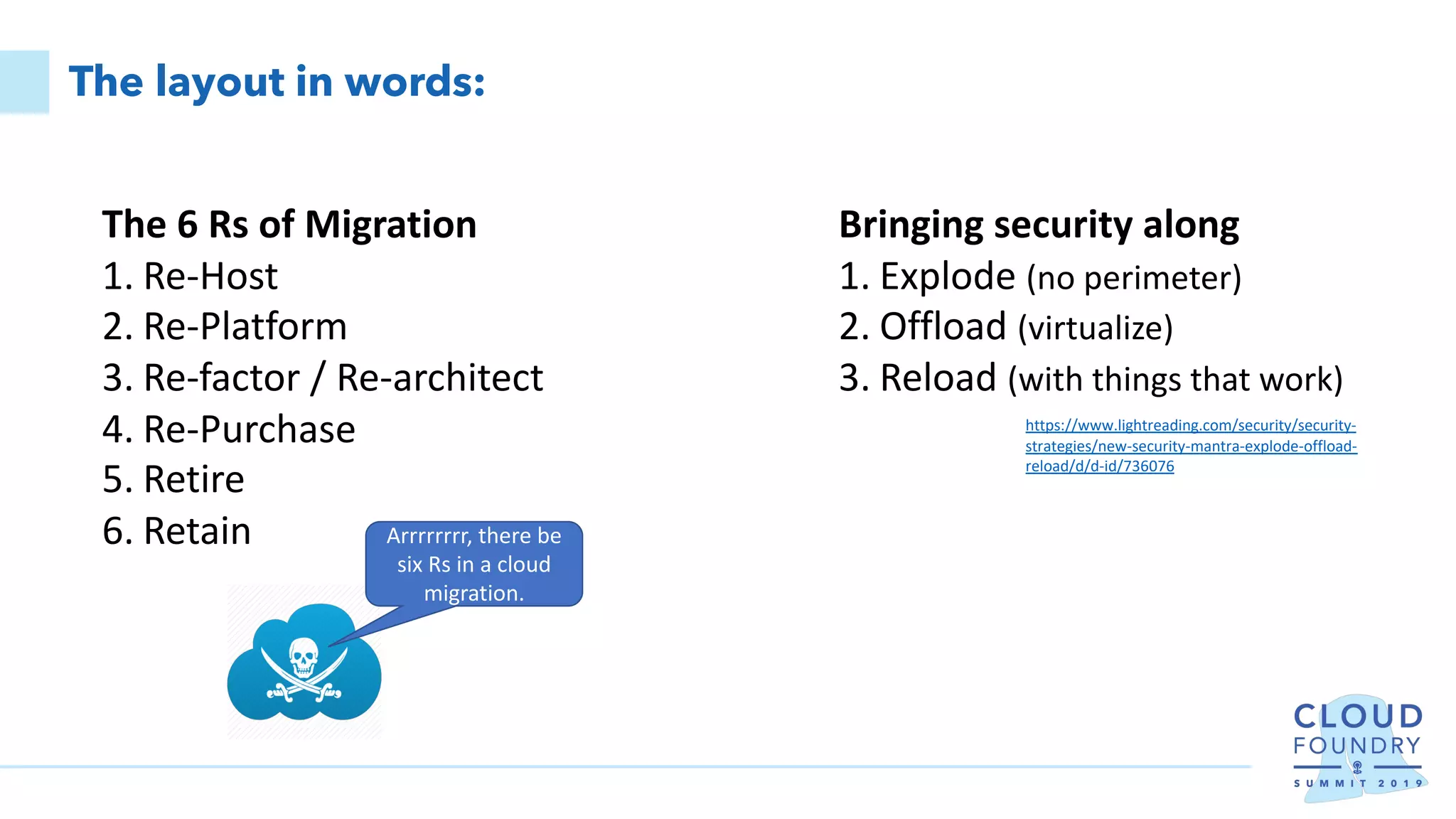
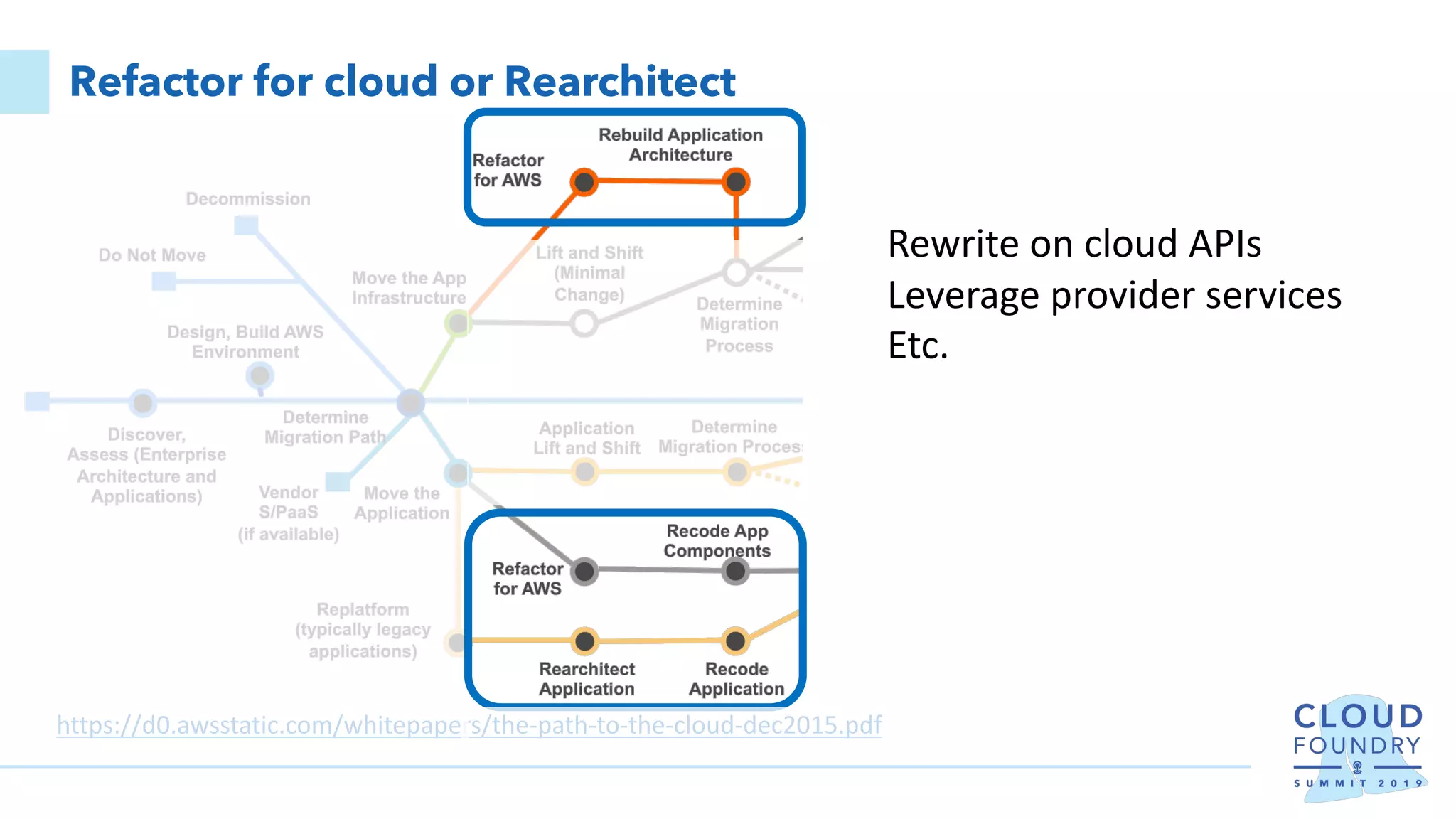
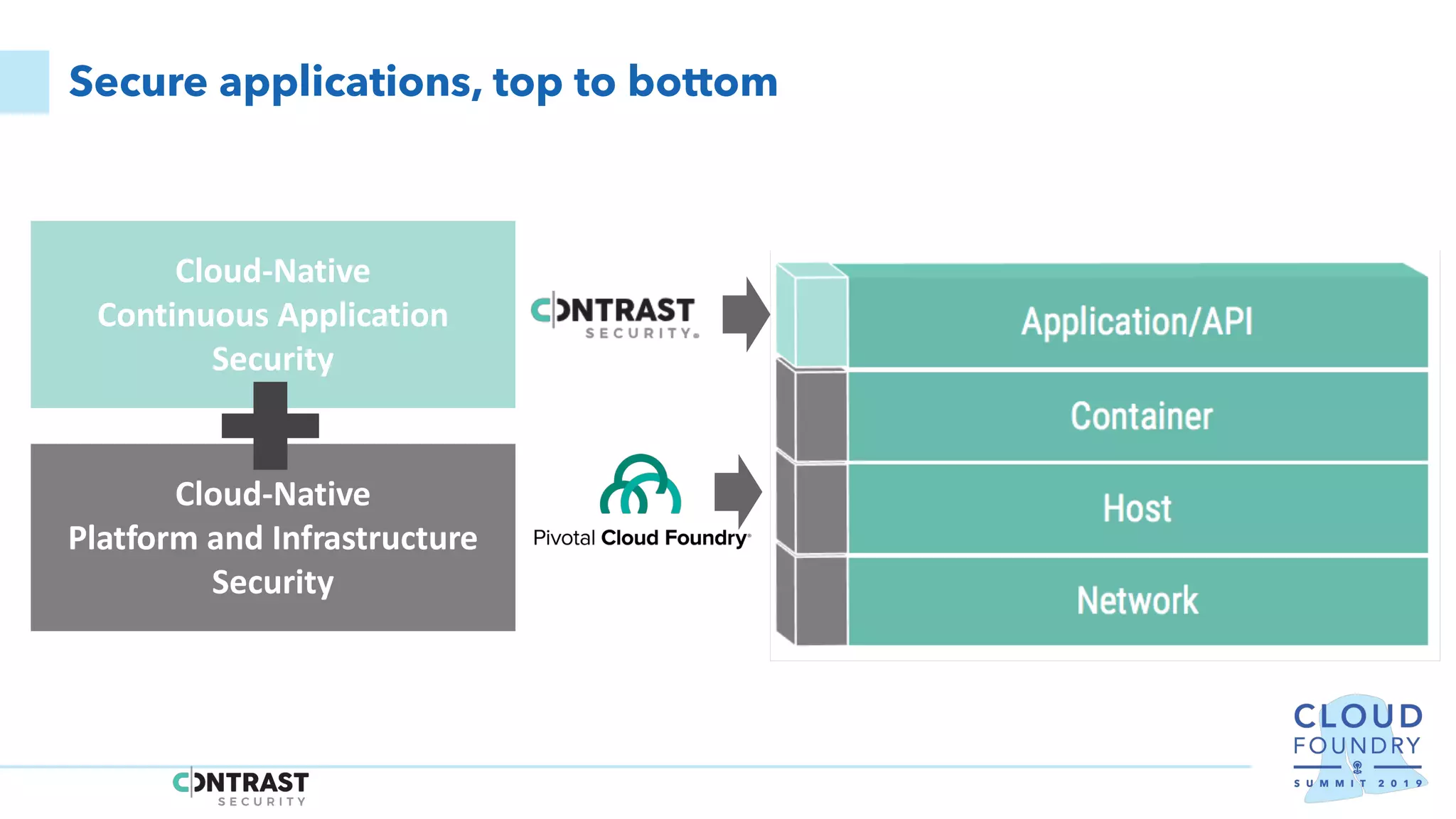
