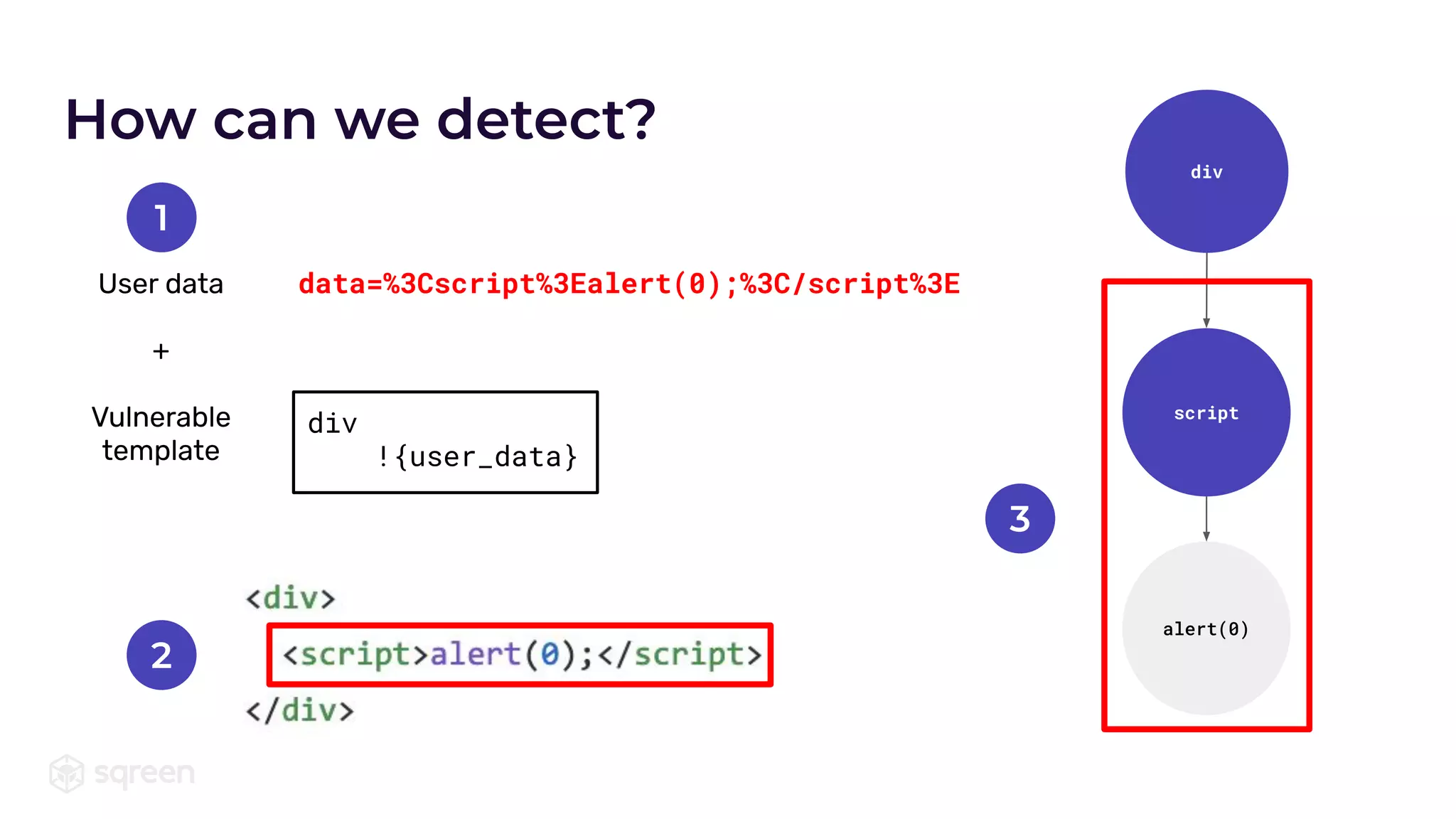
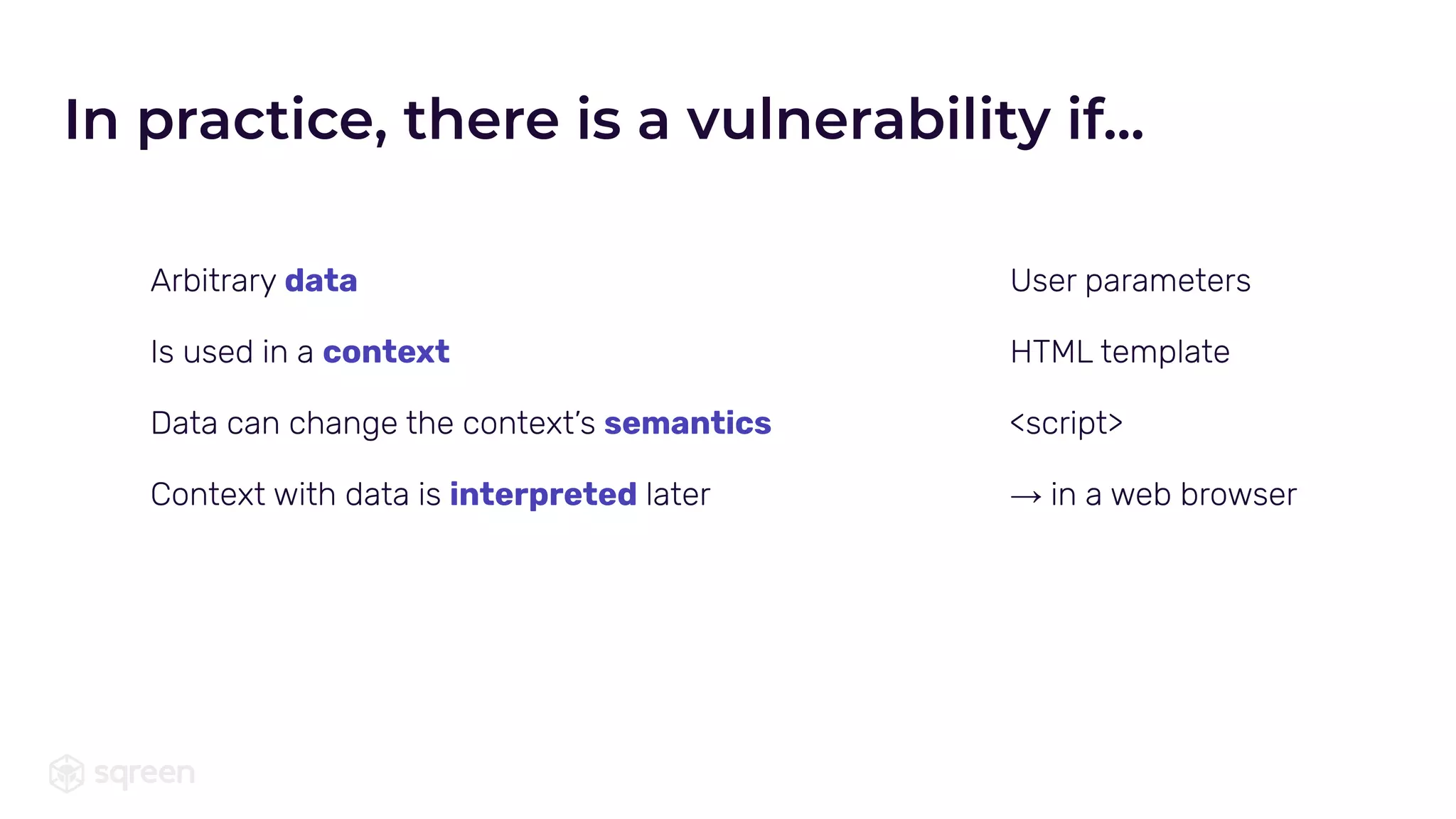
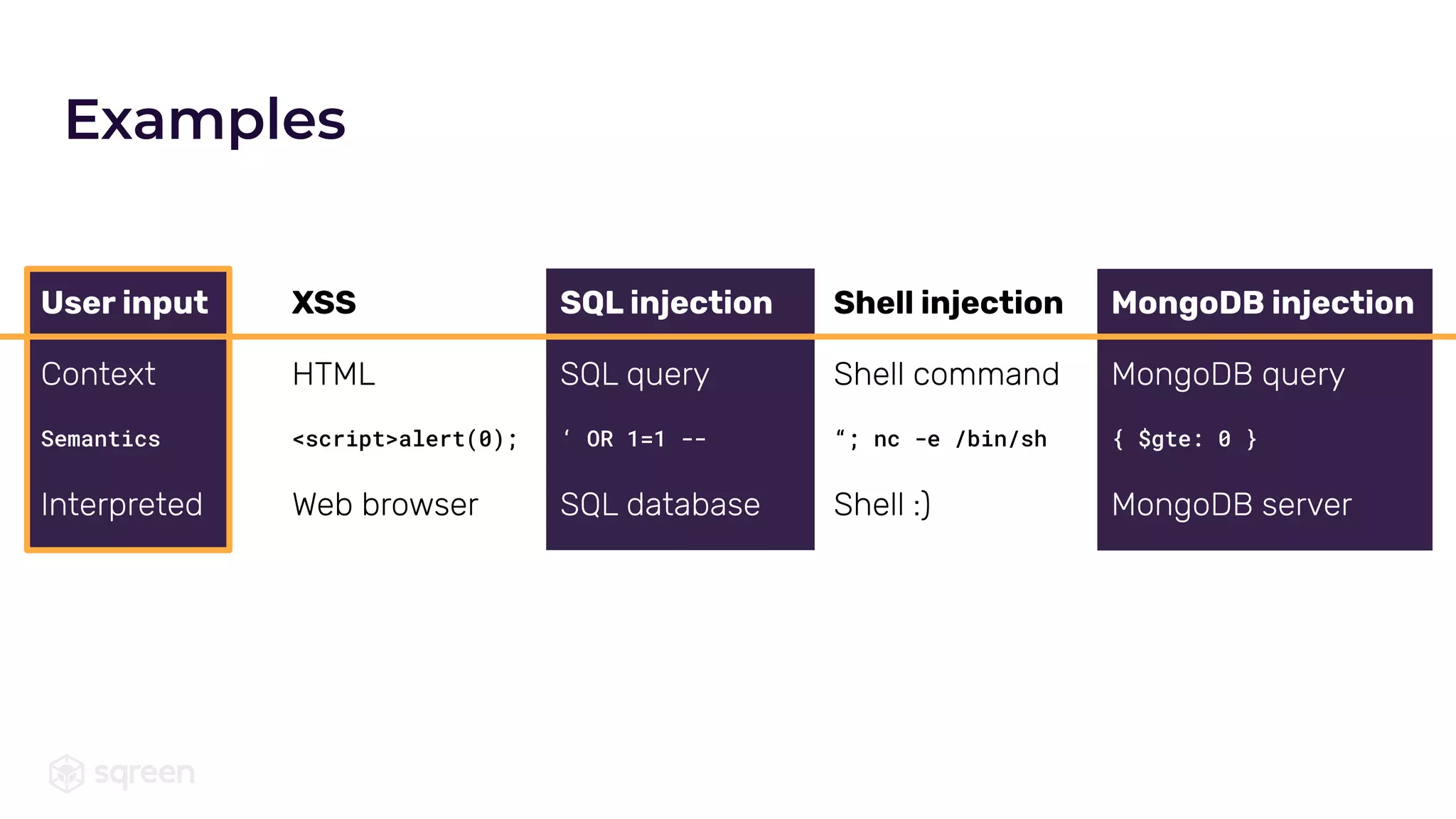
