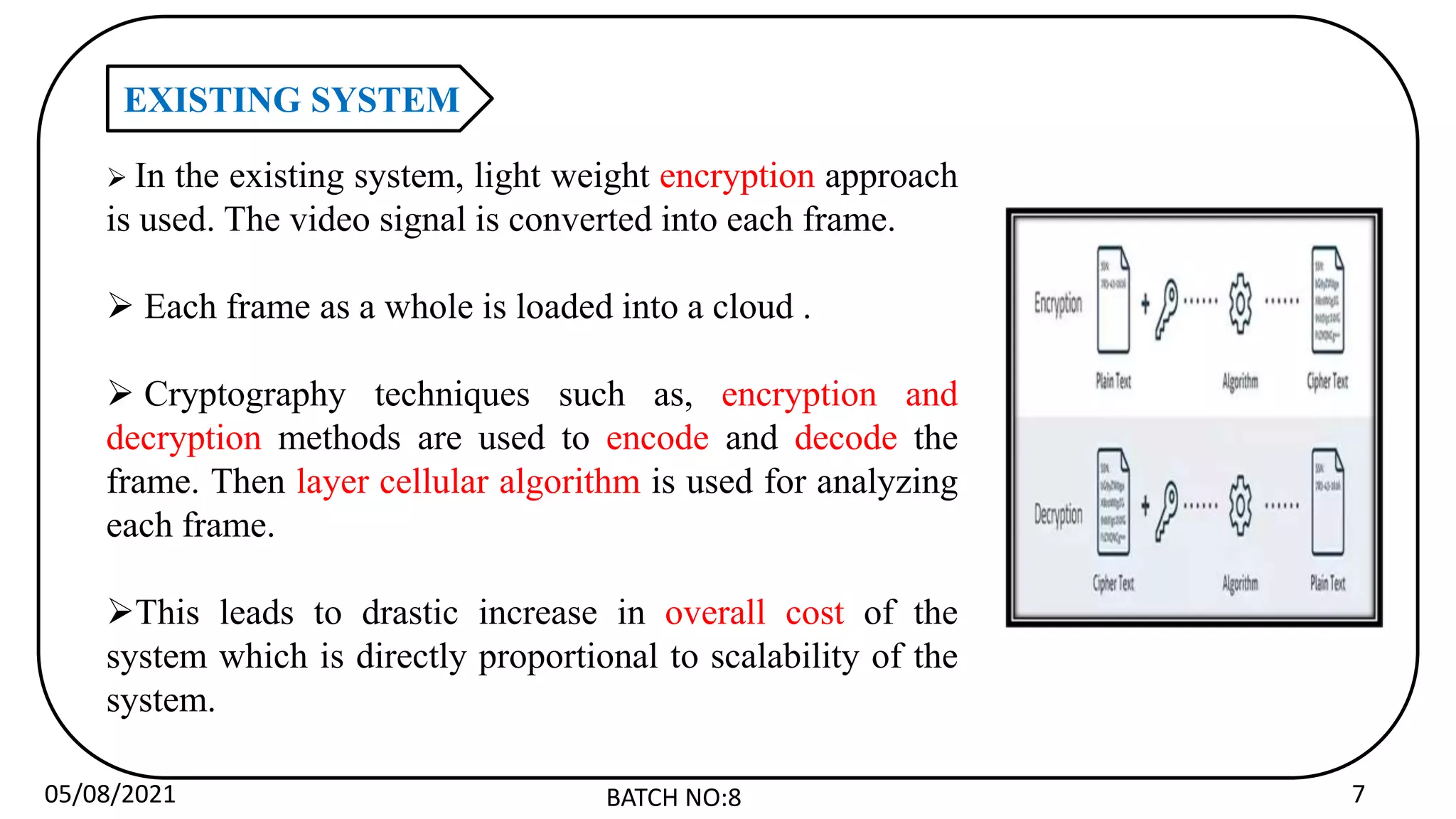
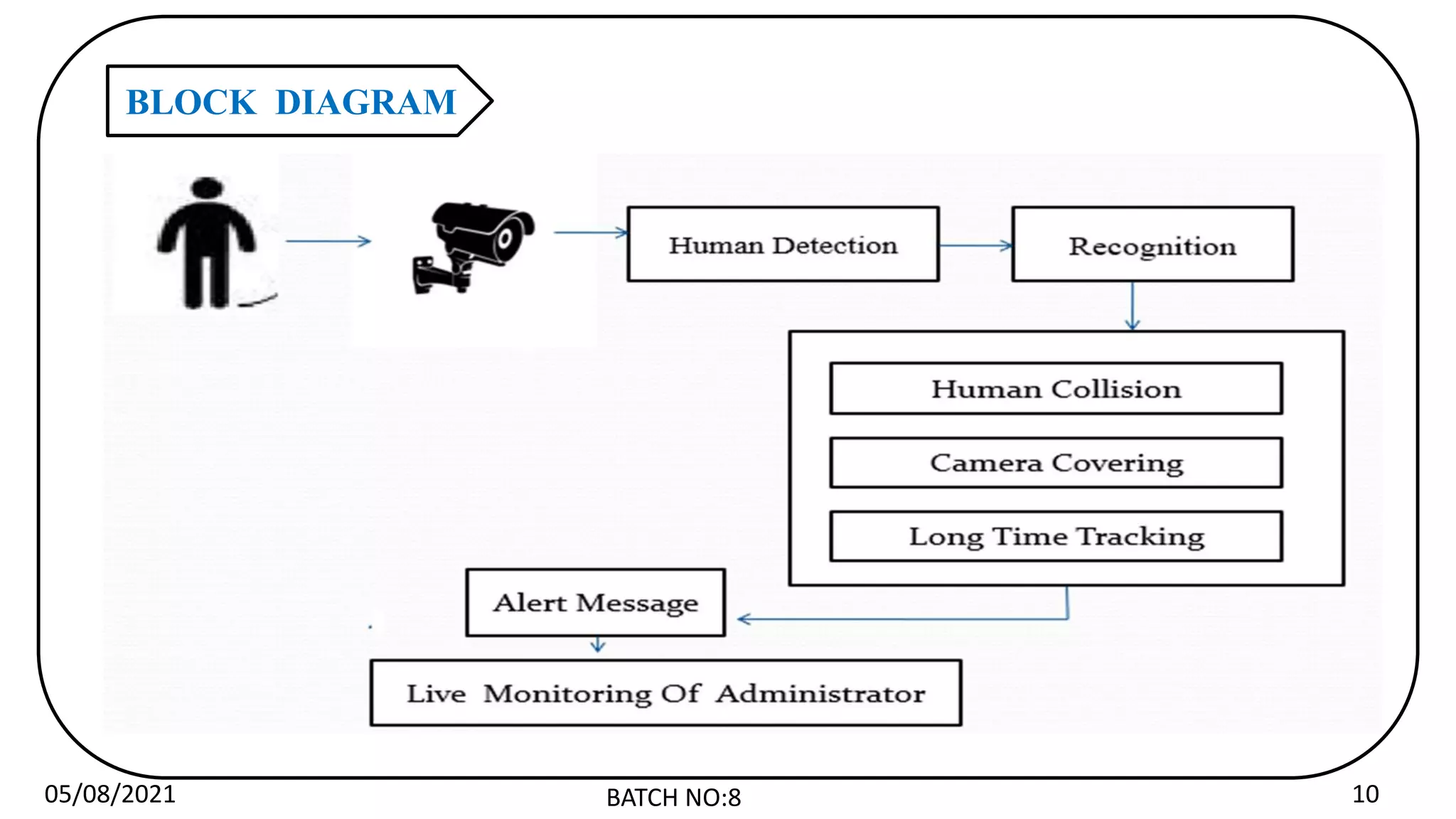
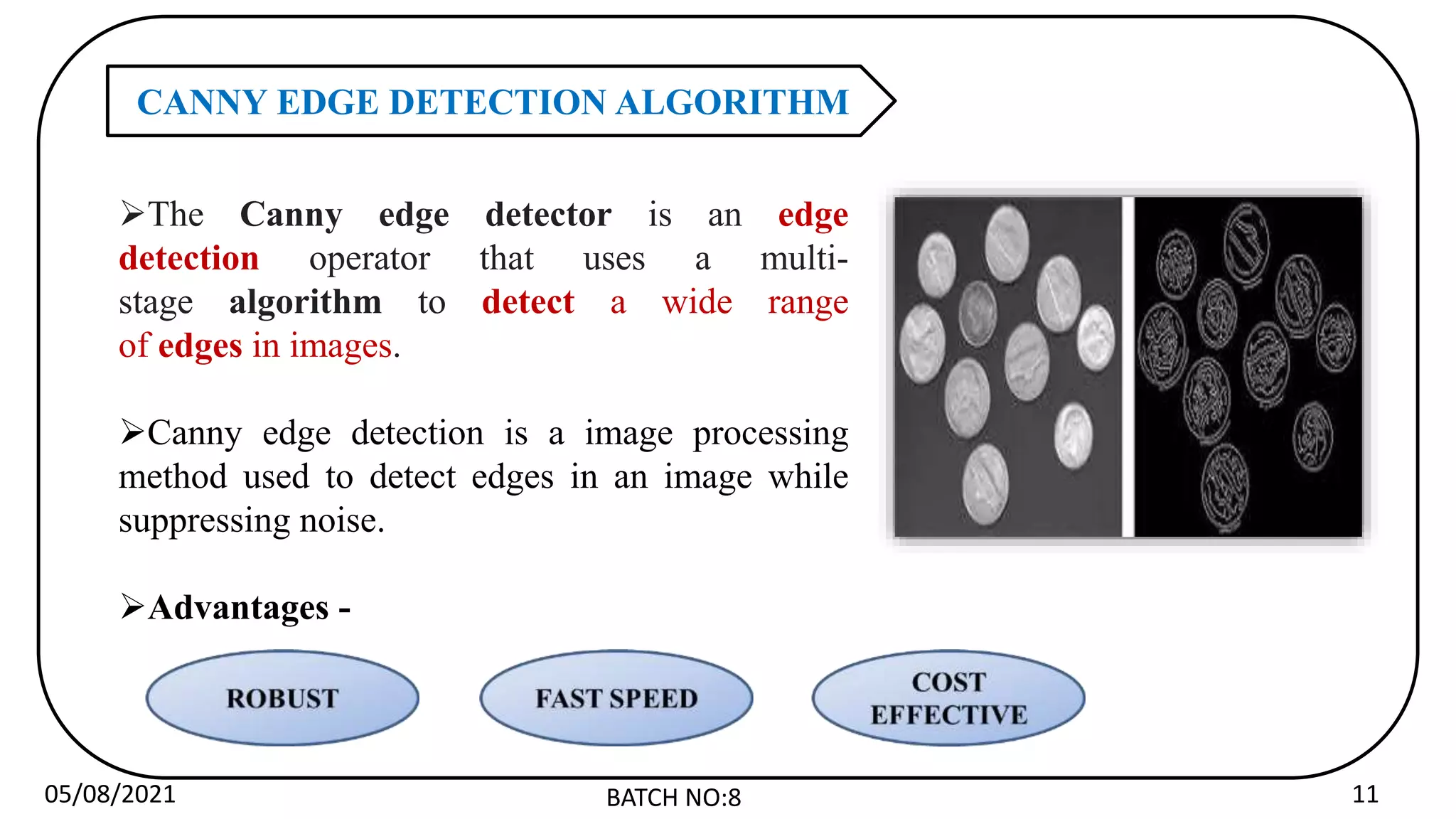
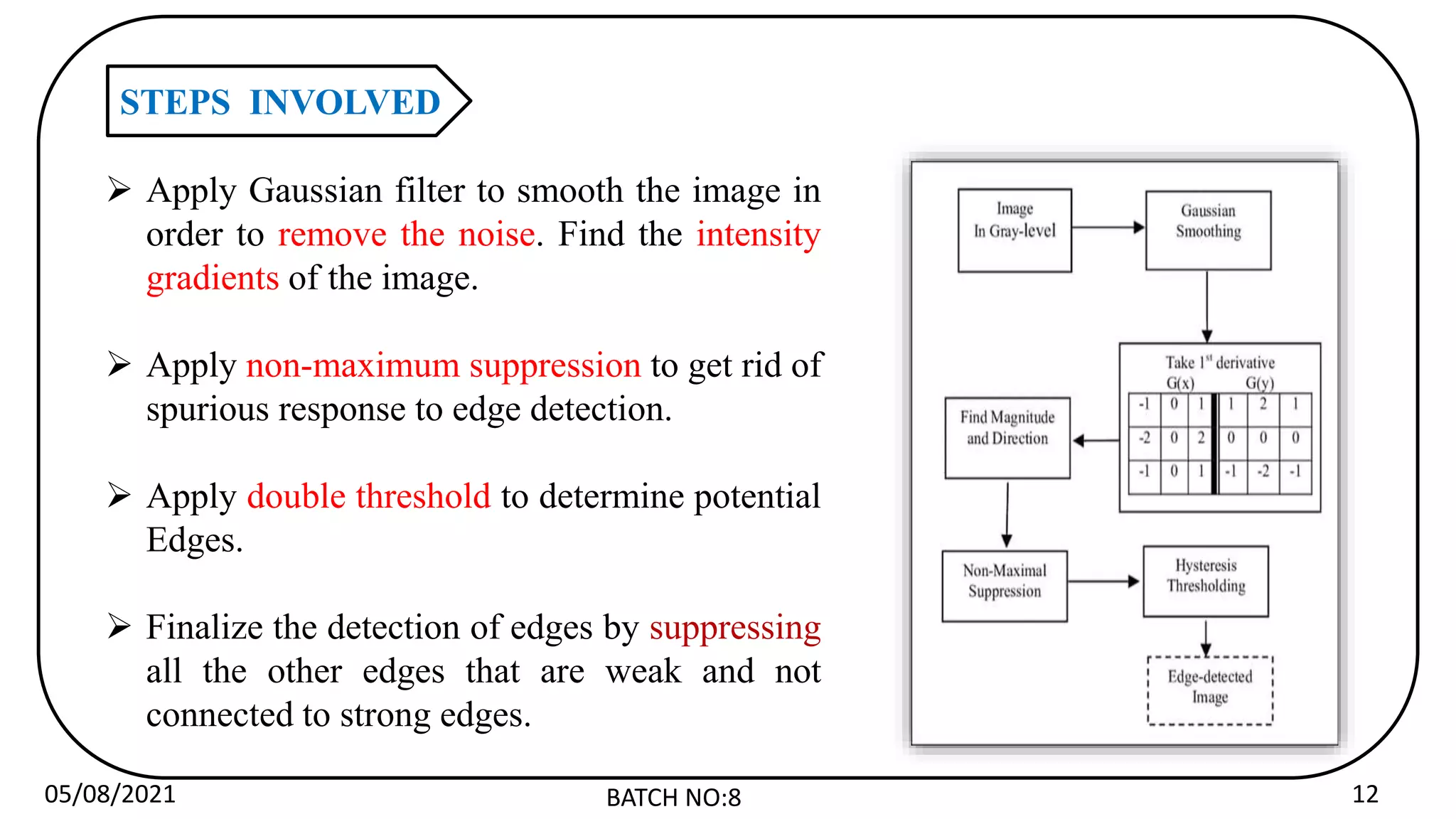
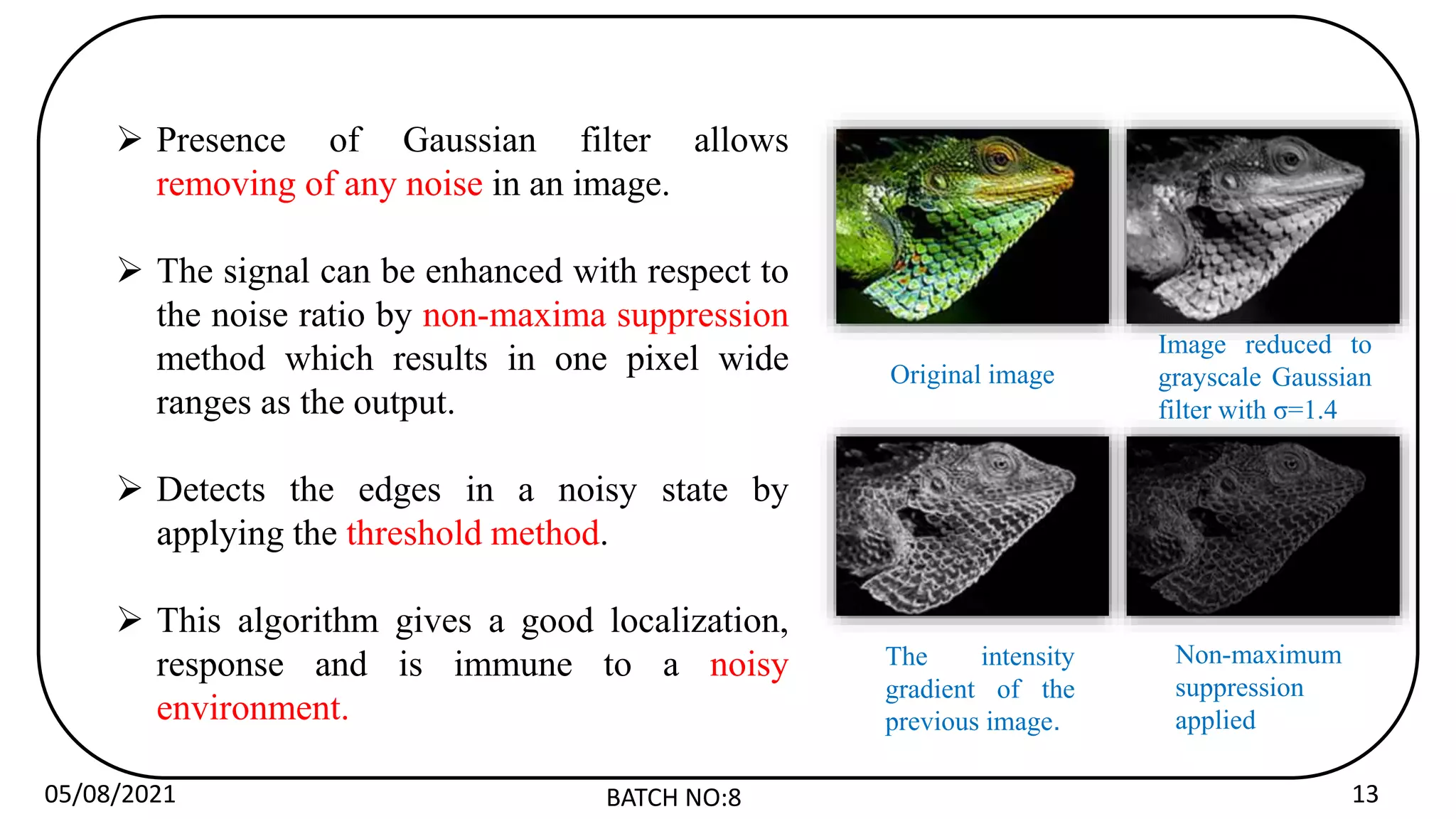
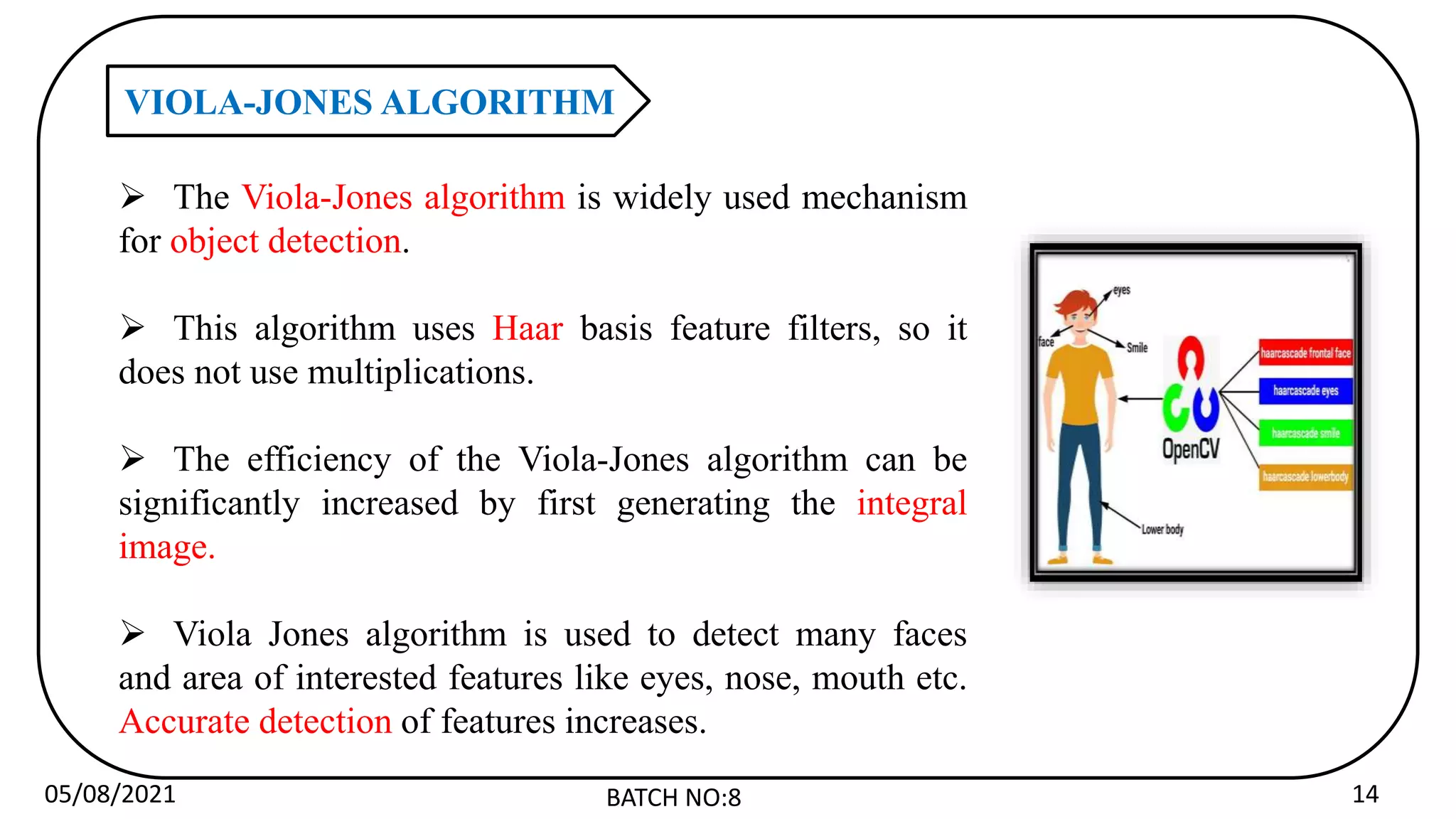
