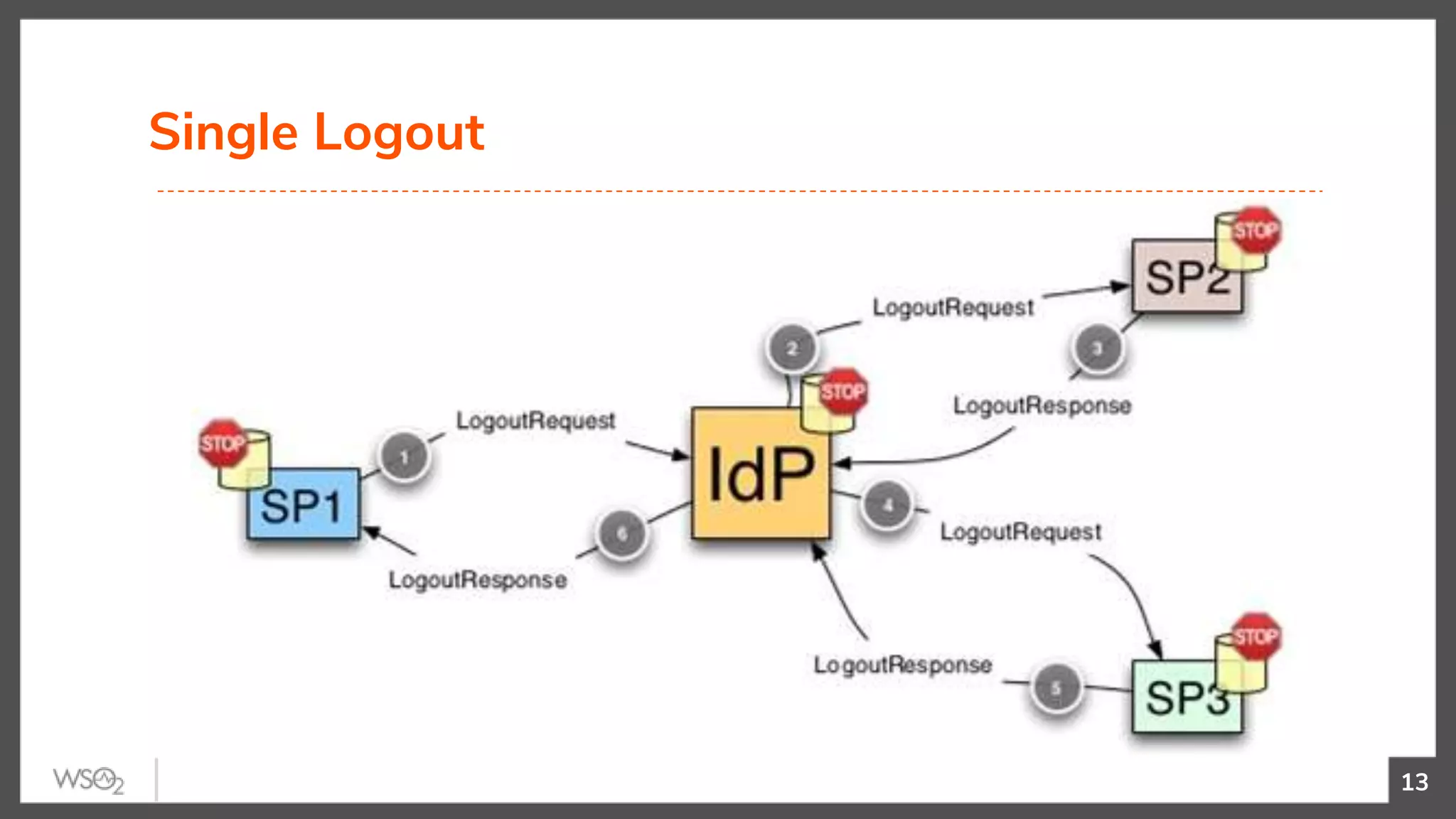
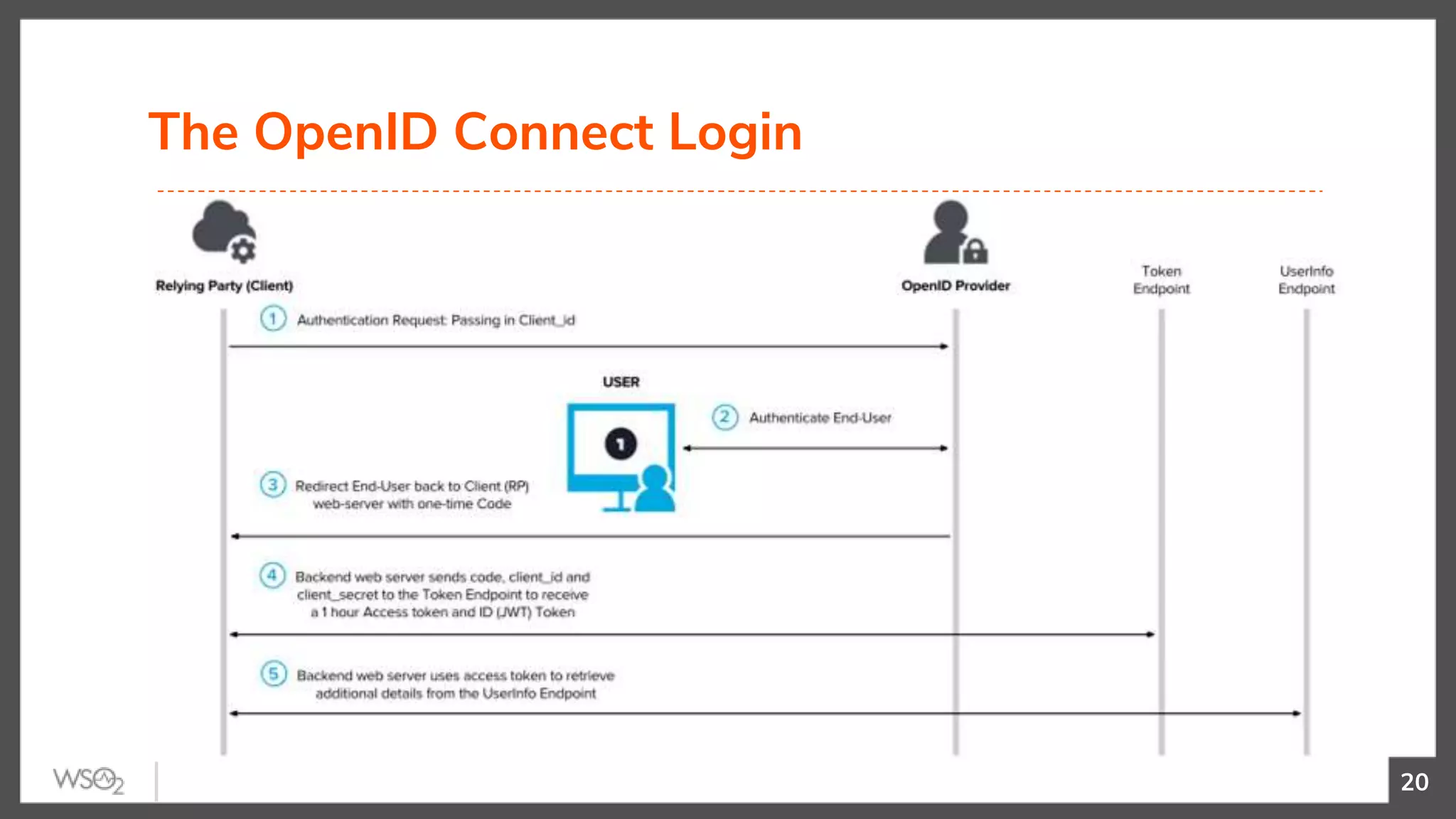
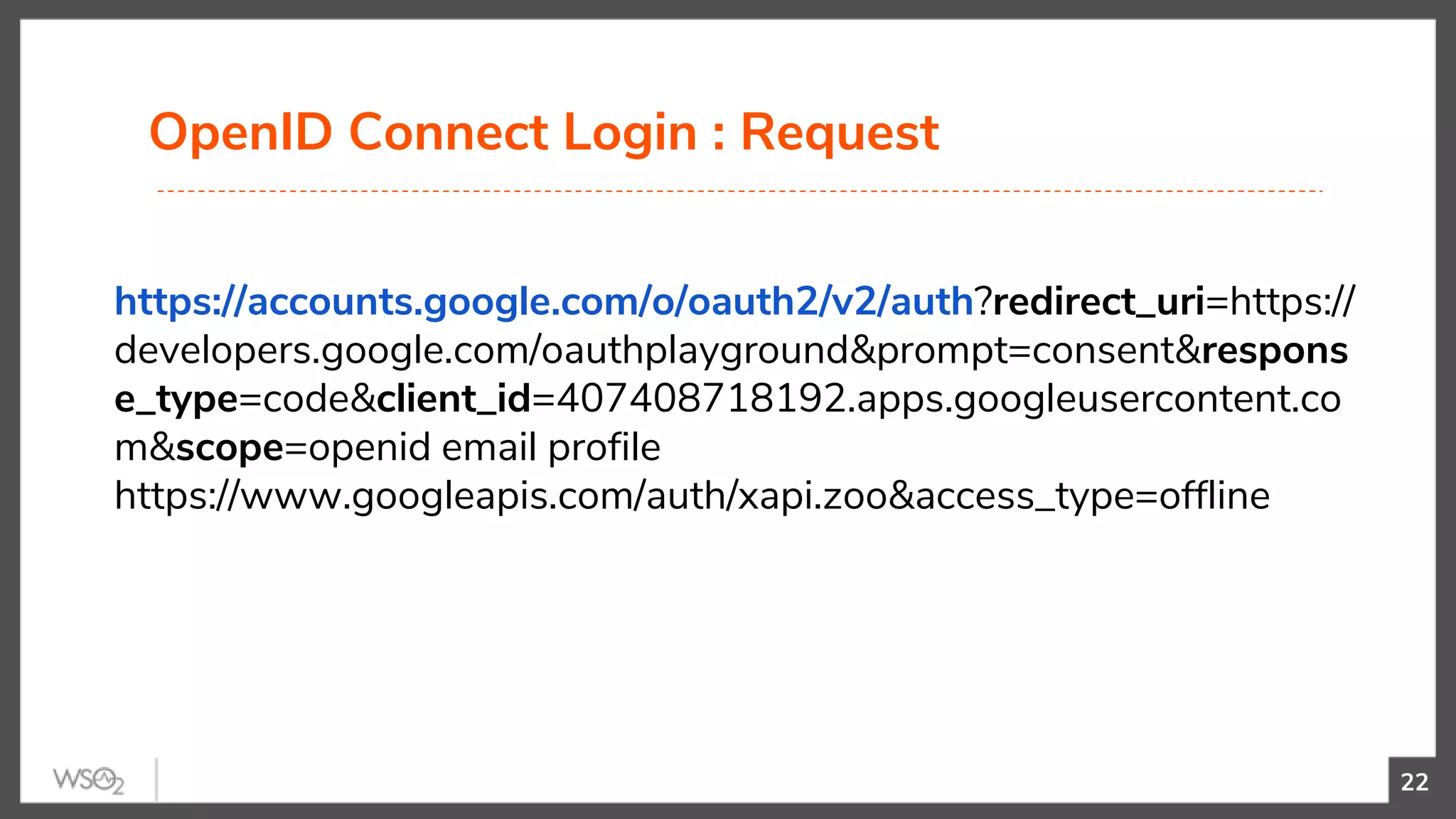
