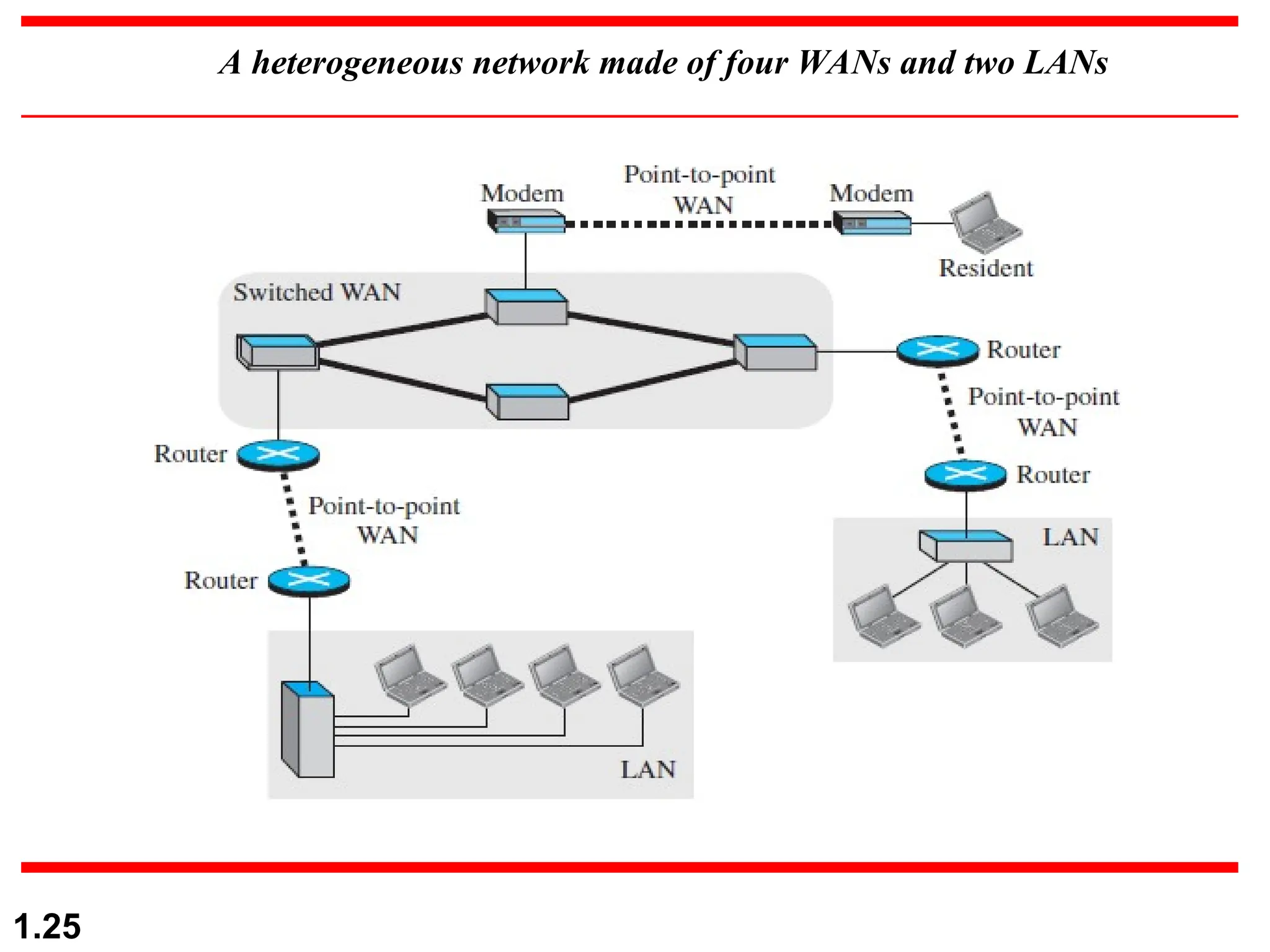
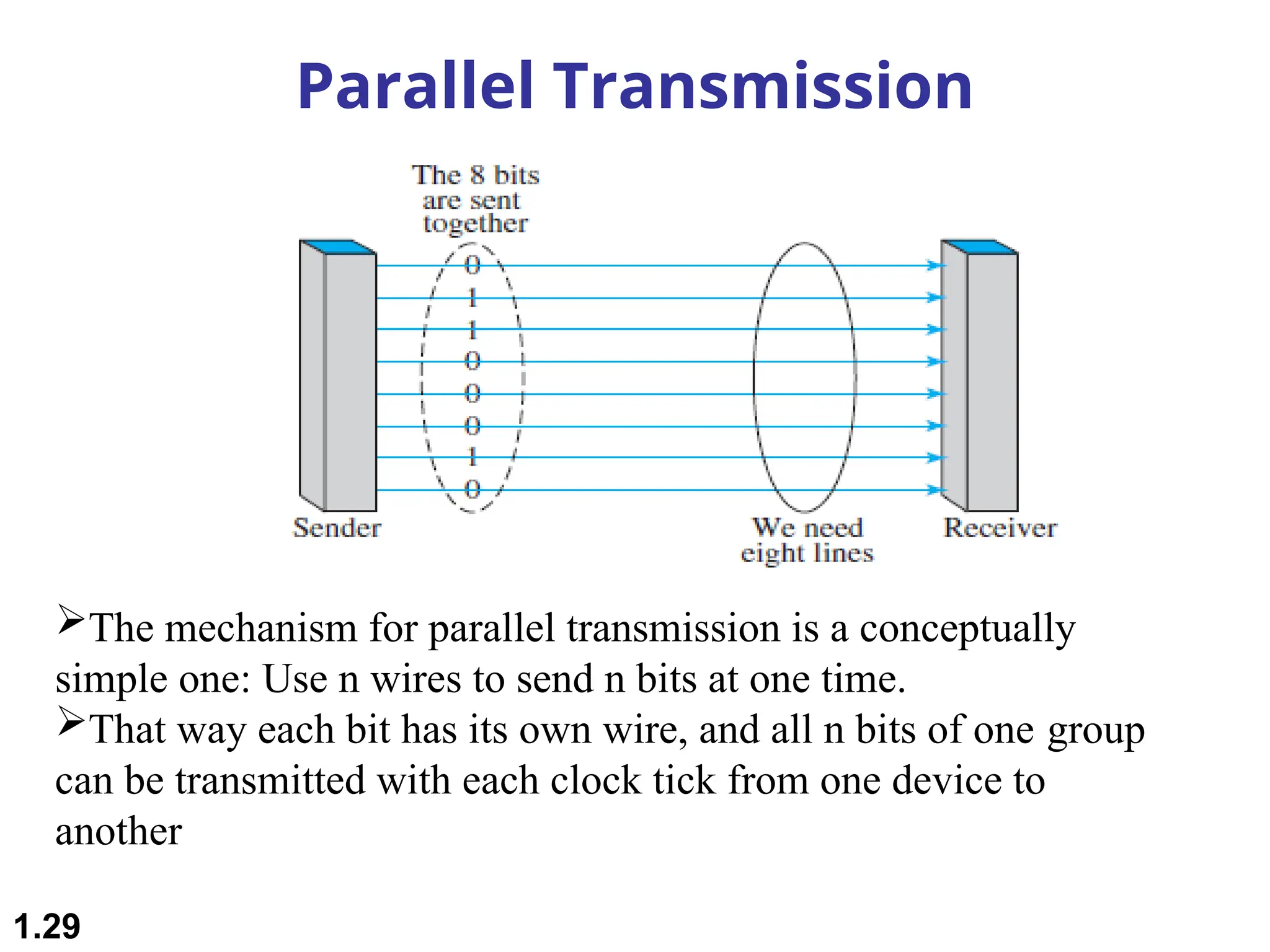
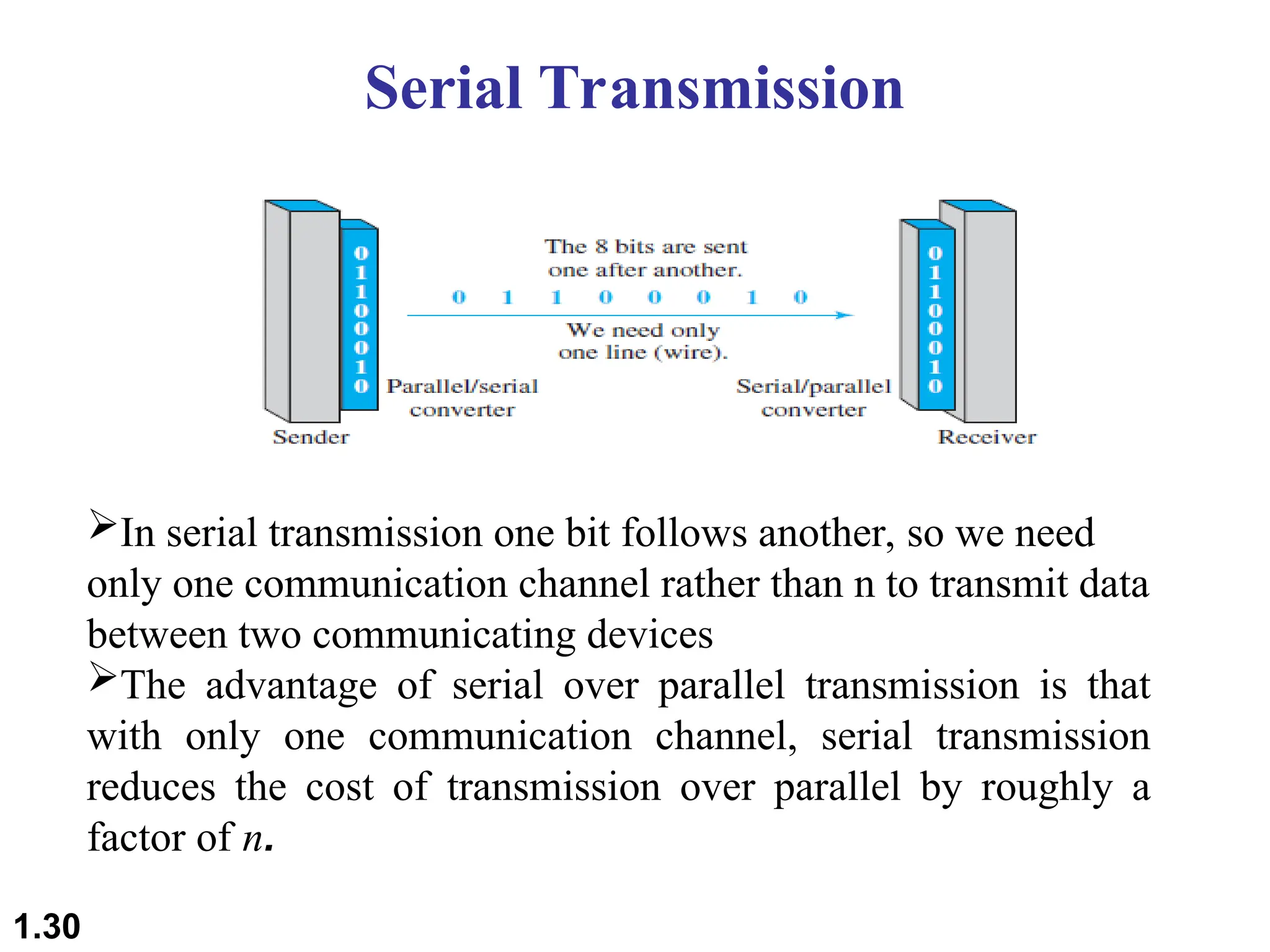
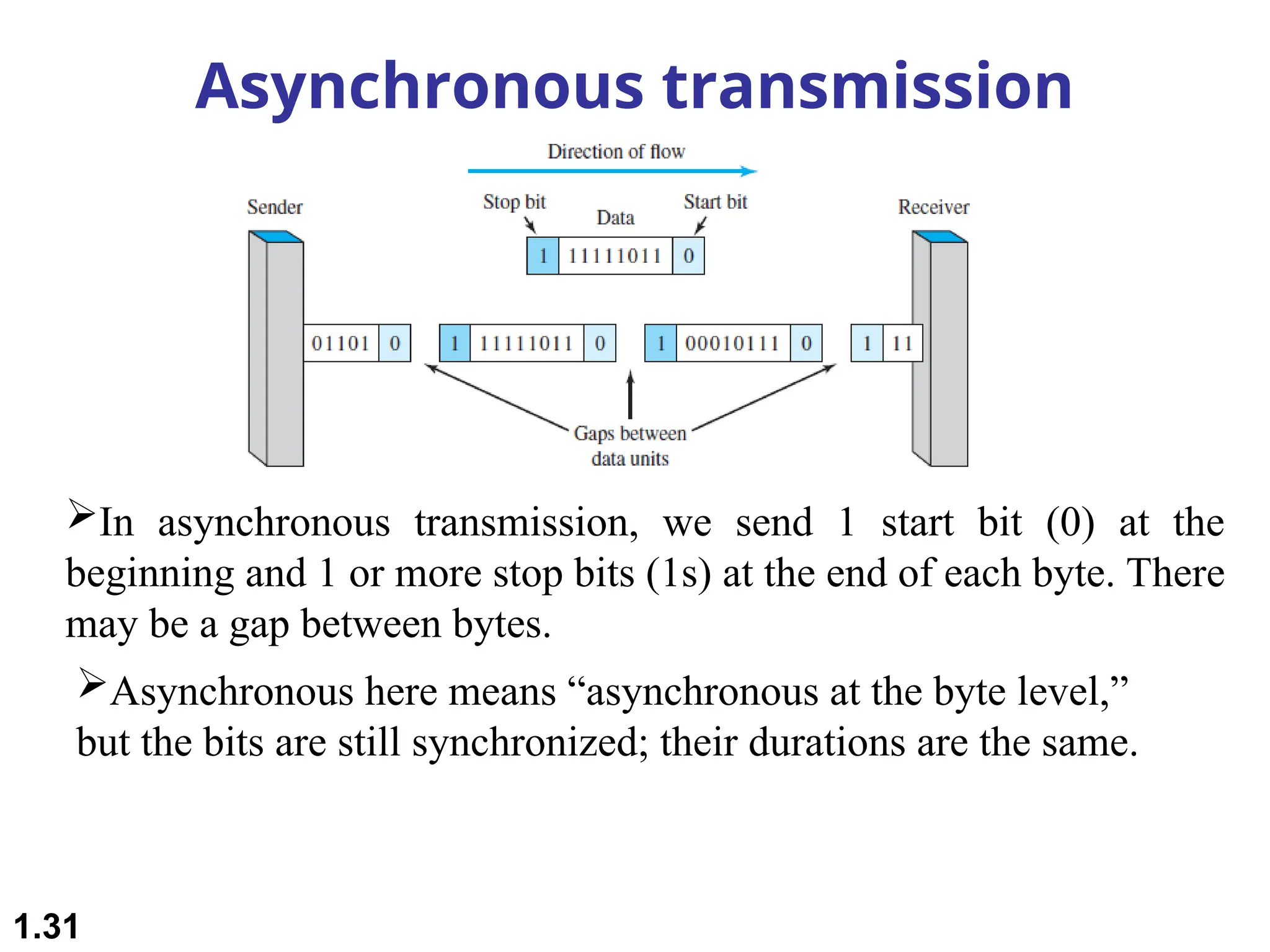
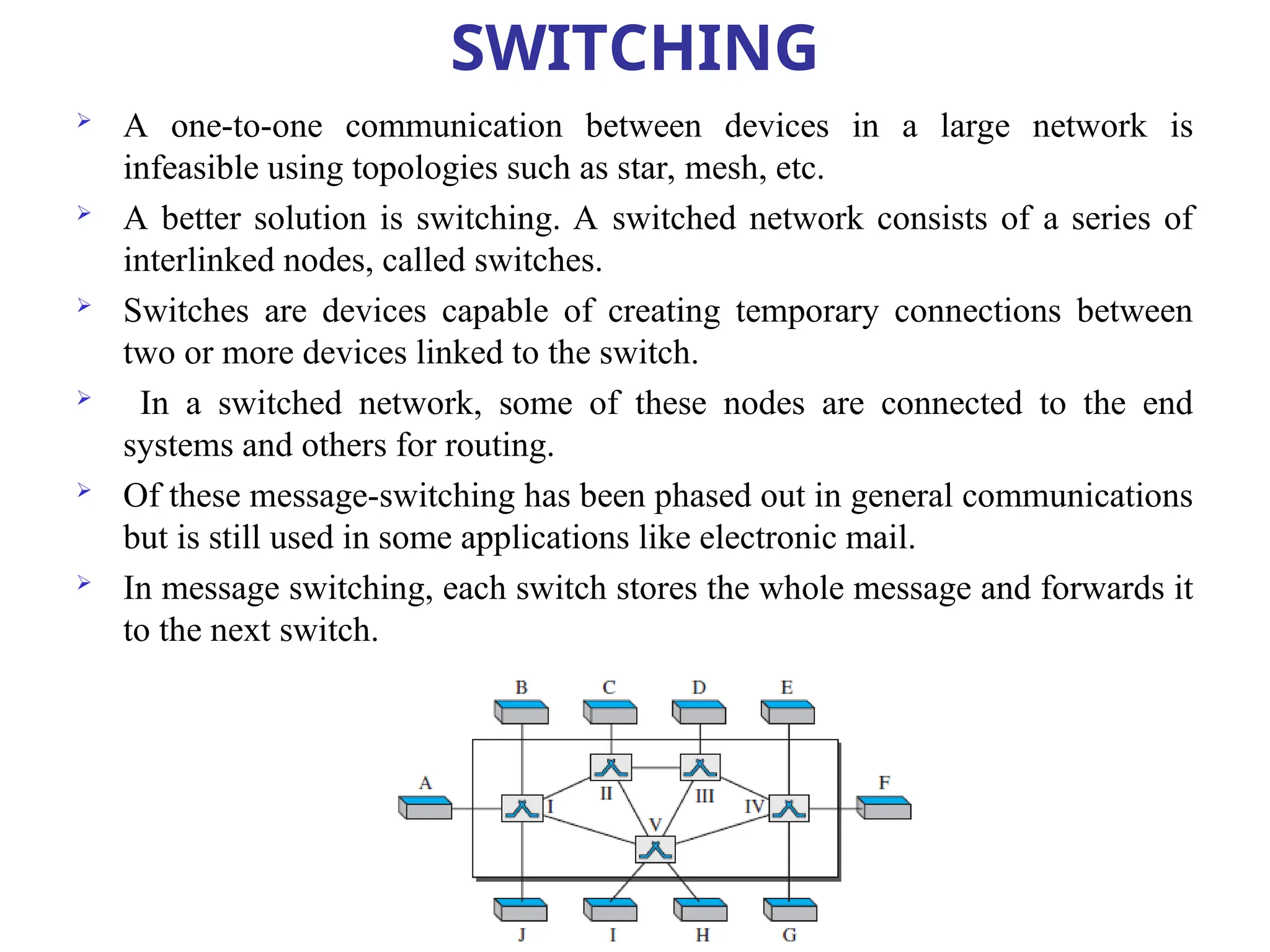
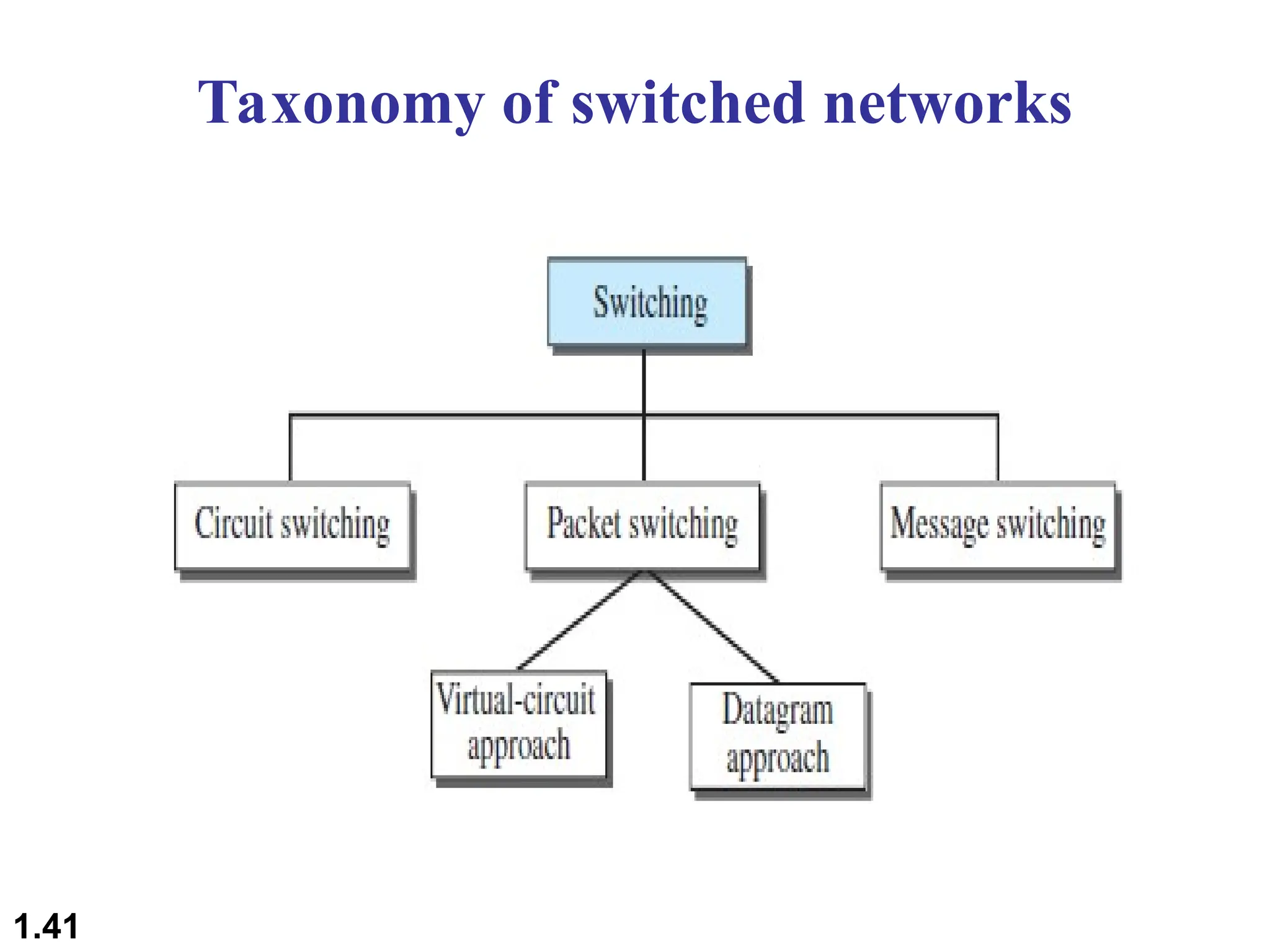