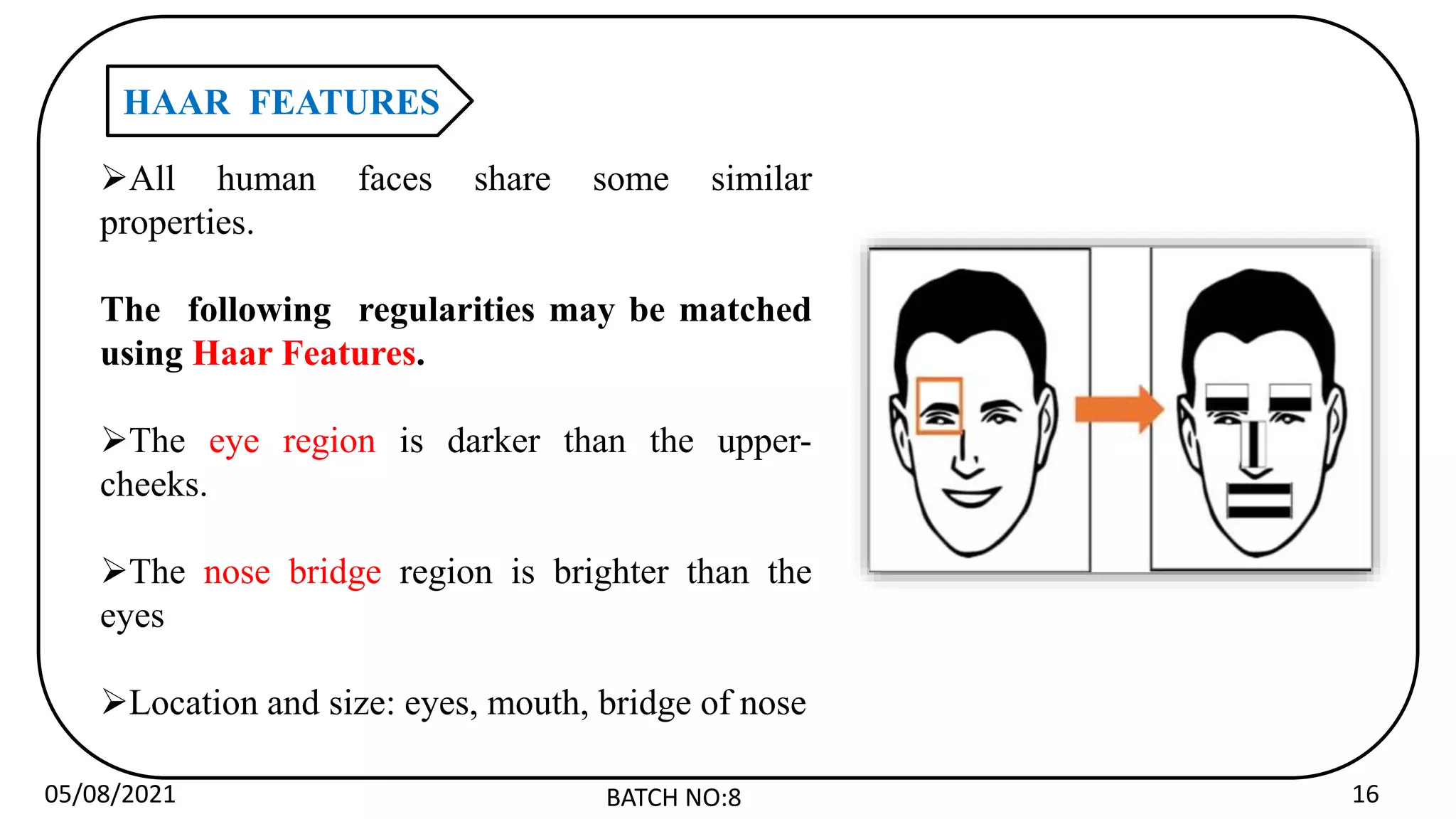
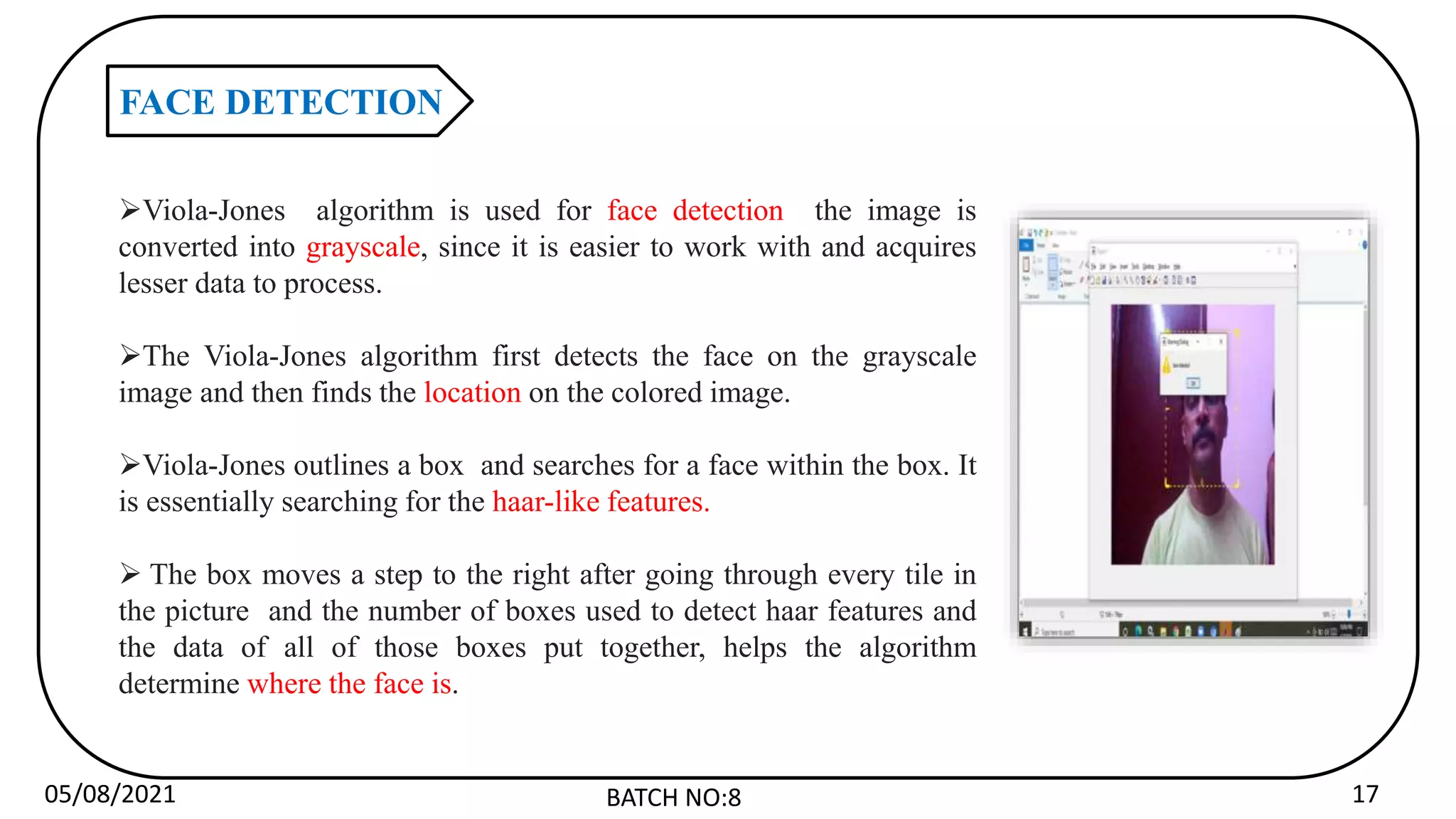
The document describes a proposed system for theft prevention using artificial intelligence and credibility-based suspicious behavior recognition in video surveillance. The