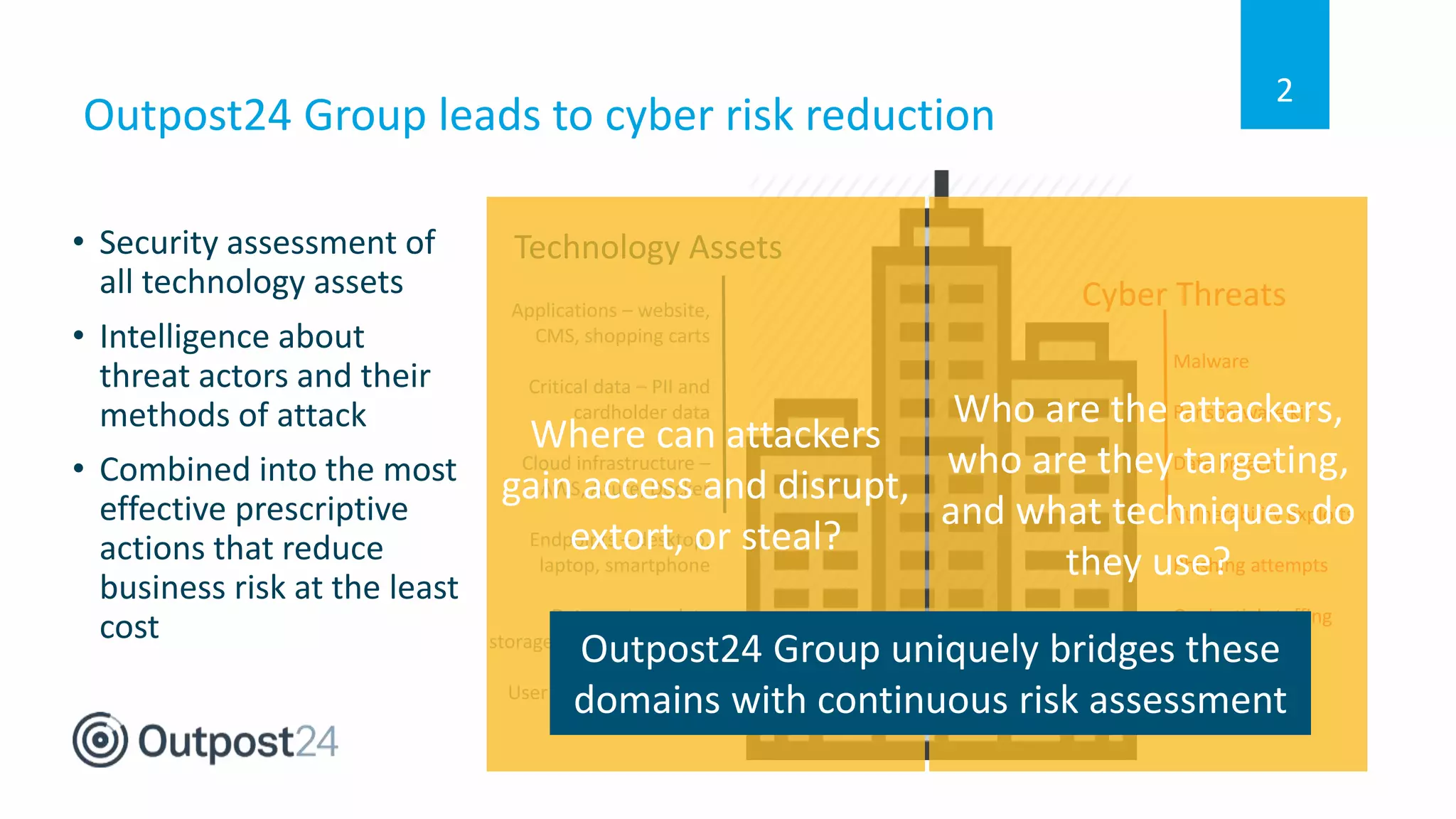
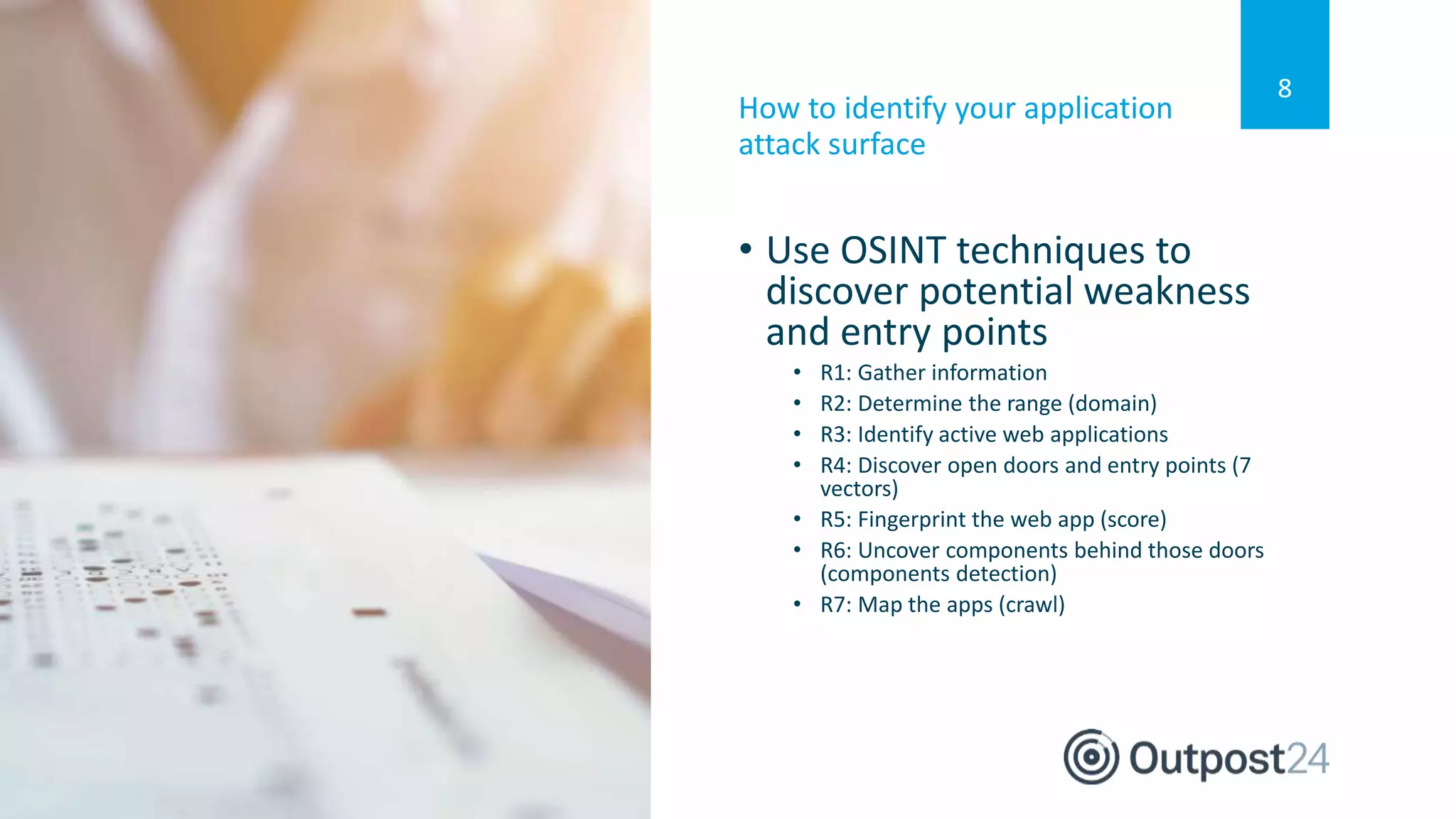
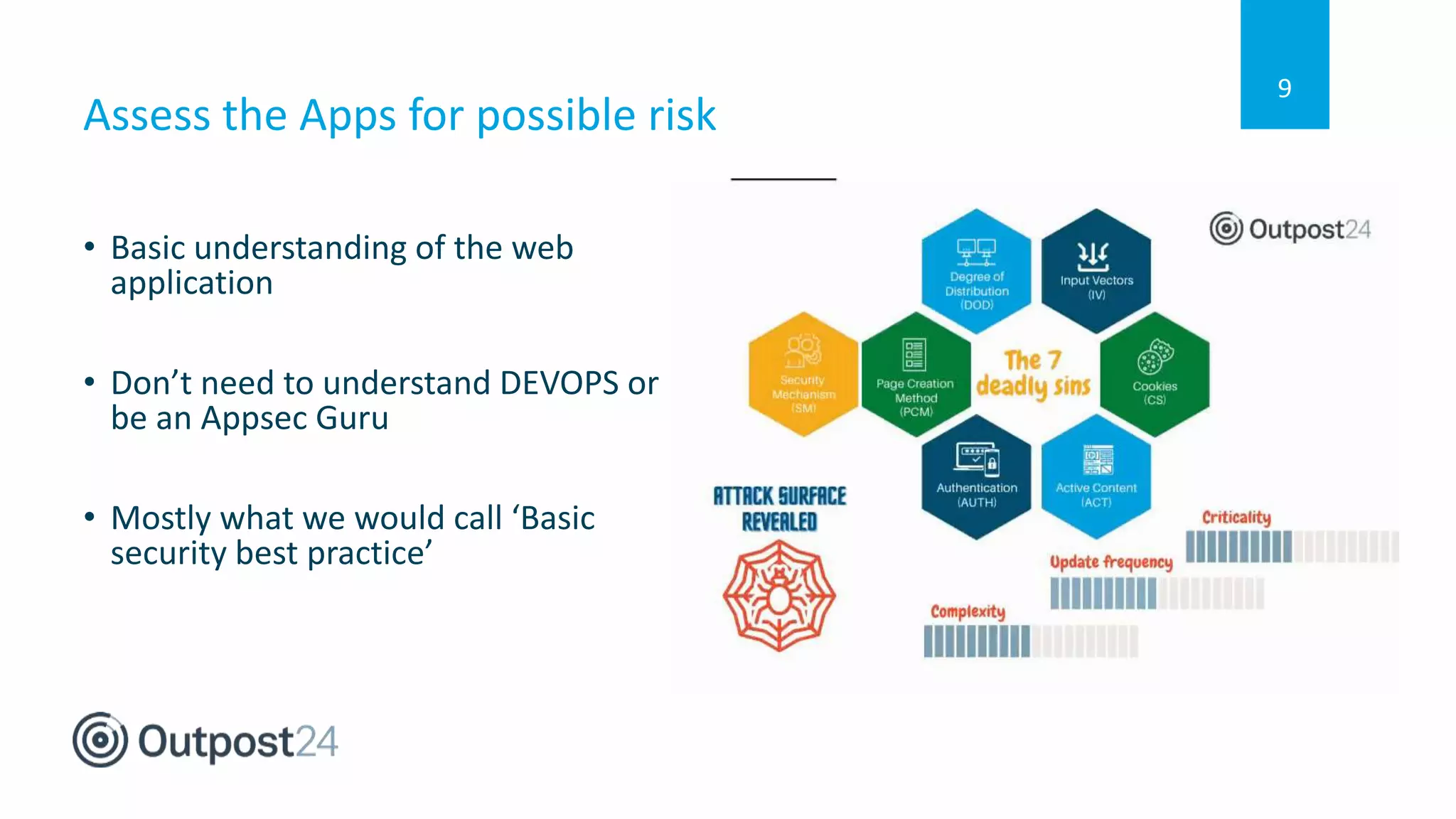
