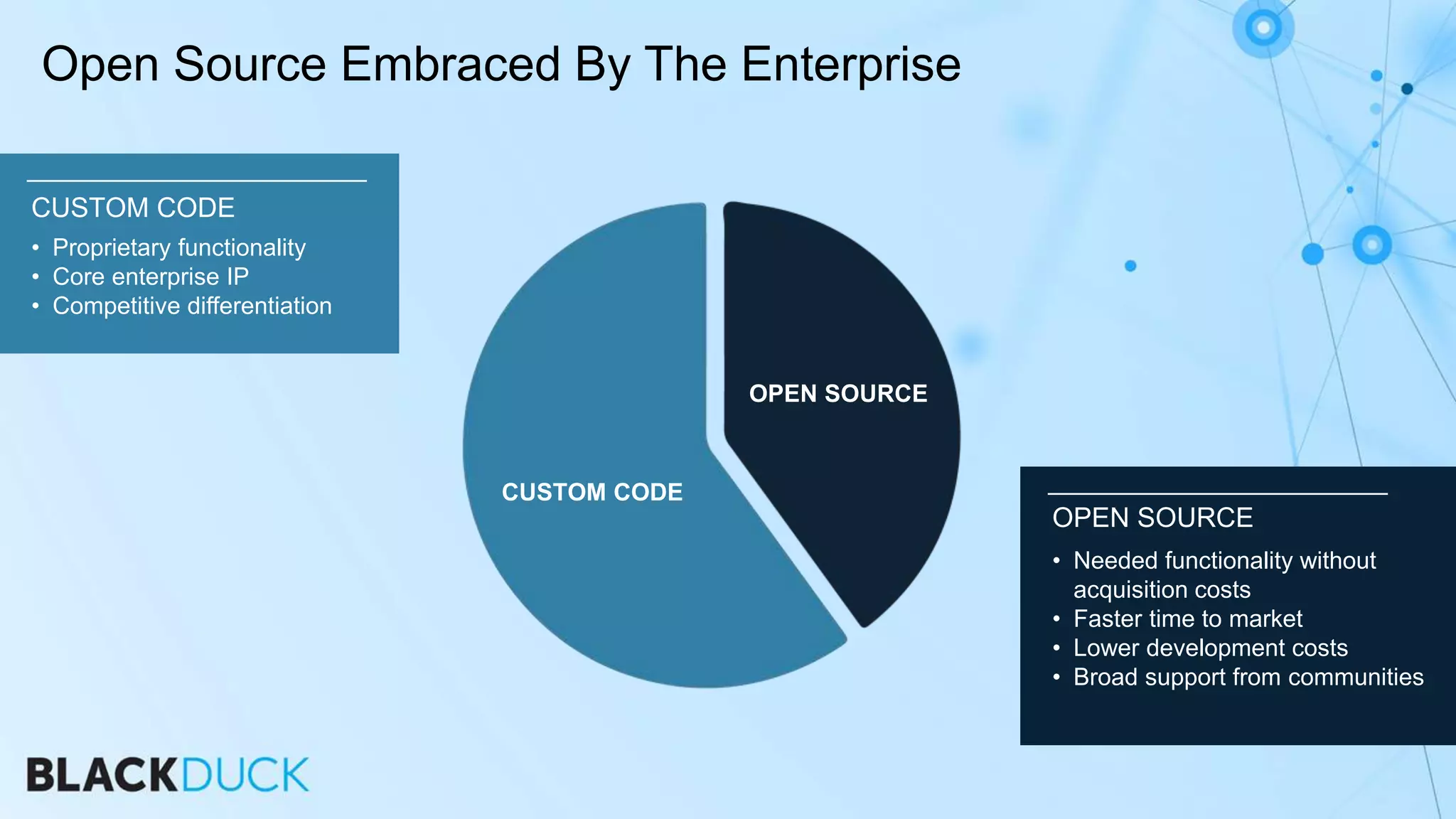
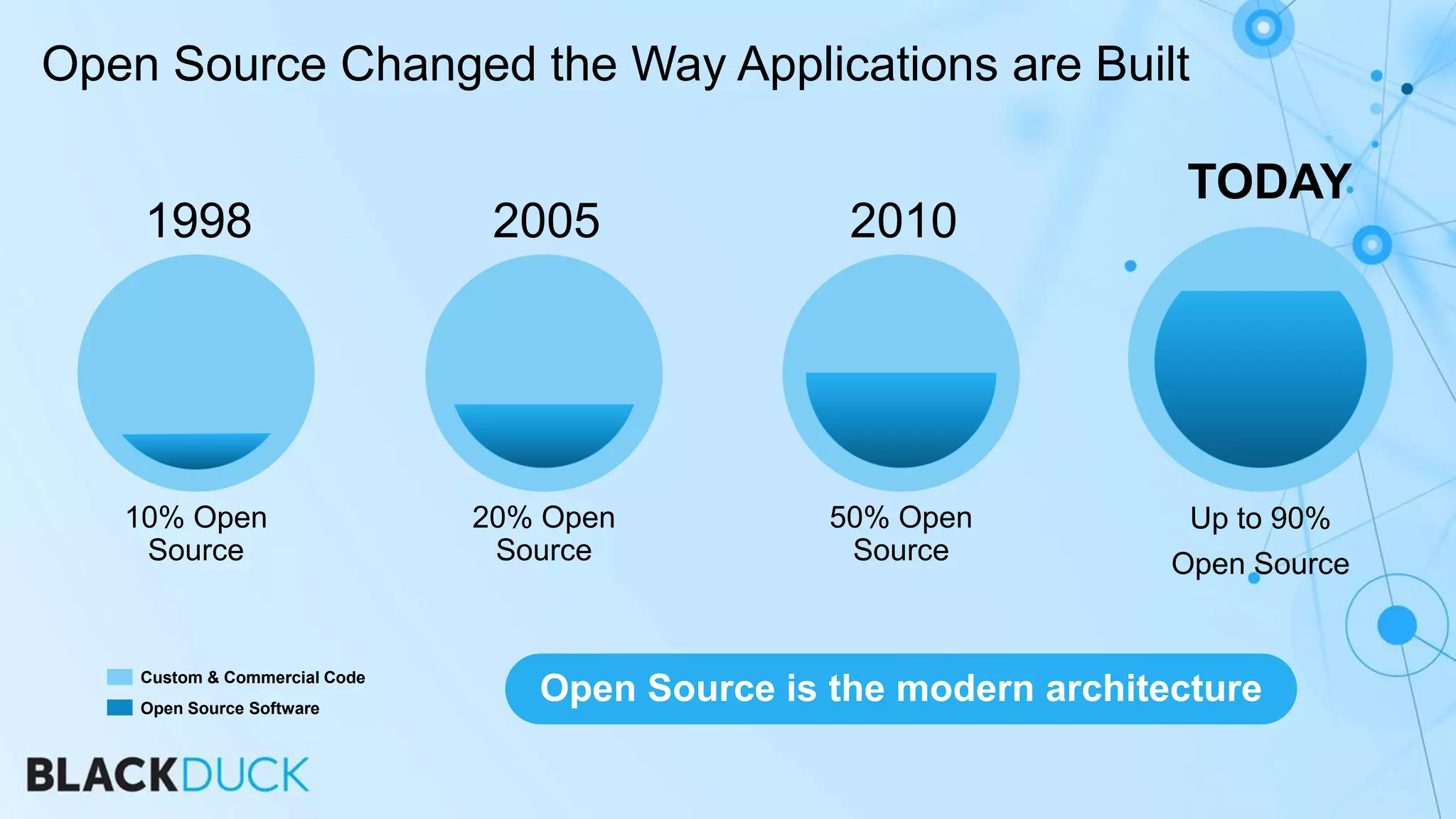
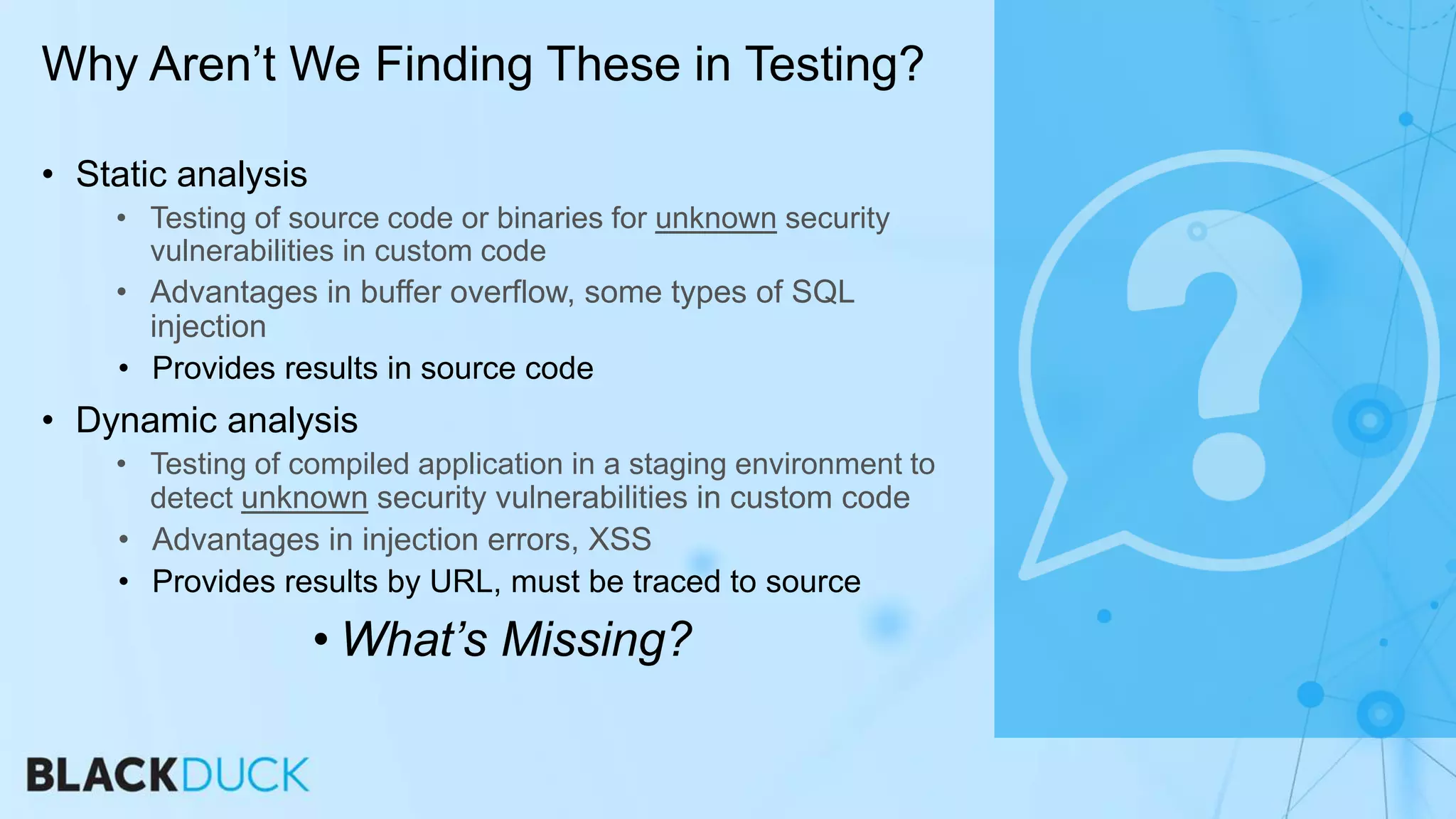