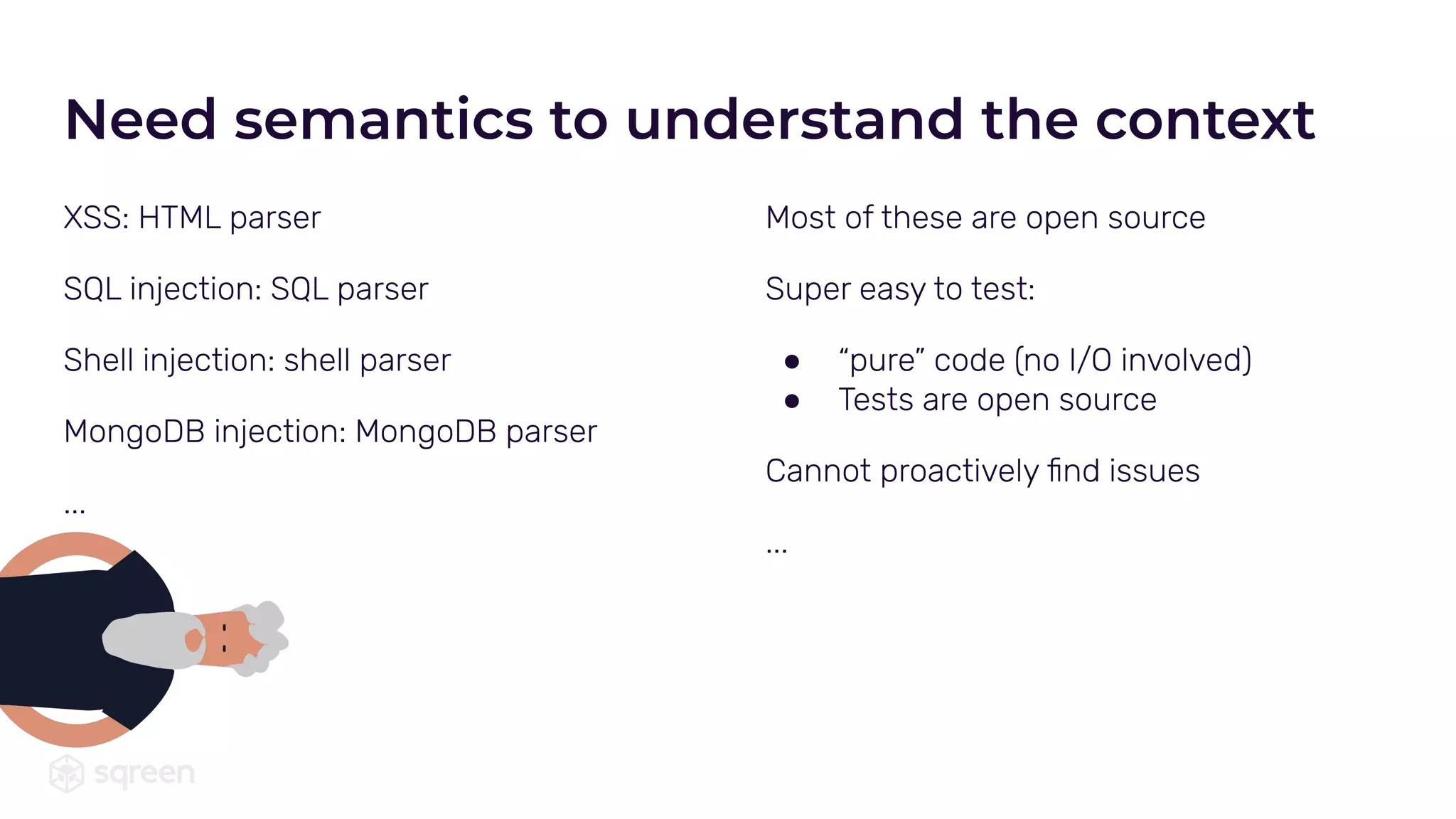
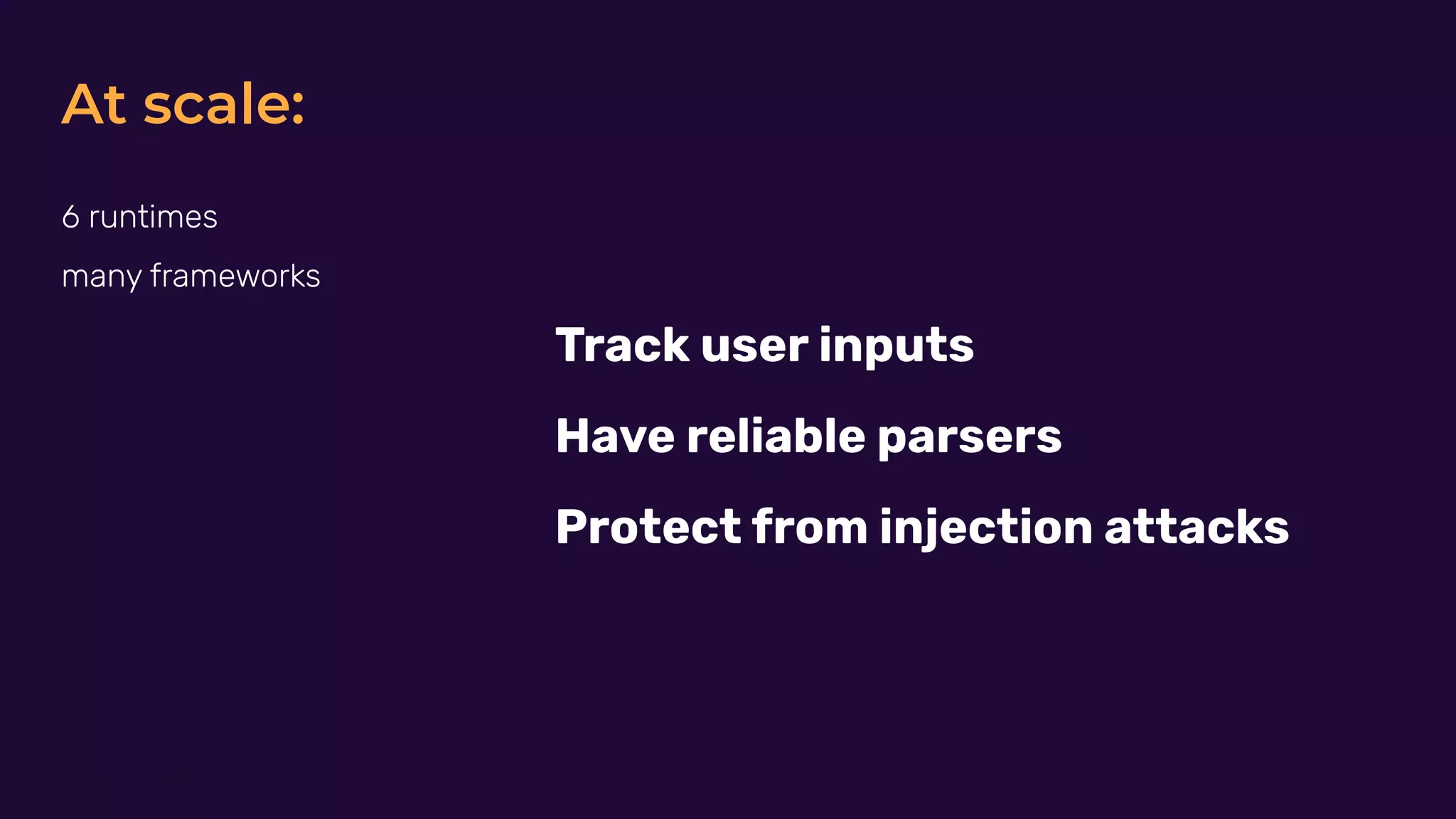
The document discusses the protection against injection vulnerabilities, focusing on XSS, SQL, and shell injections, which can change the semantics of contexts, allowing attackers to exploit them. It emphasizes the importance of context-aware detection methods over pattern-based approaches to effectively secure applications at scale. The content encourages testing and highlights job opportunities related to this field.
