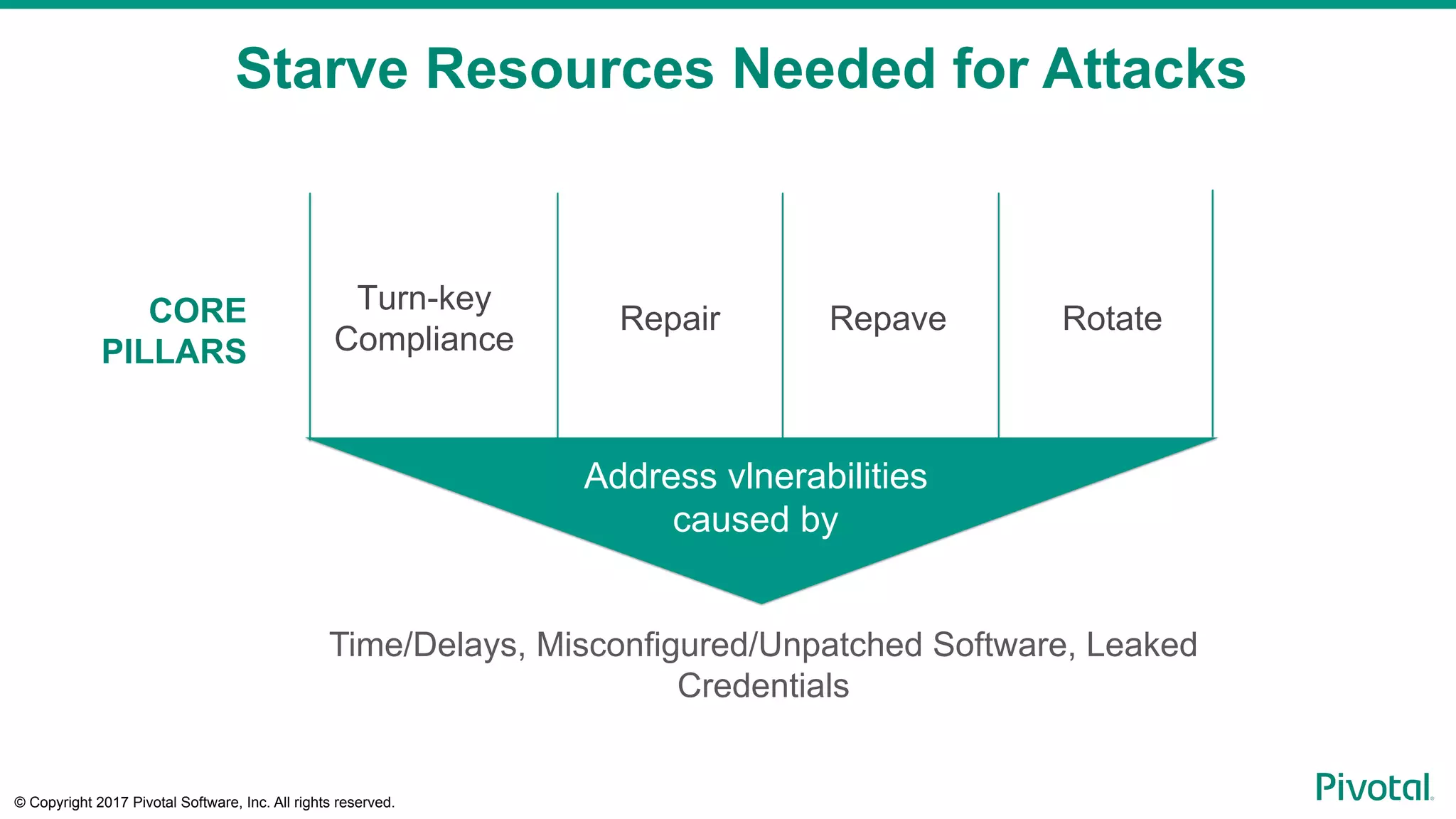
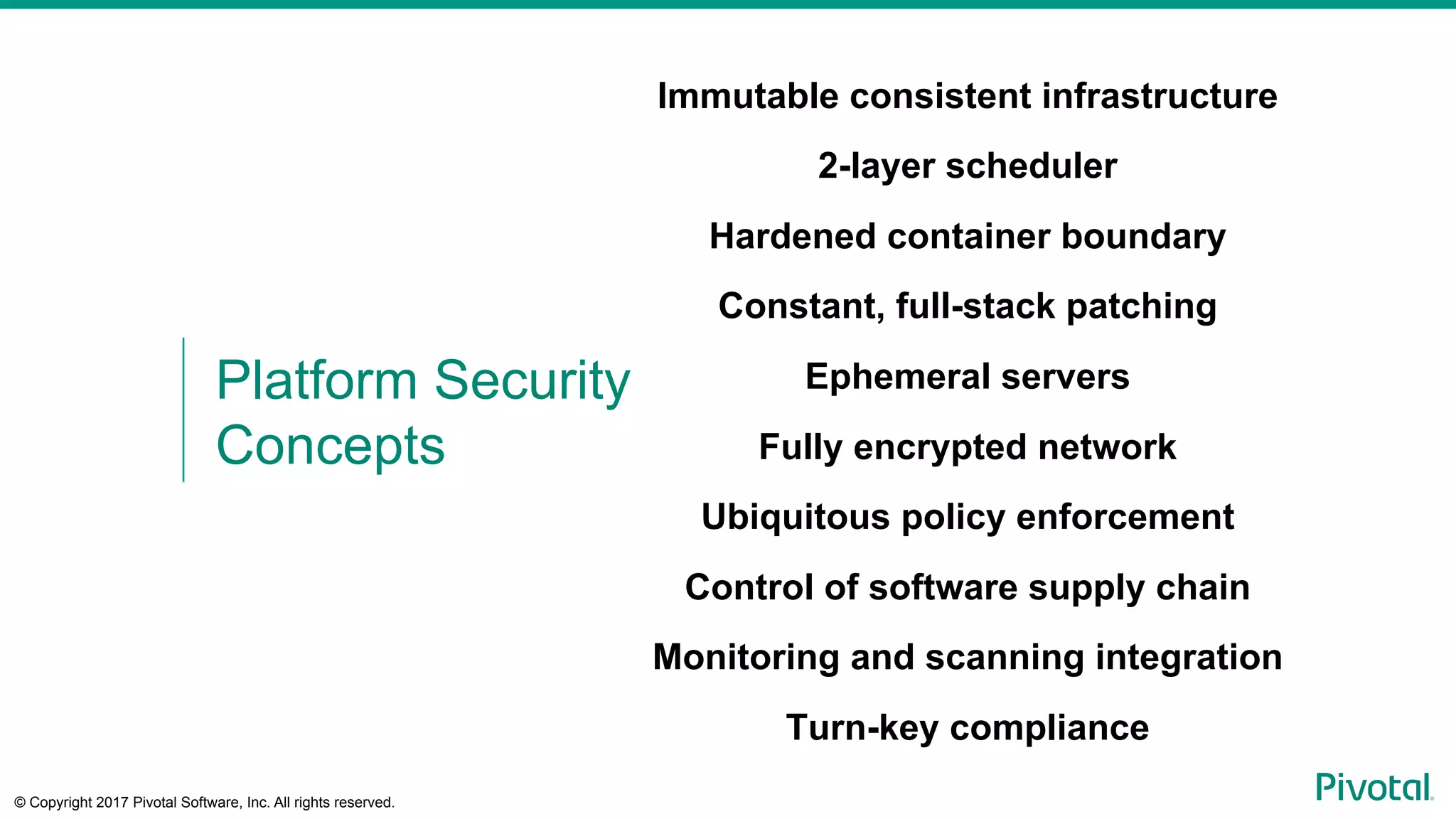
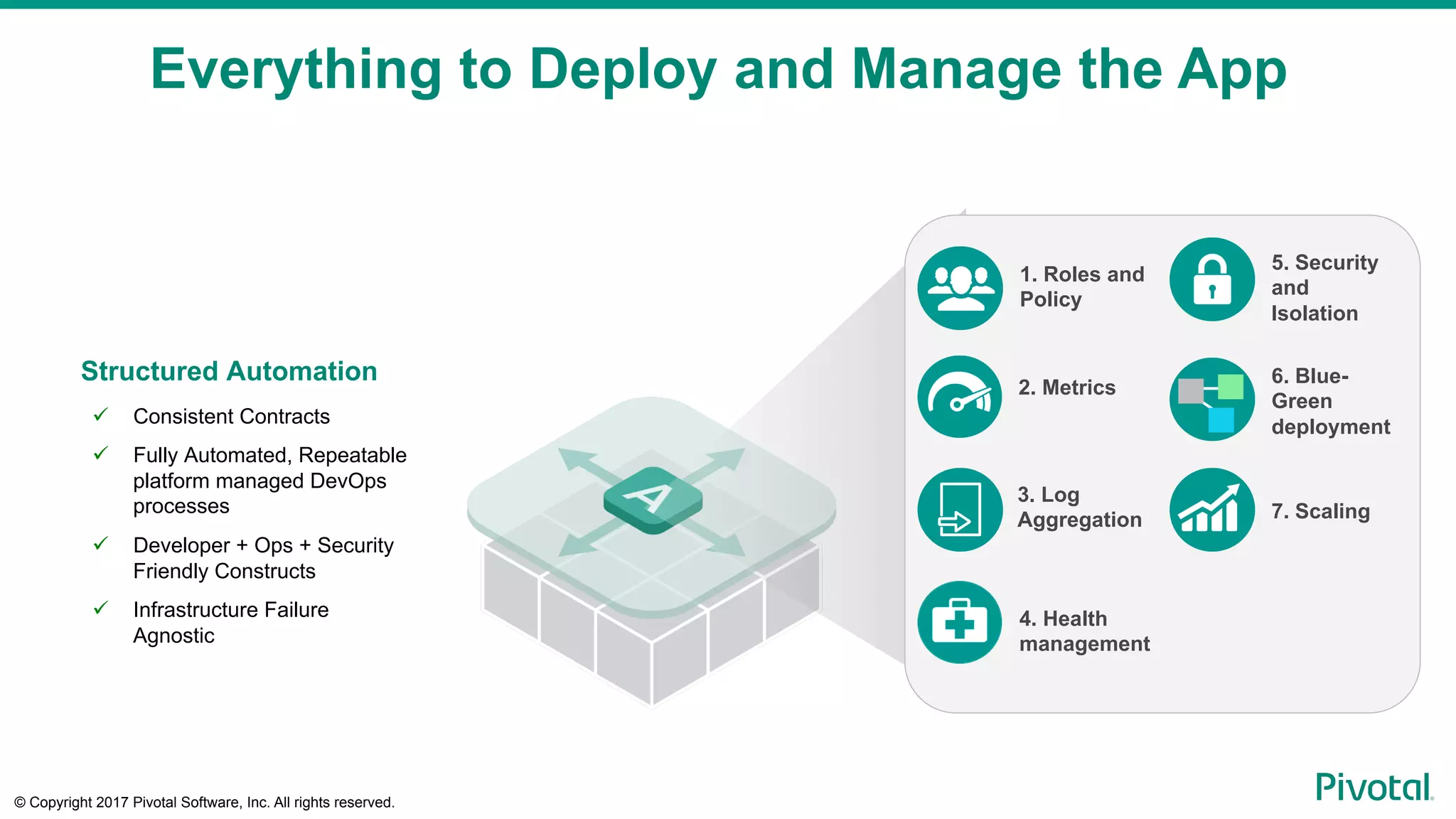
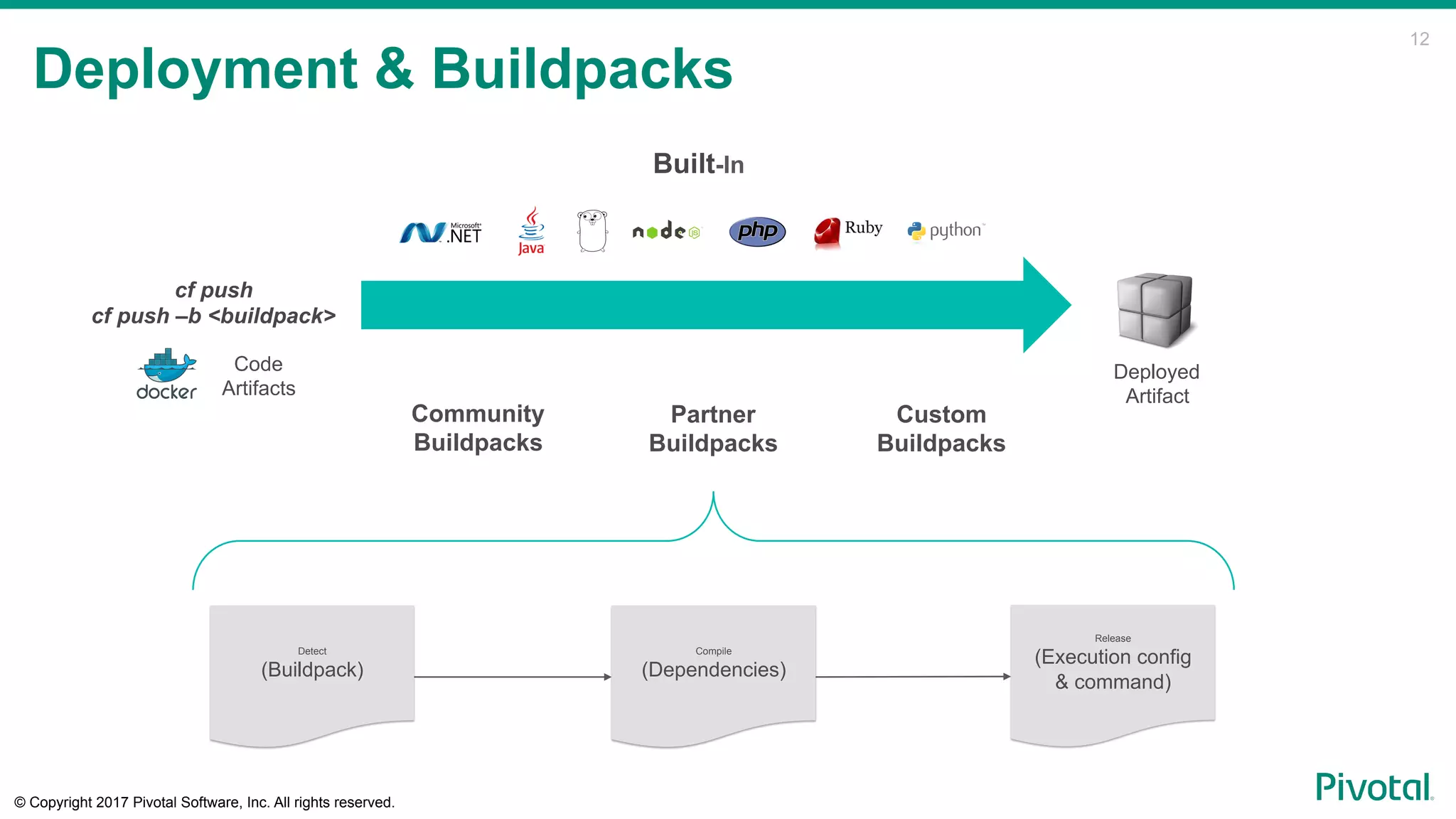
