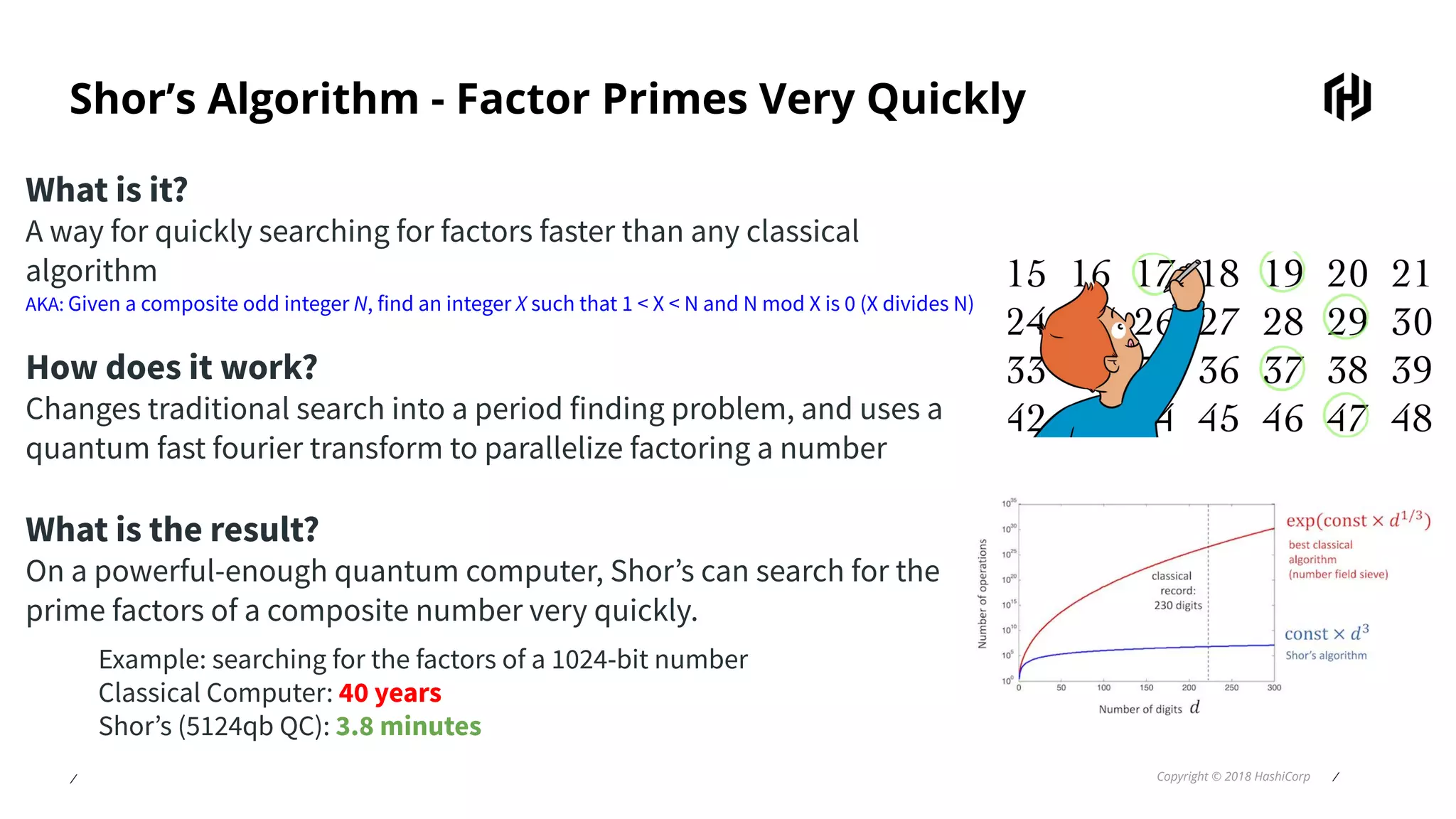
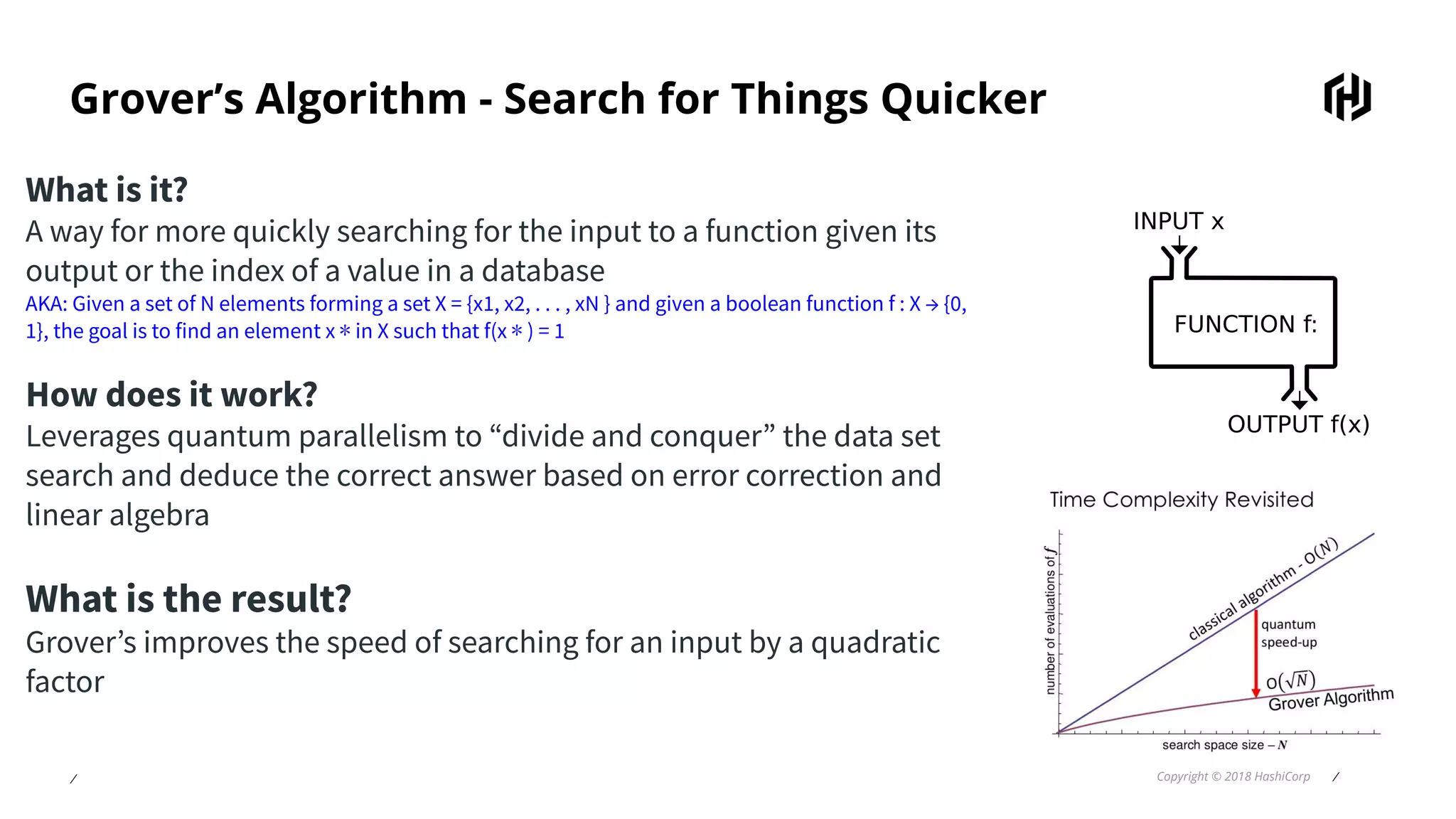
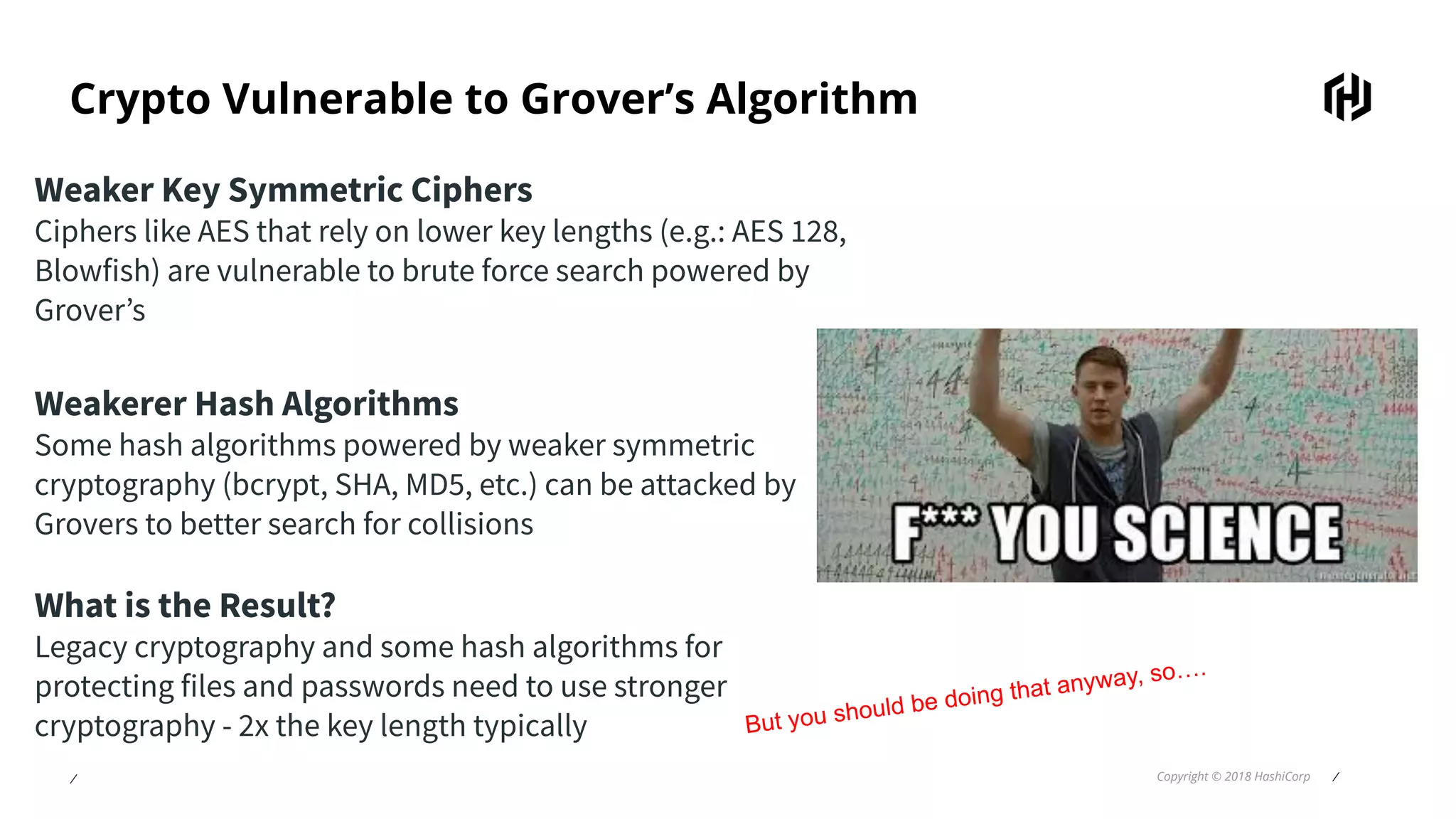
