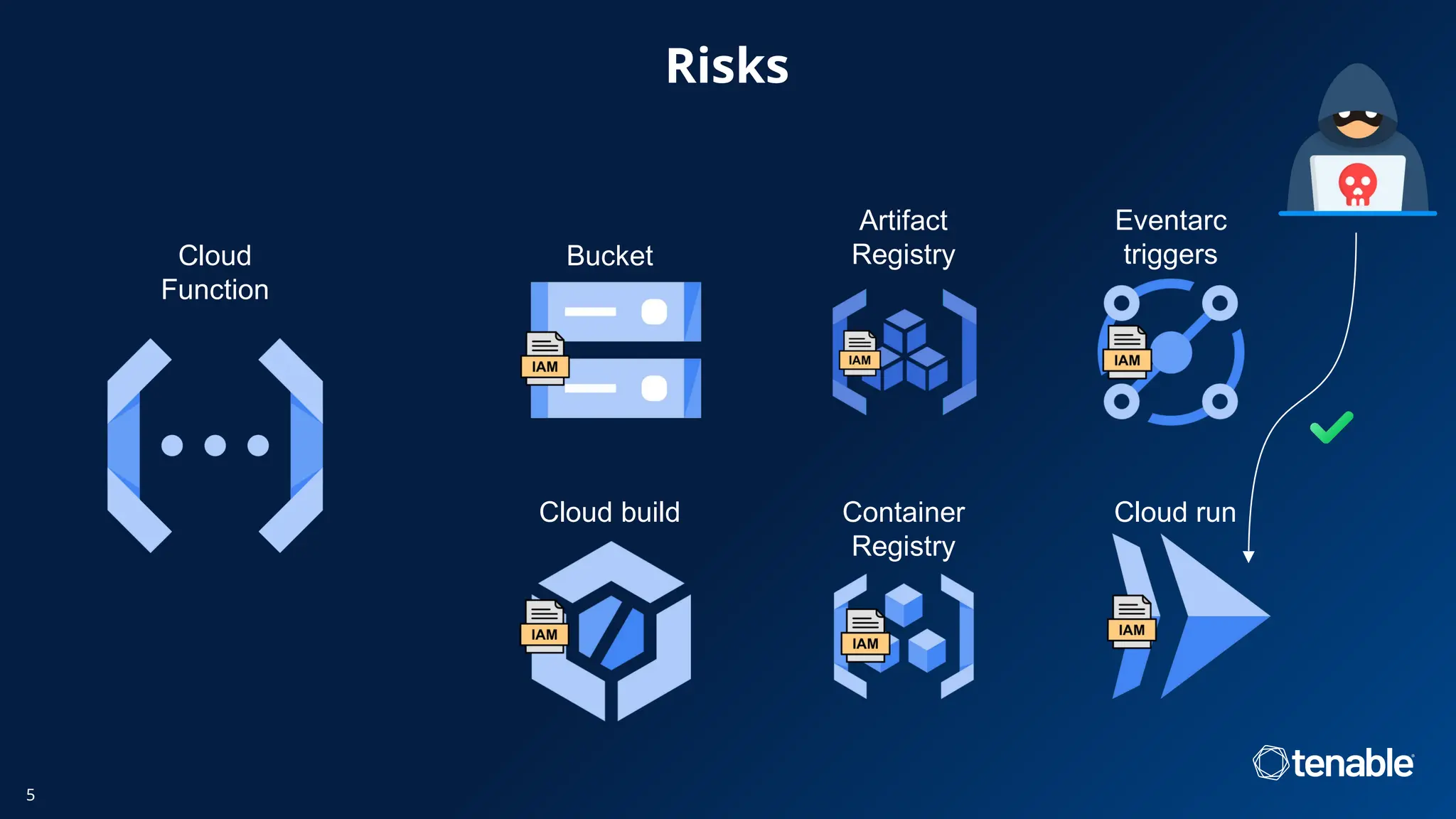
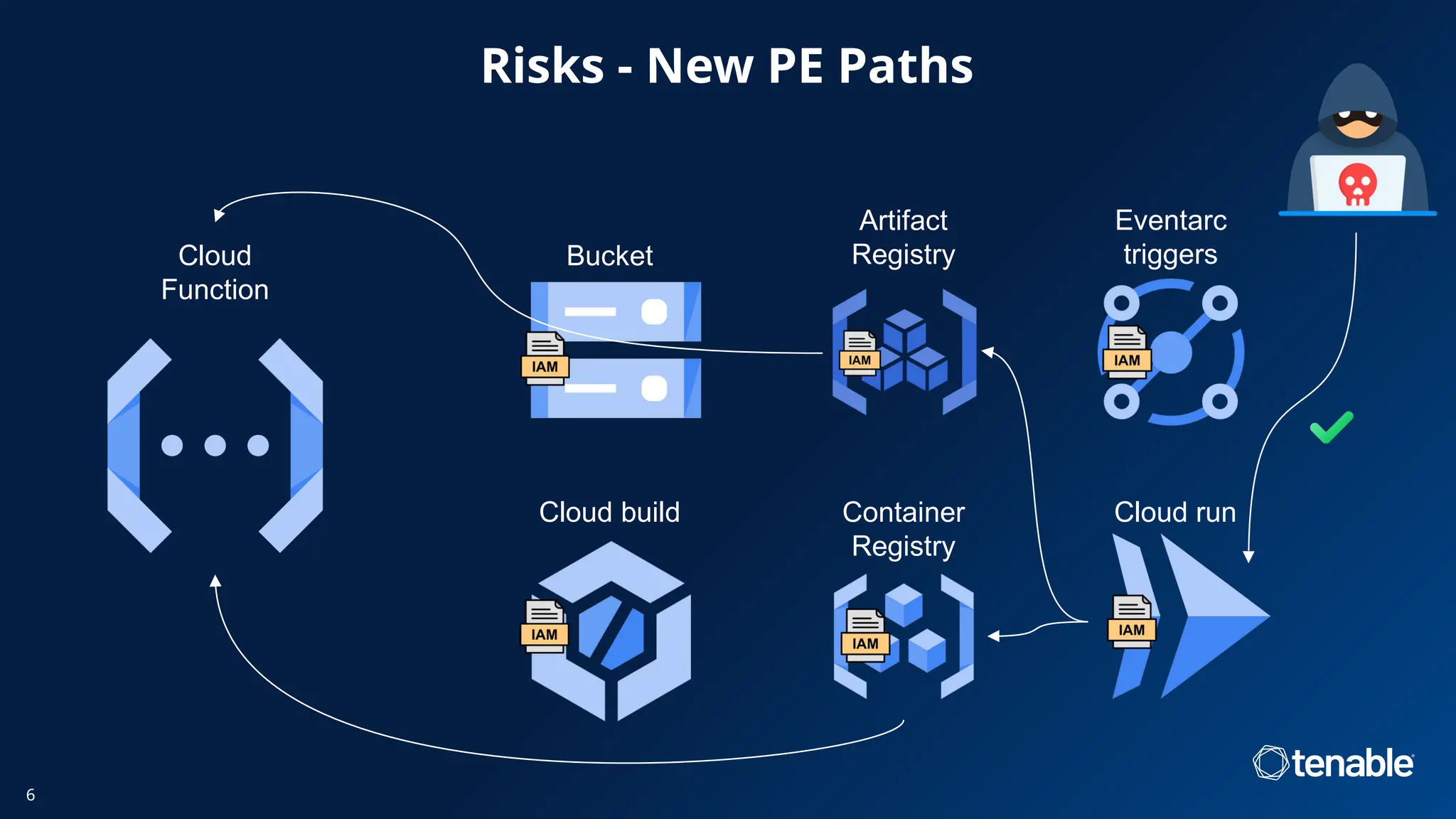
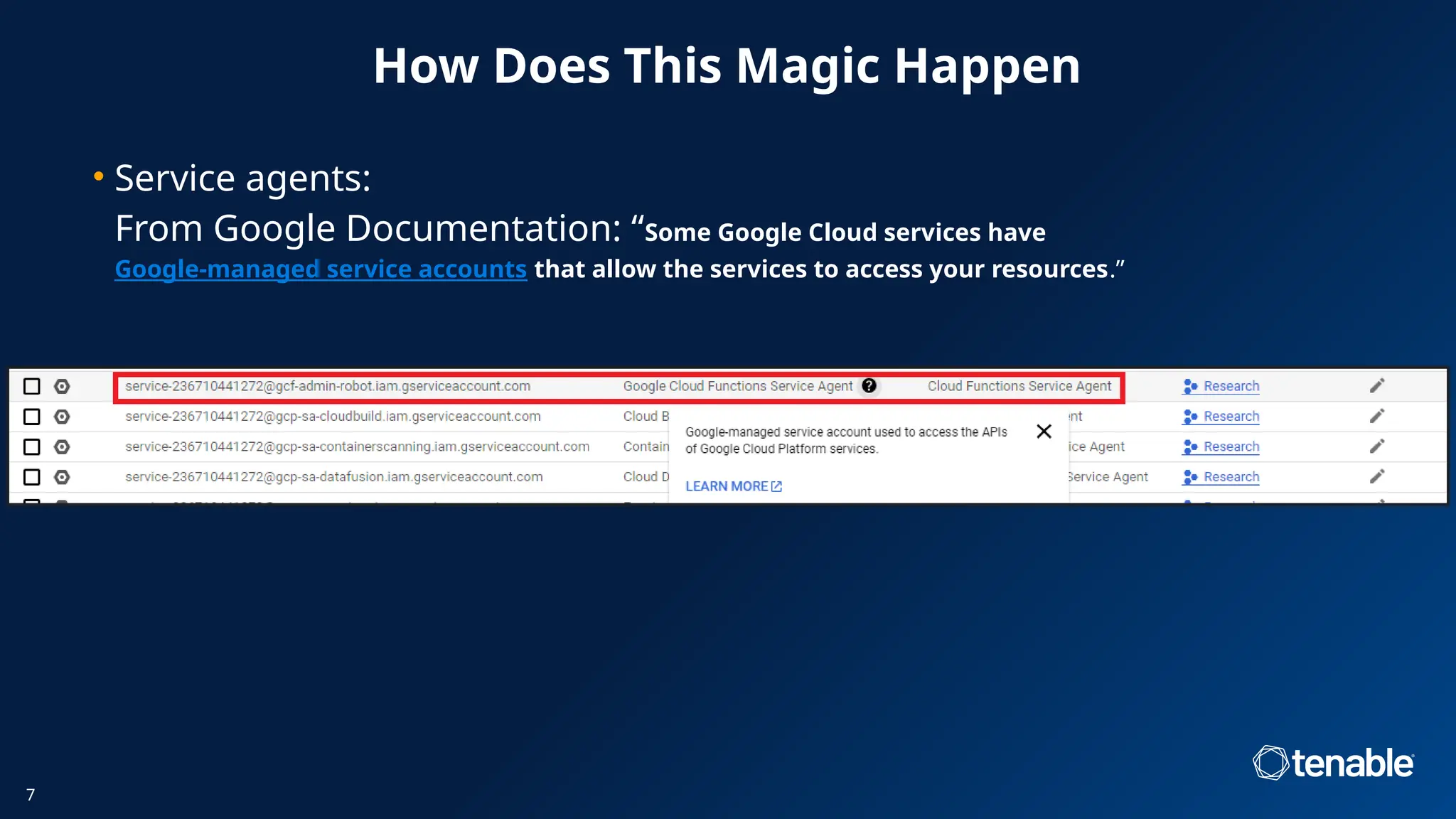