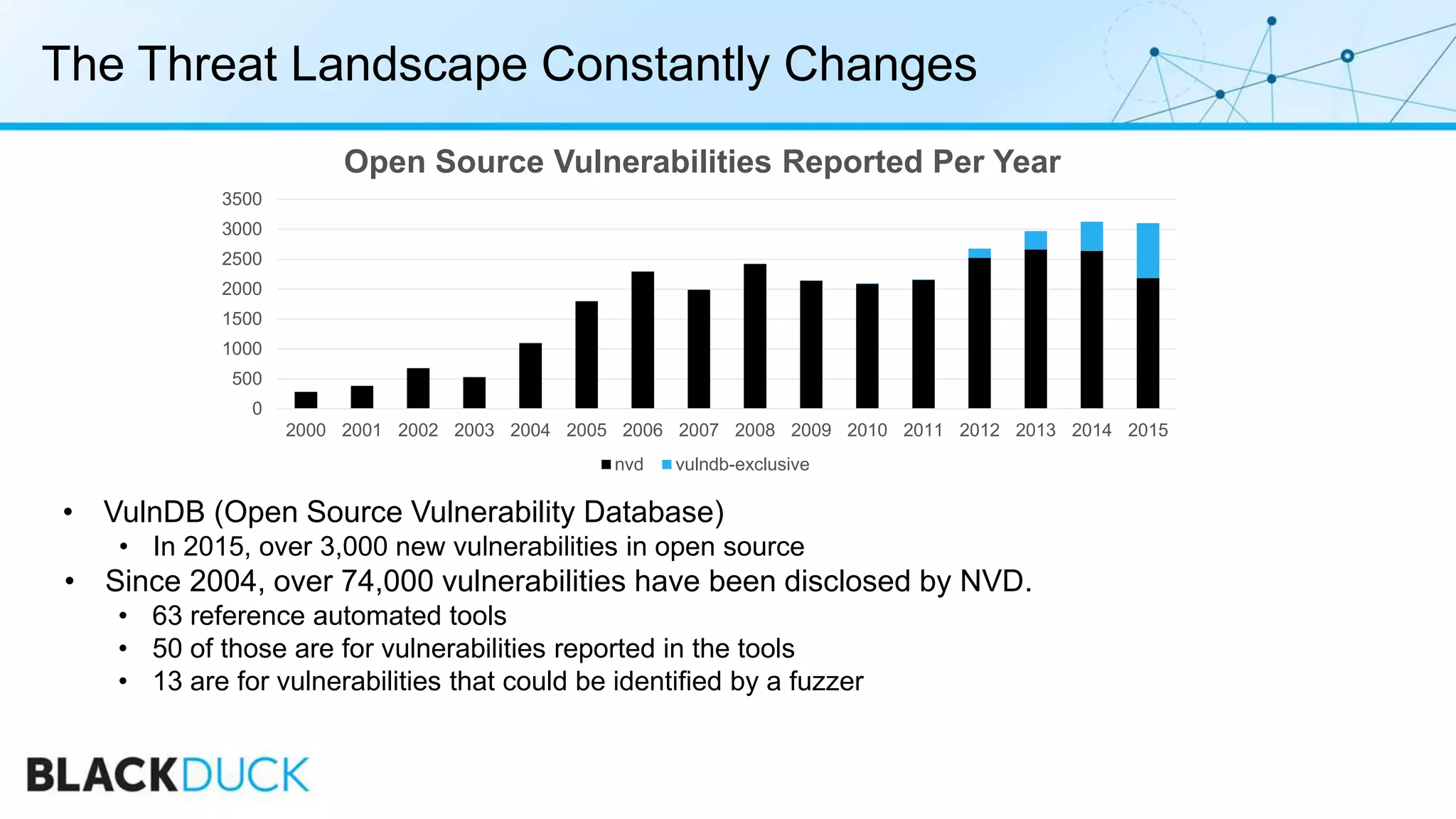
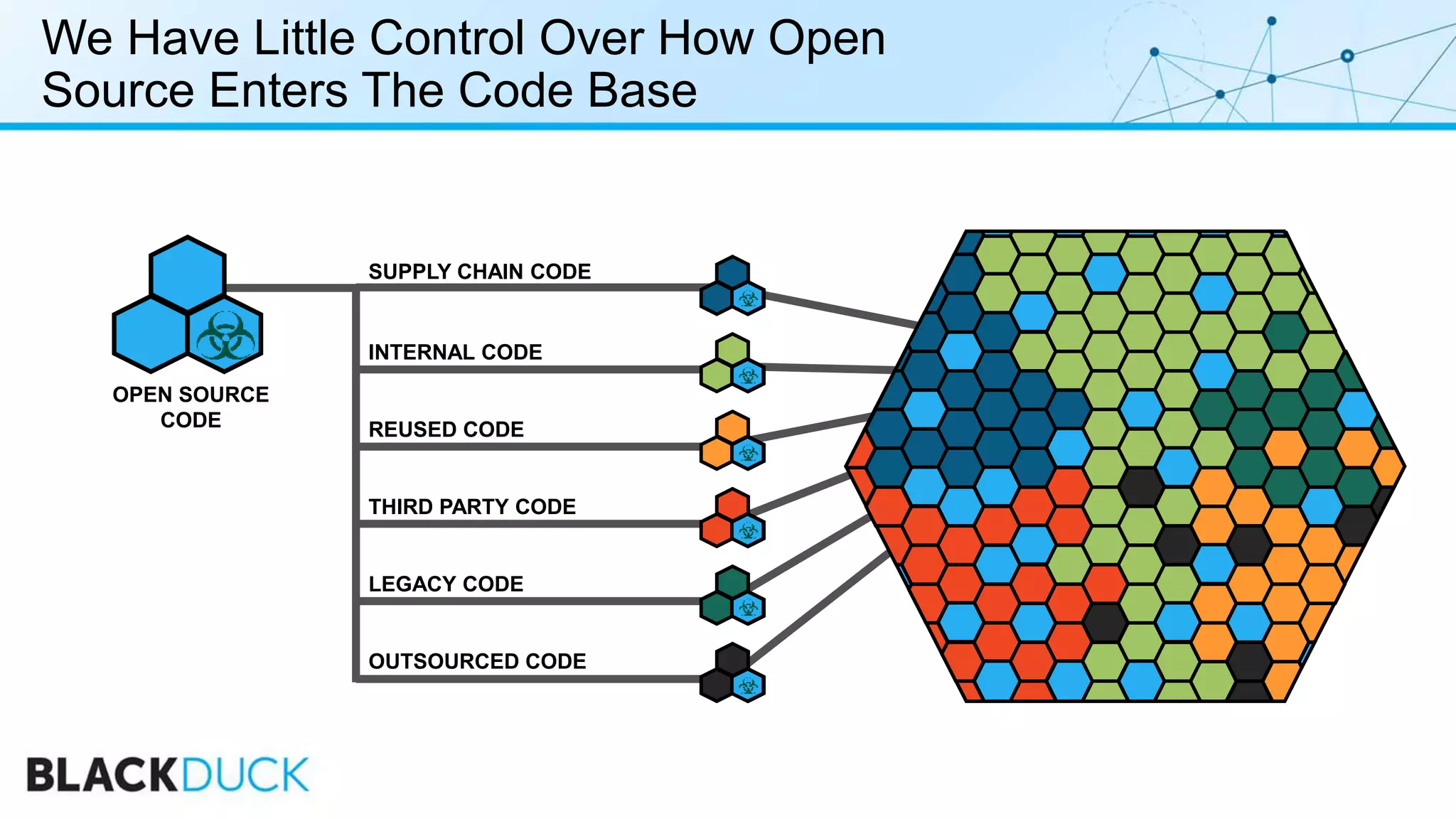
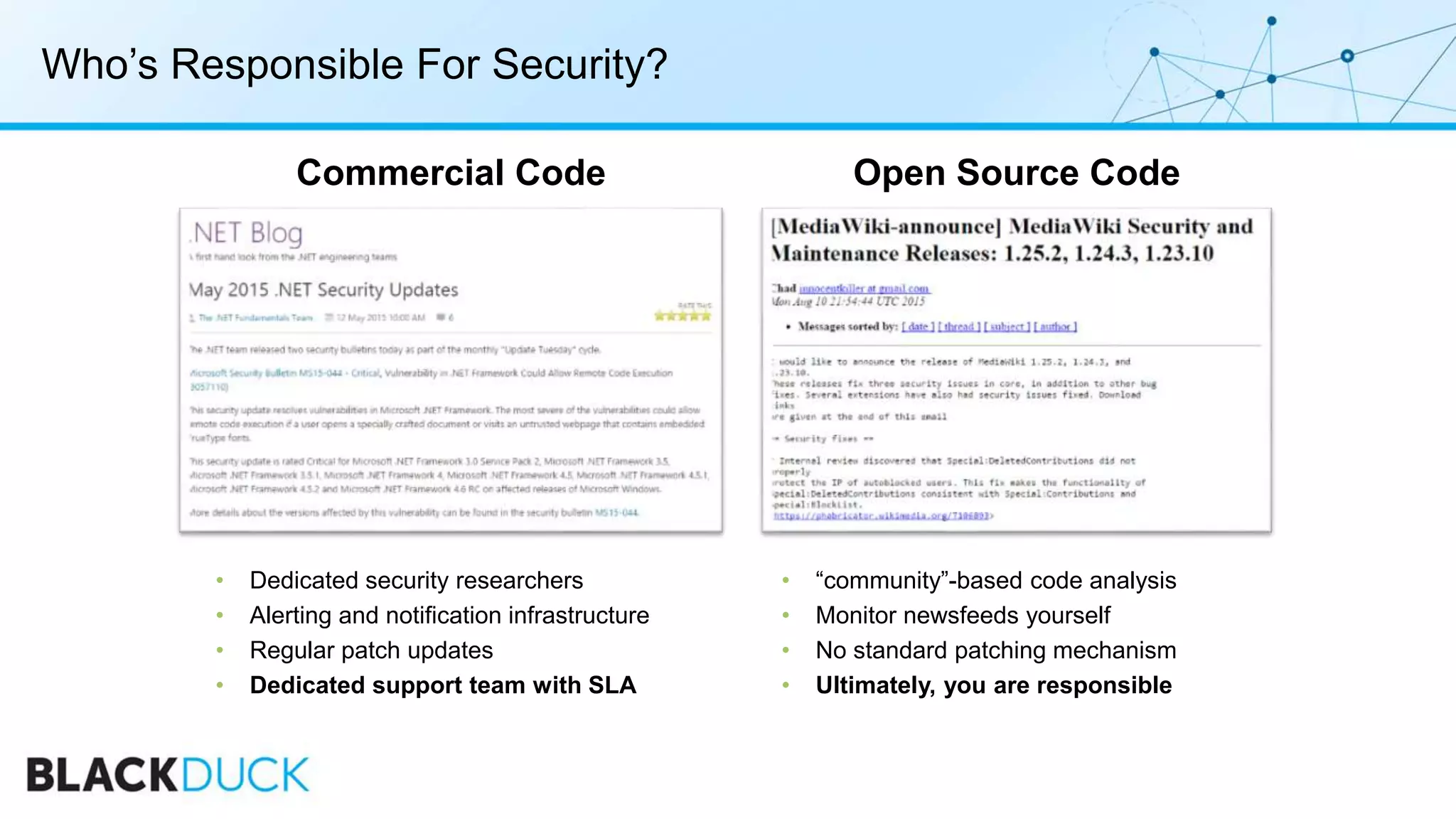
