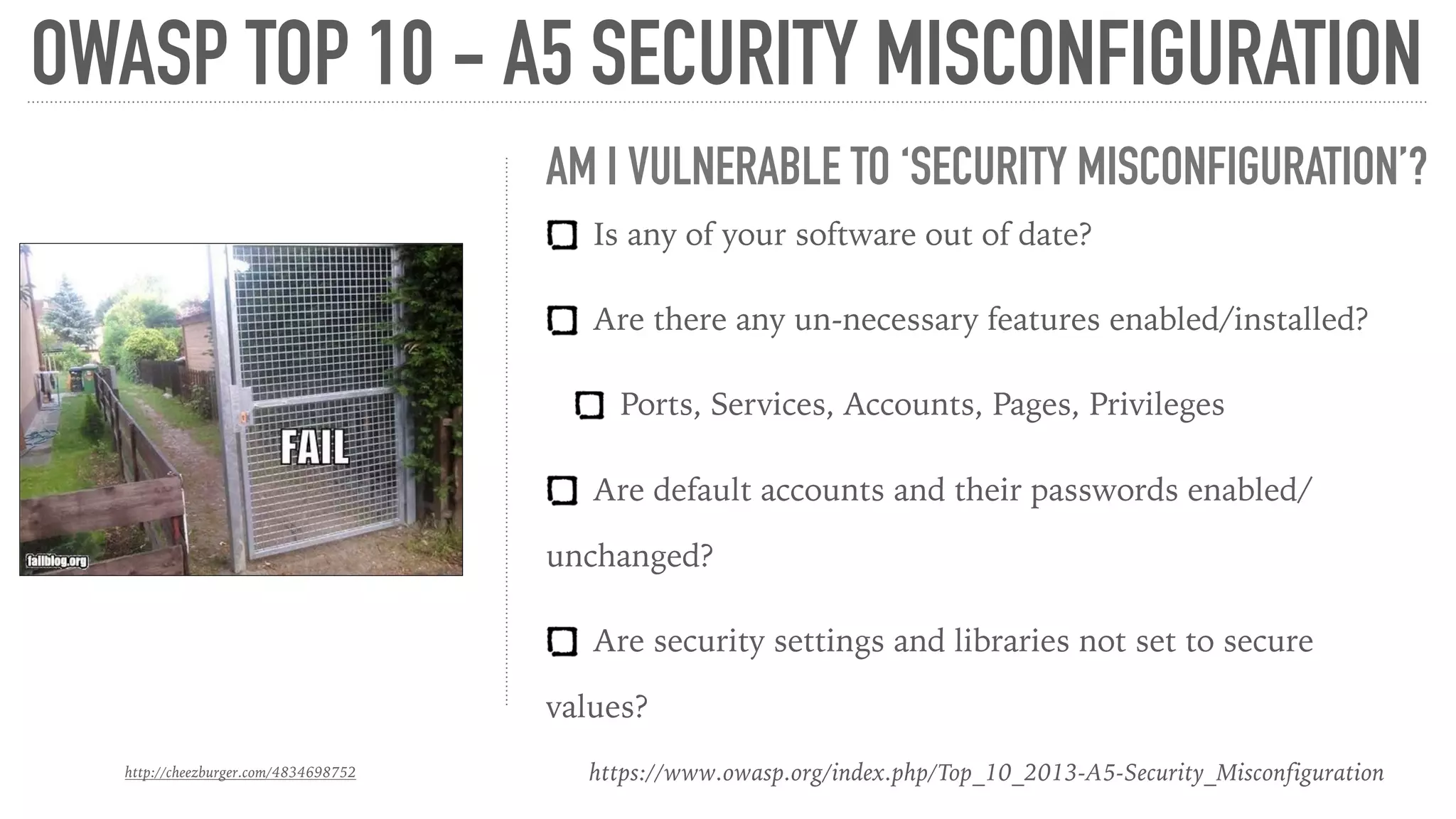
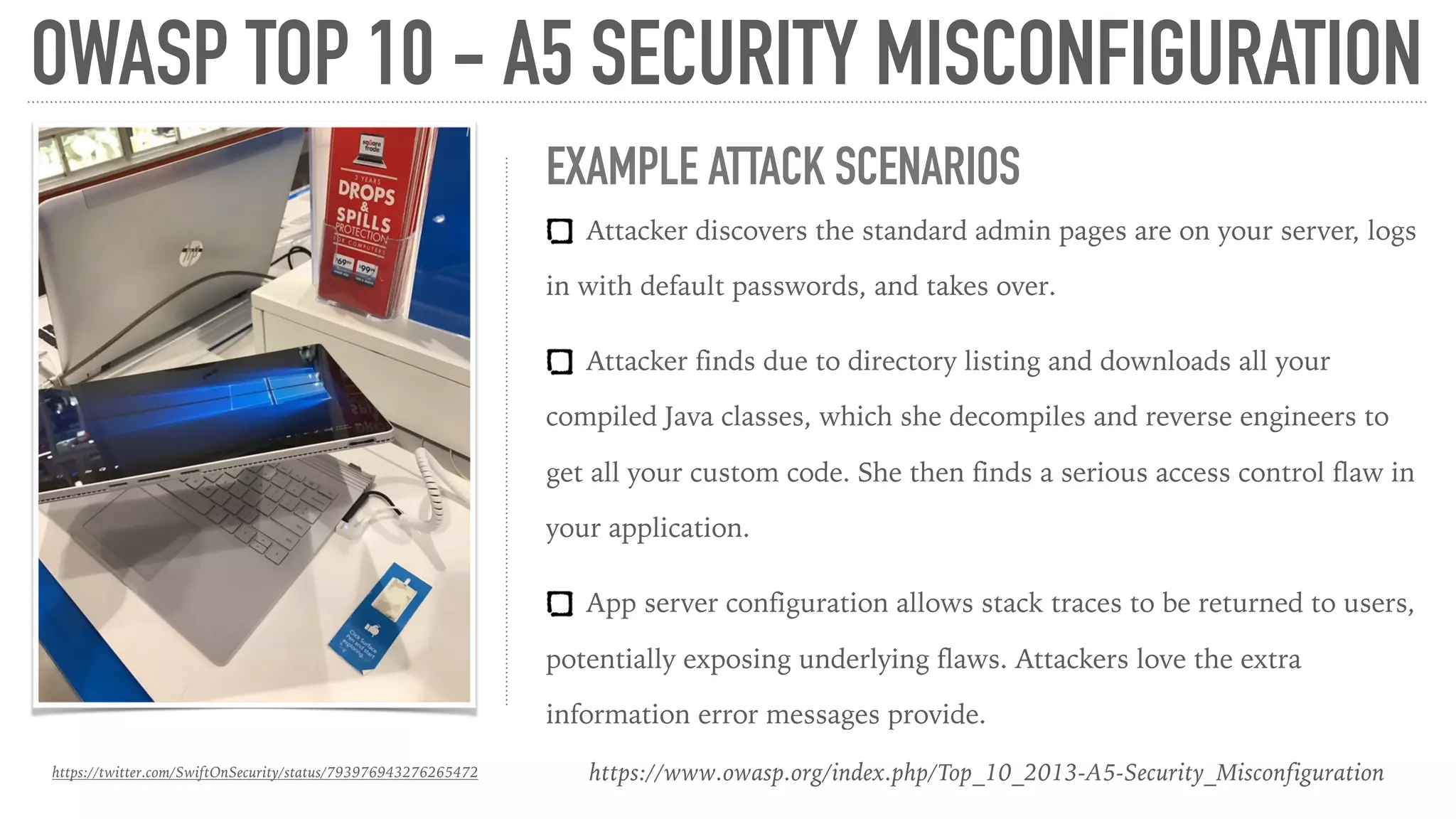
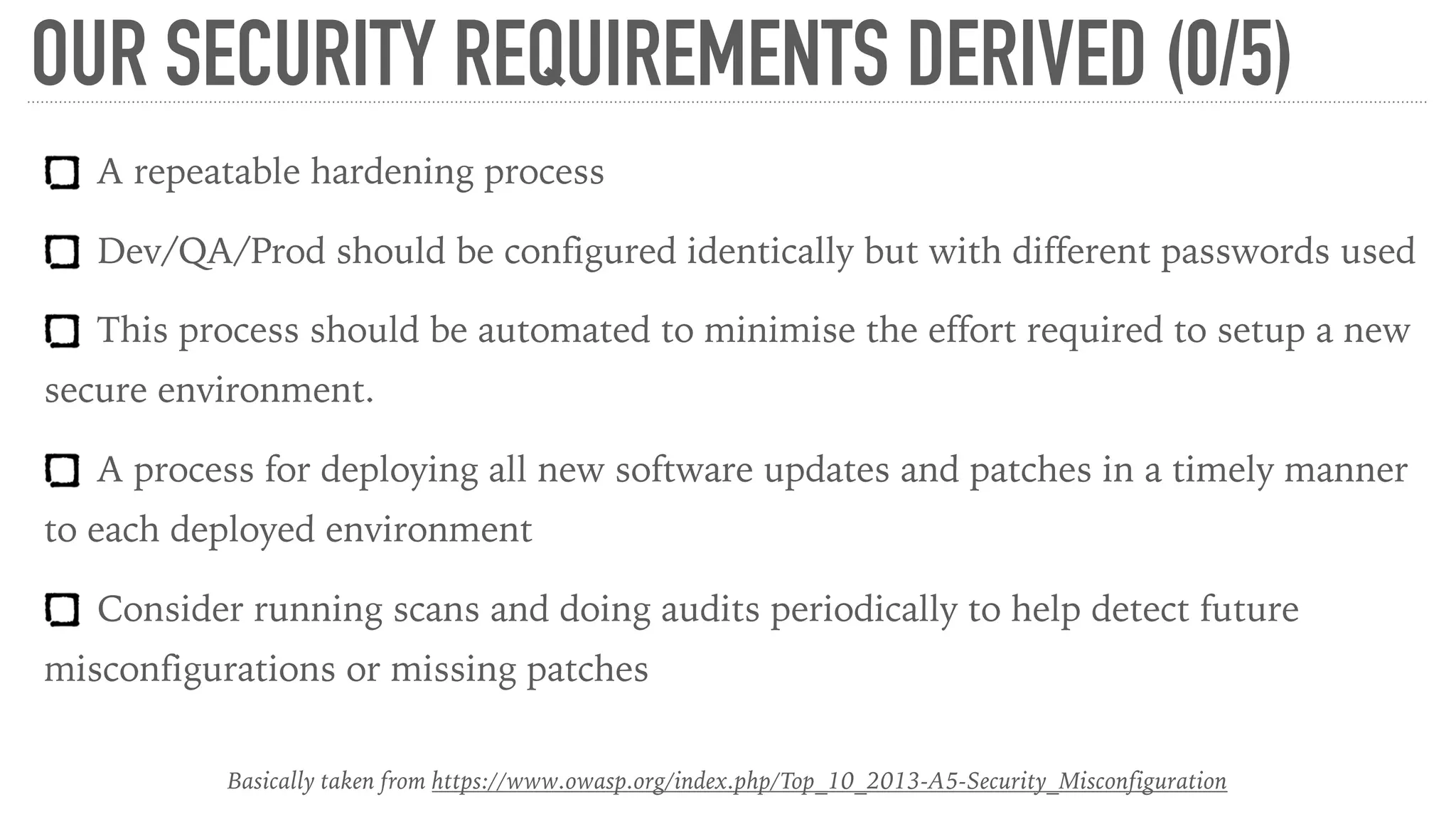
