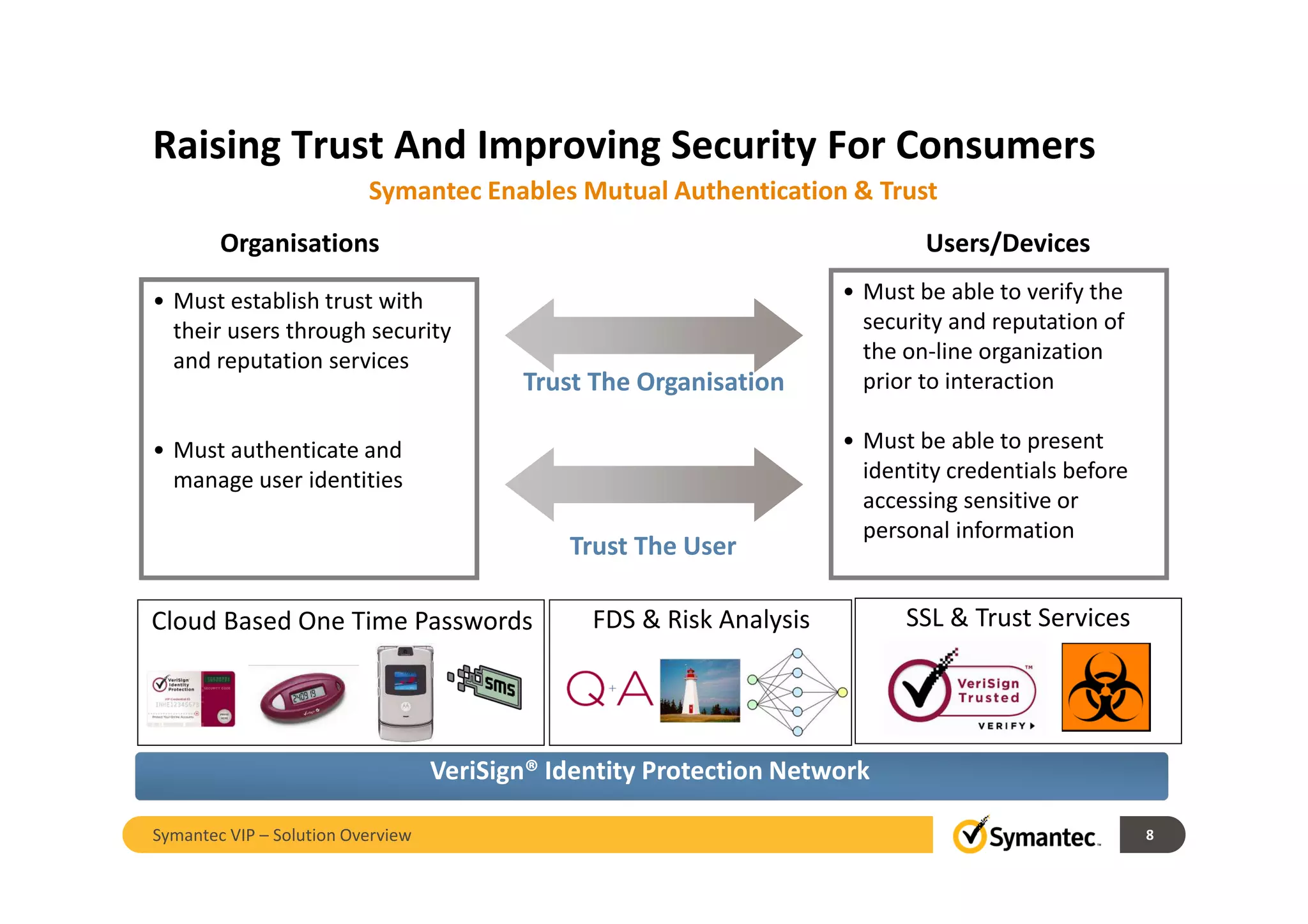
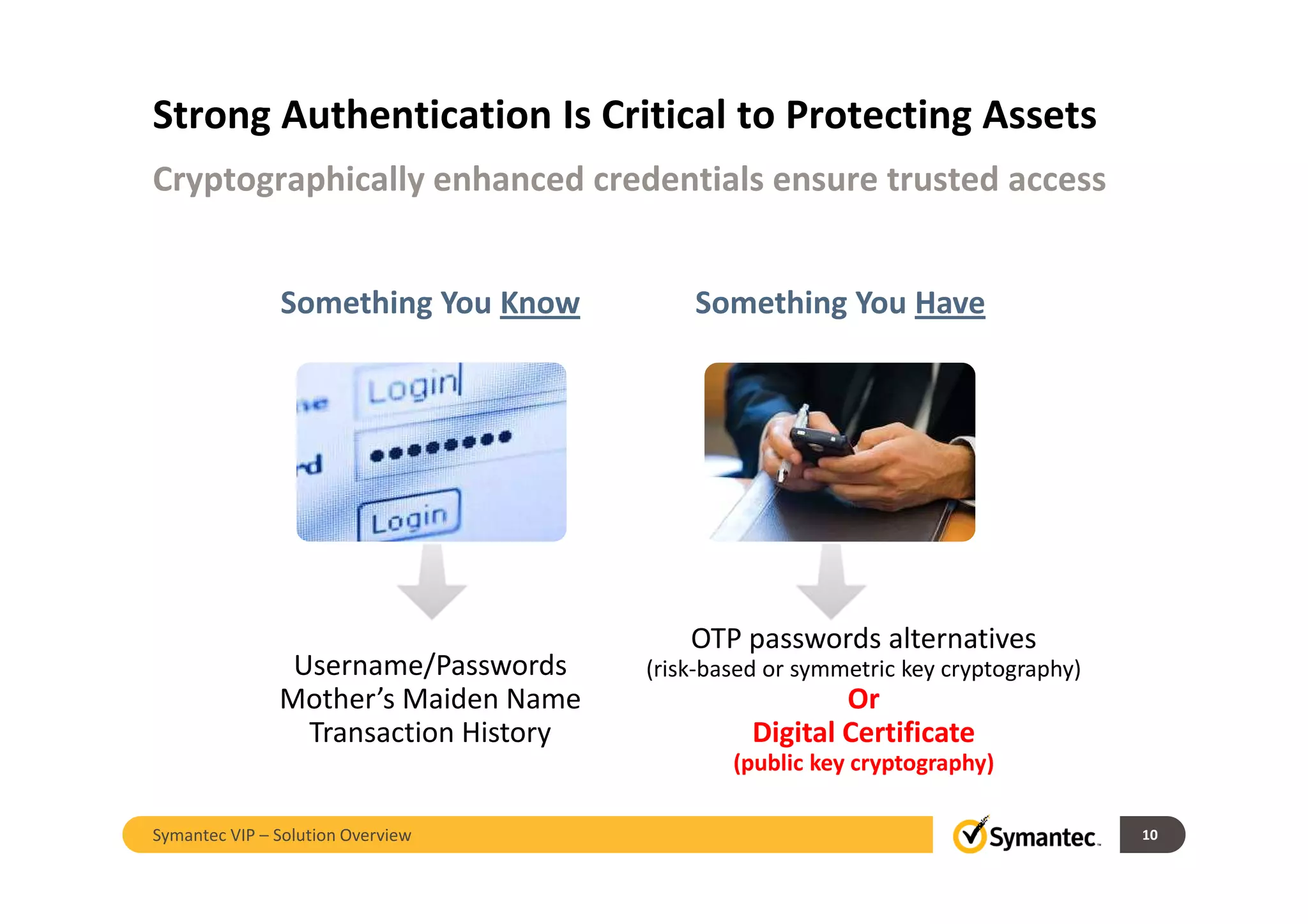
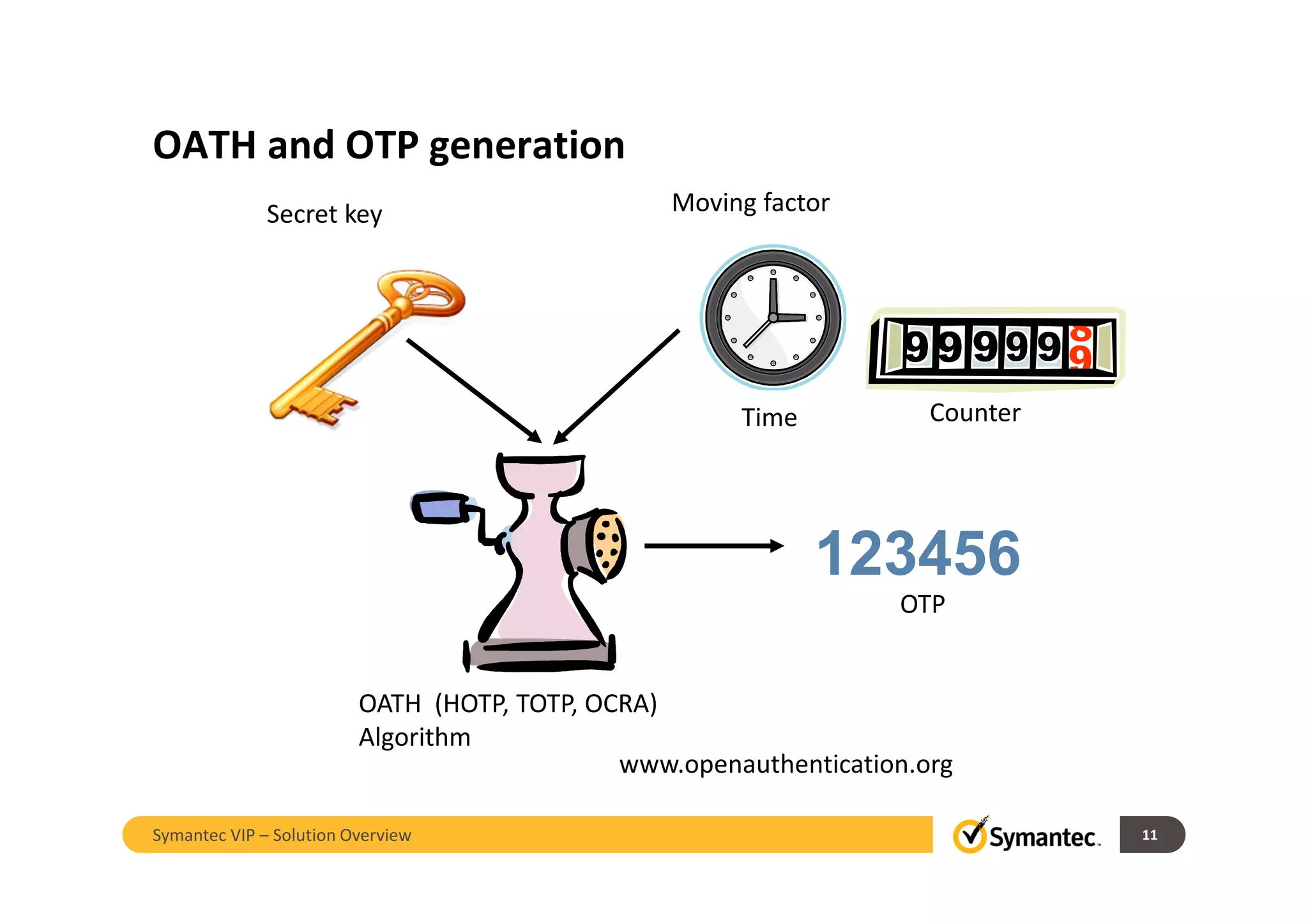
