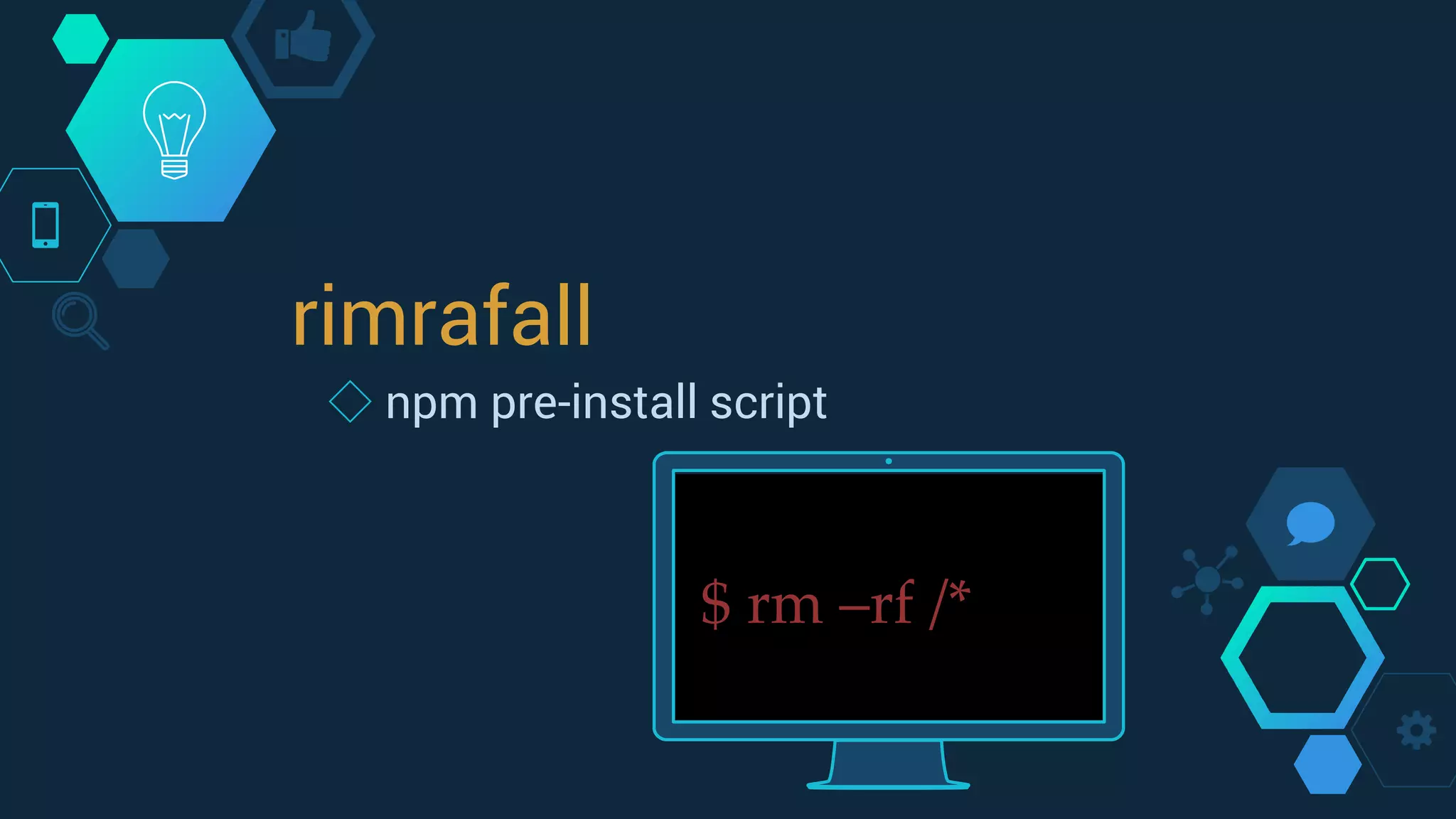
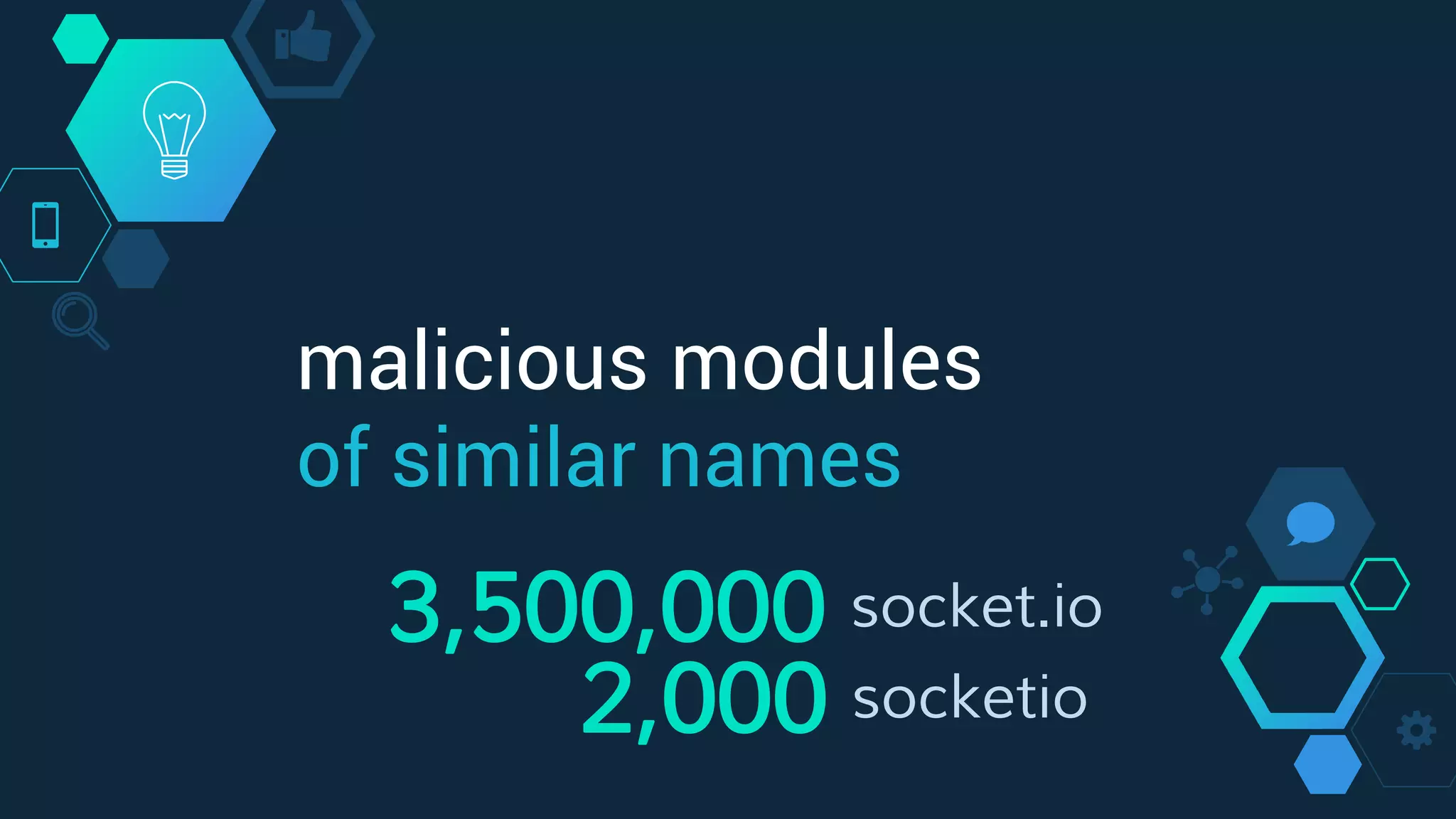
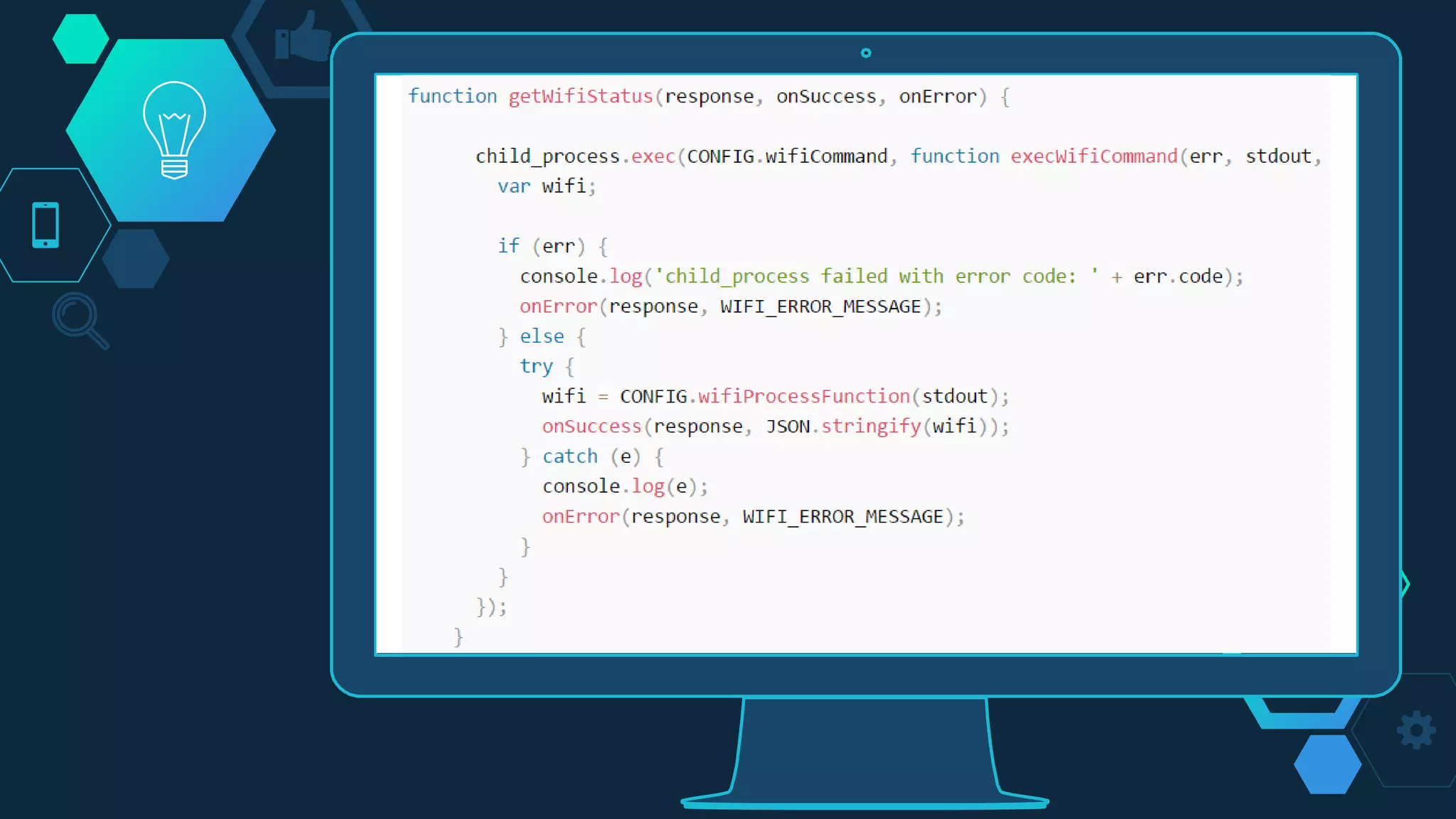
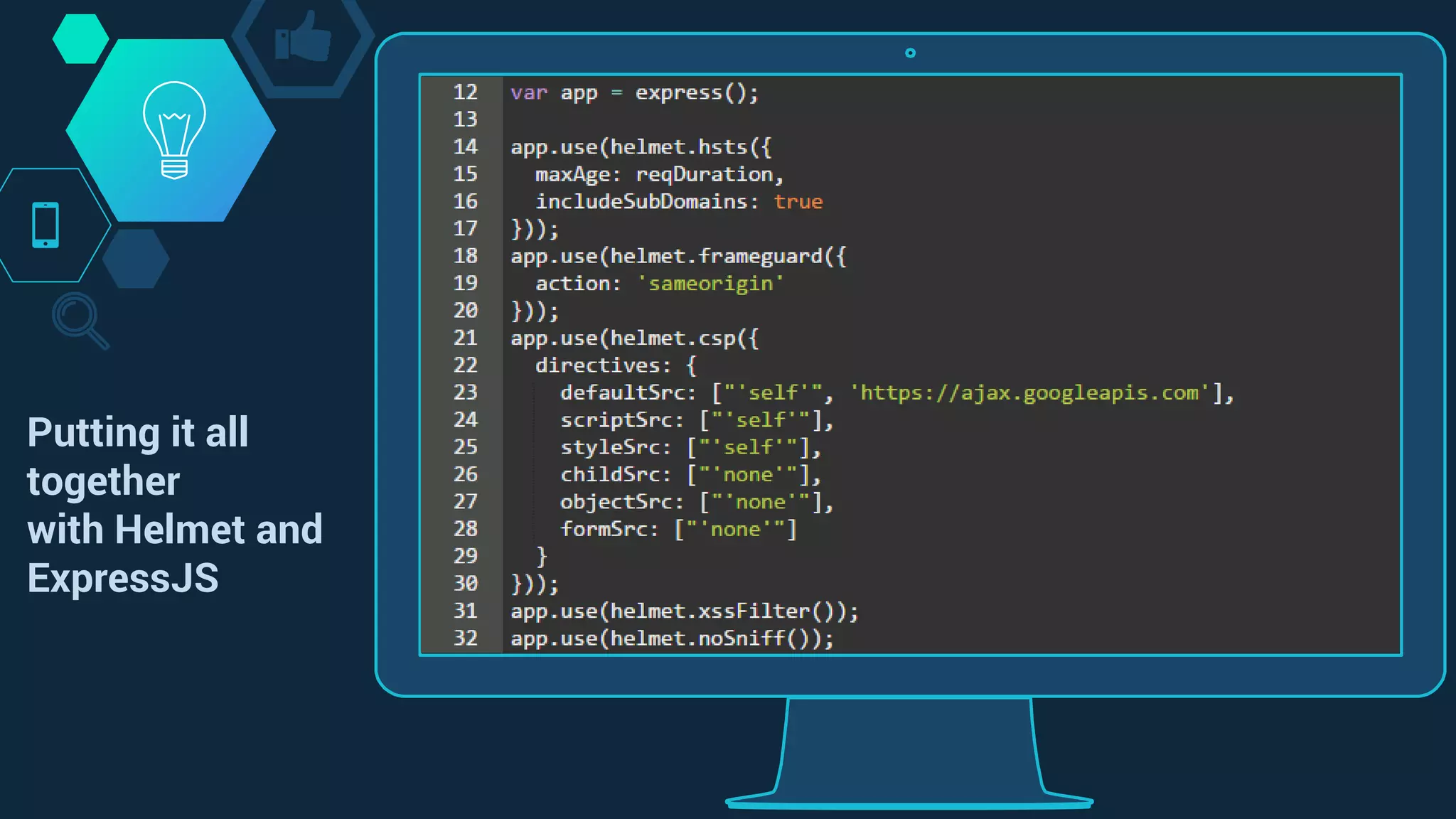
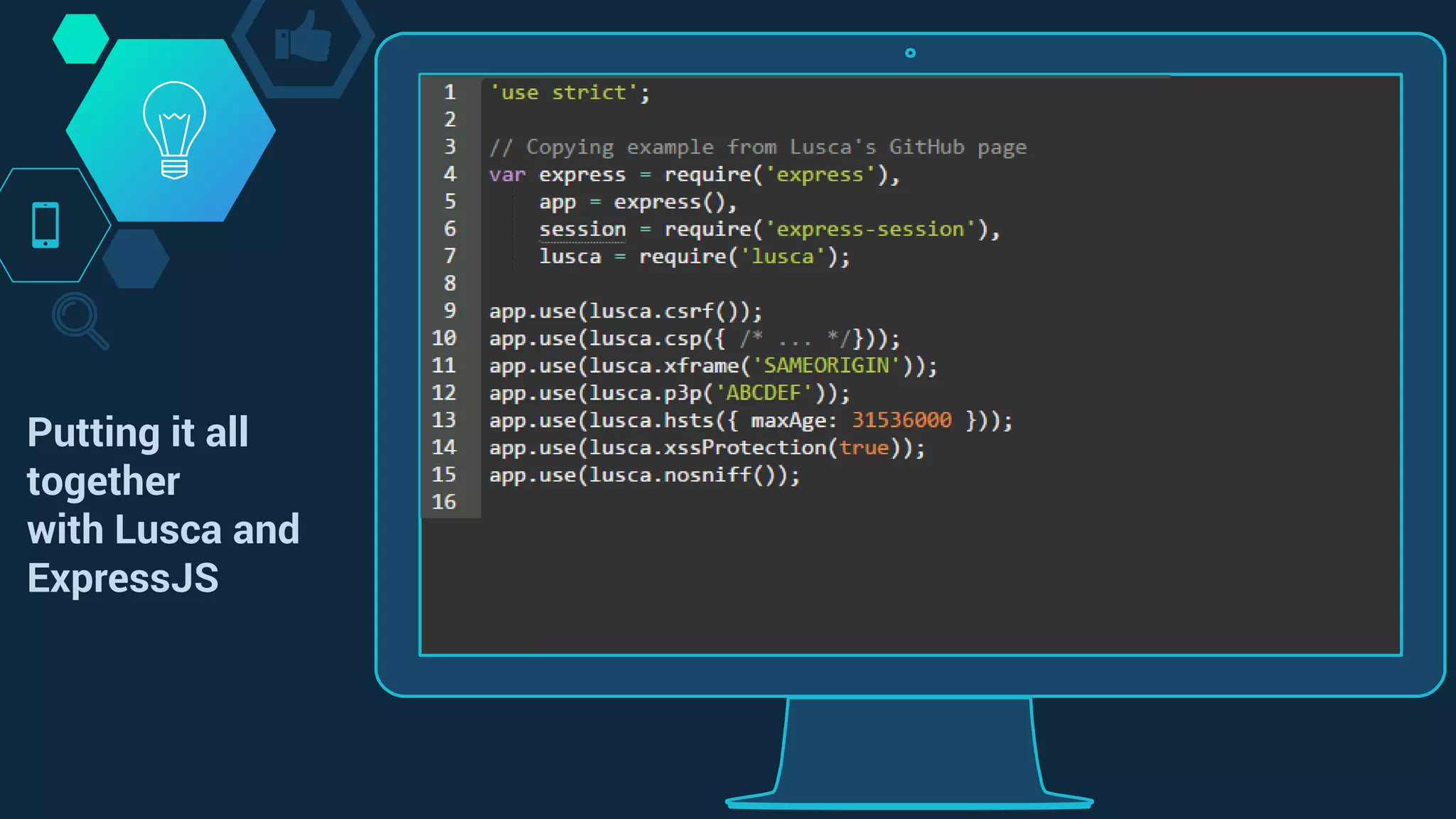