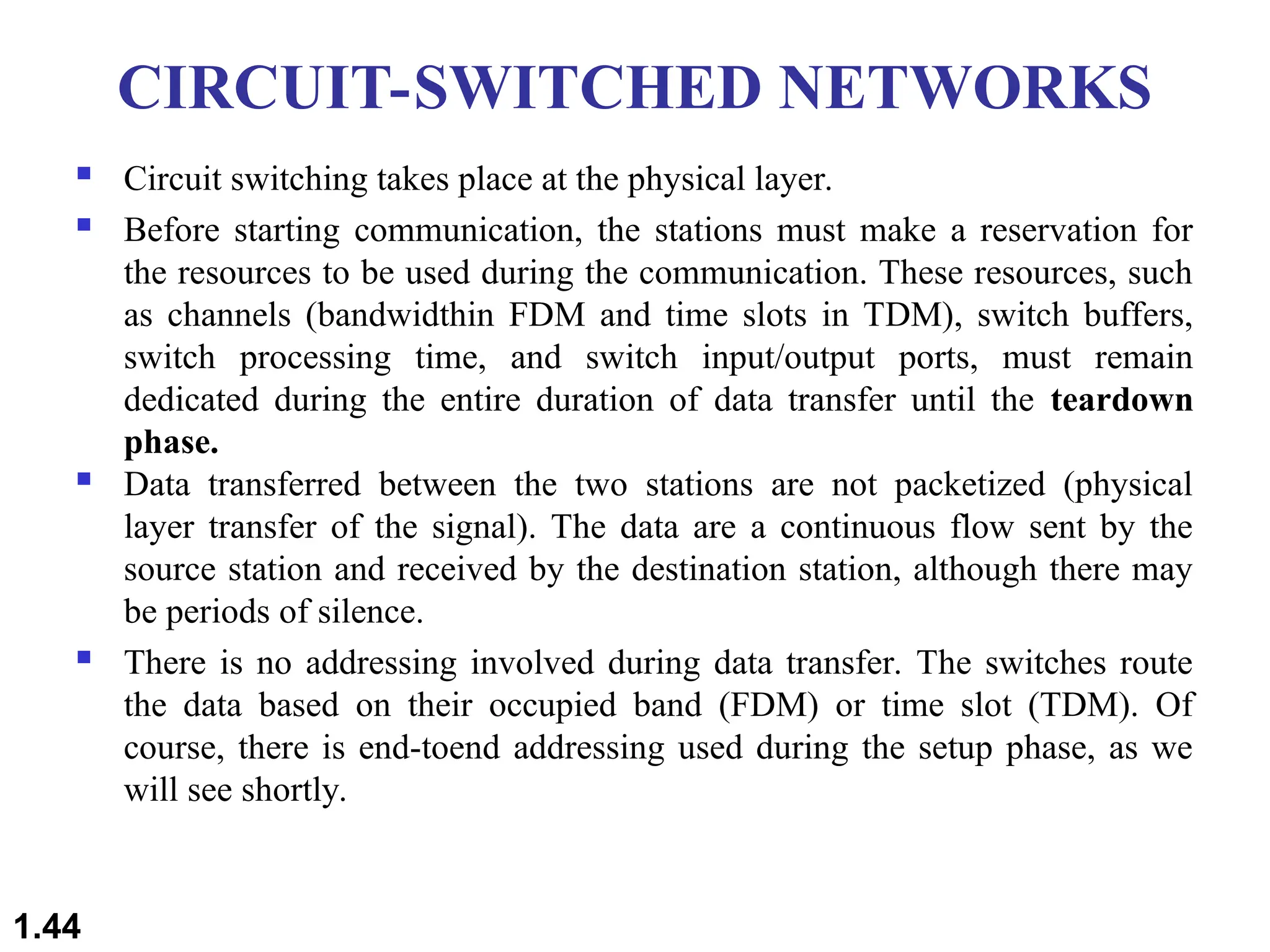
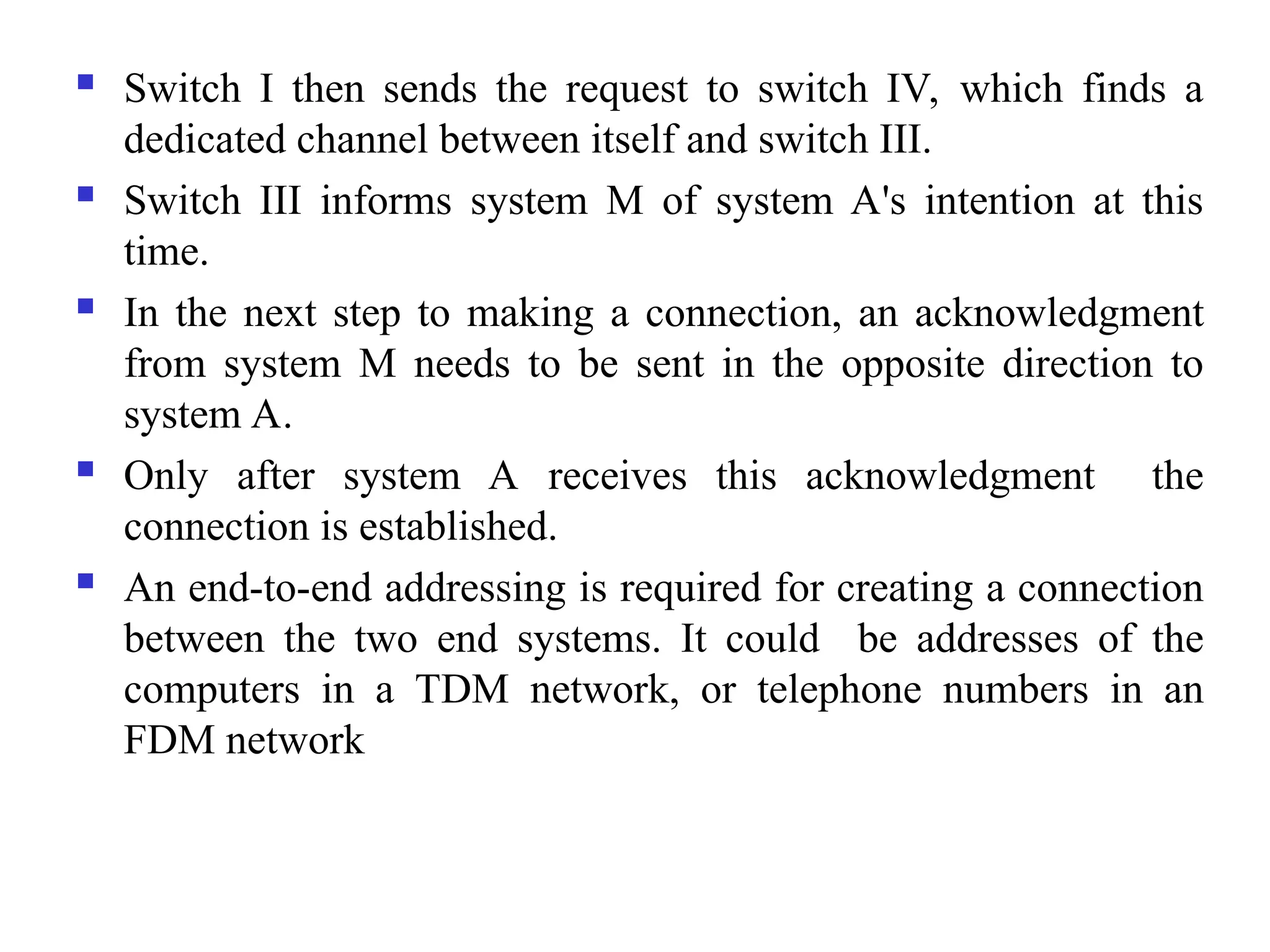
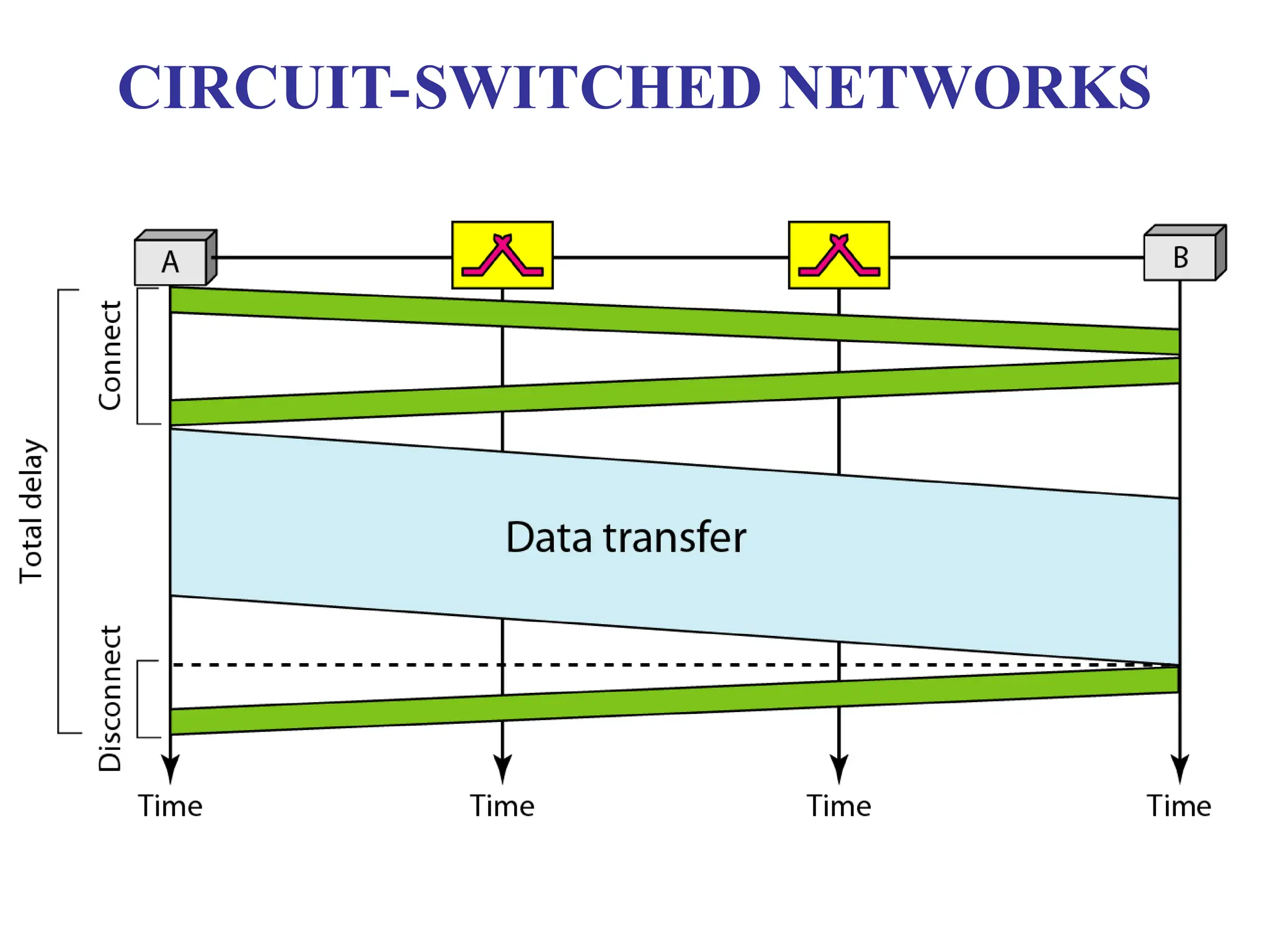
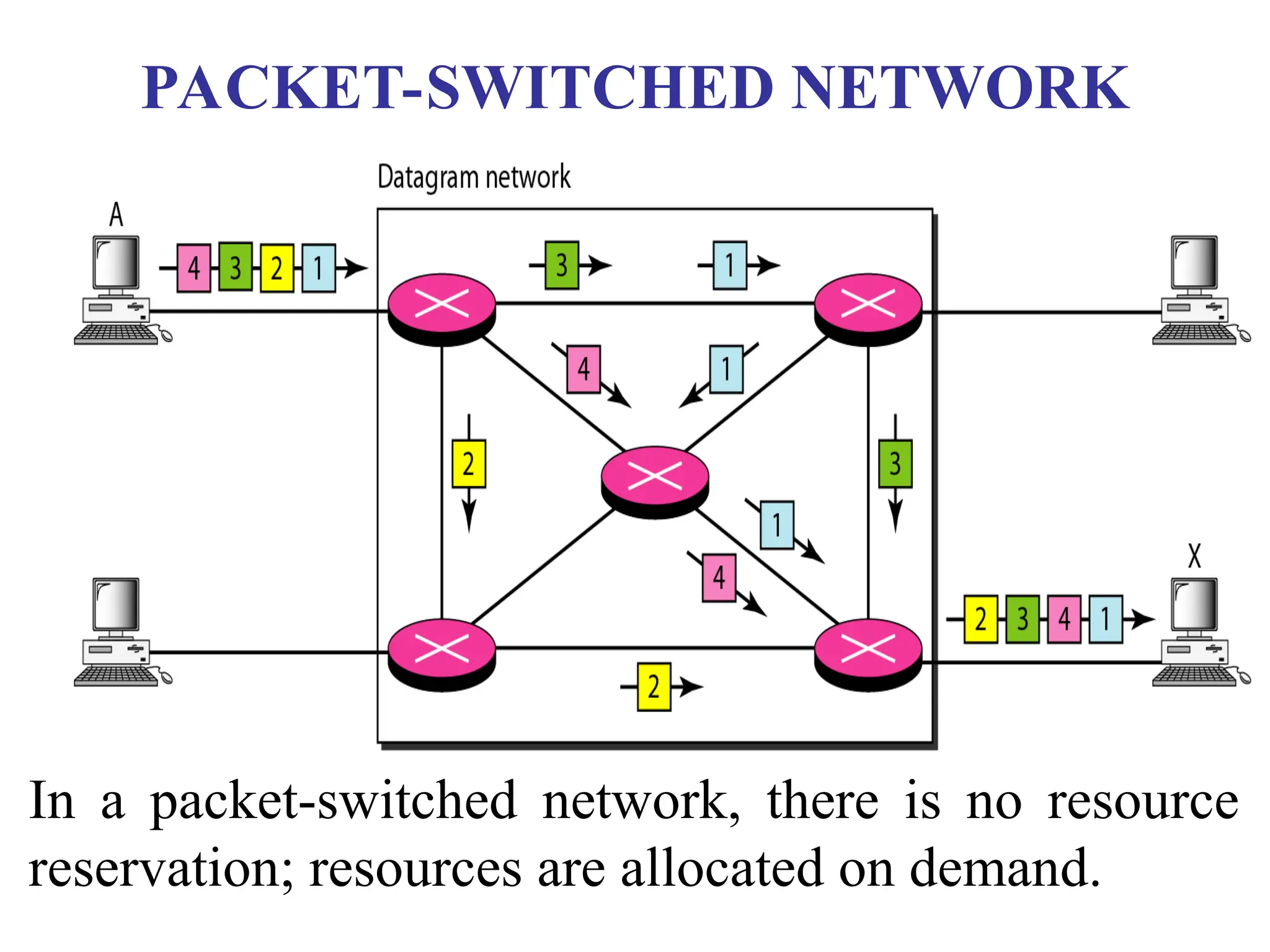
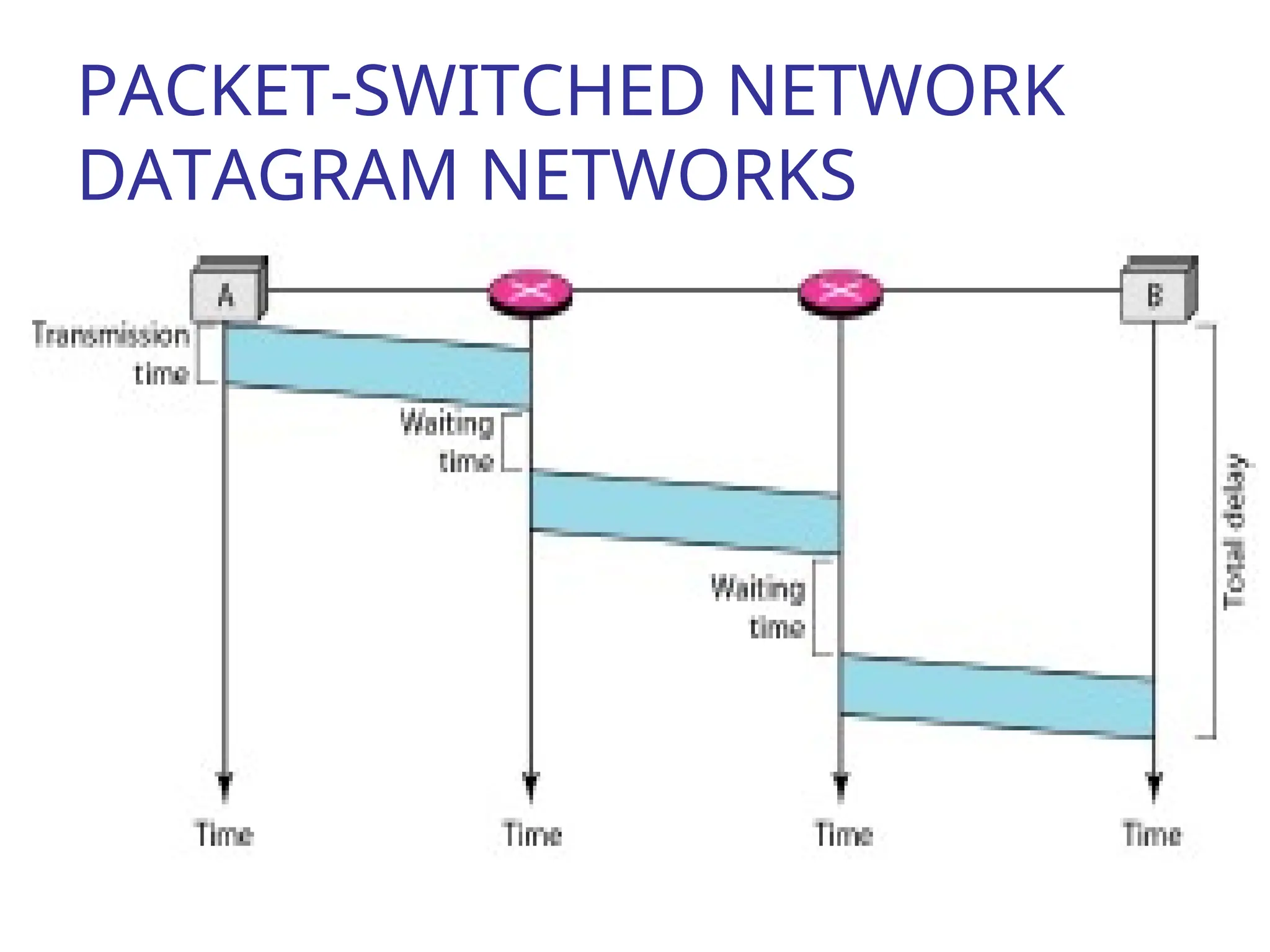