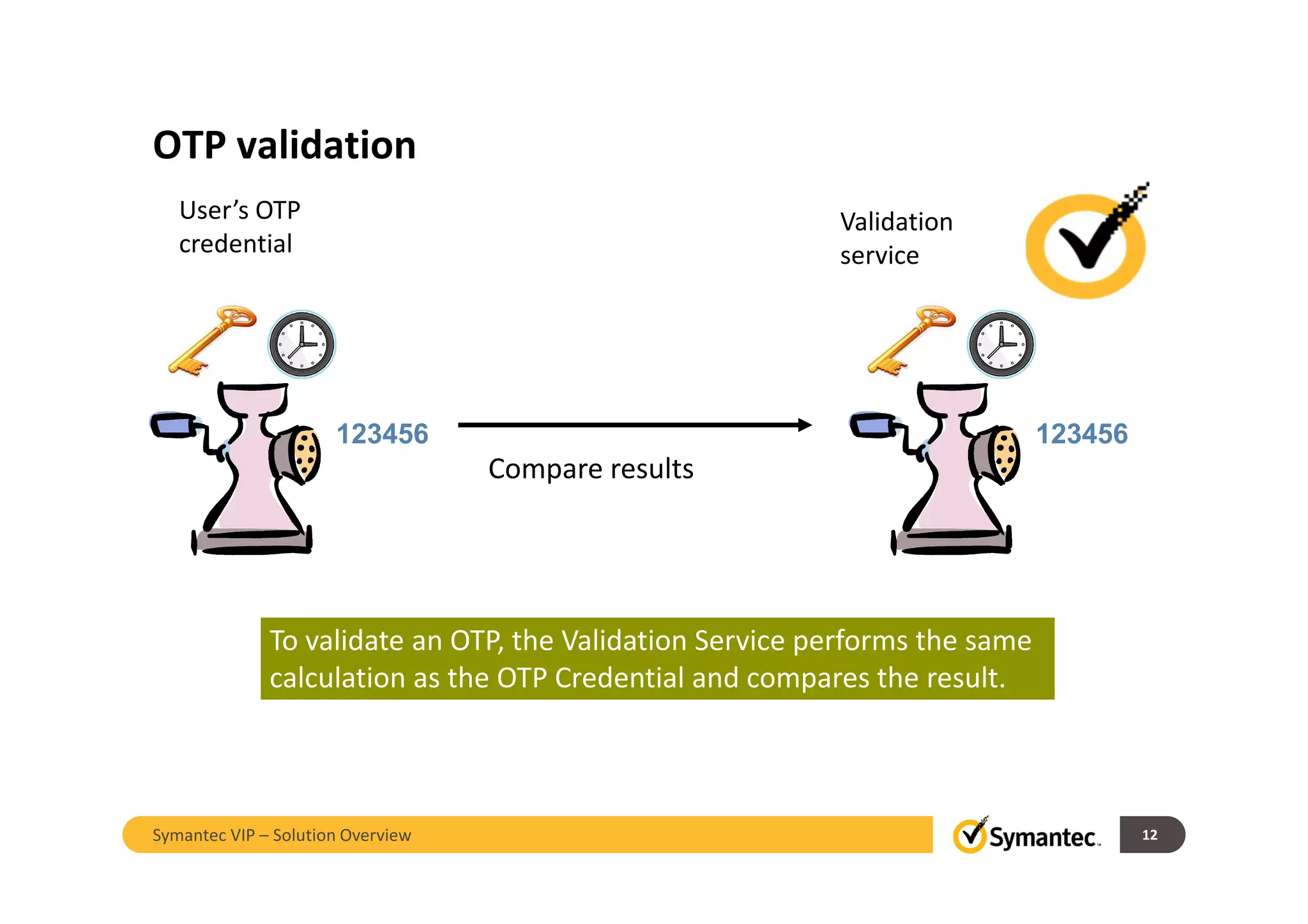
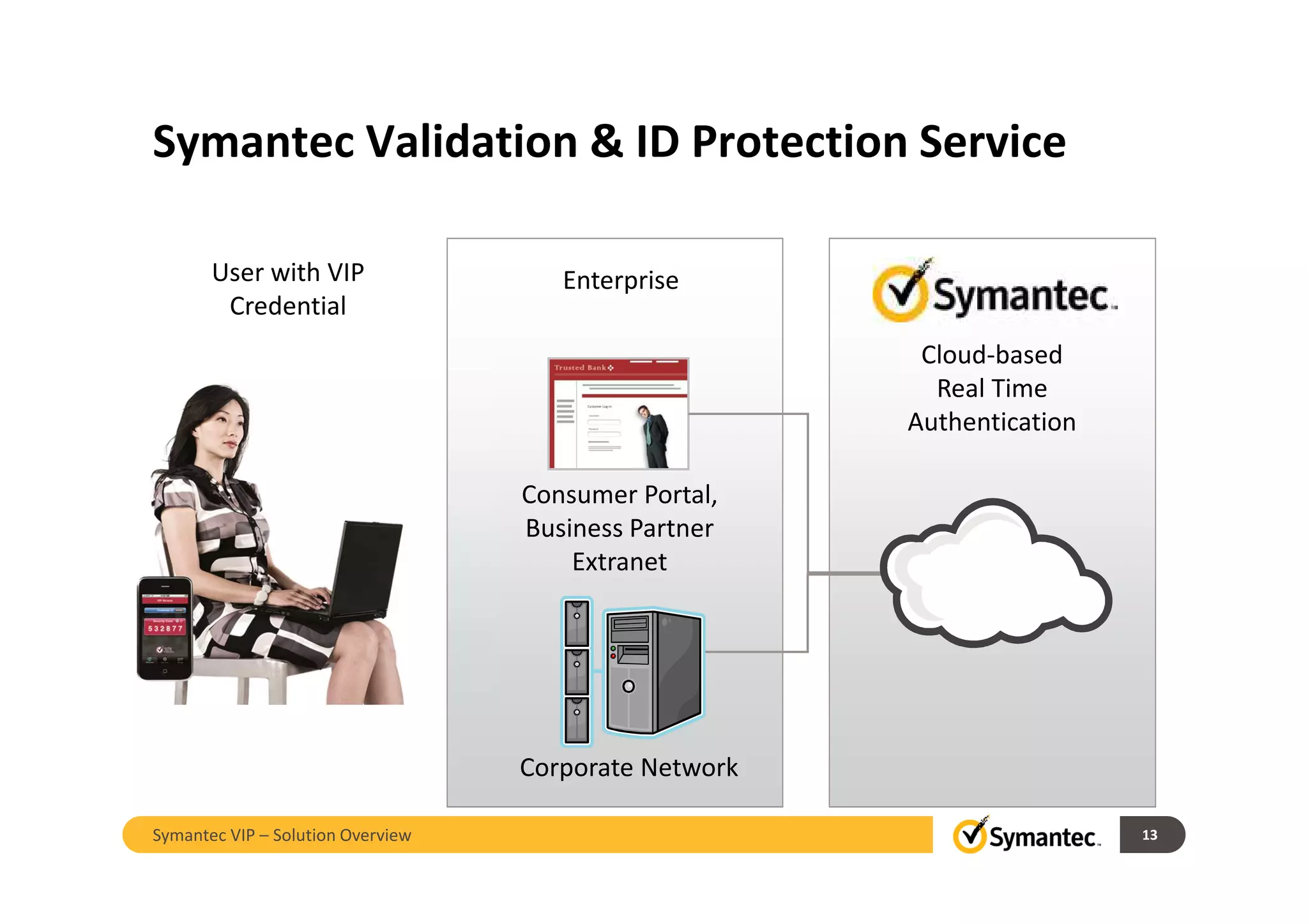
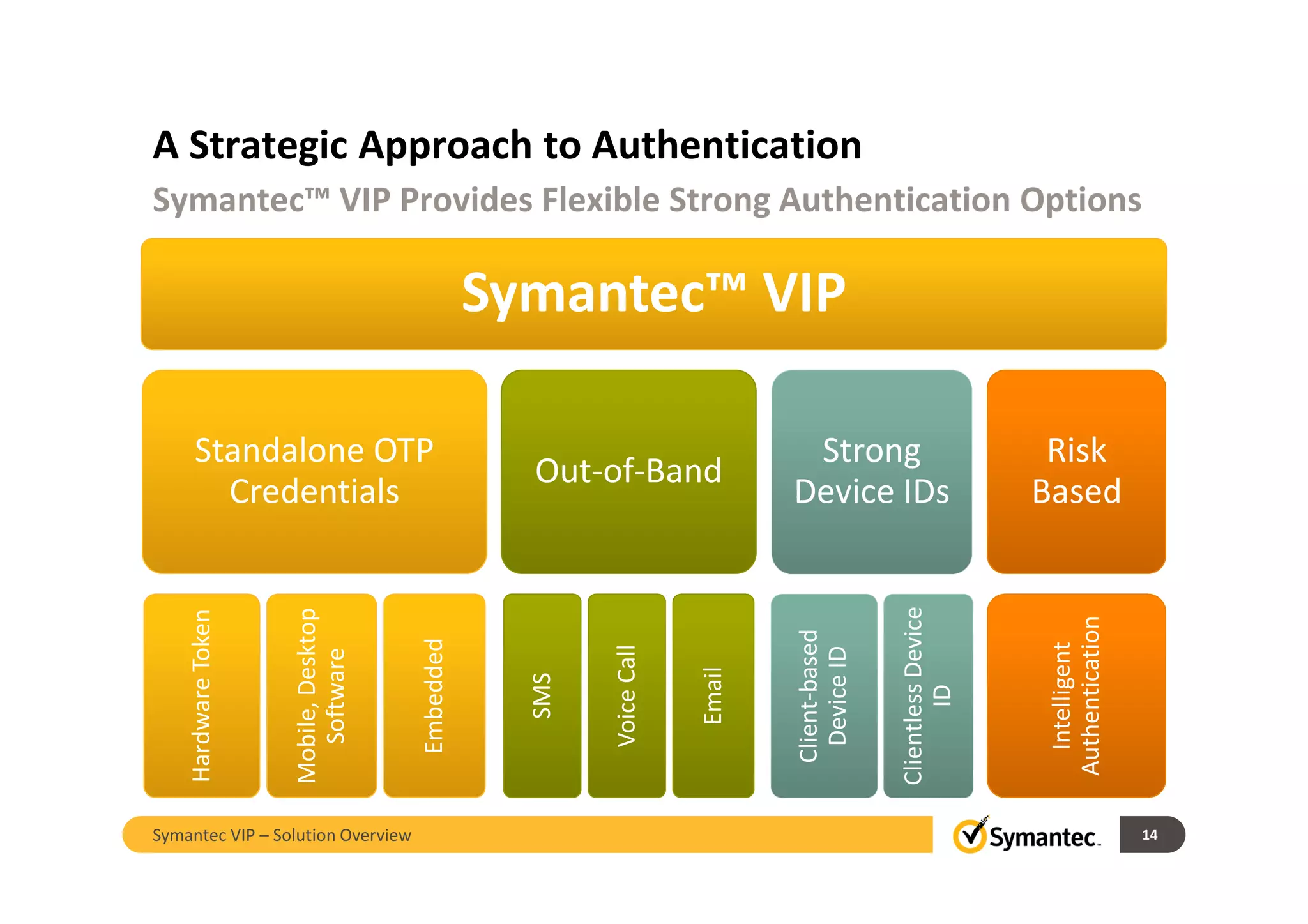