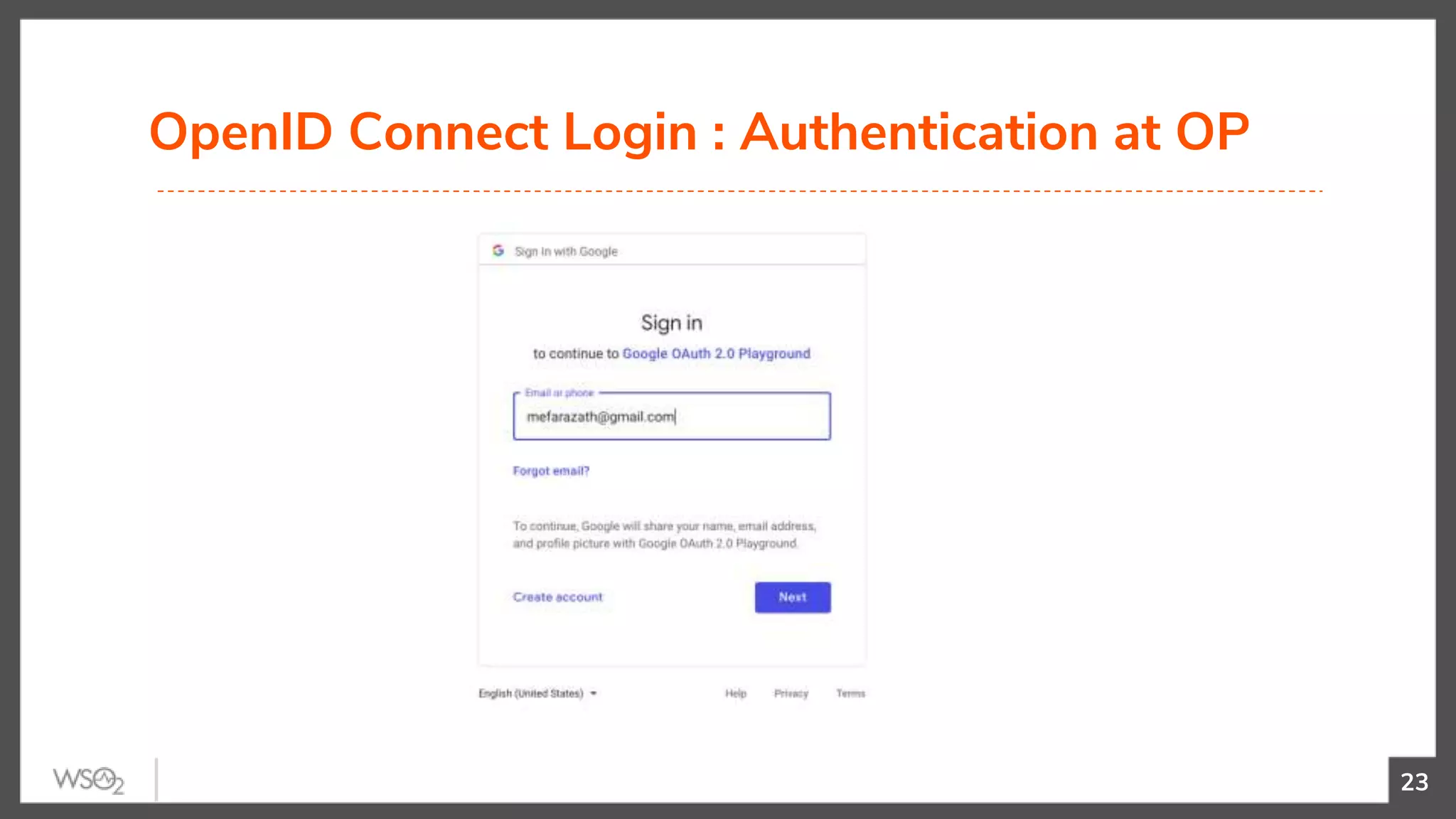
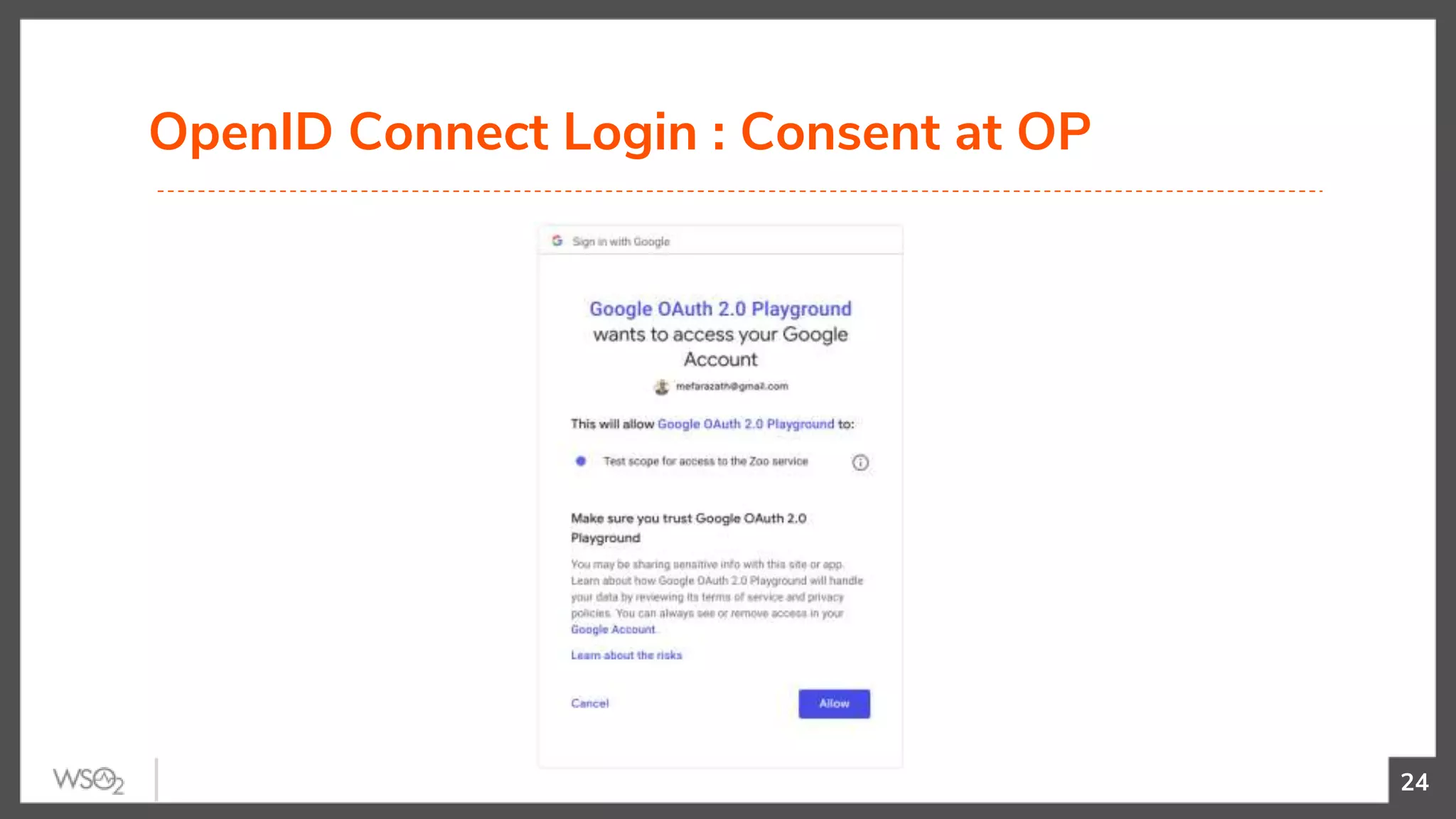
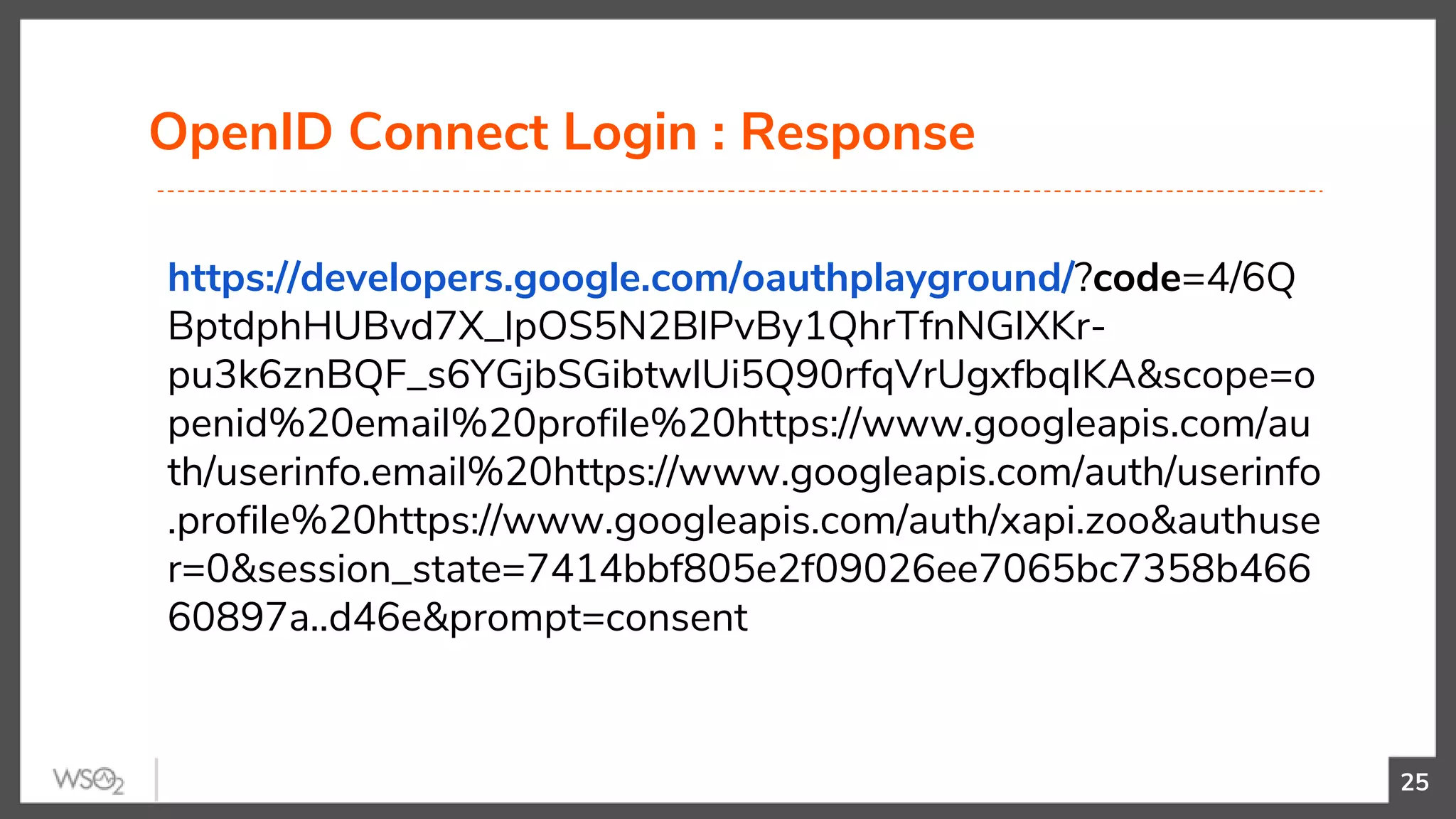
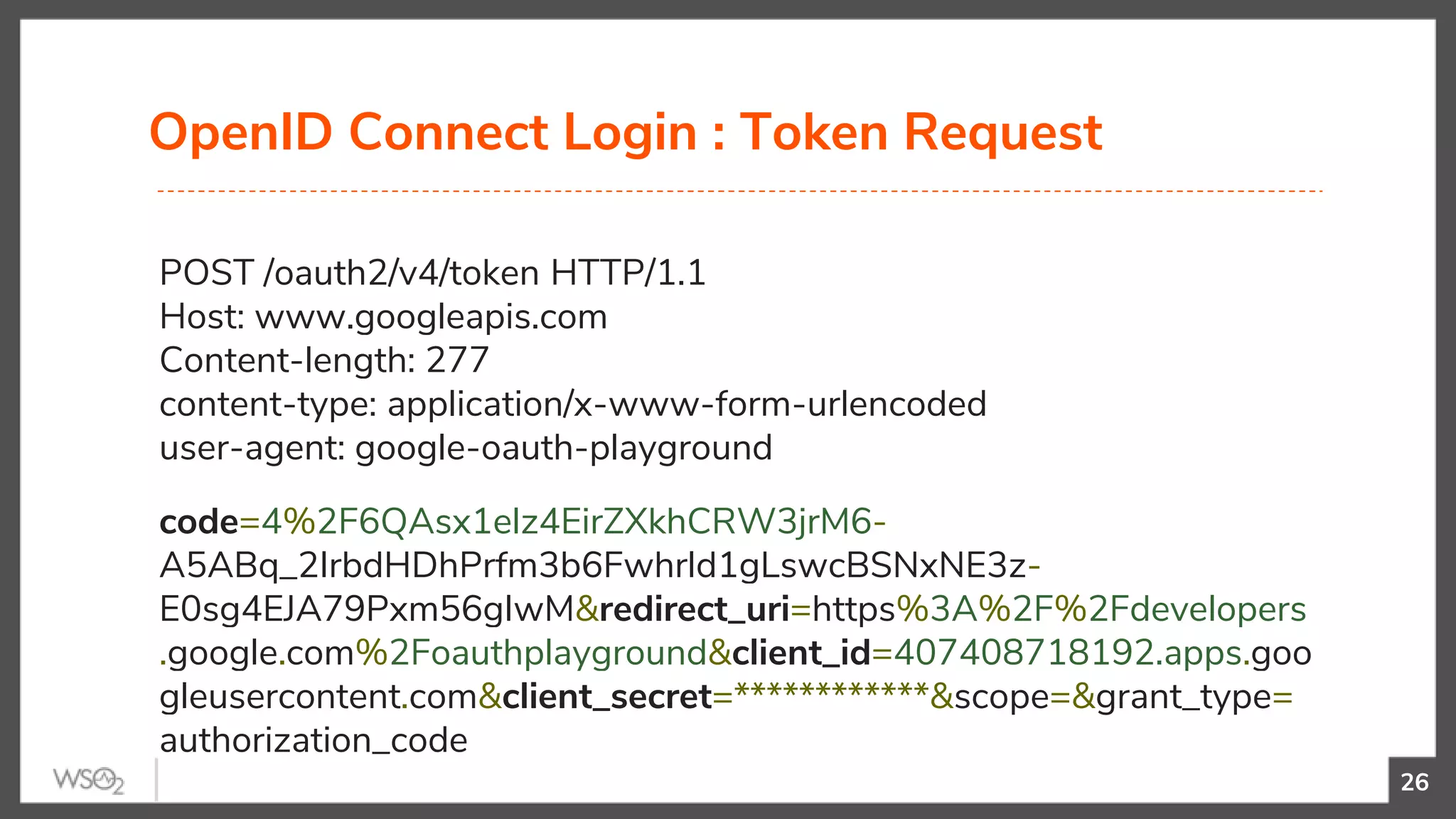