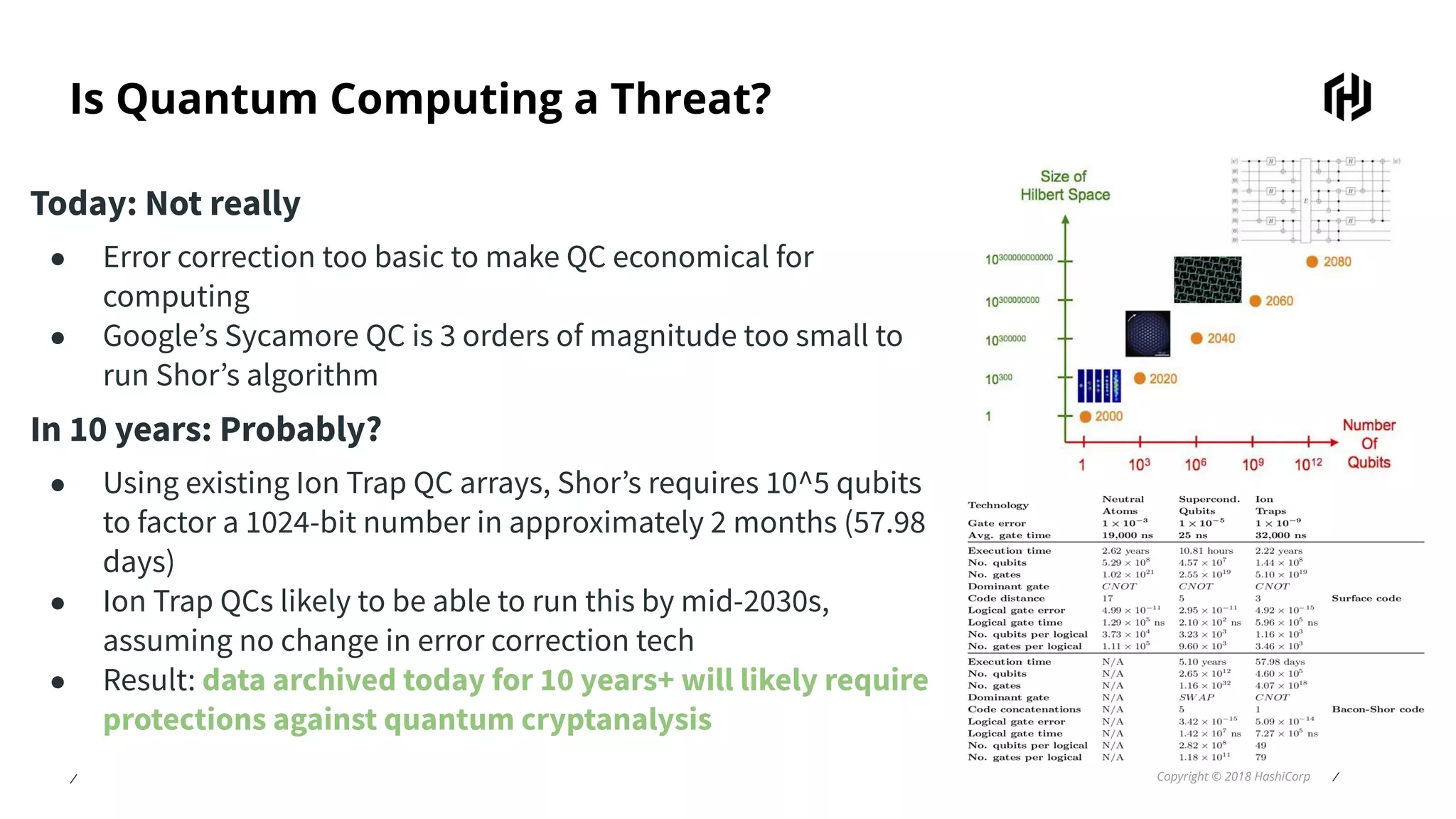
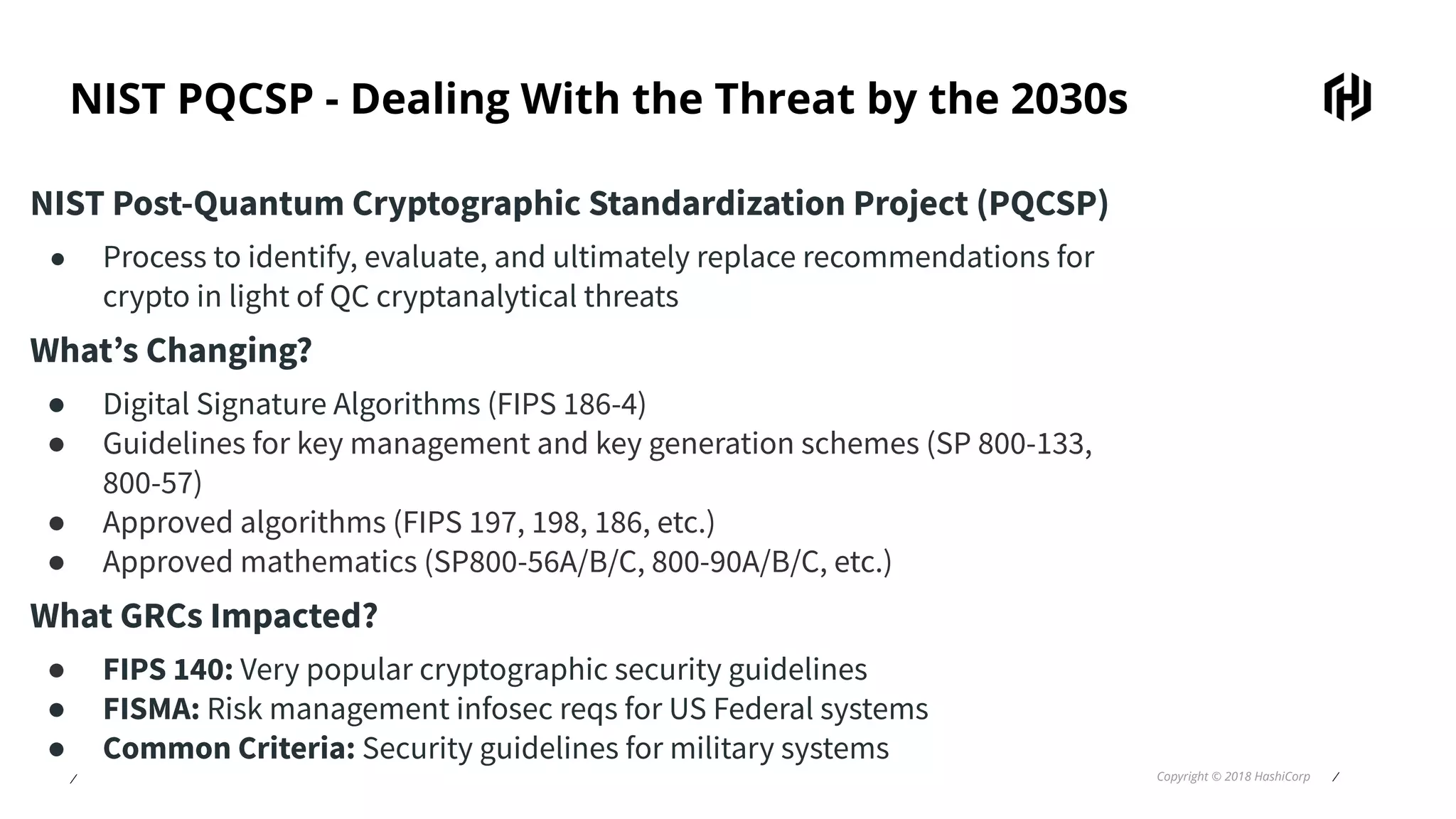
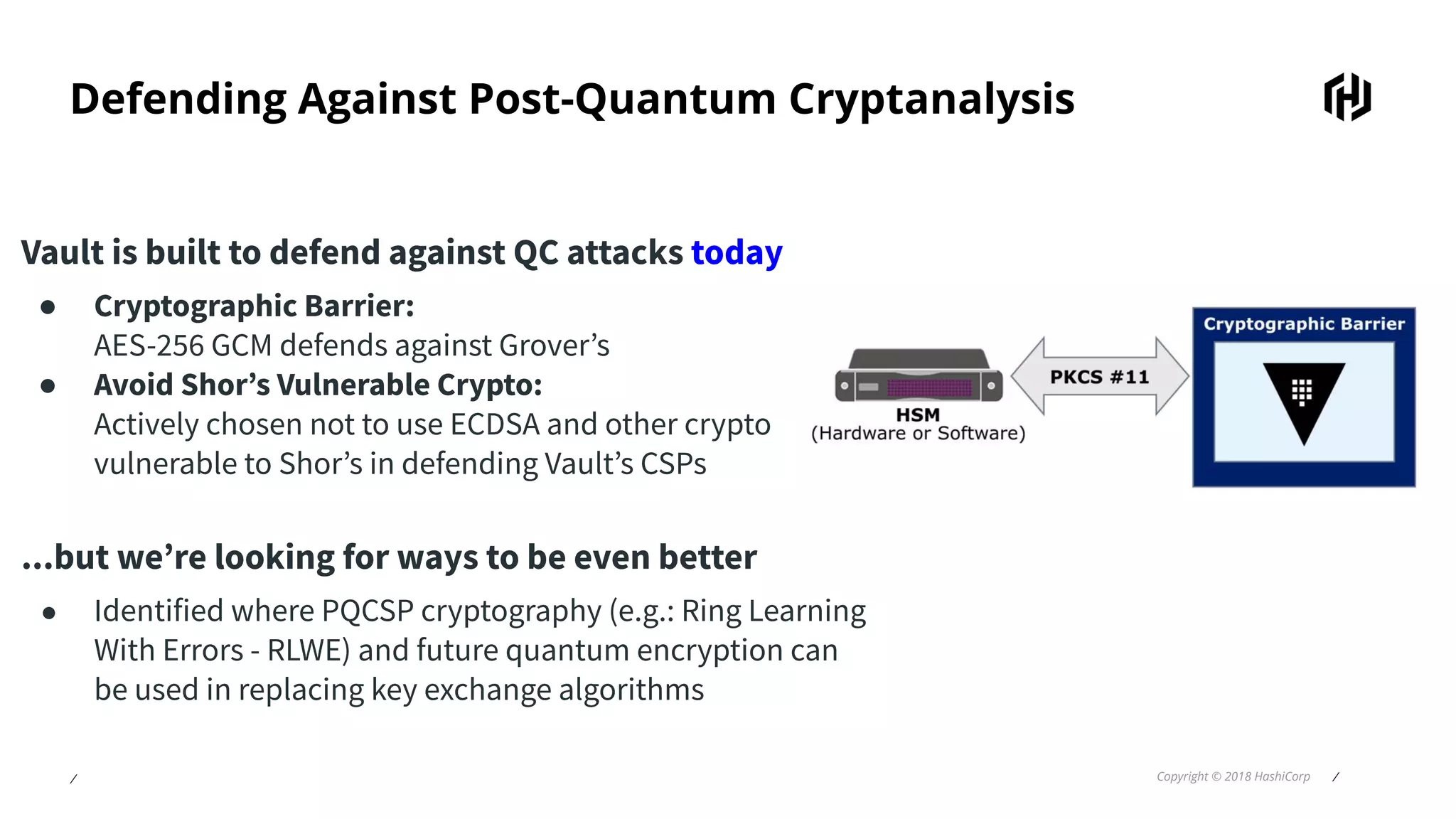
The document discusses the implications of quantum computing on cryptography, focusing on how quantum algorithms like Shor's and Grover's can threaten traditional encryption methods. While current quantum computers are not economically feasible for breaking encryption, the document emphasizes the need for preparations against potential future threats, especially for data archived beyond the 2030s. HashiCorp Vault is highlighted as utilizing post-quantum cryptographic techniques to enhance security against quantum attacks.