system aims to identify suspicious behaviors and generate alerts before theft occurs. It will use computer vision techniques like Canny edge detection and Viola-Jones face detection algorithms to analyze video feeds in real-time and detect behaviors like camera tampering, collisions between people, and long durations of tracking individuals. The system is intended to automate video surveillance in critical areas and improve security over traditional approaches.
![05/08/2021 BATCH NO:8 27
REFERENCES
[1] H. He and E. A. Garcia, “Learning from imbalanced data,” IEEE Transactions on Knowledge
and Data Engineering, vol. 21, no. 9, pp. 1263–1284, Sept 2009.
[2] S. Zhou, W. Shen, D. Zeng, M. Fang, Y. Wei, and Z. Zhang, “Spatial–temporal convolutional
neural networks for anomaly detection and localization in crowded scenes,” Signal Processing:
Image Communication, vol. 47, pp. 358–368, 2016.
[3] C. Lu, J. Shi, and J. Jia, “Abnormal event detection at 150 fps in matlab,” in Proceedings of the
IEEE International Conference on Computer Vision, 2013, pp. 2720–2727.
[4] S.-H. Yen and C.-H. Wang, “Abnormal event detection using hosf,” in IT Convergence and
Security (ICITCS), 2013 International Conference on. IEEE, 2013, pp. 1–4.
[5] X. Zhu, J. Liu, J. Wang, C. Li, and H. Lu, “Sparse representation for robust abnormality
detection in crowded scenes,” Pattern Recognition, vol. 47, no. 5, pp. 1791–1799, 2014.](https://image.slidesharecdn.com/newppt-221215160129-b77e07b6/75/new-ppt-pptx-27-2048.jpg)