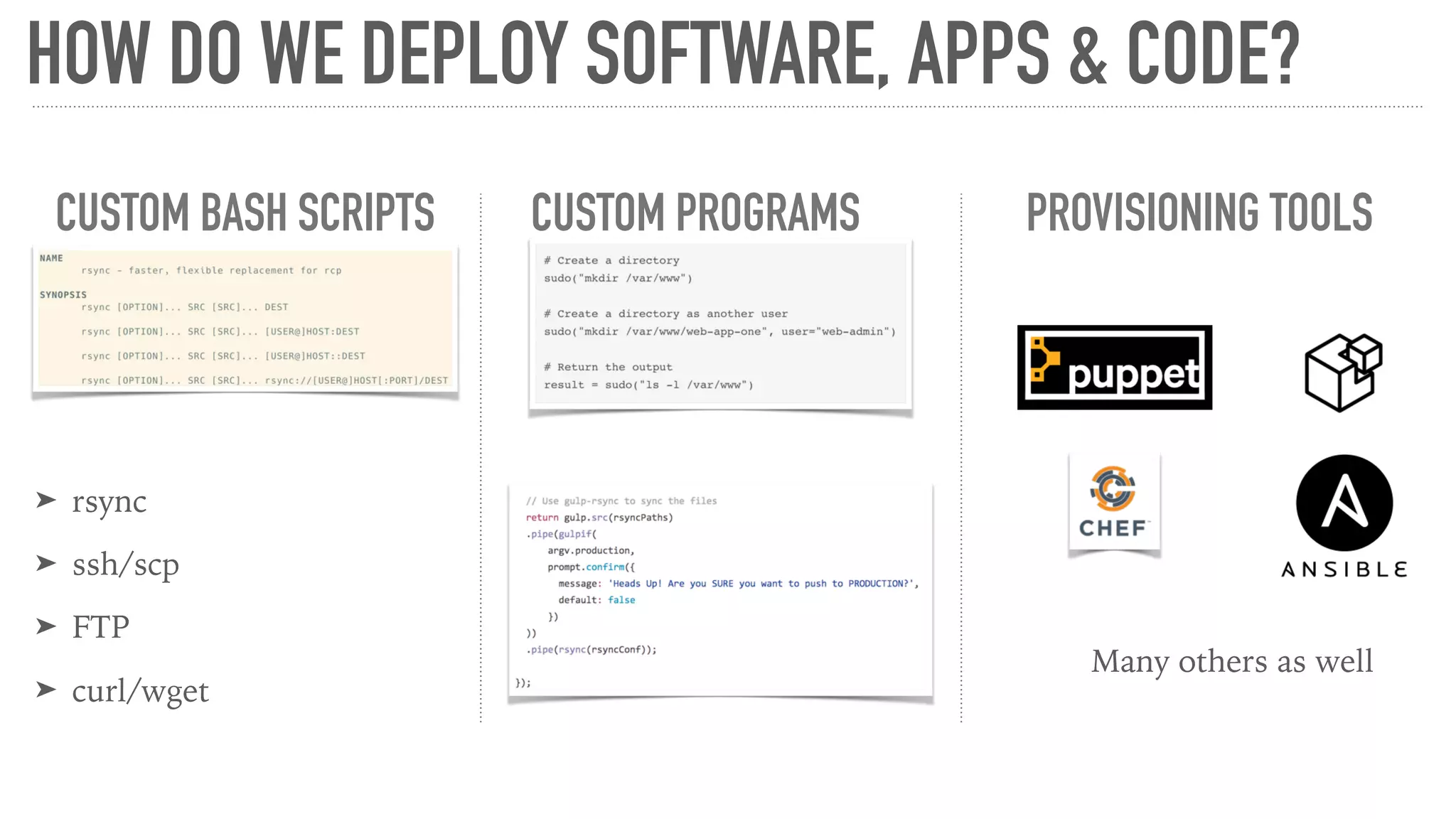
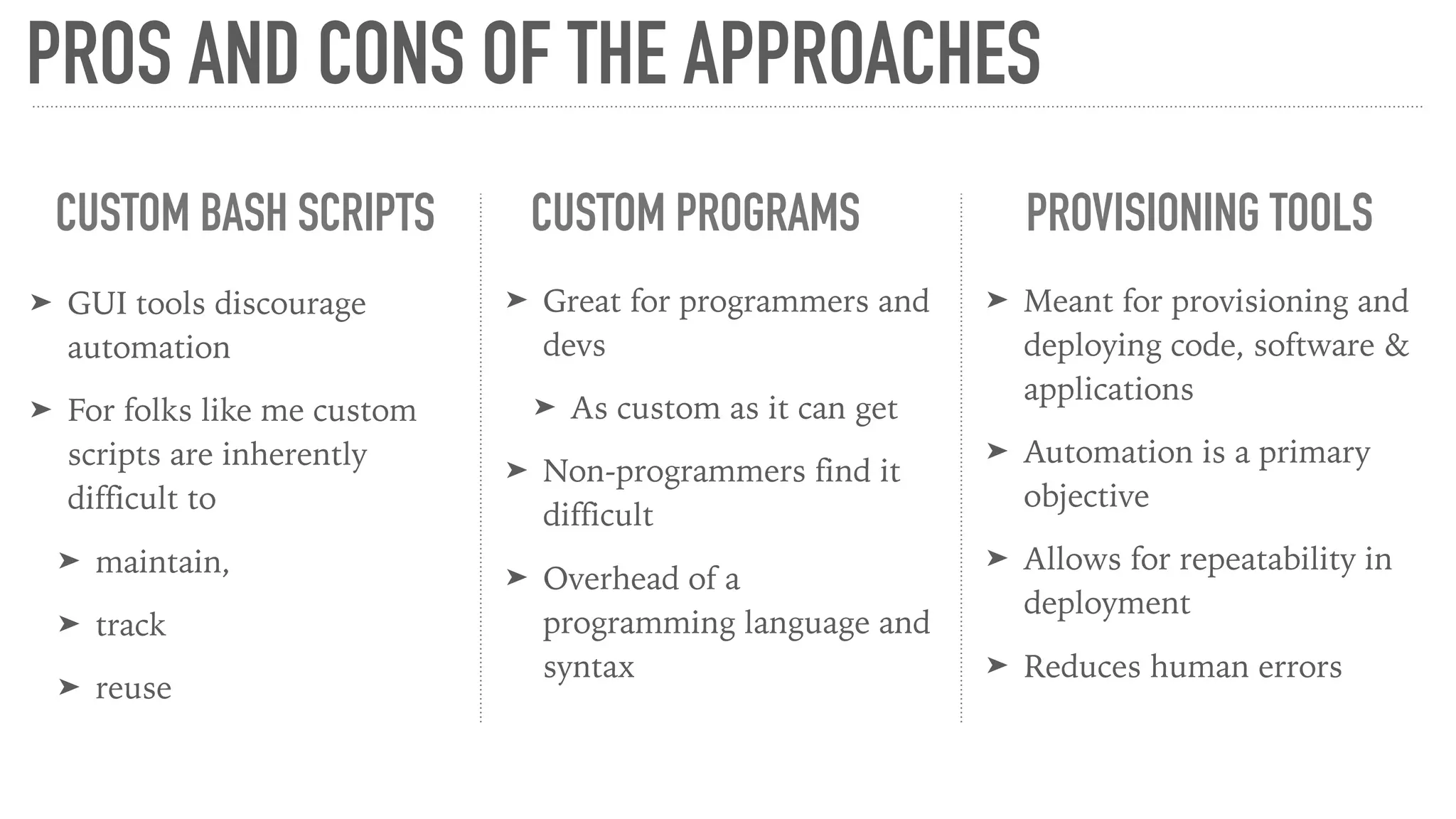
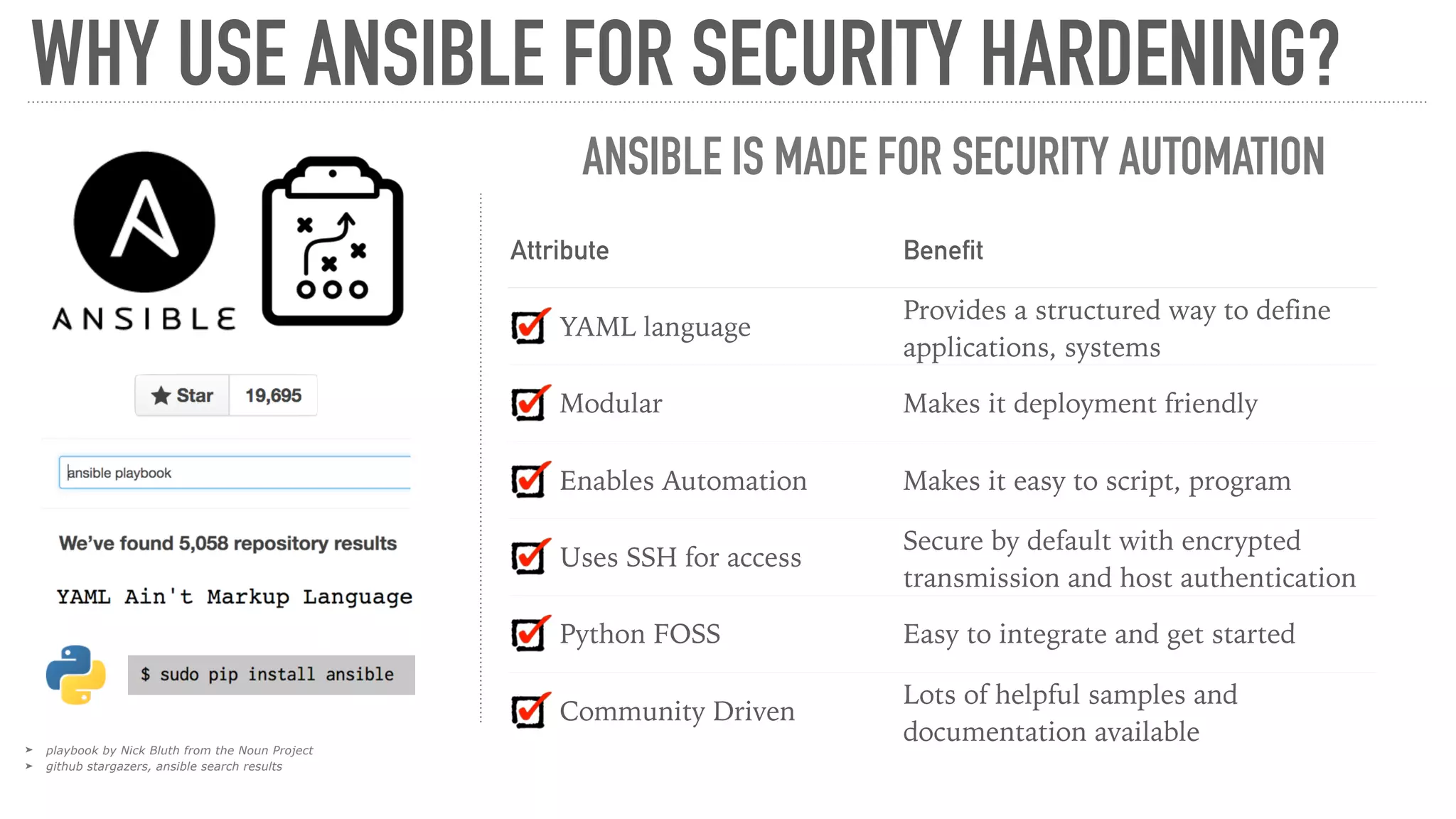