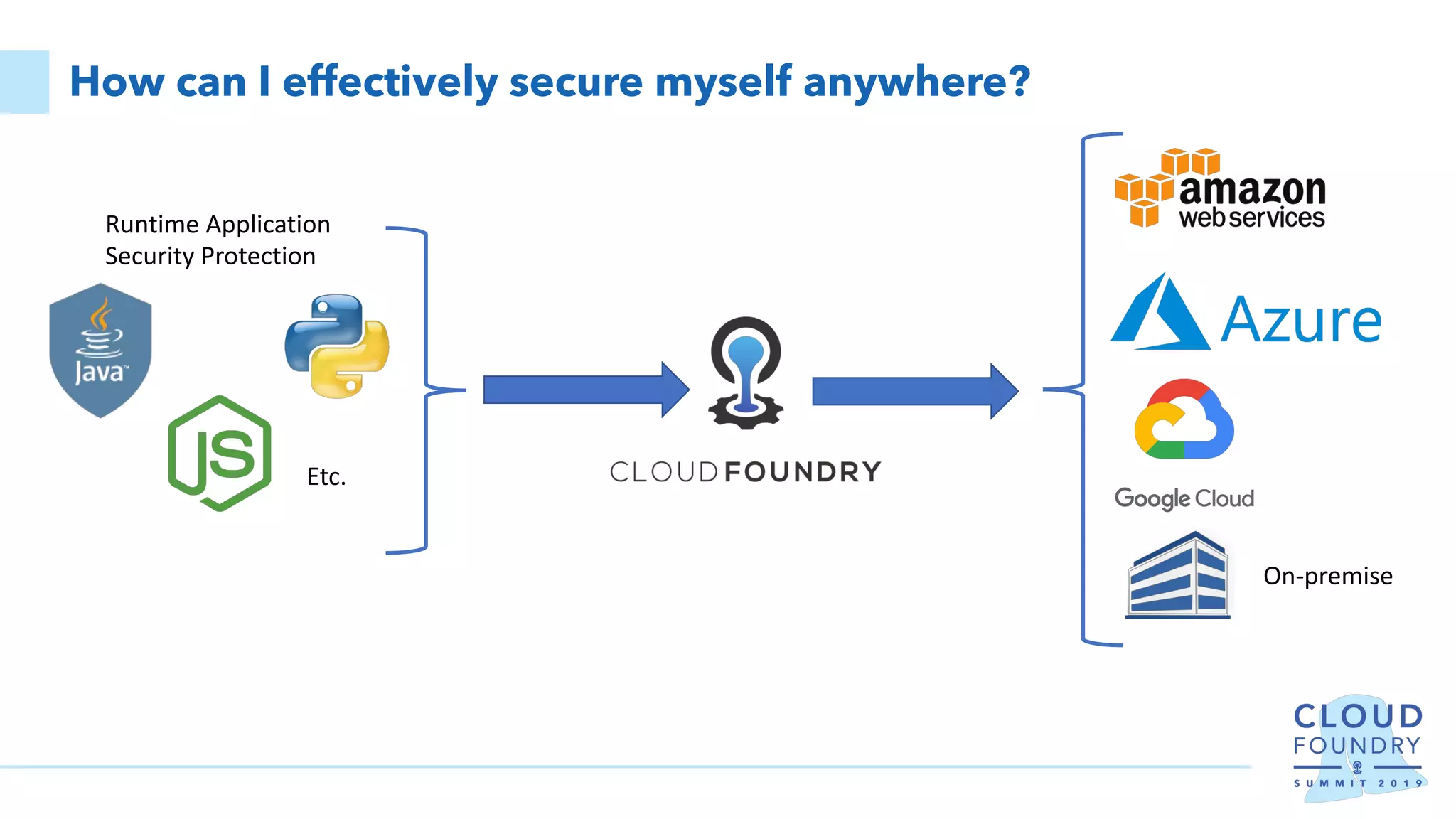
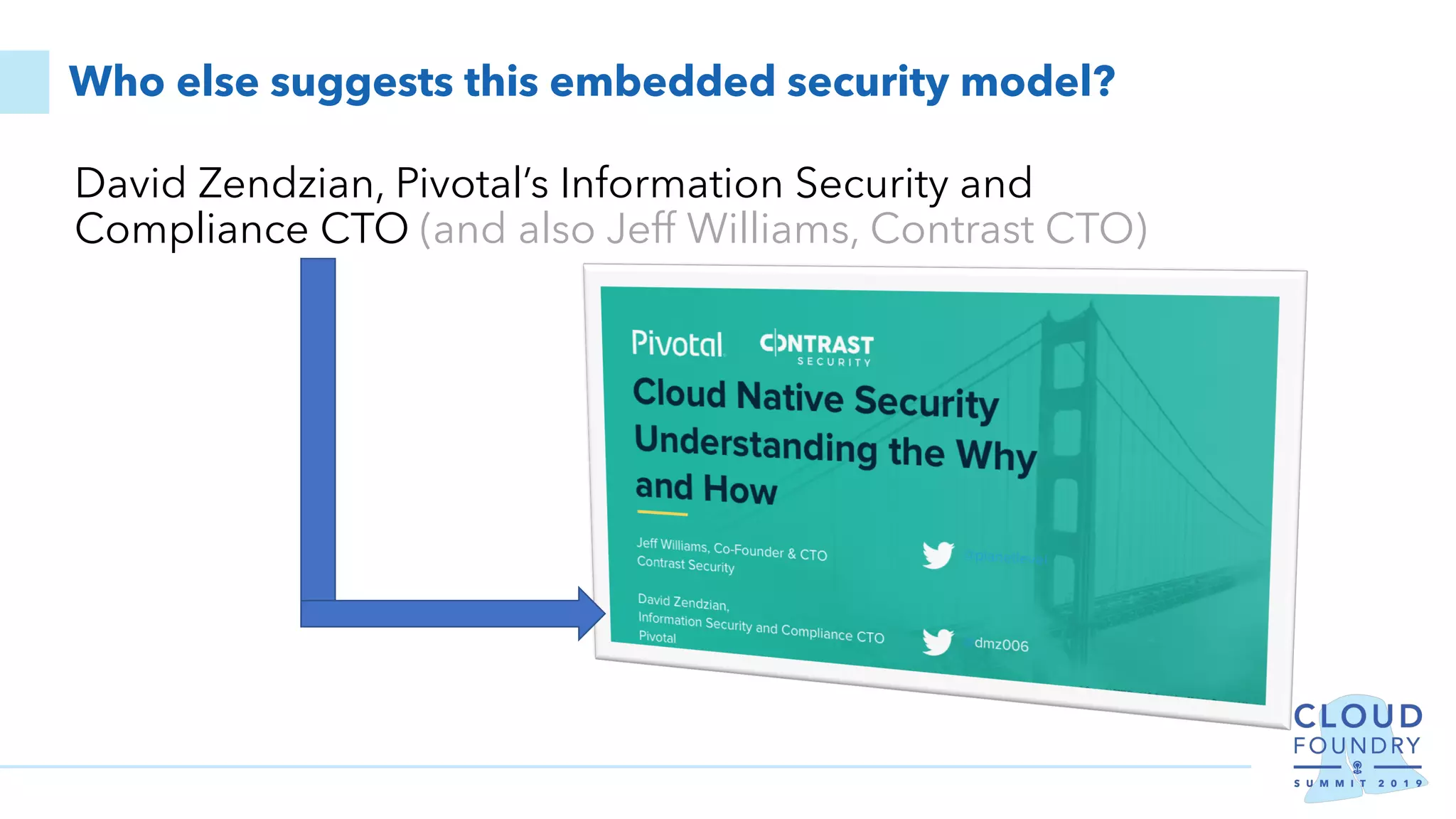
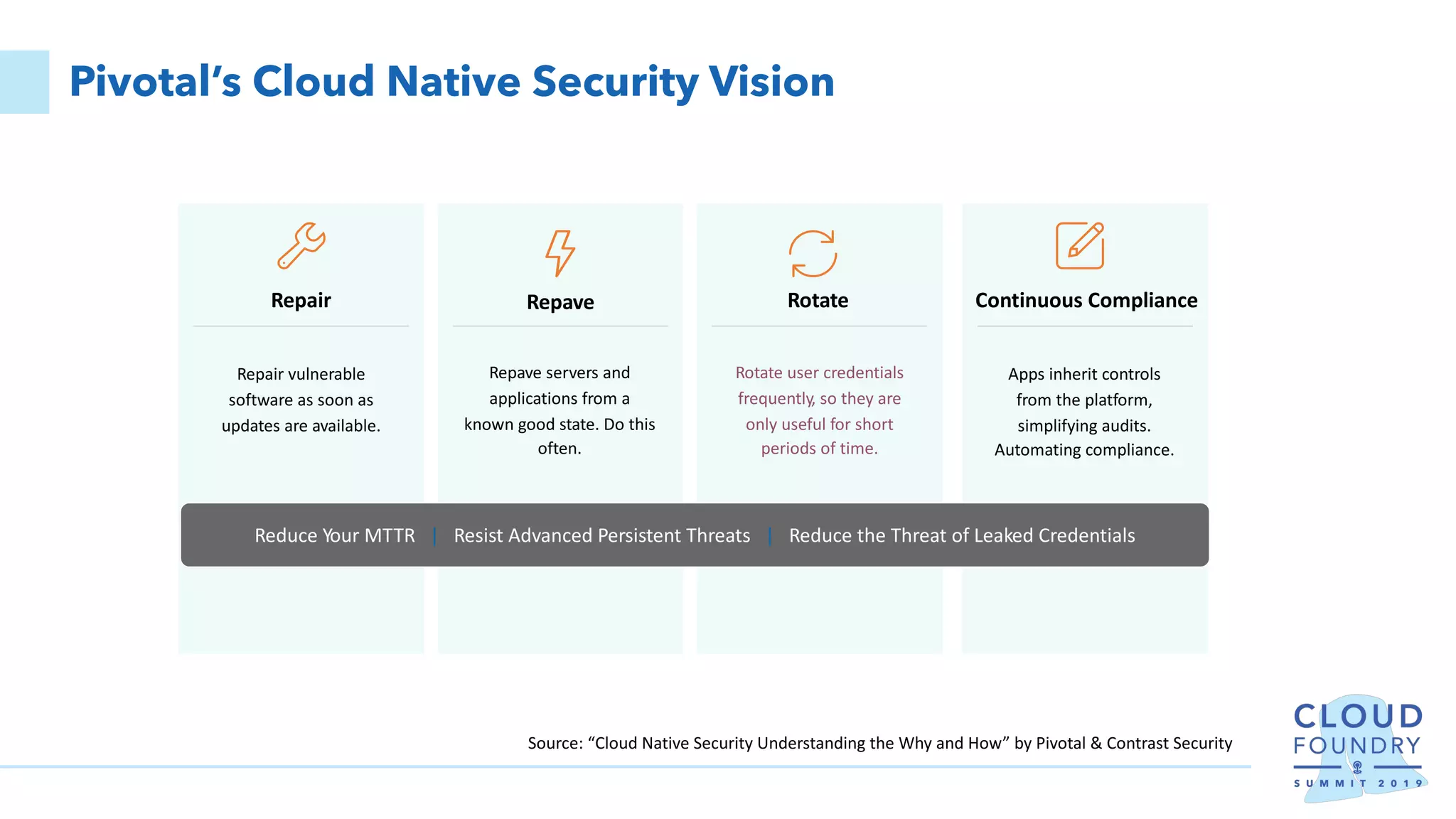
