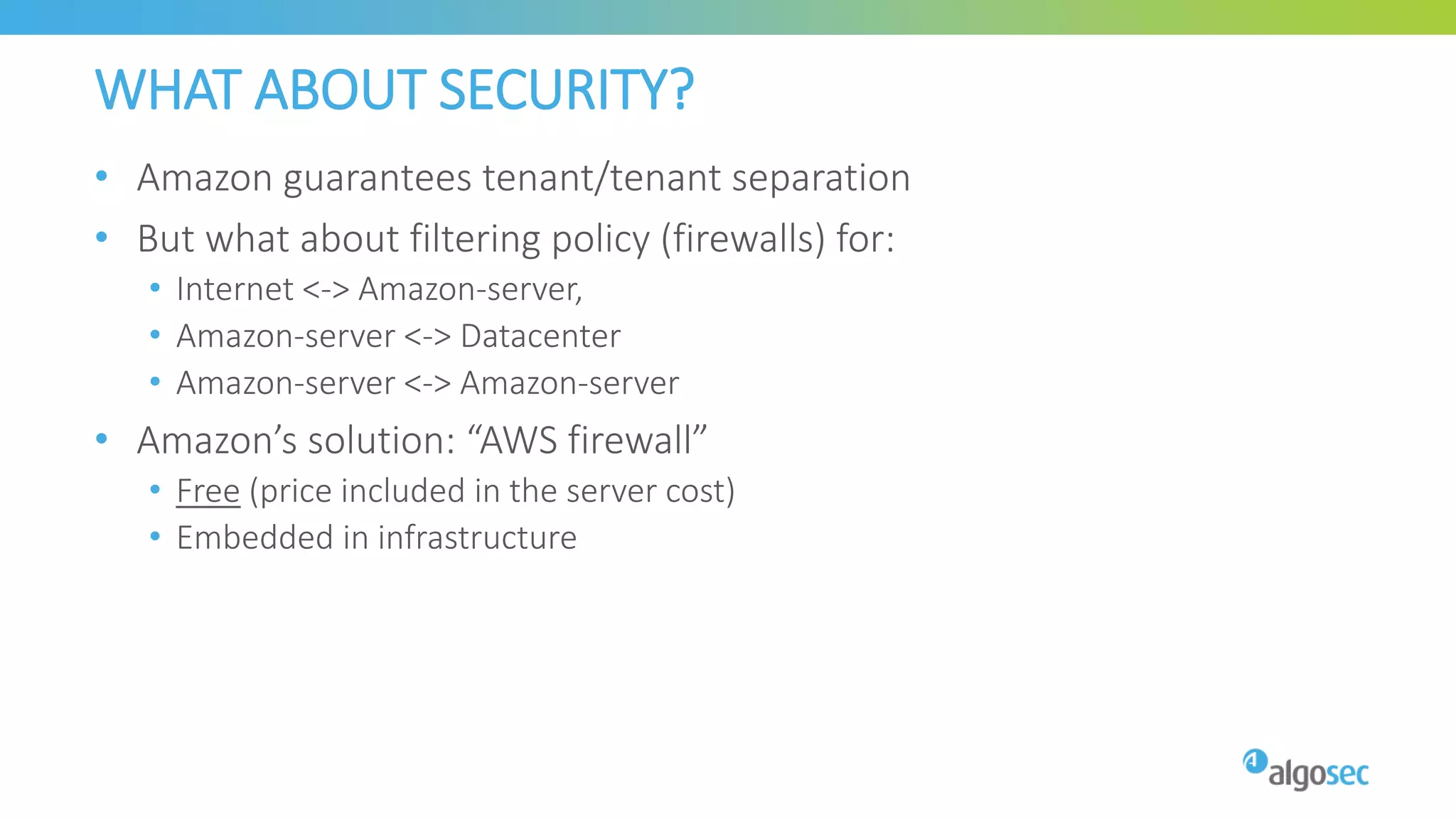
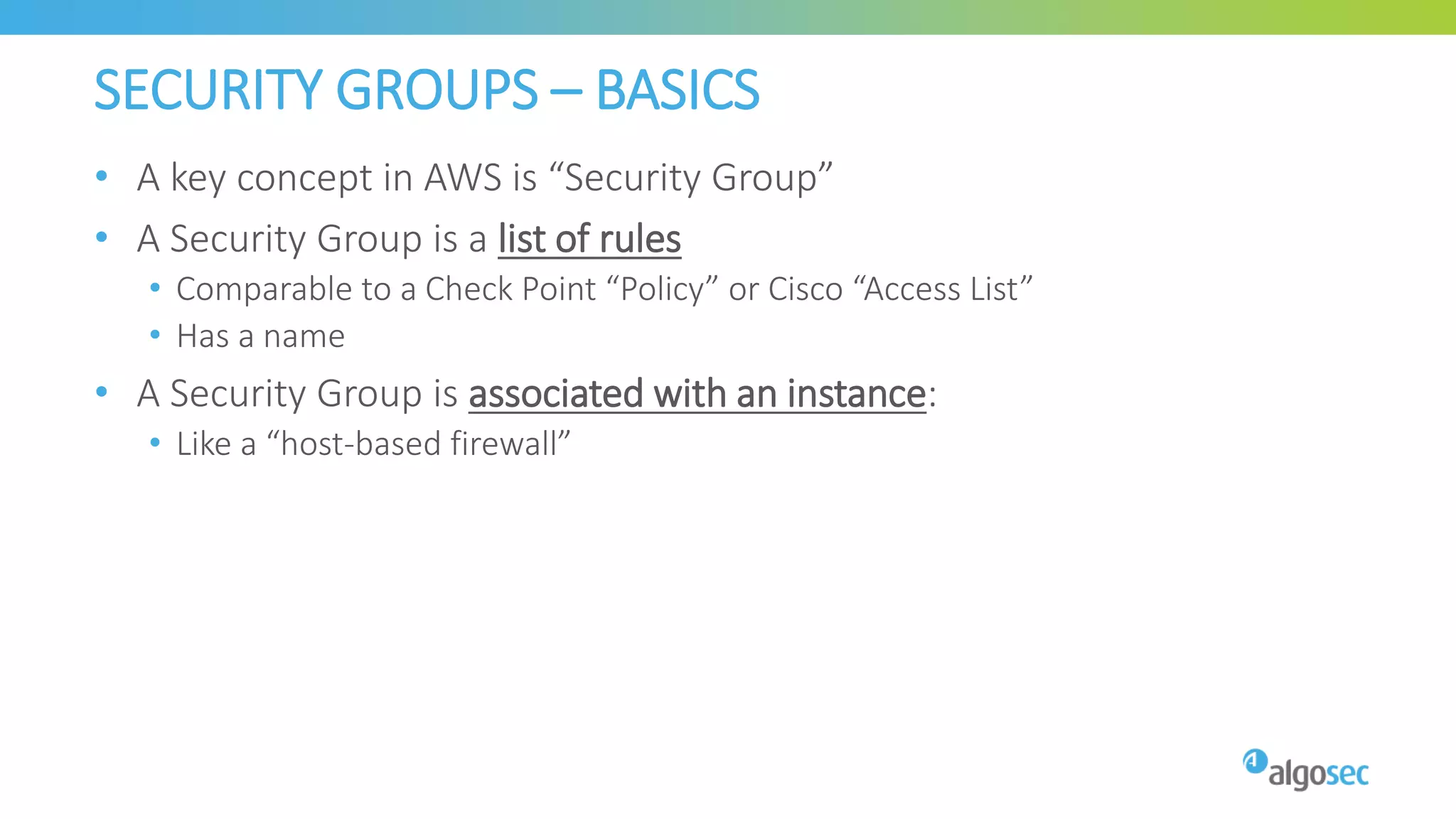
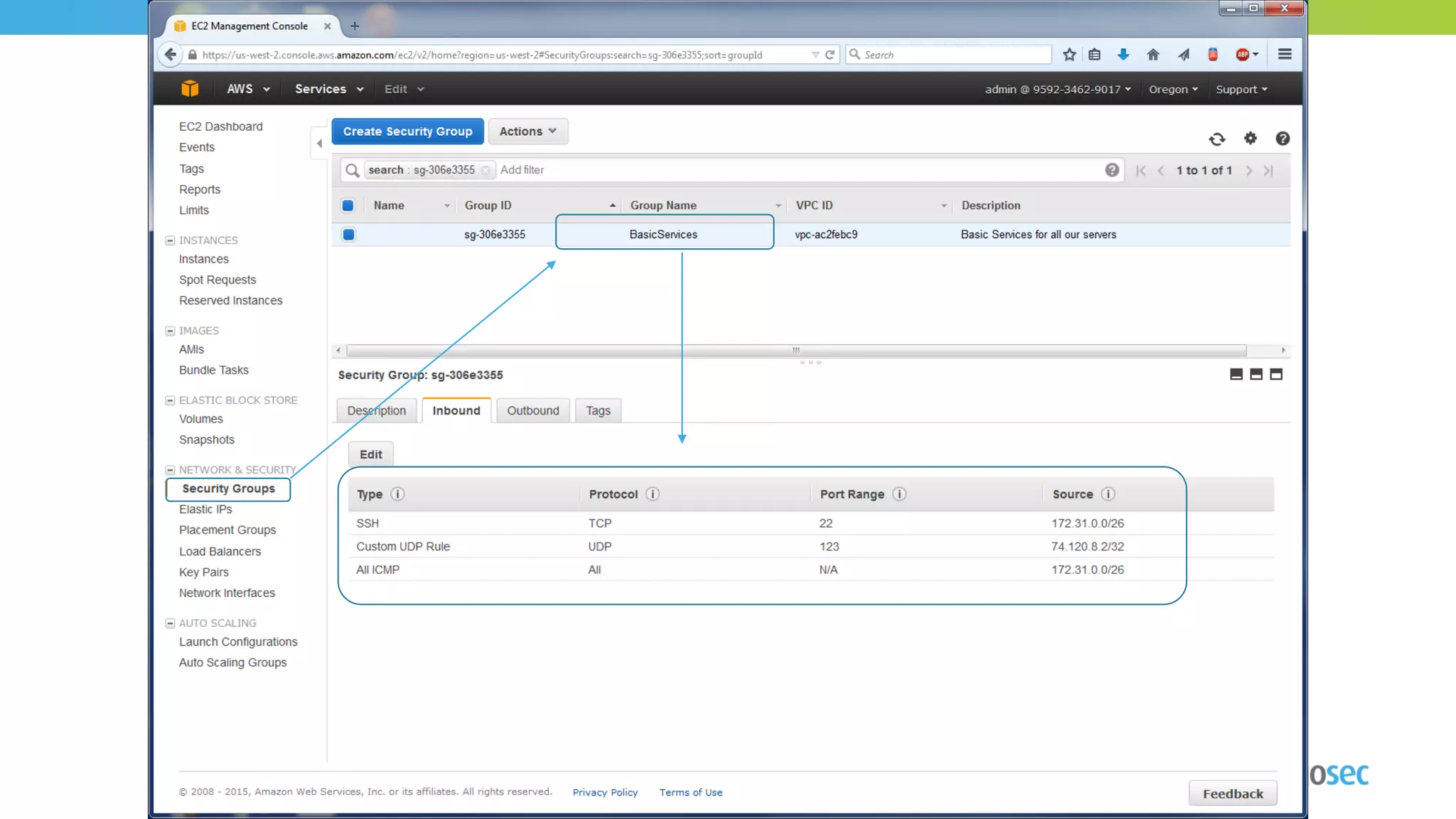
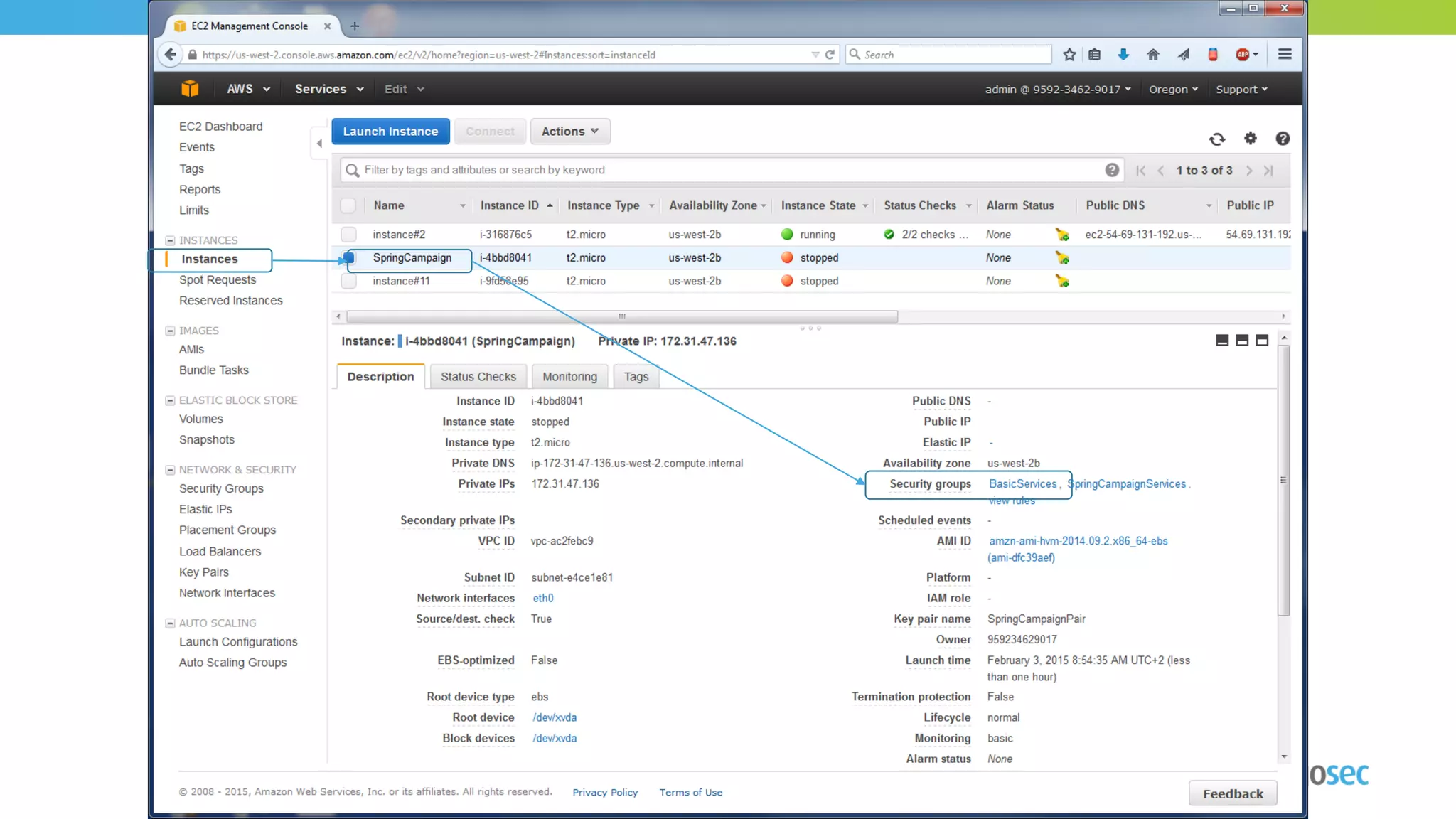