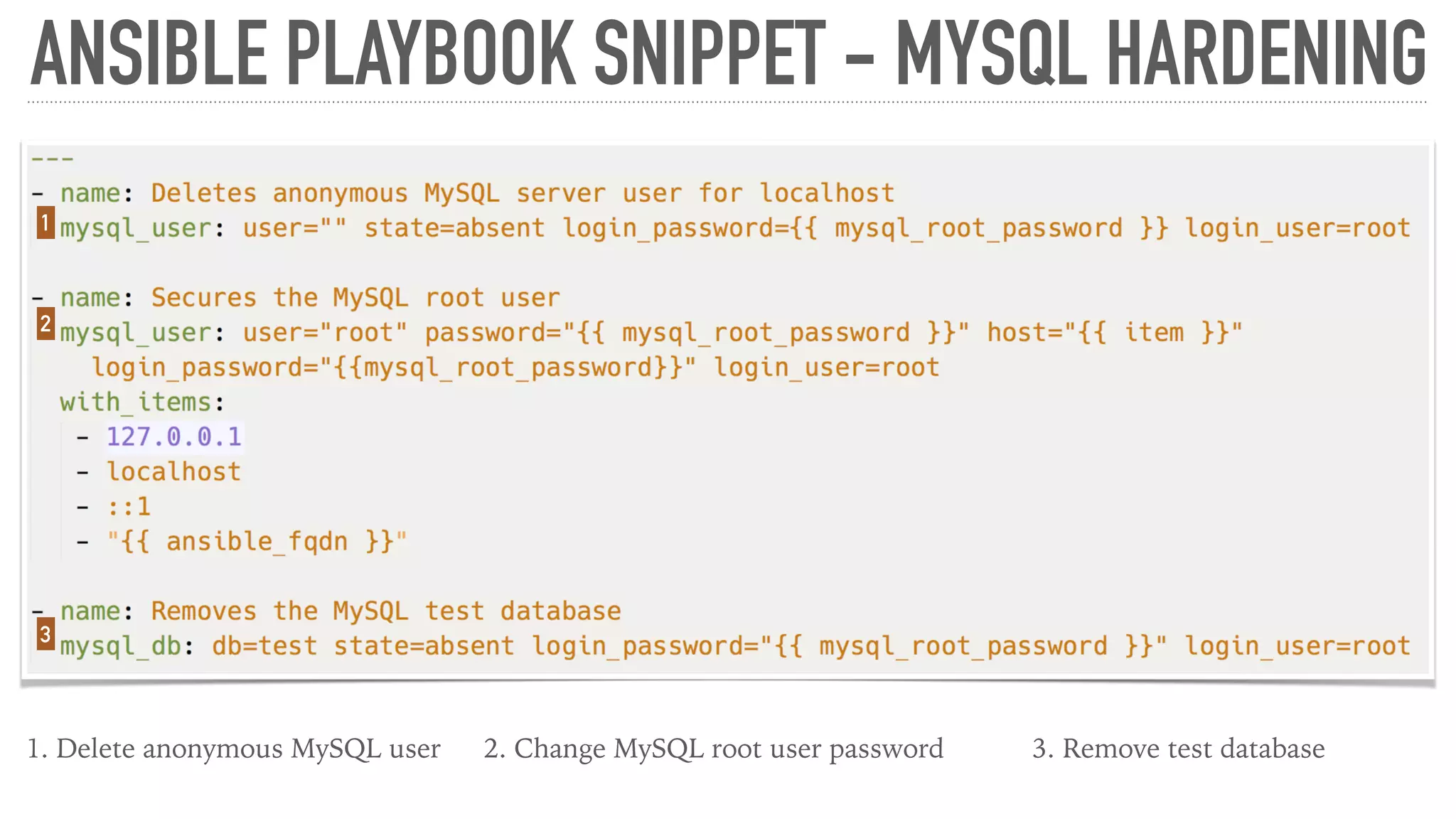
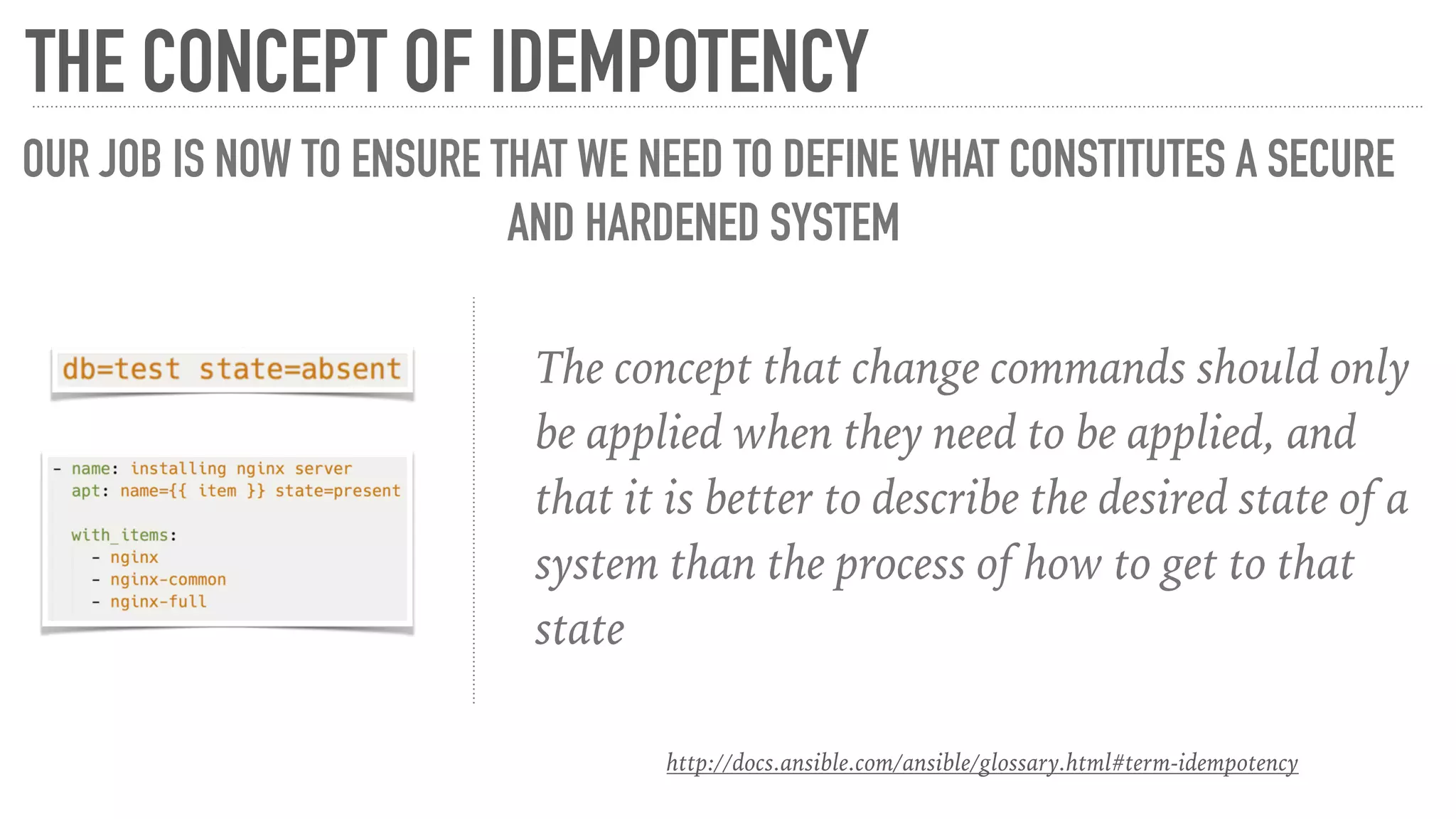
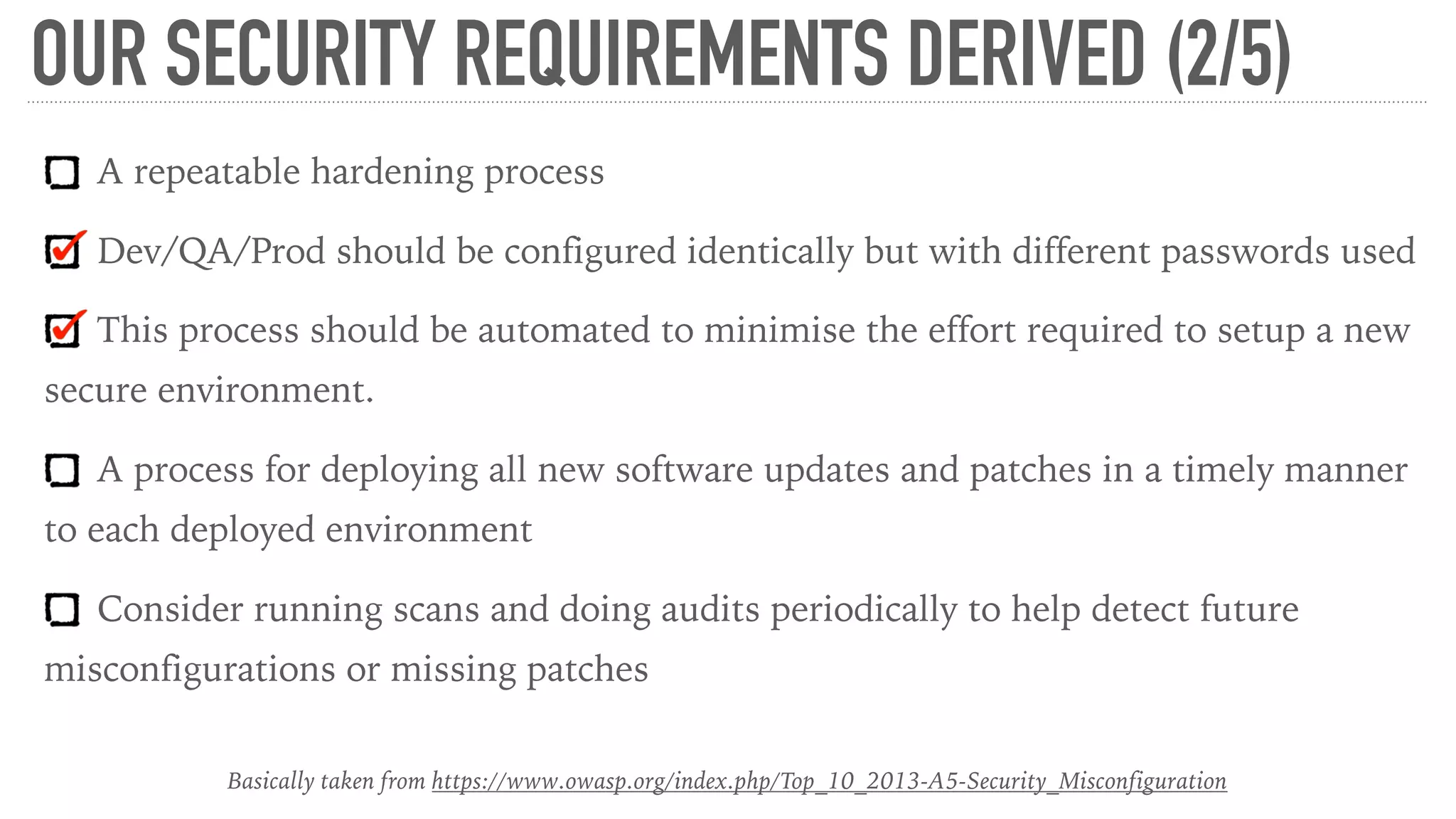