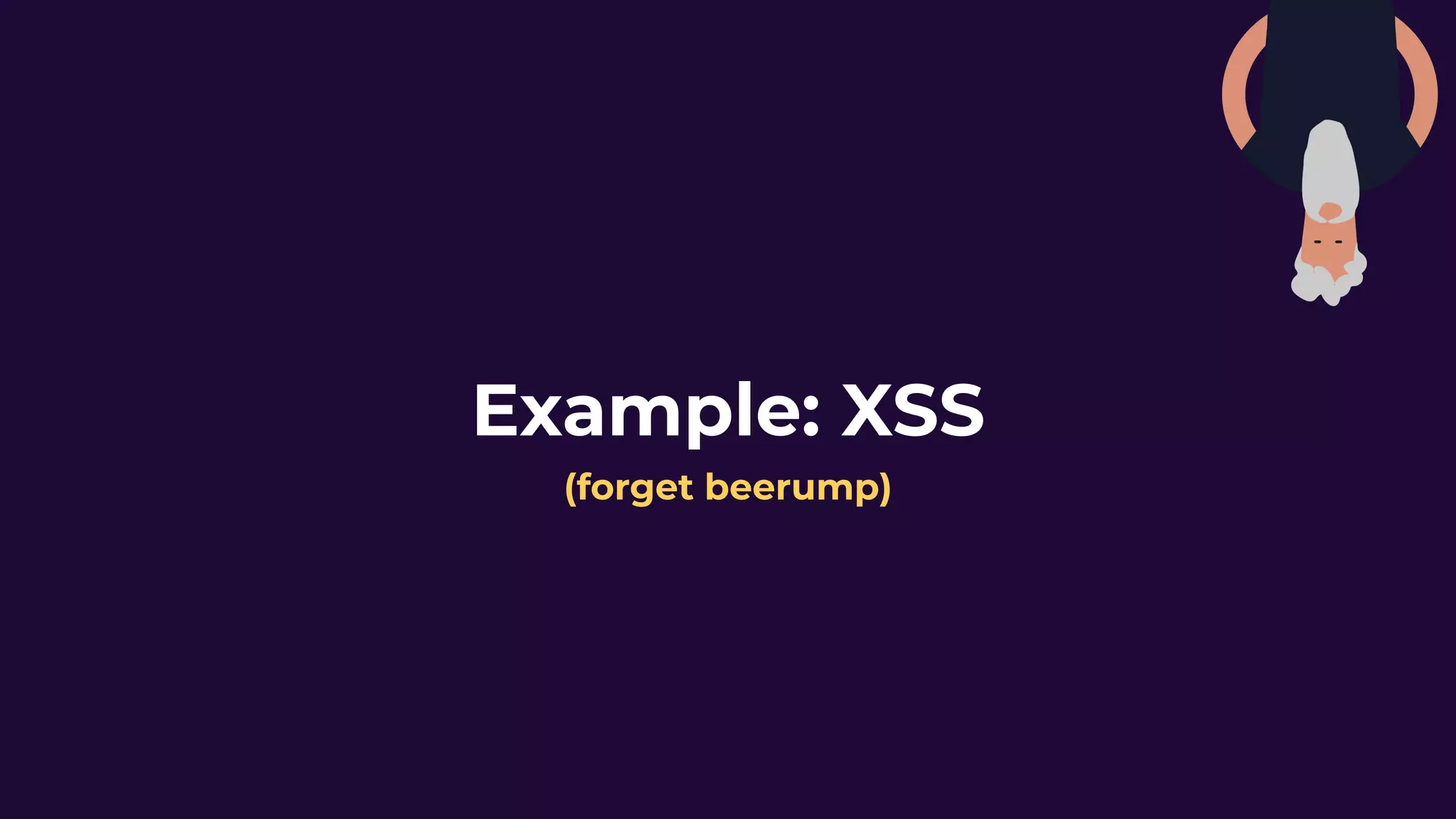
![XSS when: user parameter is not escaped
OK if param in: [a-z0-9]
✅ Cannot change HTML semantics
Potential exploit if param has: [<>”’]
❌ Can change HTML semantics
XSS (reflected)](https://image.slidesharecdn.com/protectingagainstinjectionsatscale-201215162955/75/Protecting-against-injections-at-scale-3-2048.jpg)