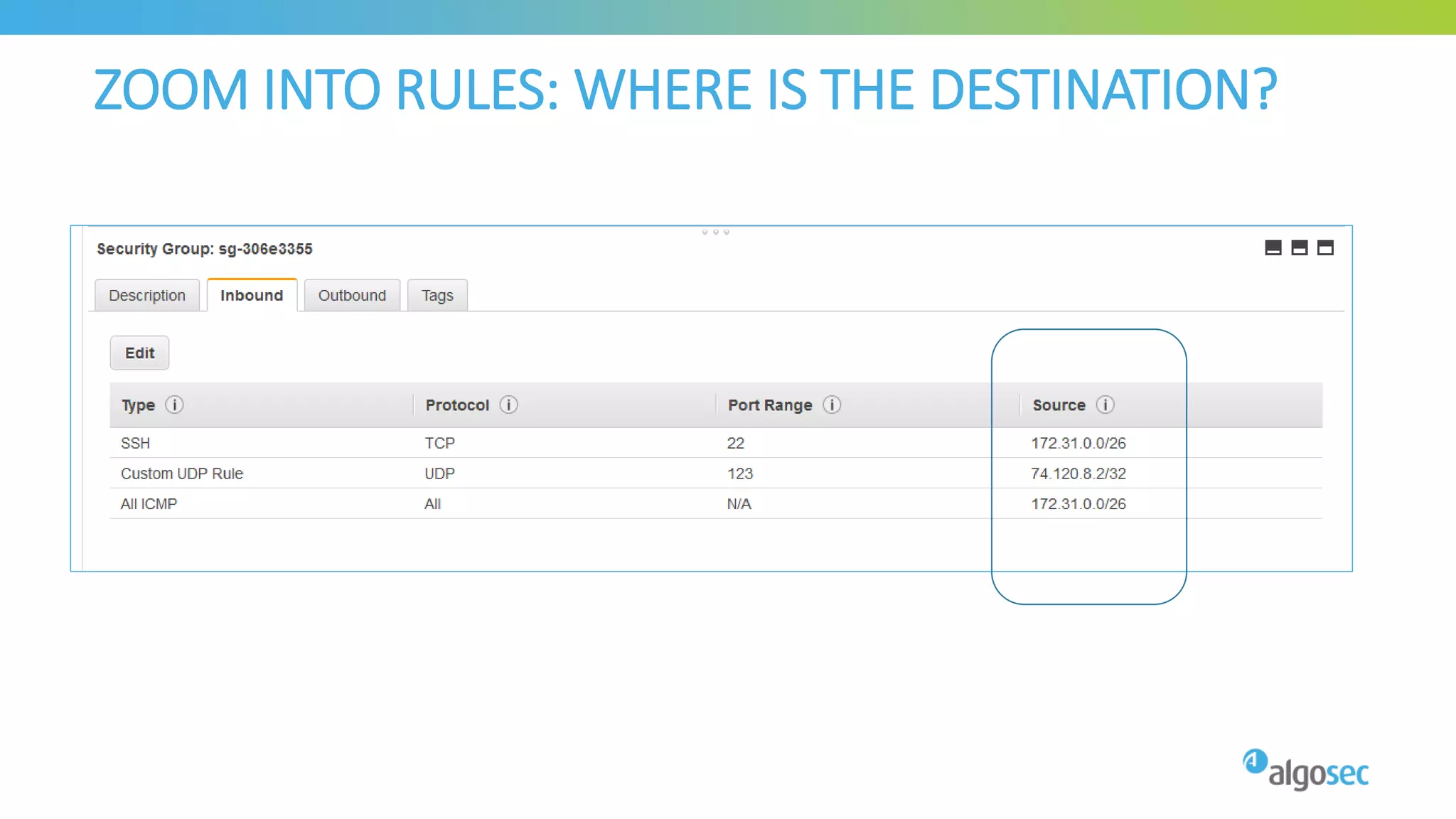
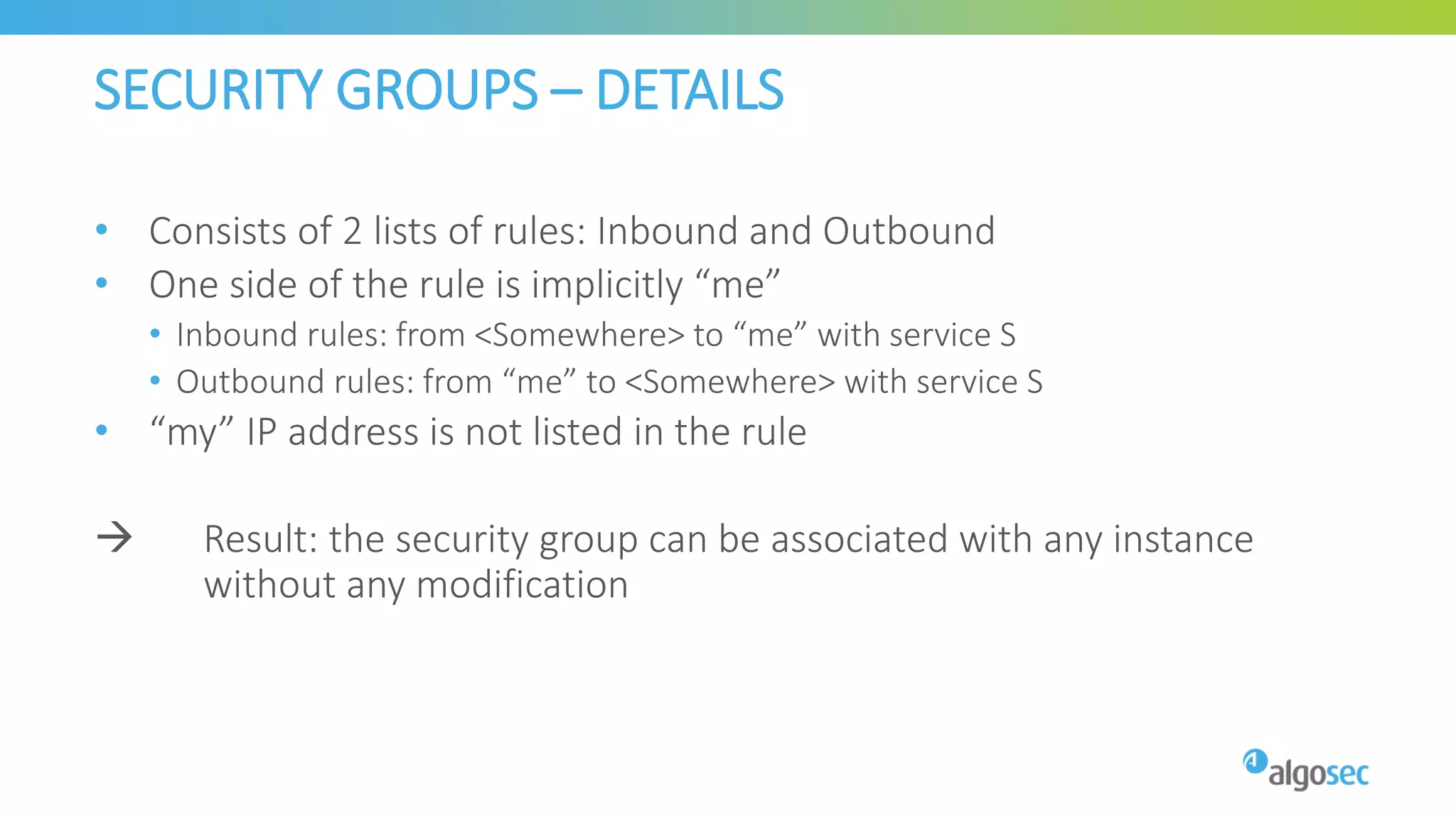
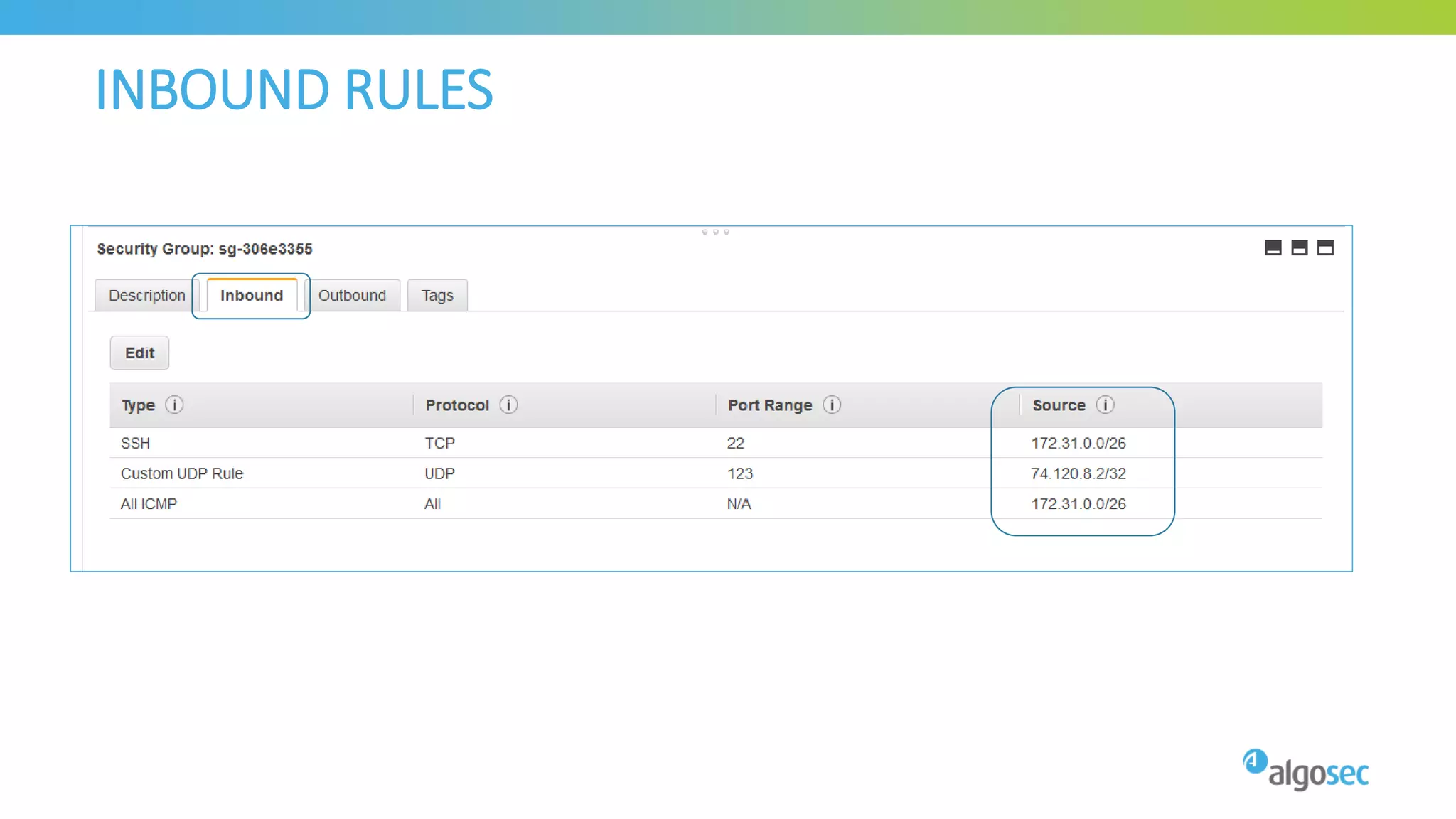
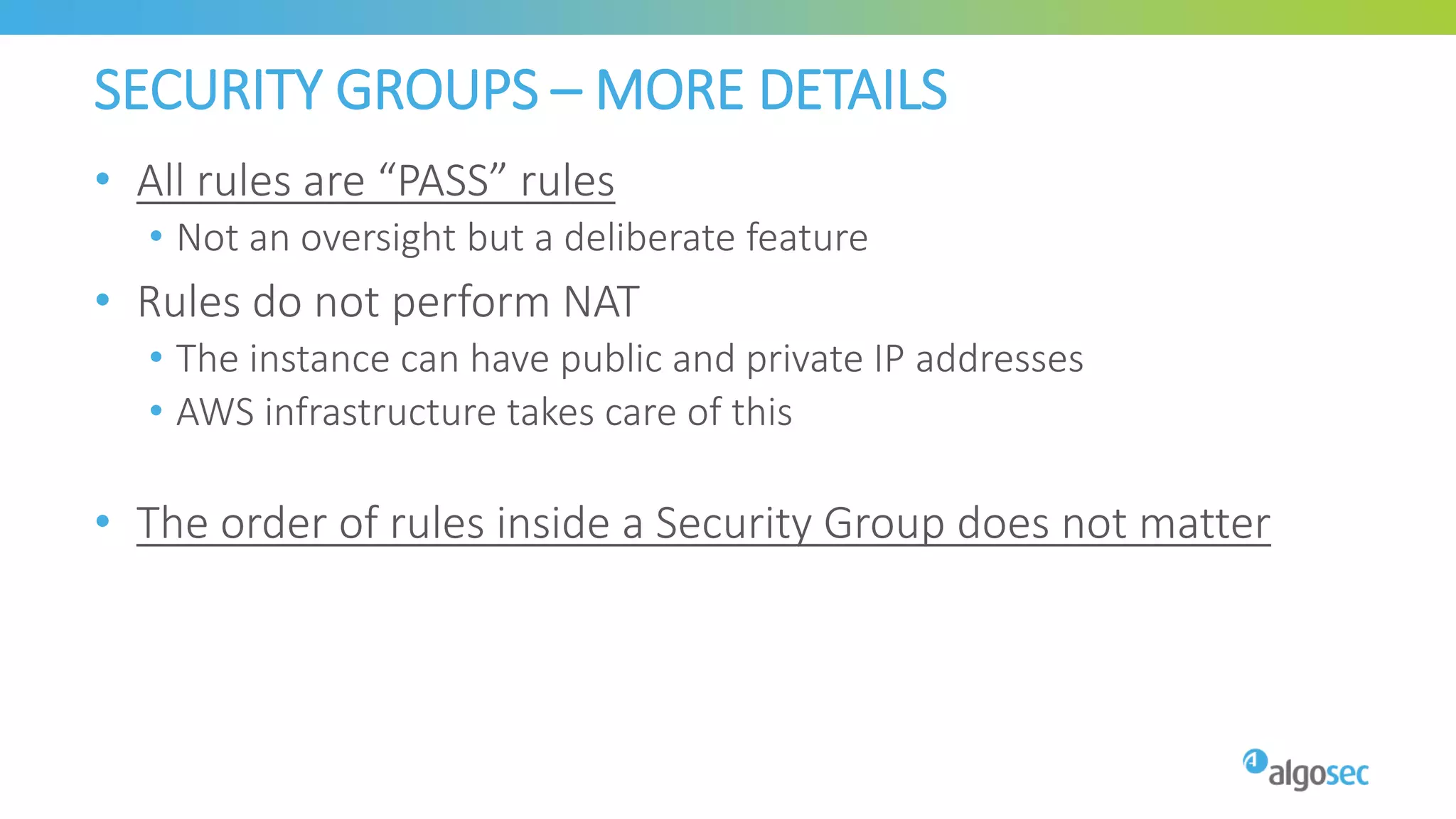