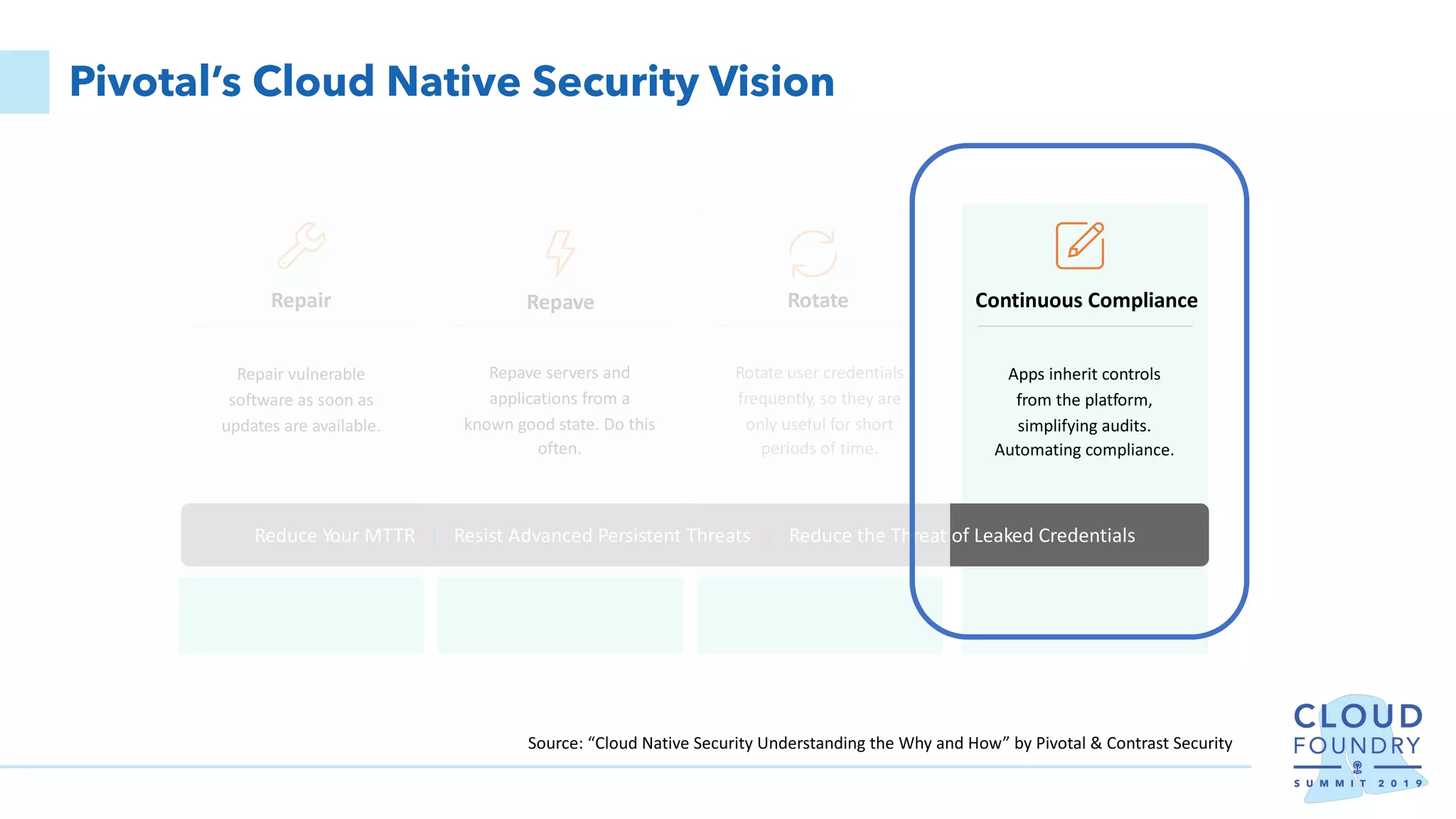
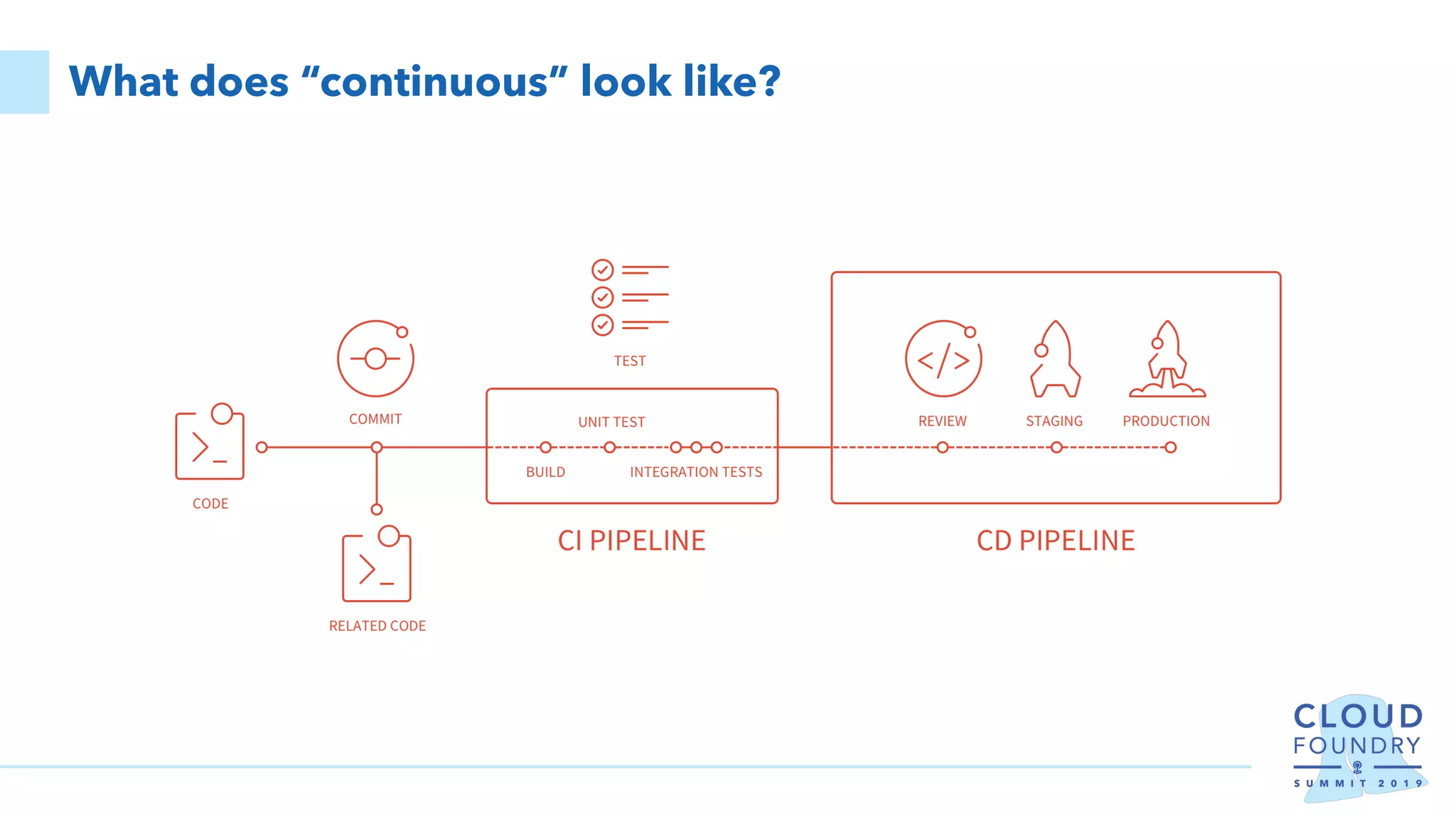
