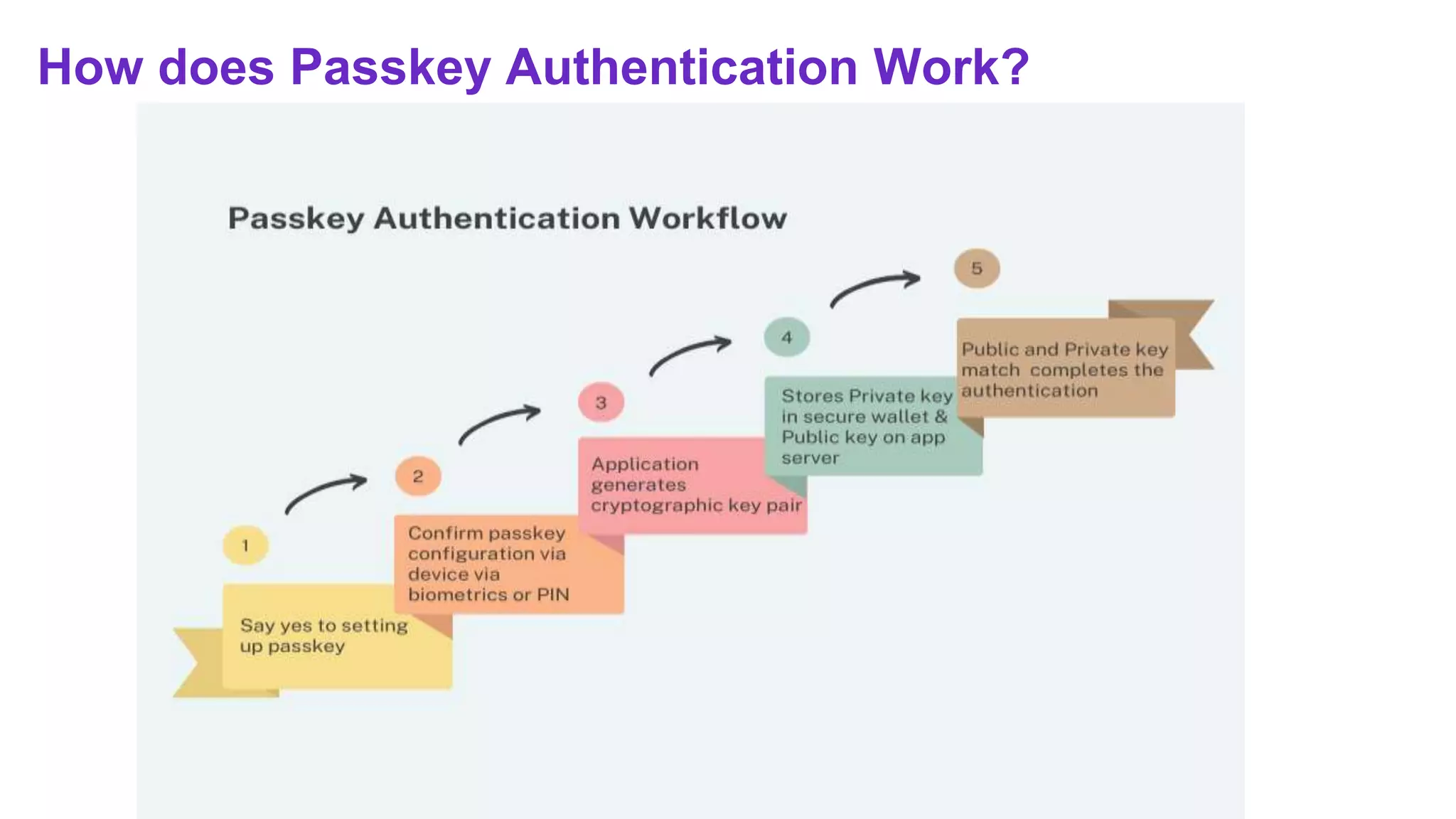
The document explains the concept of passkeys as a safer and more convenient alternative to traditional passwords, utilizing public-key cryptography for authentication. It details how passkeys work, their advantages over passwords, recovery processes, and various use cases, including login options, reauthentication, possession-based authentication, and cross-platform interoperability. Additionally, it highlights the transition towards passwordless authentication and promotes MojoAuth as a solution for implementing secure, password-free systems.