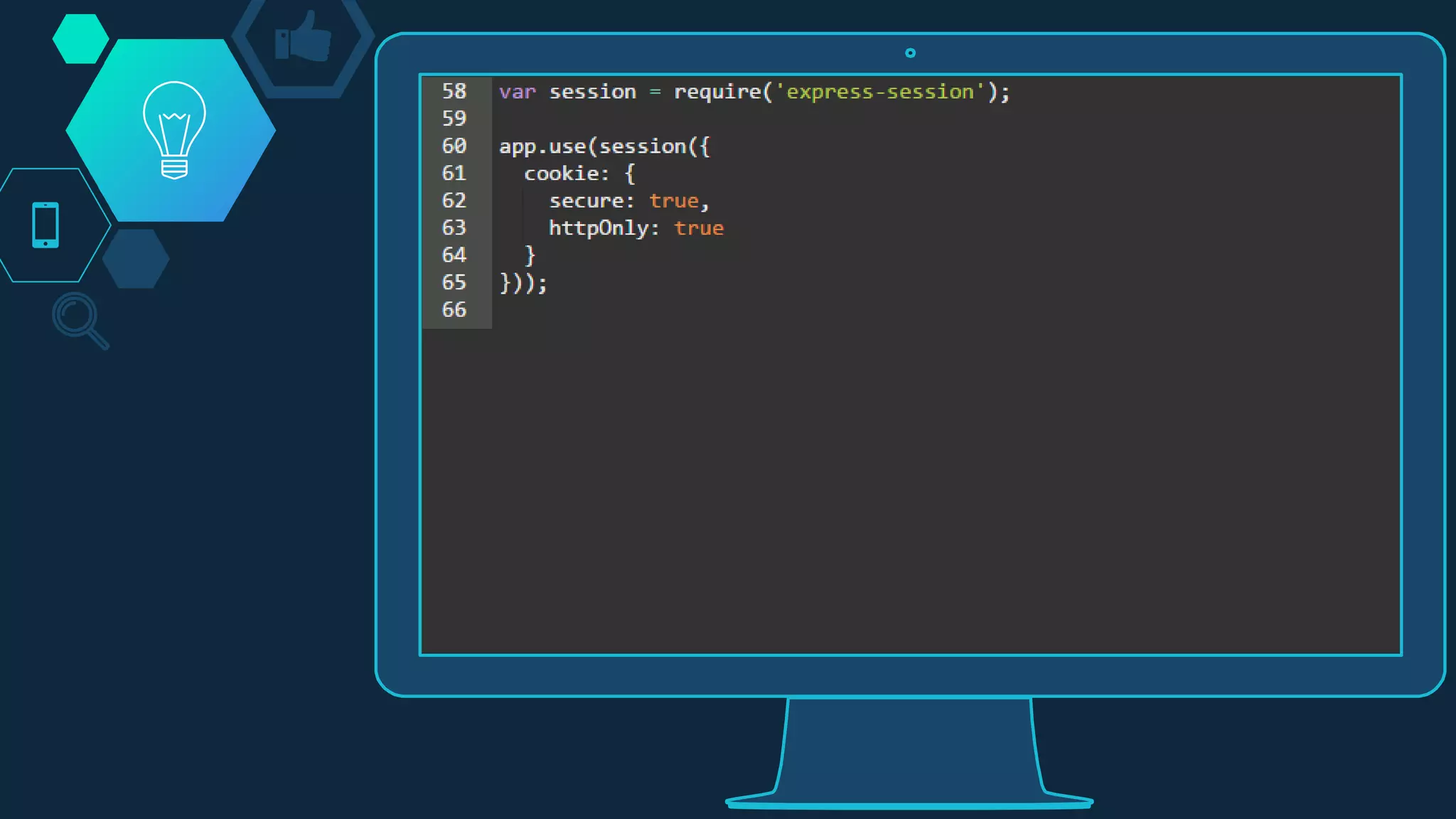
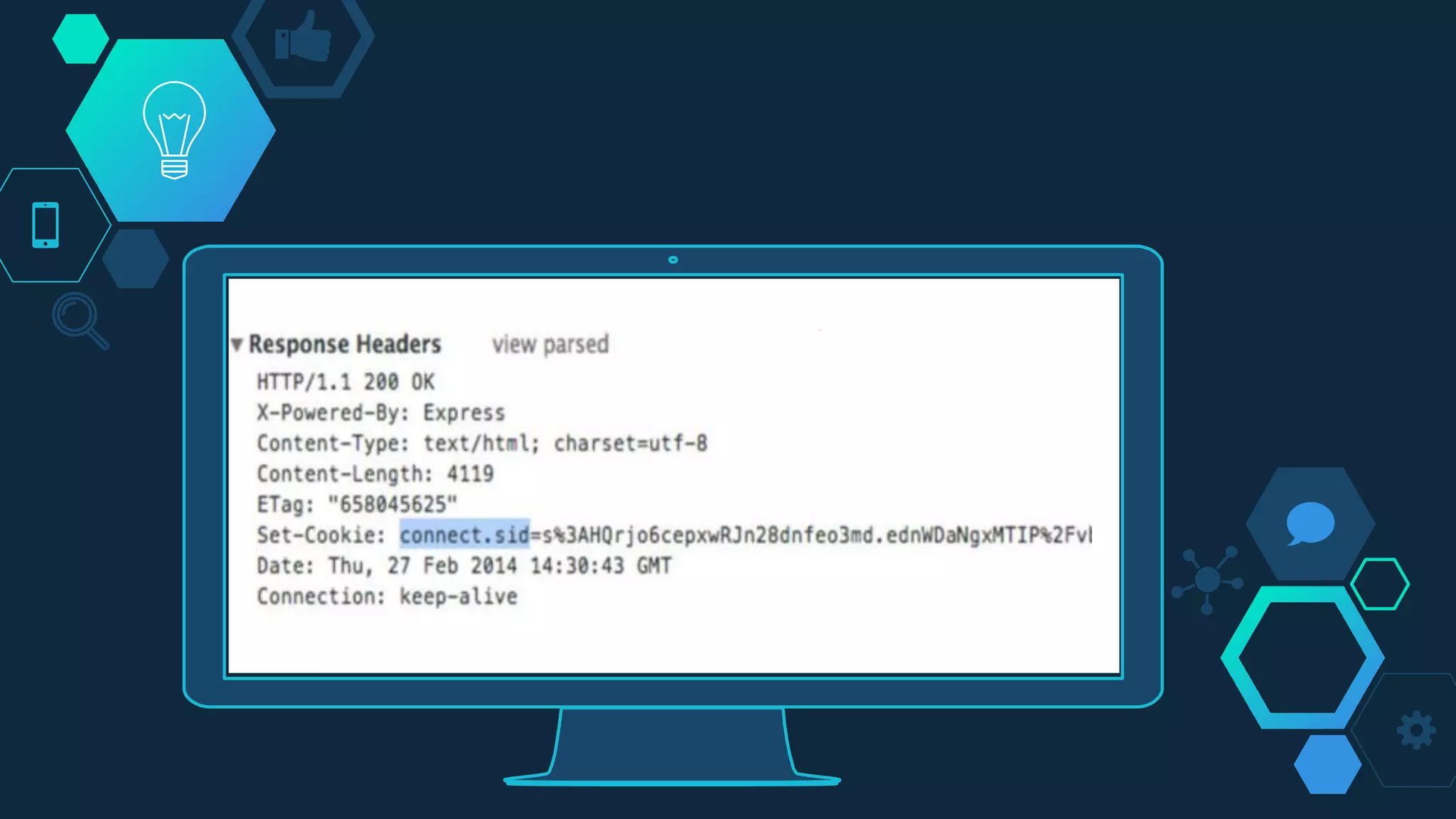
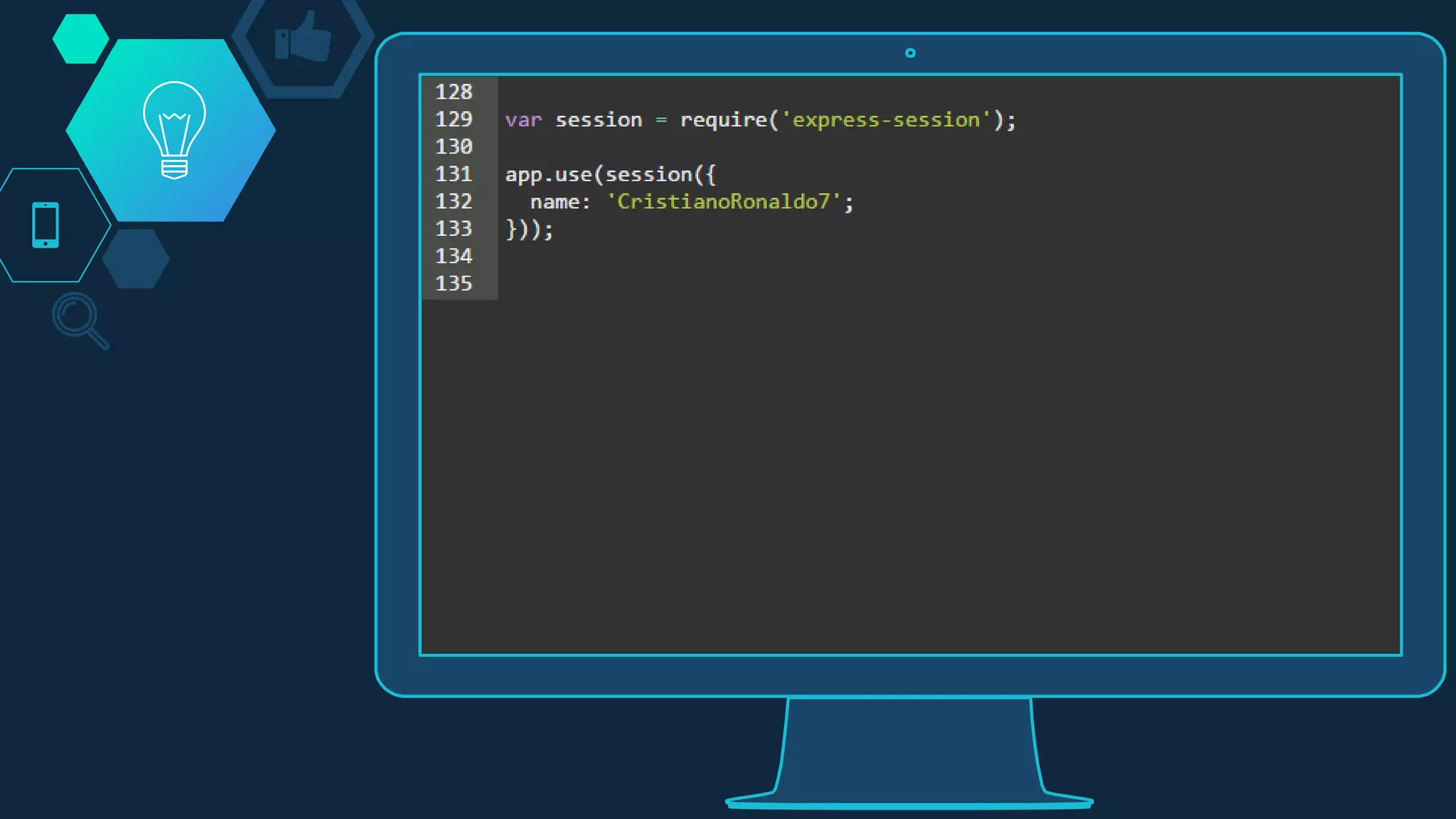
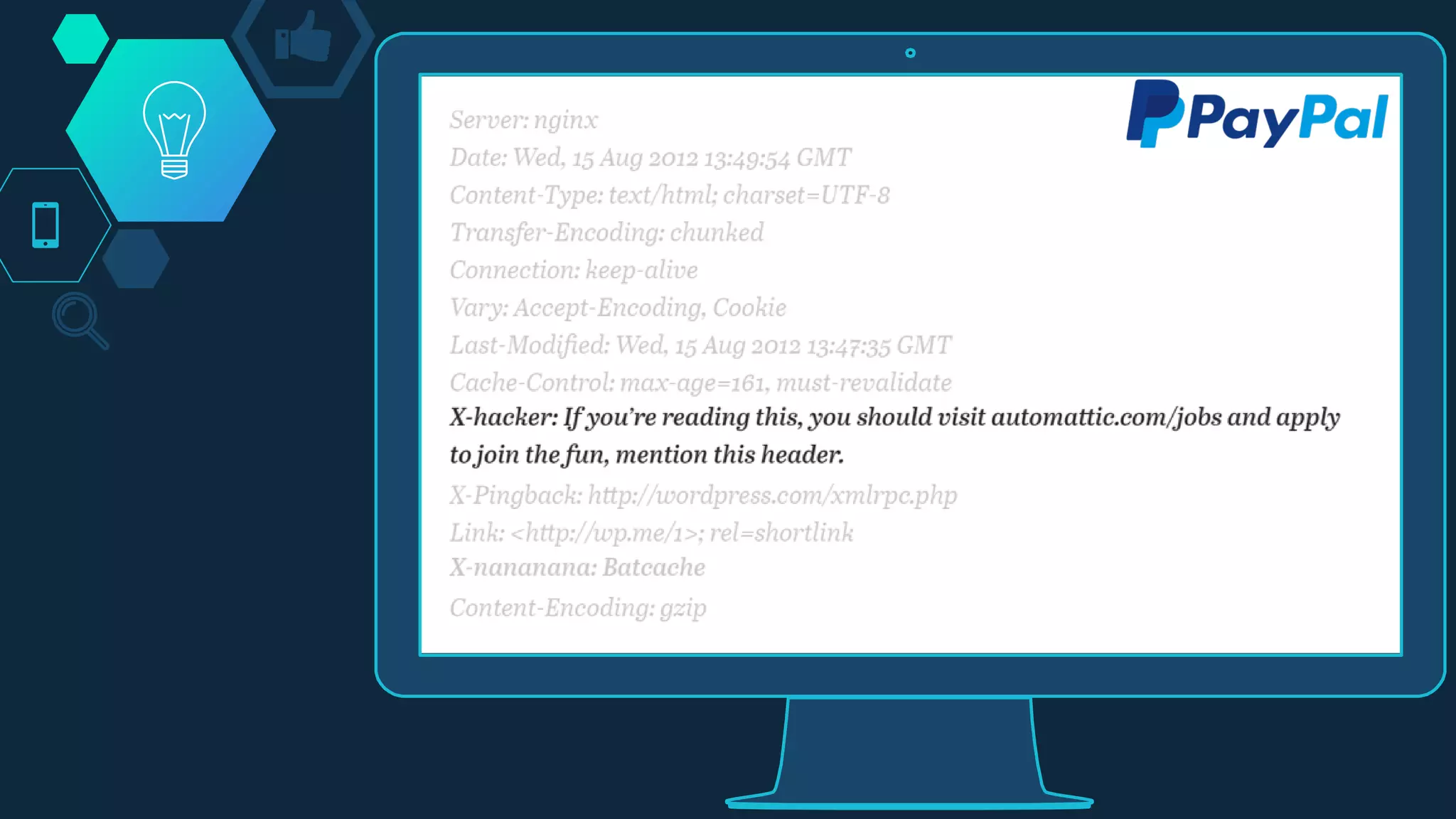
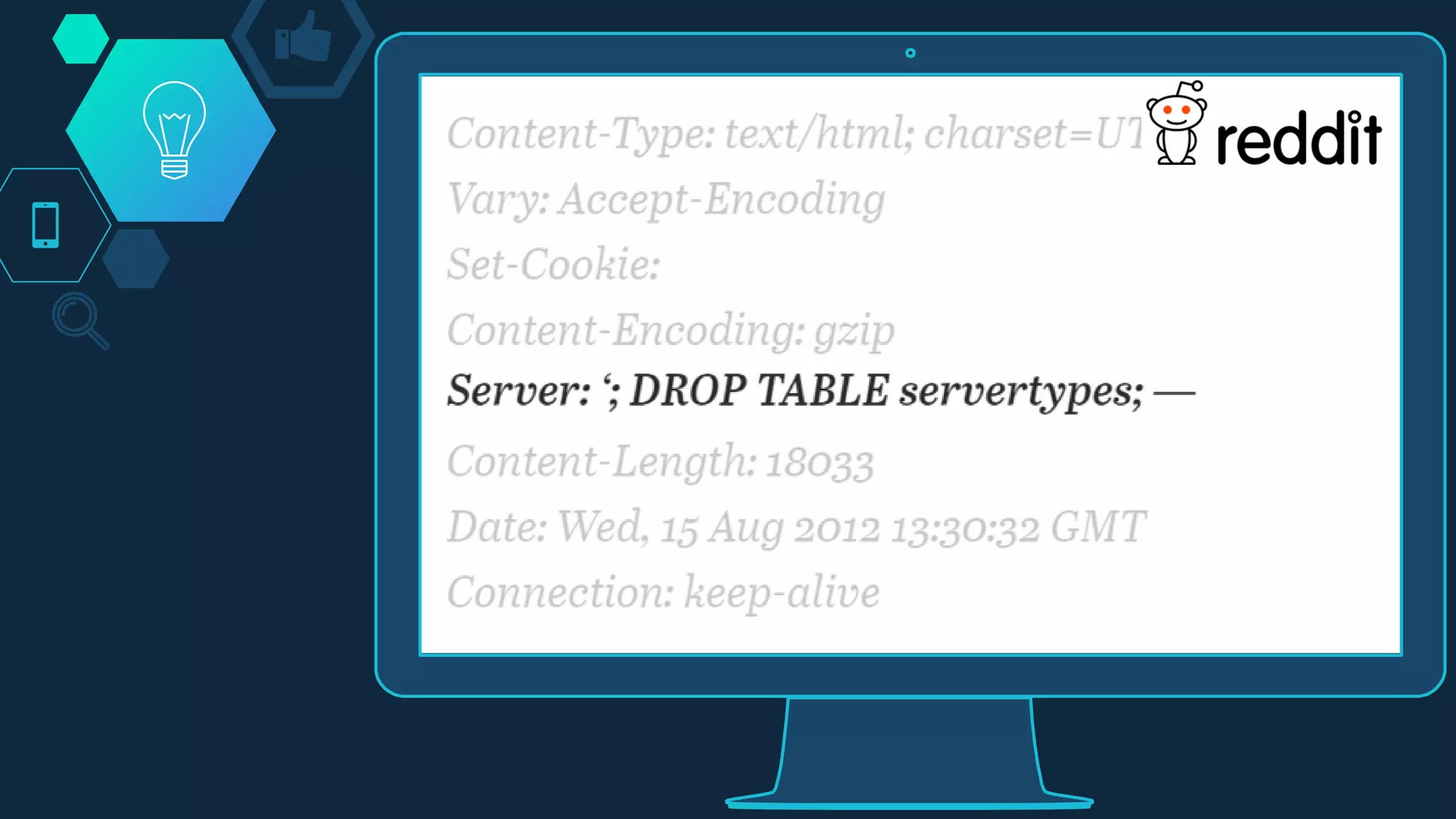
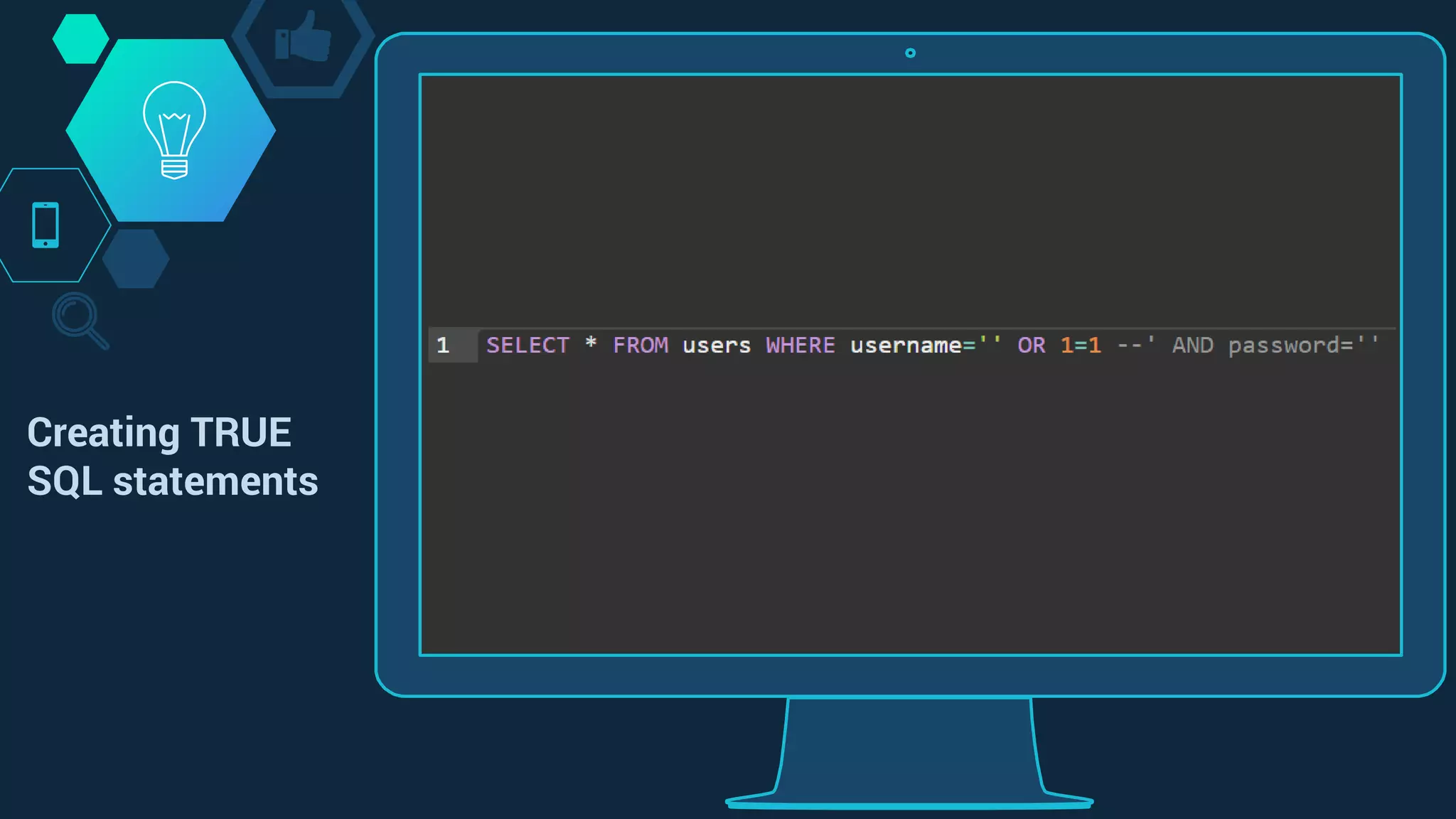
