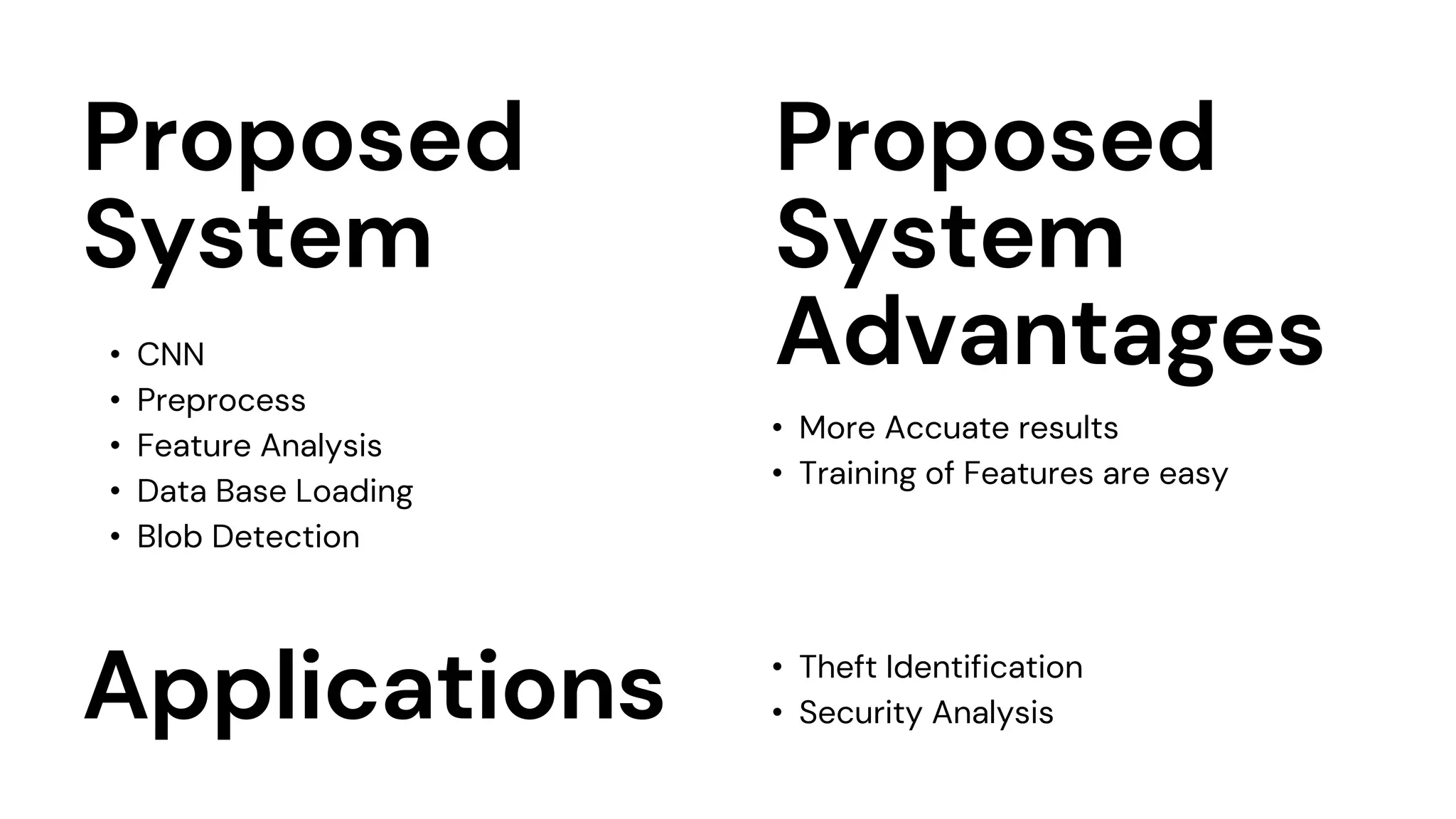
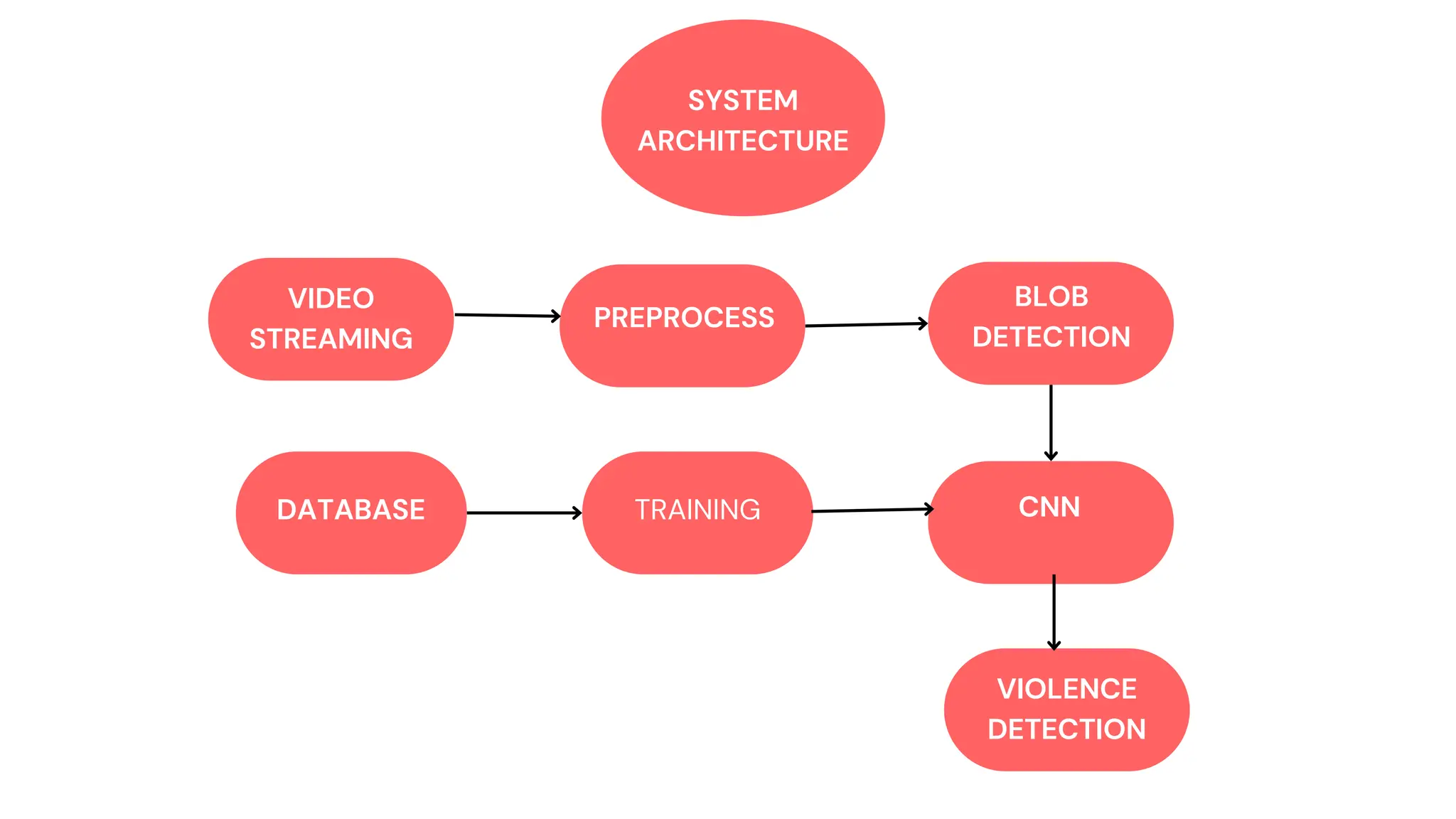
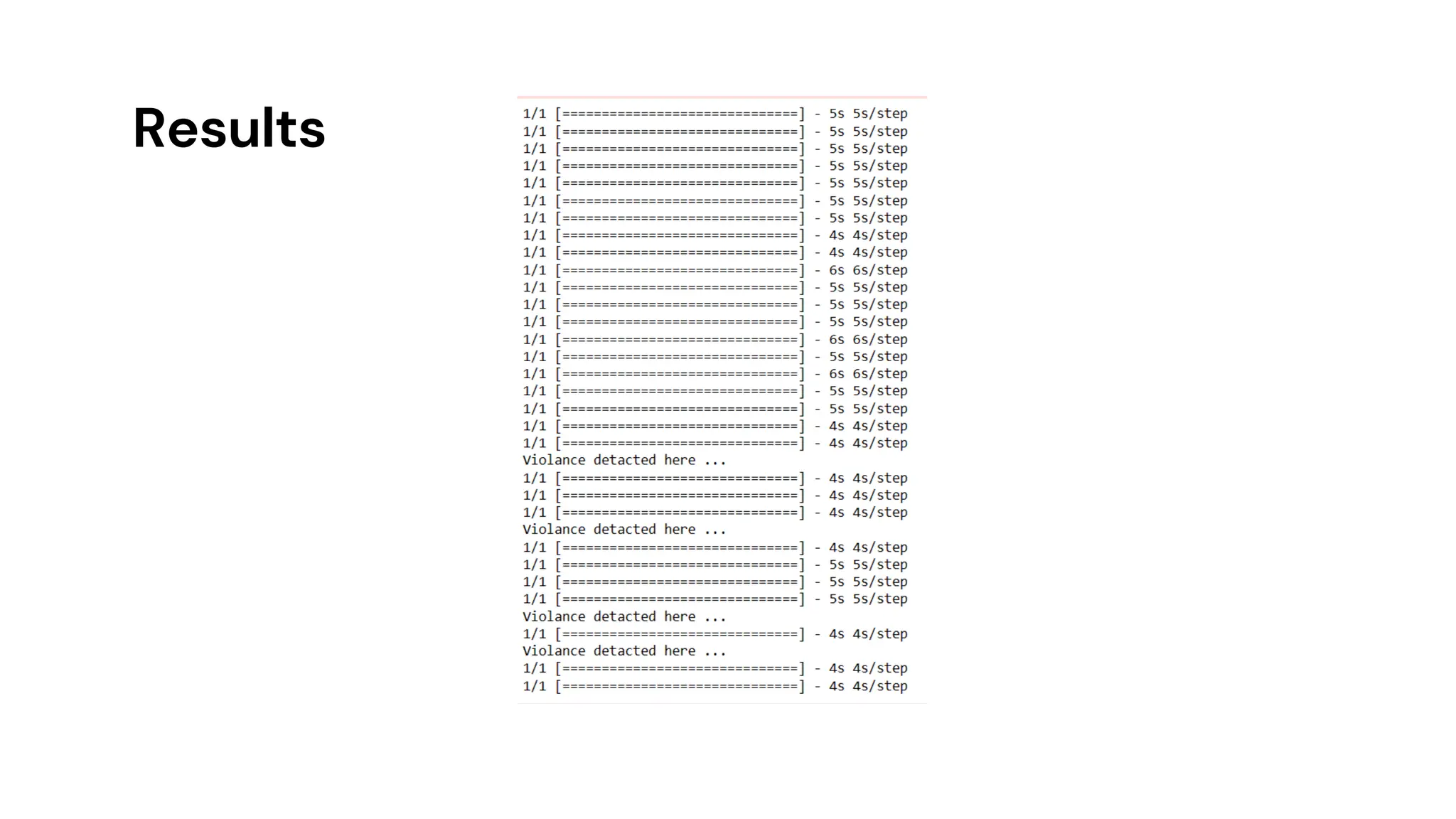
The document describes a real-time video-based violence detection system using a convolutional neural network (CNN) to analyze video footage for signs of violent behavior in public areas. The proposed system aims to improve detection accuracy and assist authorities in monitoring violent incidents, addressing the challenges faced by security personnel in identifying perpetrators. By training on the UCF Crime Anomaly Dataset, the system demonstrates effectiveness in detecting and analyzing violent events, contributing to public safety.

![References
[1] E. B. Nievas, O. D. Suarez, G. B. Garc´ıa, and R. Sukthankar, “Violence detection in video using computer vision