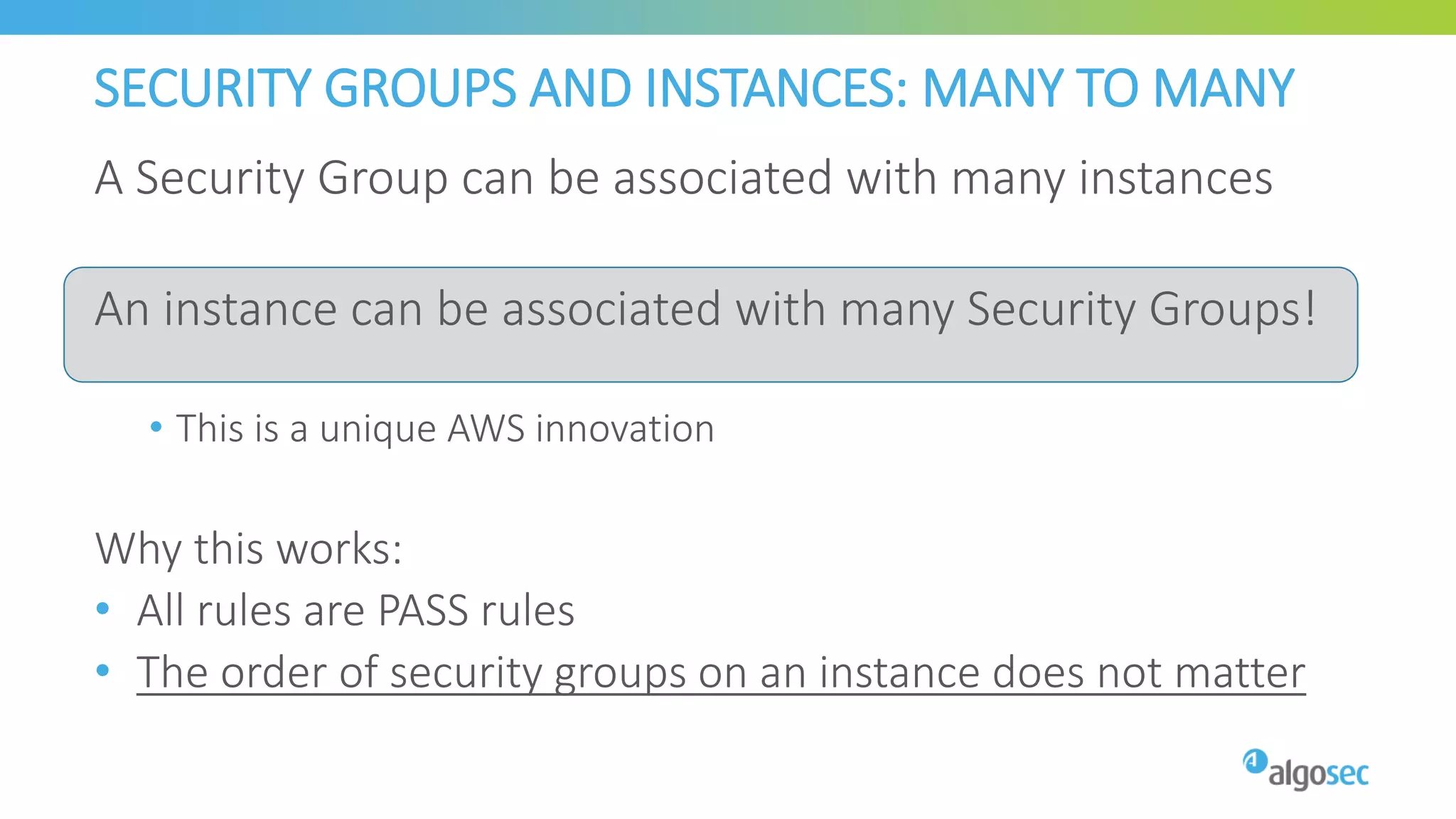
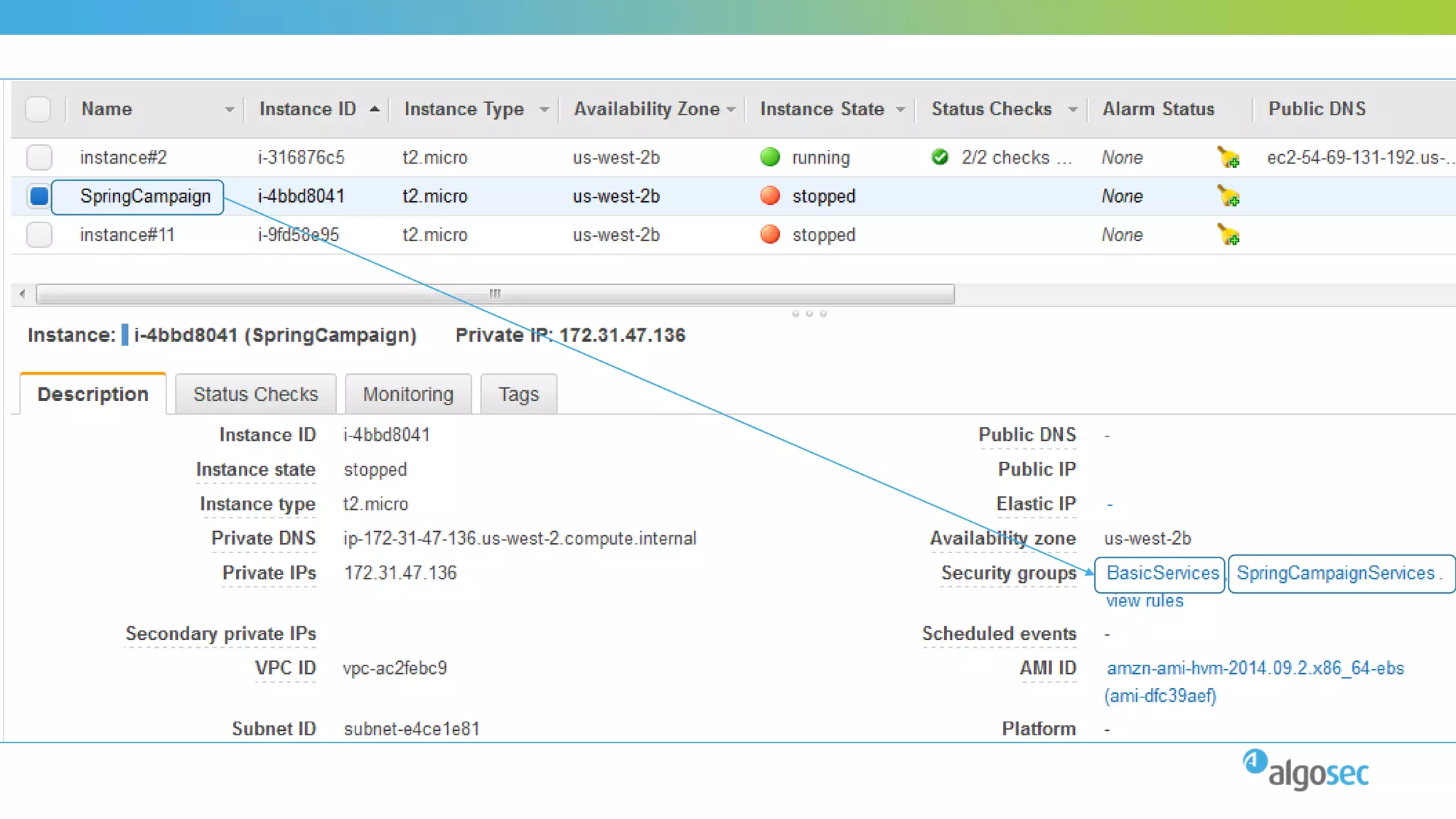
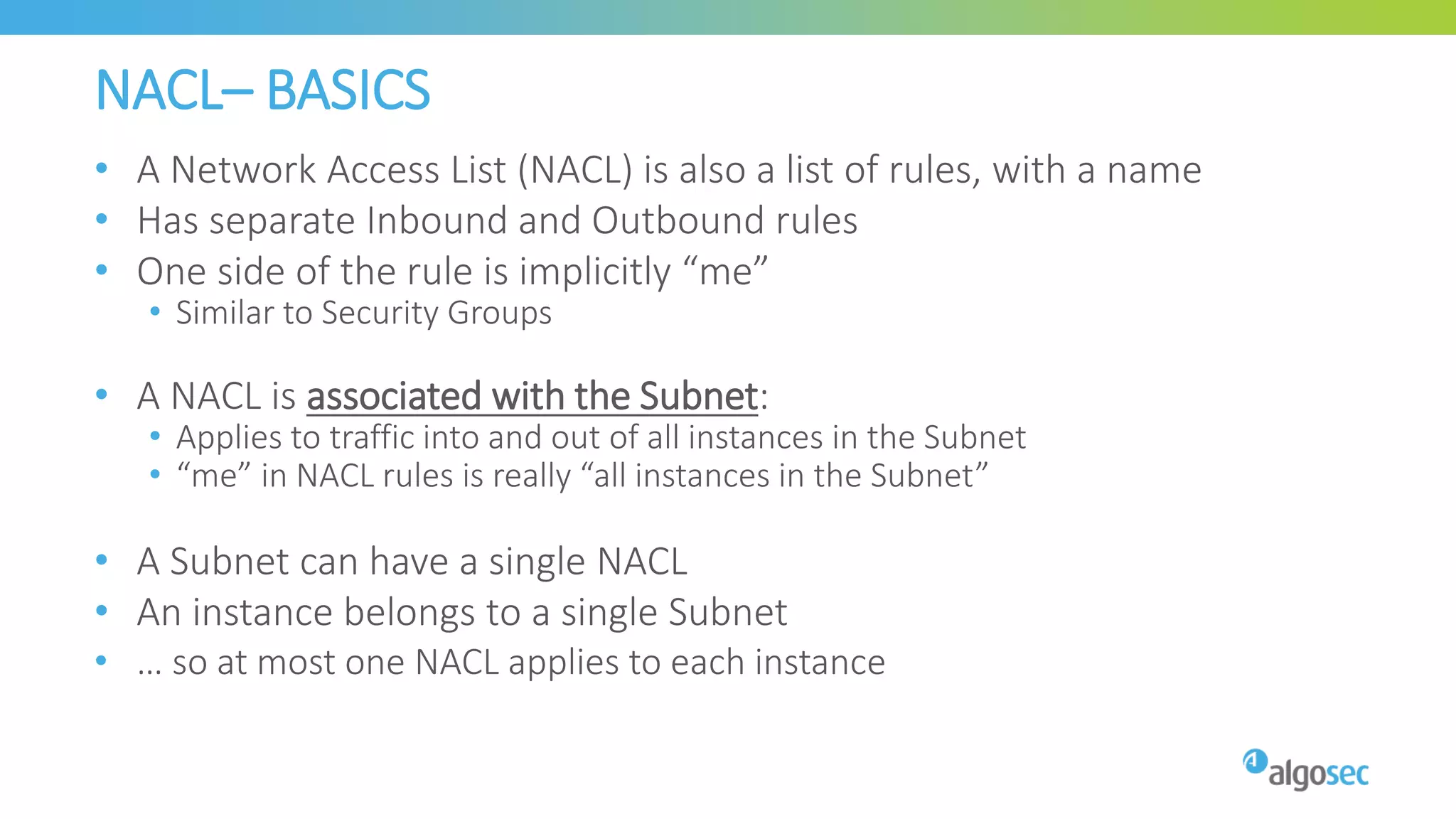
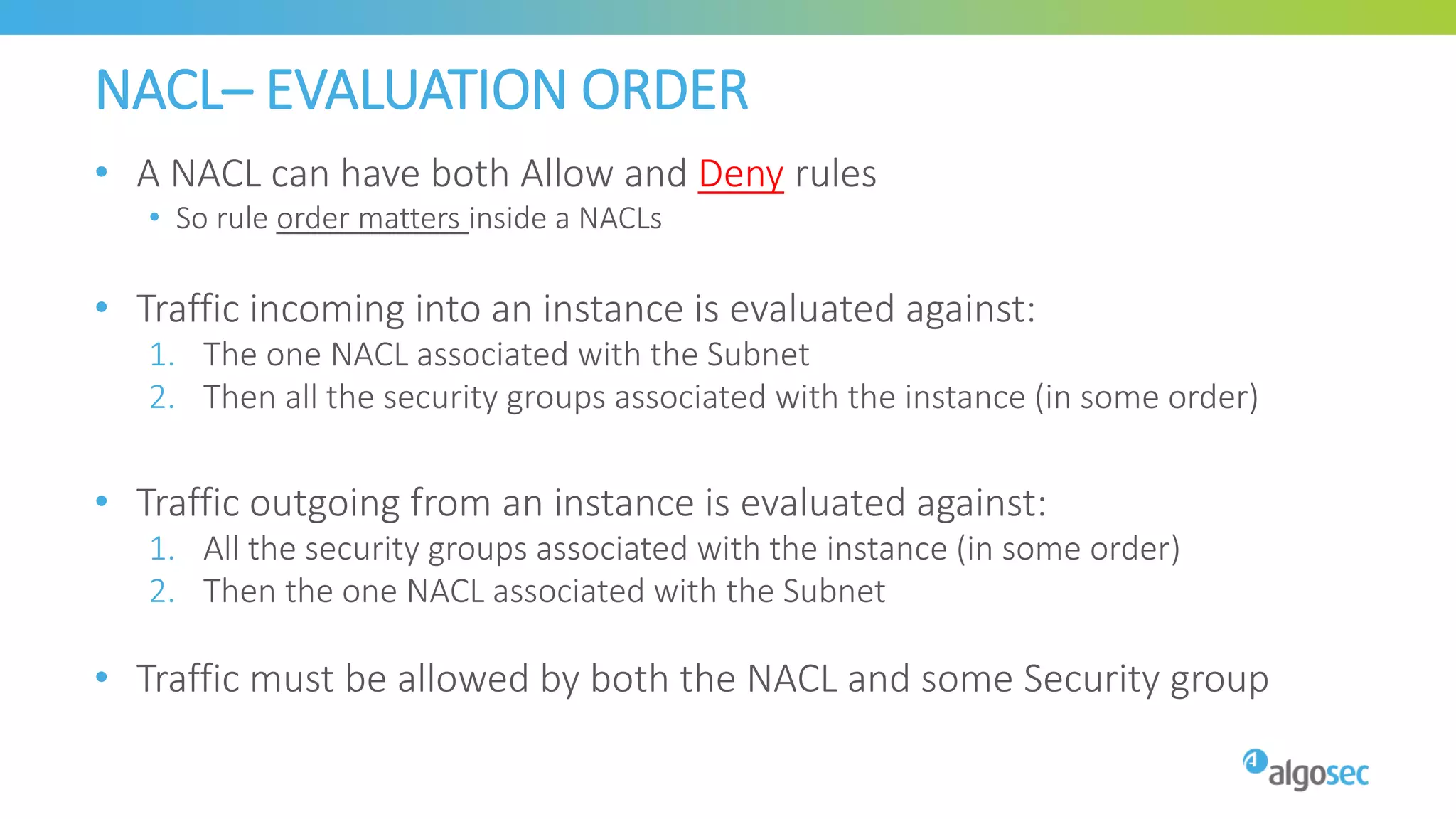
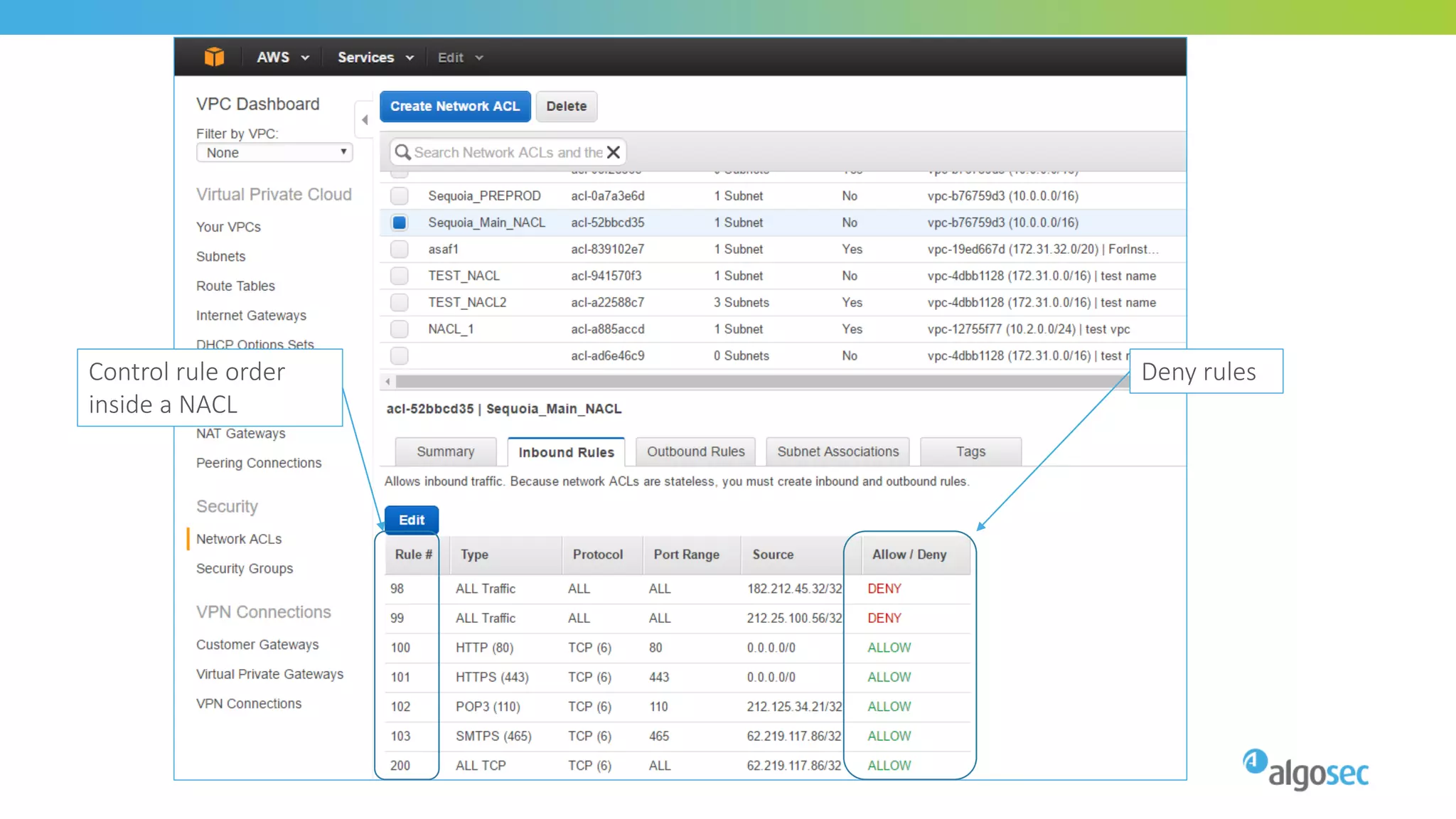
