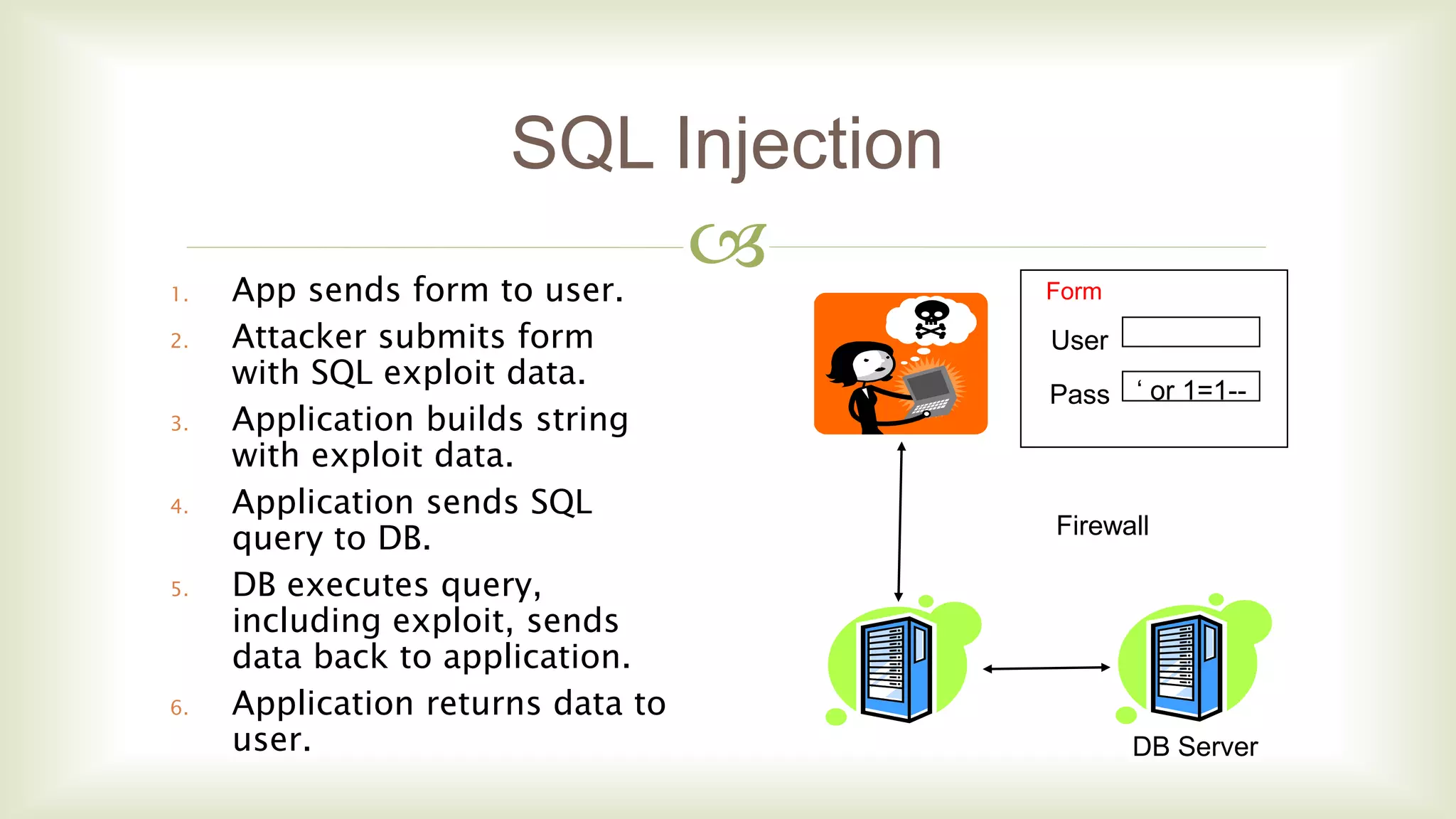
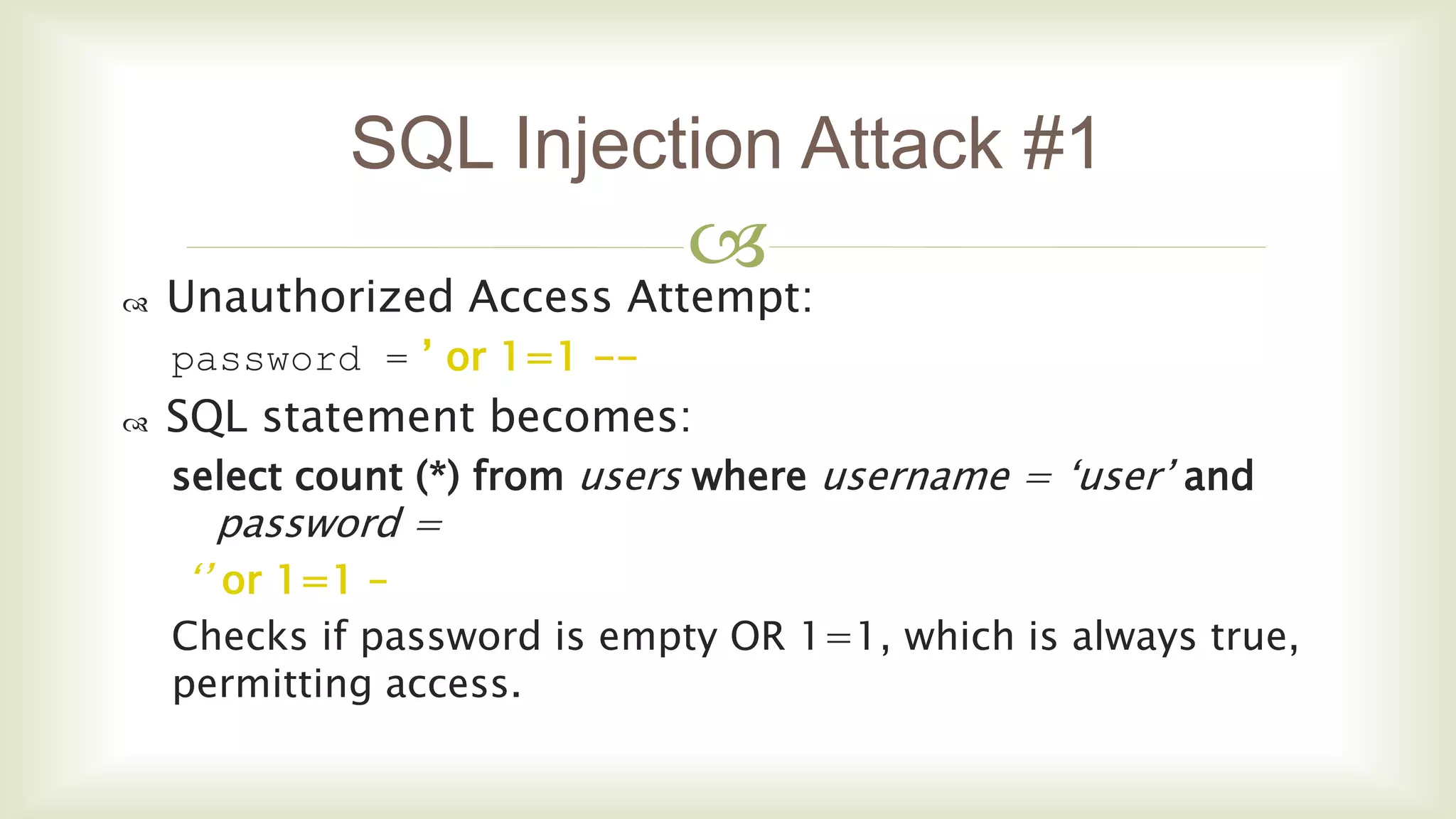
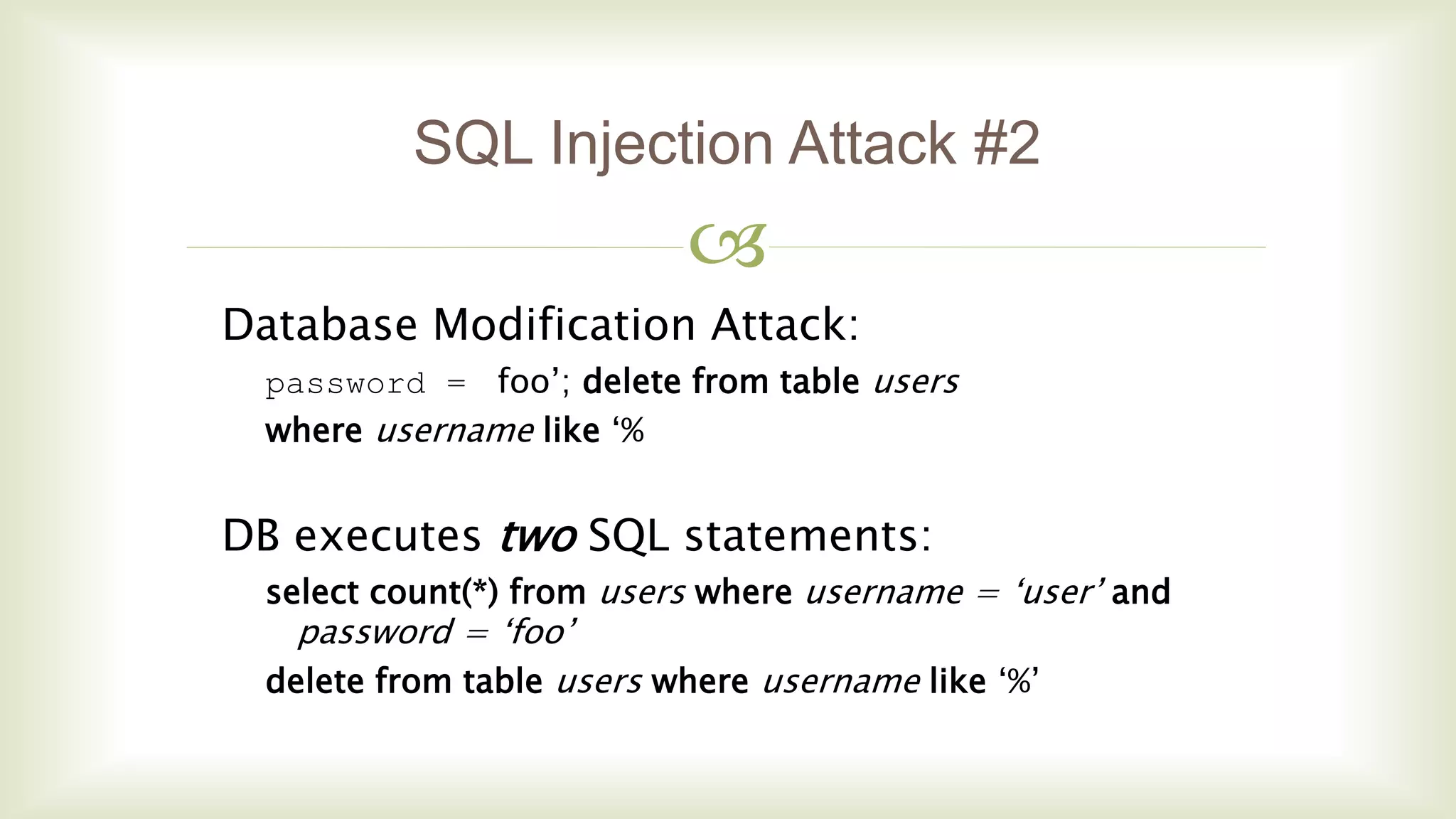
