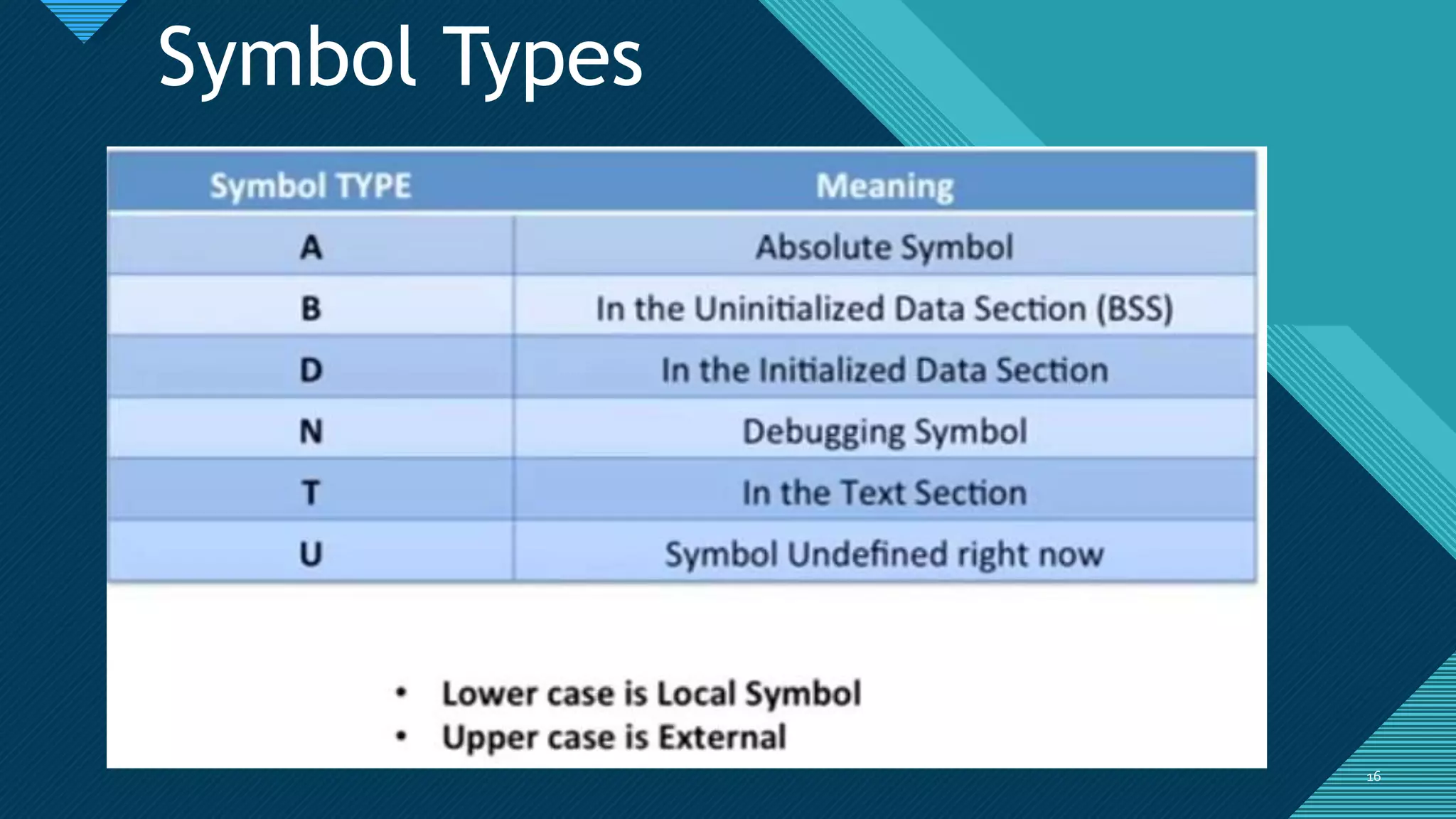
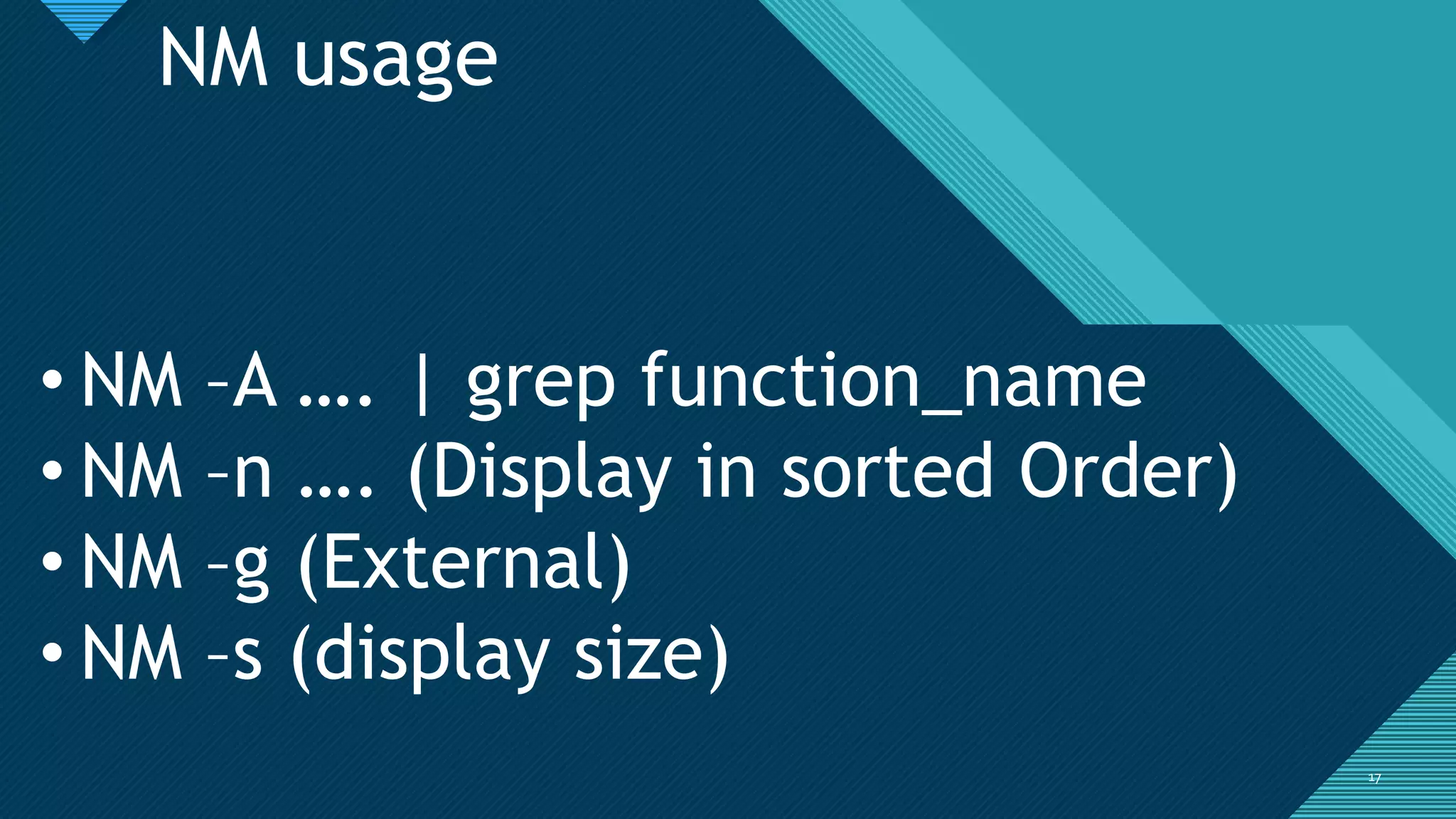
The document provides an overview of debugging using gdb, covering concepts from basic to advanced usage across multiple platforms. It explains debugging symbols, how to compile programs with debug symbols, utilize tools like strace, and set breakpoints during execution. The content is aimed at enhancing the understanding of program analysis and reverse engineering techniques.



![Click to edit Master title style
2929
Convenience Variables
• You can create variables in GDB to hold data
• Set $i = 10
• Set $dyn = (char *)malloc(10)
• $demo=“show”
• Set argv[1] = $demo
• Call Function(args_list)
• Call strlen(“show”)
• ….. Anything and everything which is linked](https://image.slidesharecdn.com/reversingwithgdb-190118174431/75/Reversing-with-gdb-29-2048.jpg)