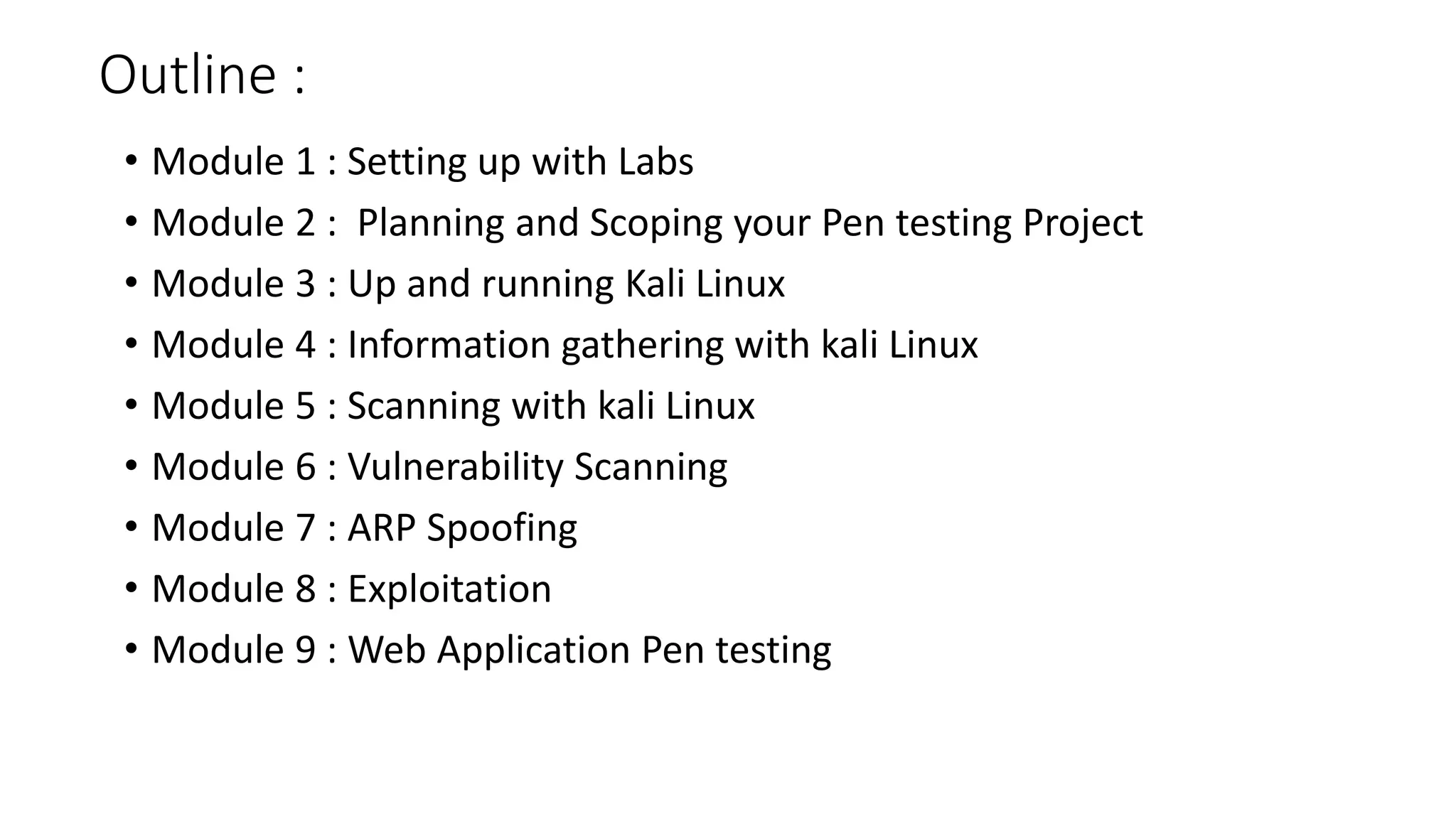
This document outlines the modules of a hands-on penetration testing course. The 9 modules cover: 1) setting up labs; 2) planning penetration tests; 3) using Kali Linux; 4) information gathering techniques; 5) scanning with tools like Nmap; 6) vulnerability scanning with OpenVAS and Nessus; 7) ARP spoofing tools; 8) exploitation tools and techniques; and 9) web application penetration testing tools like Burp Suite. The course uses virtual machines like Windows, Linux, and Kali Linux and teaches methodologies for planning, assessing, and reporting on penetration tests.