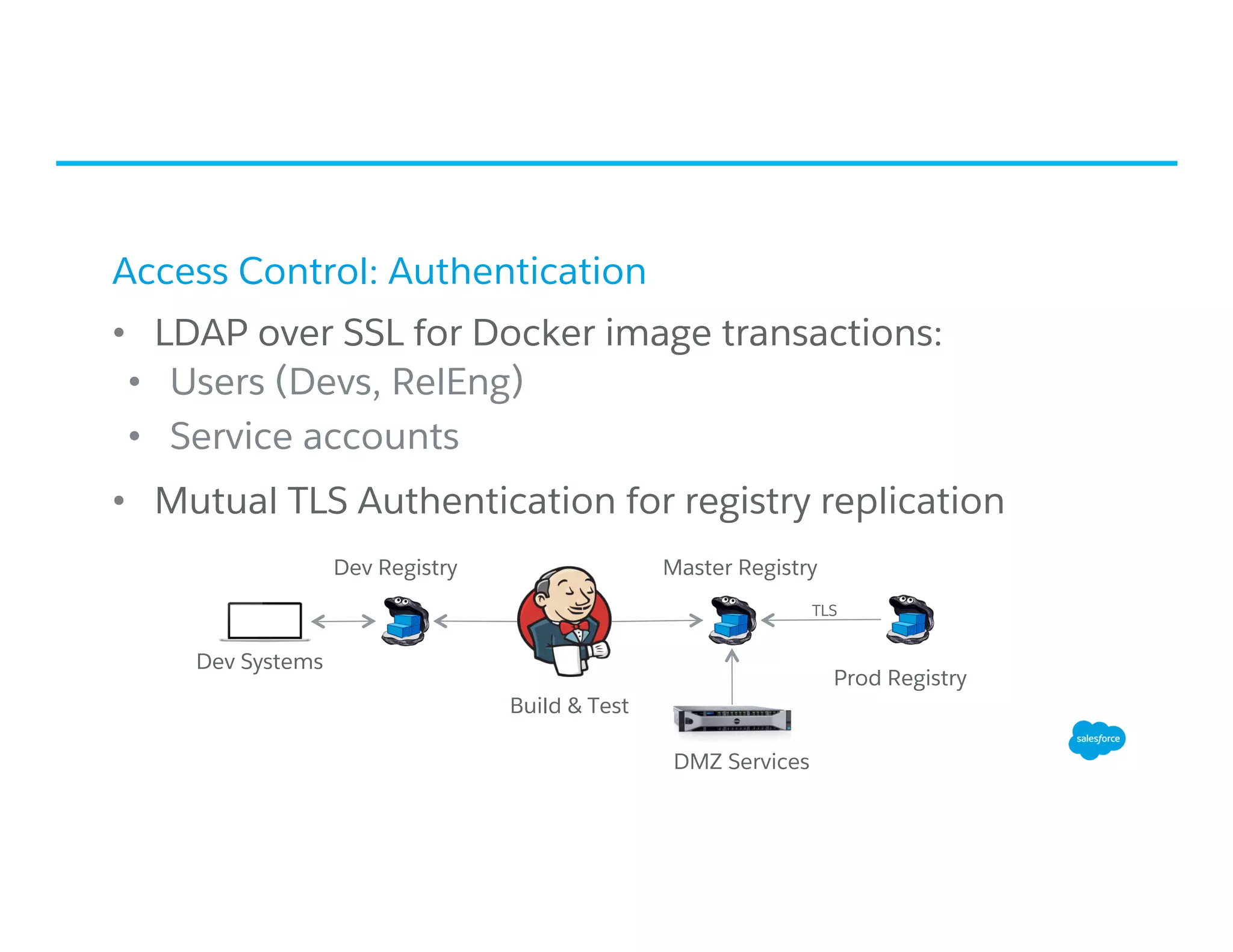
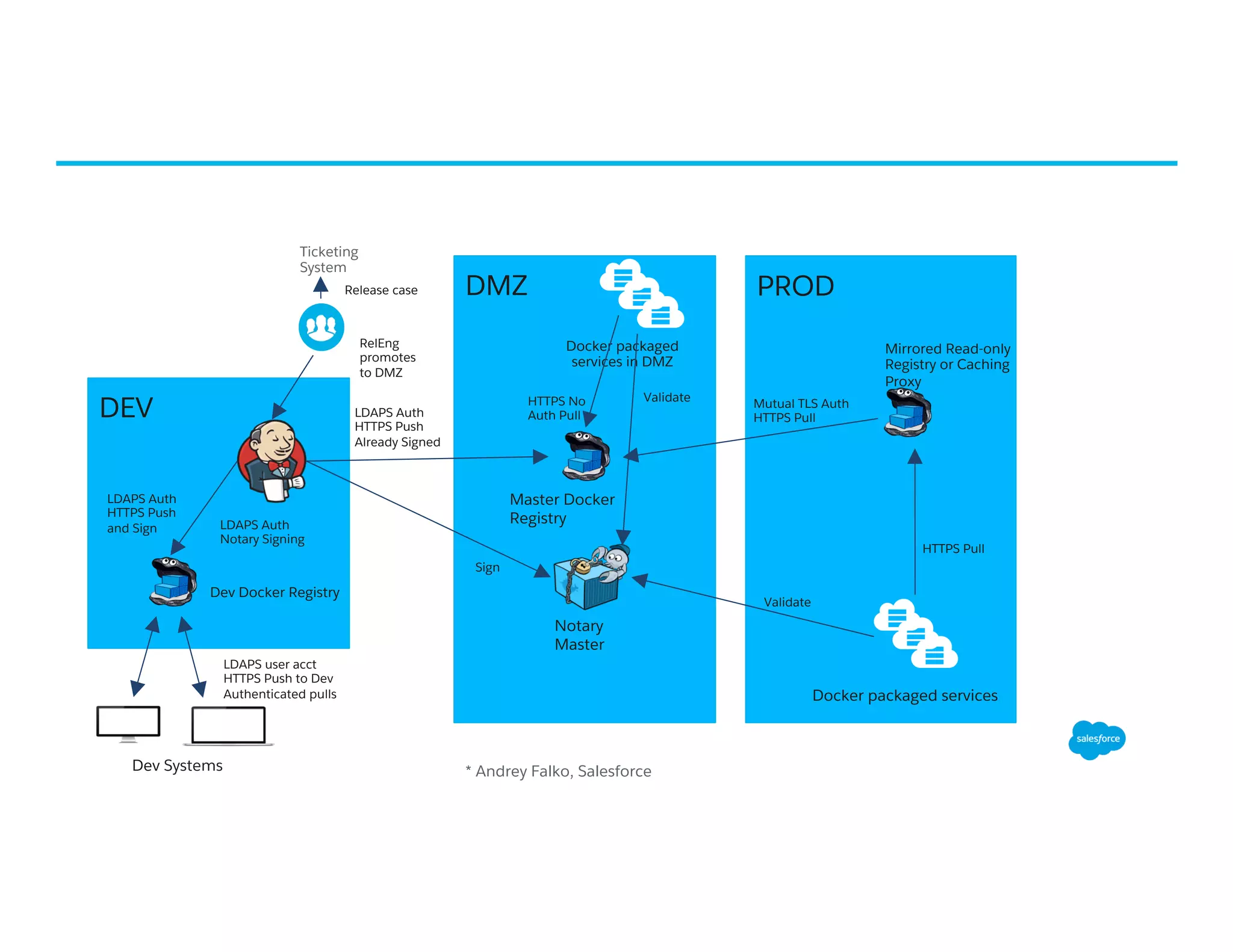
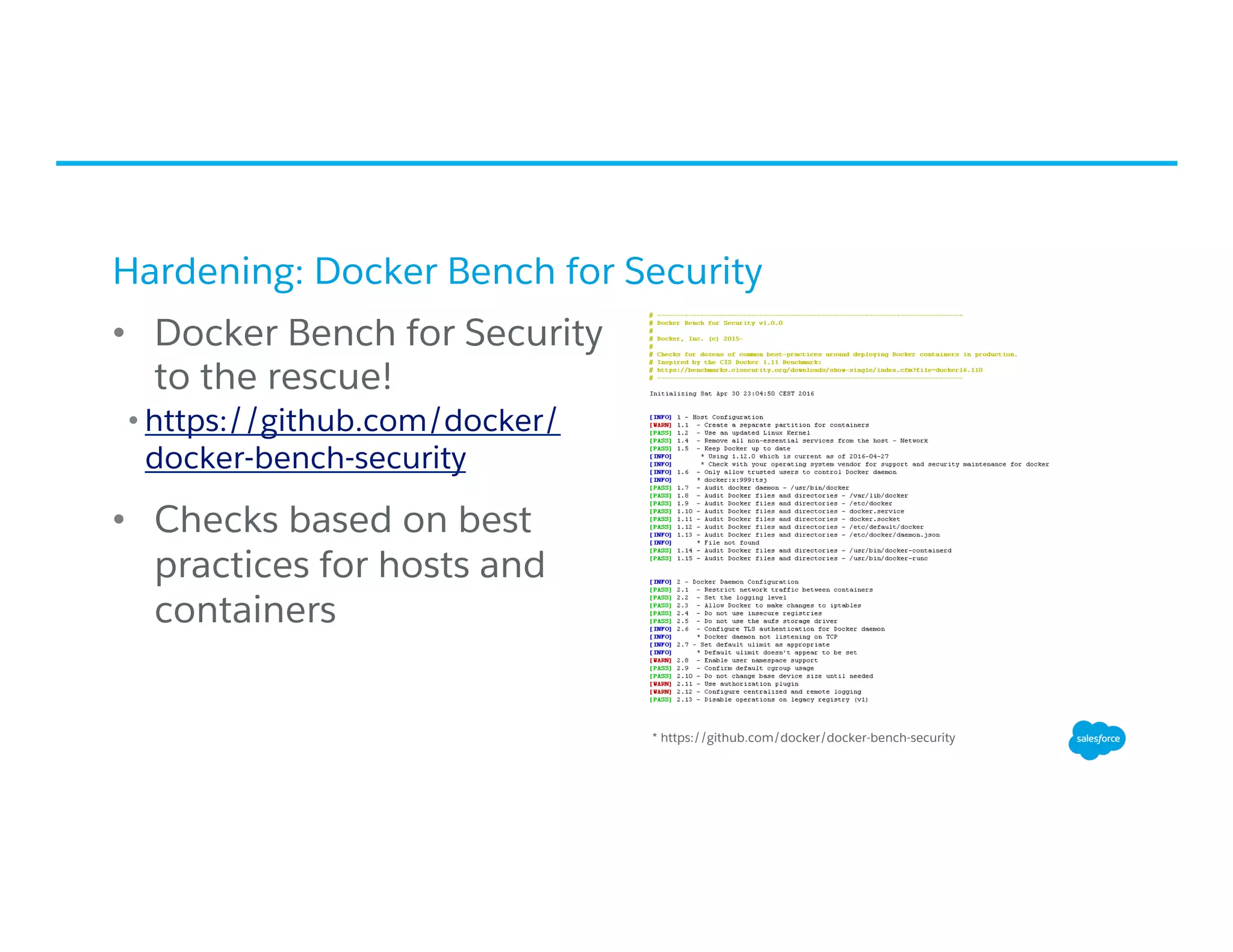