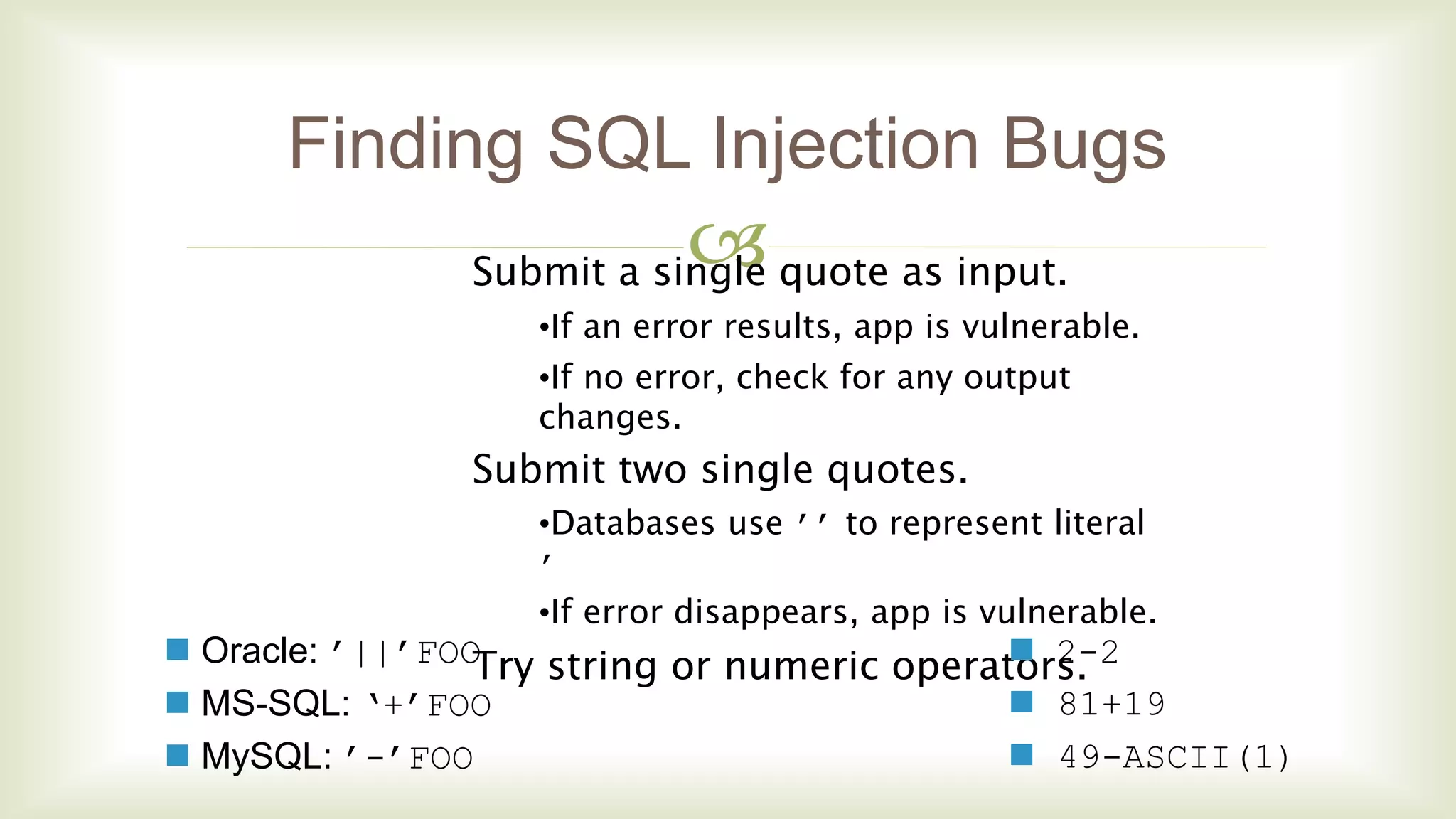
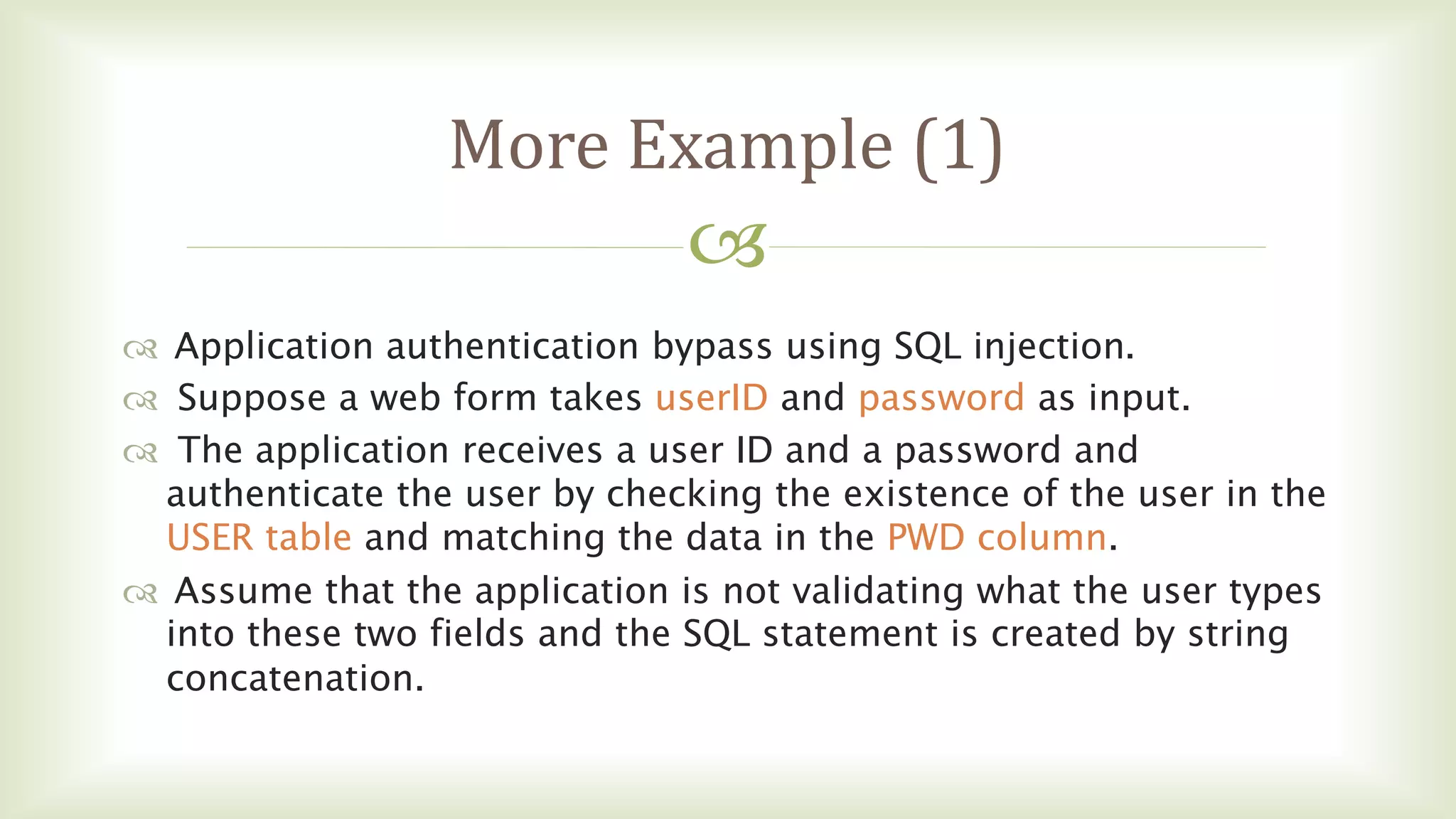
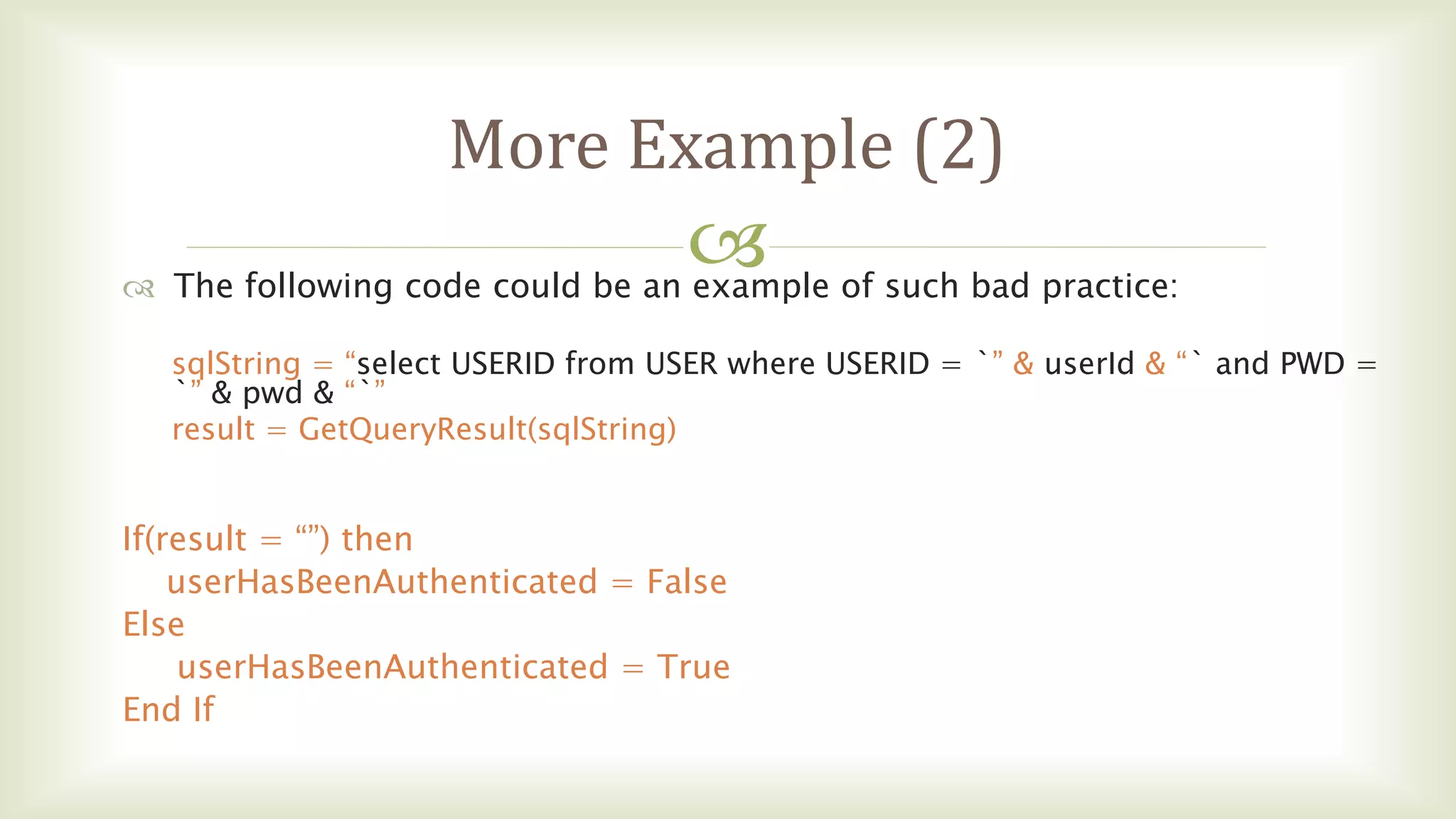
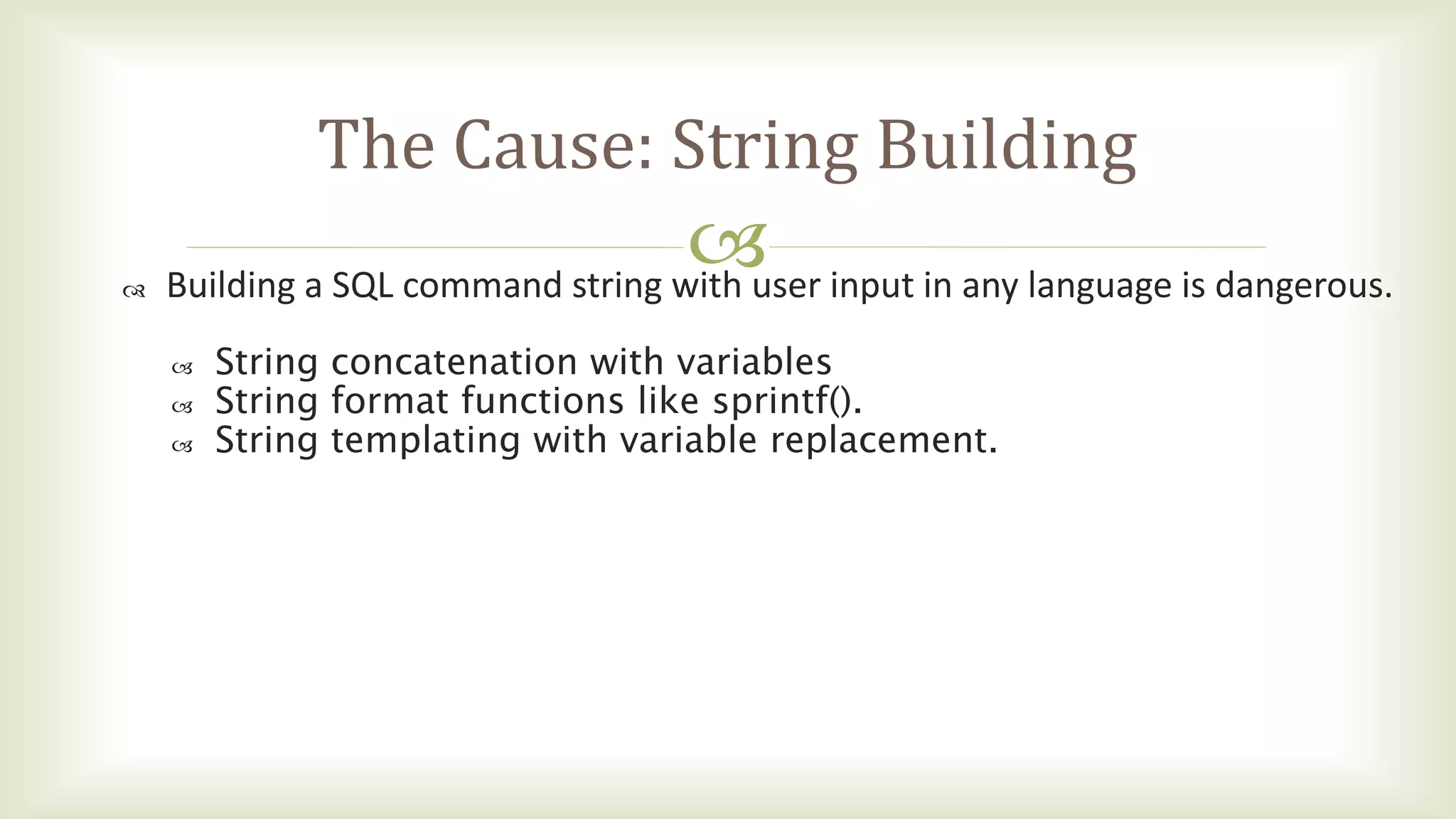