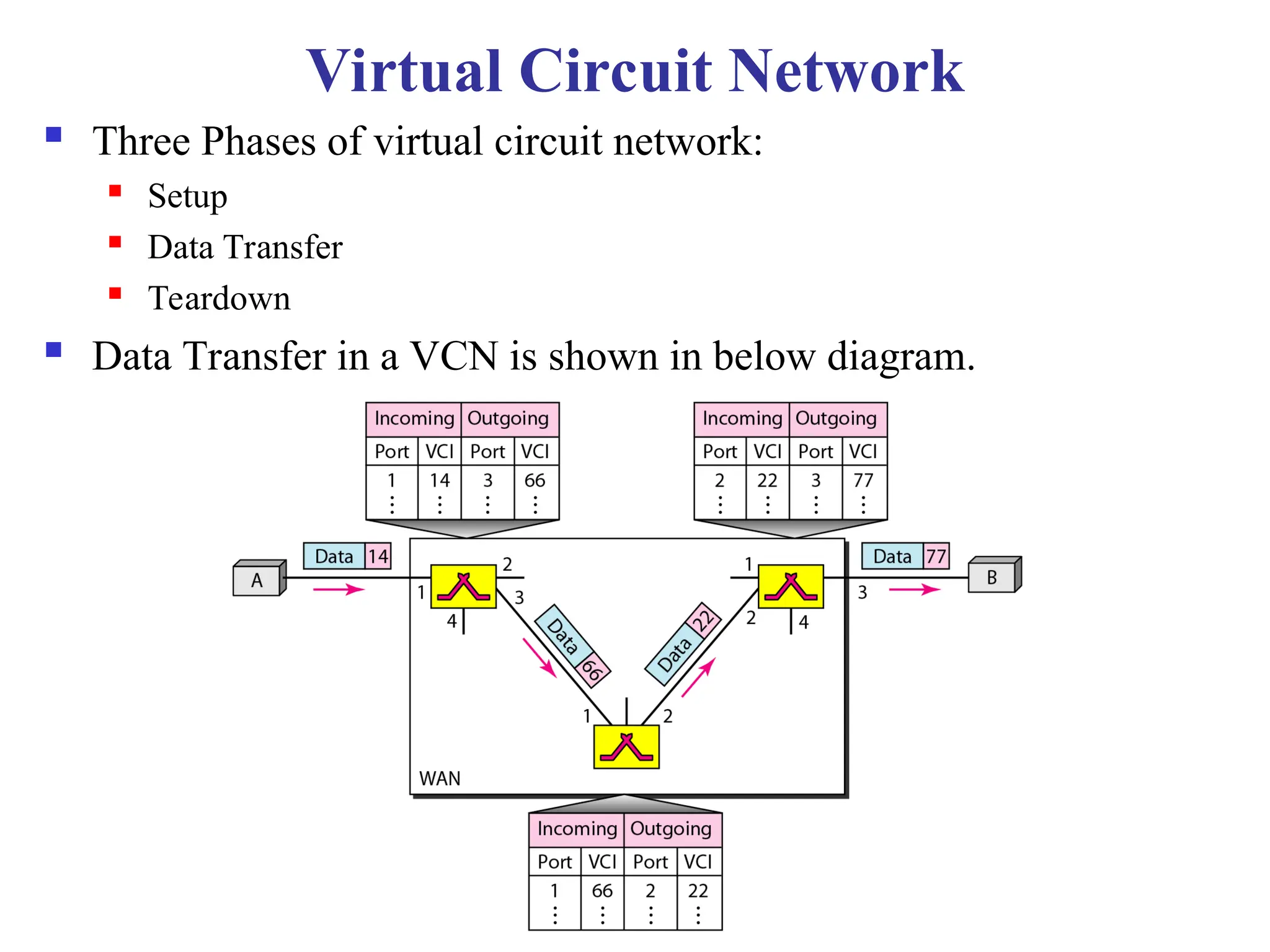
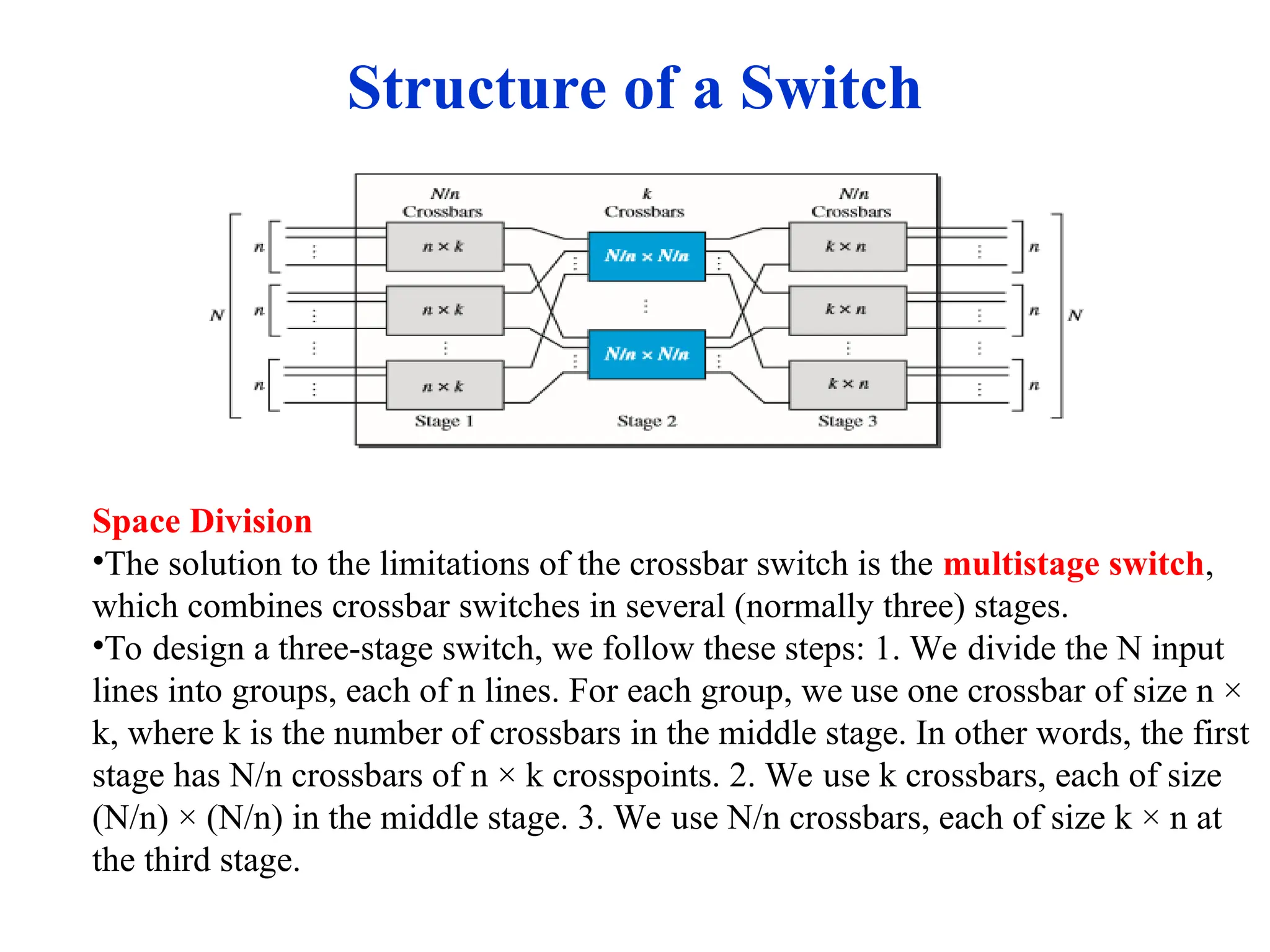
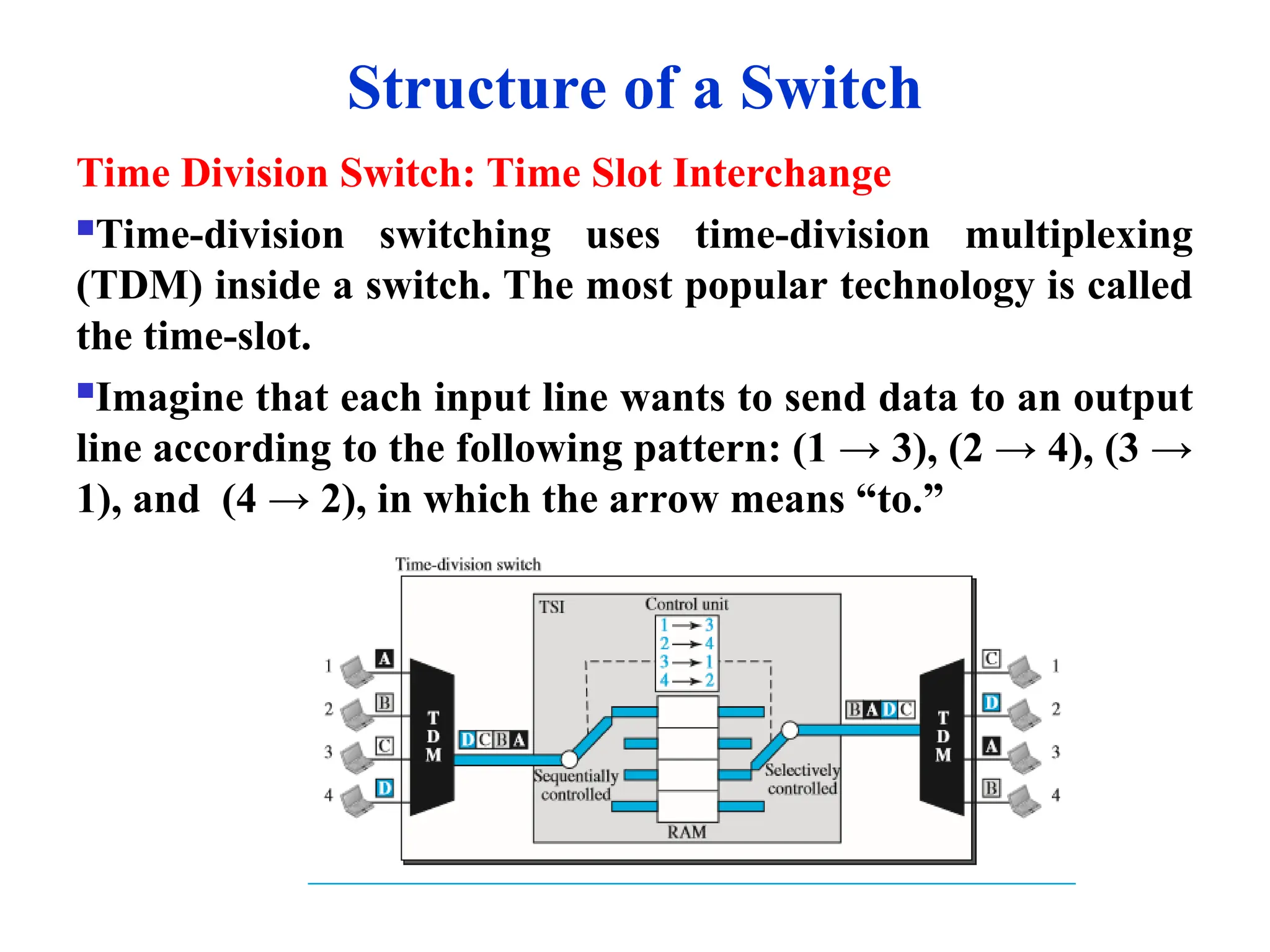
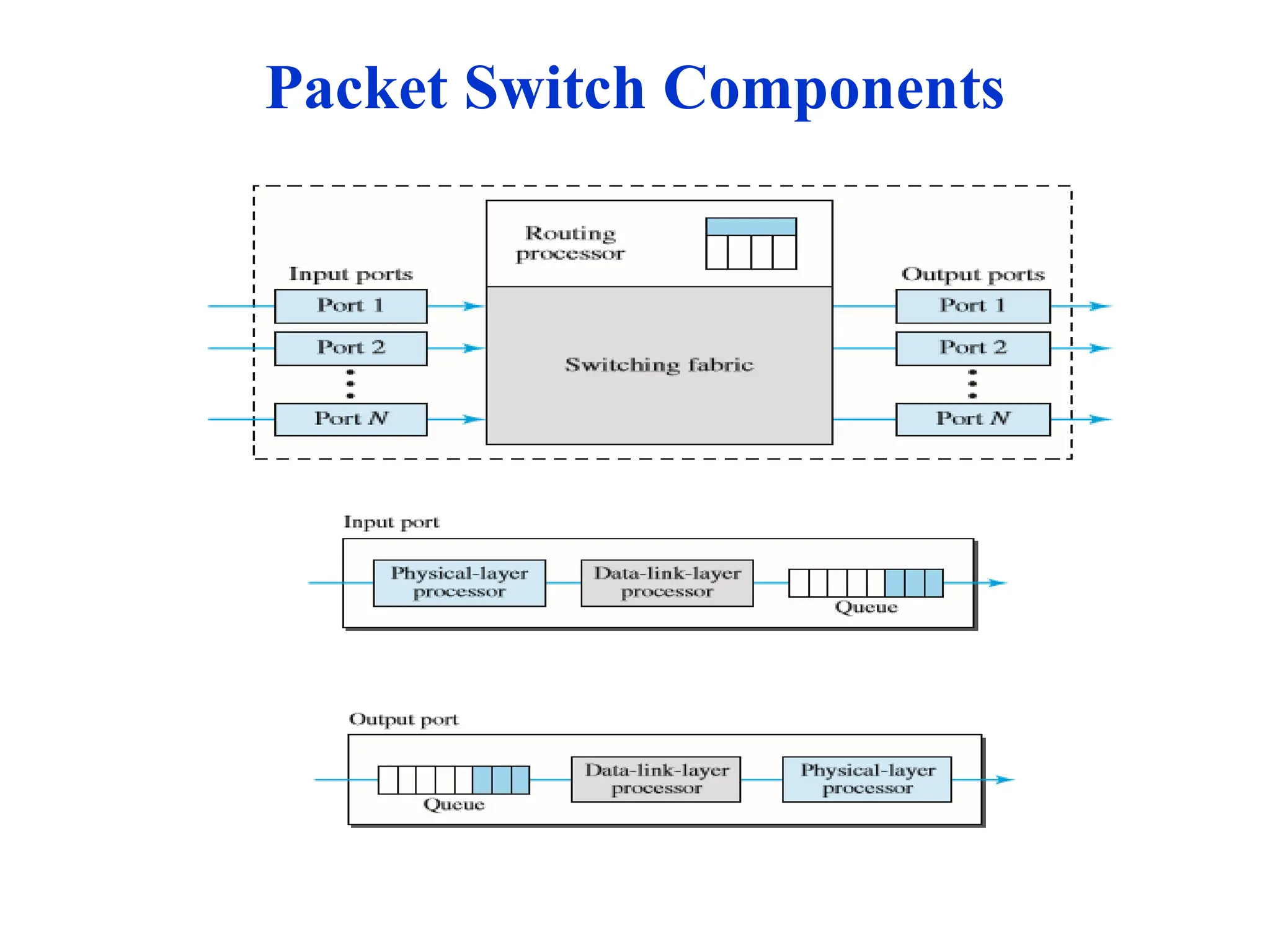
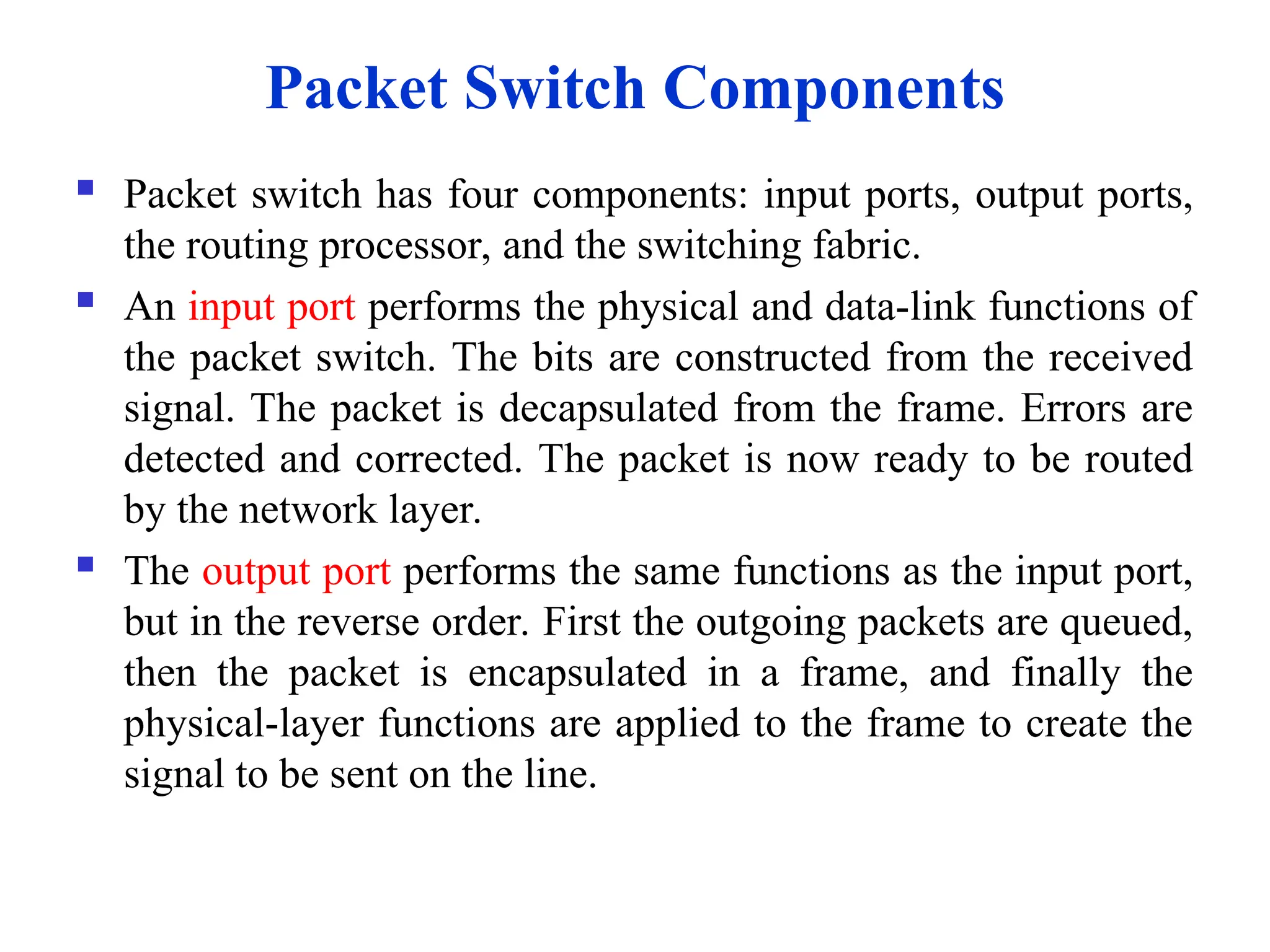
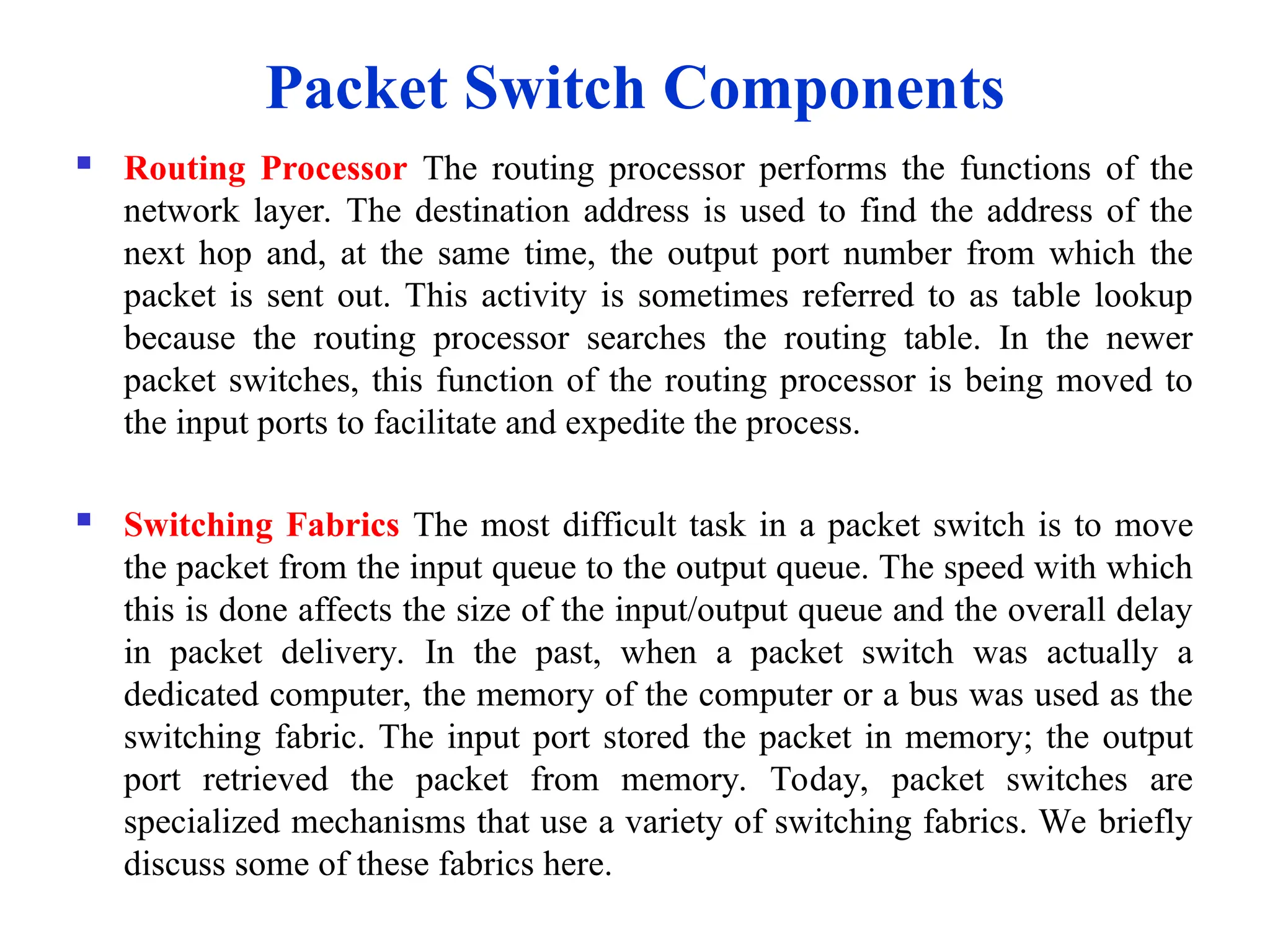