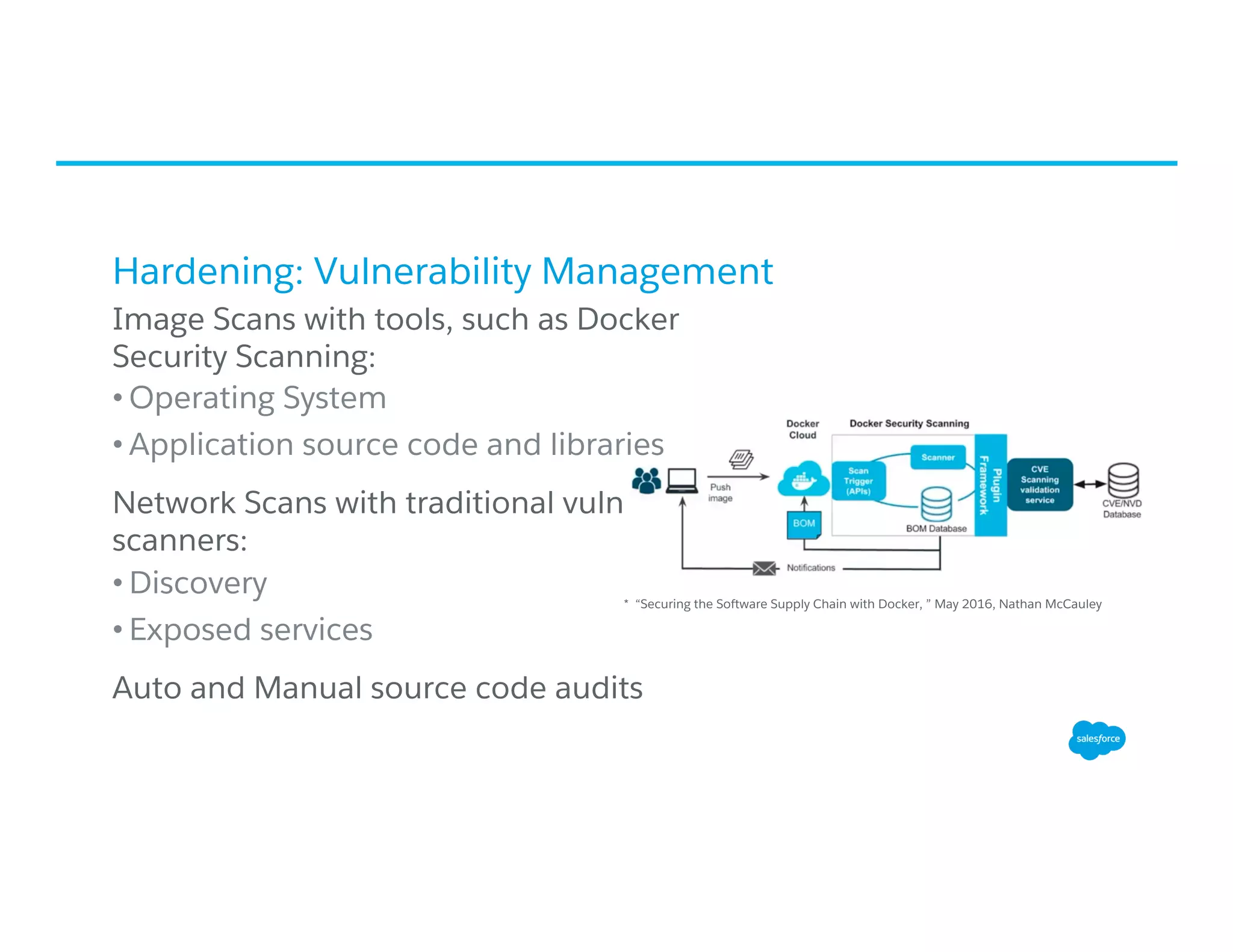
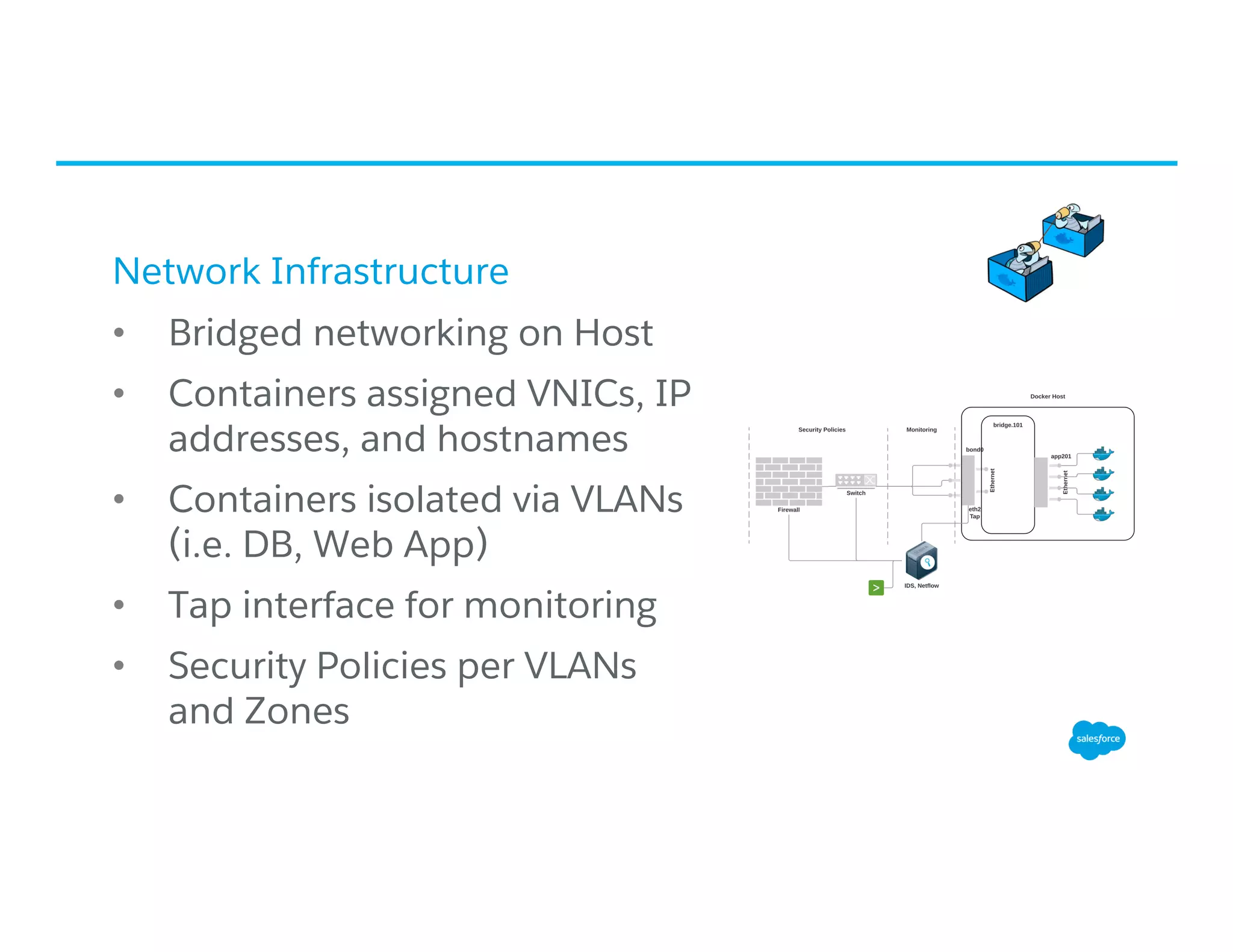
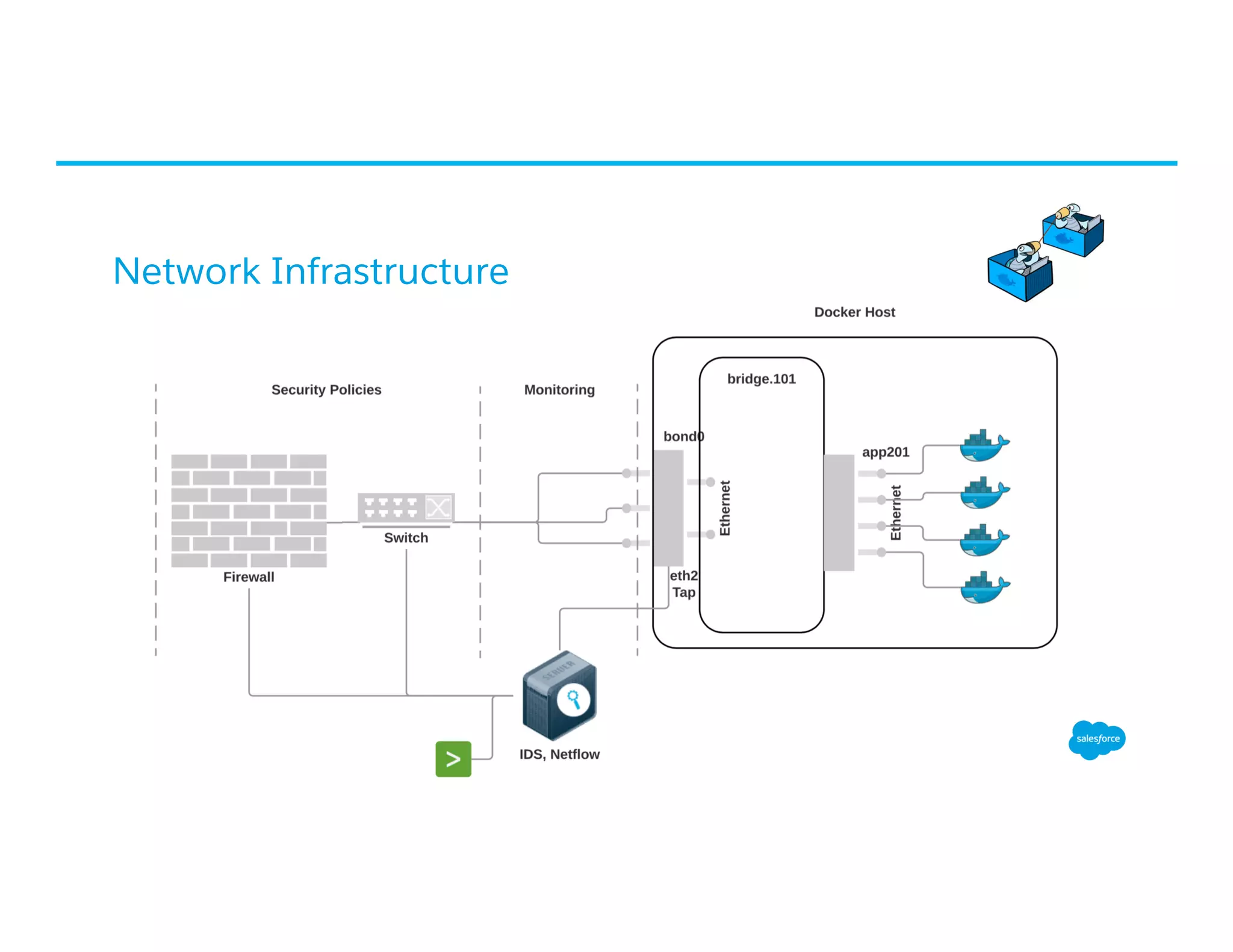