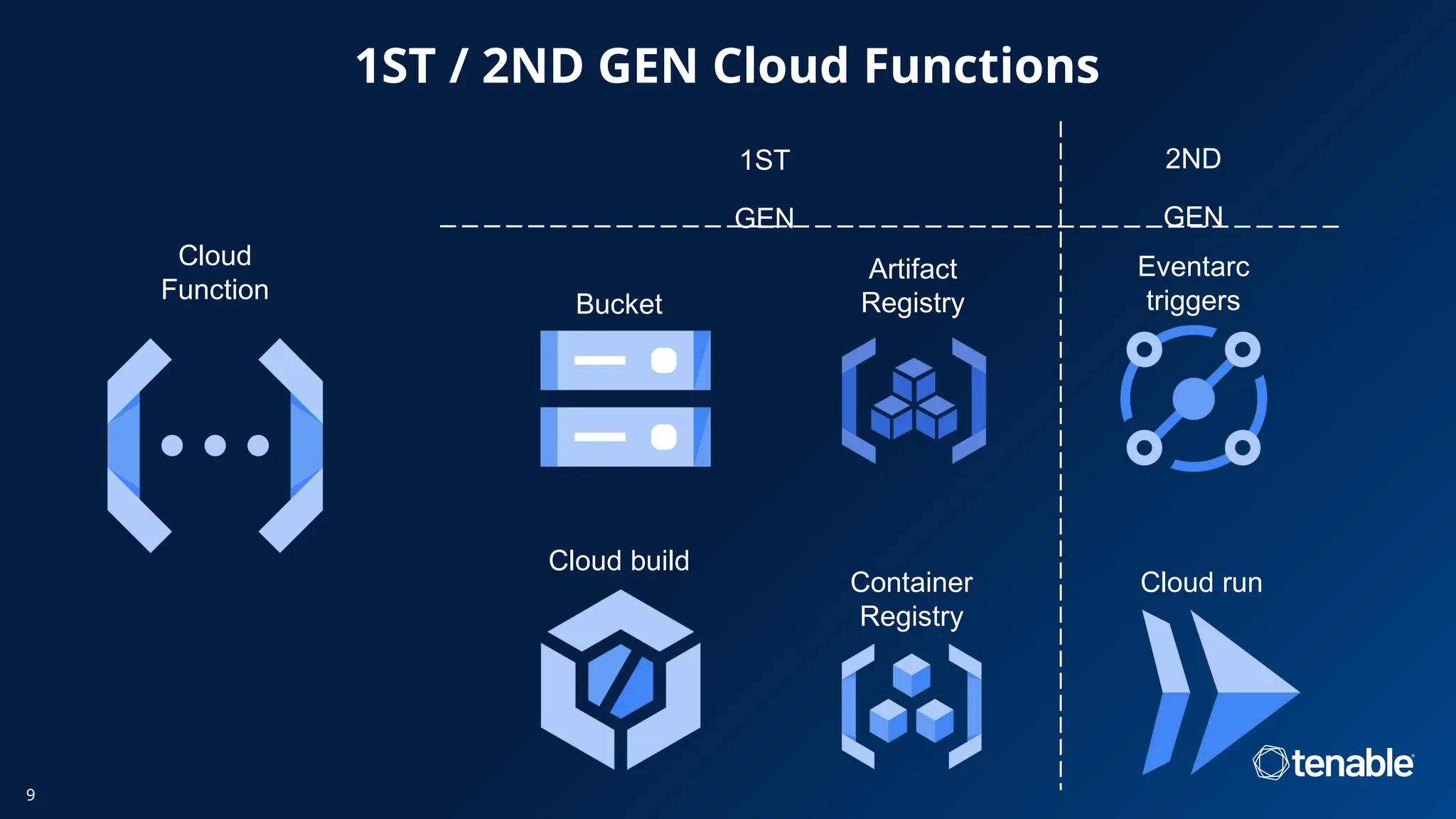
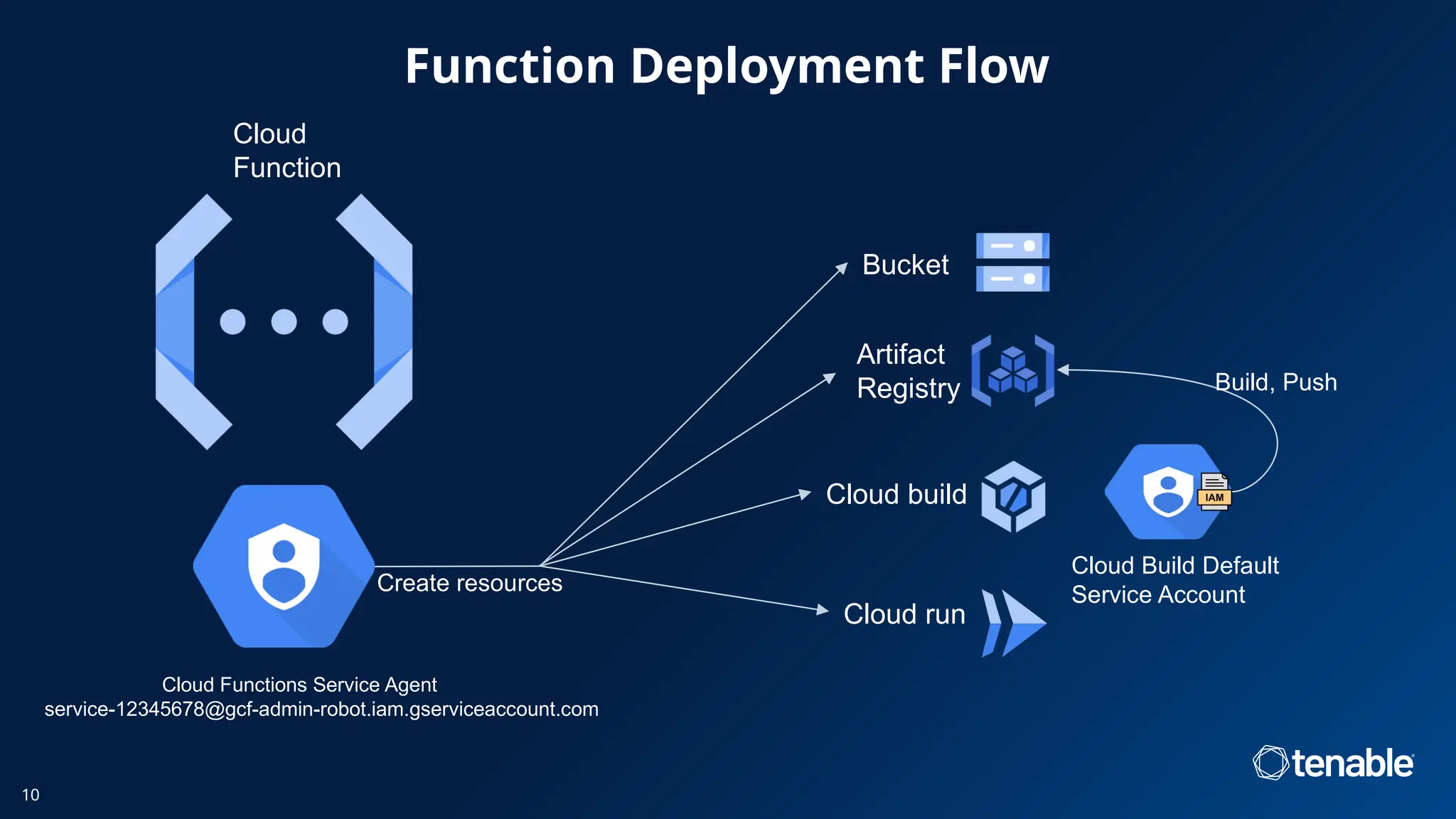
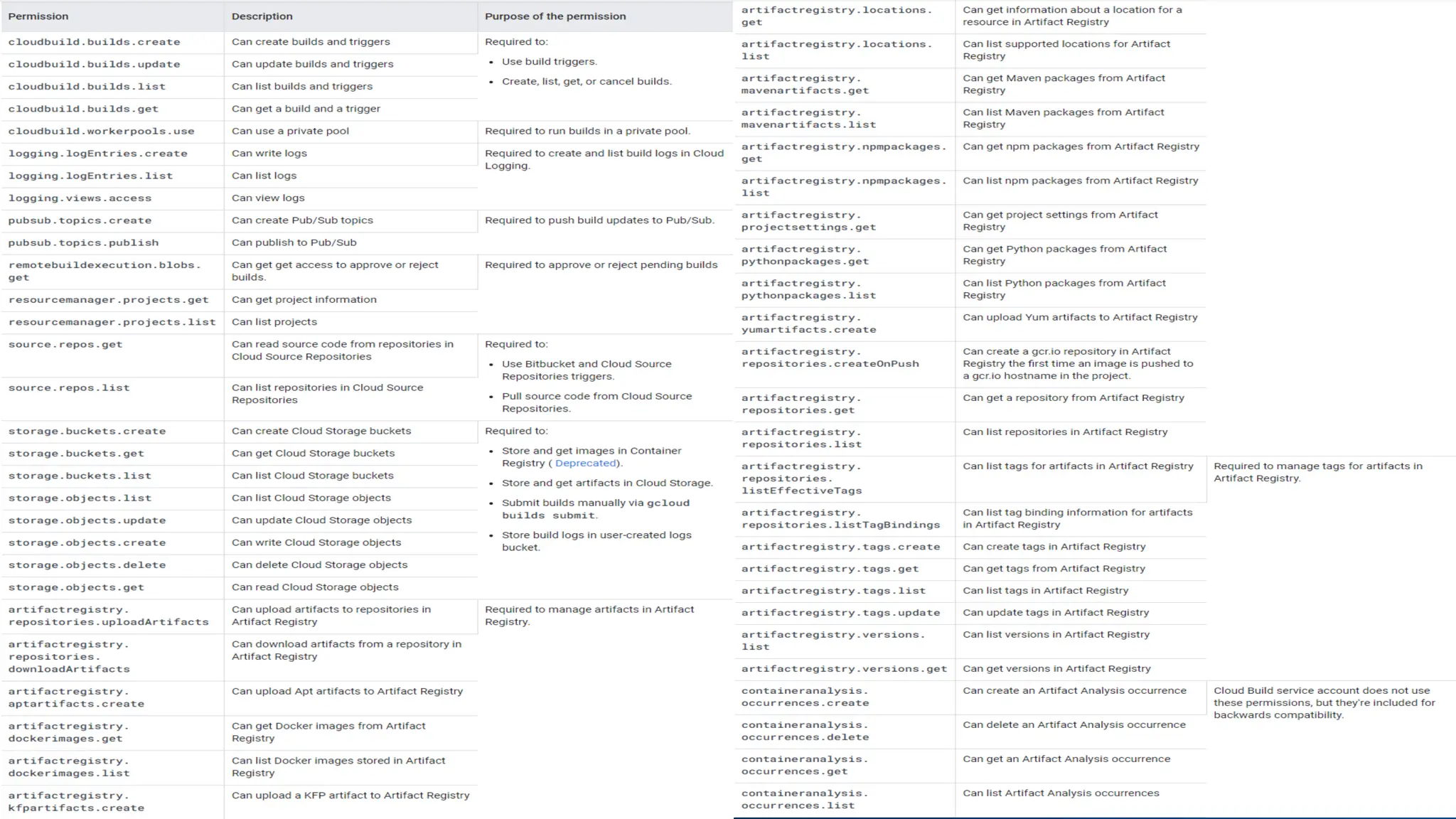