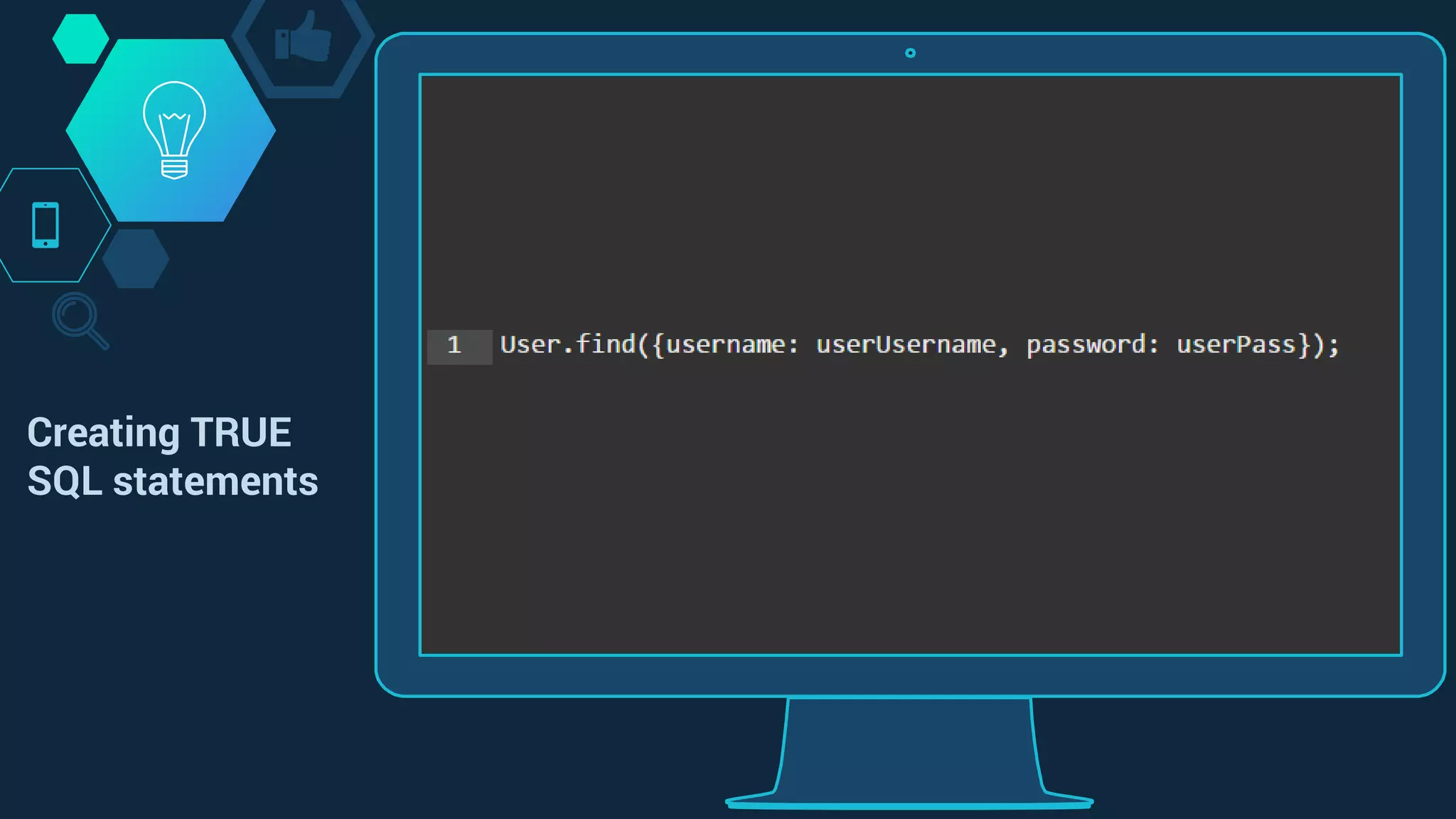
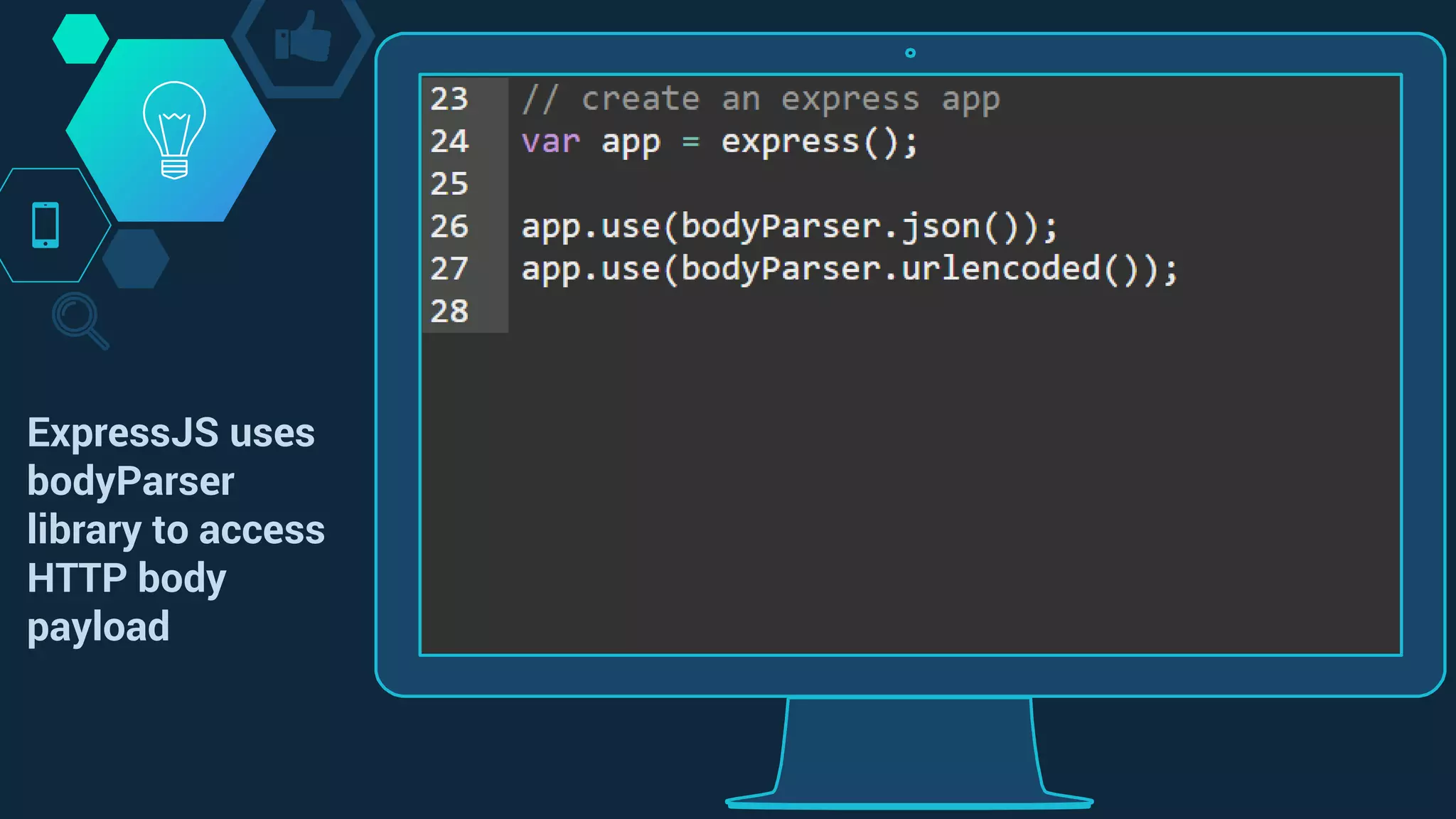
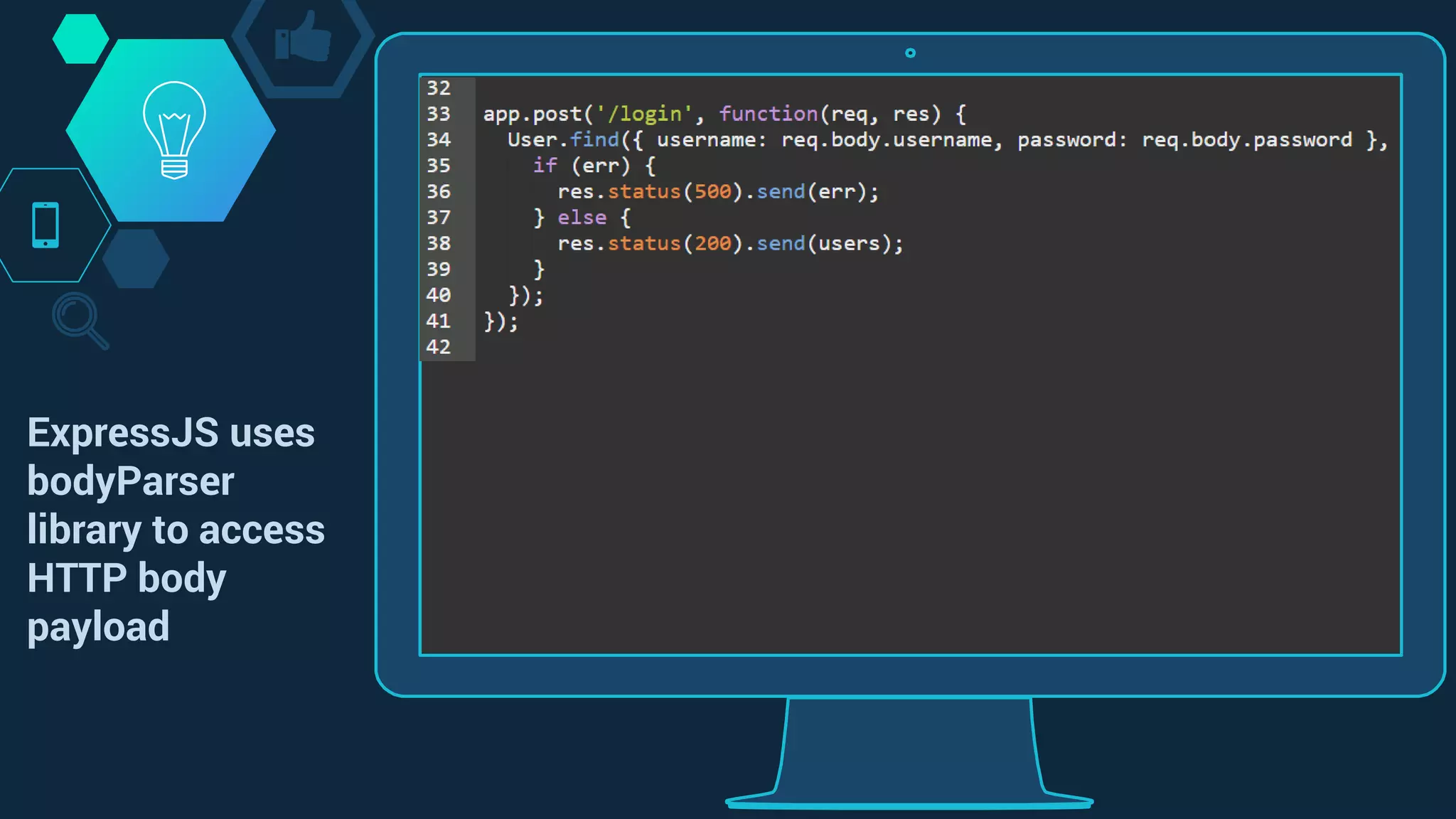
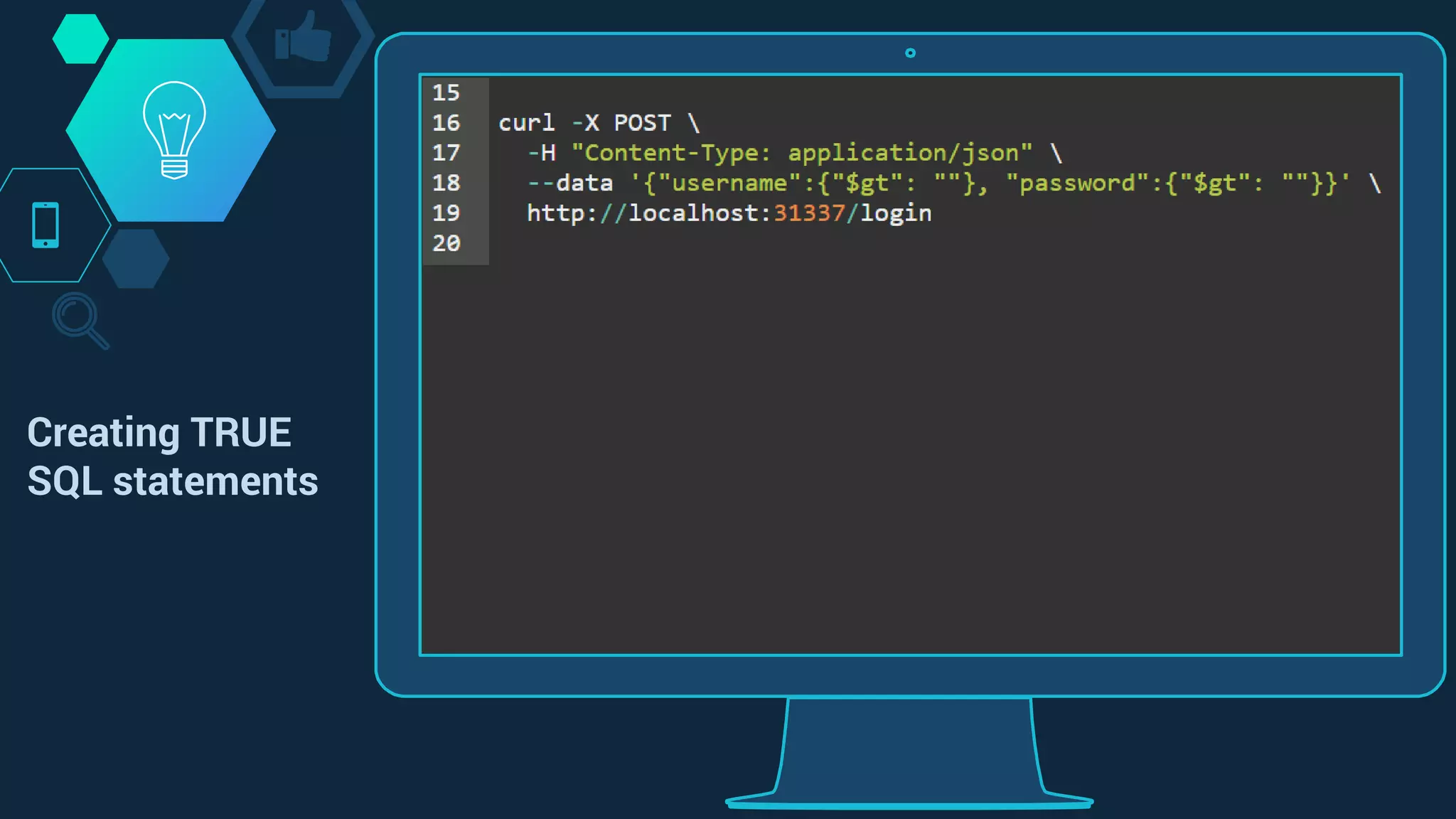
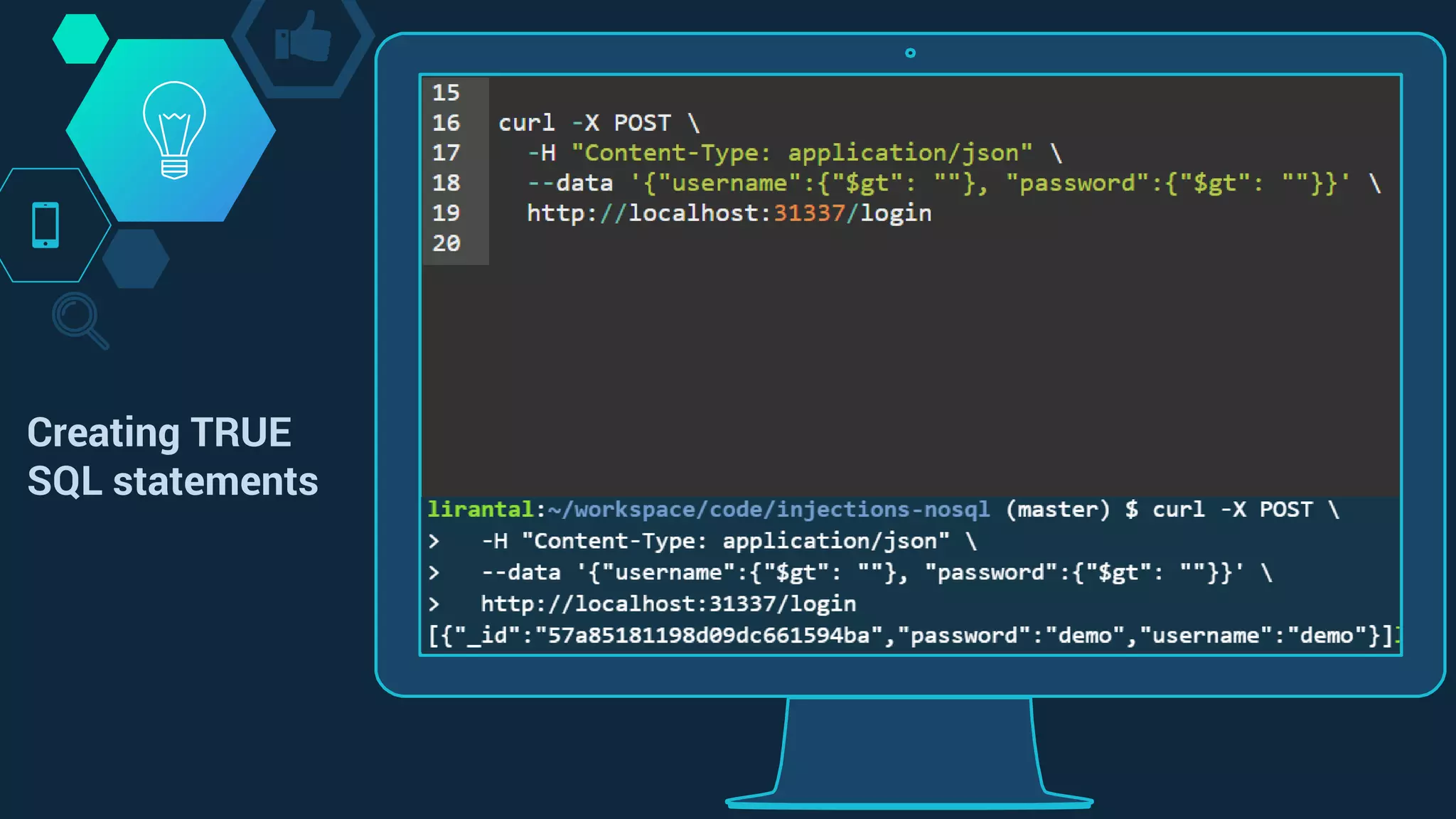