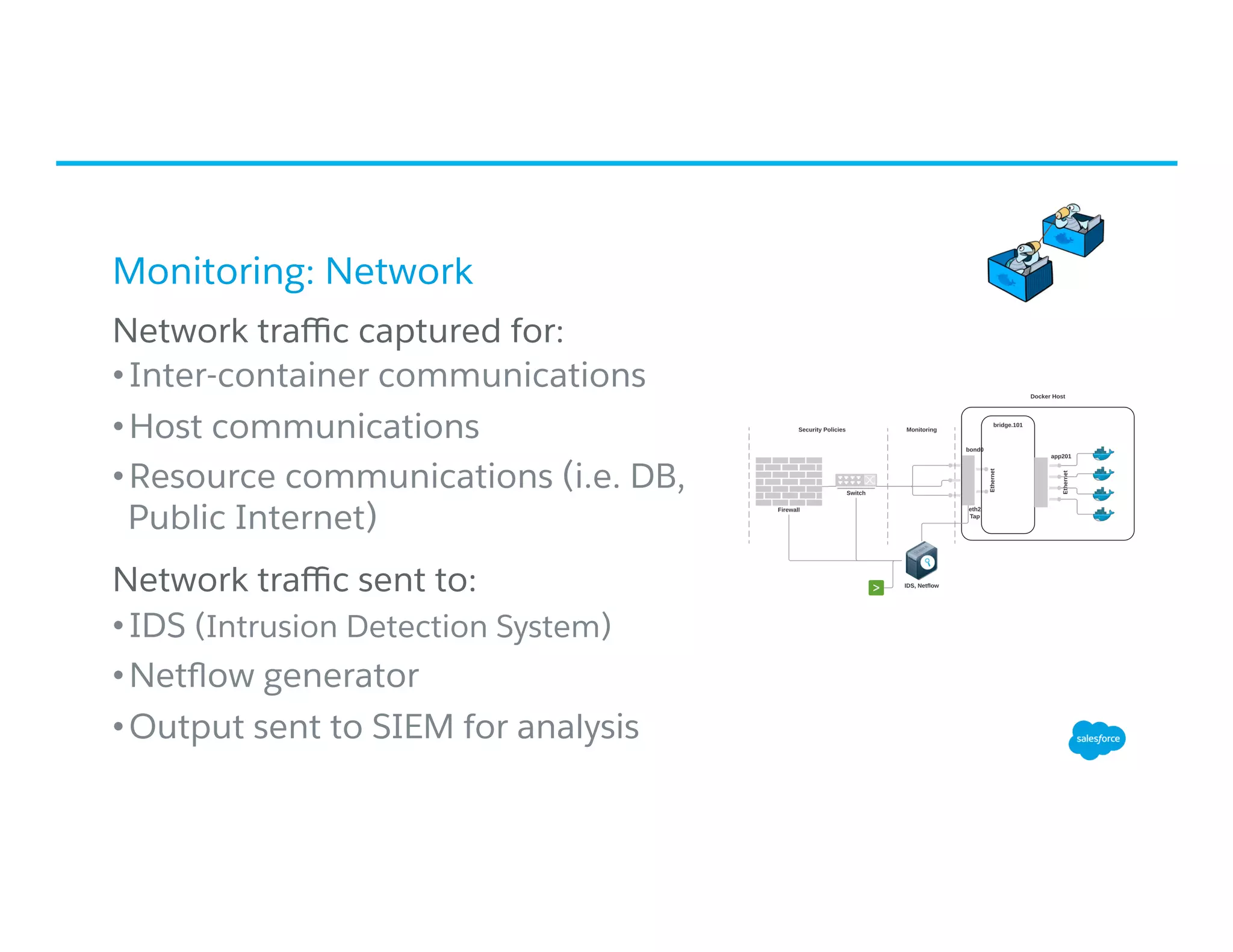
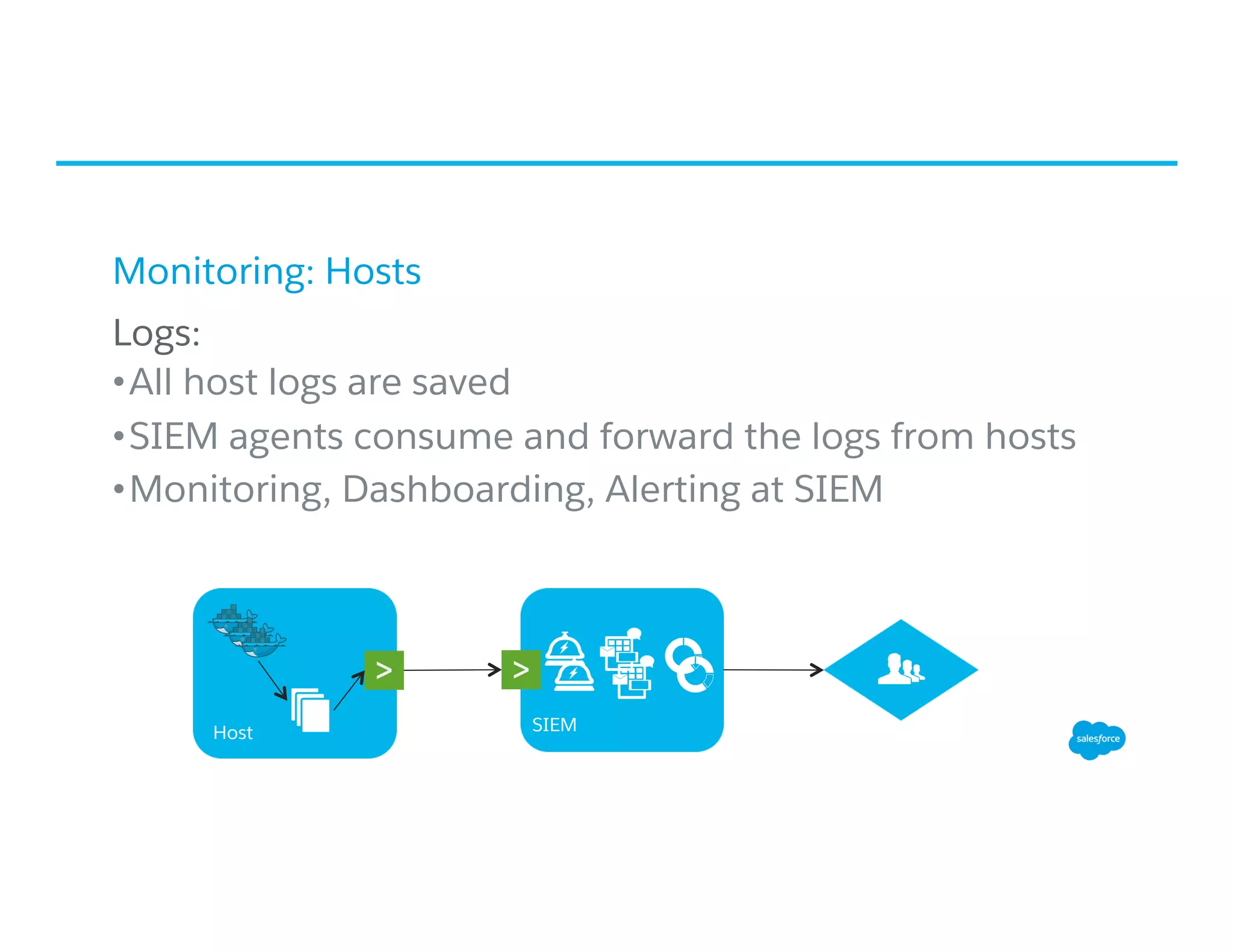
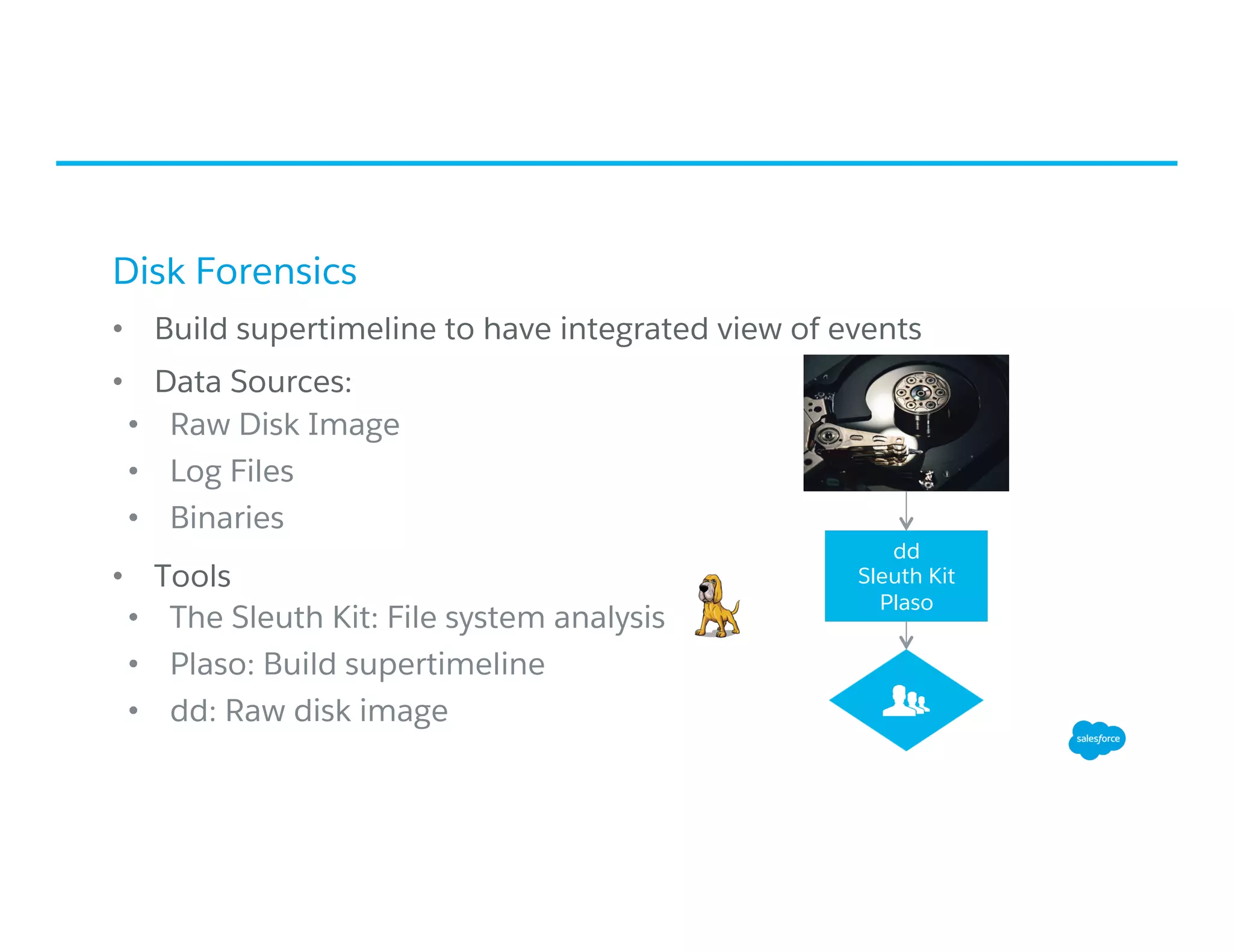
The document discusses securing container pipelines, outlining key threats, mitigation strategies, and the importance of monitoring throughout the pipeline process. It emphasizes hardening both host and container environments, implementing strict access controls, and employing vulnerability management techniques. Additionally, it covers digital forensics and network infrastructure monitoring as essential components of maintaining container security.