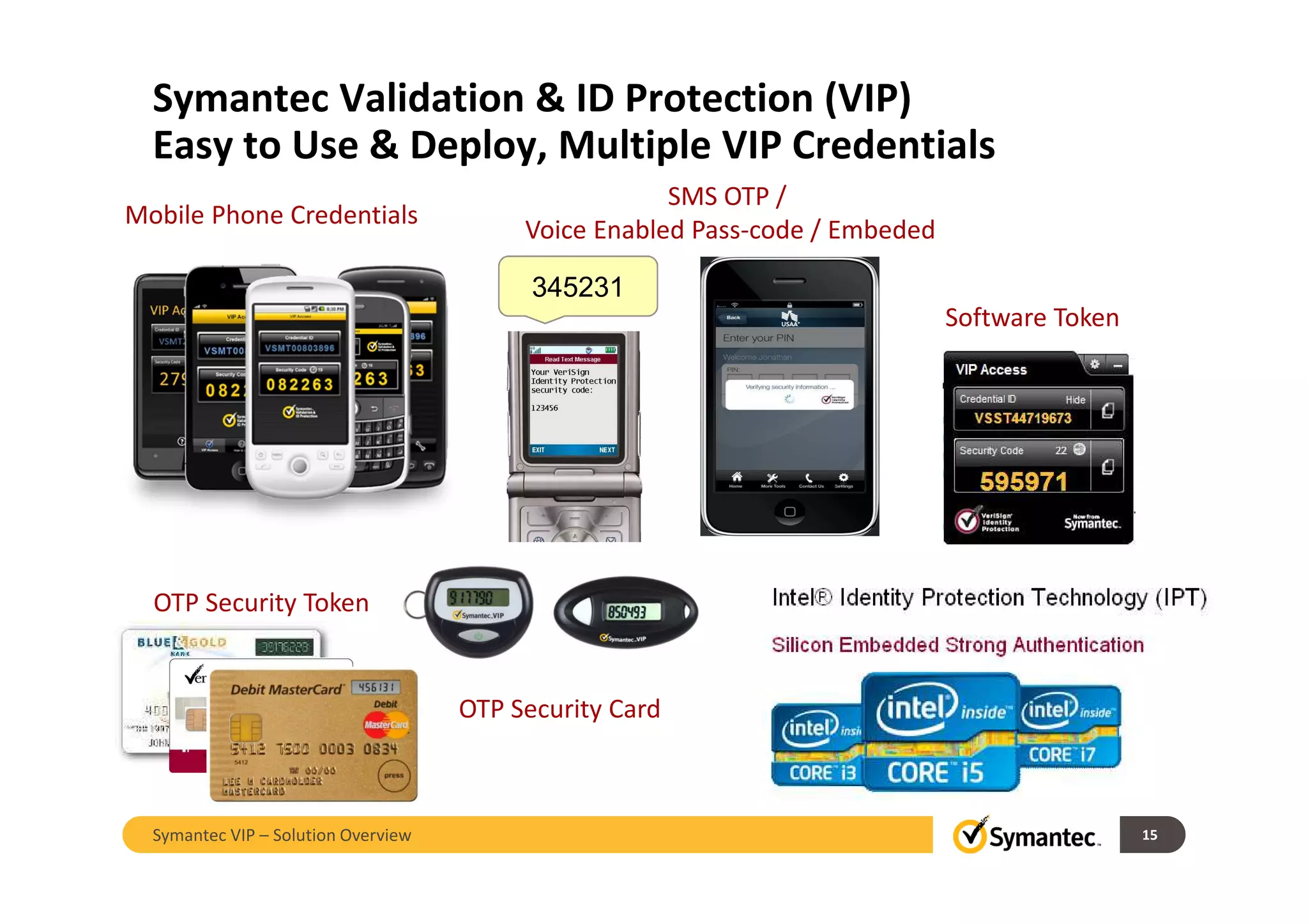
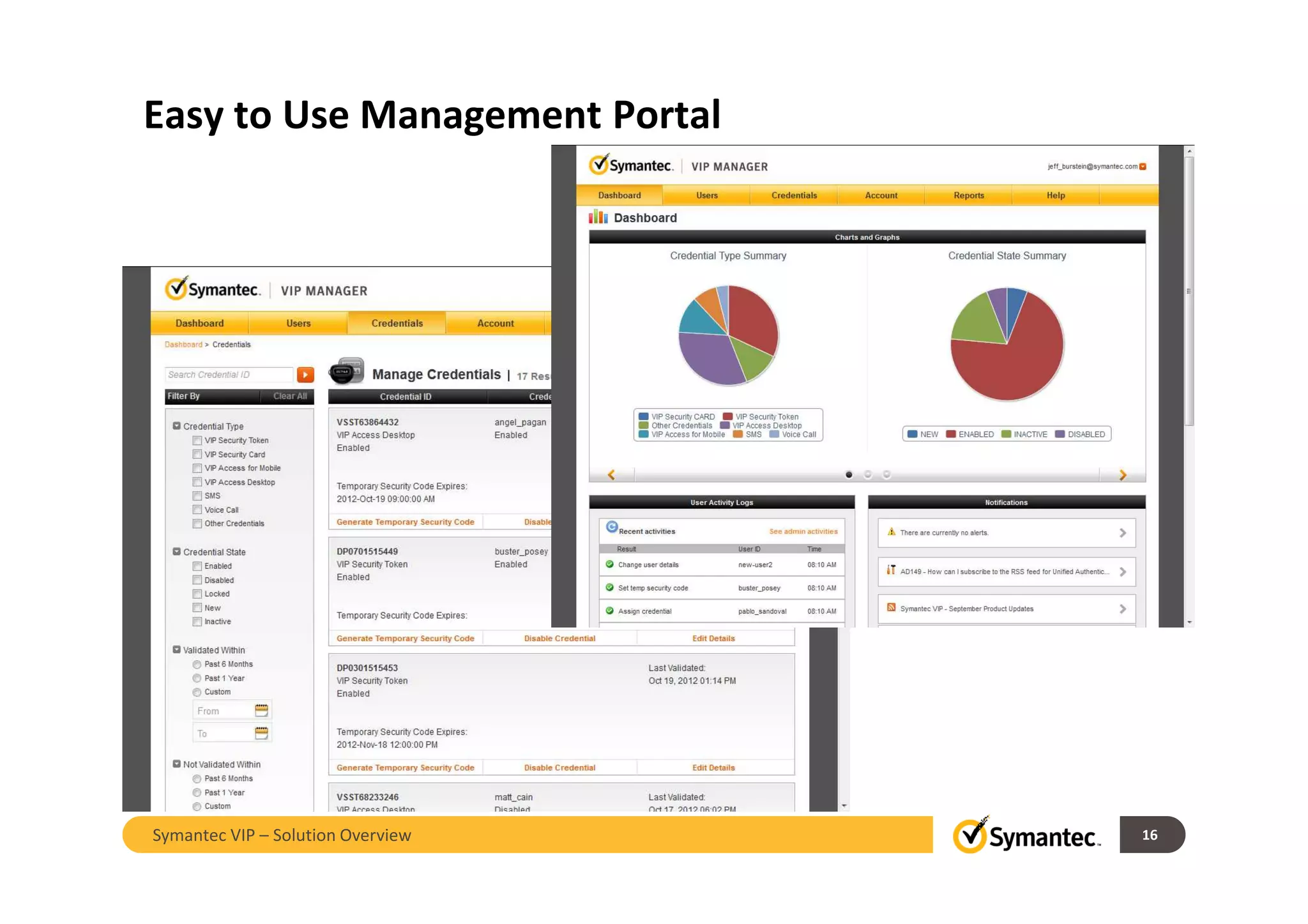
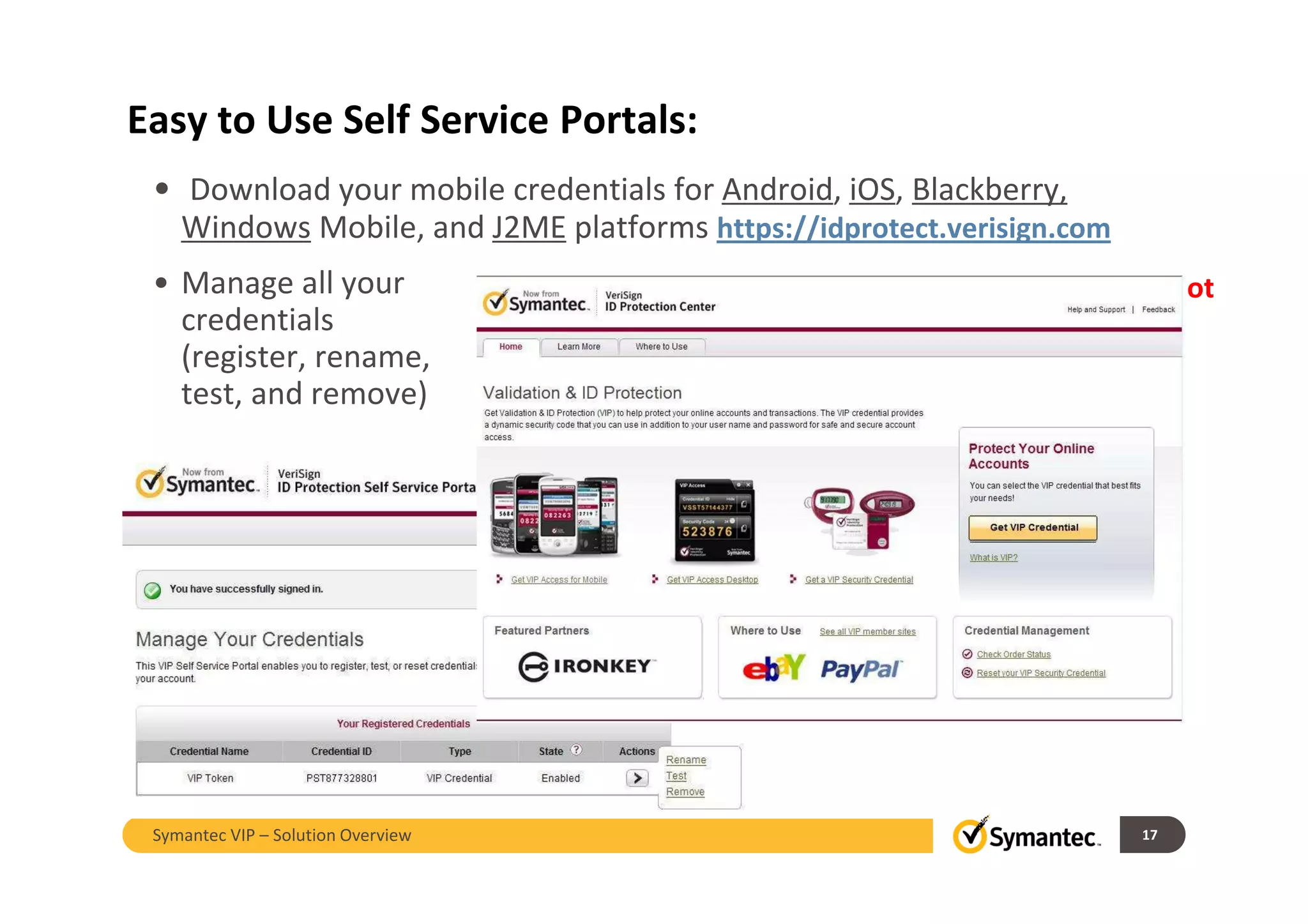