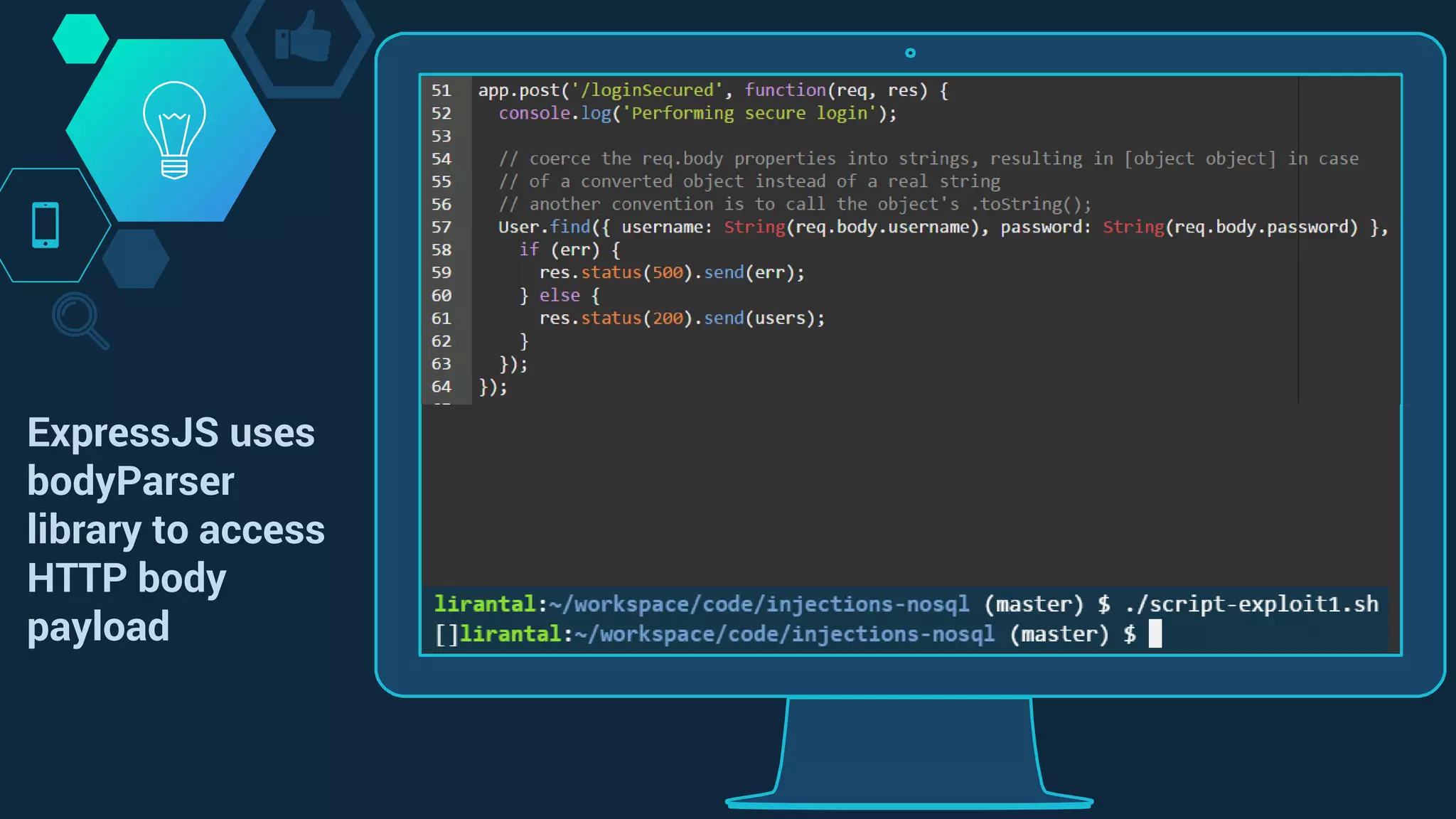
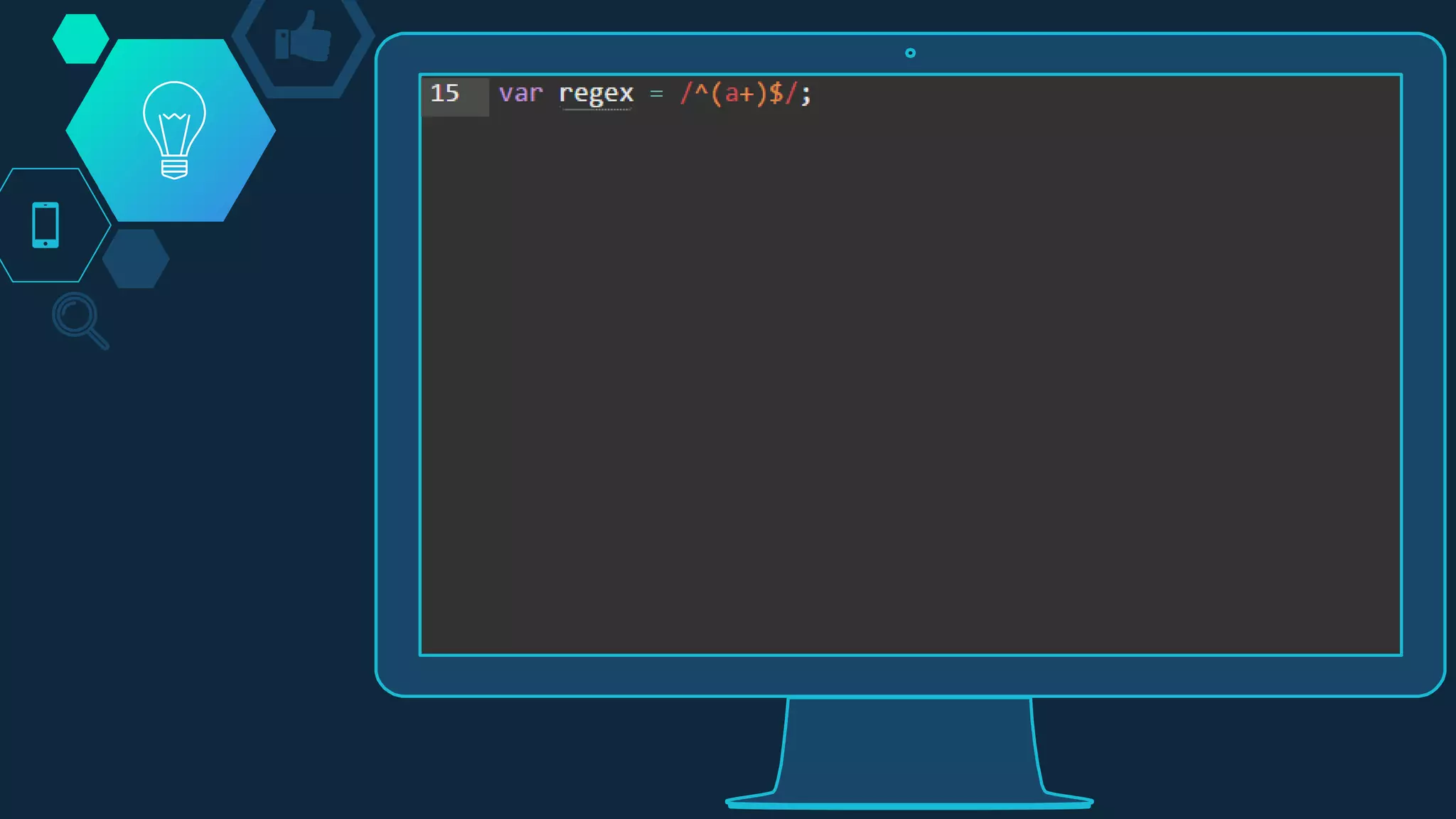
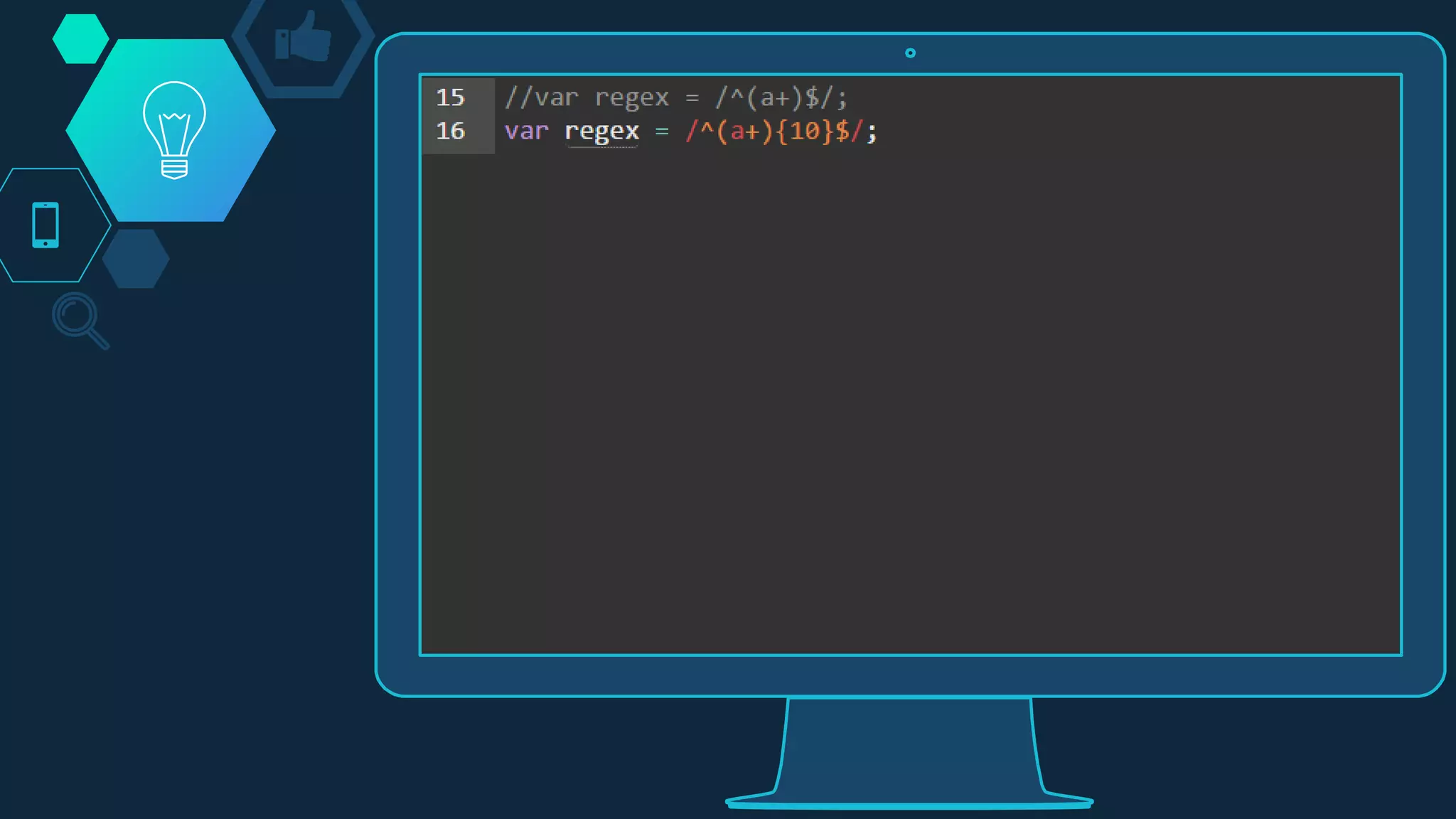
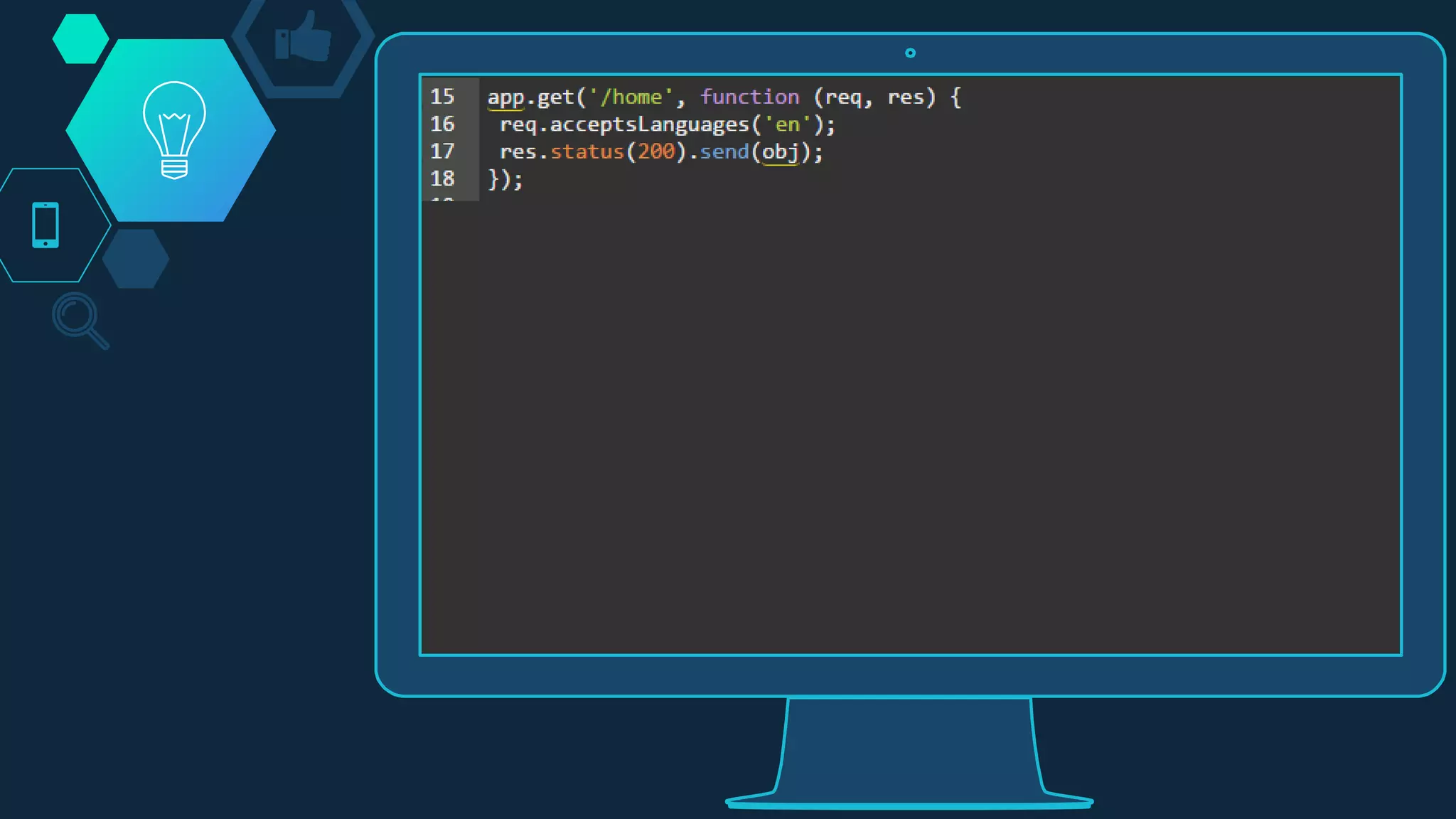
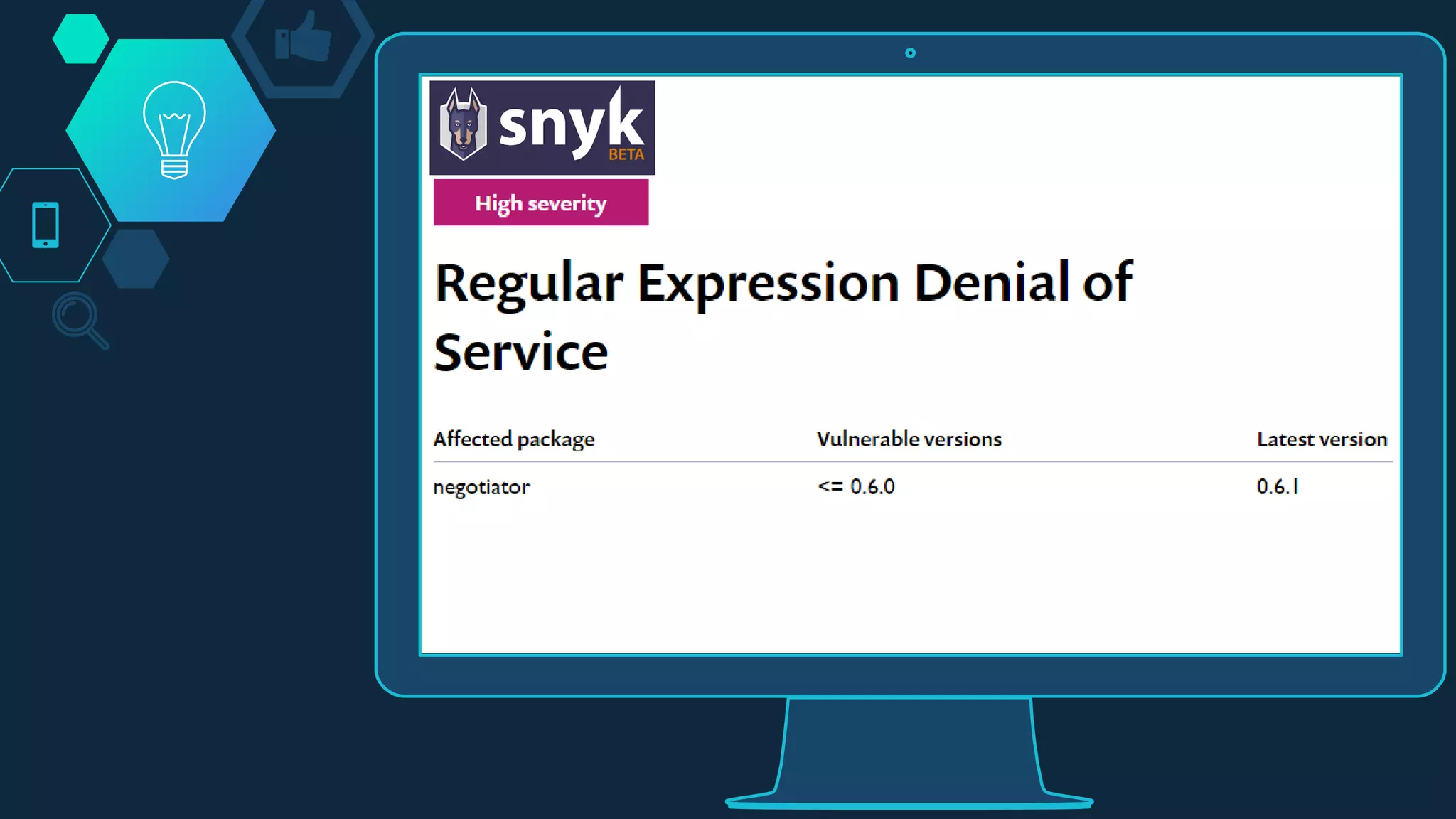
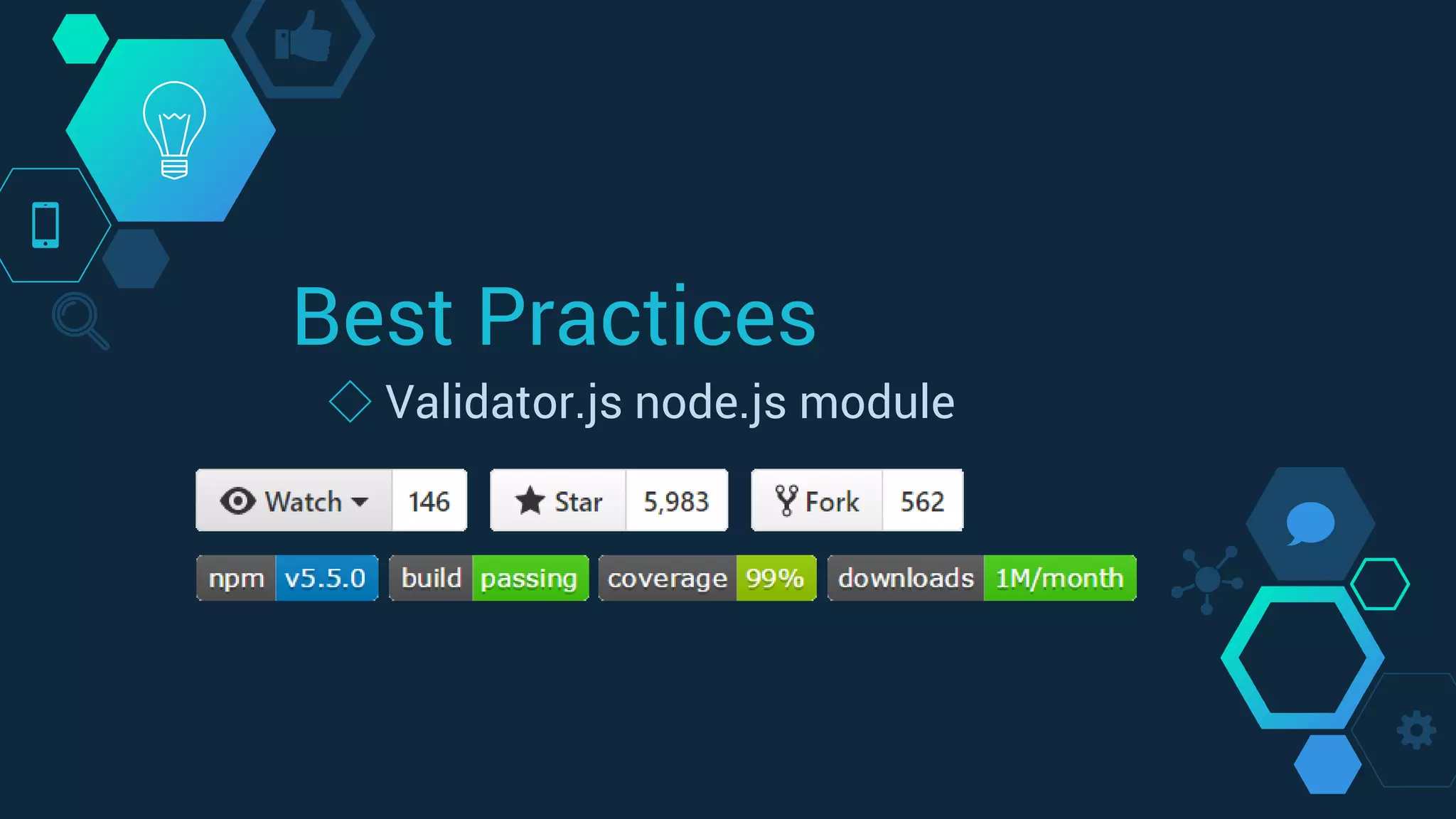