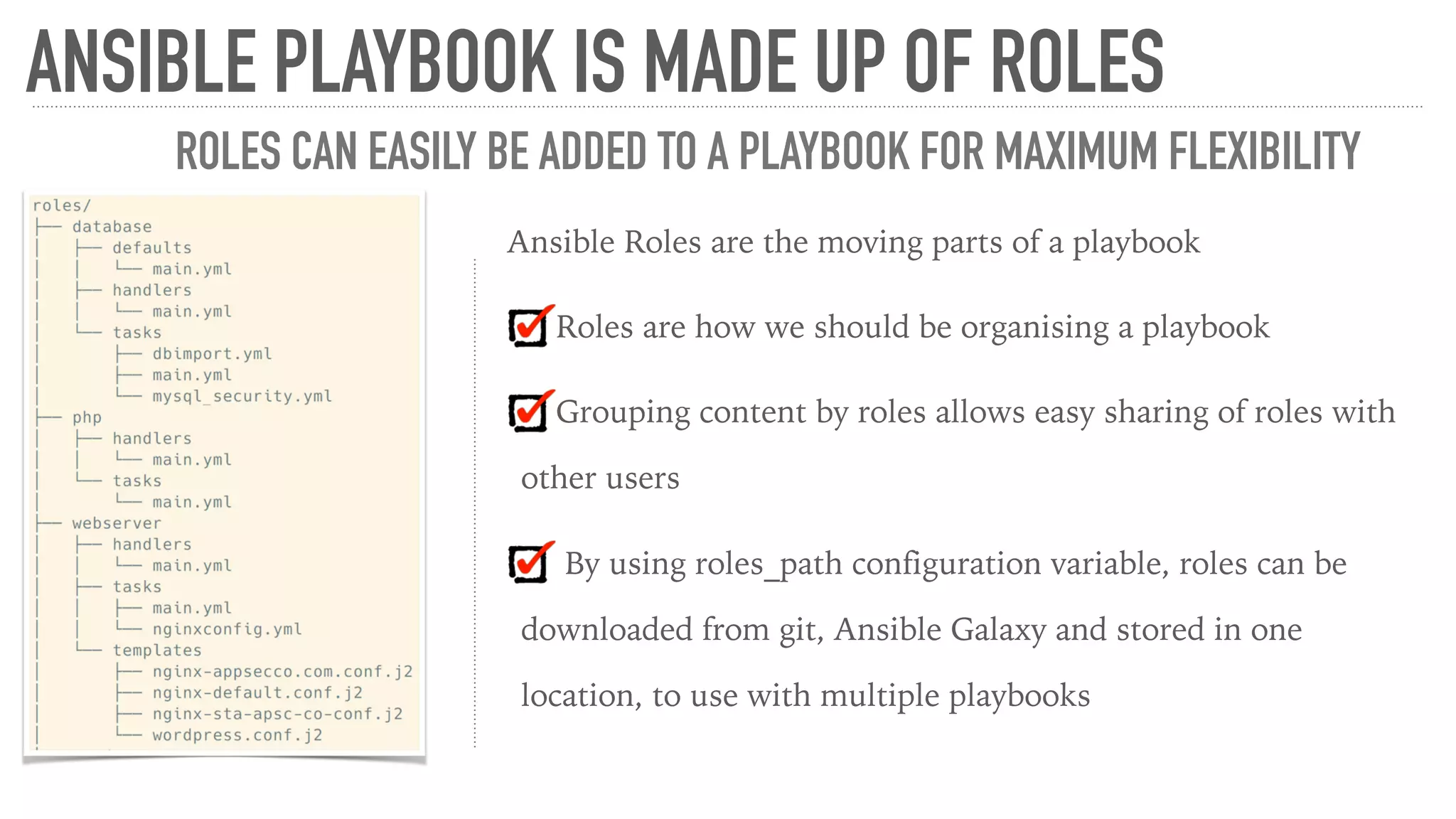
The document discusses the importance of security hardening for applications using Ansible for automated deployment and configuration management. It outlines common vulnerabilities related to security misconfiguration as per OWASP's top 10, offers strategies for establishing repeatable hardening processes, and emphasizes the need for continuous monitoring and timely software updates. The text also highlights the benefits of using best practices and existing resources from the community for enhanced security automation workflows.