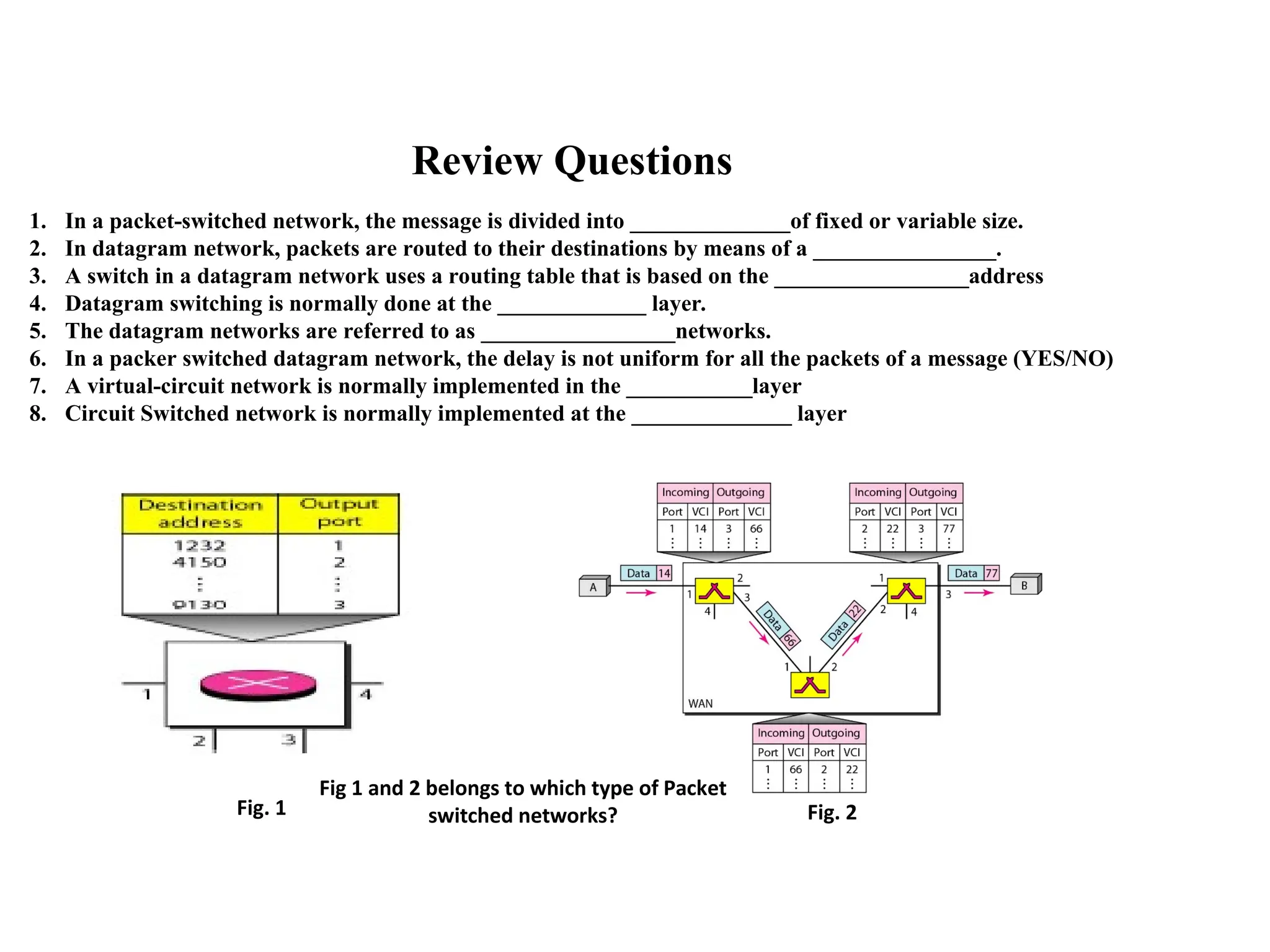
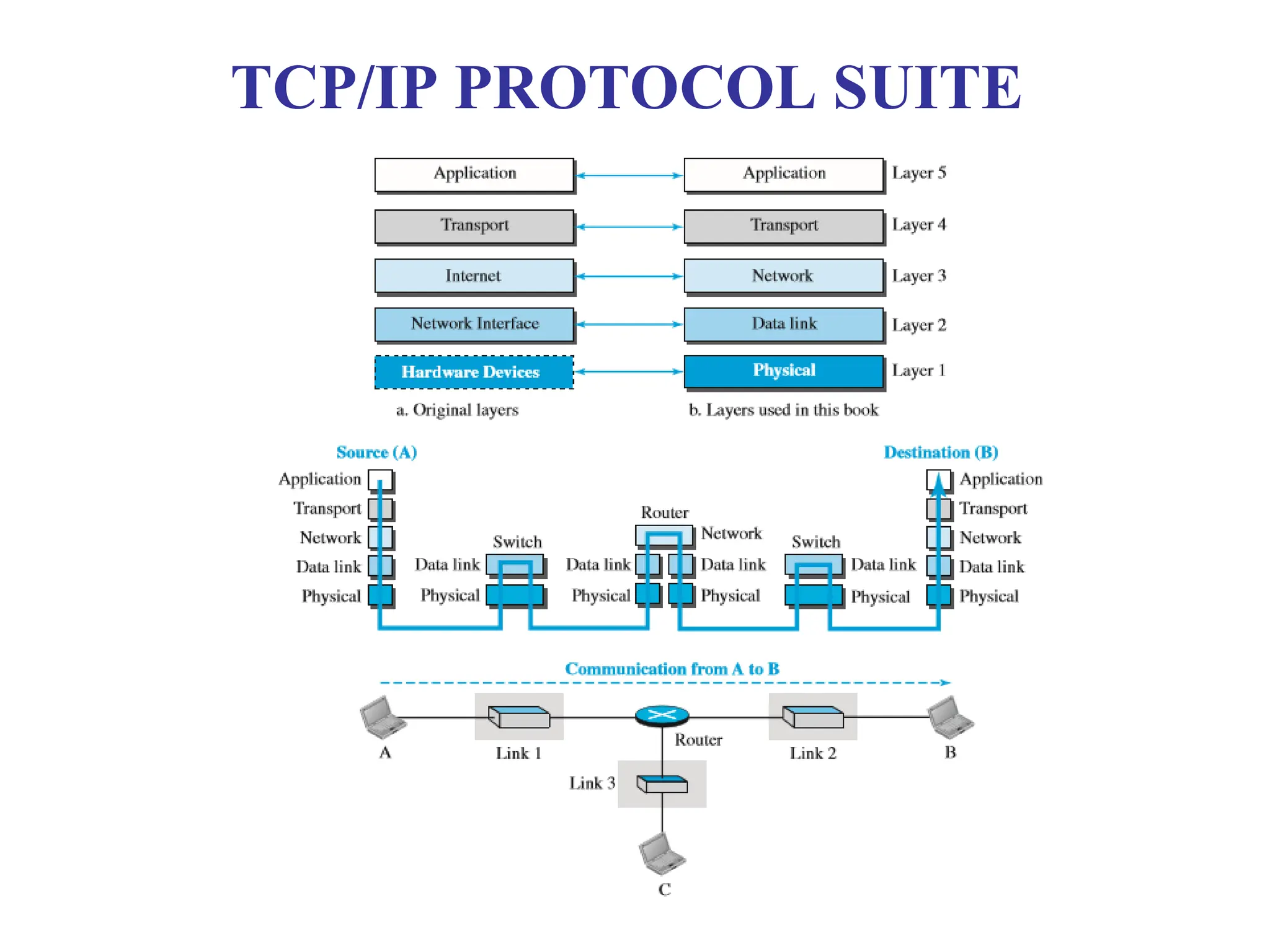
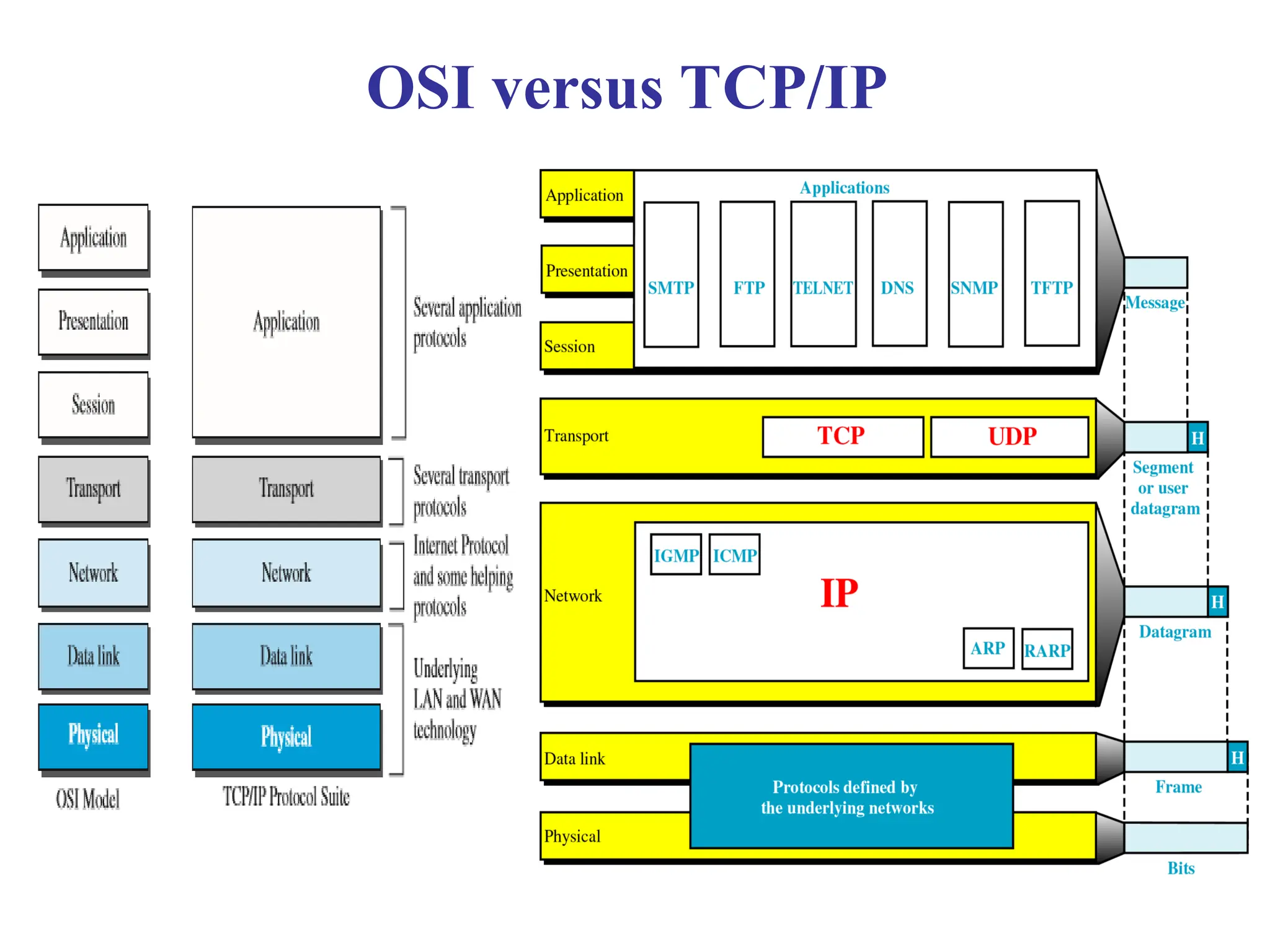
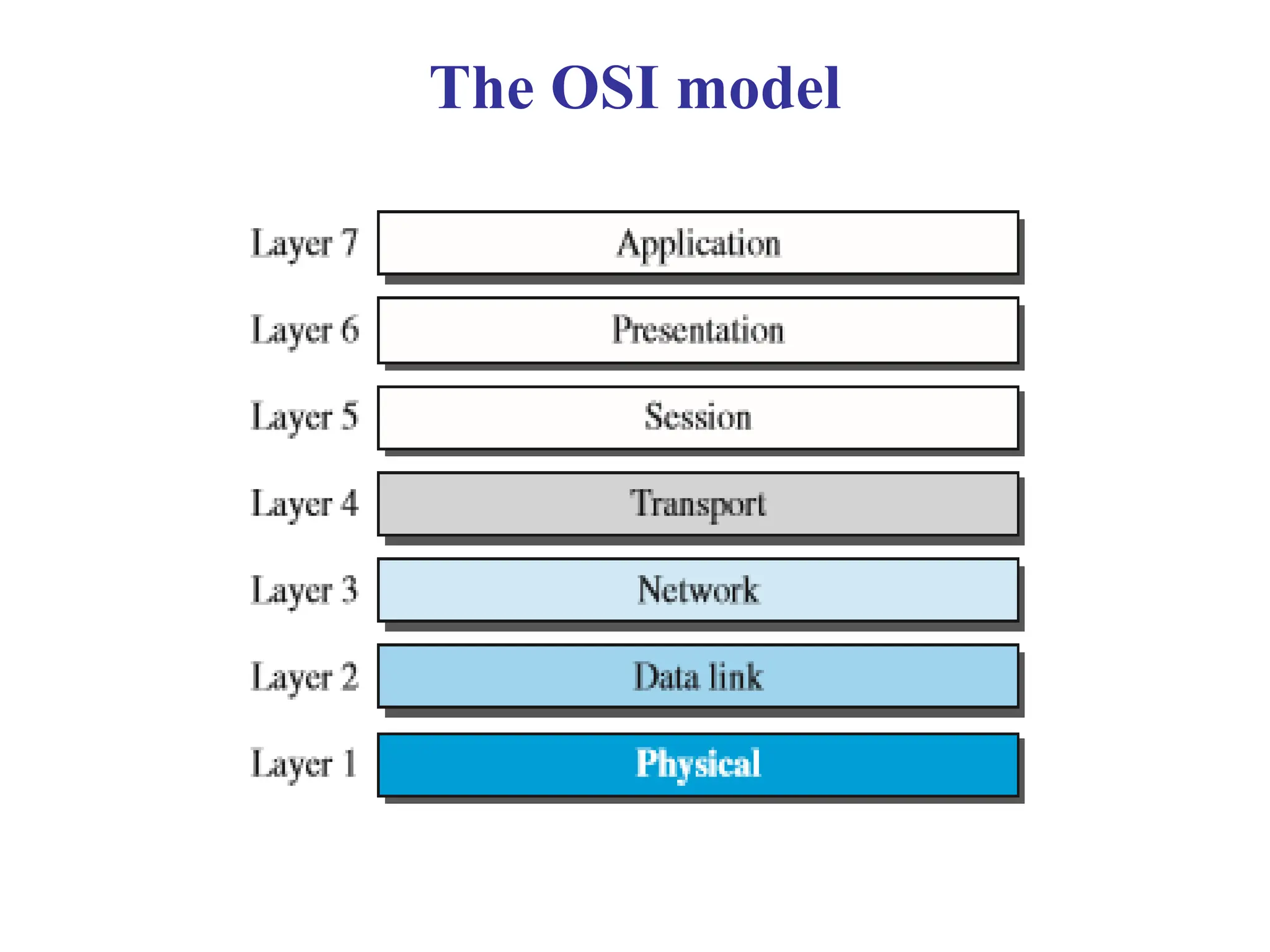
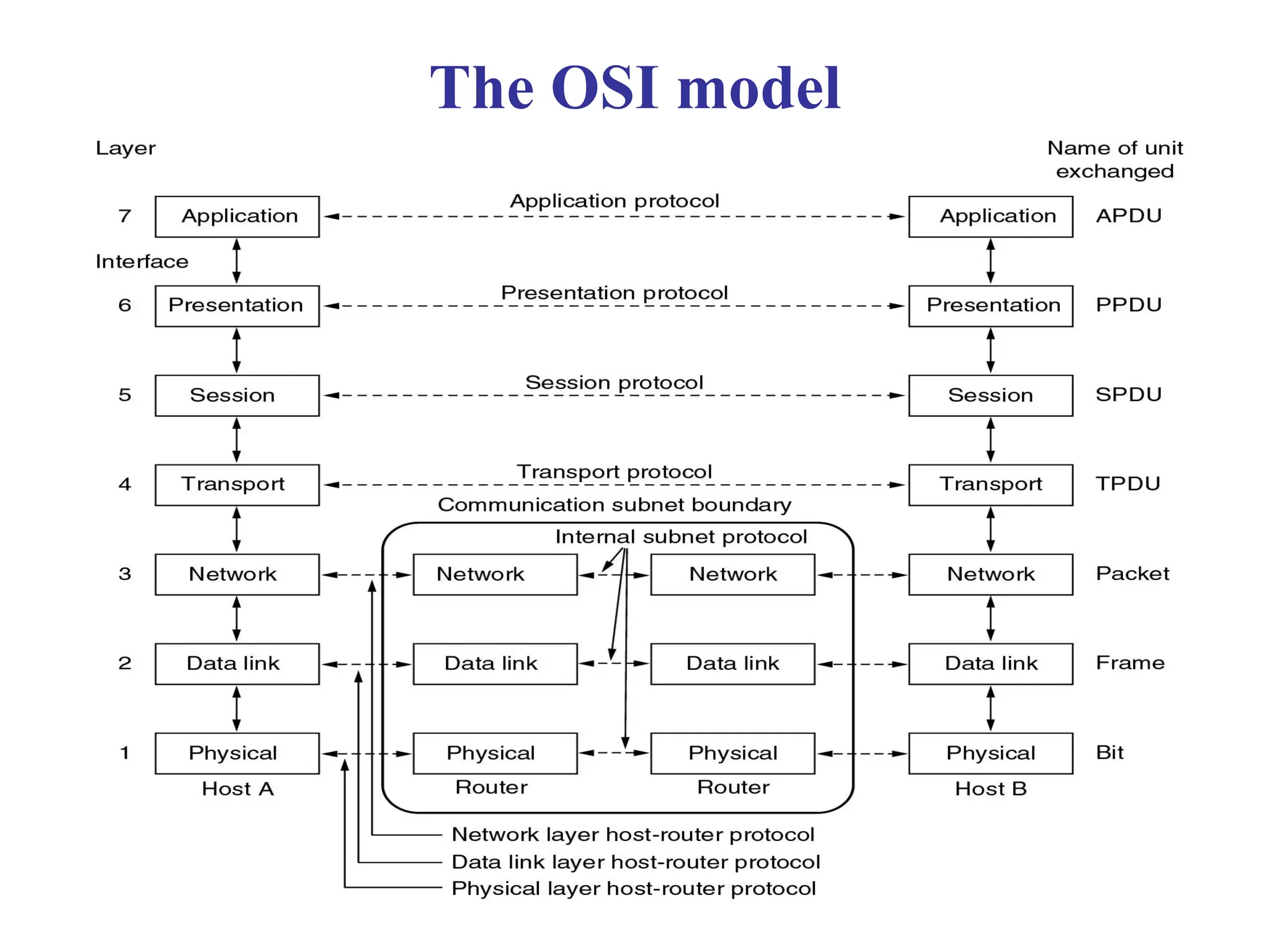