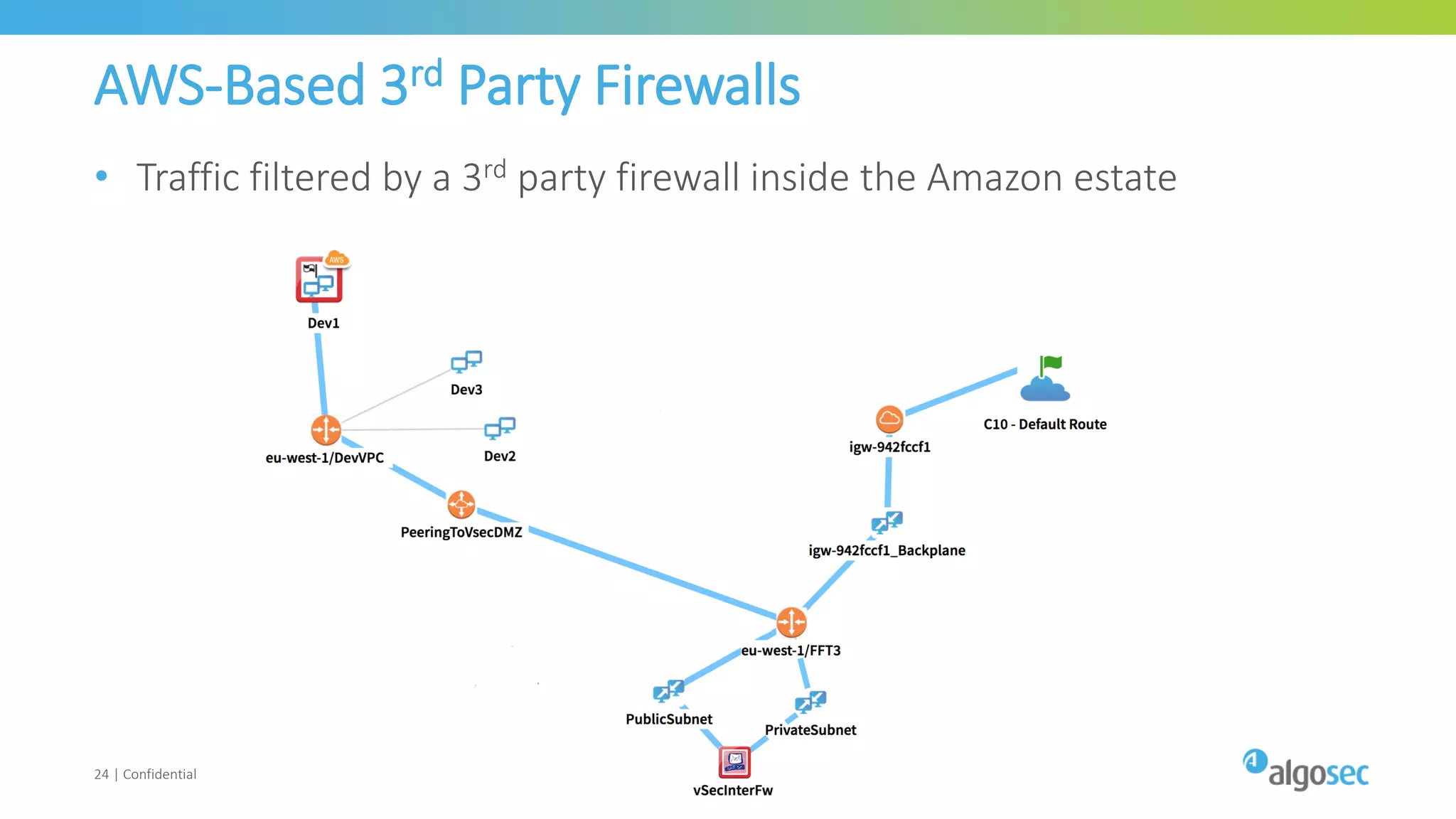
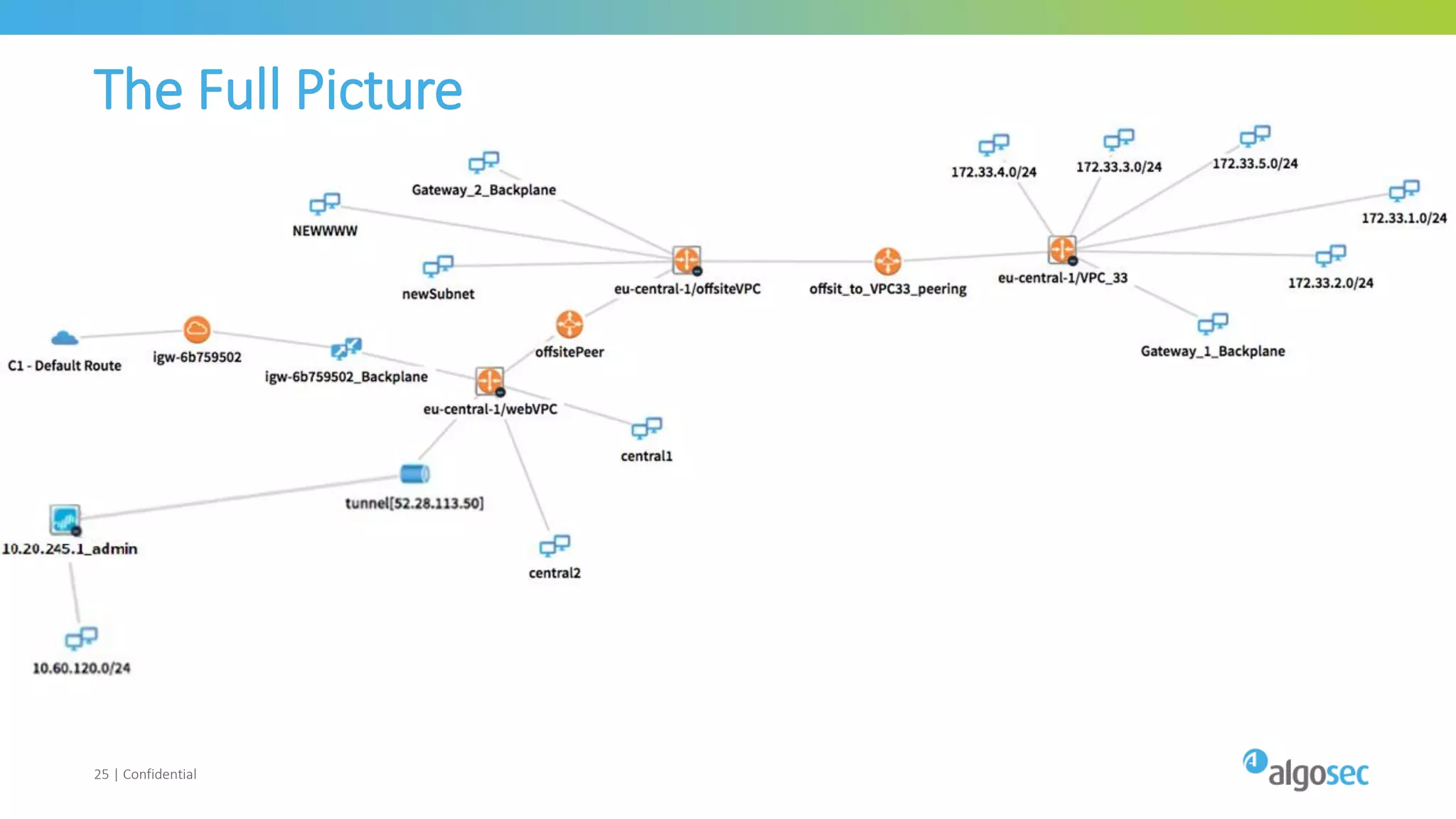
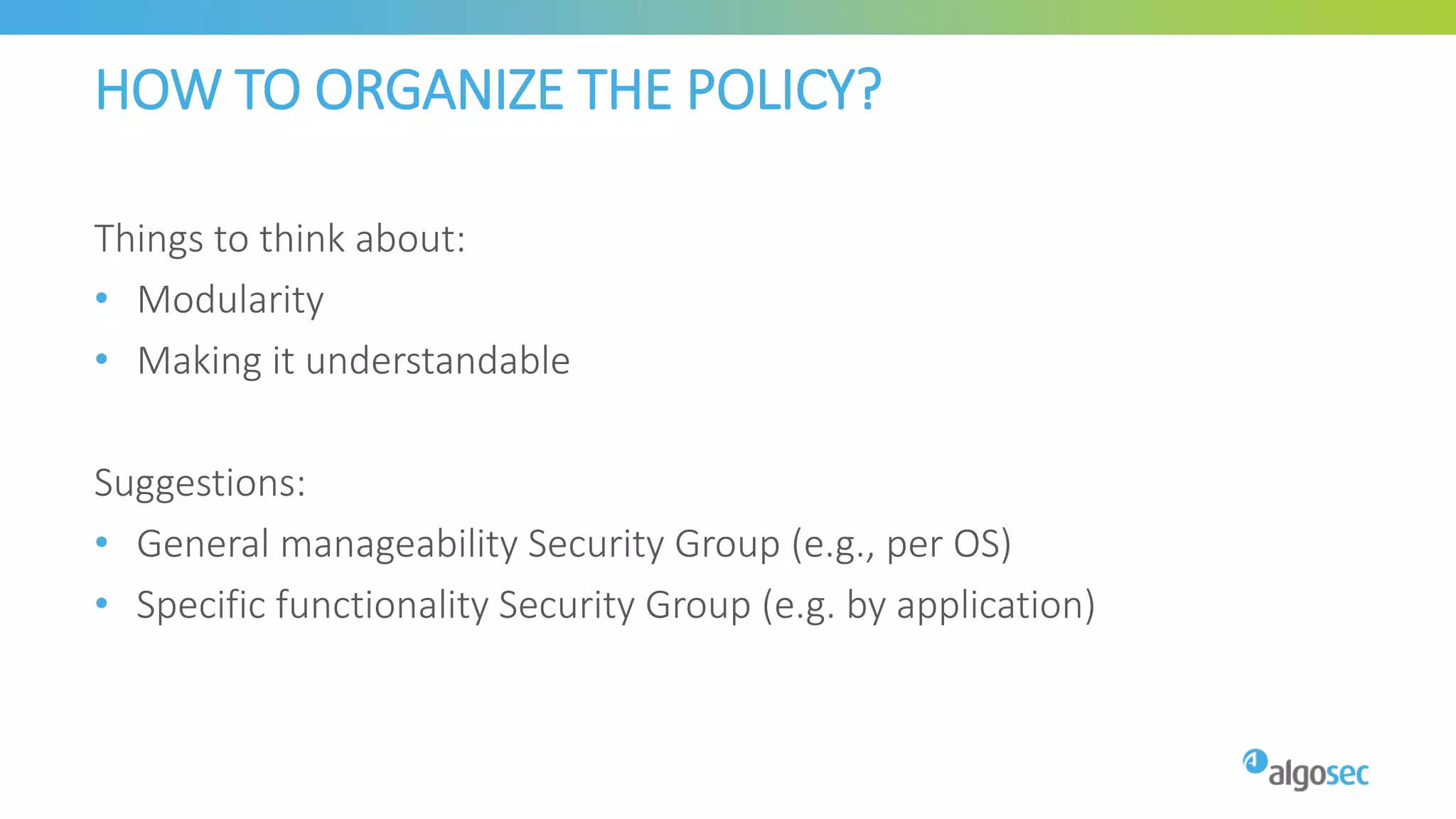
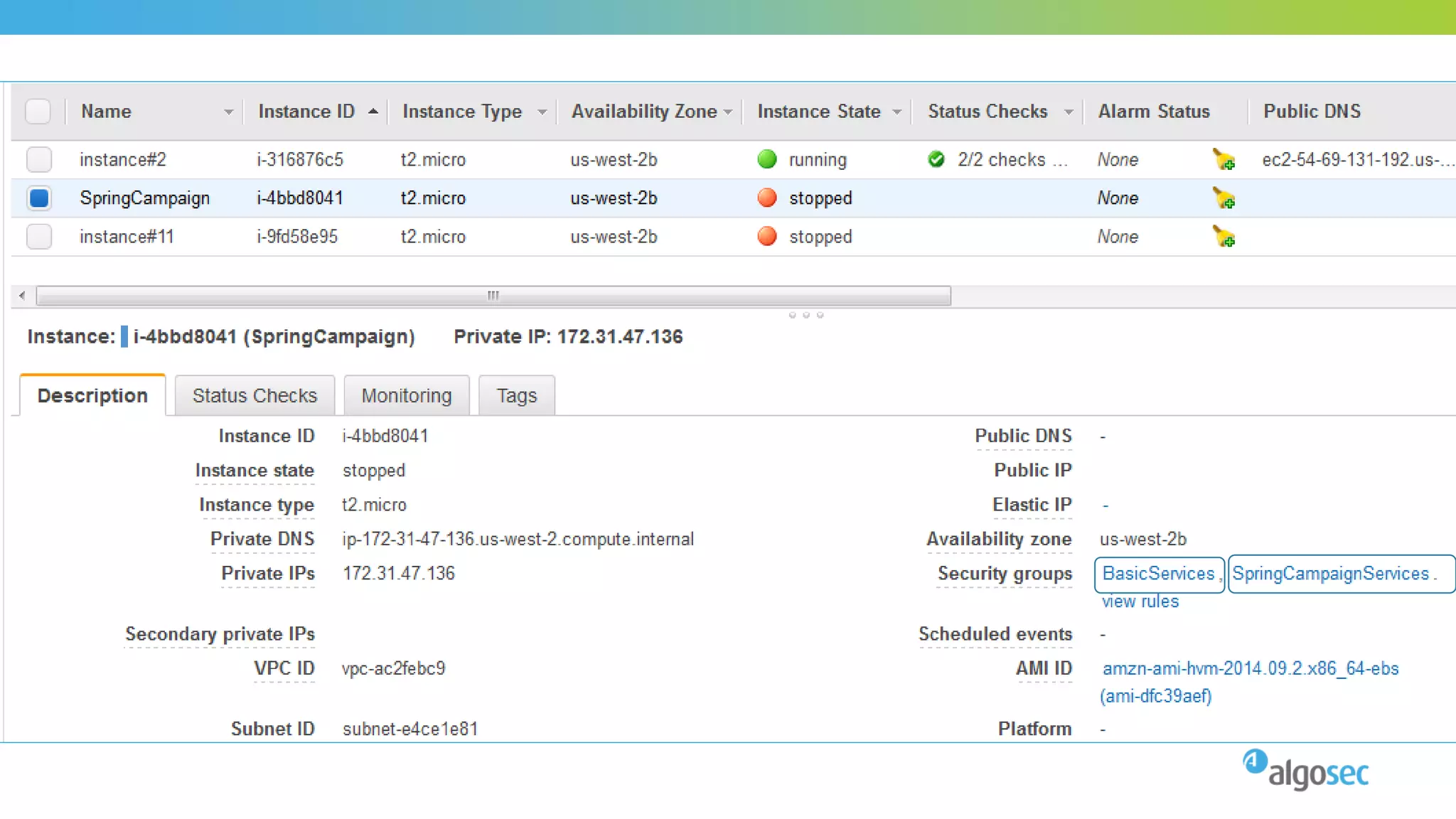