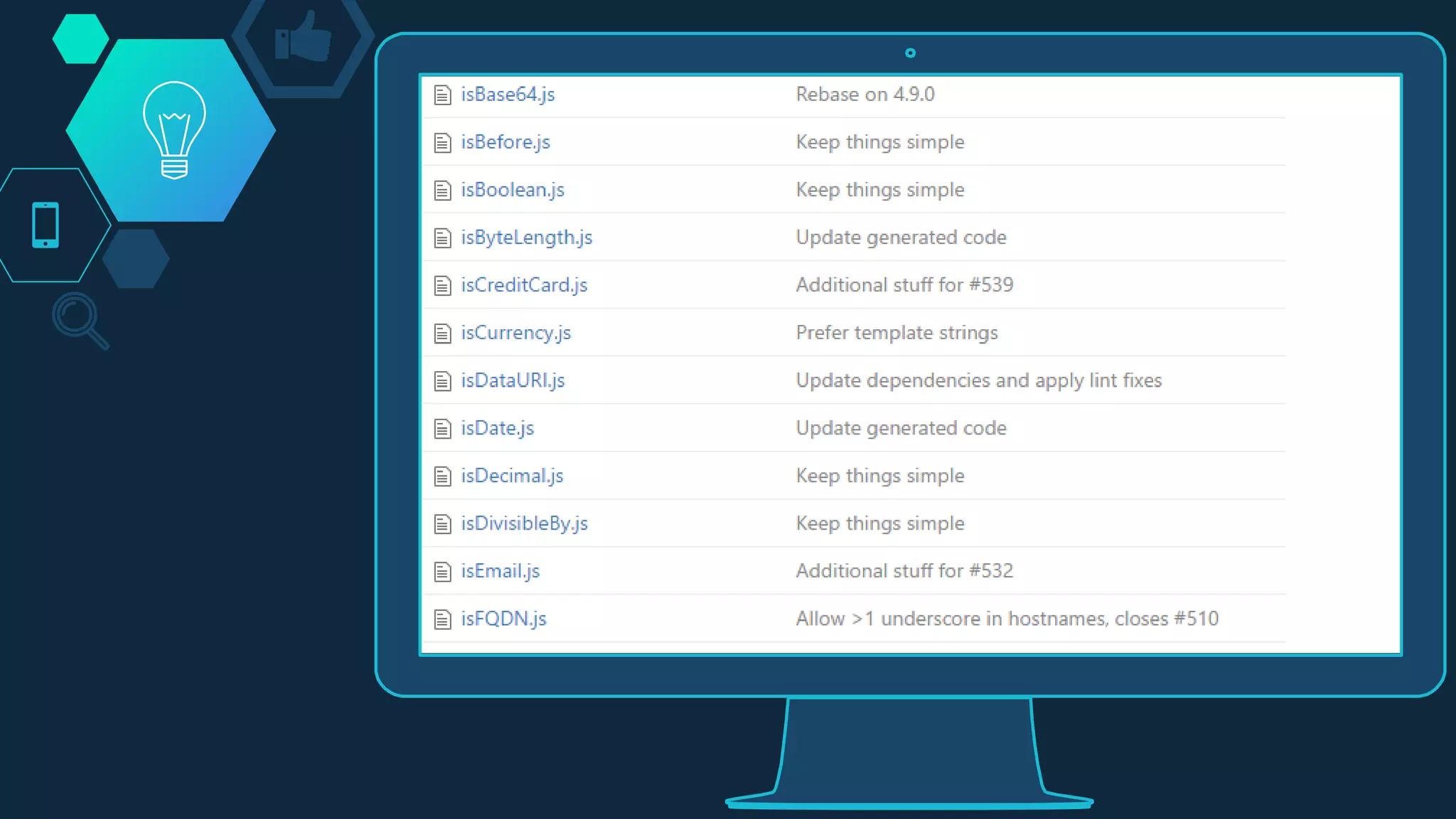
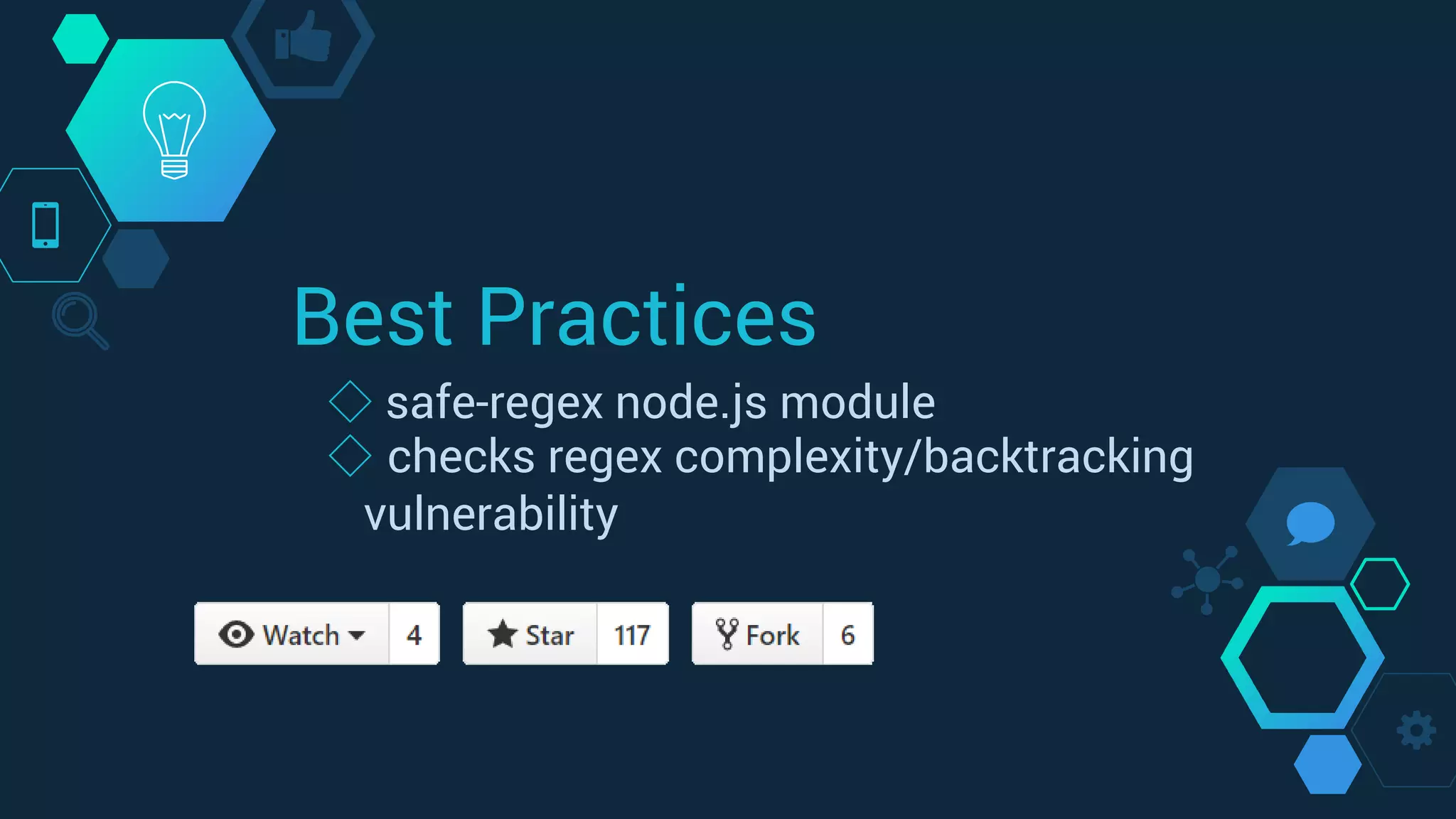
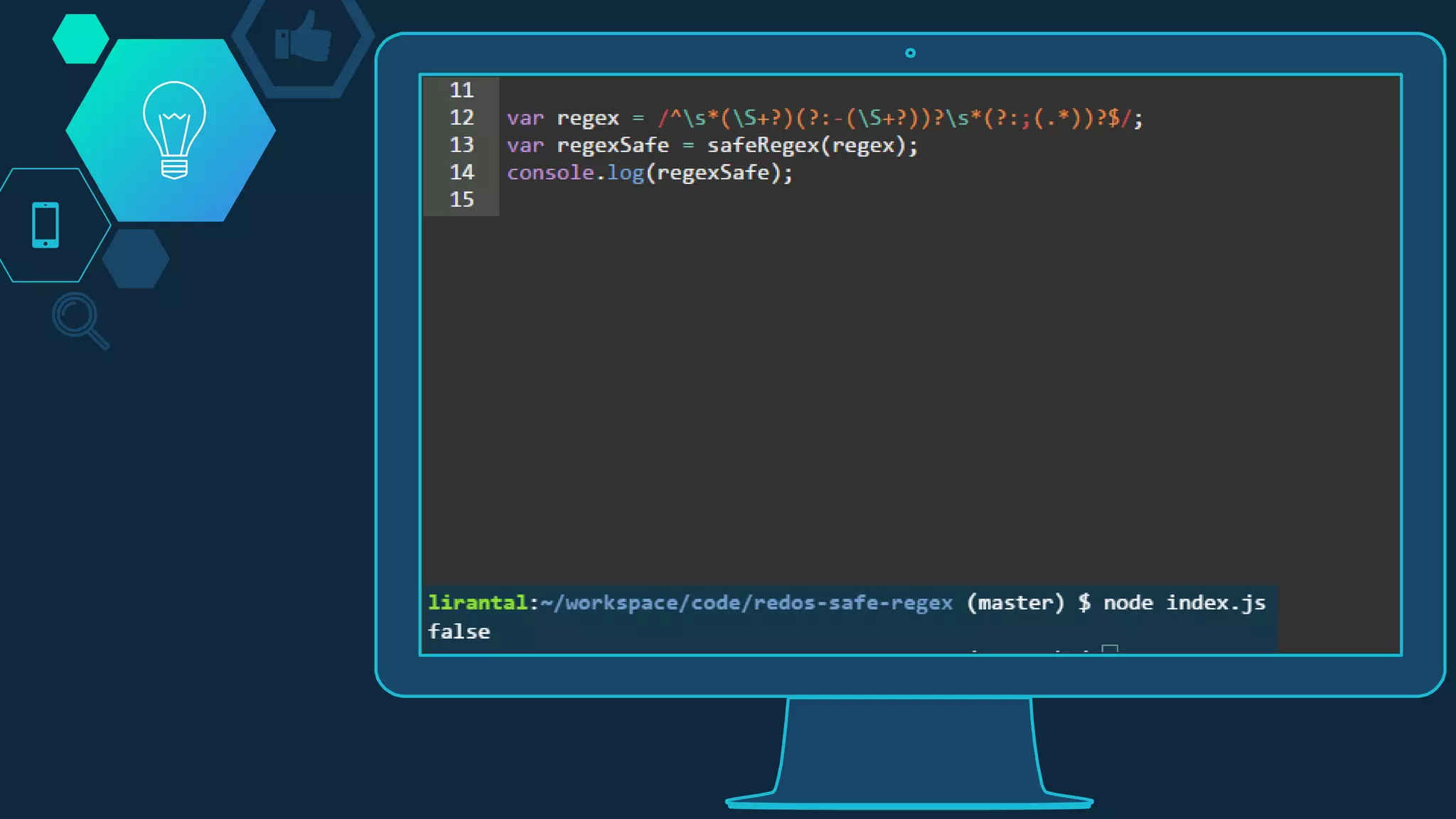
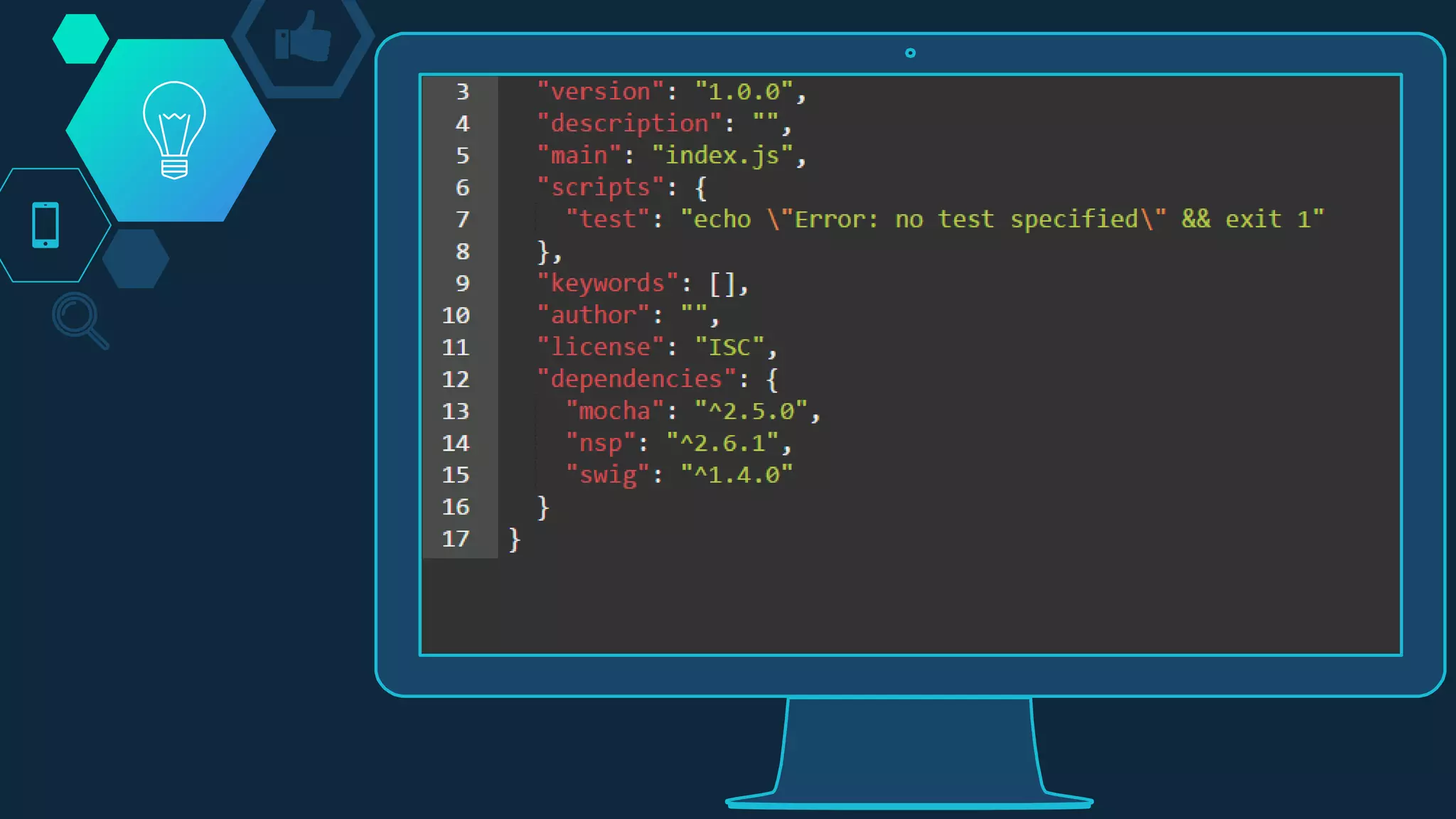
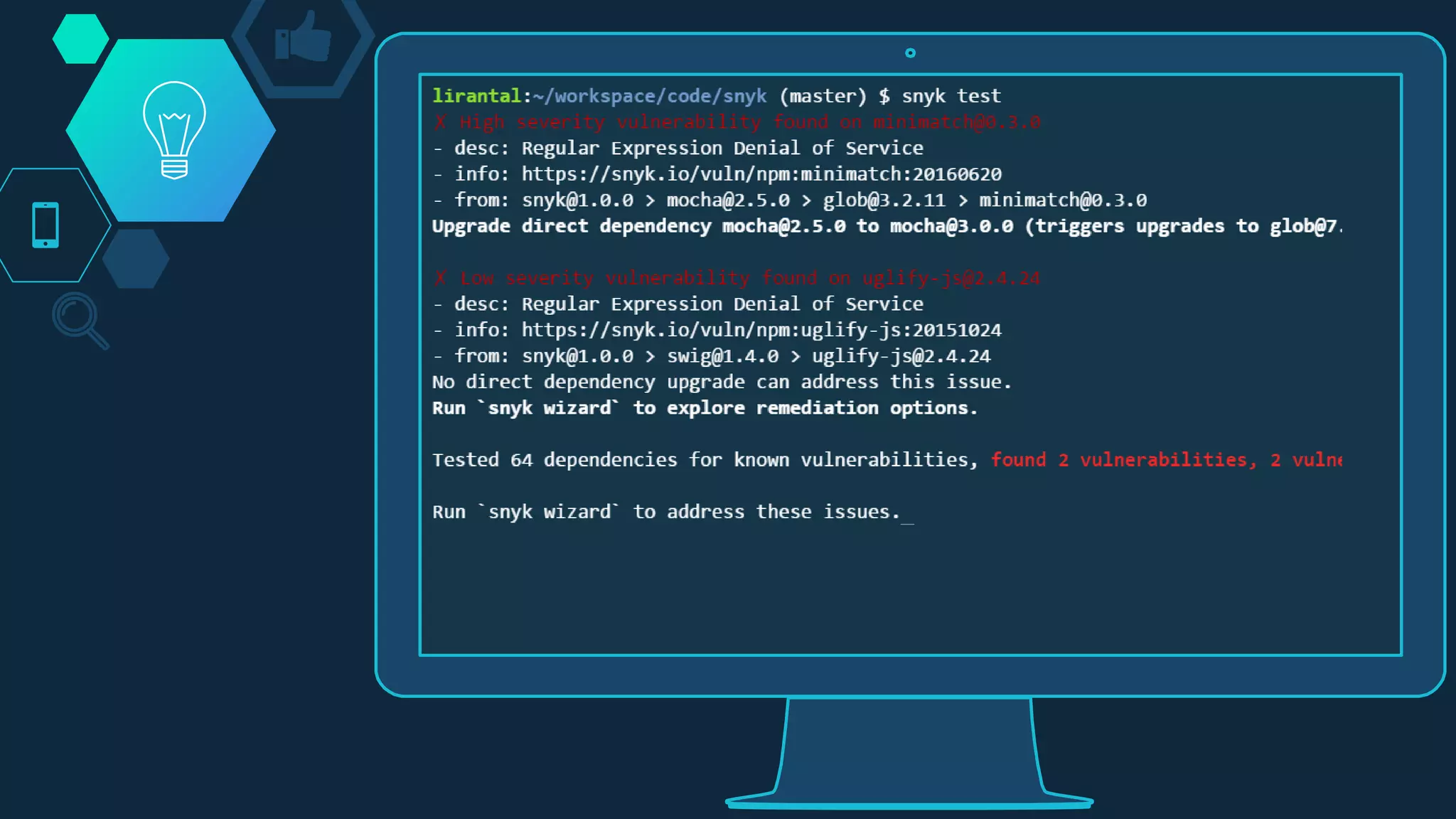