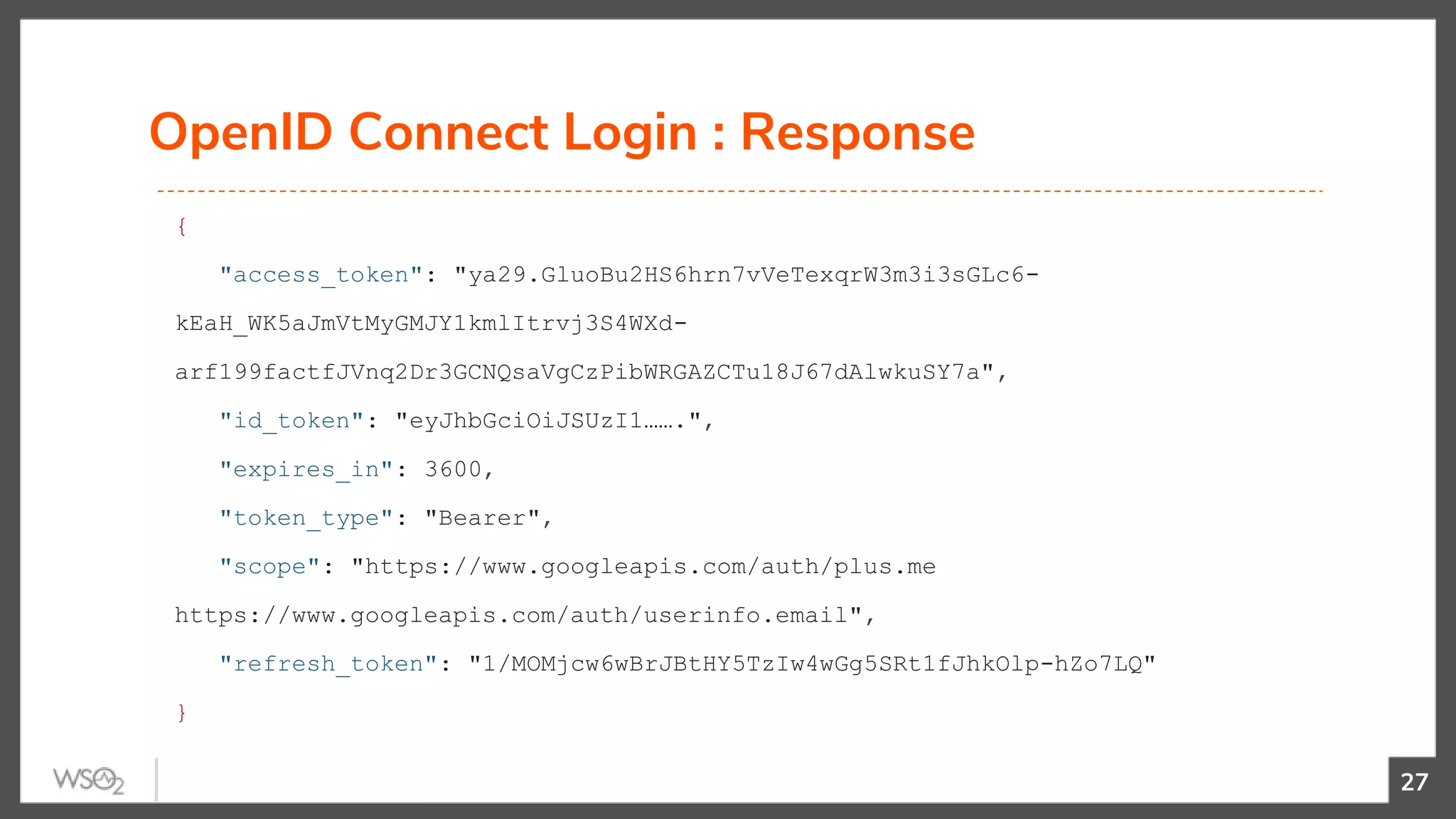
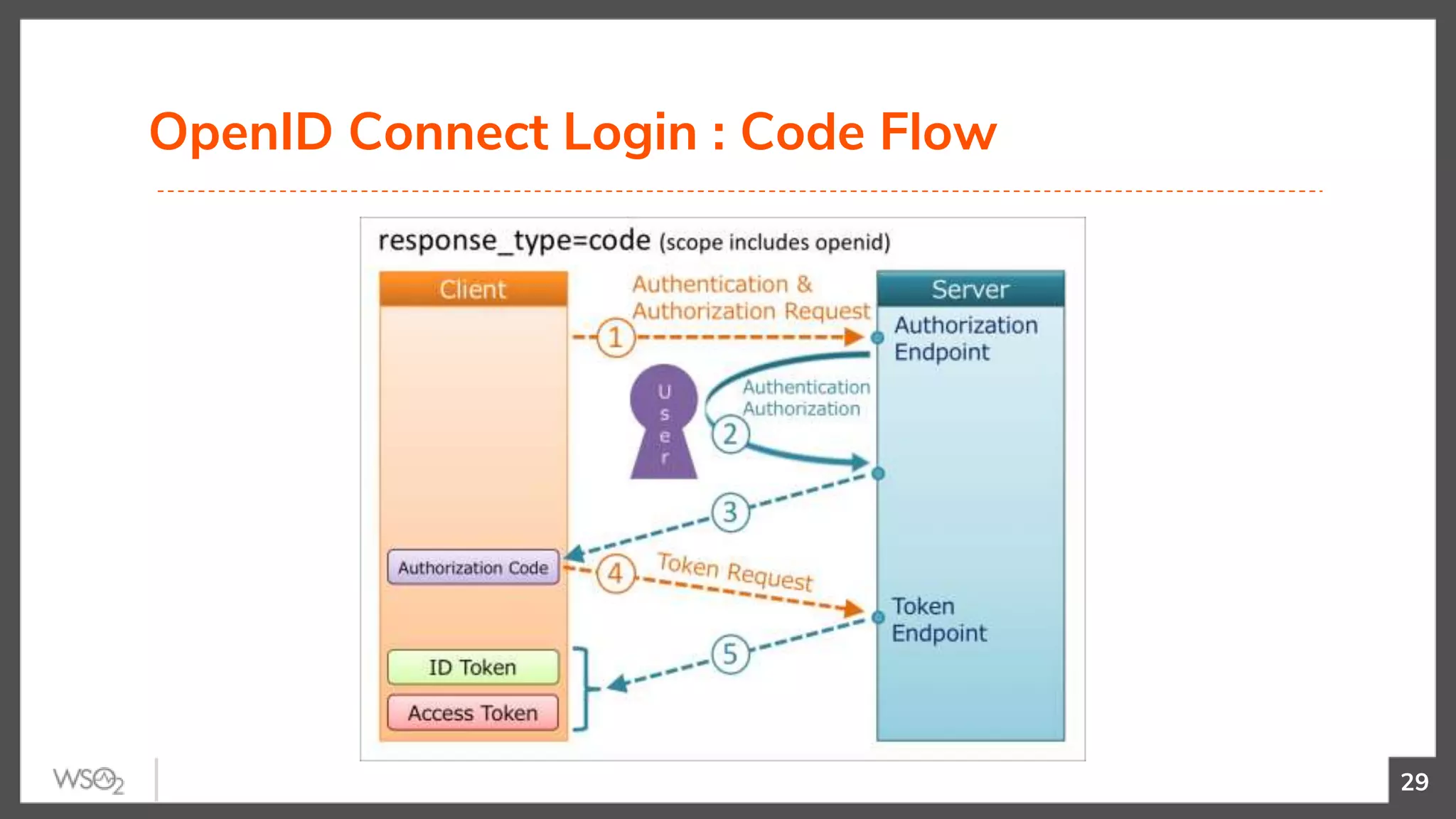
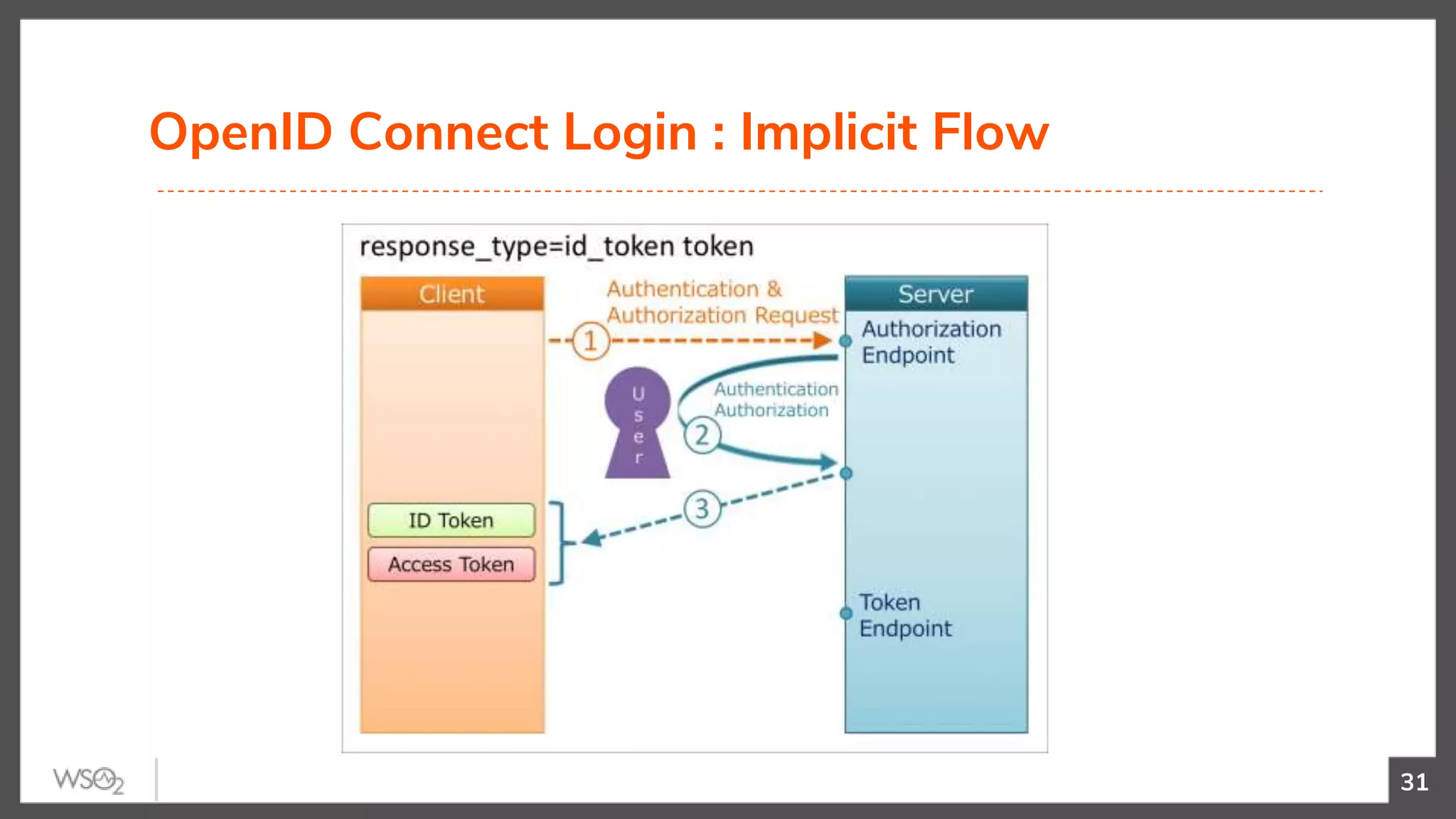