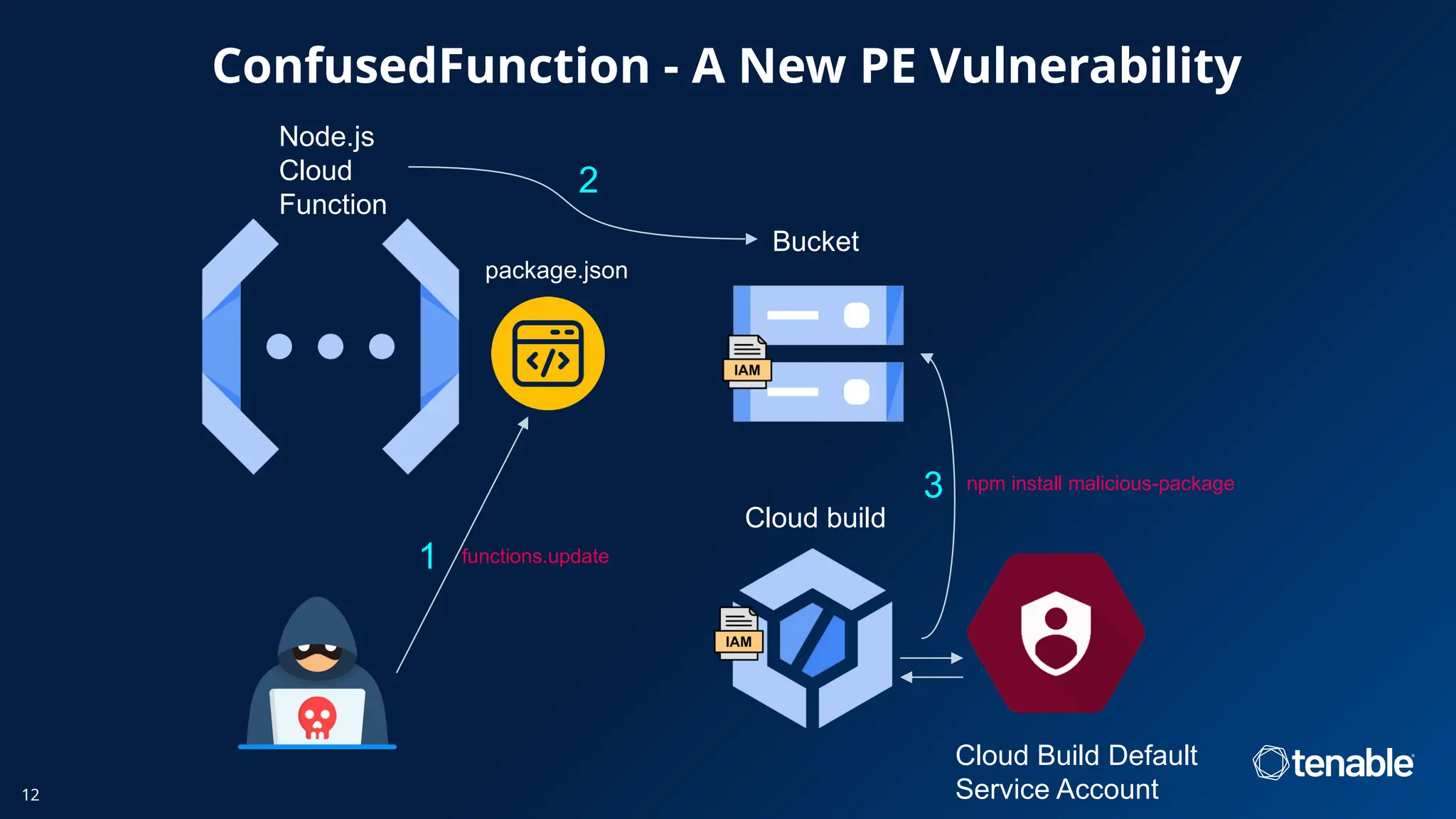
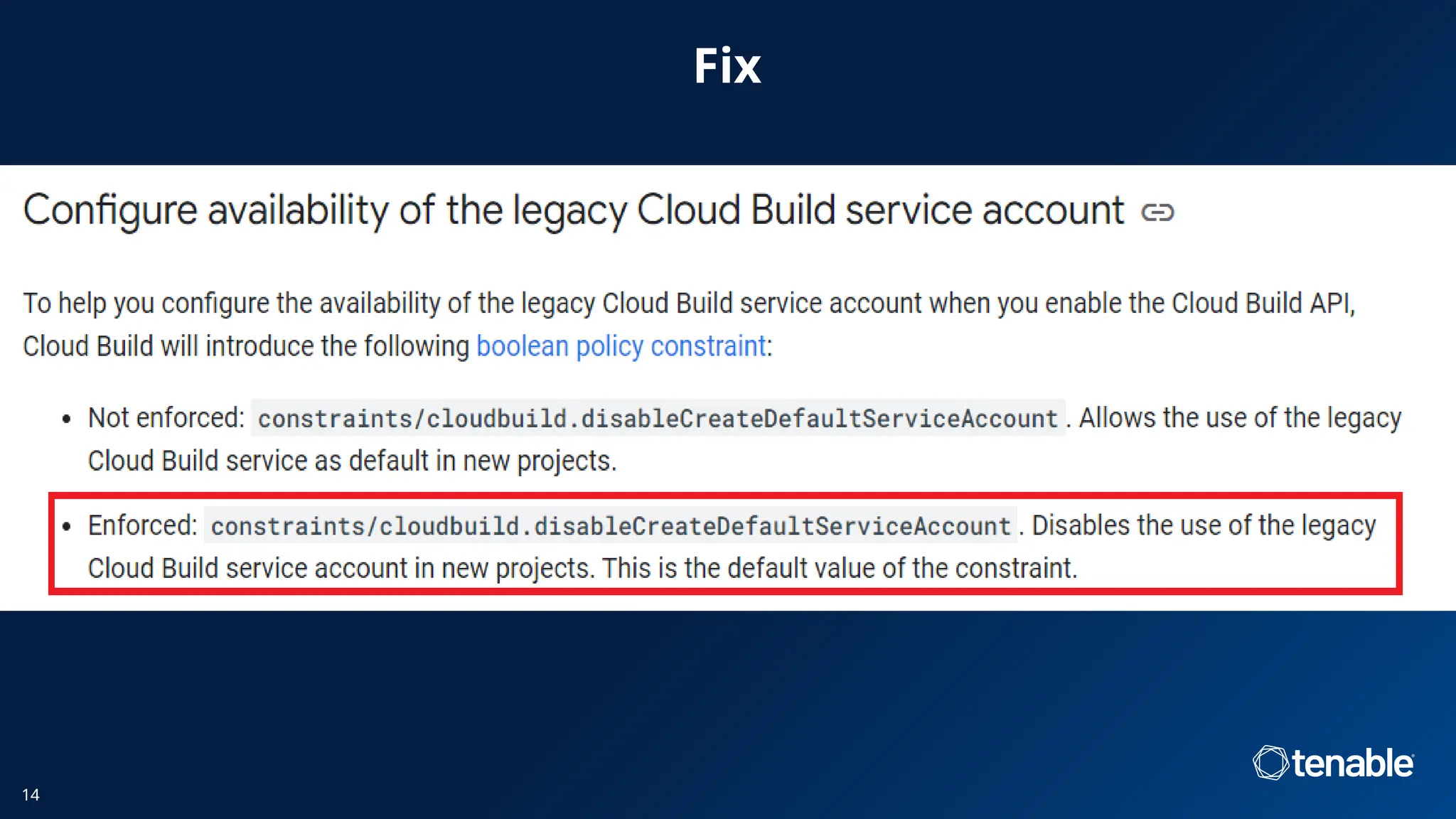
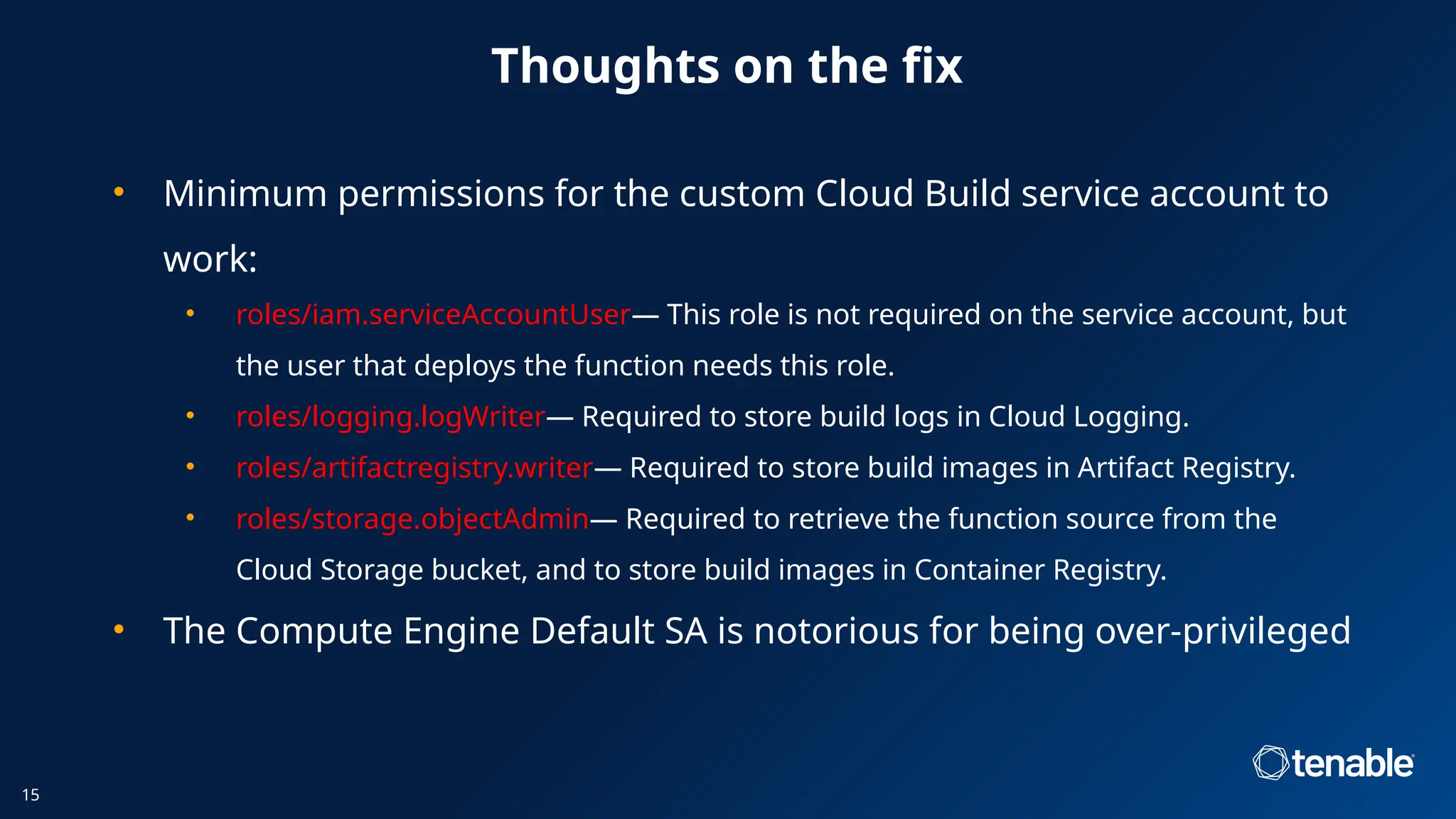
