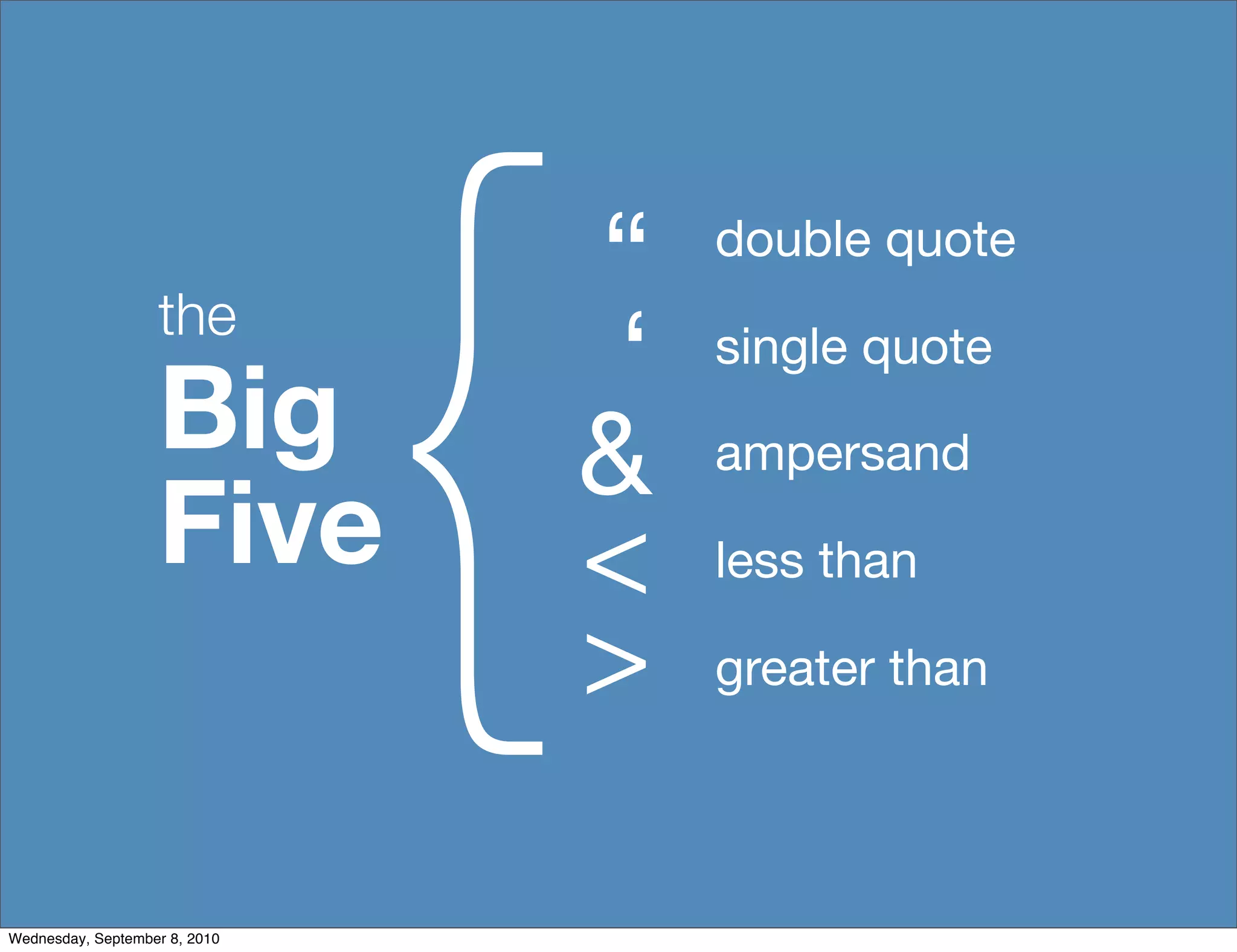
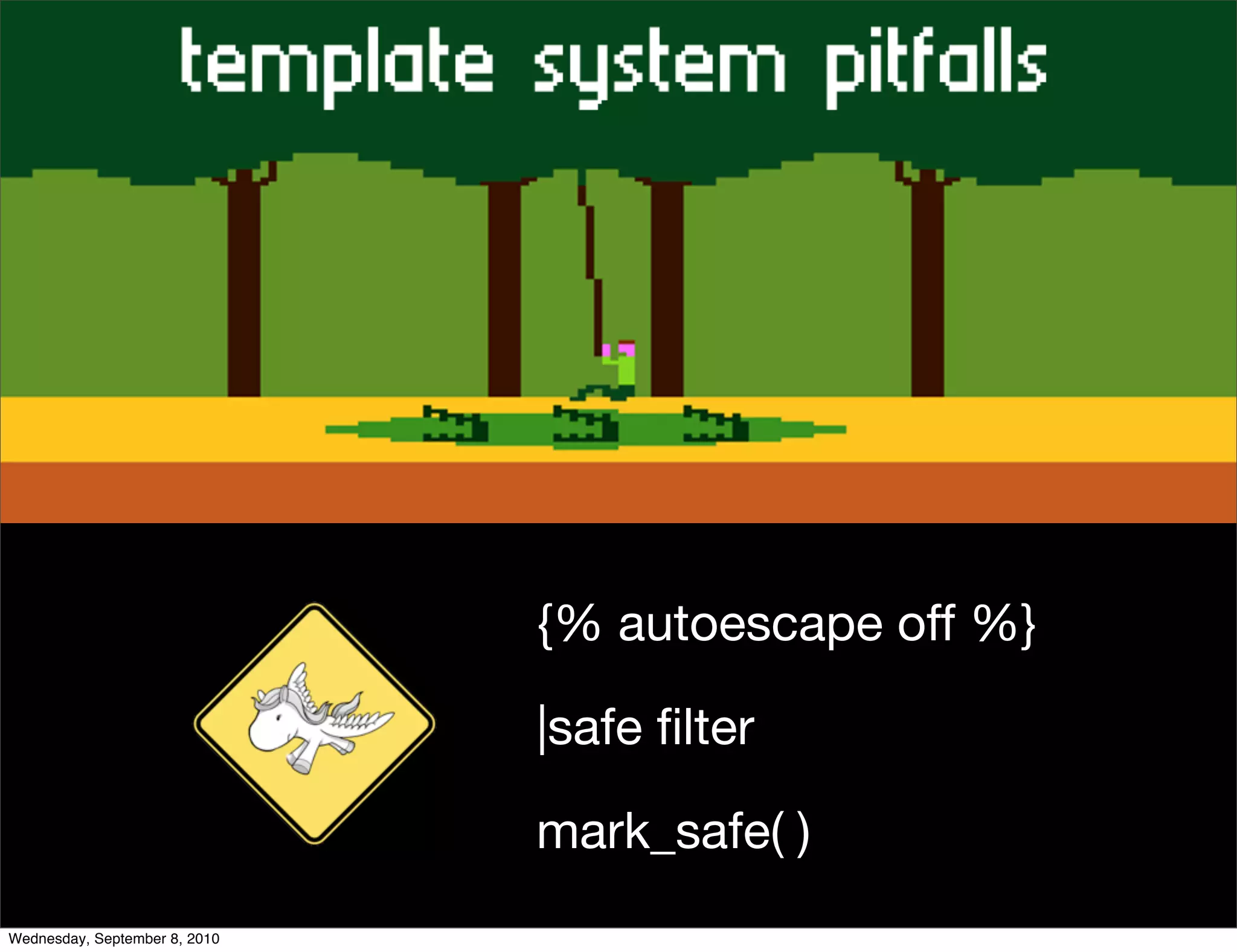
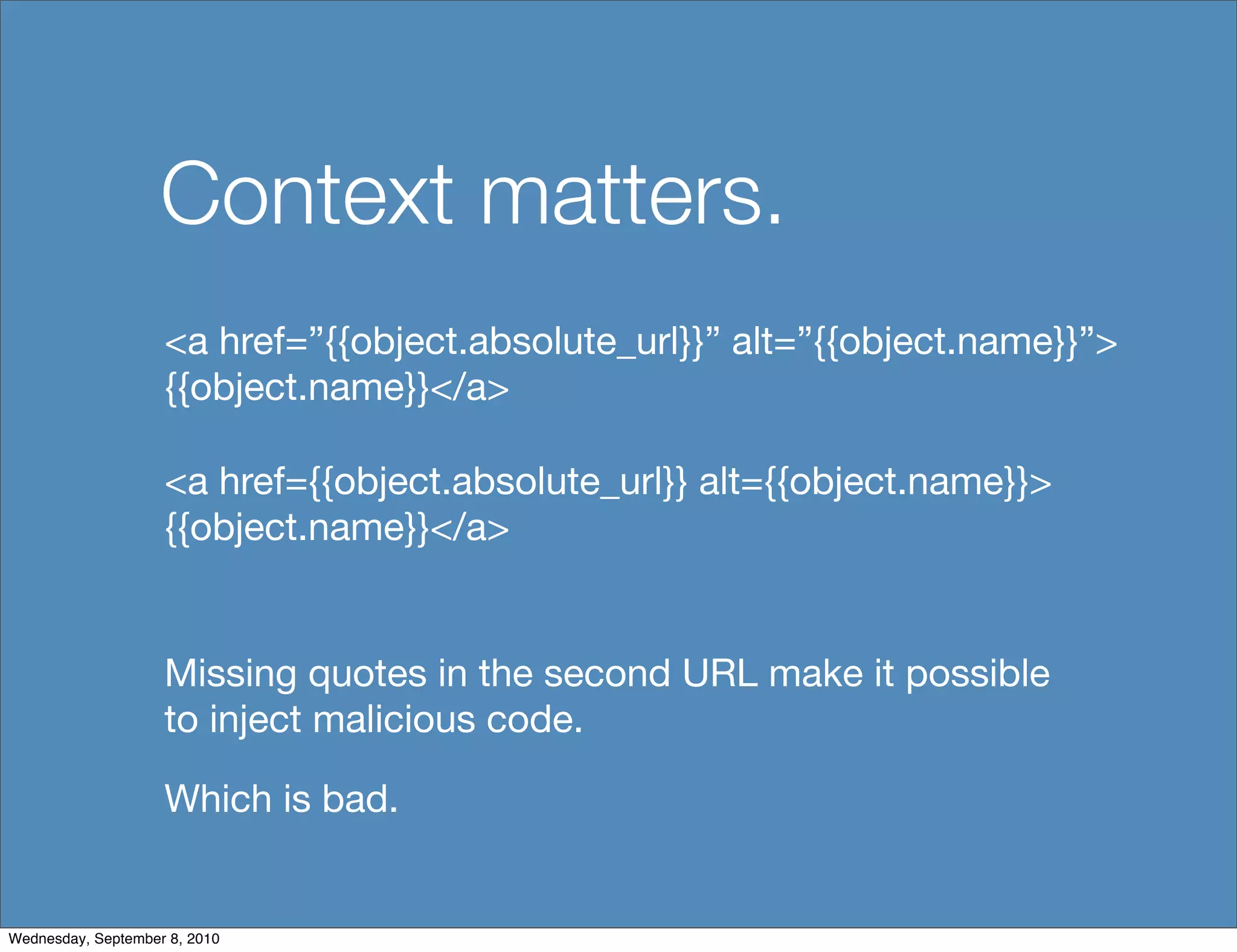
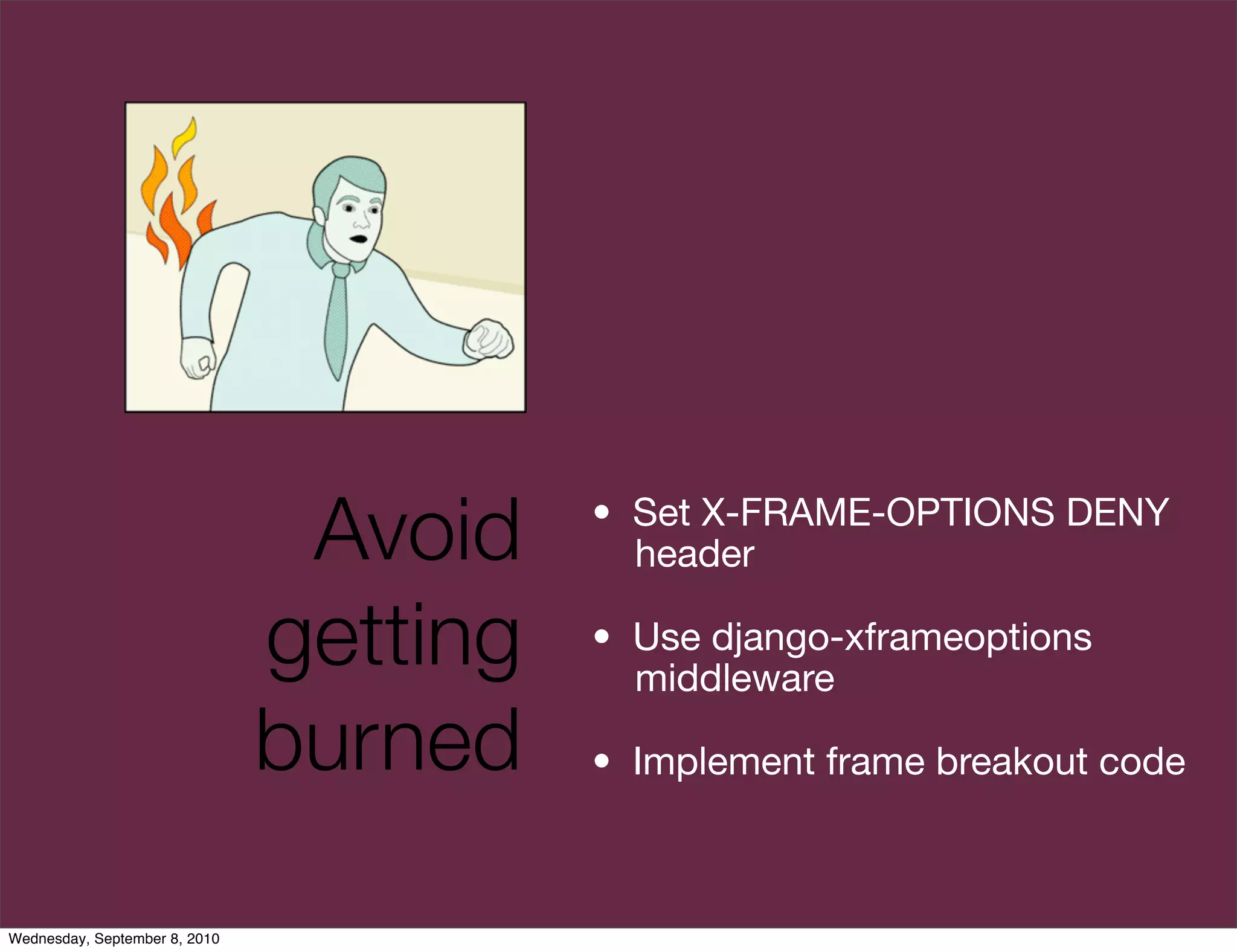
This document summarizes a presentation on Django web application security given by Adam Baldwin. The presentation covered common security failures in Django projects including cross-site scripting due to improper validation of user input in templates, file uploads that do not check extensions or store files in protected directories, direct access to objects without authorization checks, and other issues. Baldwin emphasized avoiding security problems by following best practices like input validation, using middleware to set security headers, and not allowing privileged operations with HTTP GET.





![Browser behavior
This works in IE8, without the “big five” and executes
without user interaction.
<style /><a href="[user provided data here]">click</a>
<style /><a href="}@import/**/data:text/css
%3Bbase64,Knt4OmV4cHJlc3Npb24oYWxlcnQoMSkpf
Q%3D%3D;">click</a>
Wednesday, September 8, 2010](https://image.slidesharecdn.com/ngenuitydjangocon2010ponypwning-100908154406-phpapp01/75/Pony-Pwning-Djangocon-2010-23-2048.jpg)

![Wuh-oh, kids.
[ REDACTED ]
Wednesday, September 8, 2010](https://image.slidesharecdn.com/ngenuitydjangocon2010ponypwning-100908154406-phpapp01/75/Pony-Pwning-Djangocon-2010-39-2048.jpg)