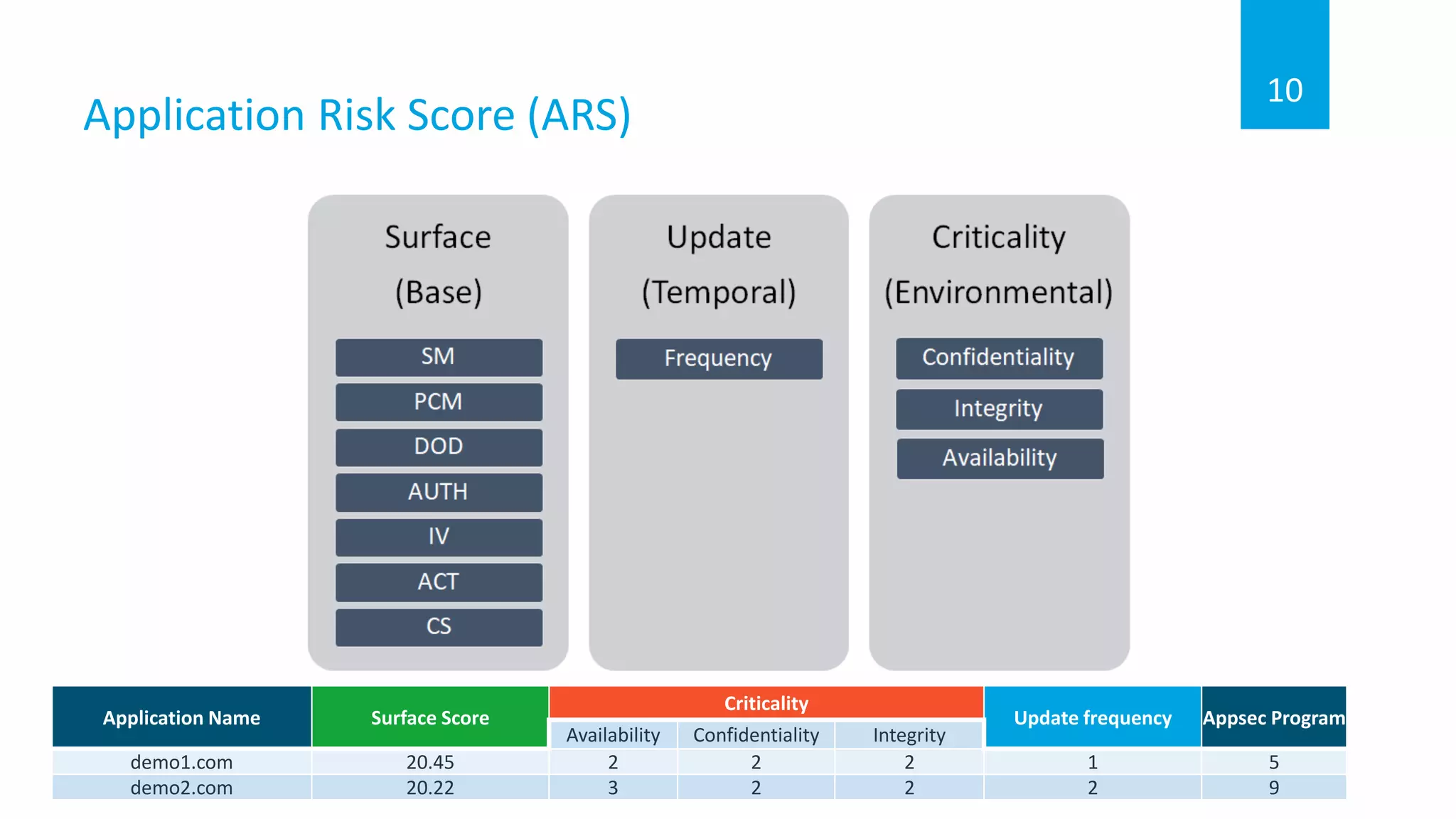
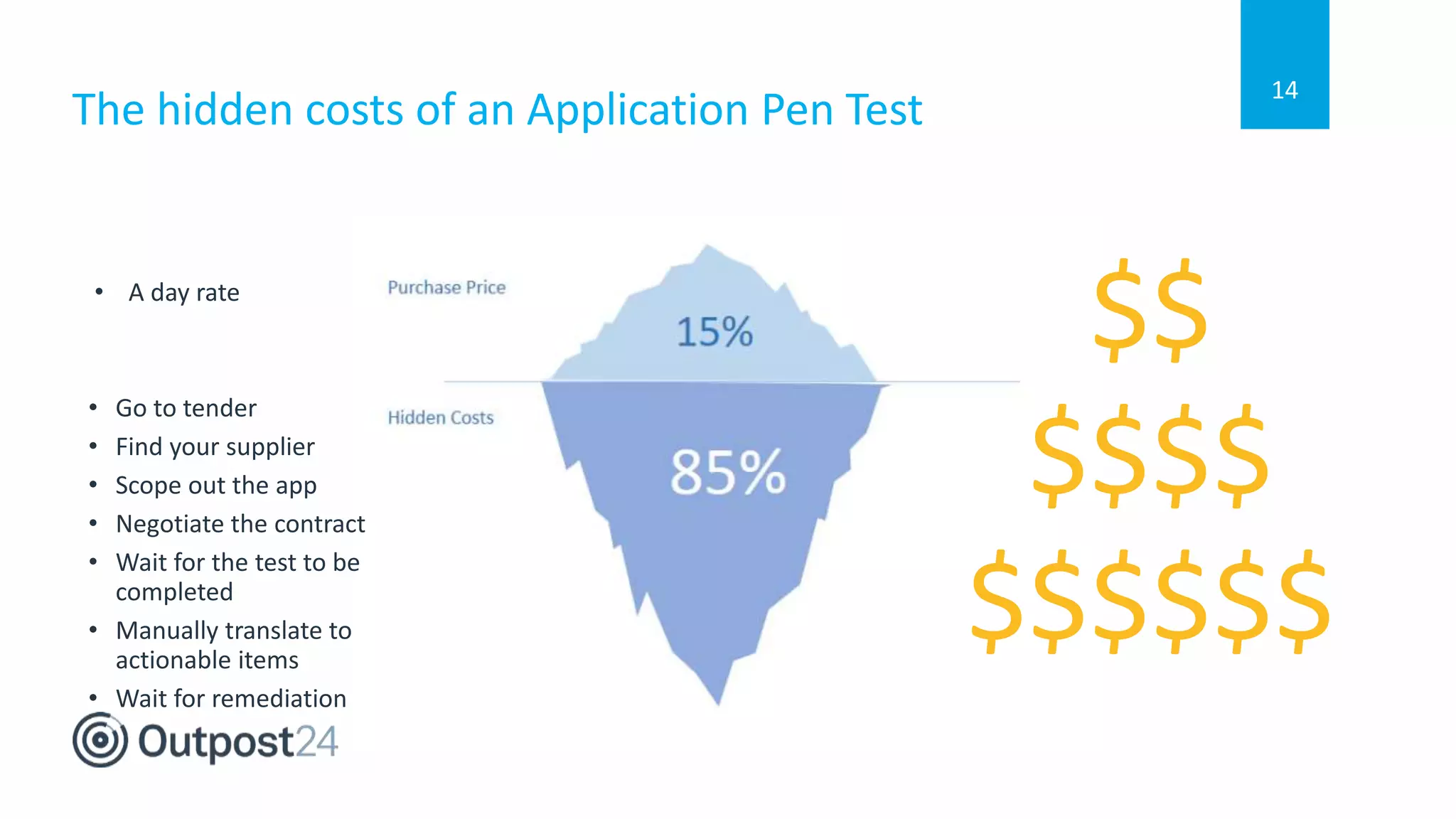
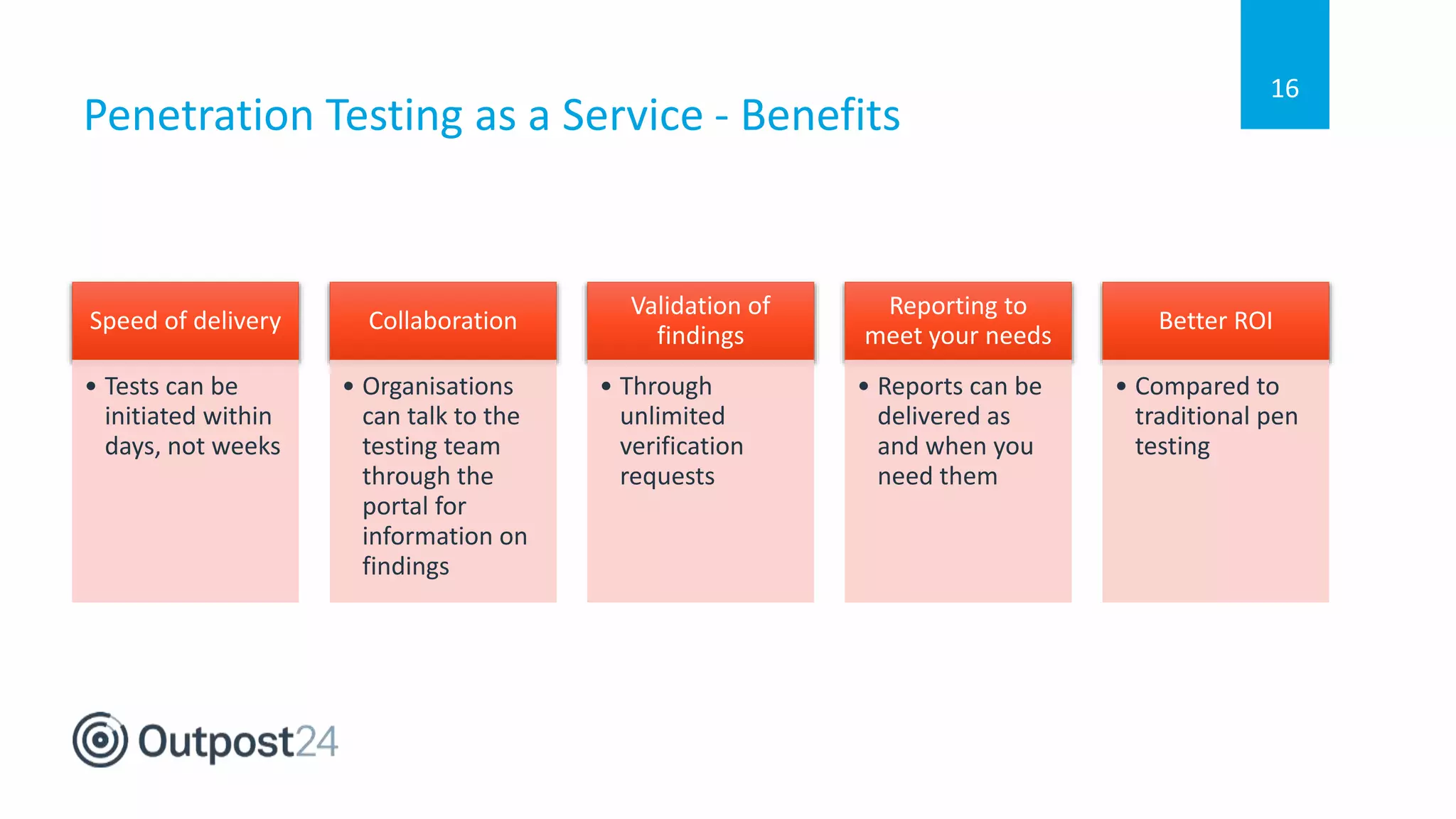