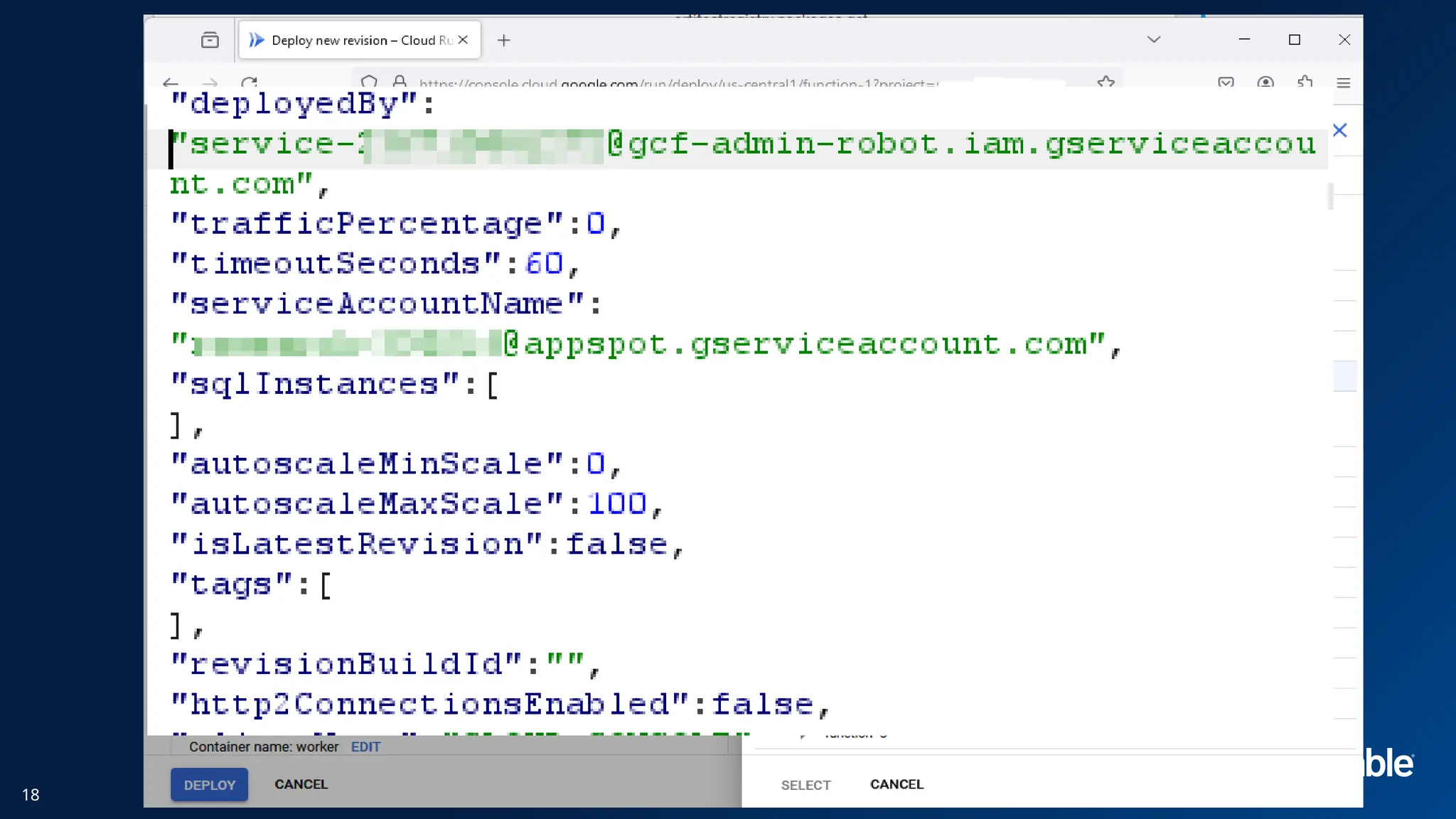
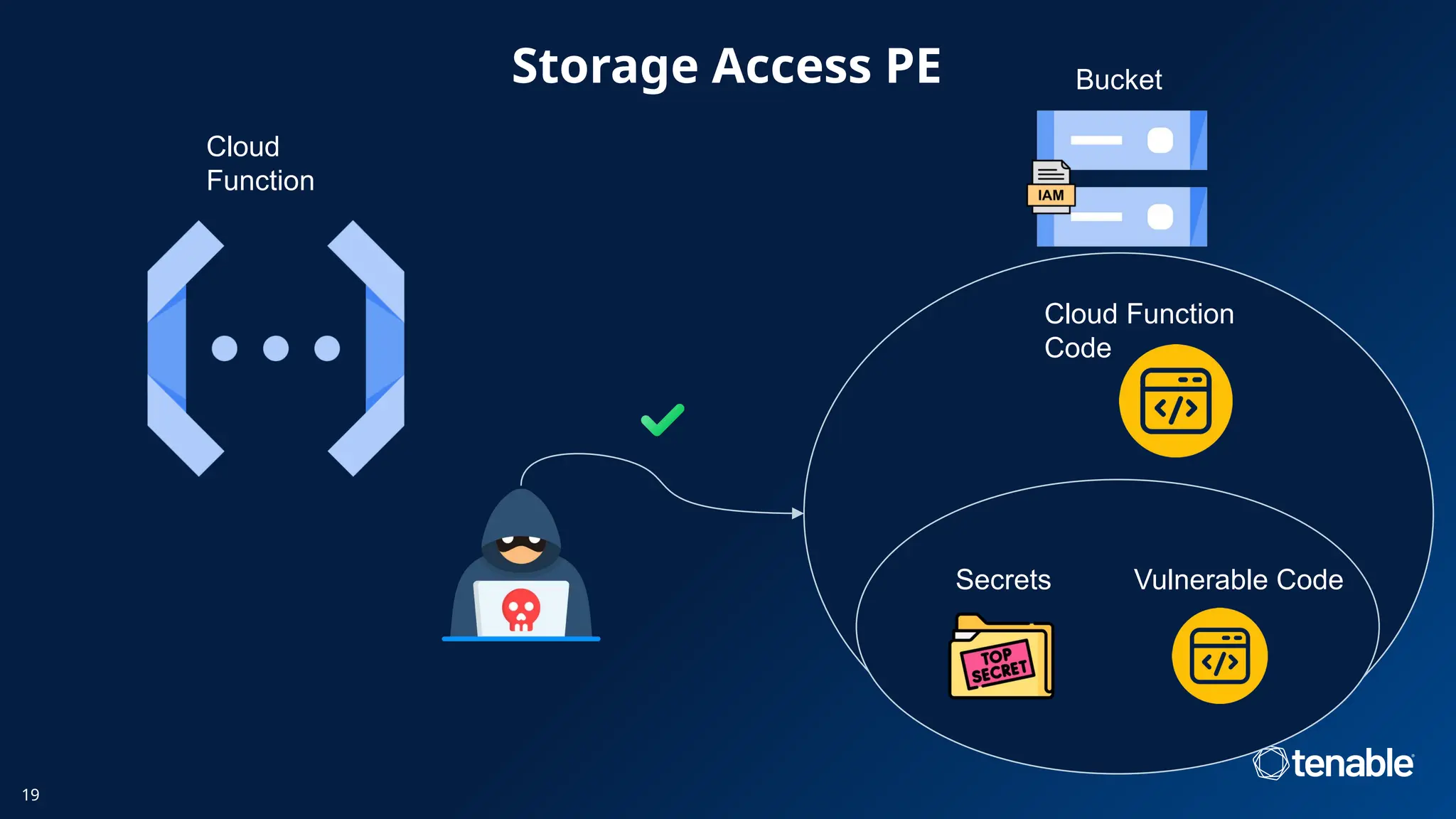
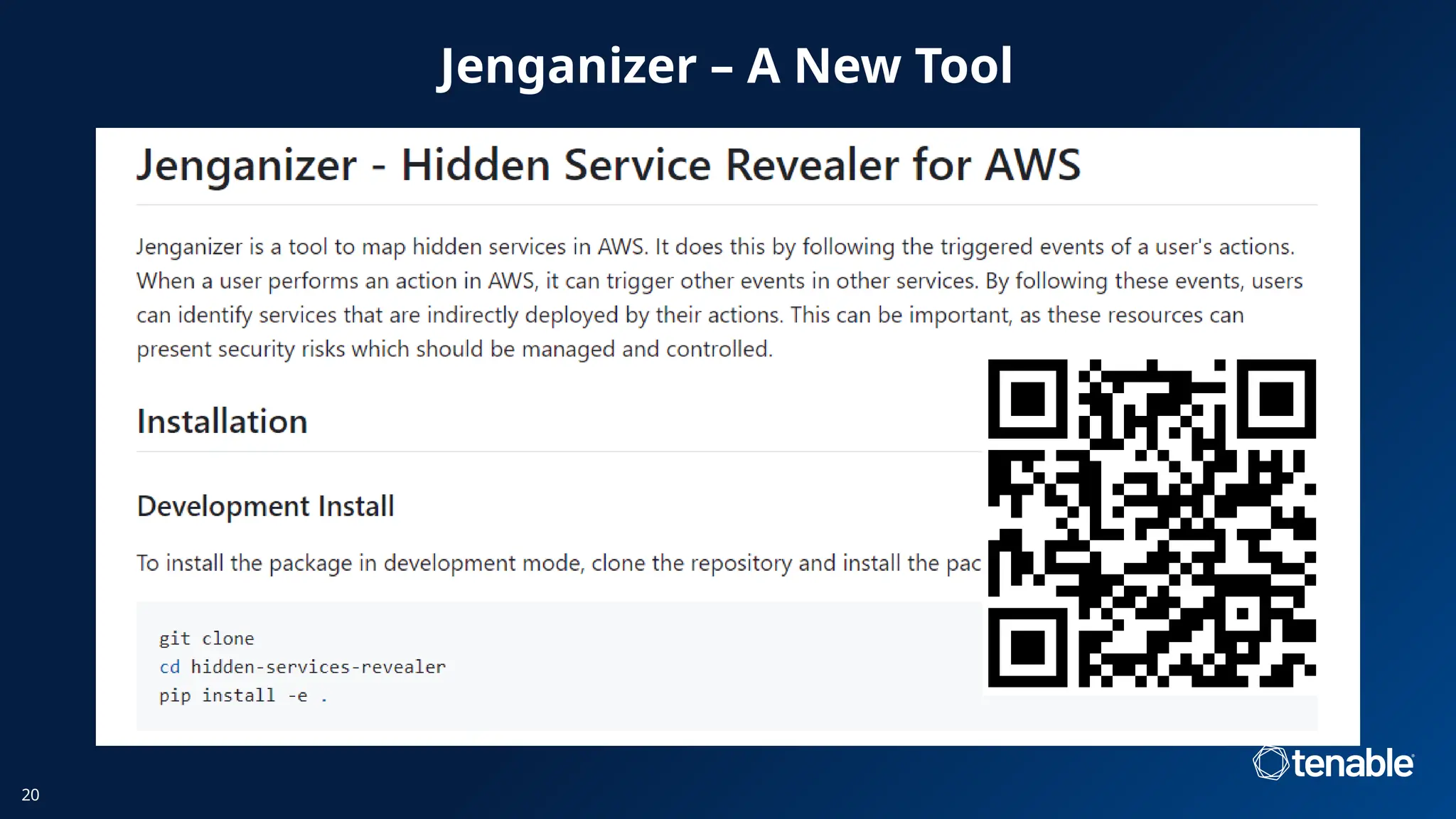