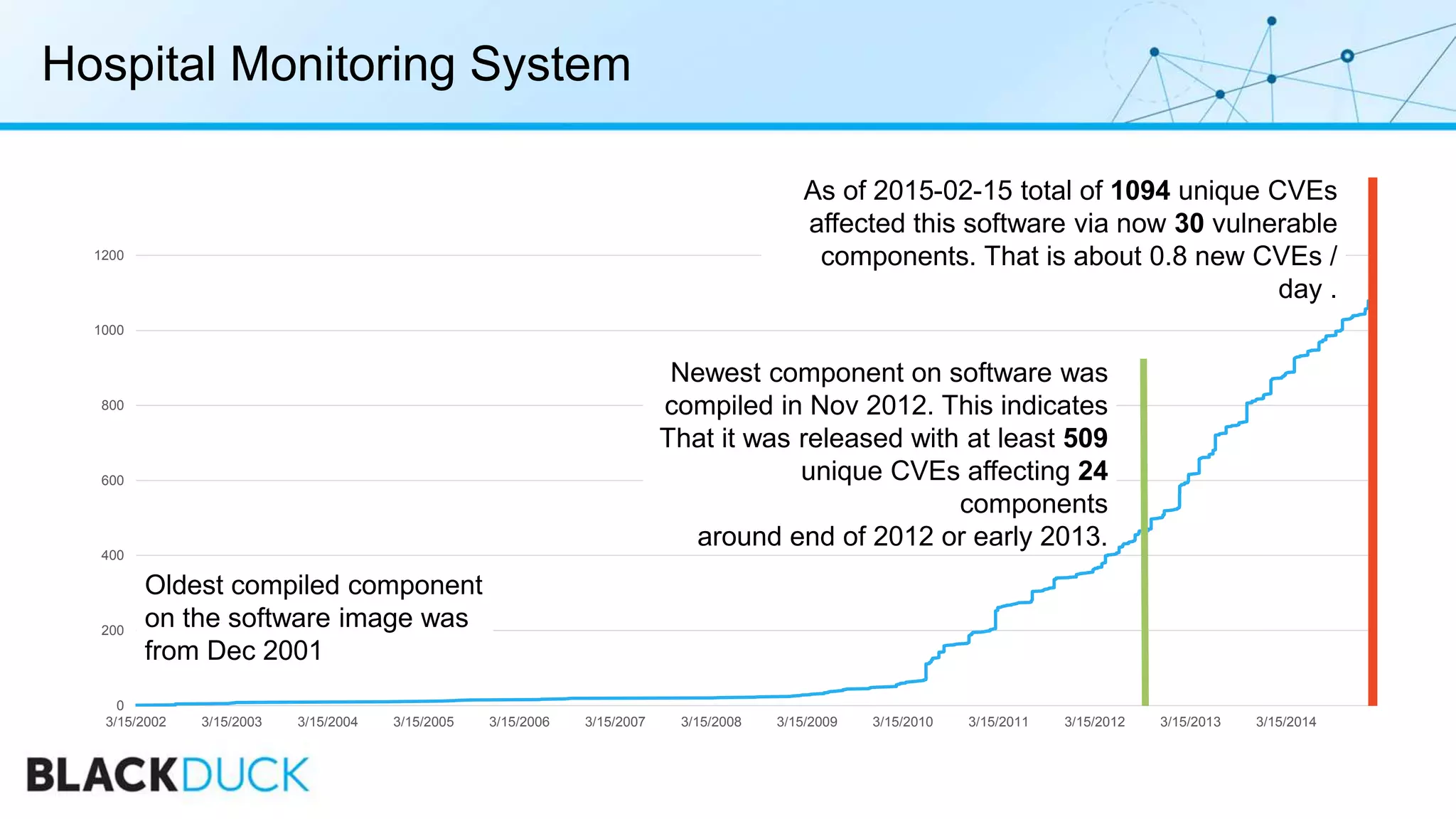
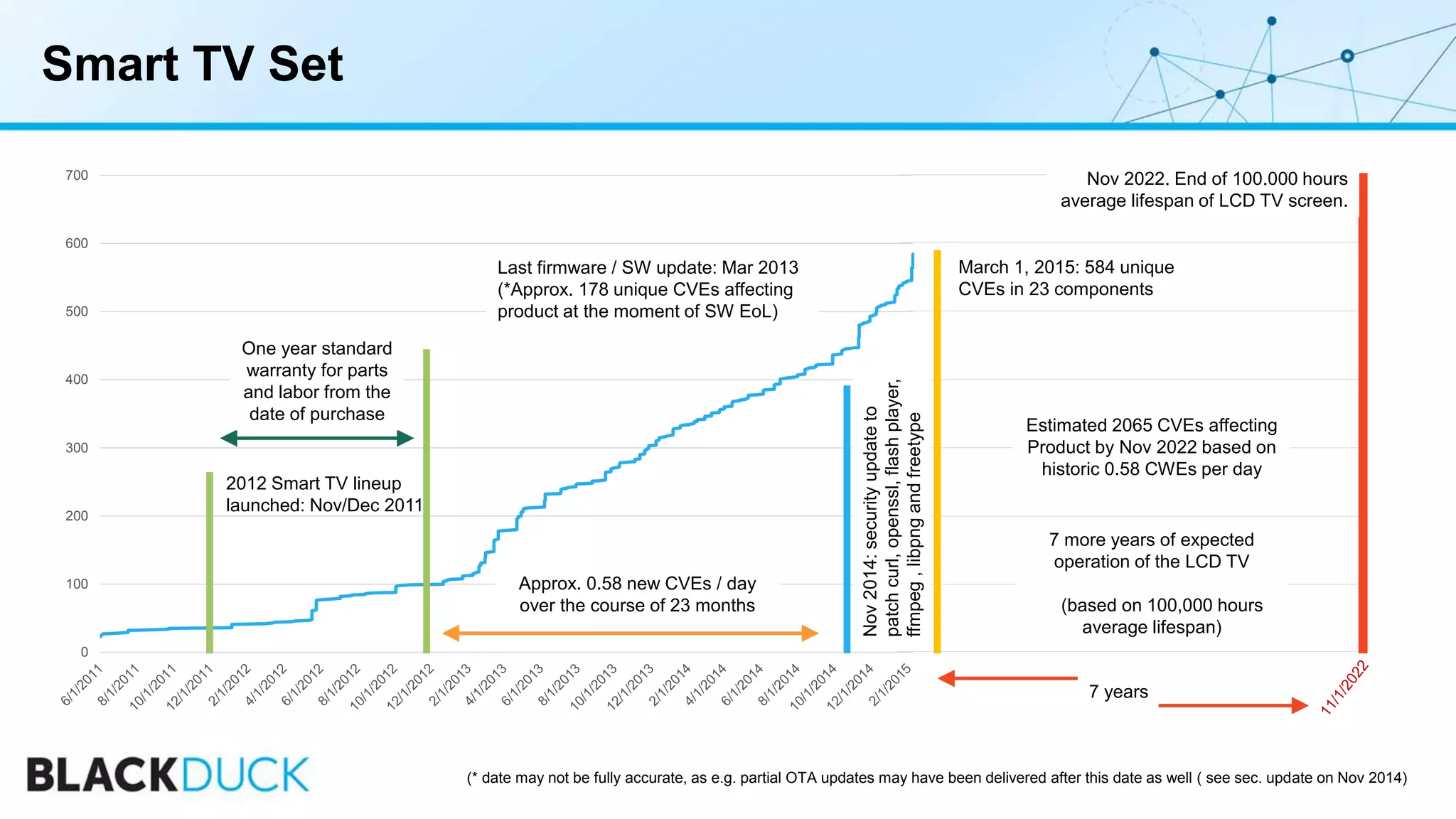
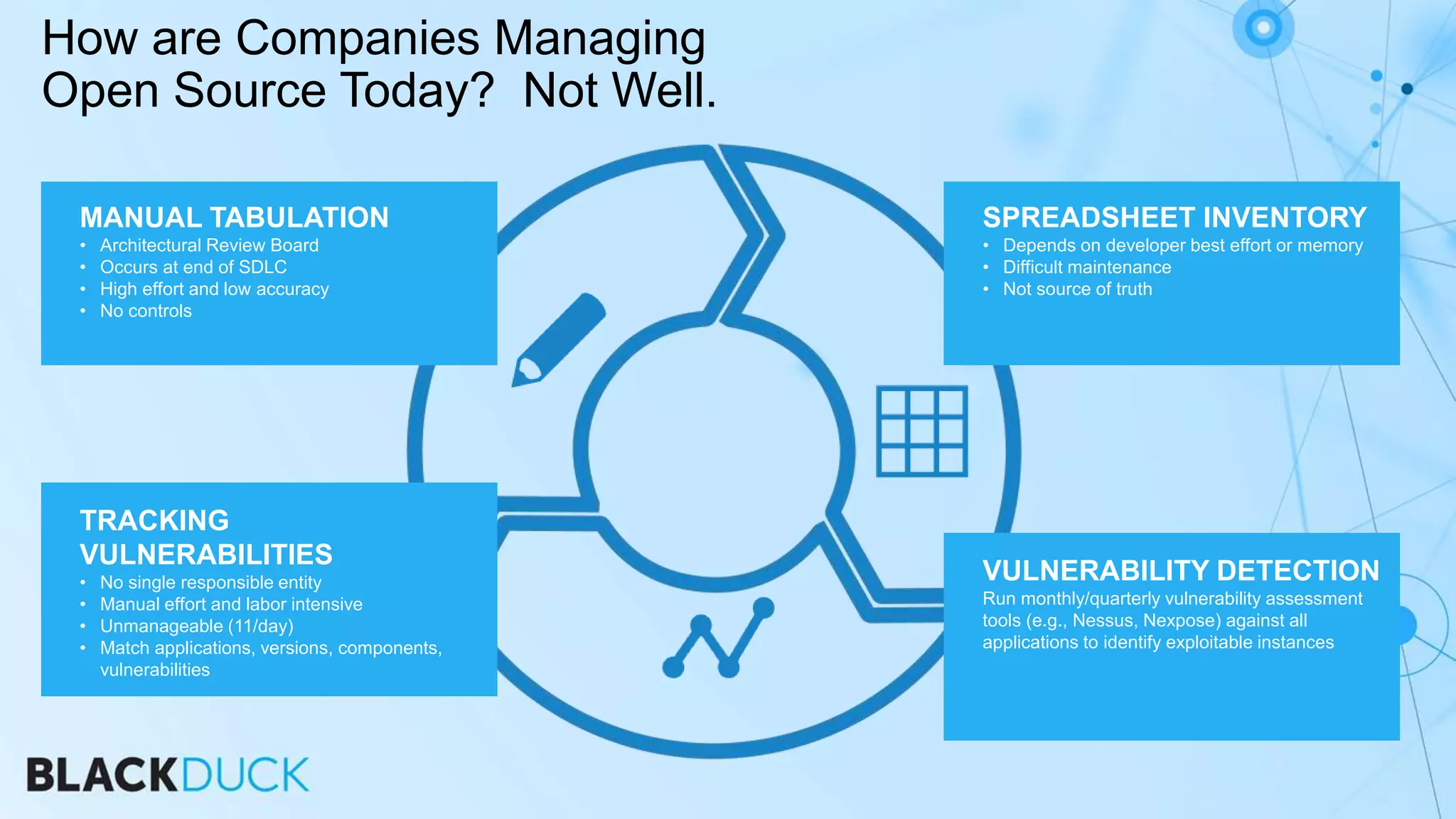