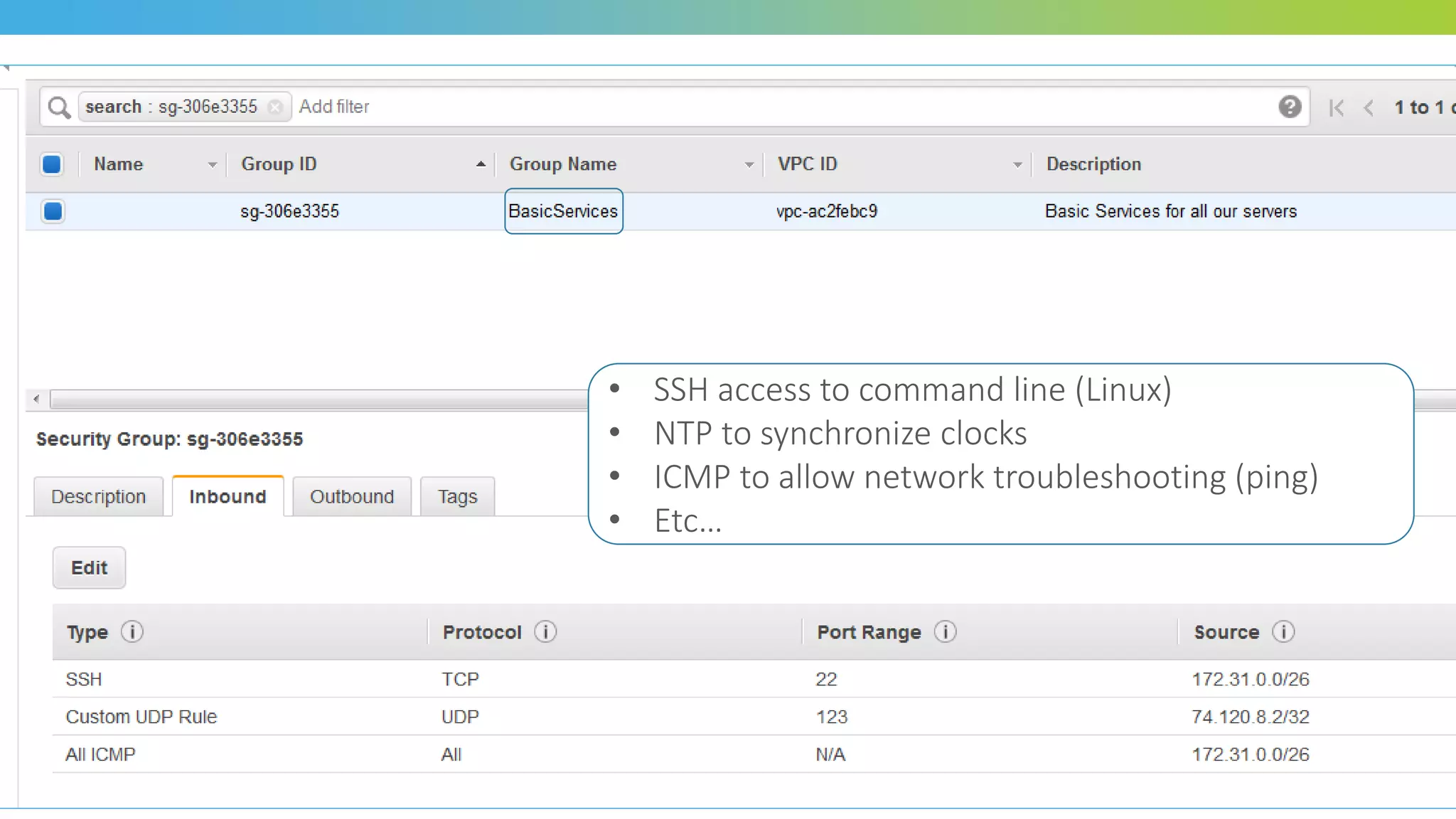
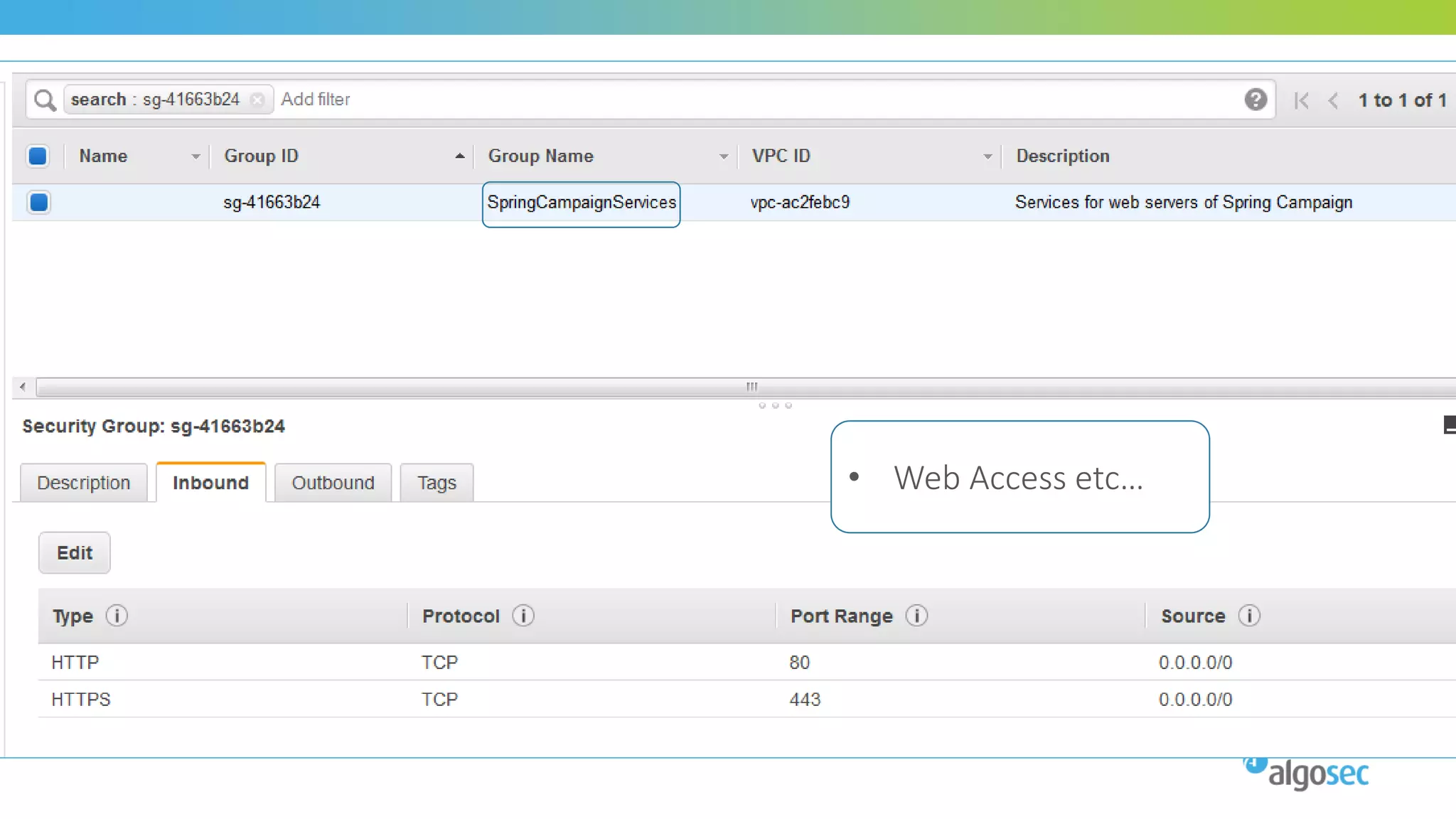
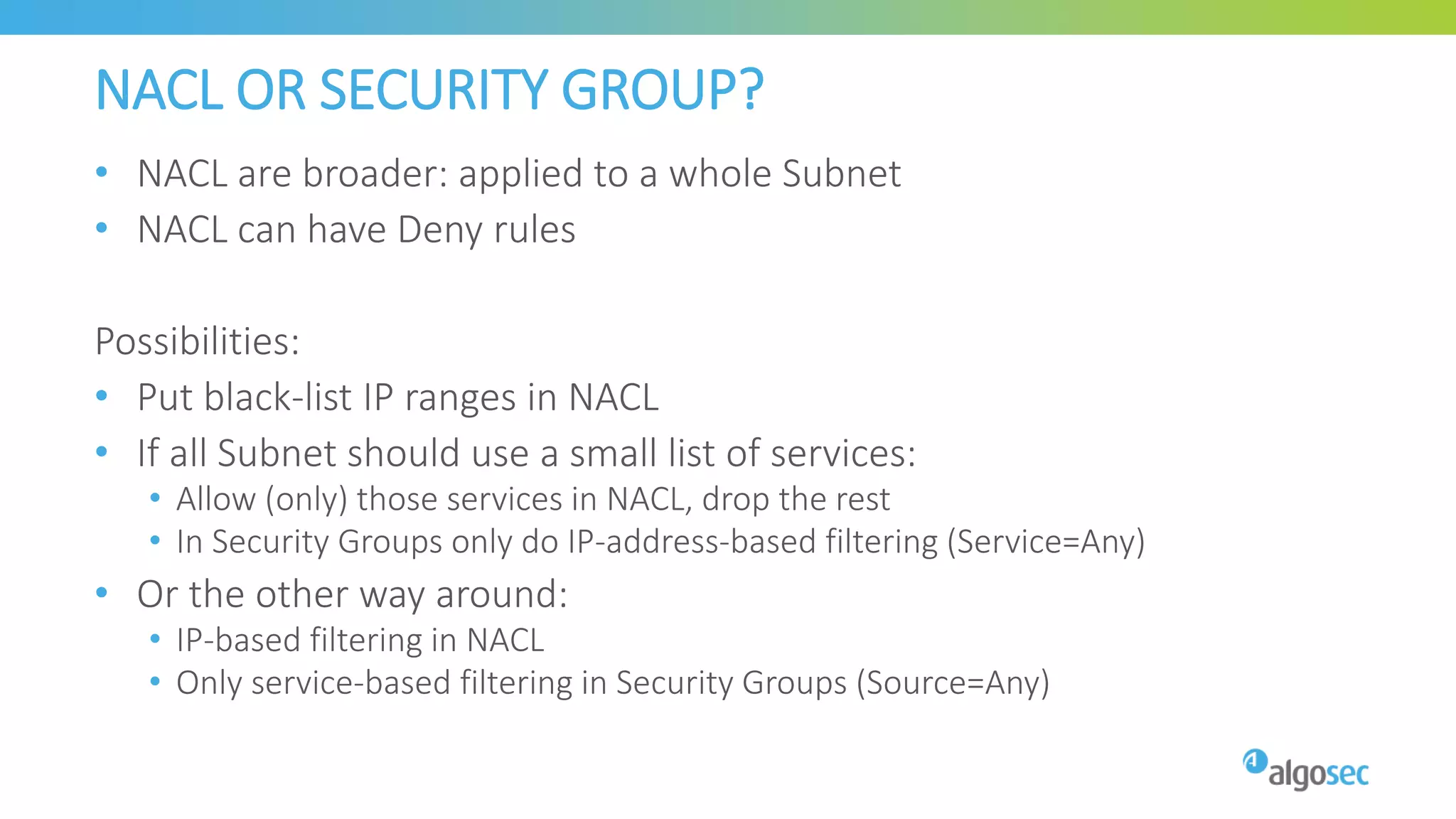
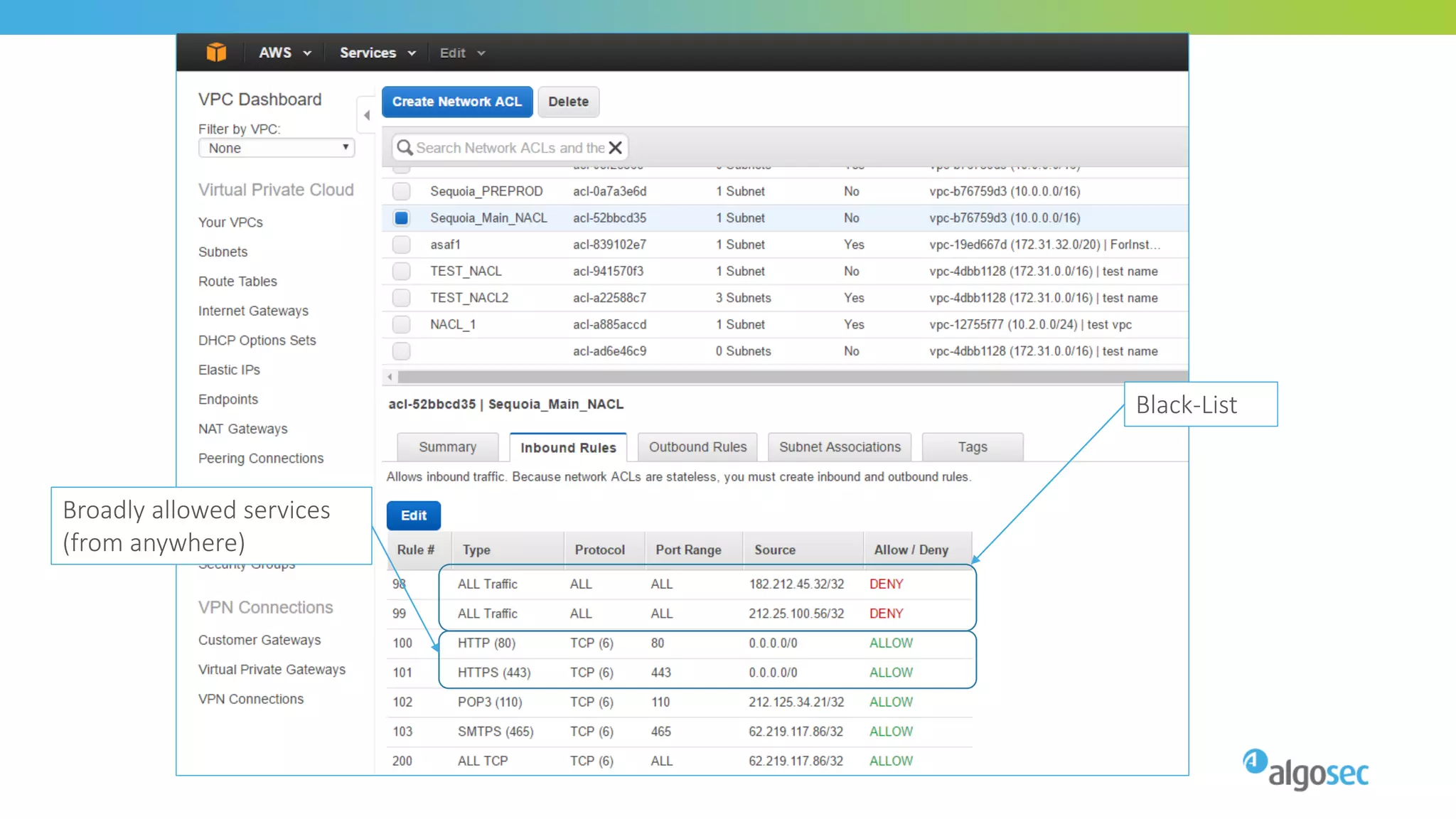