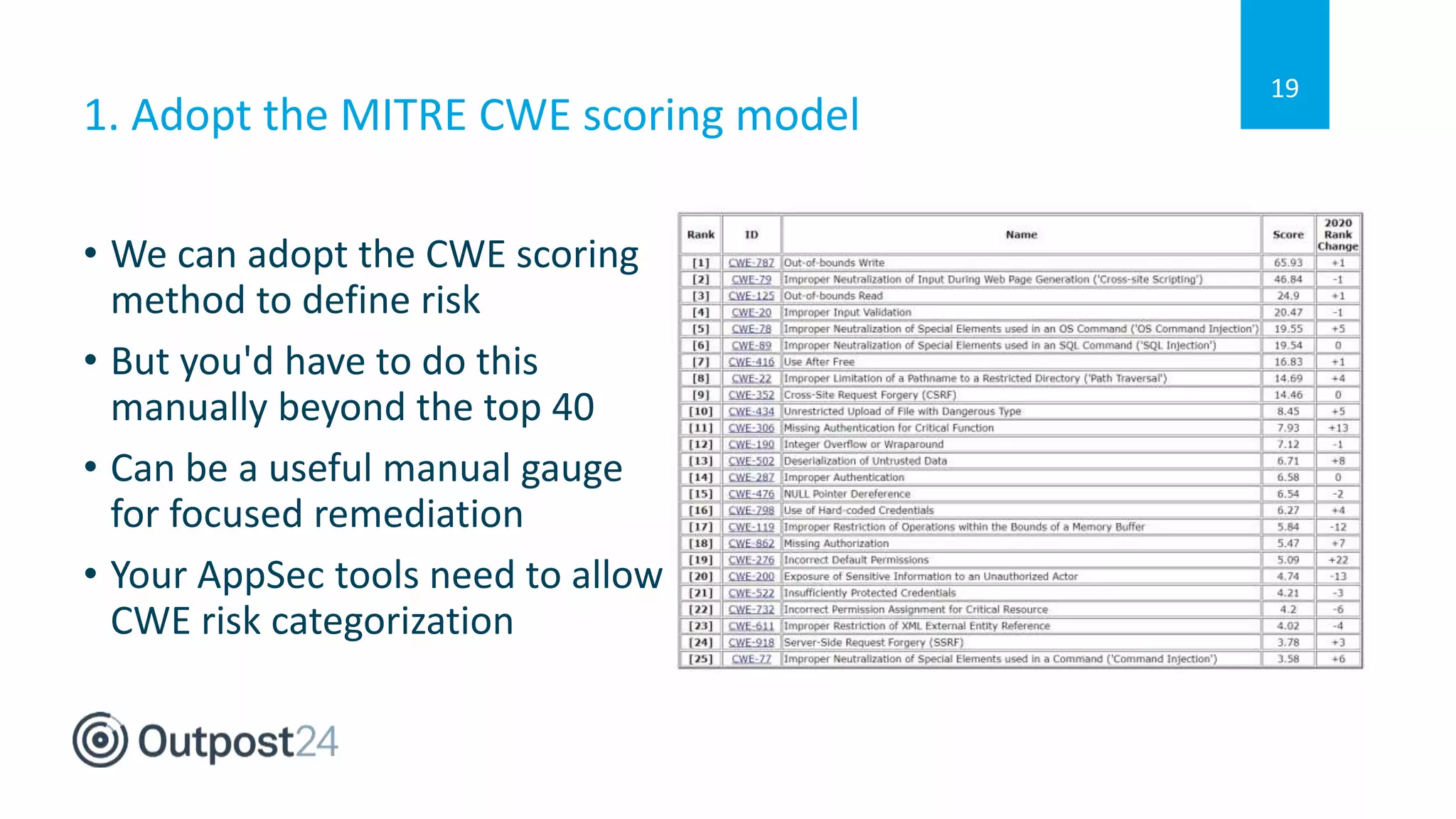
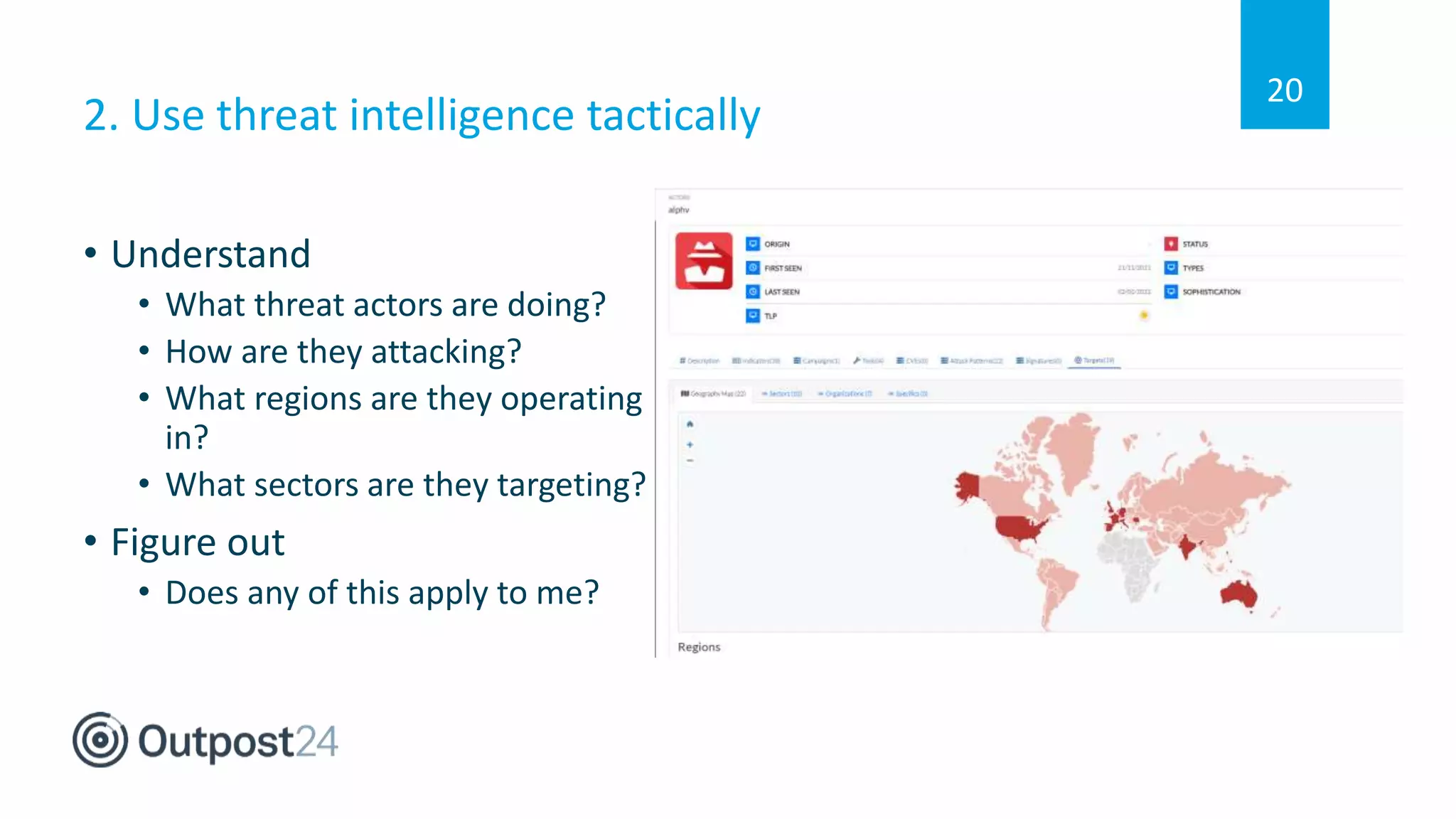
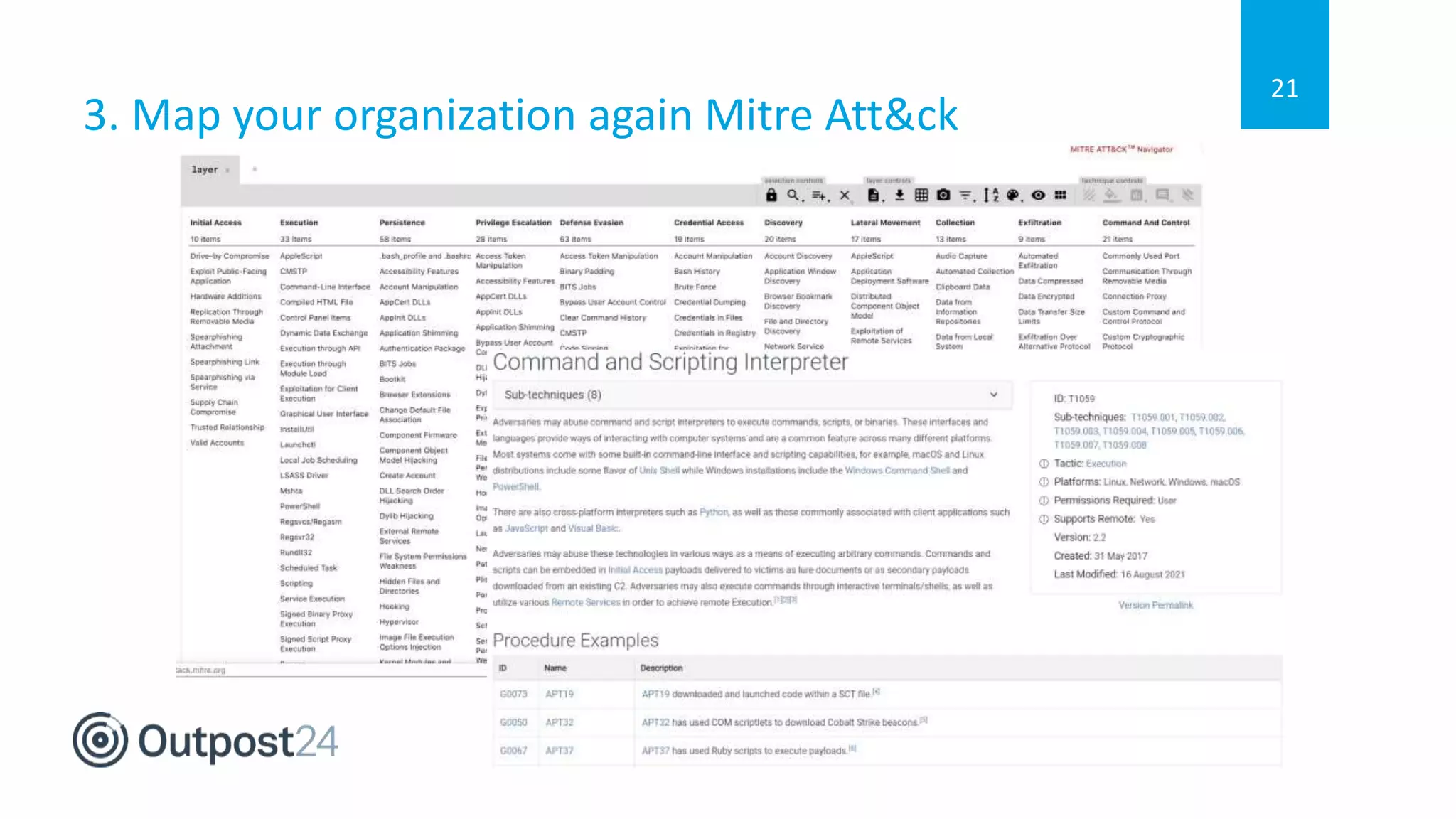
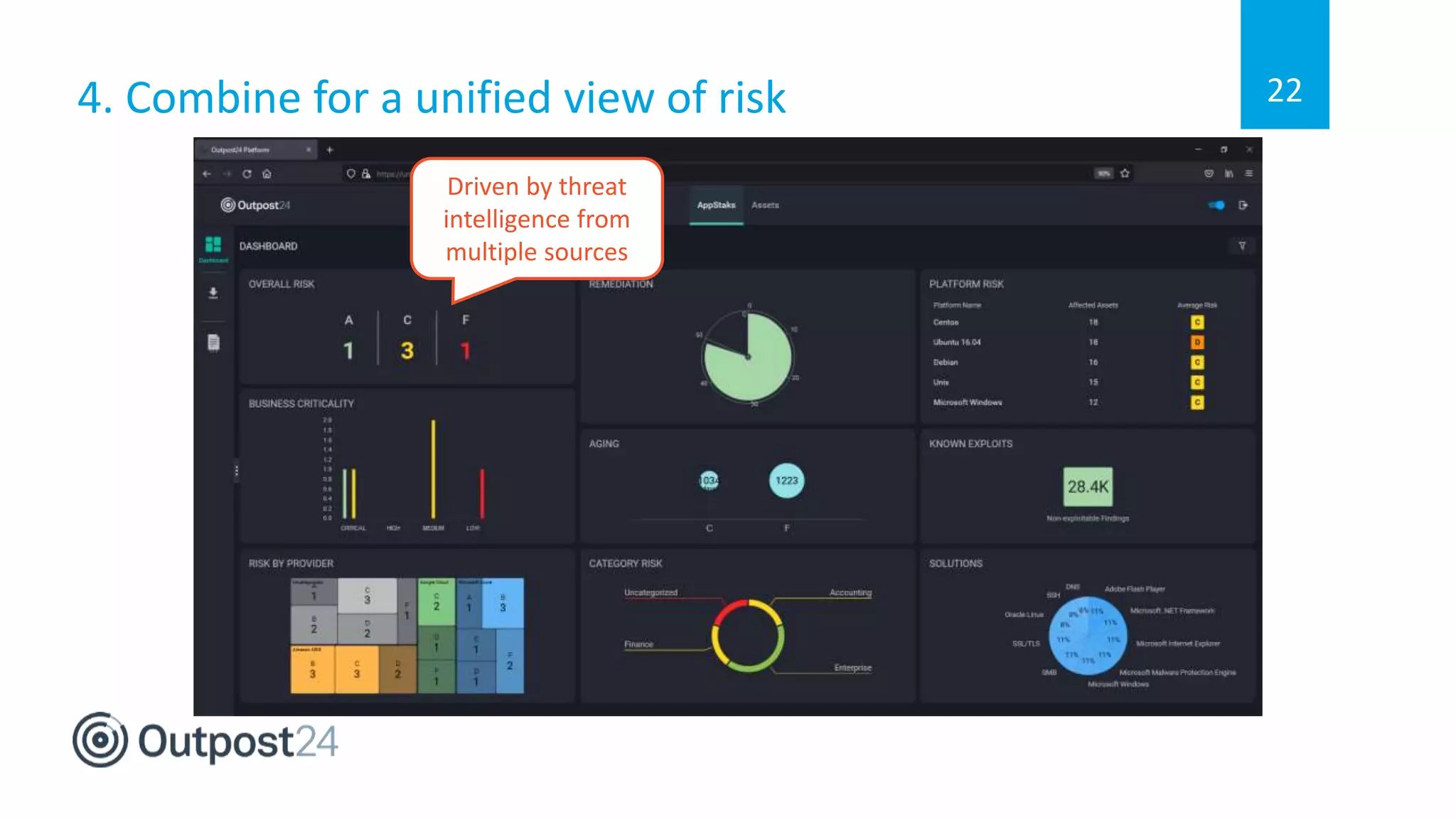