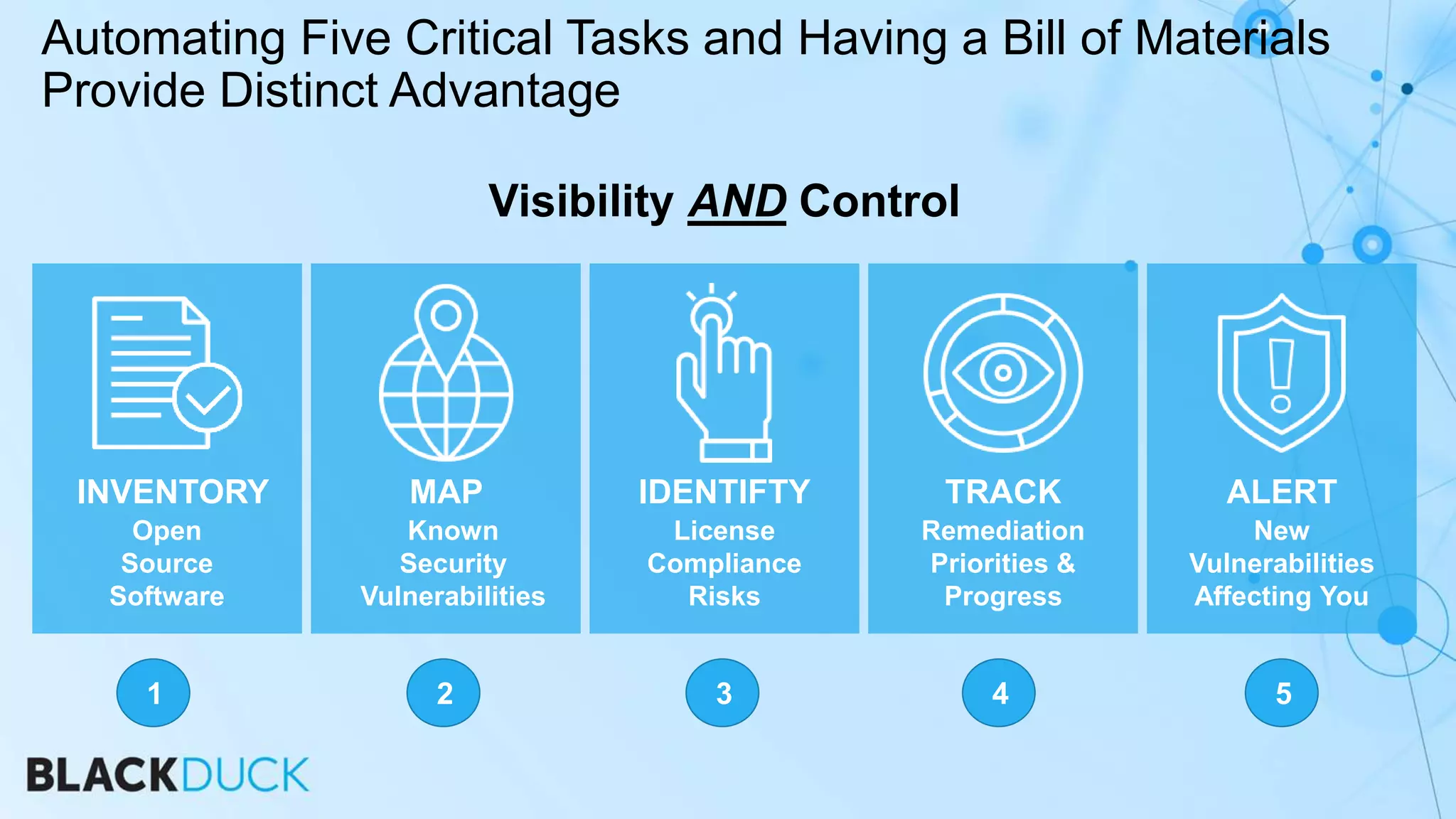
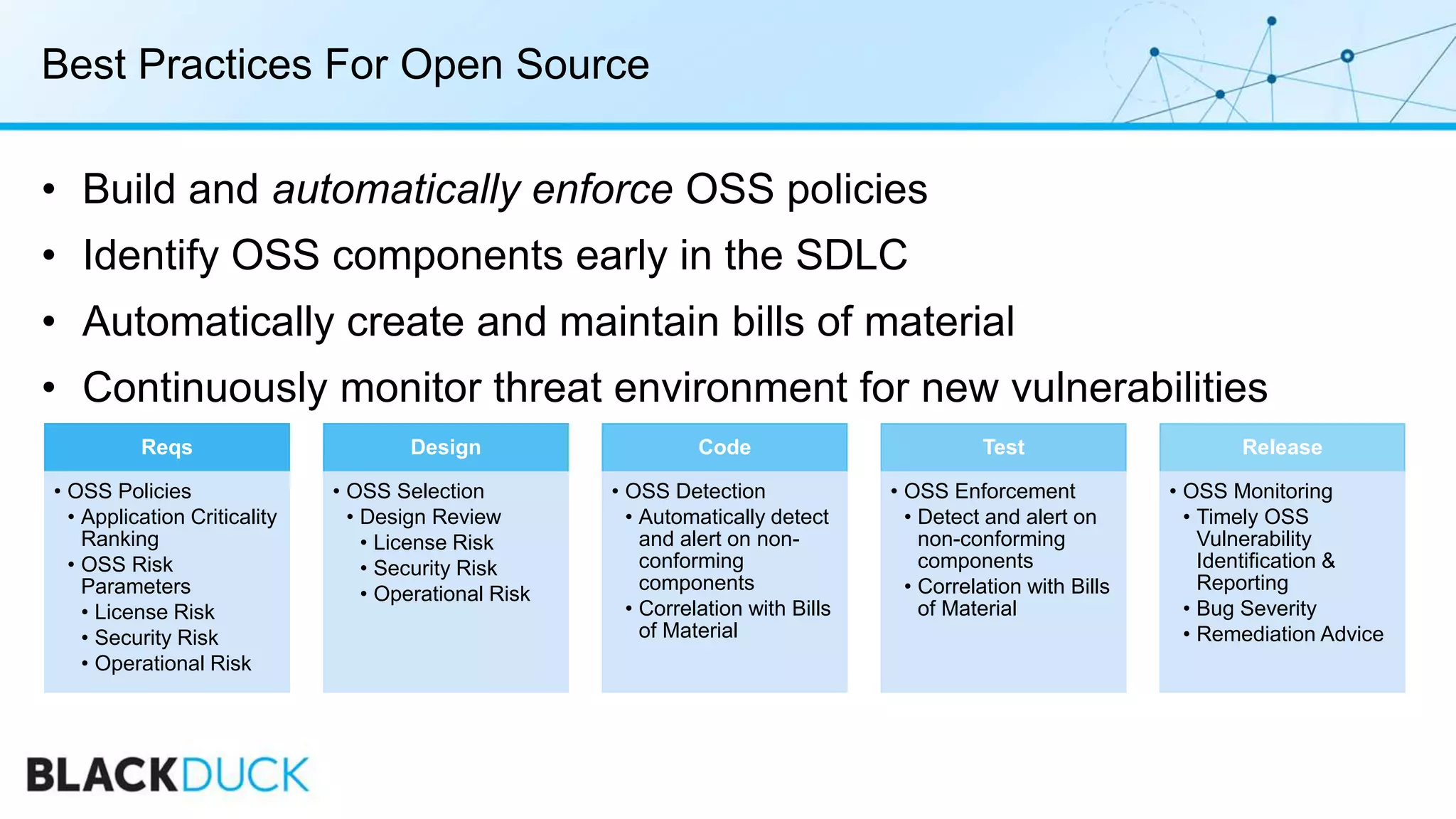
The document discusses the security challenges associated with open source software, highlighting the need for companies to manage vulnerabilities effectively. It outlines the limitations of traditional security testing tools in identifying issues within open source components and the growing number of vulnerabilities reported each year. Key takeaways emphasize the importance of continuous monitoring and adopting best practices throughout the software development lifecycle to mitigate risks associated with open source code.