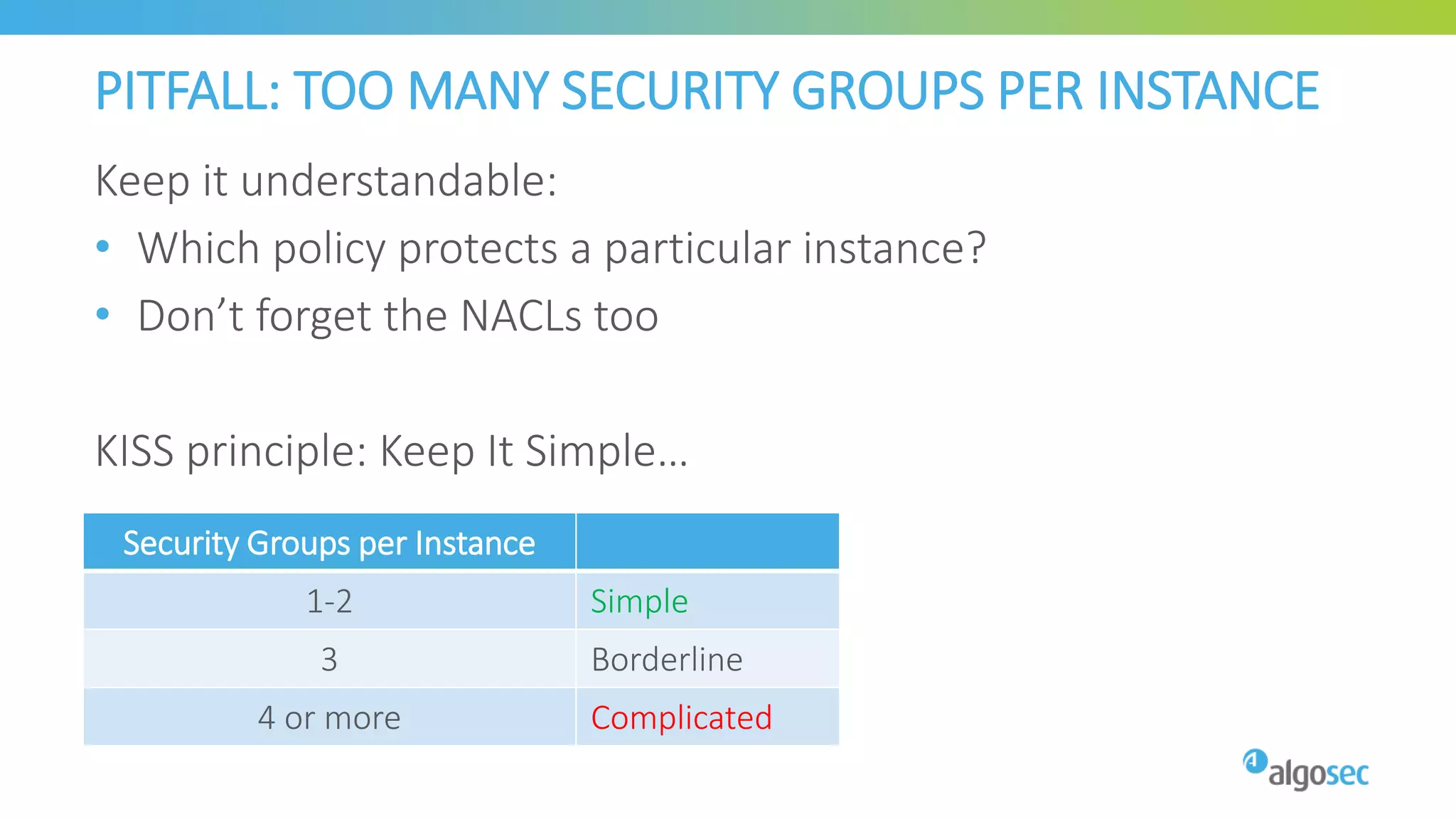
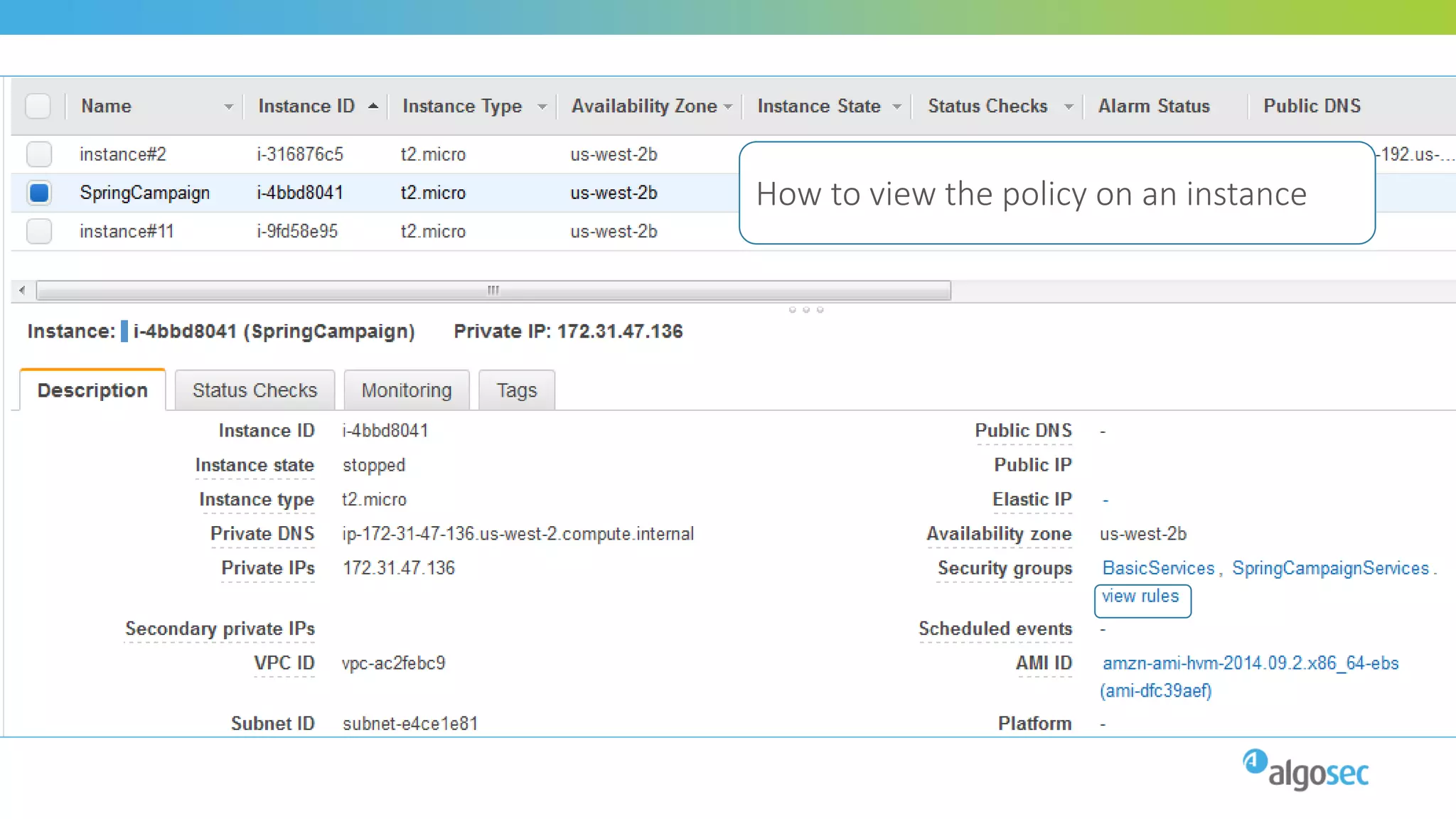
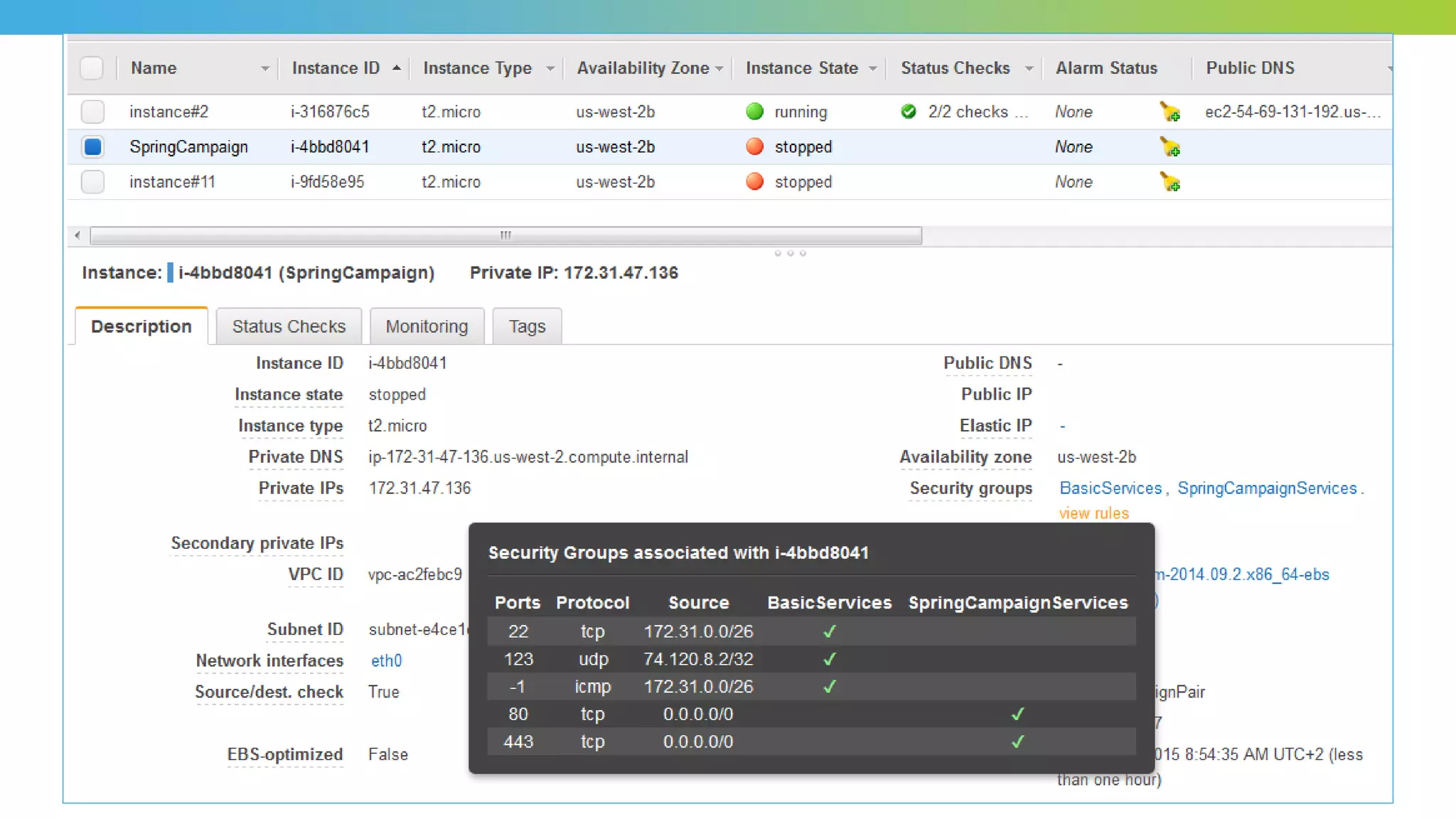
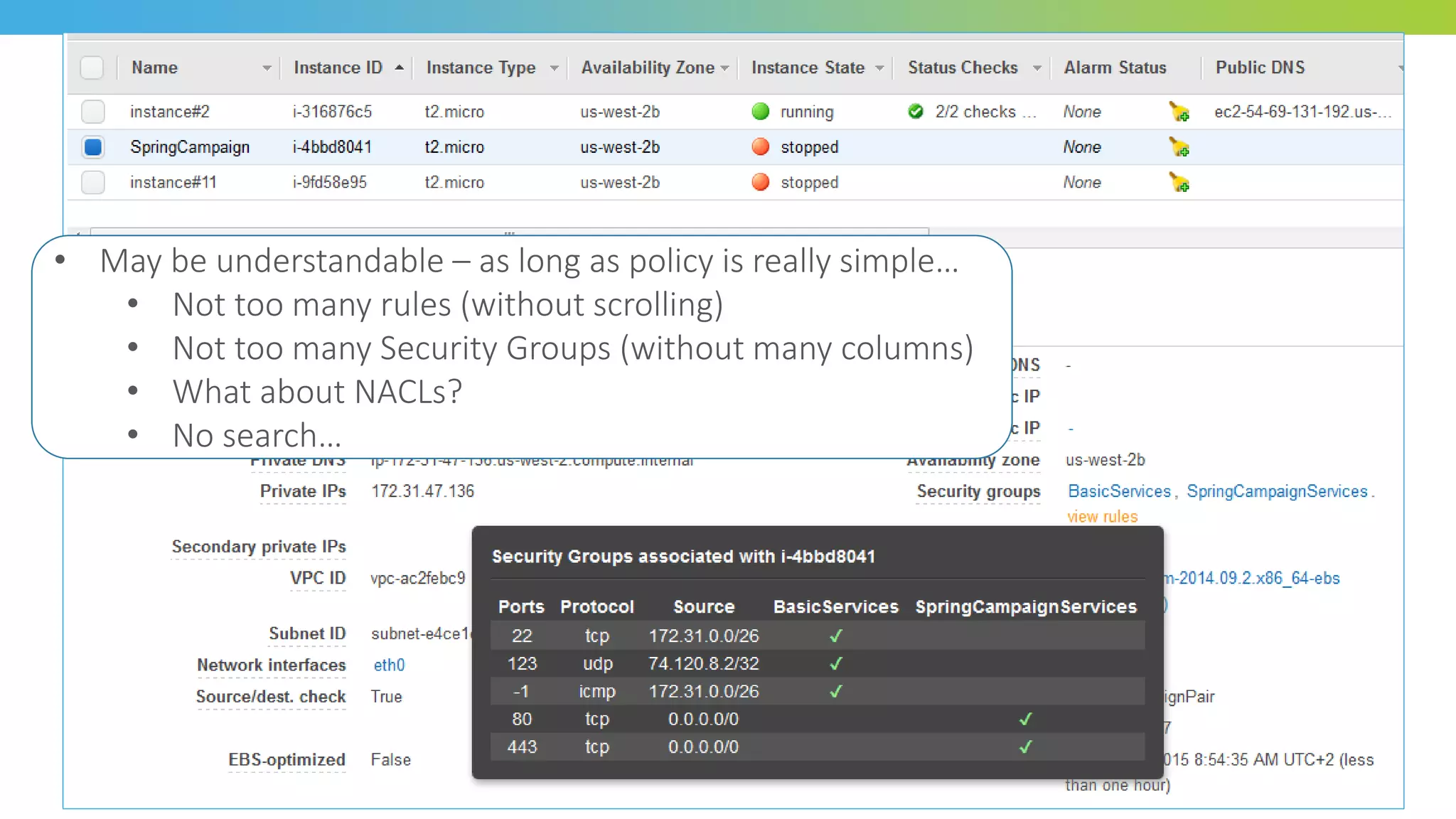