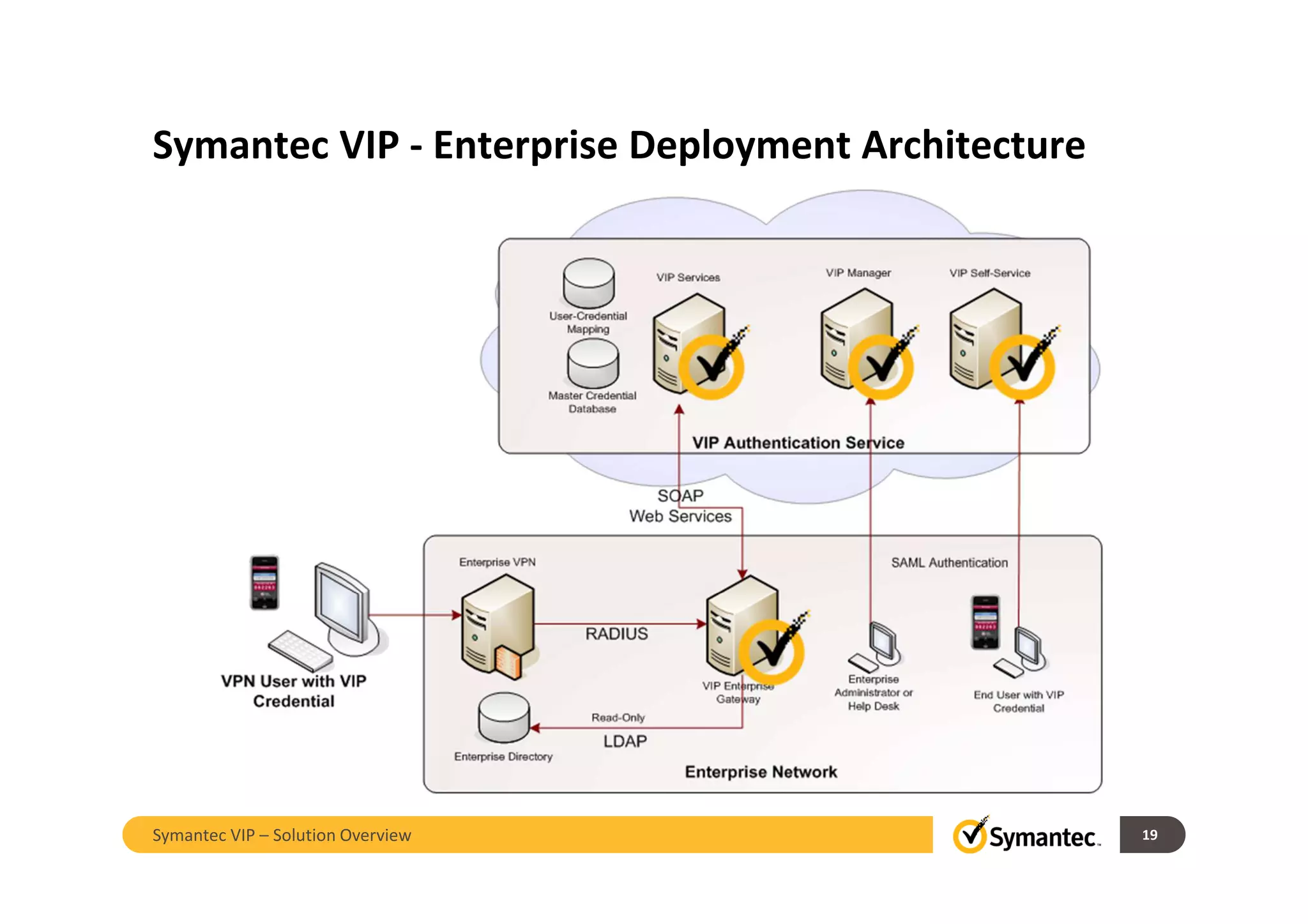
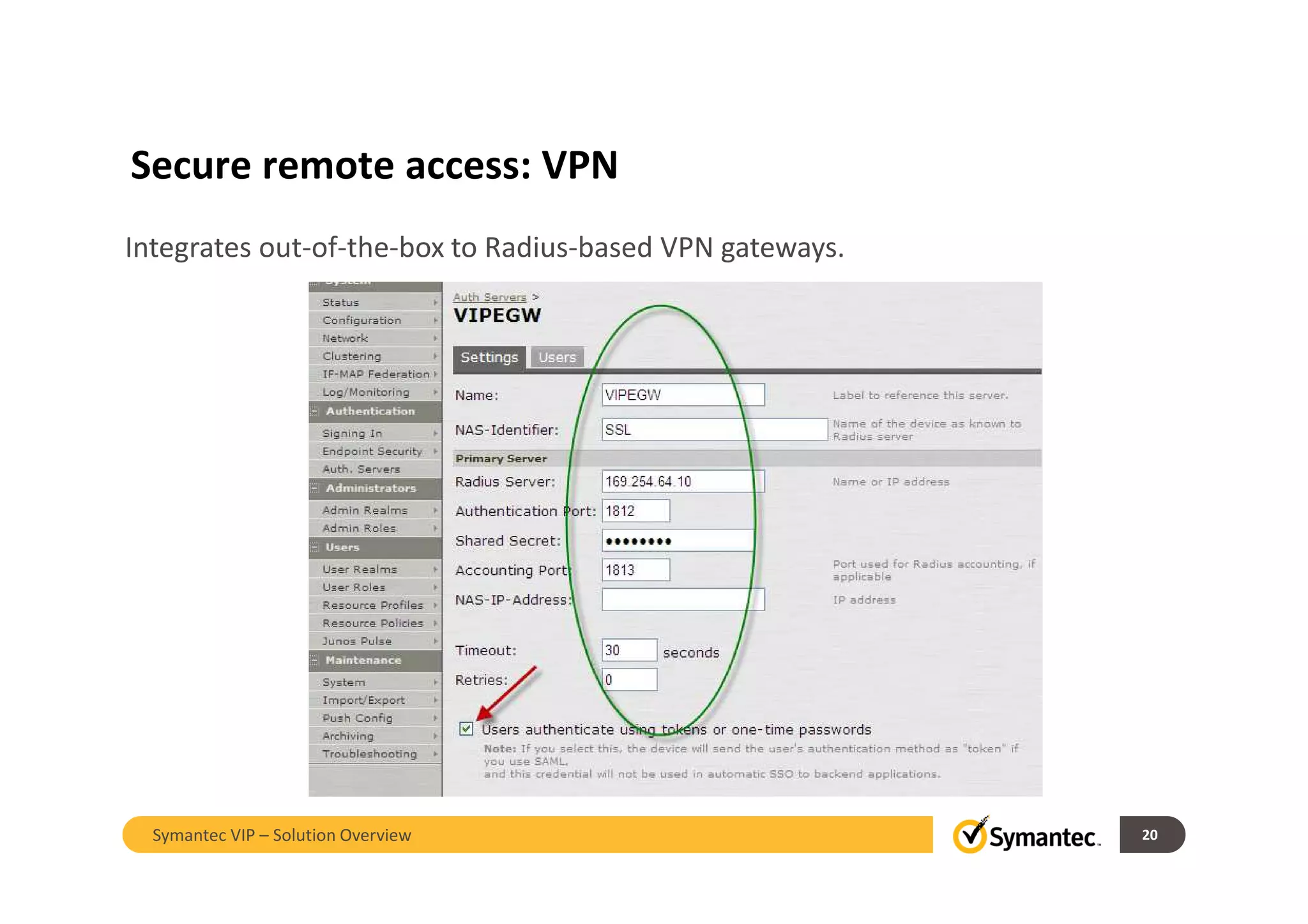
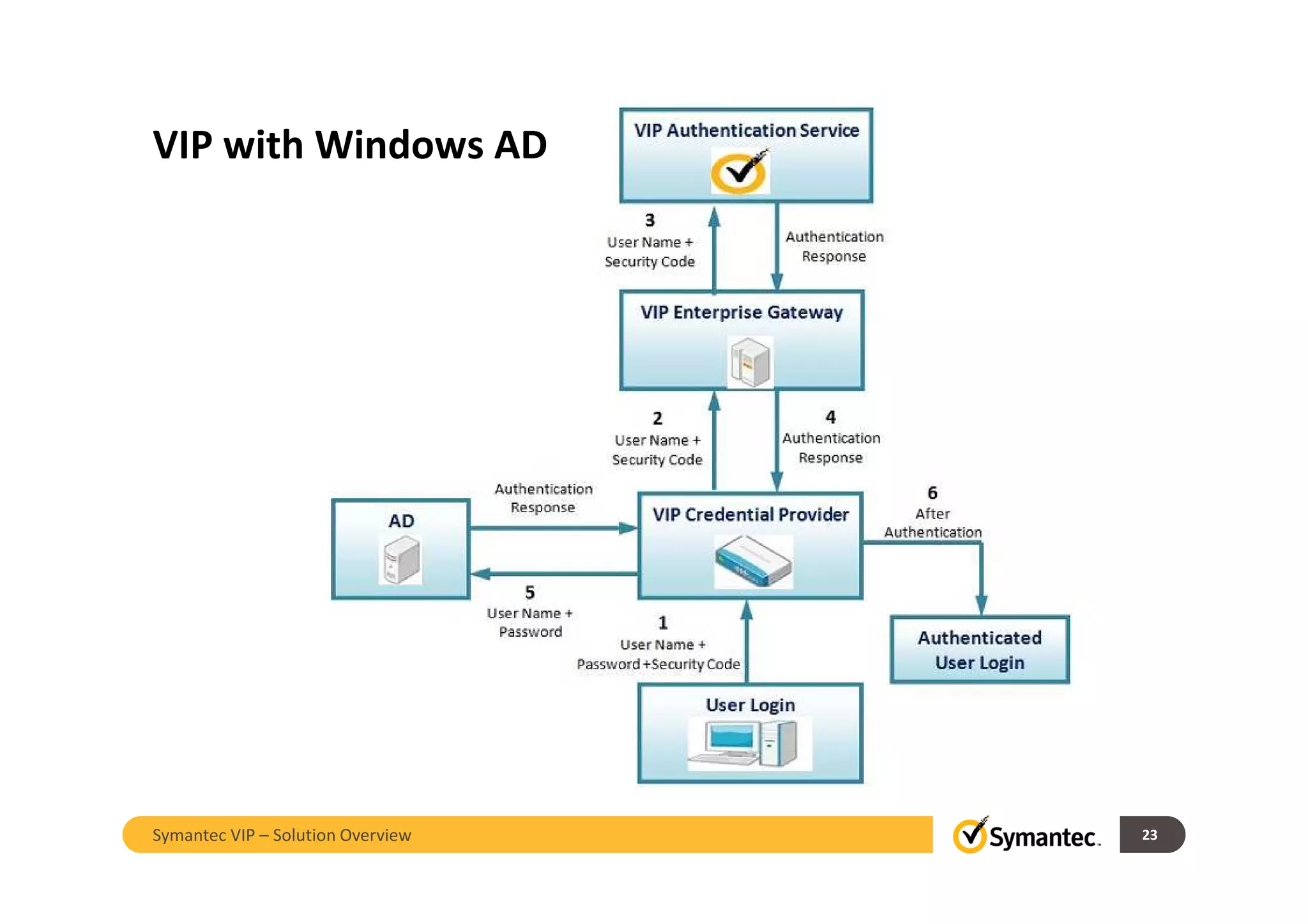