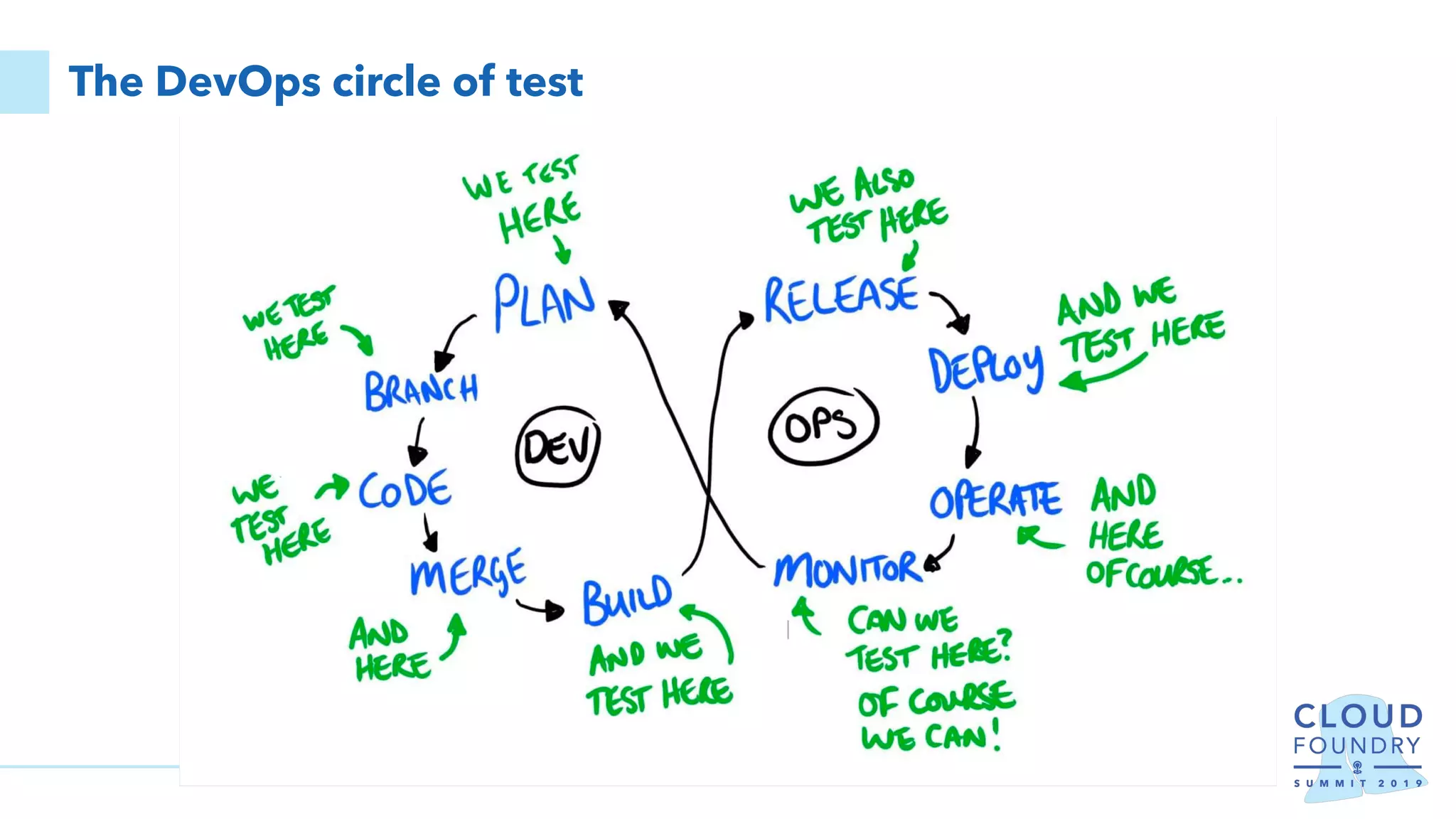
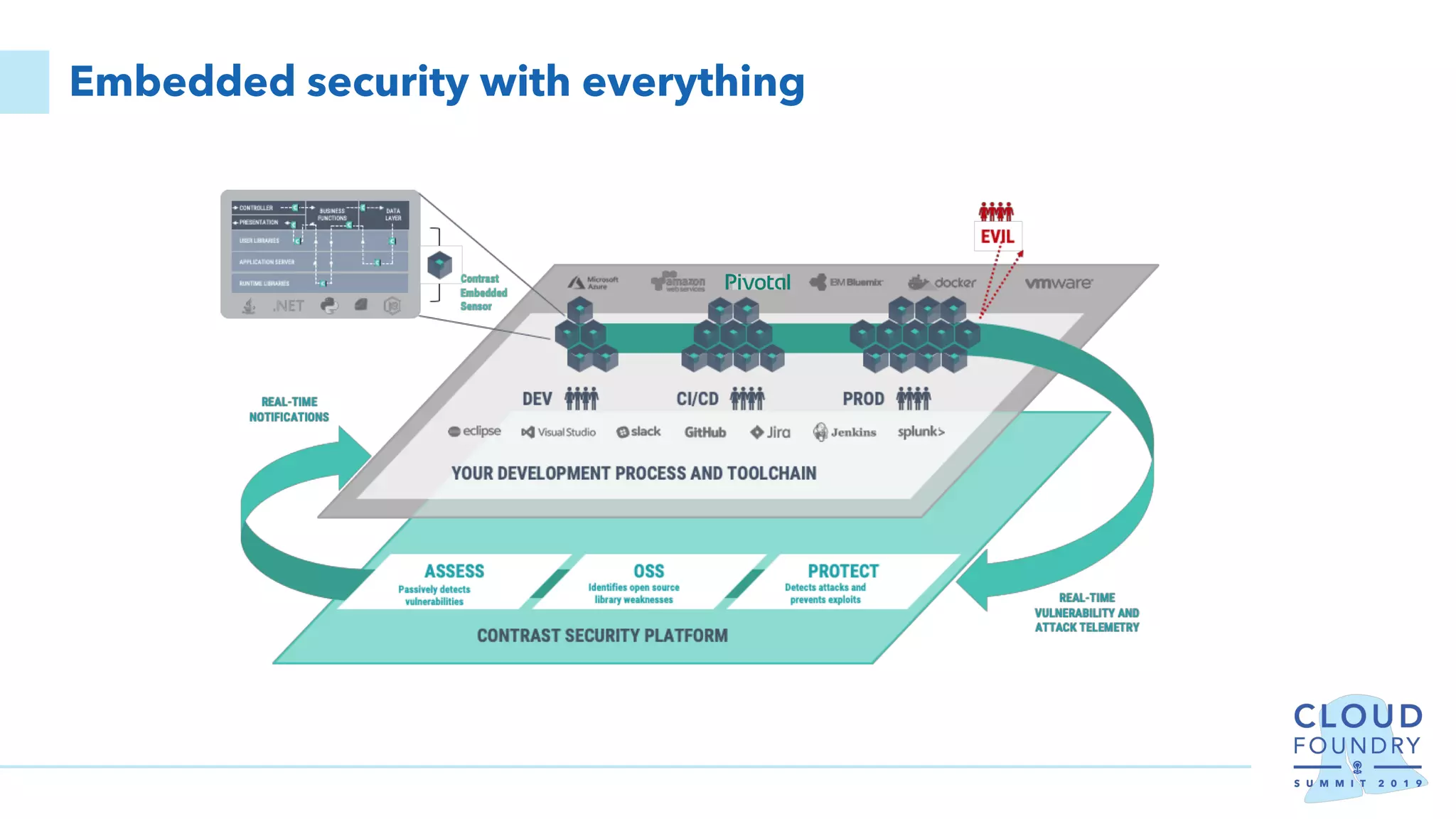
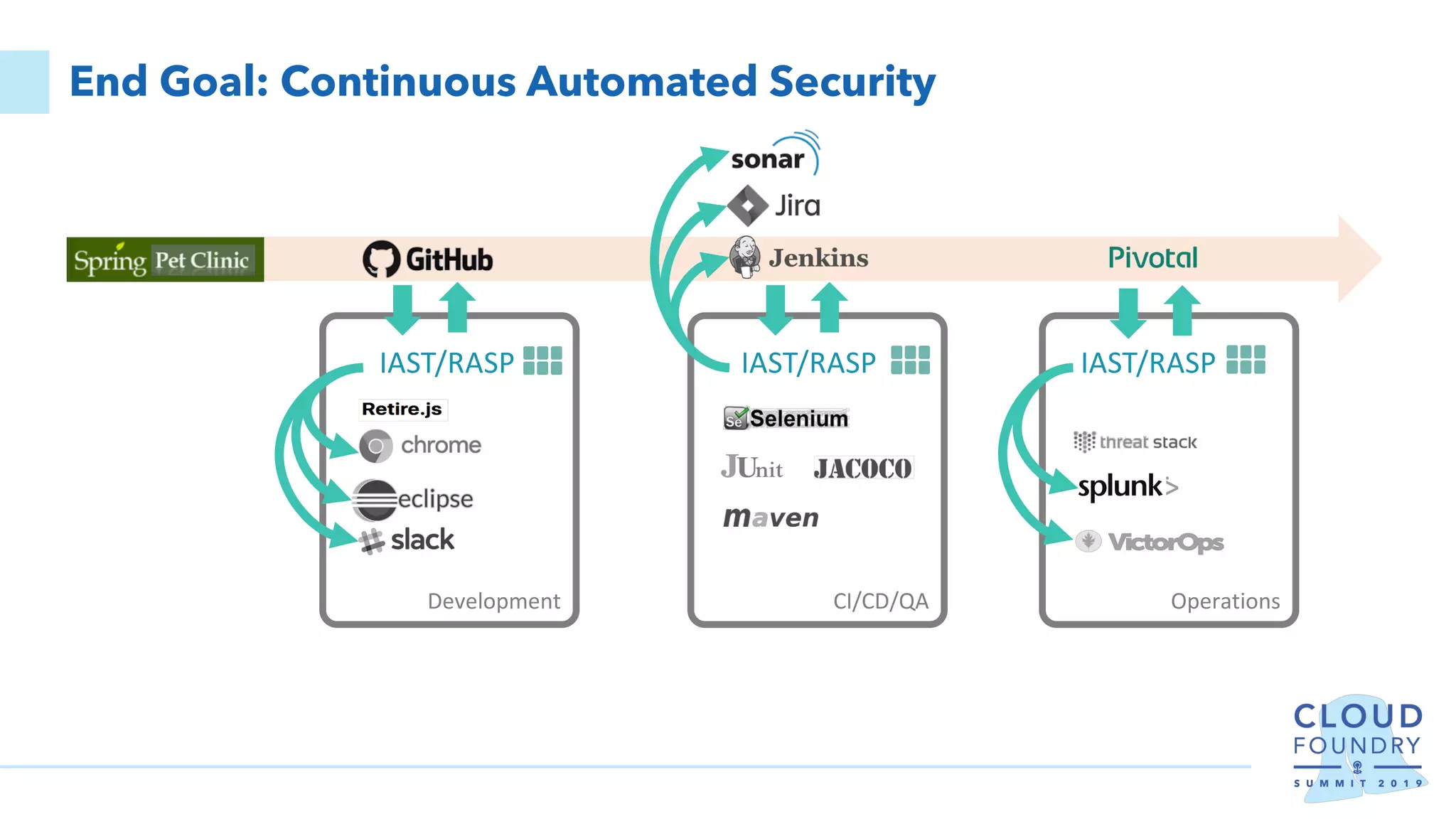
Erik Costlow discusses cloud migration strategies, application security risks, and methods to defend applications effectively, emphasizing the importance of built-in security within software. He highlights the six R's of migration and the significance of embedding security in the runtime of applications. Costlow also outlines automated tools that can enhance security throughout the development process, aiming for continuous compliance and rapid response to vulnerabilities.