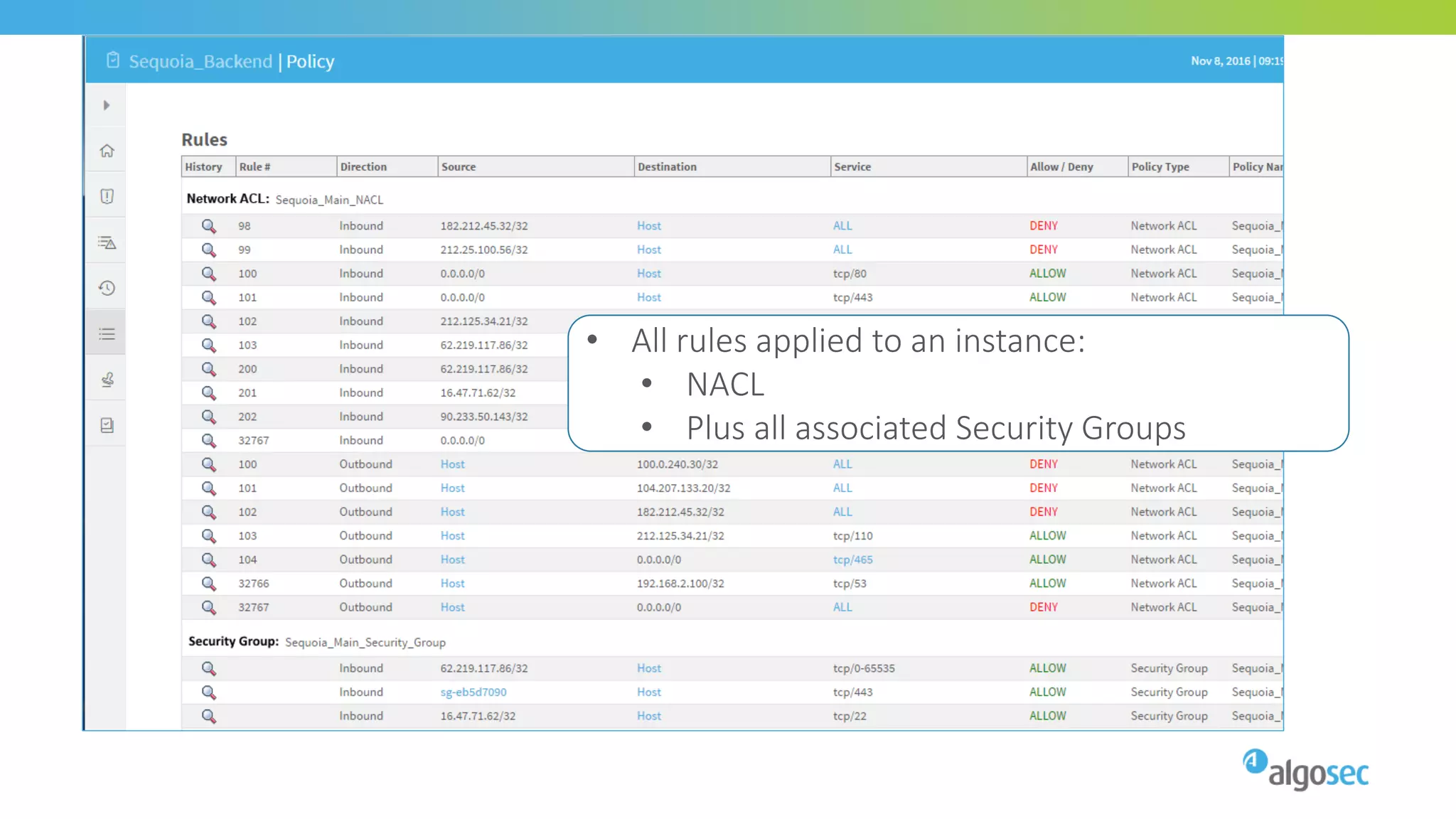
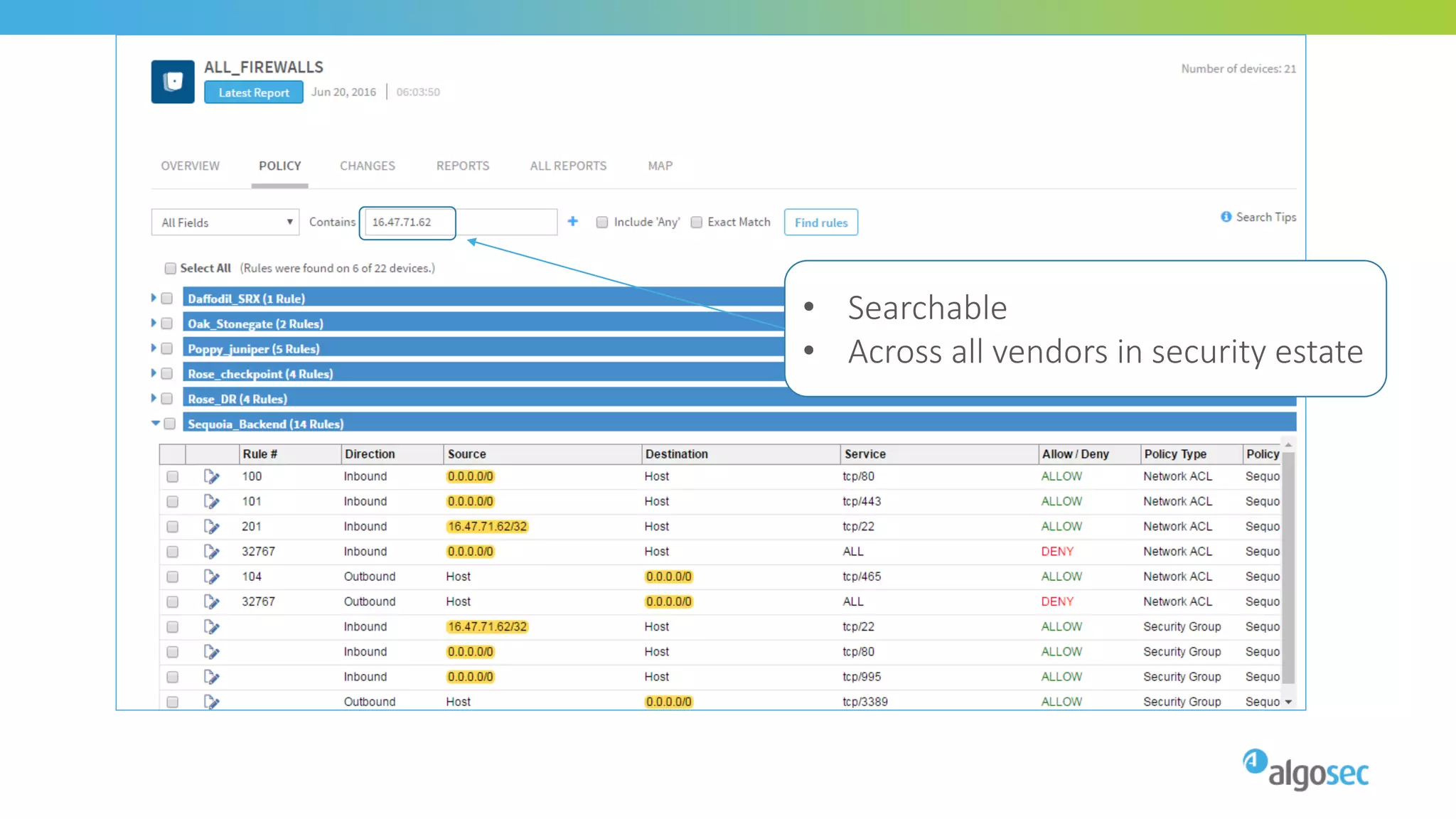
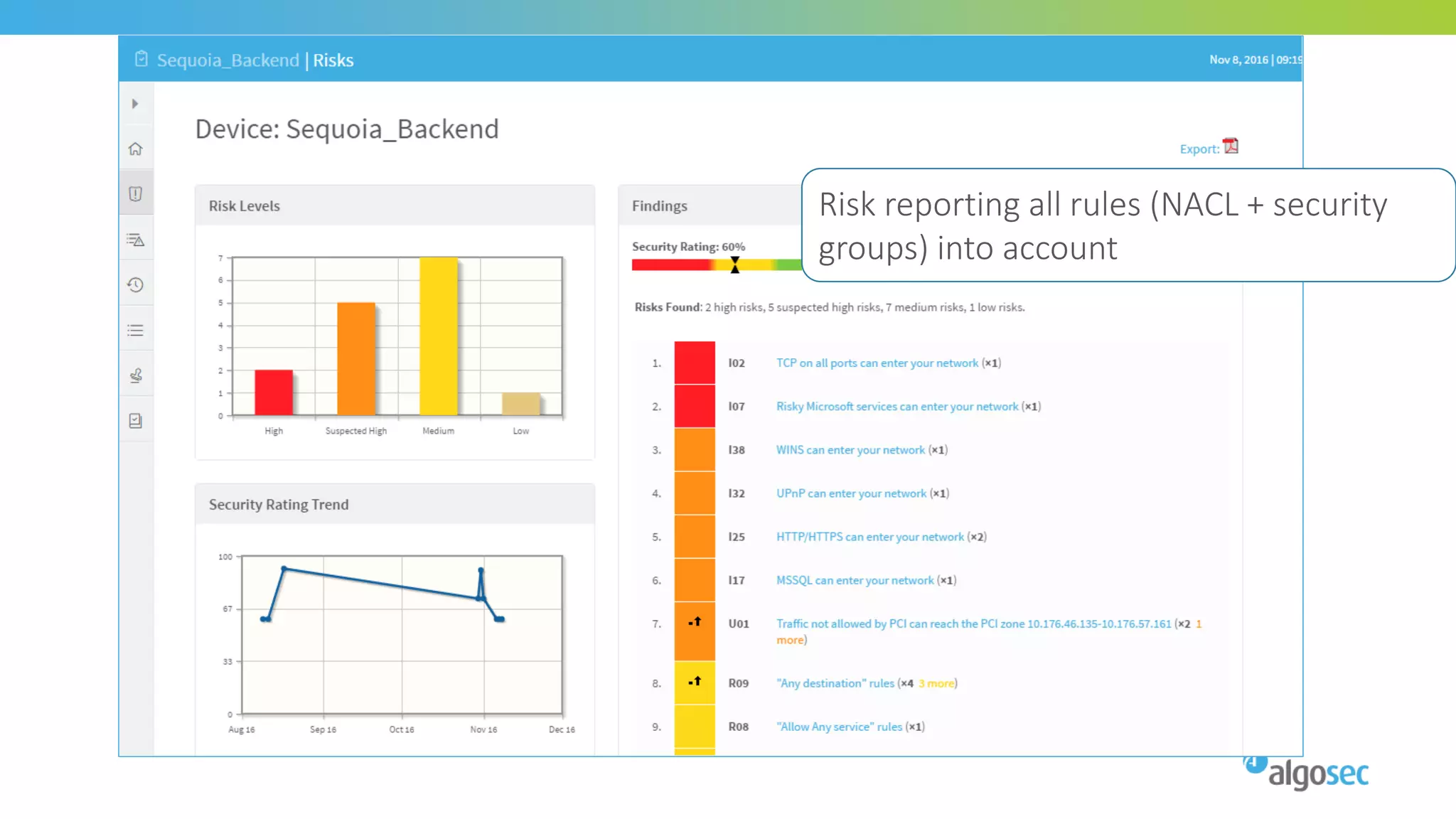
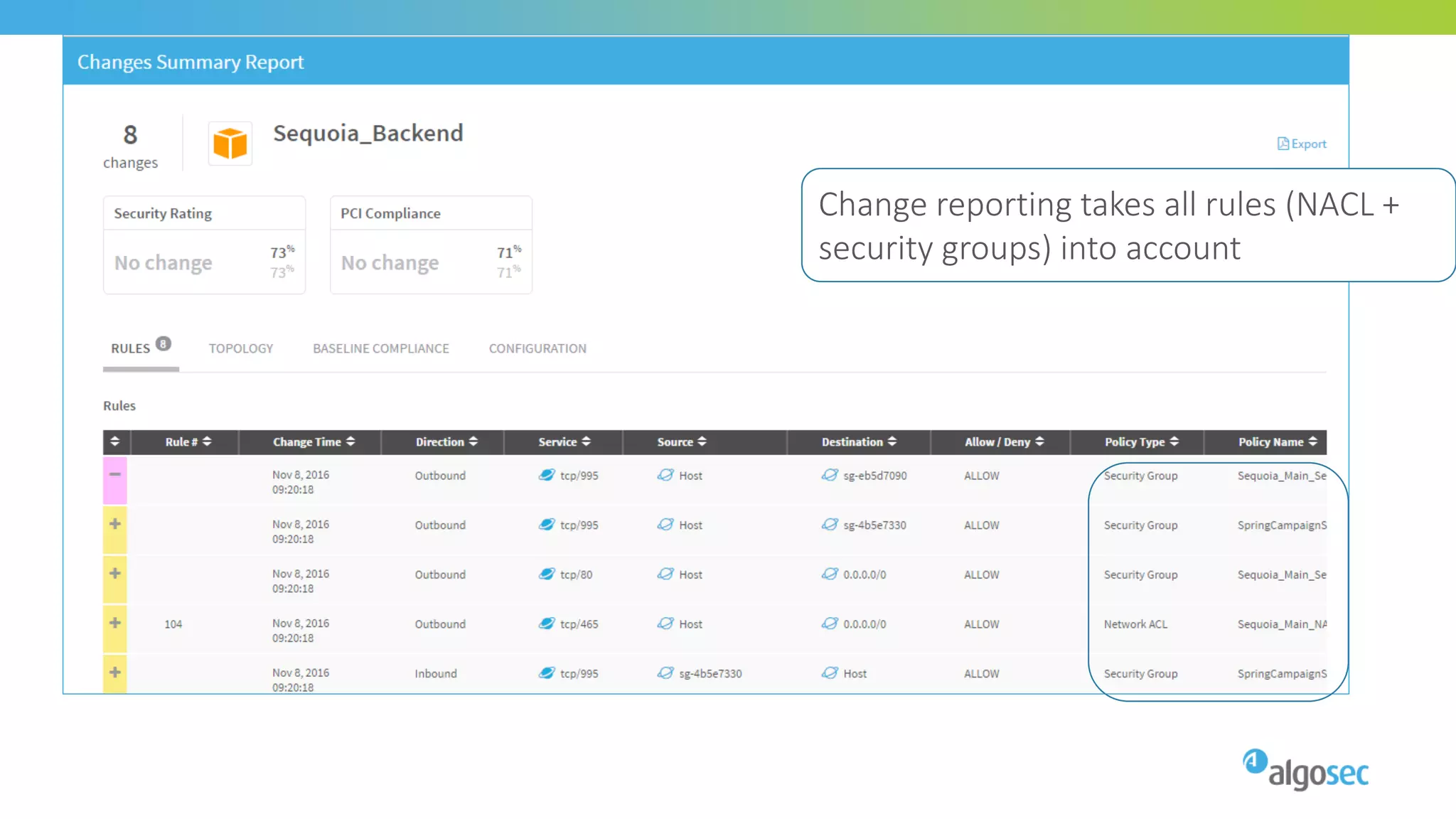
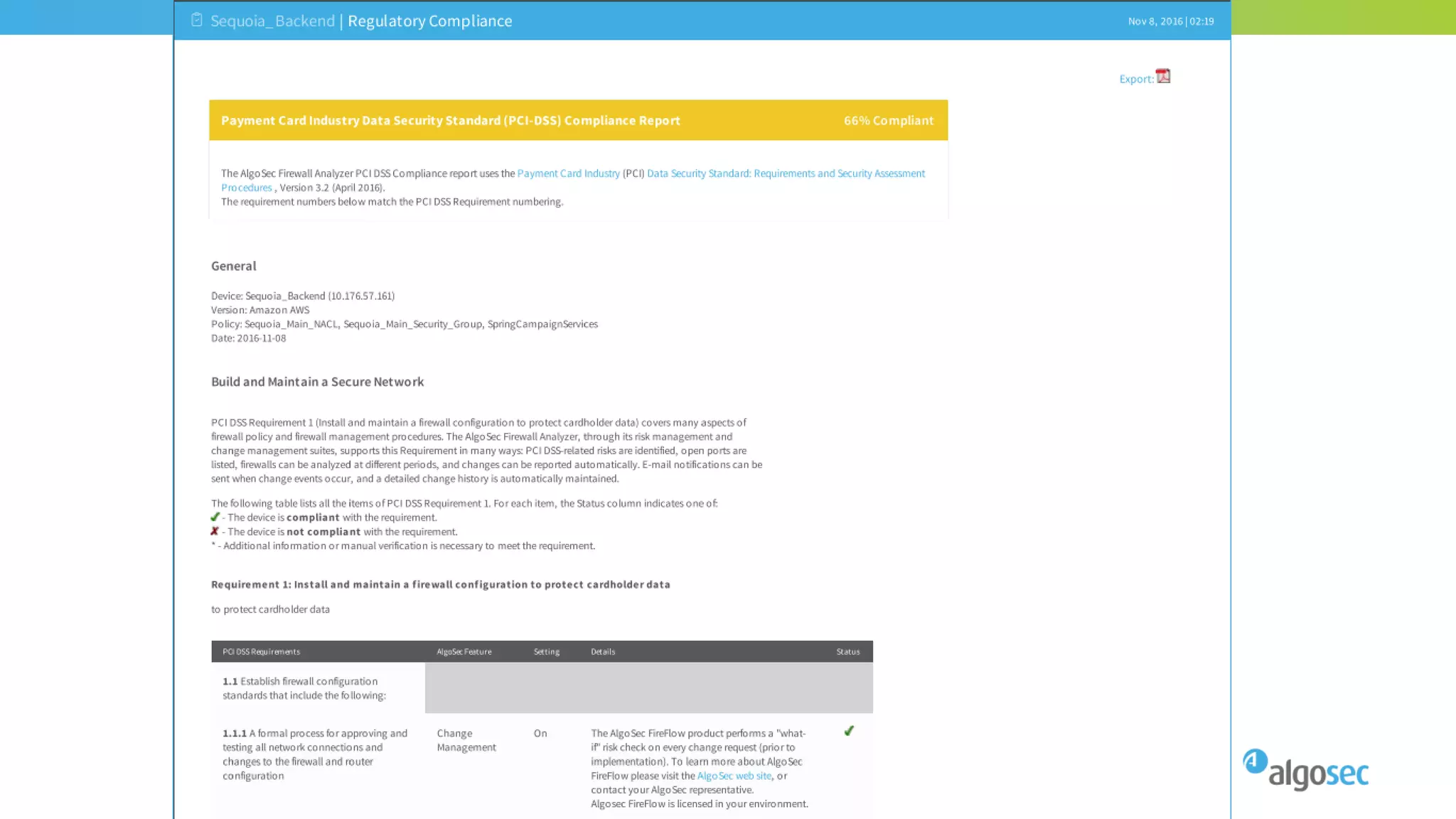