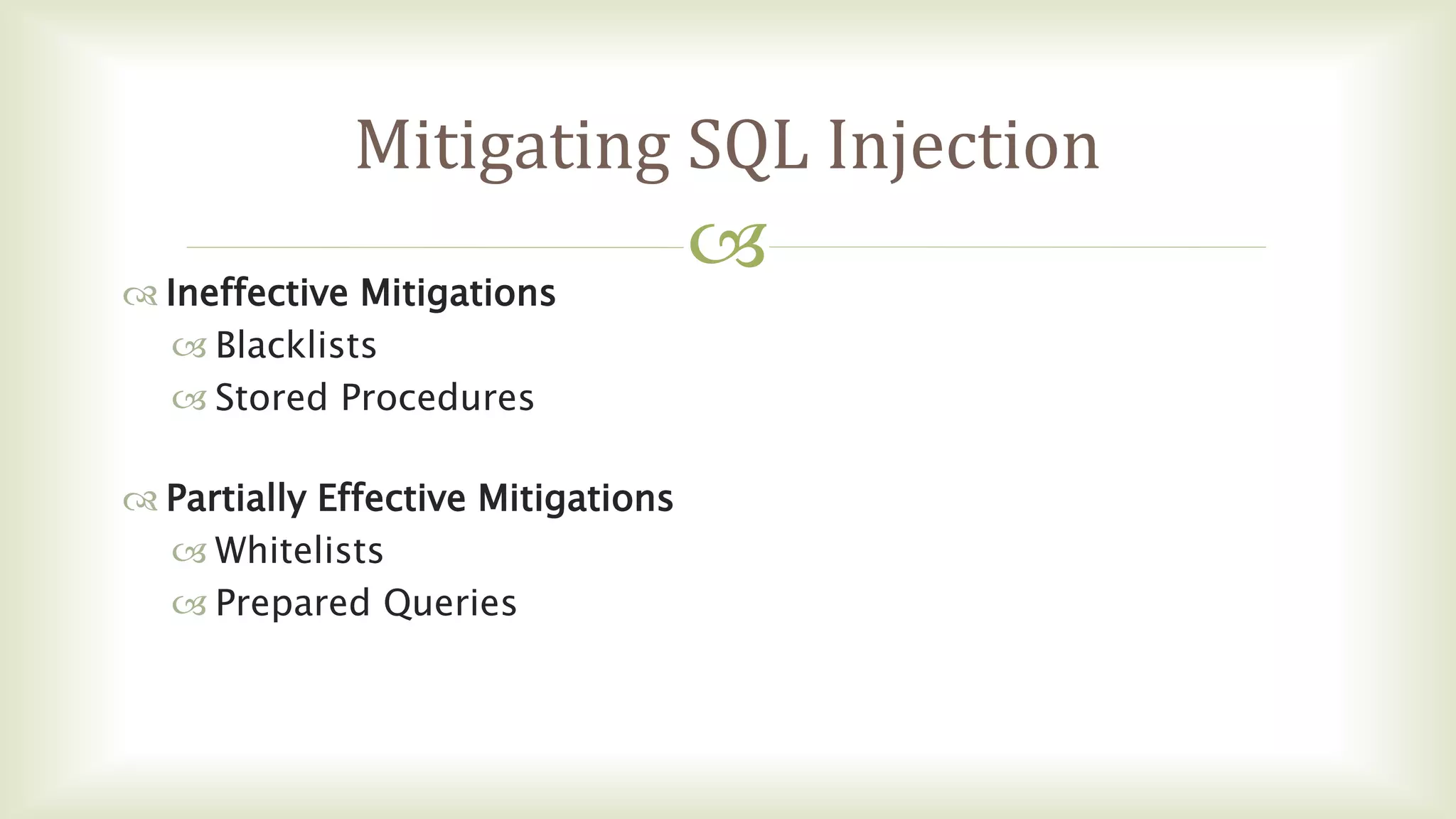
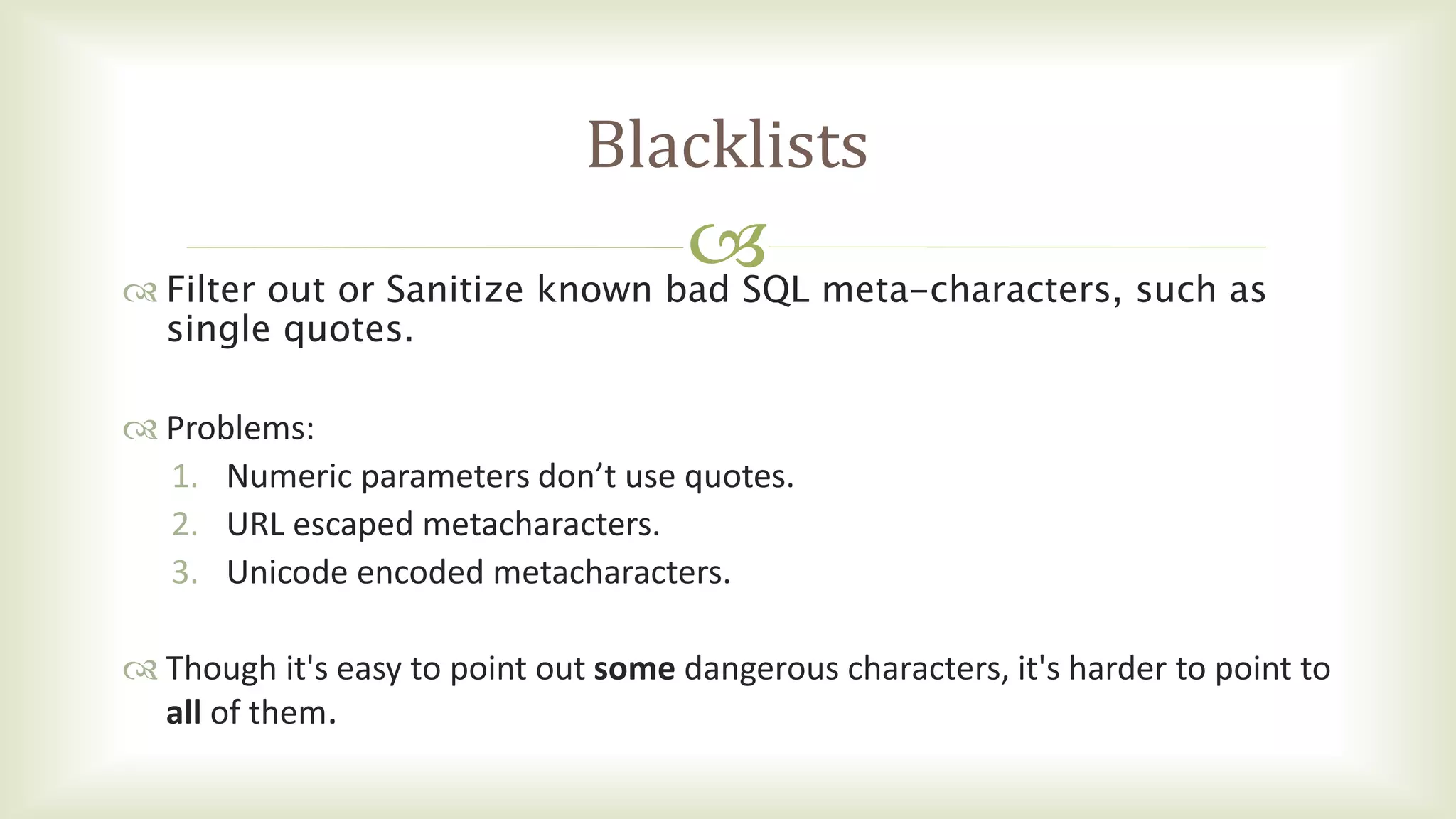
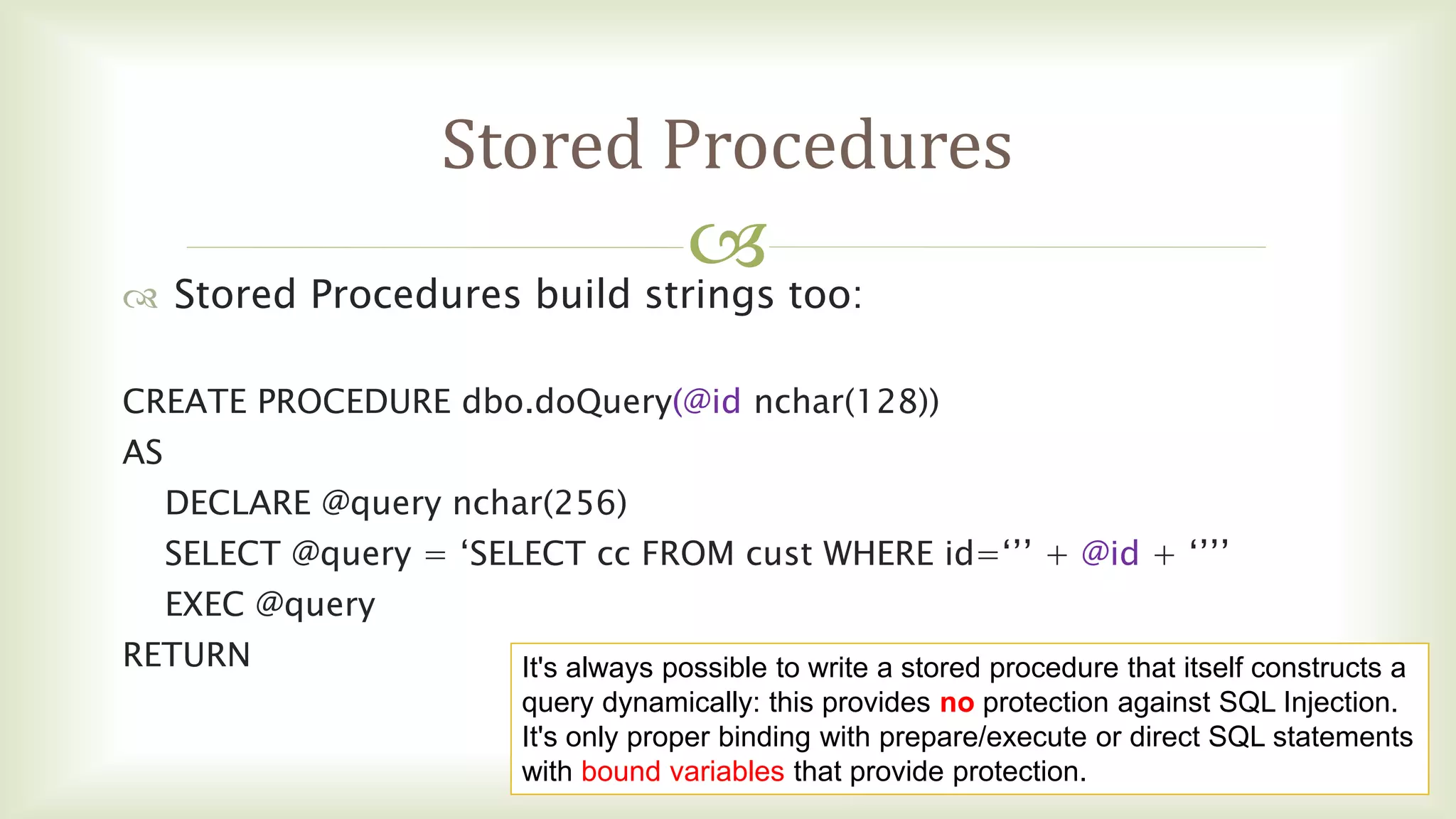