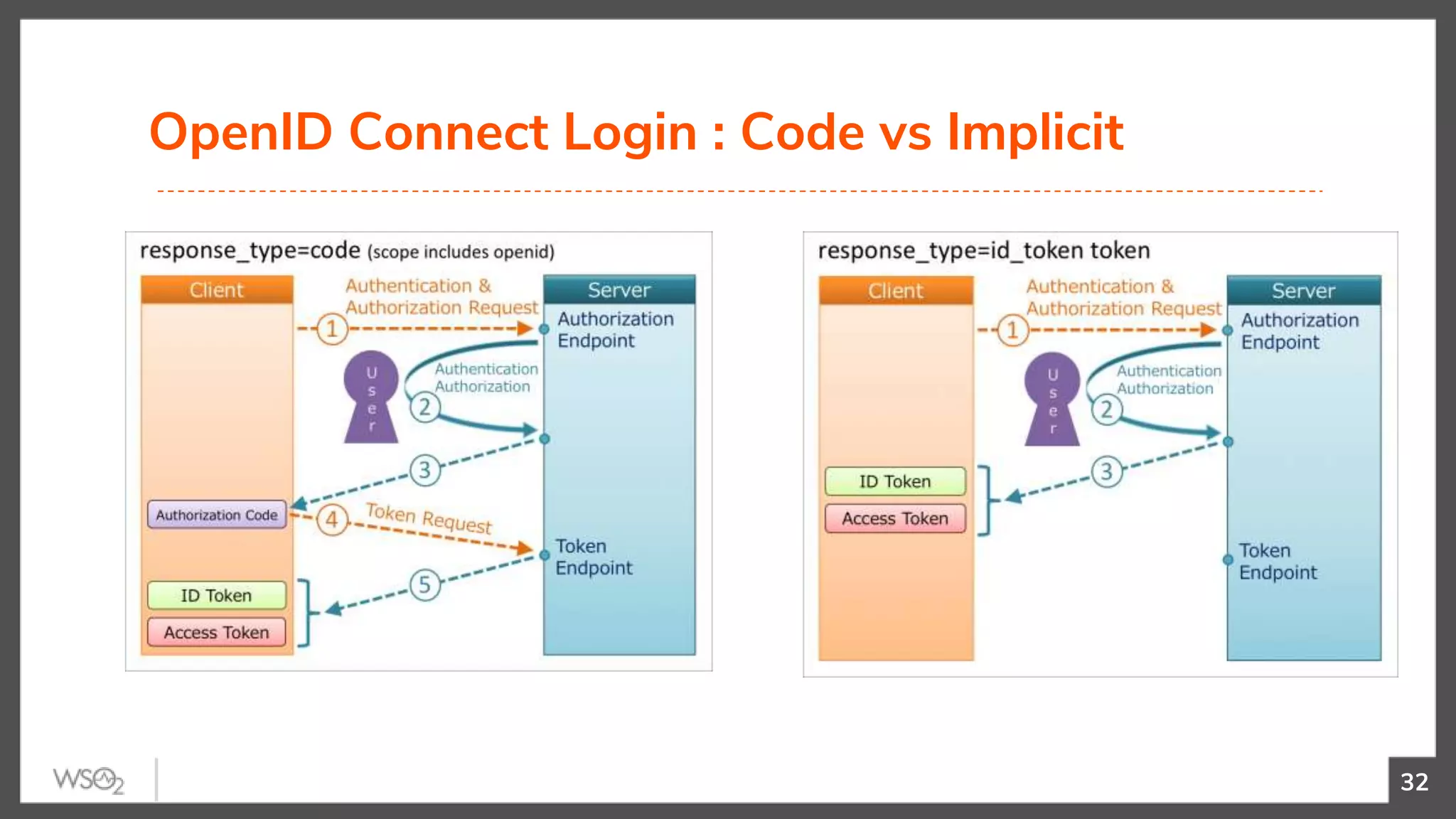
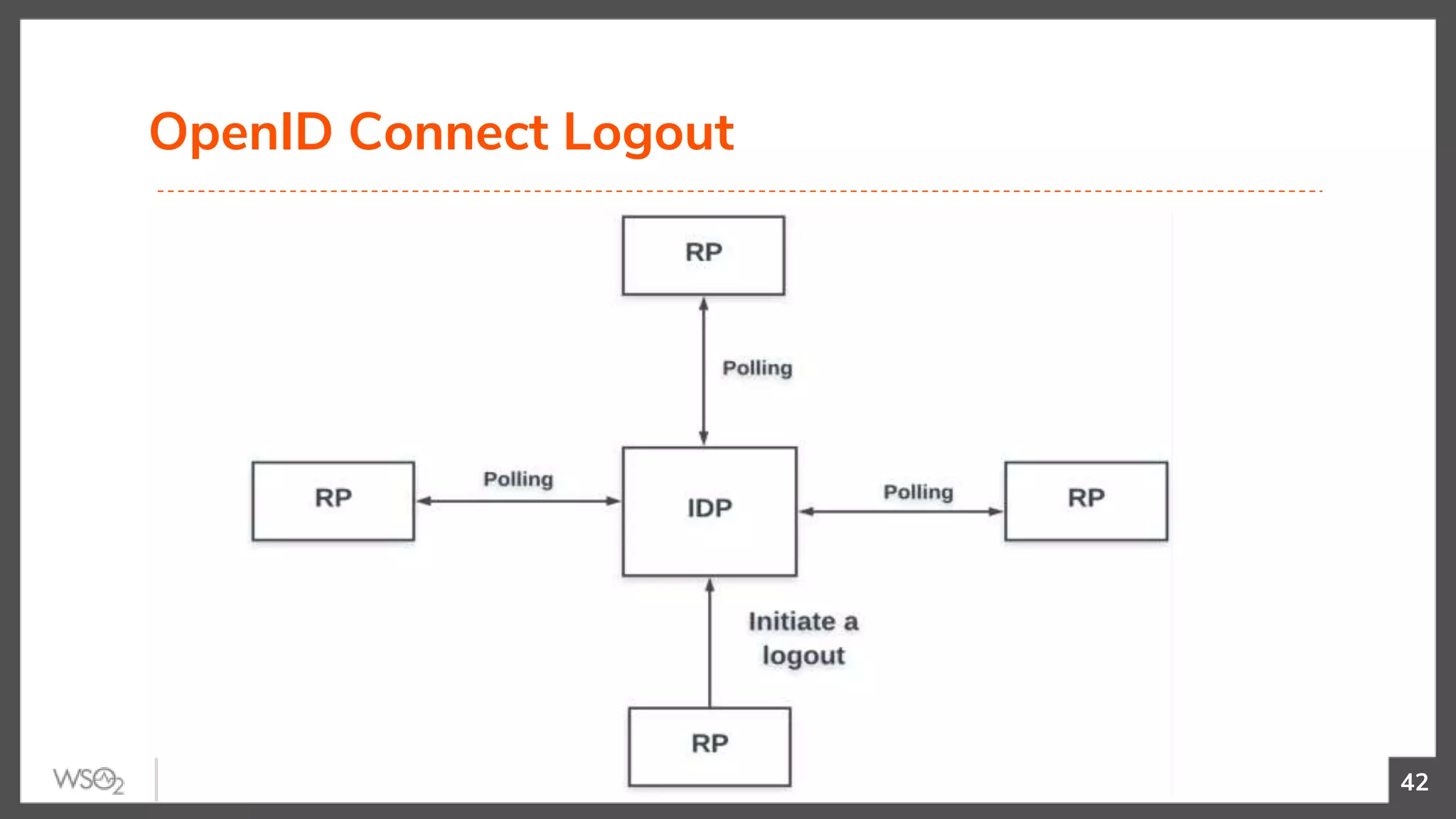
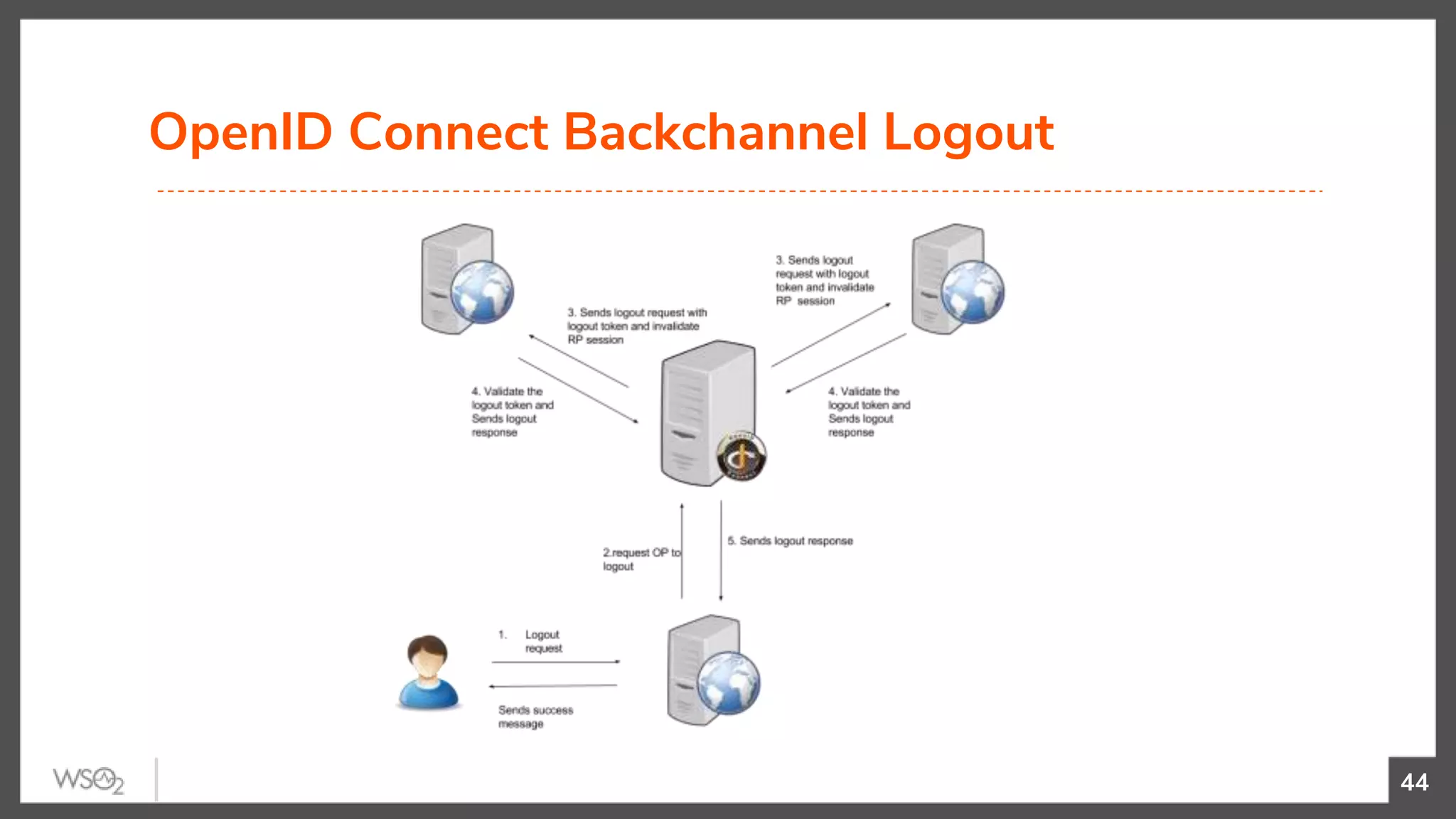
This document provides an overview of OpenID Connect, which is a standard protocol for user authentication and authorization. It describes how OpenID Connect provides a secure login mechanism for applications by defining standard APIs for authentication, authorization, single sign-on, and single logout. The document explains the OpenID Connect flow, advantages of using the standard, and security aspects like signed JSON Web Tokens and preventing request tampering. It also discusses solutions built on OpenID Connect and tips for application developers in implementing authentication securely.