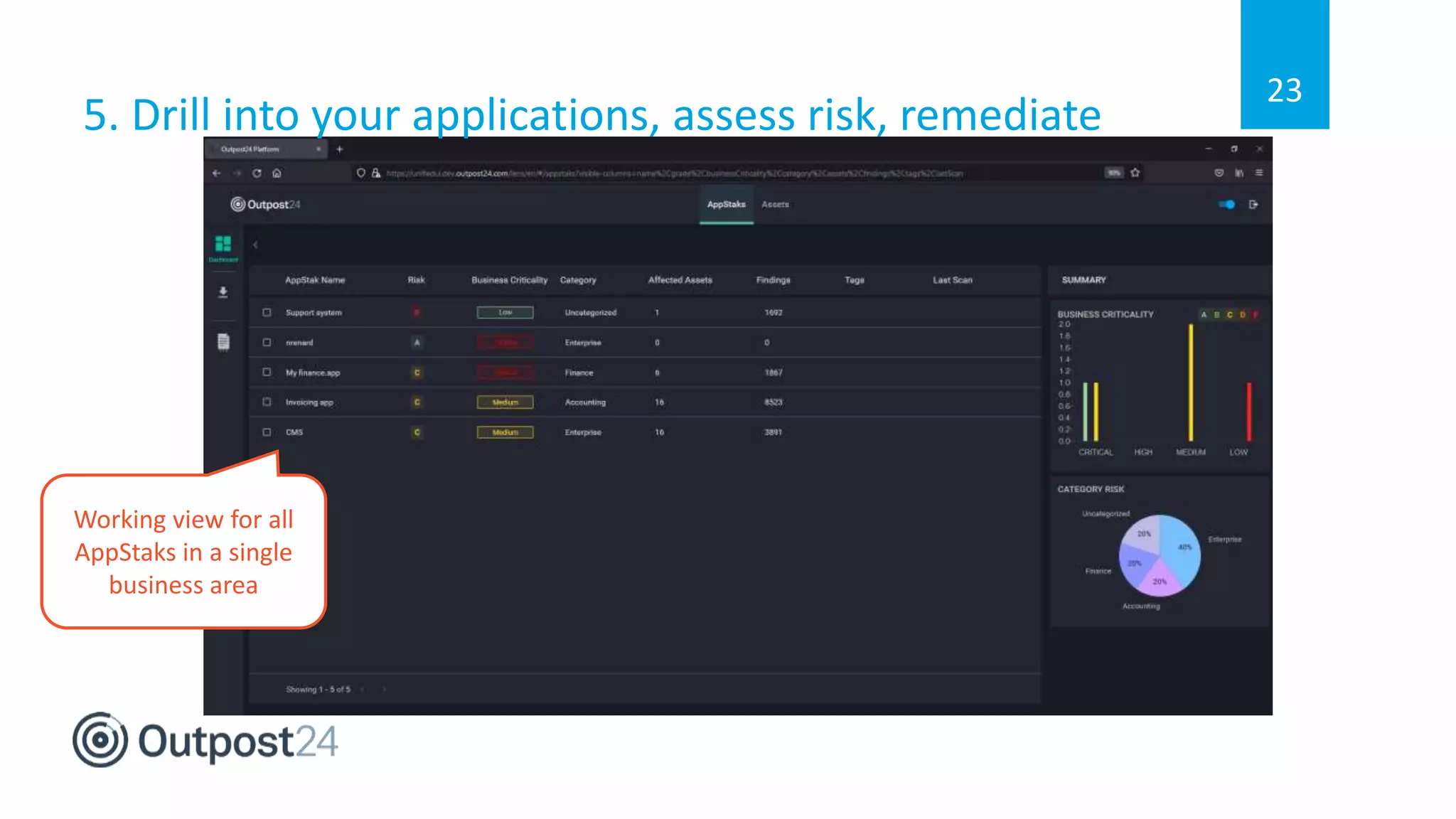
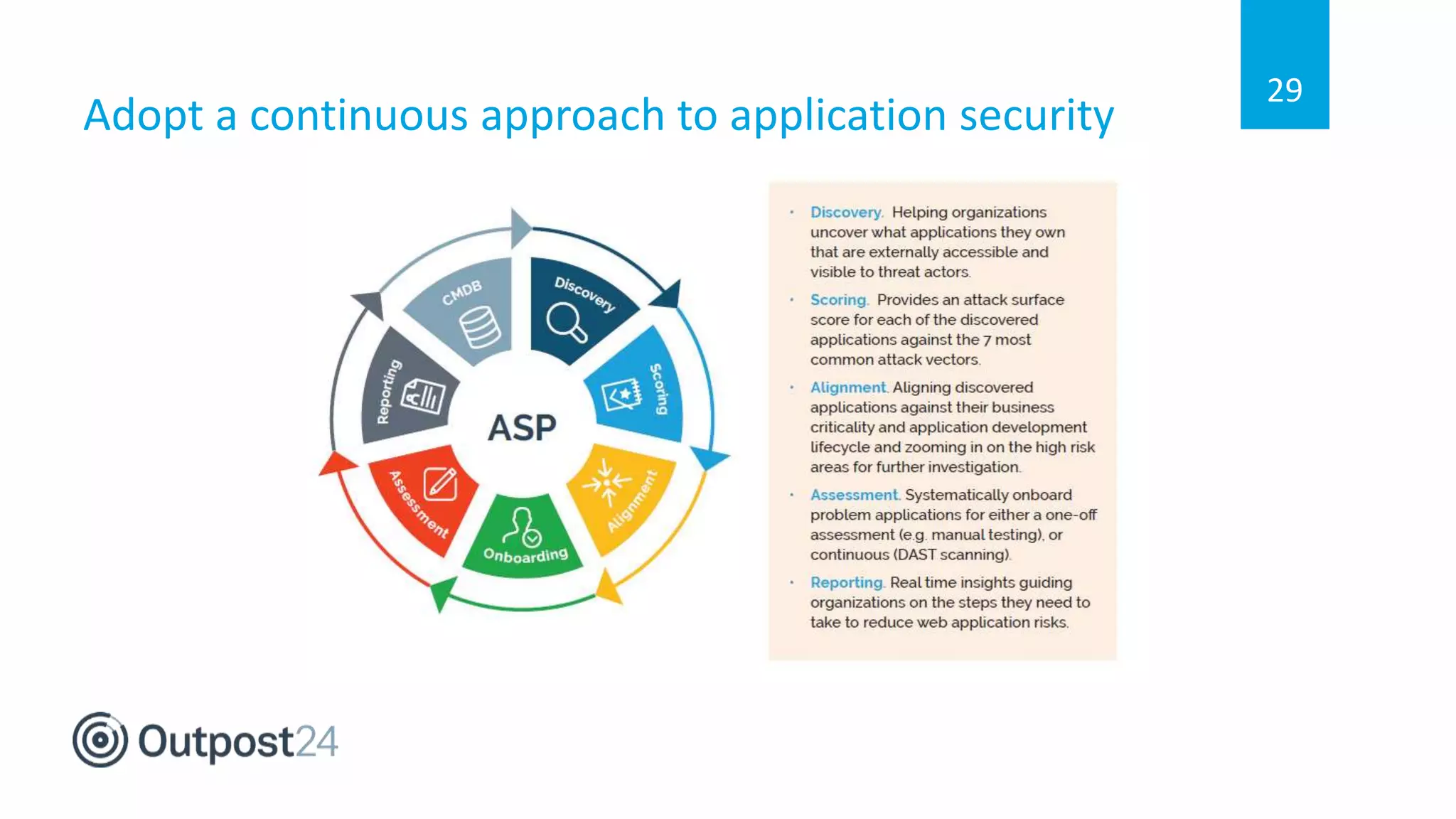
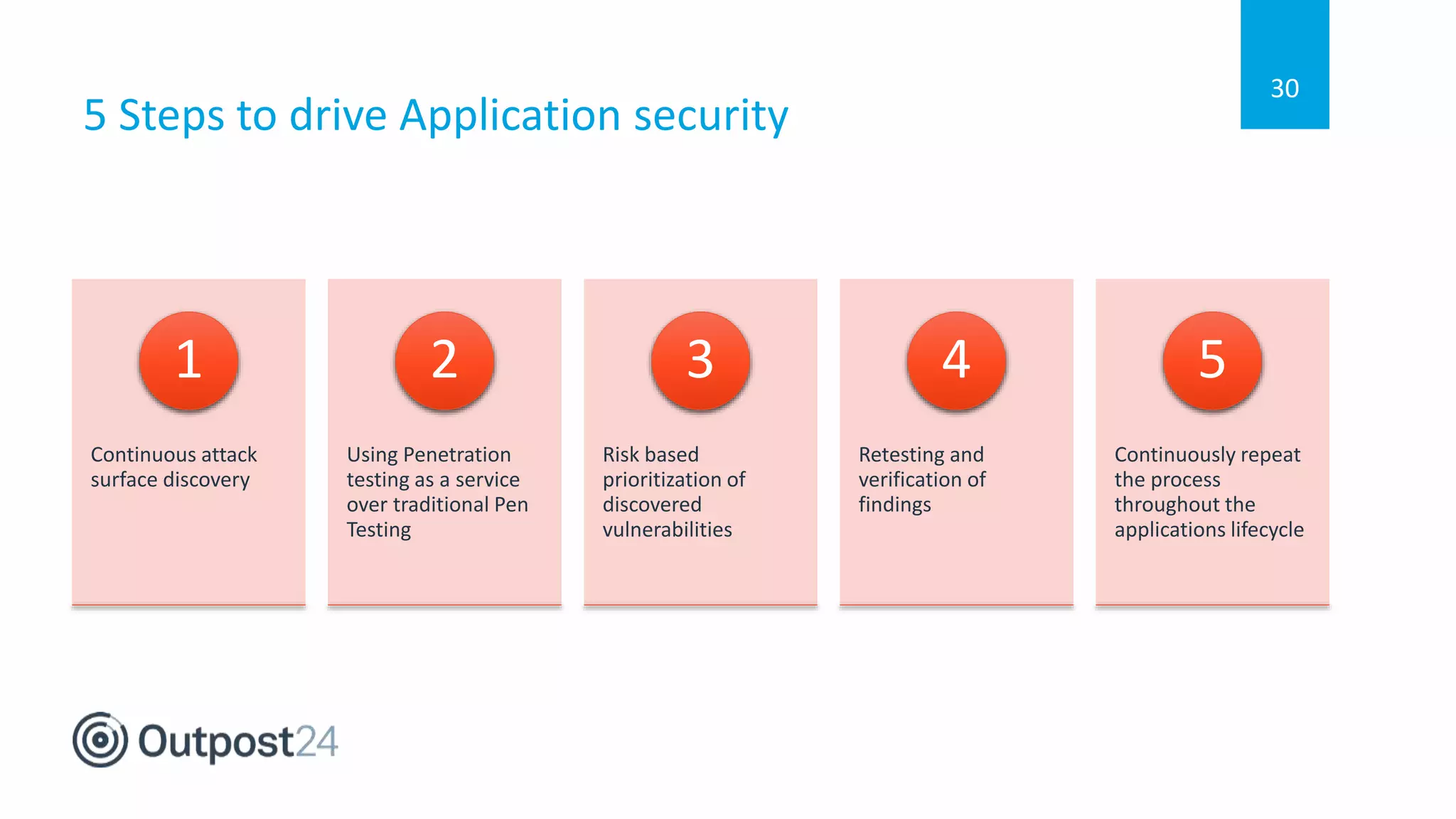
The document outlines a 5-step approach to building a continuous application security program, emphasizing the importance of understanding both deployed applications and overall attack surface. It advocates for using Penetration Testing as a Service (PTaaS) over traditional methods, employing risk-based remediation strategies, and maintaining continuous vulnerability assessment throughout the application lifecycle. Effective collaboration and threat intelligence are key components to successfully reducing cyber risks.