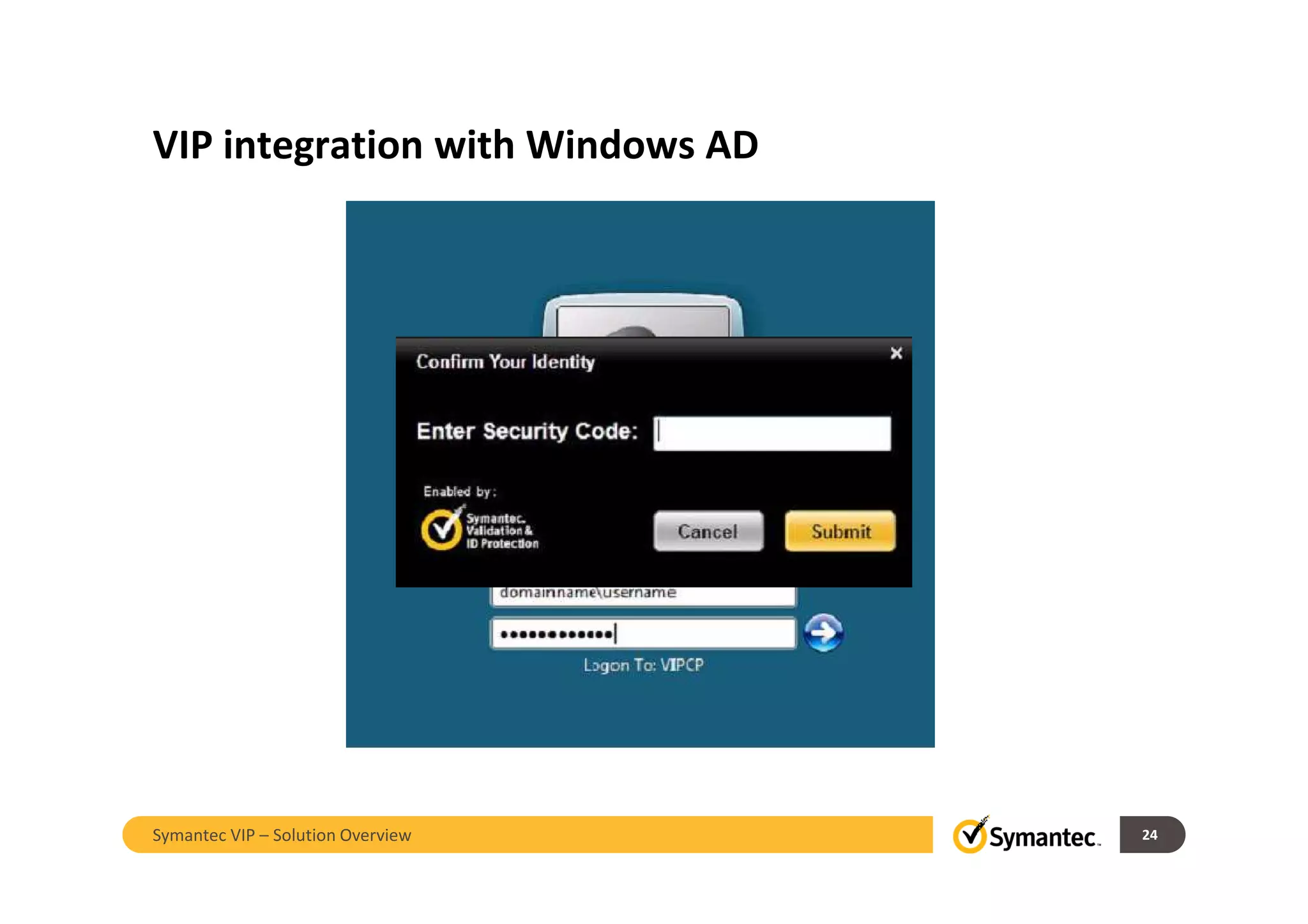
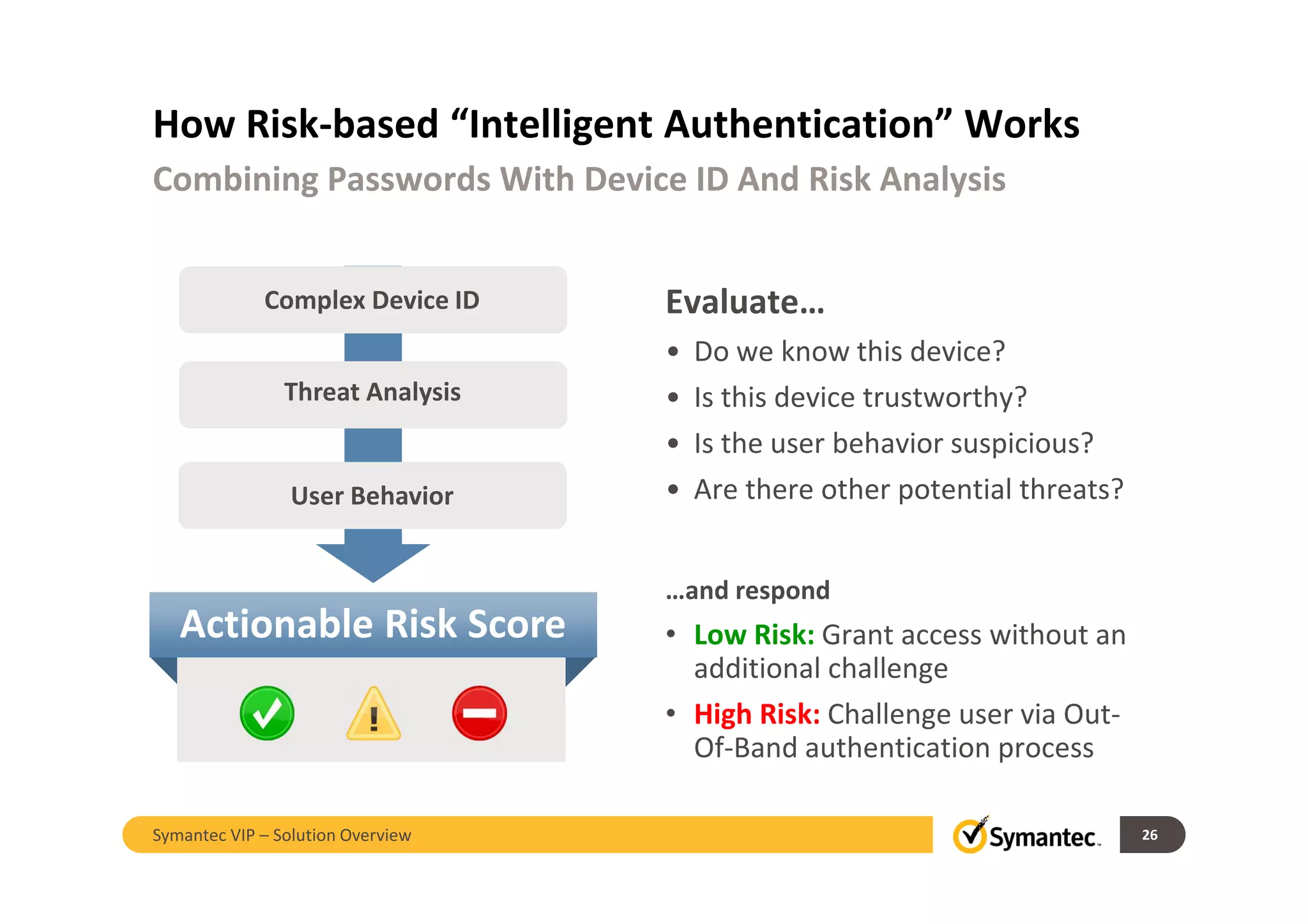
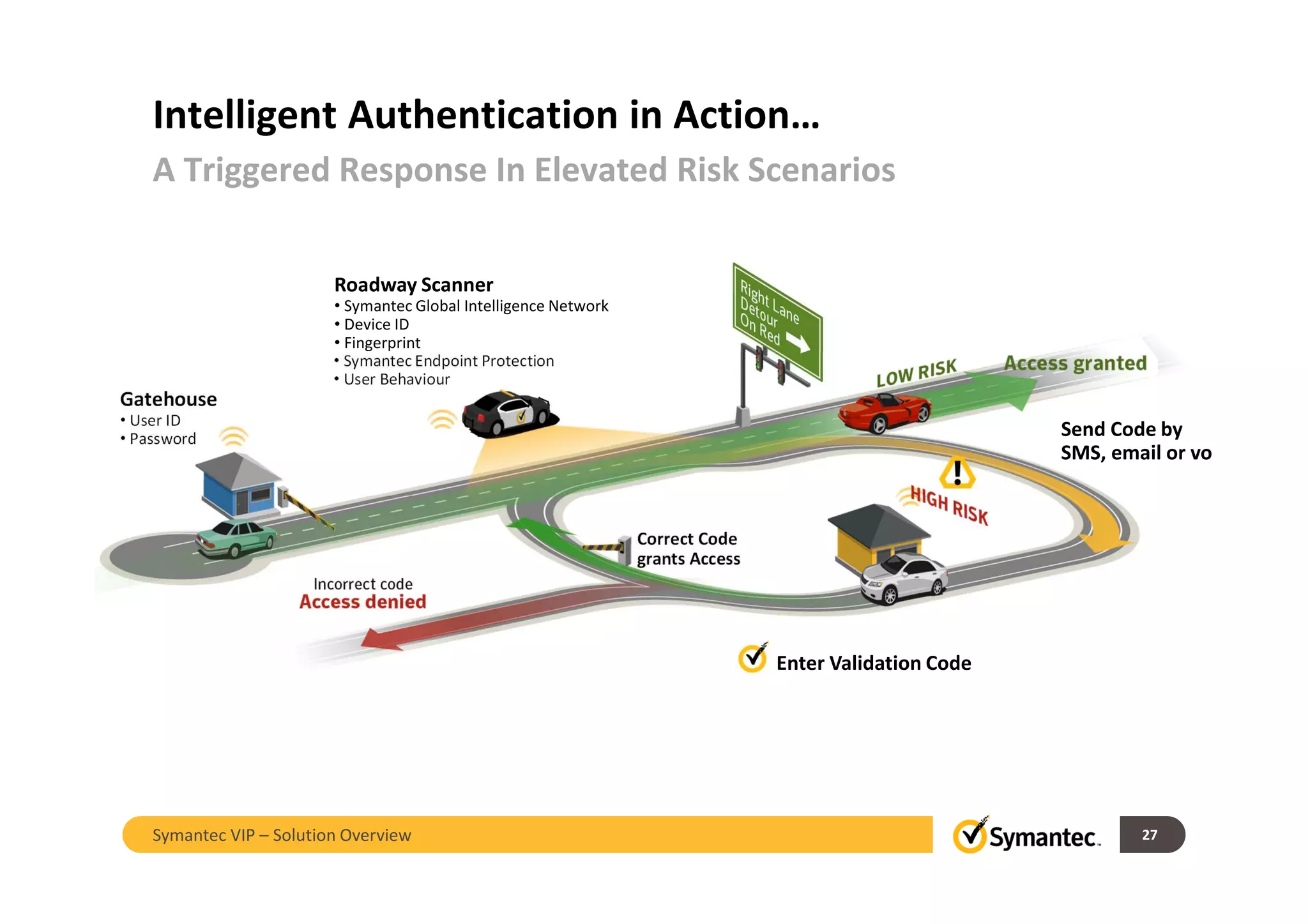
The document discusses Symantec VIP, a cloud-based strong authentication solution. It provides an overview of Symantec VIP's validation and identity protection services, use cases including VPN access and Active Directory integration, and risk-based authentication. Symantec VIP allows flexible deployment of one-time passwords on mobile devices, software tokens, and cards for secure access from any device.