This document provides an overview of OAuth, including its history, terminology, workflow, and versions. It describes how OAuth is an open standard for authorization that allows APIs to be accessed without sharing passwords. The document outlines the key actors in OAuth (consumer, service provider, user), explains the typical 3-step authorization process between these parties, and discusses some limitations of the original OAuth 1.0 specification that OAuth 2.0 aimed to address.




![Working of OAuth protocol
A Play in 3 Acts (to exchange authorization)
consumer has
Consumer key
Consumer secret
Consumer (to Service Provider):
“give me a request token”
oauth_consumer_key
oauth_signature_method
oauth_signature
oauth_timestamp
oauth_nonce
oauth_version (optional)
[additional parameters]](https://image.slidesharecdn.com/oauth-140522044435-phpapp01/75/O-auth-8-2048.jpg)
![A Play in 3 Acts (to exchange authorization)
Service Provider (to consumer):
“here is the request token(you can use it only once!)”
oauth_token (request token)
oauth_token_secret
[additional parameters]](https://image.slidesharecdn.com/oauth-140522044435-phpapp01/75/O-auth-9-2048.jpg)
![A Play in 3 Acts (to exchange authorization)
Second Act
Where the User authorizes the Request Token
Consumer (to the User):
“Please go to the Service Provider and authorize this request”
consumer ->user ->service provider
oauth_token (request token)
oauth_callback
[additional parameters]
Service Provider (to the User):
Do you authorize consumer to access your data?](https://image.slidesharecdn.com/oauth-140522044435-phpapp01/75/O-auth-10-2048.jpg)
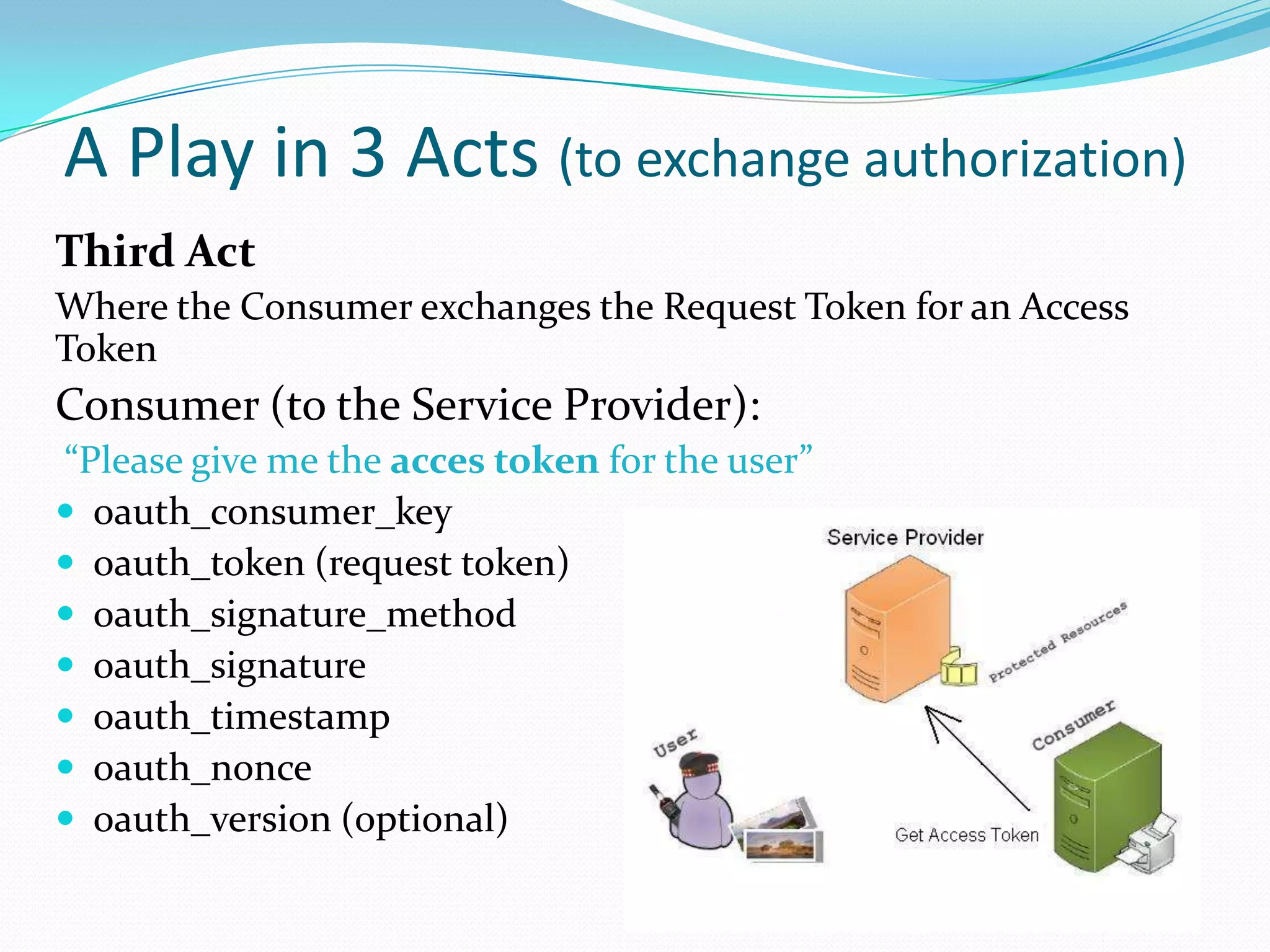
![A Play in 3 Acts (to exchange authorization)
Service Provider (to the Consumer):
“here is the access token for the user”
oauth_token (access token)
oauth_token_secret
[additional parameters]
Now consumer accesses the resources
Consumer (to the Service Provider):
“Here i am again on behalf of the user”
oauth_consumer_key
oauth_token (access token)
oauth_signature_method
oauth_signature
oauth_timestamp
oauth_nonce
oauth_version (optional)
[additional parameters]](https://image.slidesharecdn.com/oauth-140522044435-phpapp01/75/O-auth-13-2048.jpg)