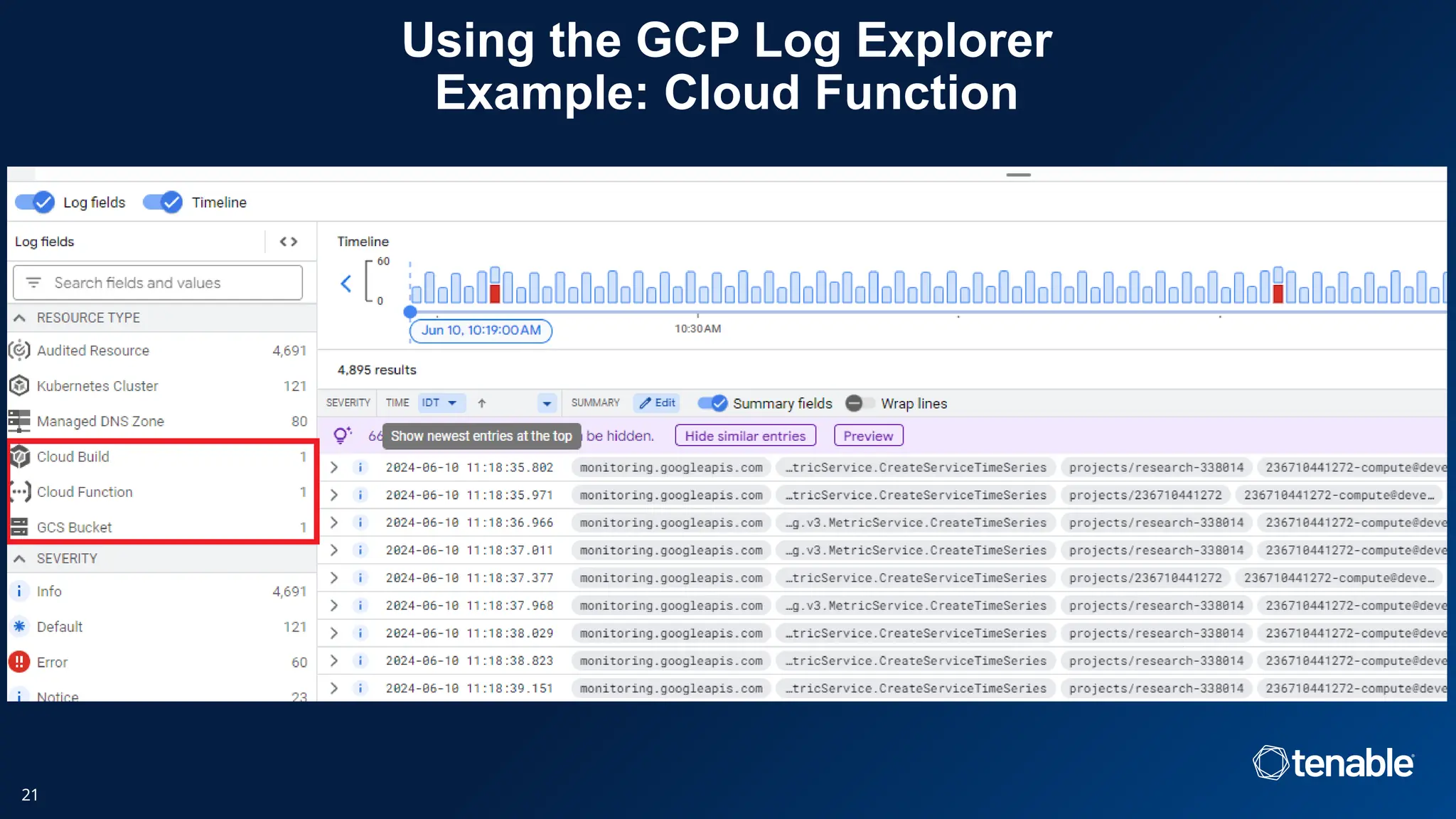
The document discusses vulnerabilities in Google Cloud Platform (GCP) services, particularly focusing on privilege escalation risks associated with multi-service orchestration. Key issues arise from using default service accounts resulting in over-privileged access, creating opportunities for malicious exploitation. Recommendations include implementing custom service accounts with minimal permissions to enhance security during function deployments.