techniques,” in the International conference on Computer analysis of images and patterns. Springer, 2011, pp. 332–
339.
[2] C. Ding, S. Fan, M. Zhu, W. Feng, and B. Jia, “Violence detection in video by using 3d convolutional neural
networks,” in International Symposium on Visual Computing. Springer,2014, pp. 551–558.
[3] Z. Dong, J. Qin, and Y. Wang, “Multi-stream deep networks for person to person violence detection in videos,” in
Chinese Conference on Pattern Recognition. Springer, 2016, pp. 517– 531.
[4] Sudhakaran and O. Lanz, “Learning to detect violent videos using convolutional long short?term memory,”
published in 2017 14th IEEE International Conference on Advanced Video andSignal Based Surveillance (AVSS). IEEE,
2017, pp. 1–6.
[5] Hanson, K. Pnvr, S. Krishnagopal, and L. Davis, “Bidirectional Convolutional LSTM forthe detection of violence in
videos,” in Proceedings of the European Conference on Computer Vision (ECCV), 2018, pp. 0–0. Dai.
[6] J. Li, X. Jiang, T. Sun, and K. Xu, “Efficient violence detection using 3d convolutional neural networks,” in 2019 16th
IEEE International Conference on Advanced Video and Signal Based Surveillance (AVSS). IEEE, 2019, pp. 1–8](https://image.slidesharecdn.com/real-timevideobasedviolencedetectionsysteminpublicareausingneuralnetwork-240625102331-397dcbeb/75/REAL-TIME-VIDEO-BASED-VIOLENCE-DETECTION-SYSTEM-IN-PUBLIC-AREA-USING-NEURAL-NETWORK-pptx-22-2048.jpg)