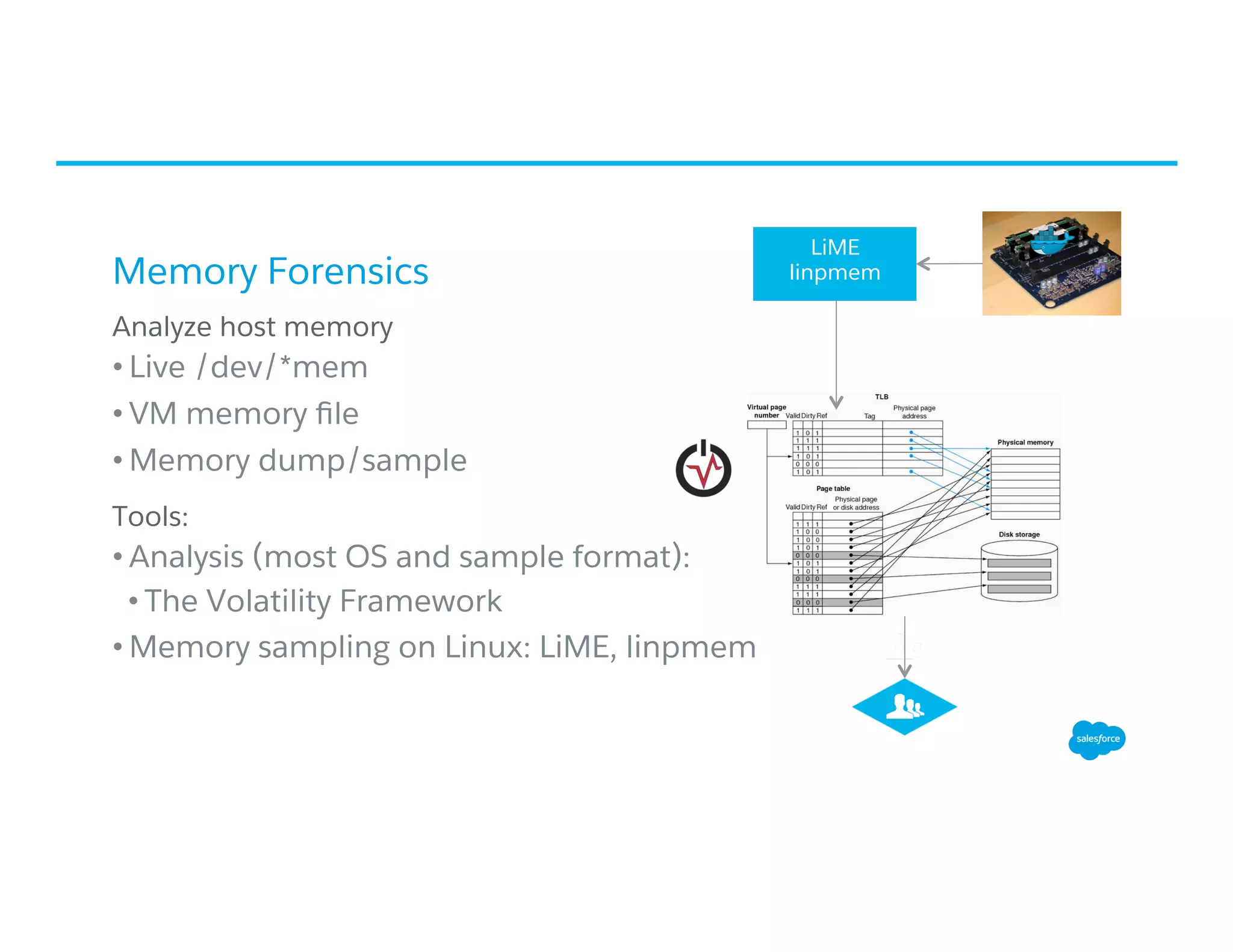
![Memory Forensics: Process Hierarchy
• pstree_hash [new]: View Docker
processes in a tree view based on
the PID hash table vs. linked list
• Use case: Detect rogue or injected
child processes/containers](https://image.slidesharecdn.com/dockercon-2016-cg-securingthecontainerpipelineatsalesforce-sf-6-23-2016-public-160627171137/75/Securing-the-Container-Pipeline-at-Salesforce-by-Cem-Gurkok-34-2048.jpg)
![Memory Forensics: Process Integrity
• process_compare [new]: Detect if user space binary has
been tampered with in memory (in memory binary vs. on
disk) [5]
• Works when binary symbols can’t be extracted](https://image.slidesharecdn.com/dockercon-2016-cg-securingthecontainerpipelineatsalesforce-sf-6-23-2016-public-160627171137/75/Securing-the-Container-Pipeline-at-Salesforce-by-Cem-Gurkok-37-2048.jpg)