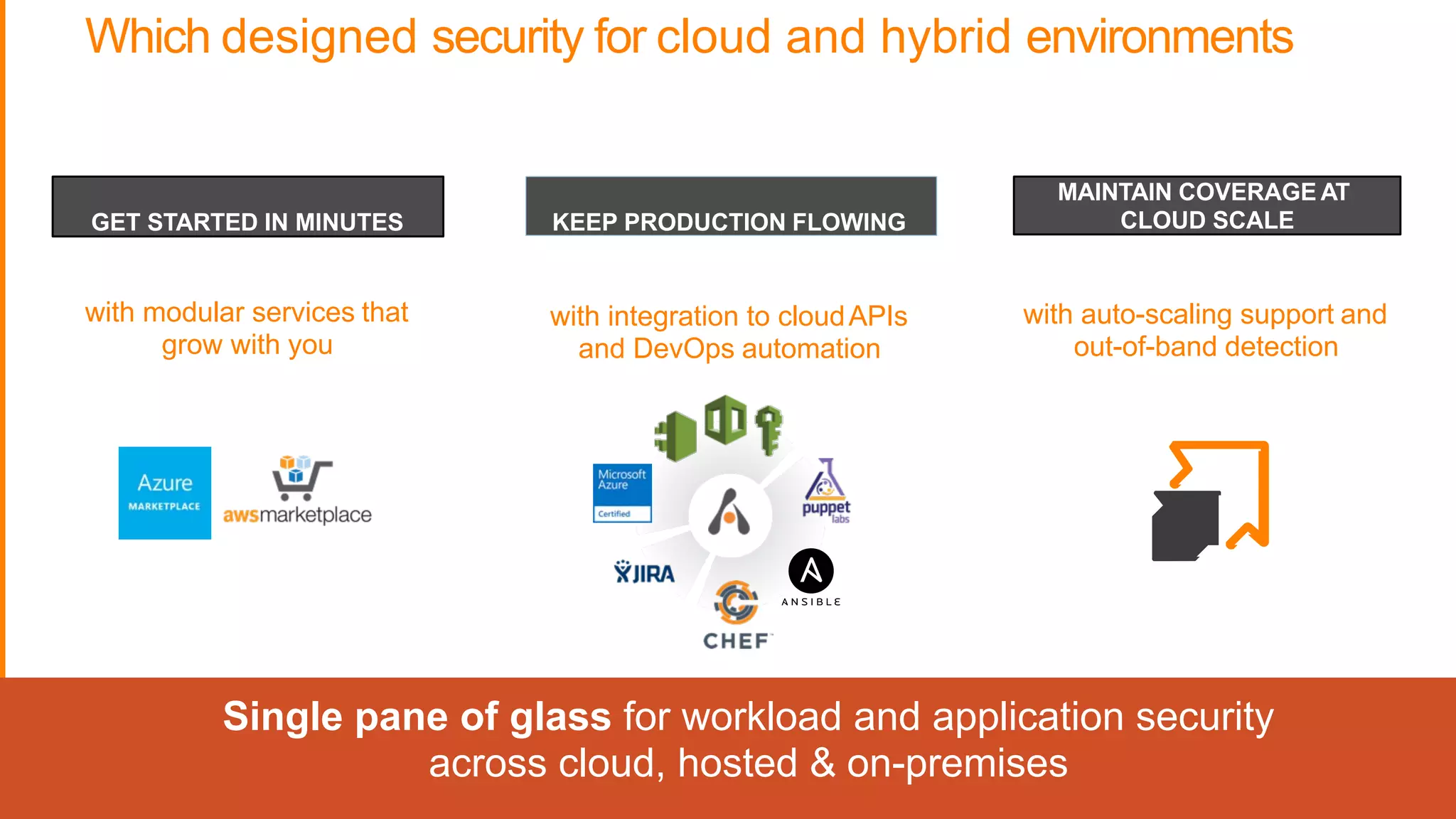
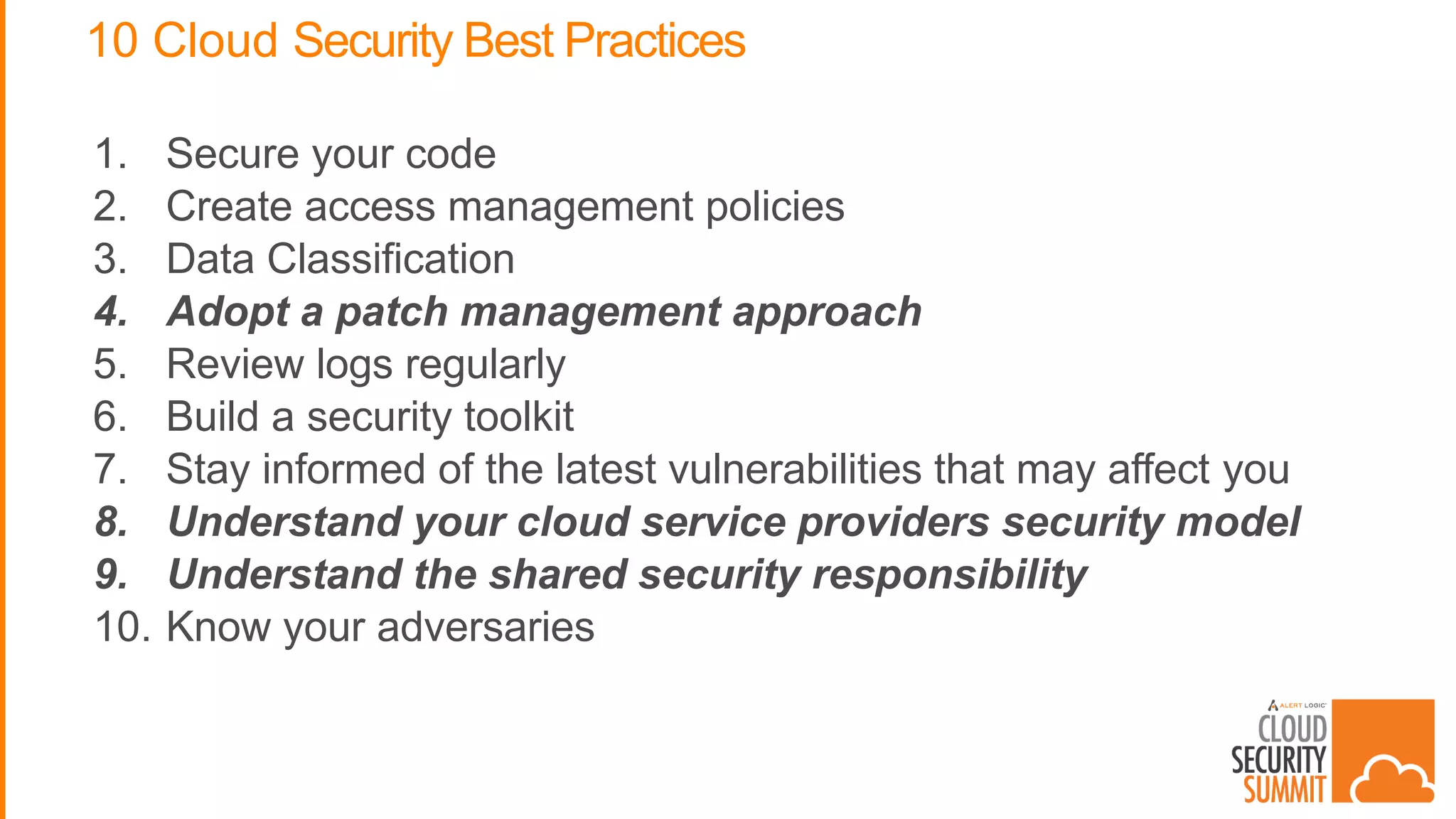
The document discusses system security when using cloud computing. It begins by describing the speaker's current big data system of over 10,000 users across 4 countries with over 1 billion user profiles and data ingested daily. It then discusses how infrastructure has changed from buying hardware to infrastructure as a service. Security has also changed, with cybercrime flourishing using organized groups. The rest of the document provides best practices for cloud security, such as understanding shared responsibilities and knowing your adversaries. It also promotes the services of Alert Logic for protecting cloud workloads and applications.