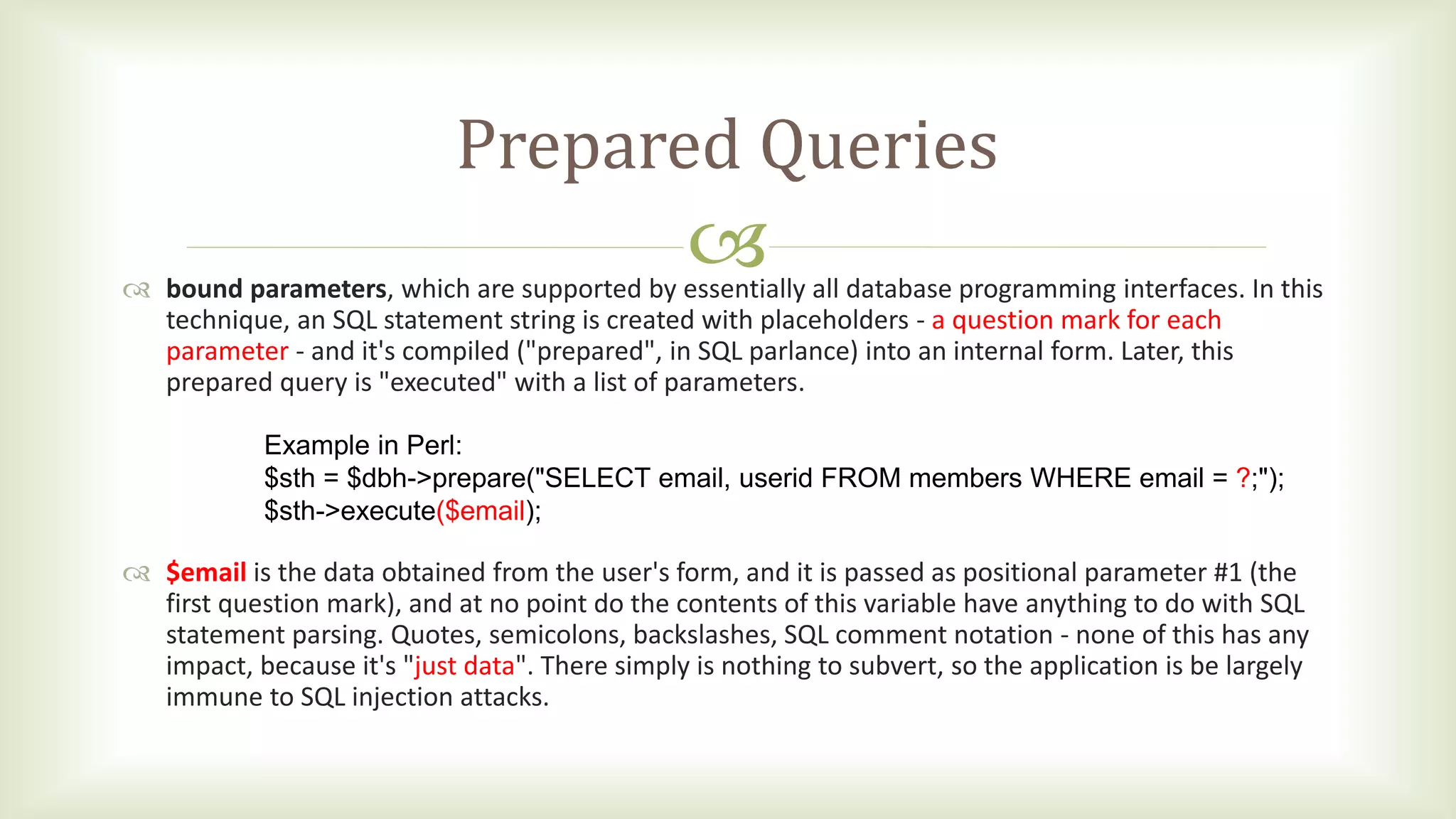
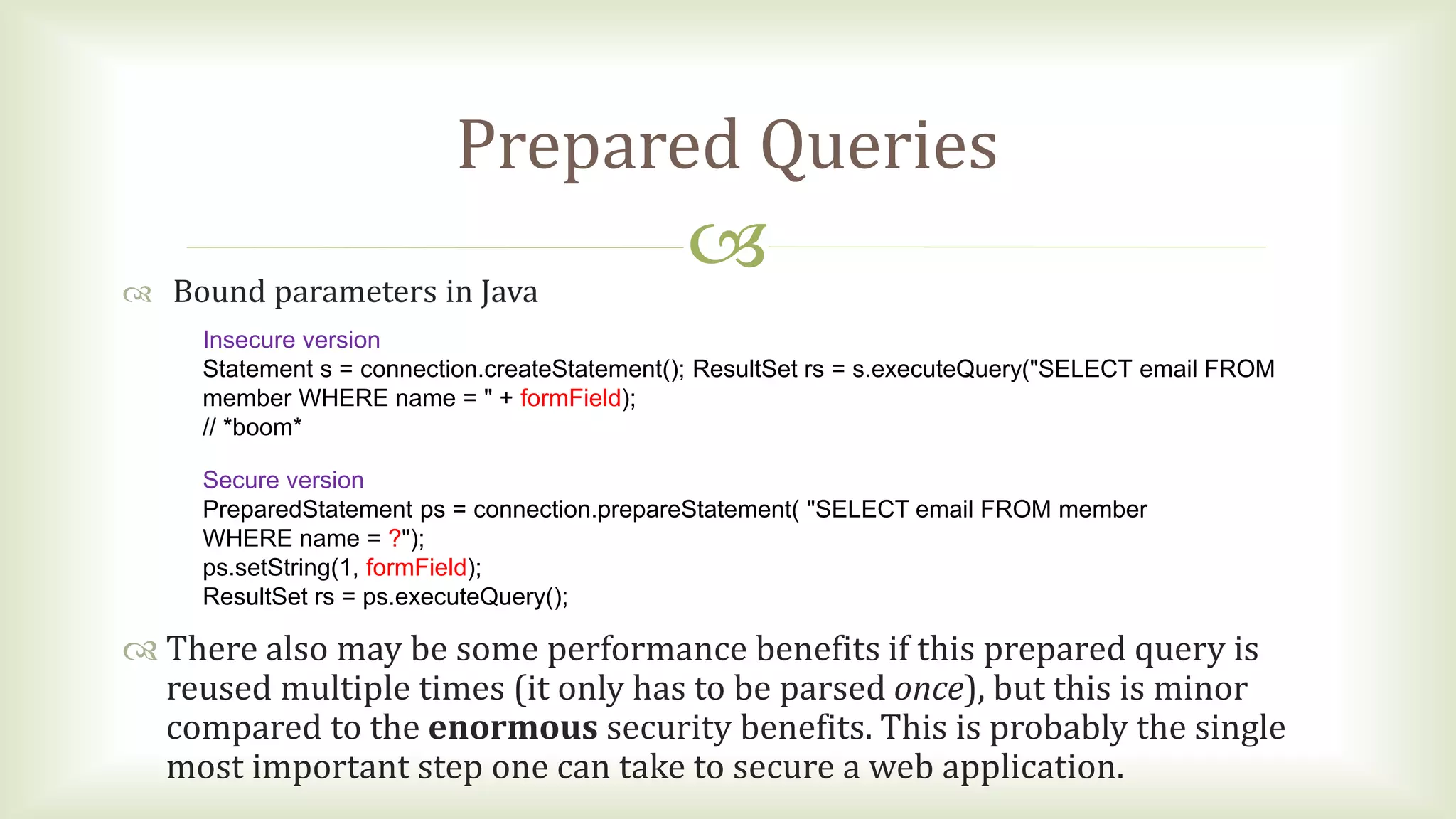
SQL injection is a common web application security vulnerability that allows attackers to control an application's database by tricking the application into sending unexpected SQL commands to the database. It works by submitting malicious SQL code as input, which gets executed by the database since the application concatenates user input directly into SQL queries. The key to preventing SQL injection is using prepared statements with bound parameters instead of building SQL queries through string concatenation. This separates the SQL statement from any user-supplied input that could contain malicious code.