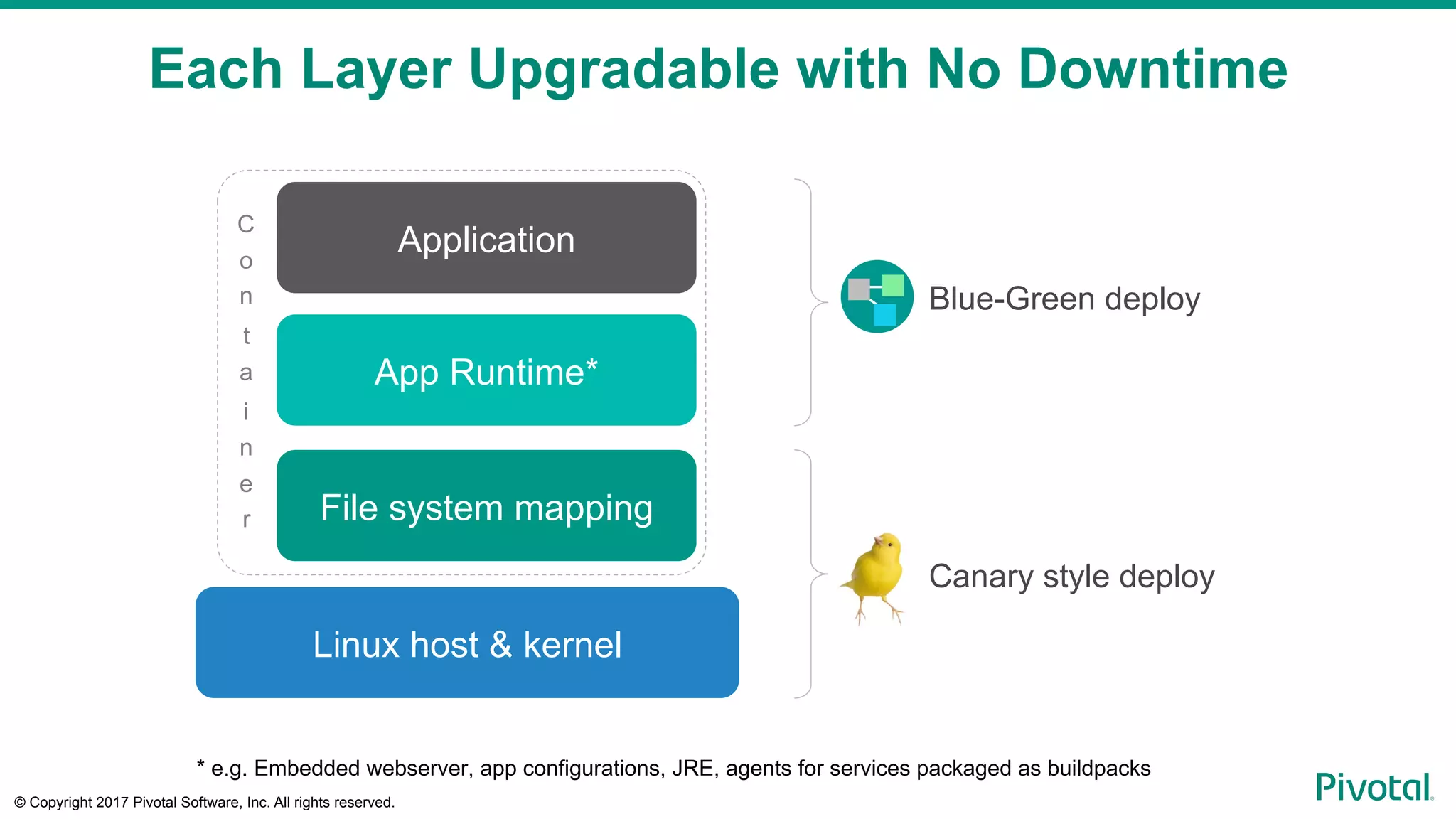
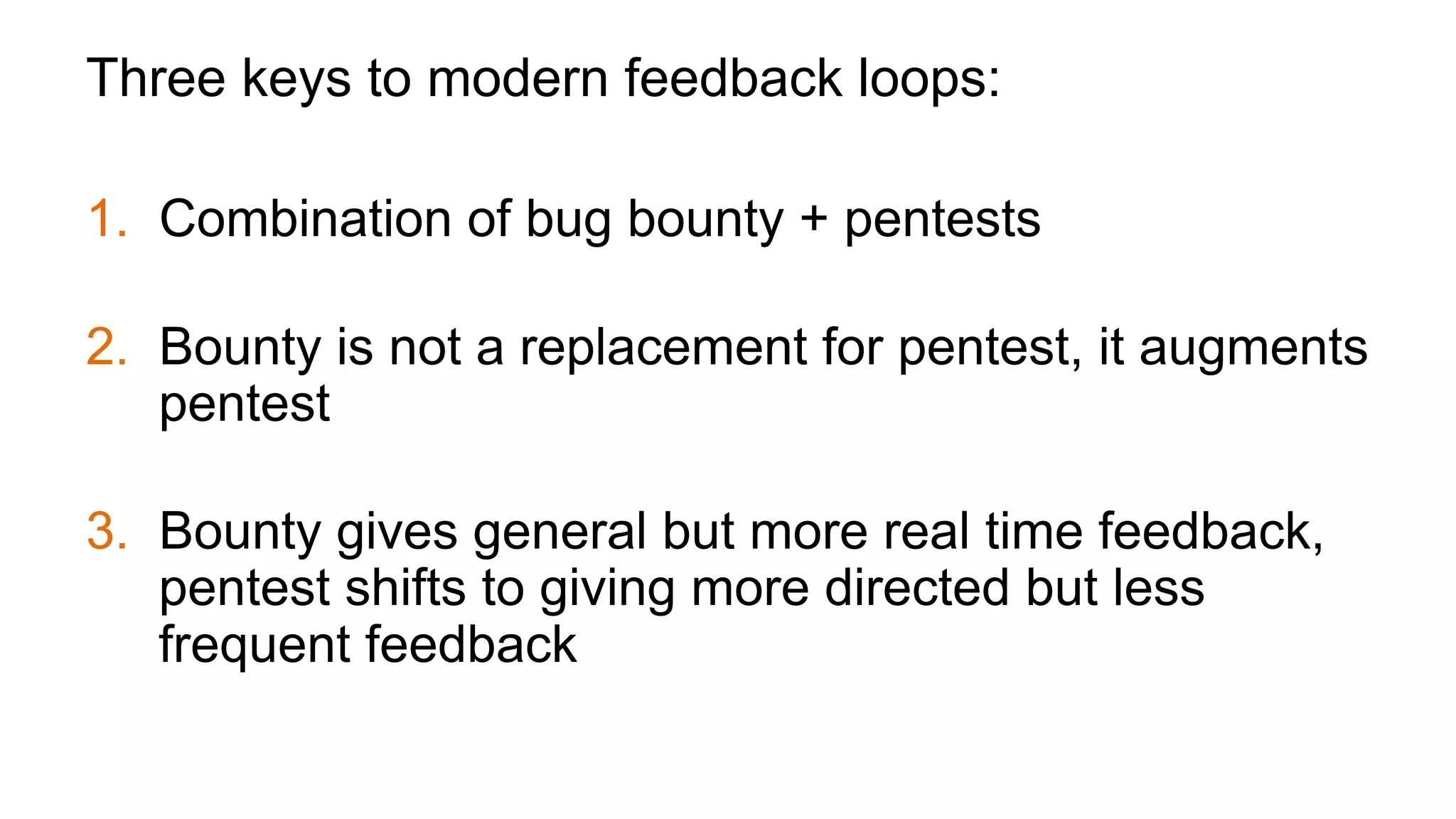
The document discusses strategies to tackle security challenges associated with cloud-native applications, emphasizing the need for faster, integrated security measures that coincide with development and deployment processes. It highlights the importance of visibility and feedback as key components in modern security practices, advocating for a blend of bug bounty programs and penetration tests to enhance vulnerability detection. Ultimately, the text reiterates that security must evolve to keep pace with rapid software development while ensuring robust protection against potential attacks.