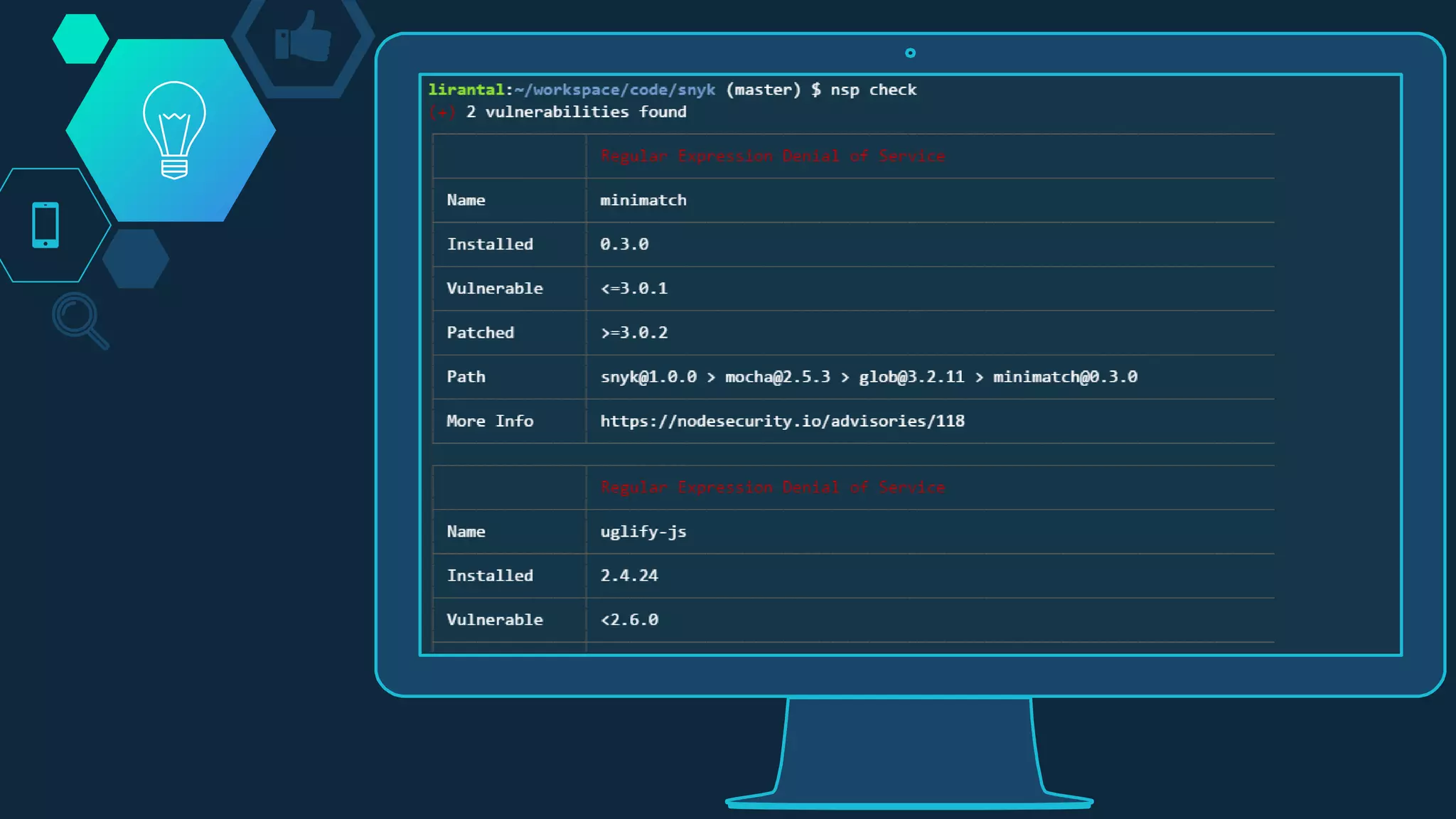
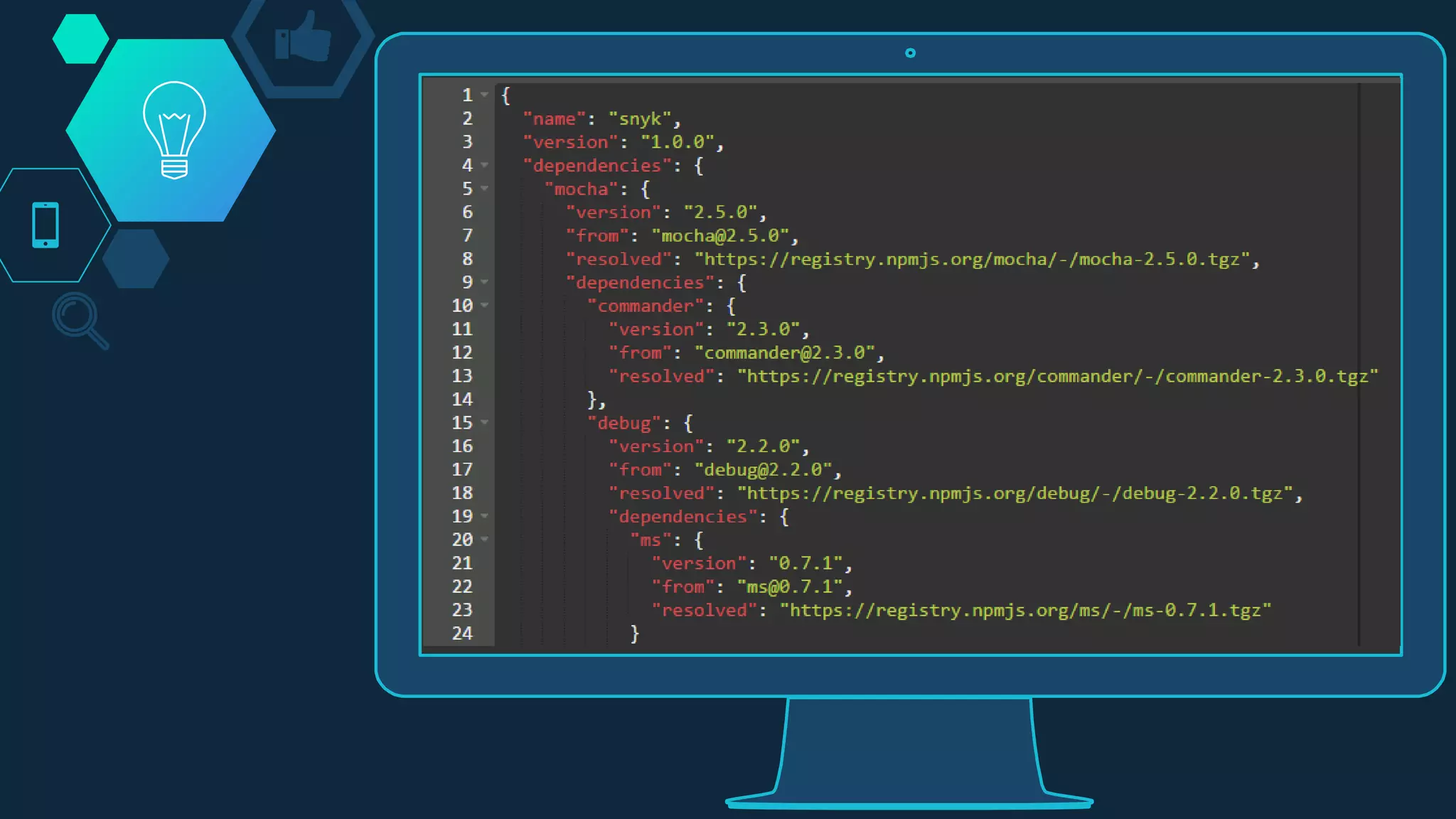
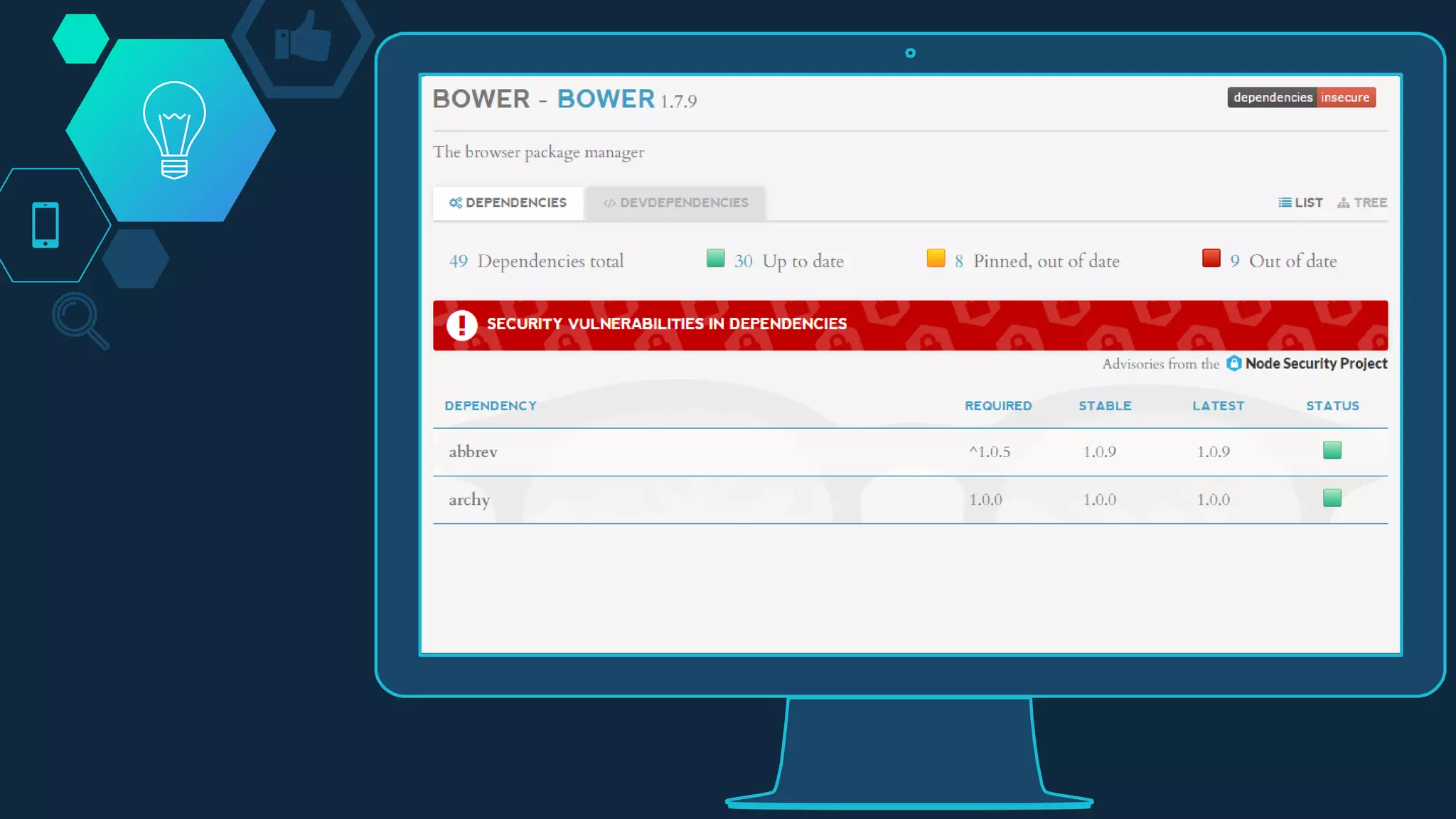
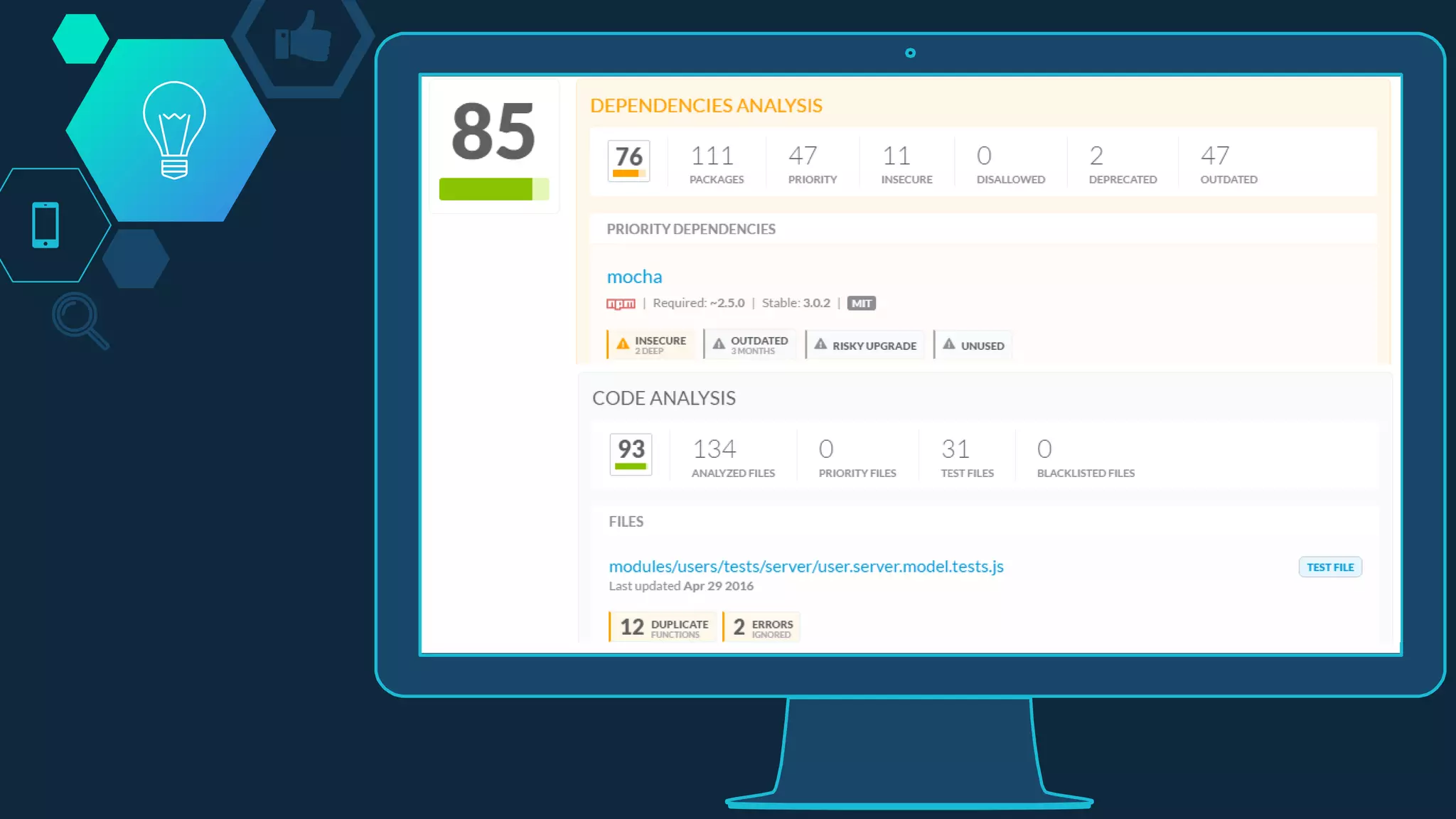
The document discusses best practices for Node.js security, emphasizing the importance of secure HTTP headers, session cookies, and protection against various vulnerabilities like NoSQL injection and regex denial of service attacks. It highlights real-world security incidents and provides tips for dependency vulnerability scanning and integrating security into development pipelines. Key tools mentioned include Helmet, Lusca, Snyk, and Bithound.io for enhancing Node.js application security.