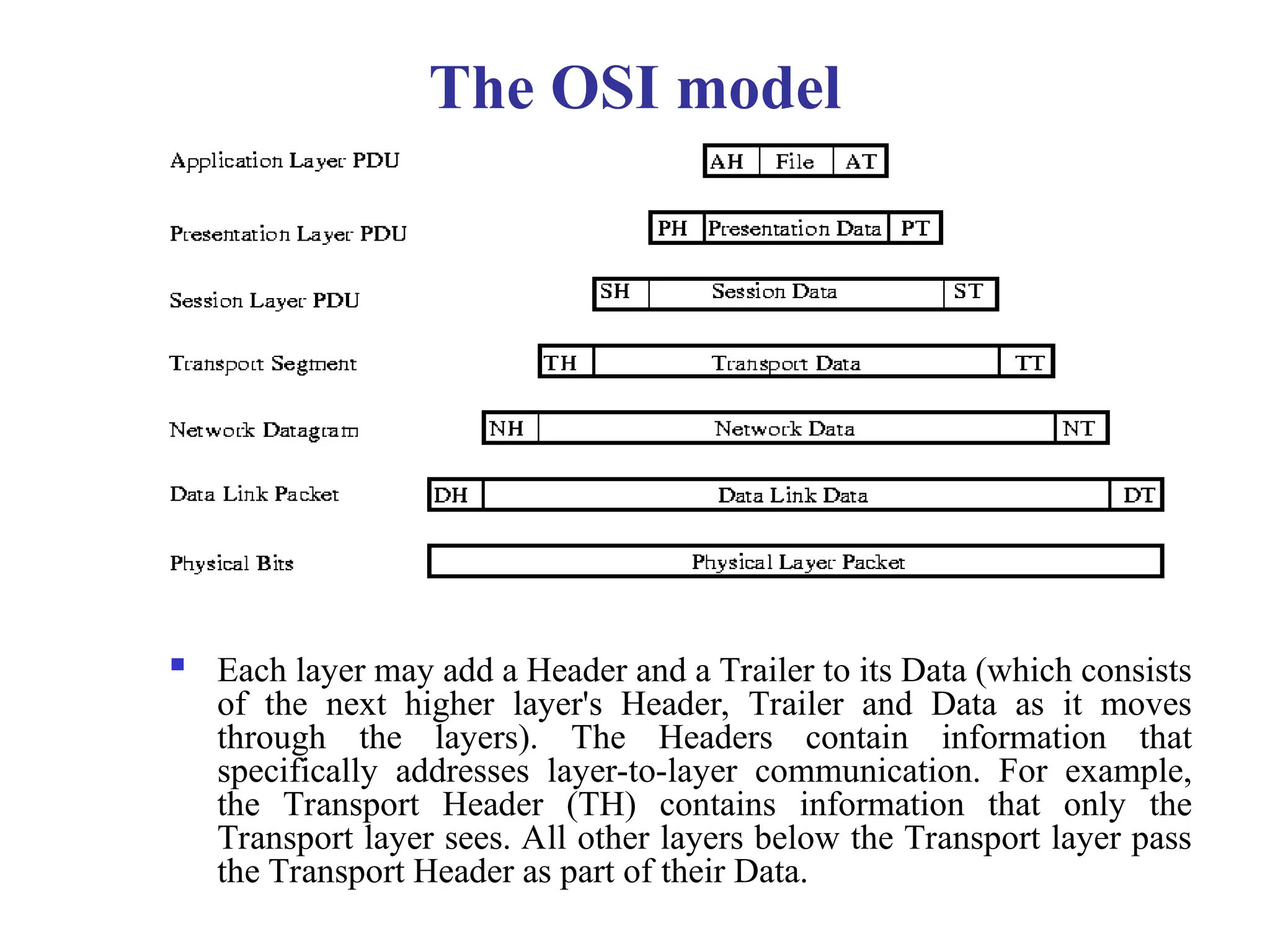
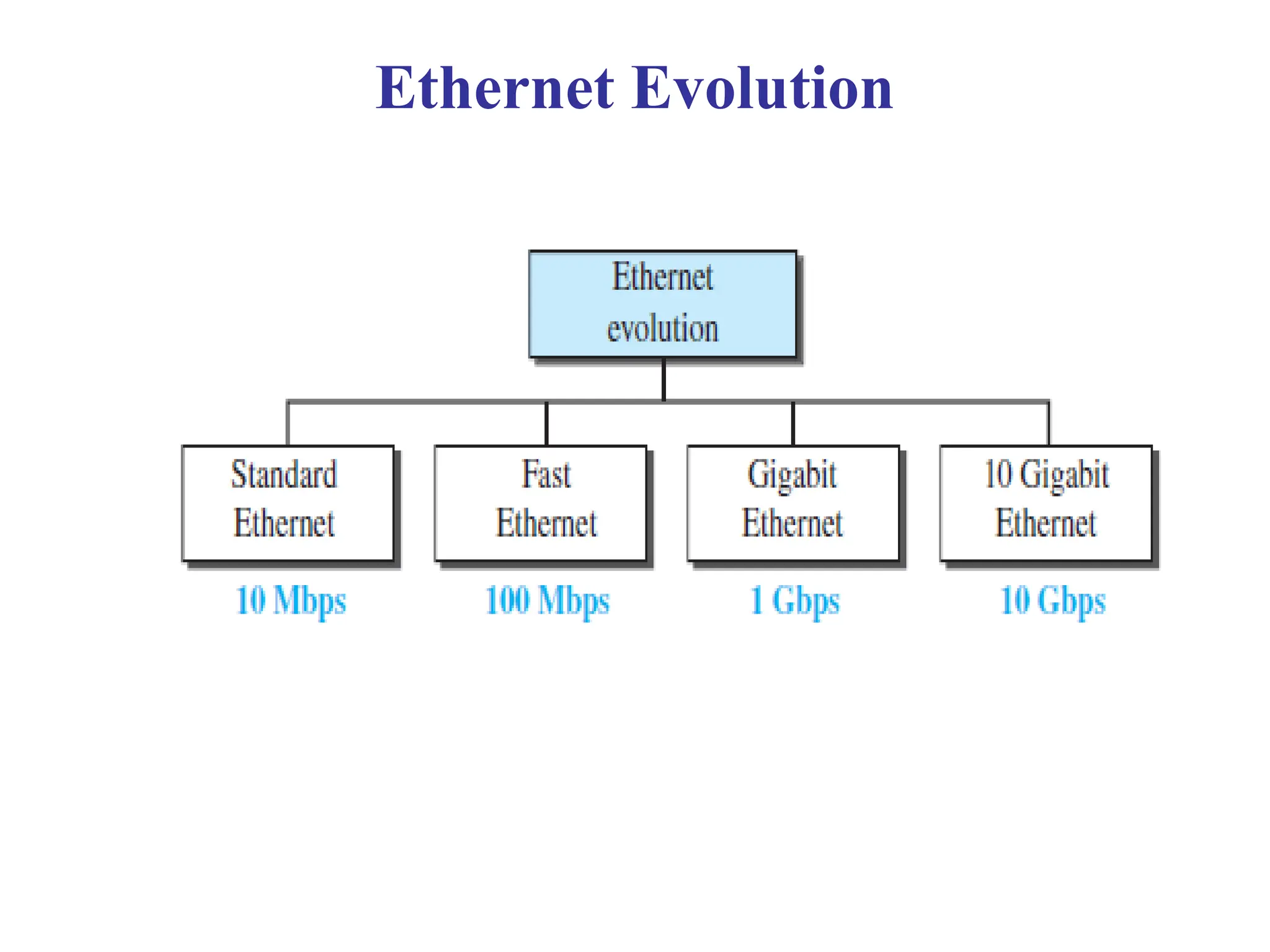
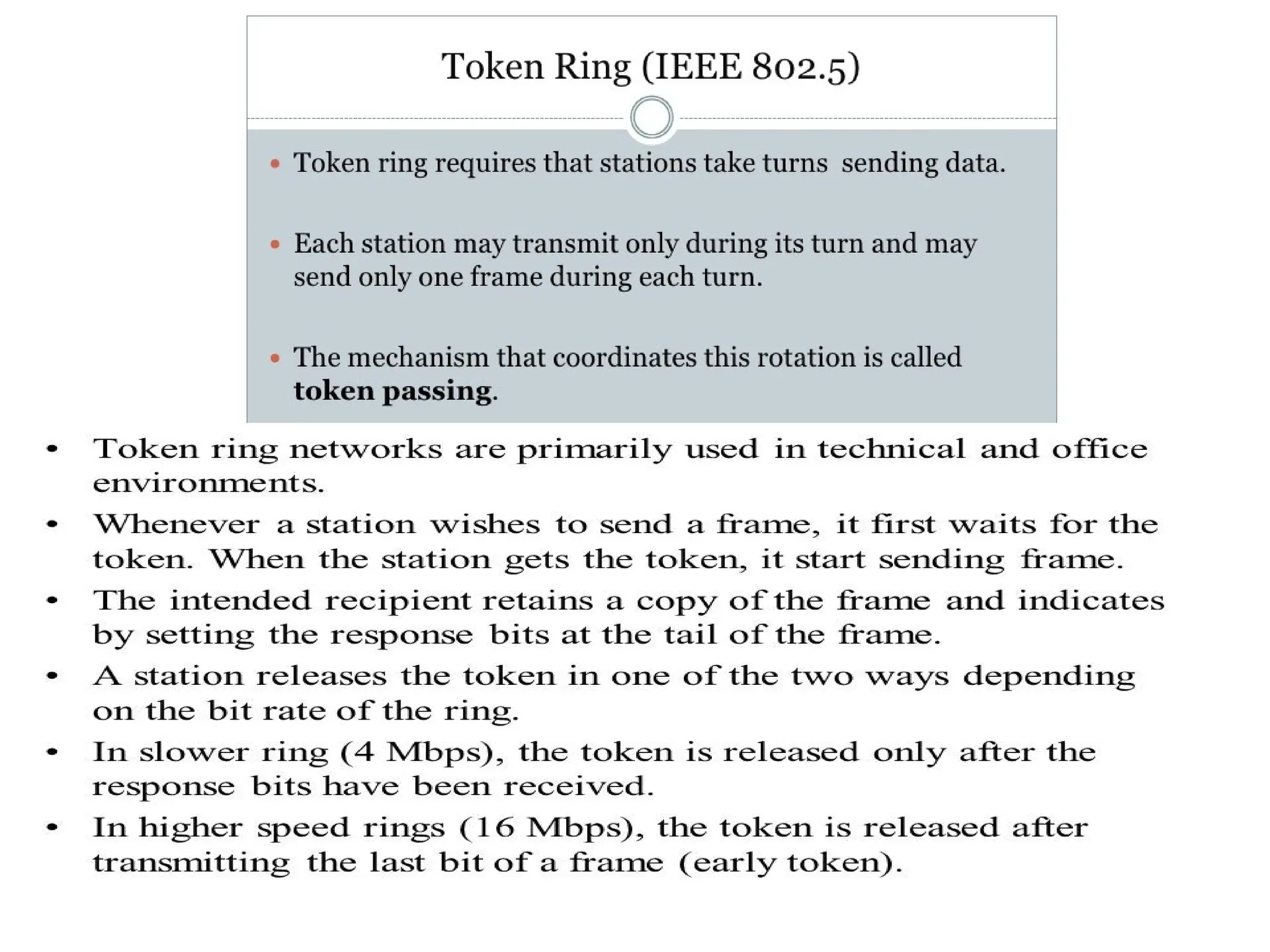
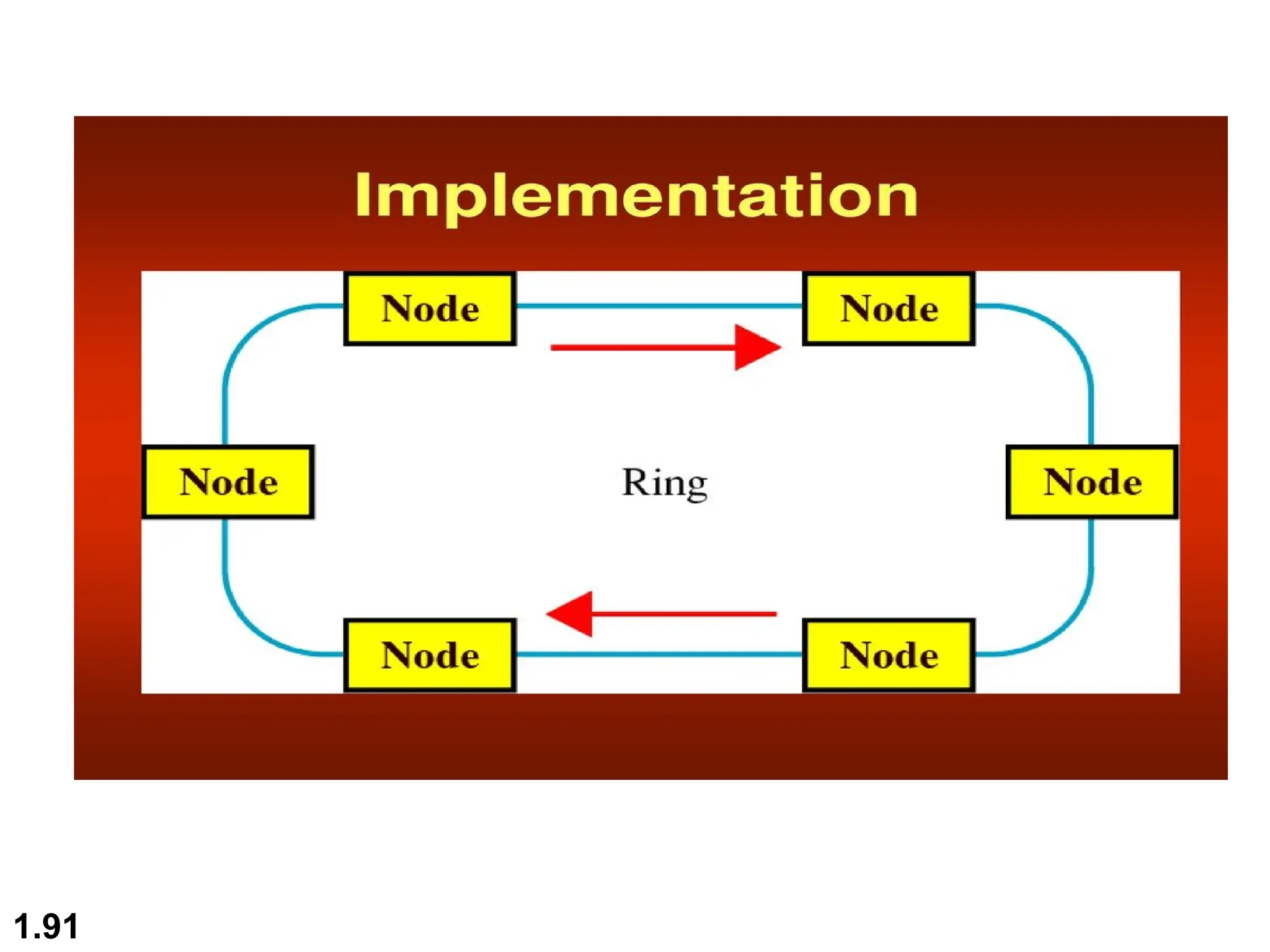
The document provides an overview of data communications, outlining fundamental characteristics such as delivery, accuracy, and timeliness, and describes various data representation forms (text, numbers, images, audio, video). It details different transmission modes (simplex, half-duplex, full-duplex) and network topologies (mesh, star, bus, ring, hybrid), their advantages and disadvantages. Additionally, it introduces protocols governing data communications and classes of networks like LANs, WANs, and MANs.