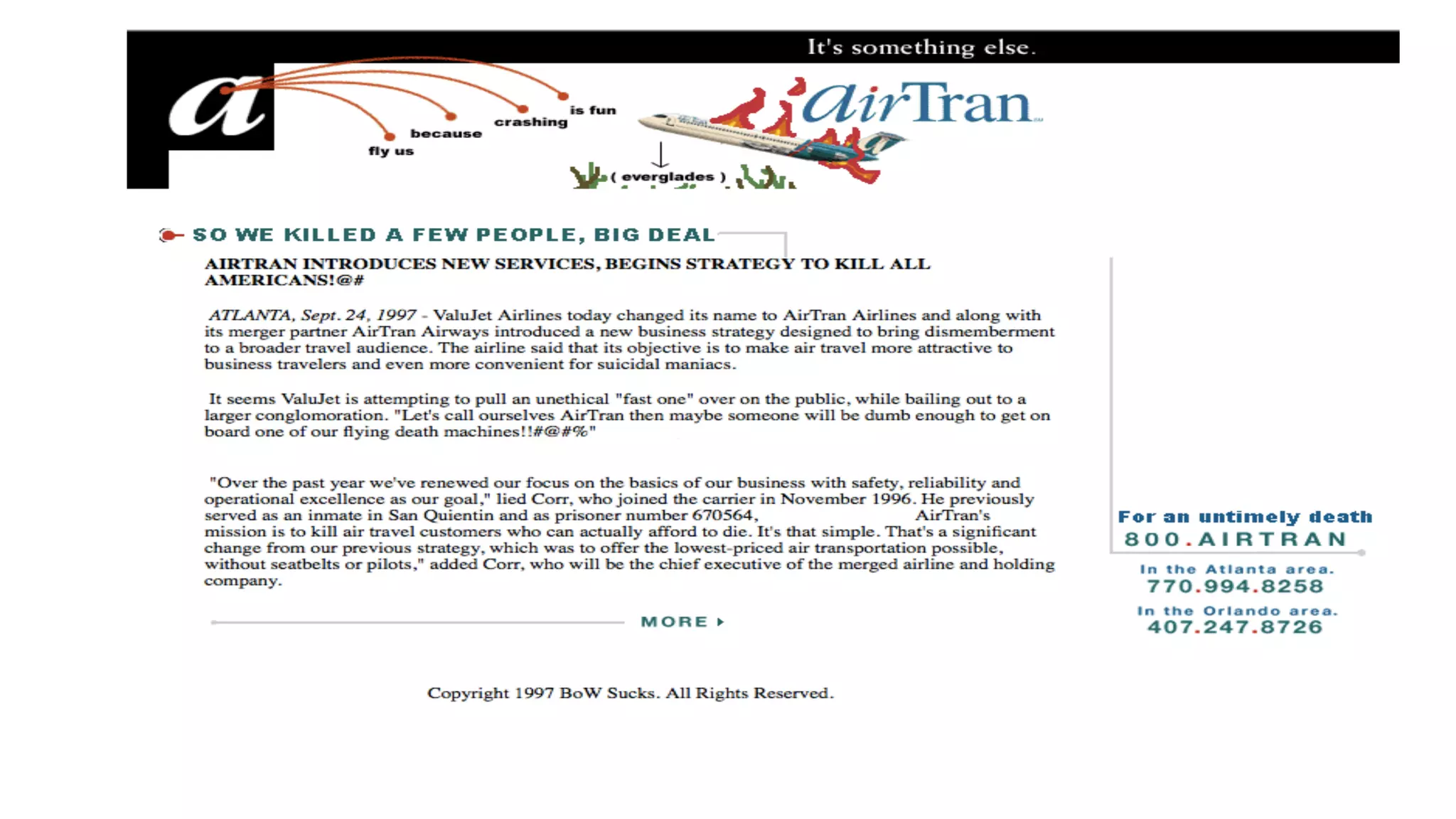
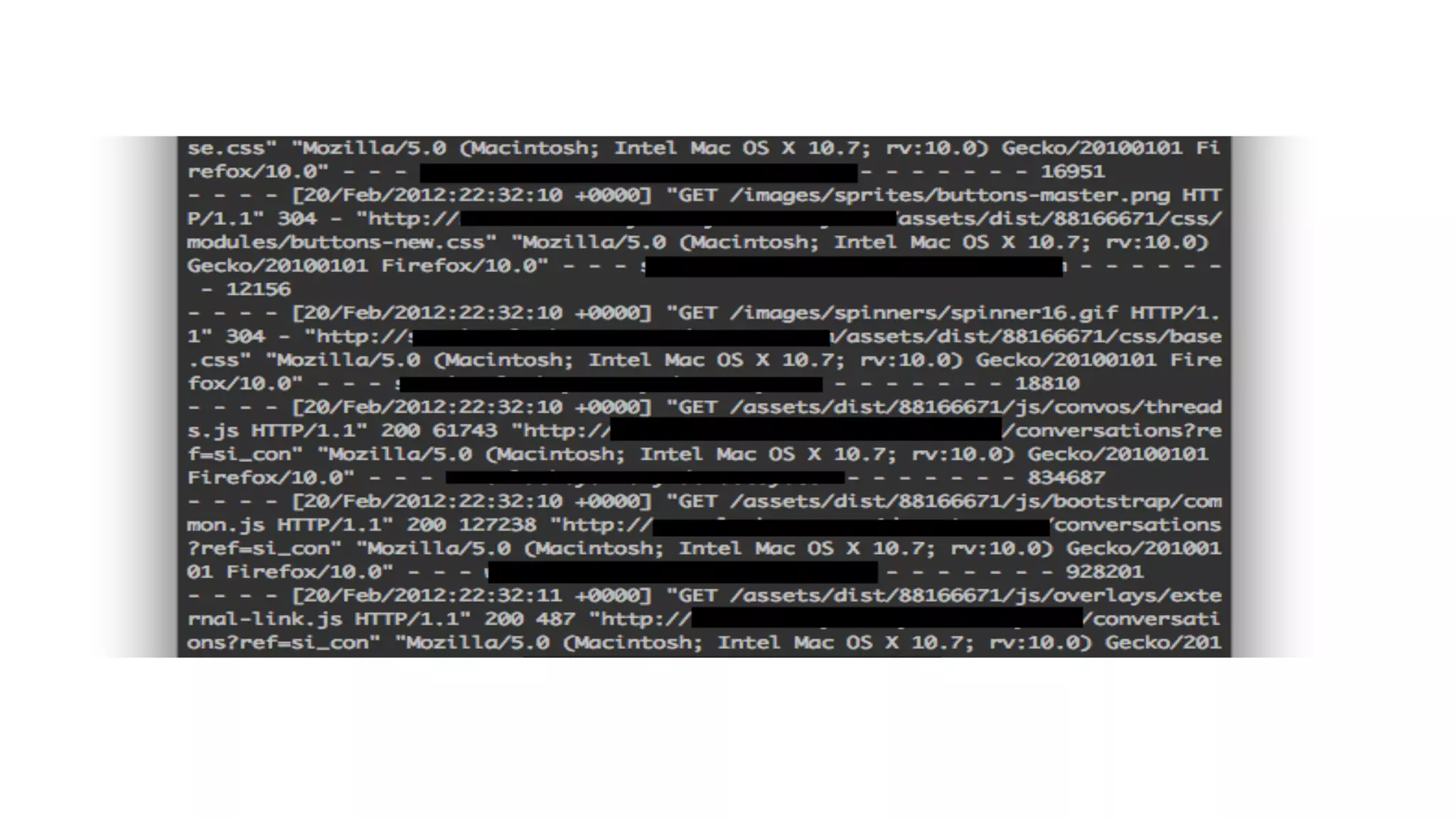
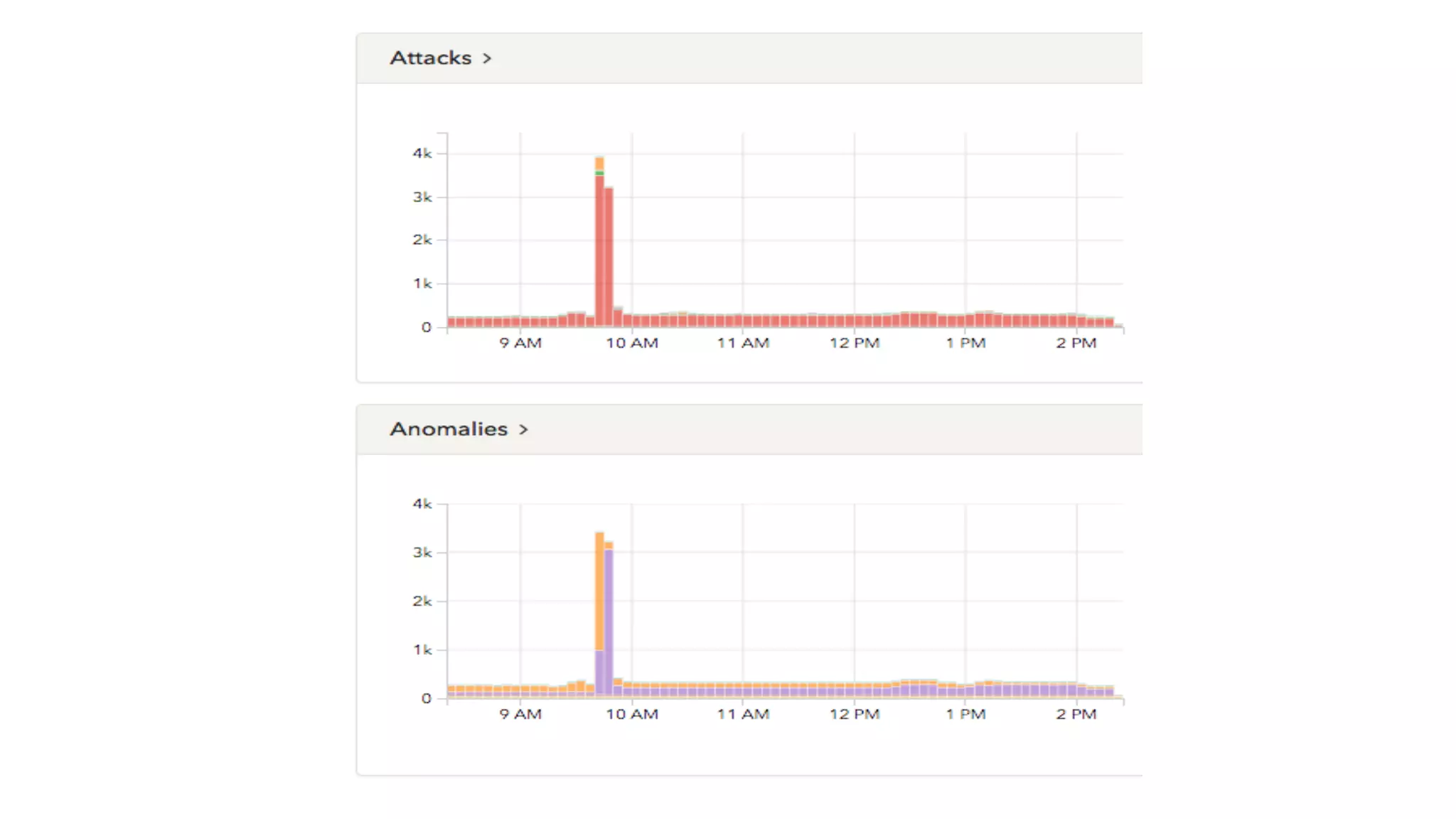


![Visibility + Feedback success story:
“I discovered the vulnerability late Friday afternoon and
wasn't quite ready to email it to them … [Etsy] had
detected my requests and pushed a patch Saturday
morning before I could email them. This was by far the
fastest response time by any company I've reported to.”
- Source: https://www.reddit.com/r/netsec/comments/vbrzg/
etsy_has_been_one_of_the_best_companies_ive](https://image.slidesharecdn.com/strategiesonhowtoovercomesecuritychallengesuniquetocloud-nativeapps-170518014129/75/Strategies-on-How-to-Overcome-Security-Challenges-Unique-to-Cloud-Native-Apps-46-2048.jpg)