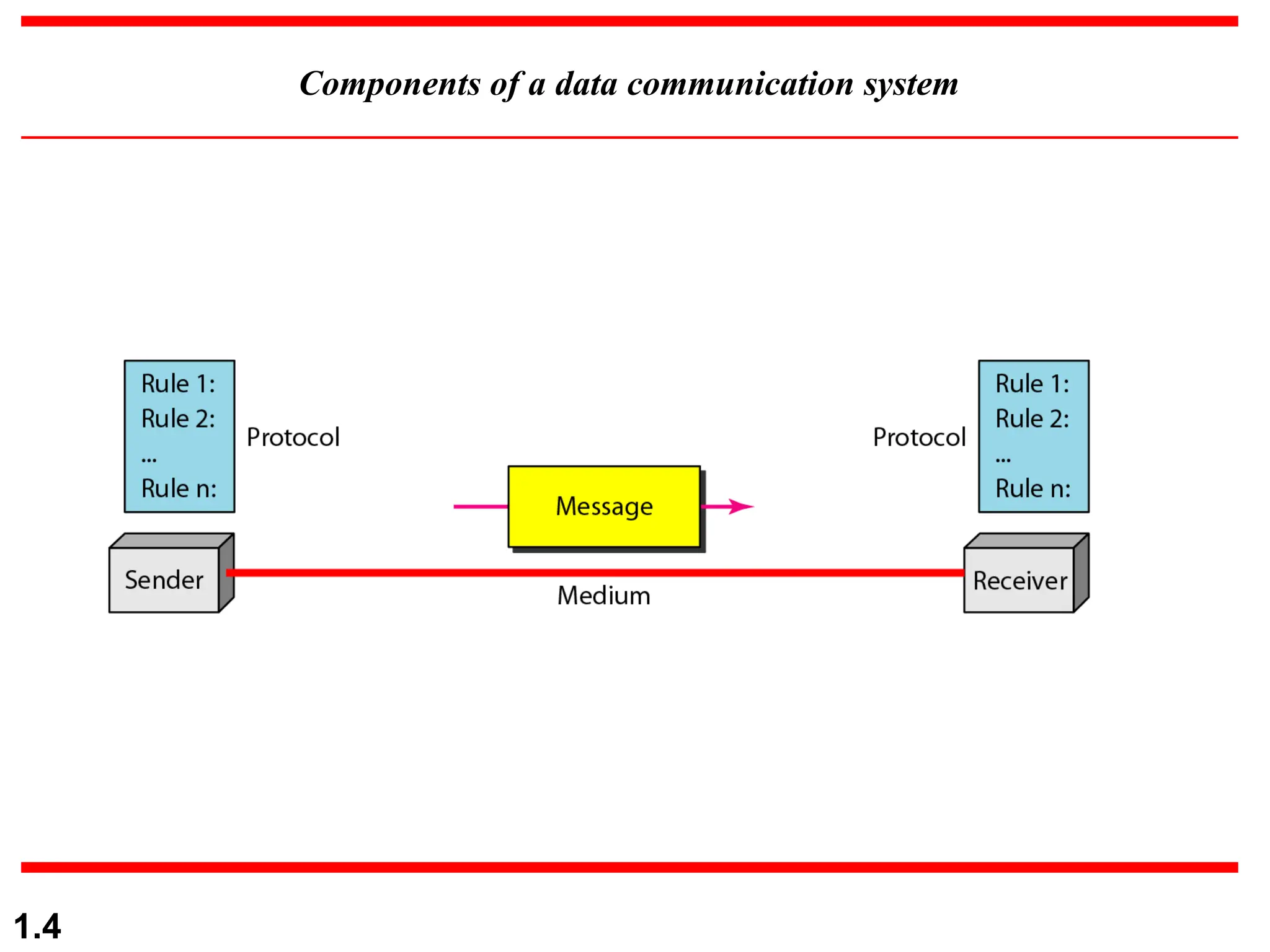



![MESH TOPOLOGY
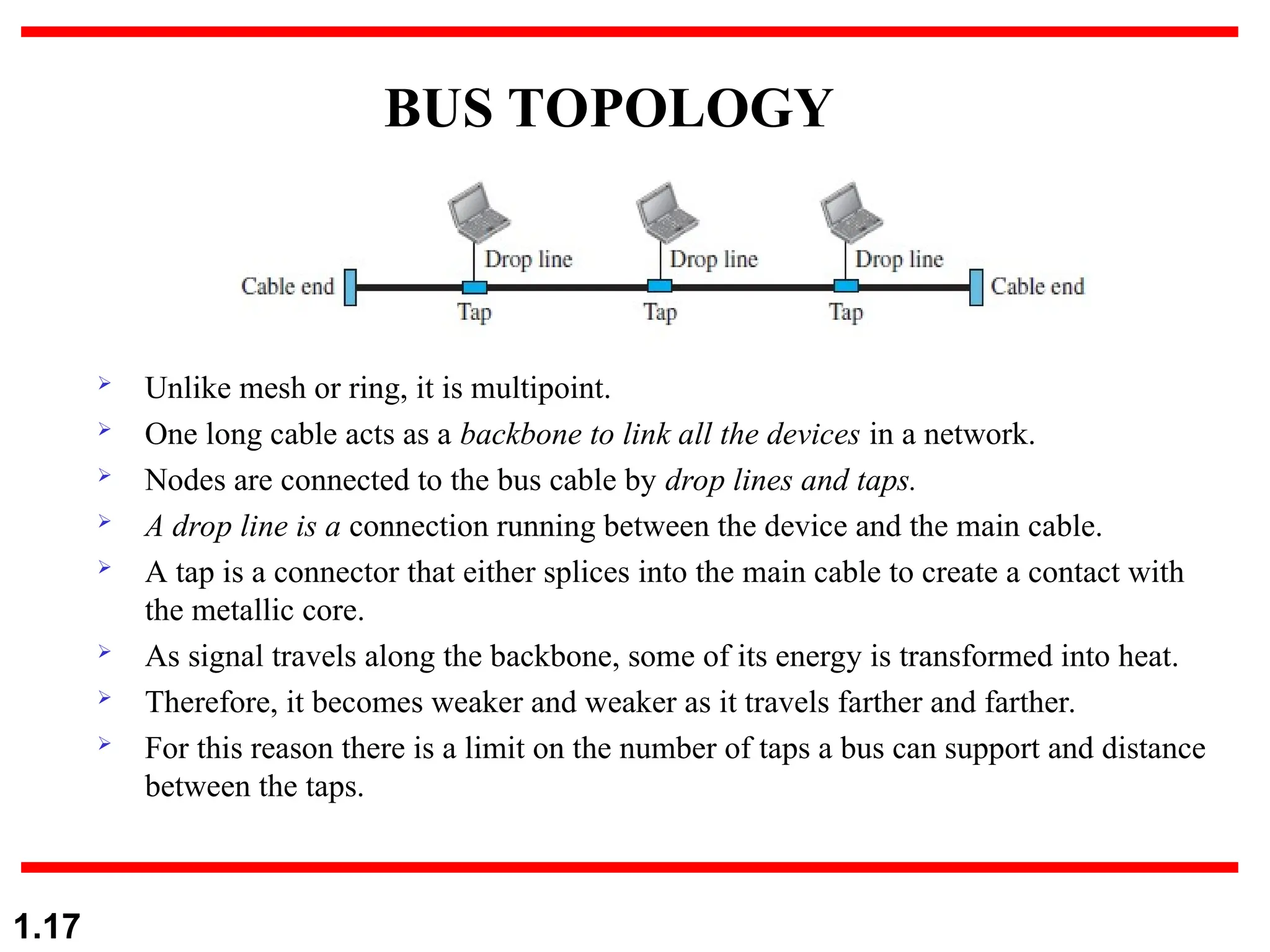
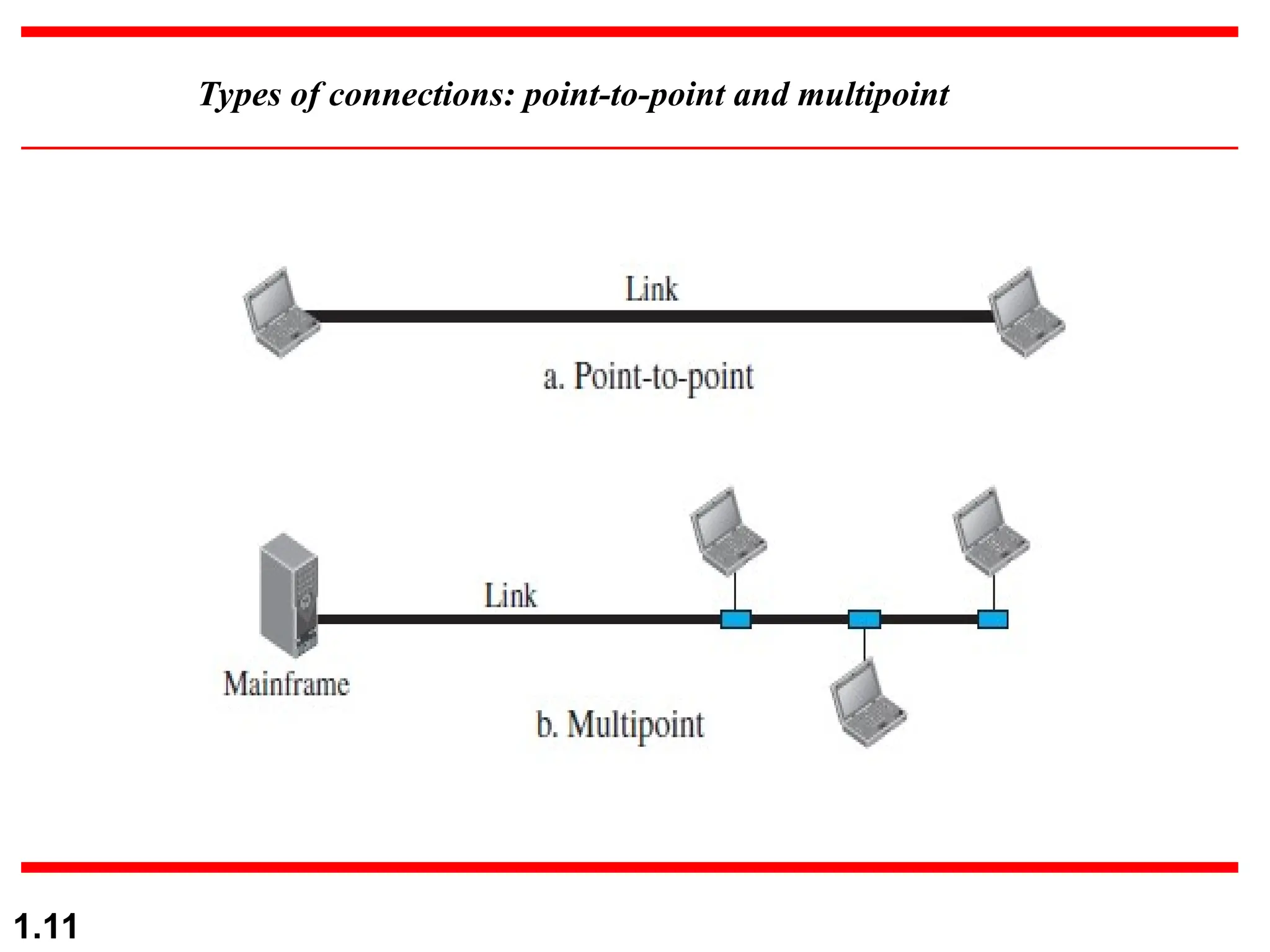
Each device has a dedicated point-
to-point link to every other device.
The term dedicated means that the
link carries traffic only between the
two devices it connects.
A mesh network with n nodes has
n(n-1) links [ n(n-1) / 2 in case of
duplex ].
The use of dedicated links
eliminates traffic problems that
occur when link is shared.
A mesh topology is robust.
If one link becomes unusable, it
does not incapacitate the entire
system. Privacy or security is
maintained.
1.13](https://image.slidesharecdn.com/uniti-250106075404-a9b1819a/75/OSI-LAYERS-FUNCTIONS-TOPOLOGIES-LAN-WAN-AND-METROPOLITAN-NETWORK-13-2048.jpg)