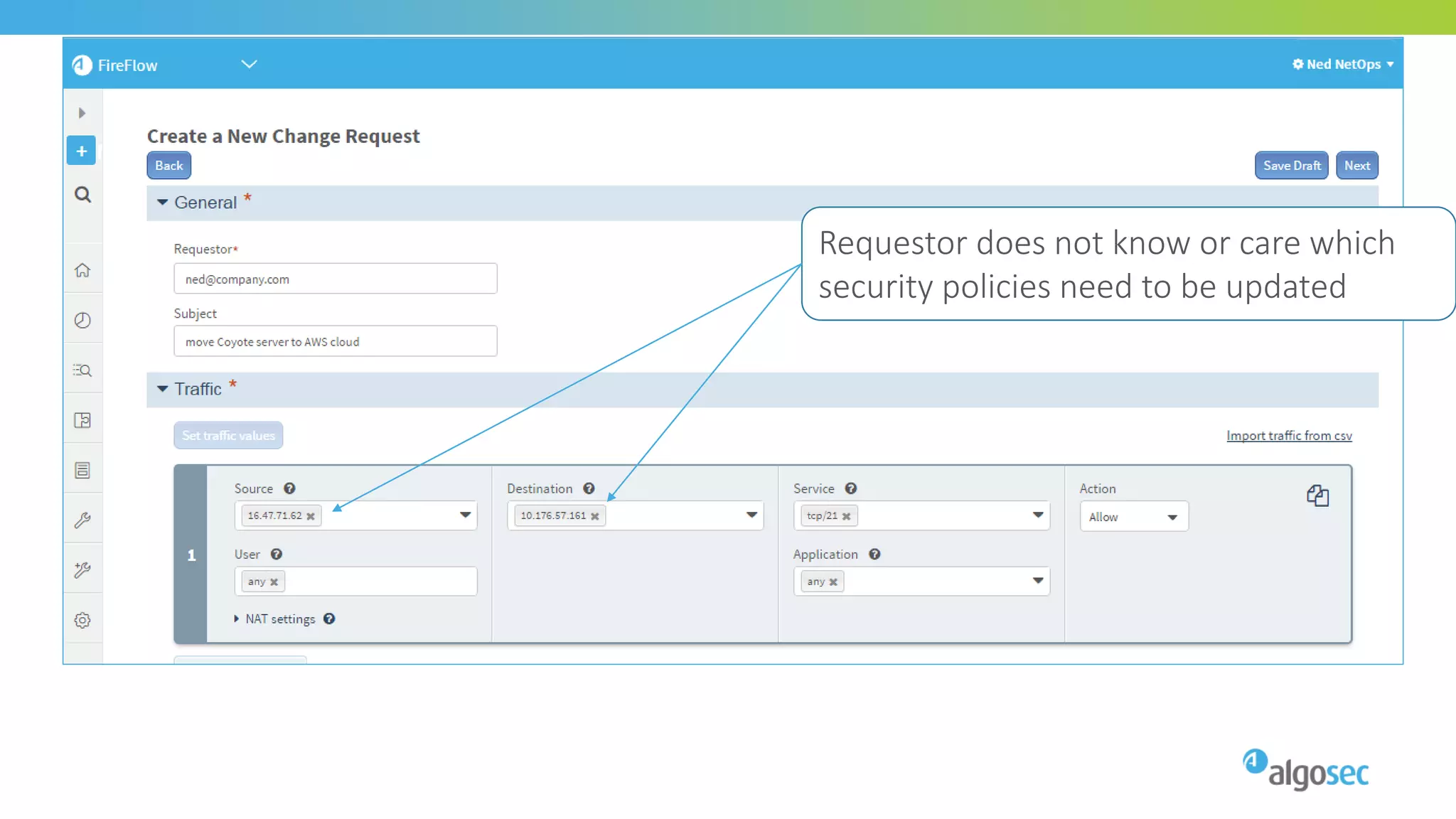
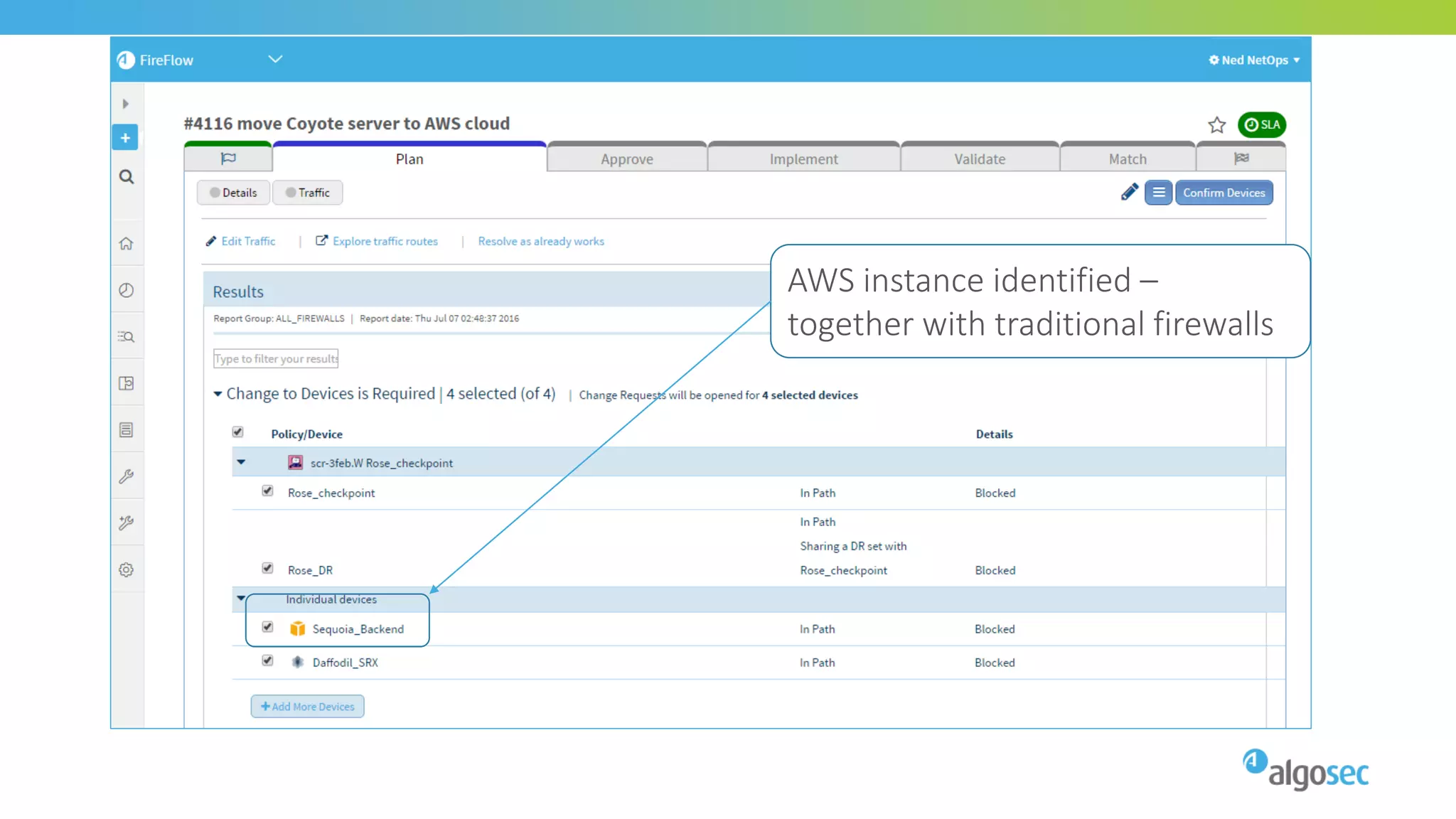
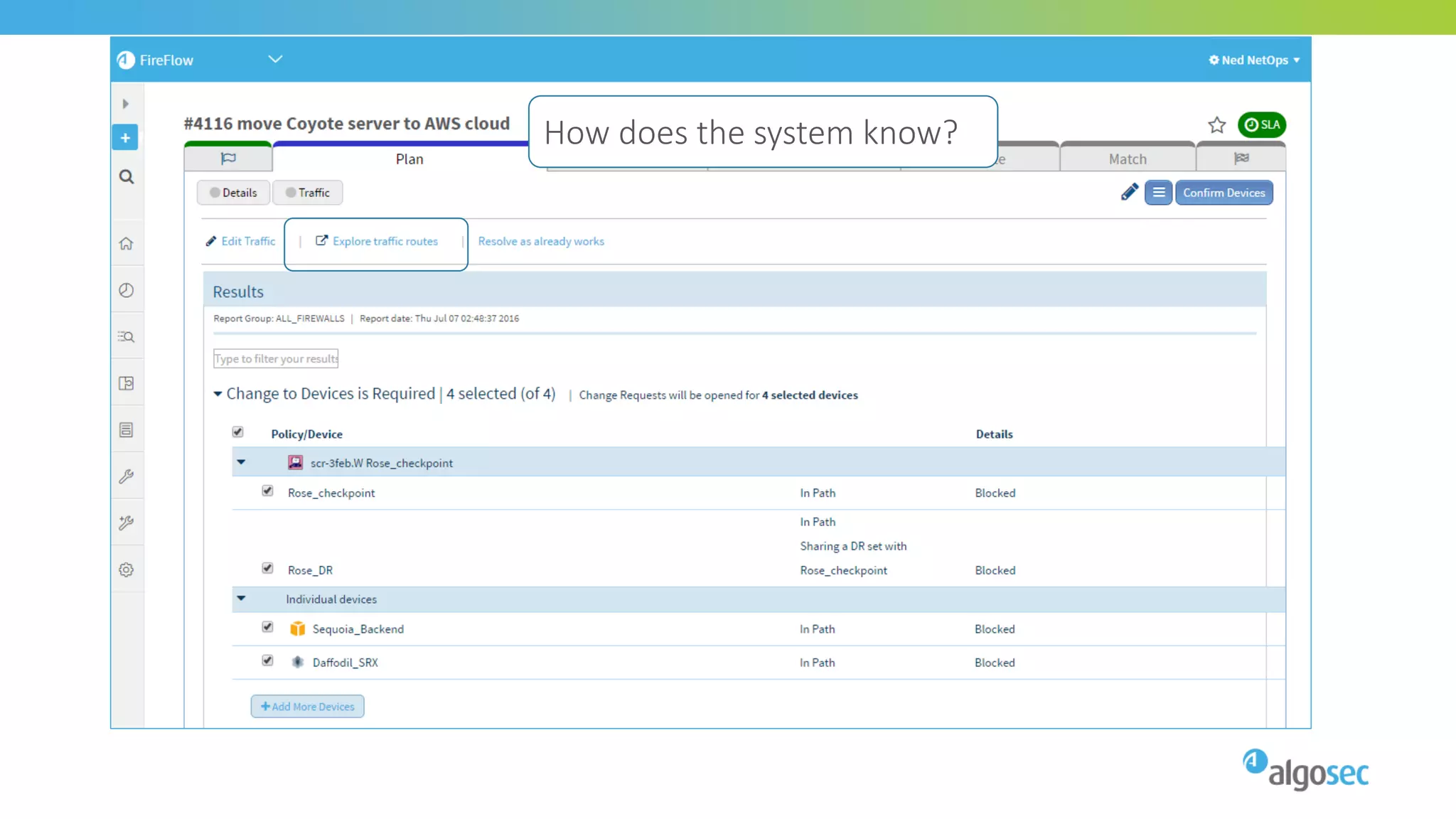
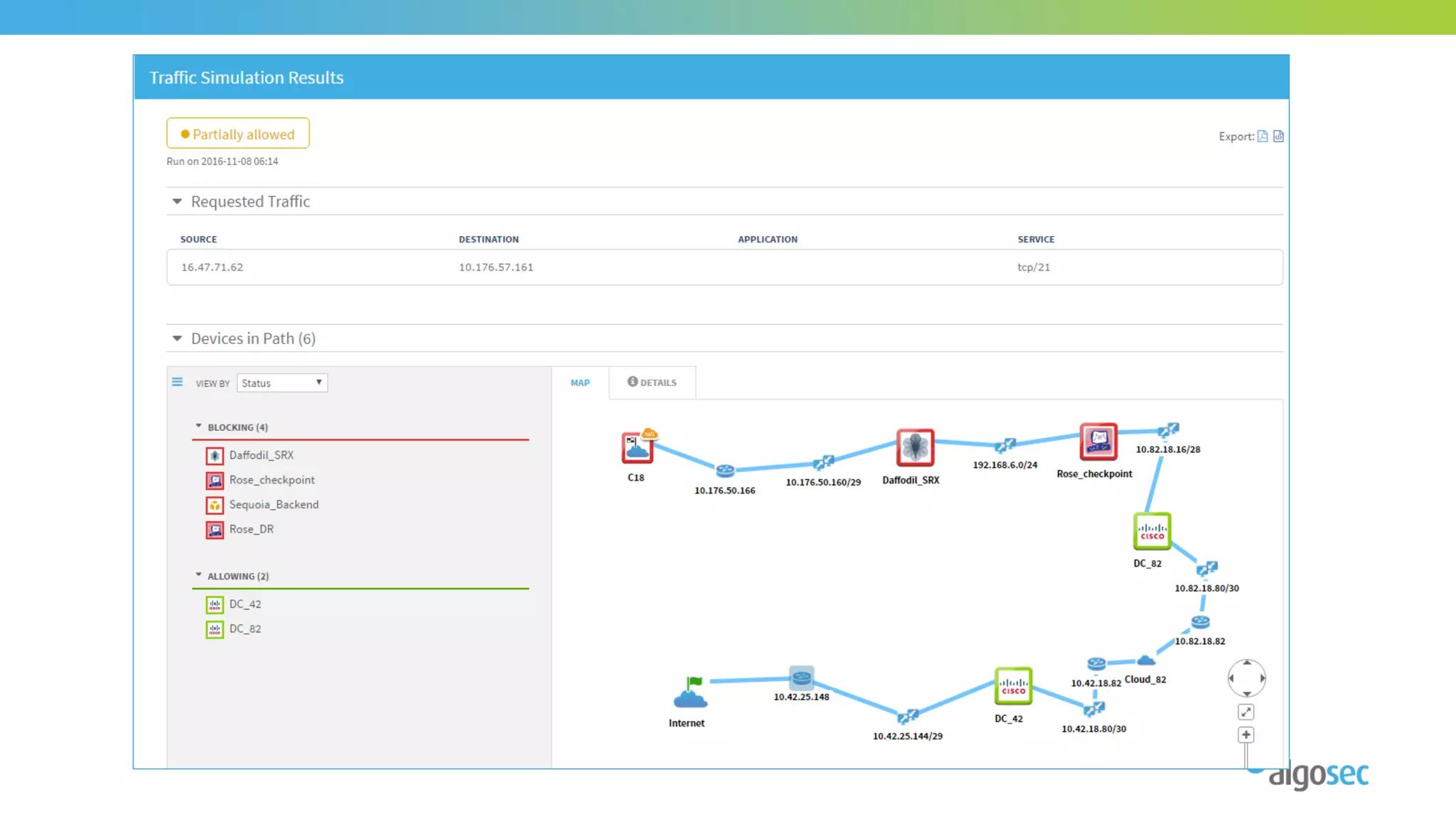
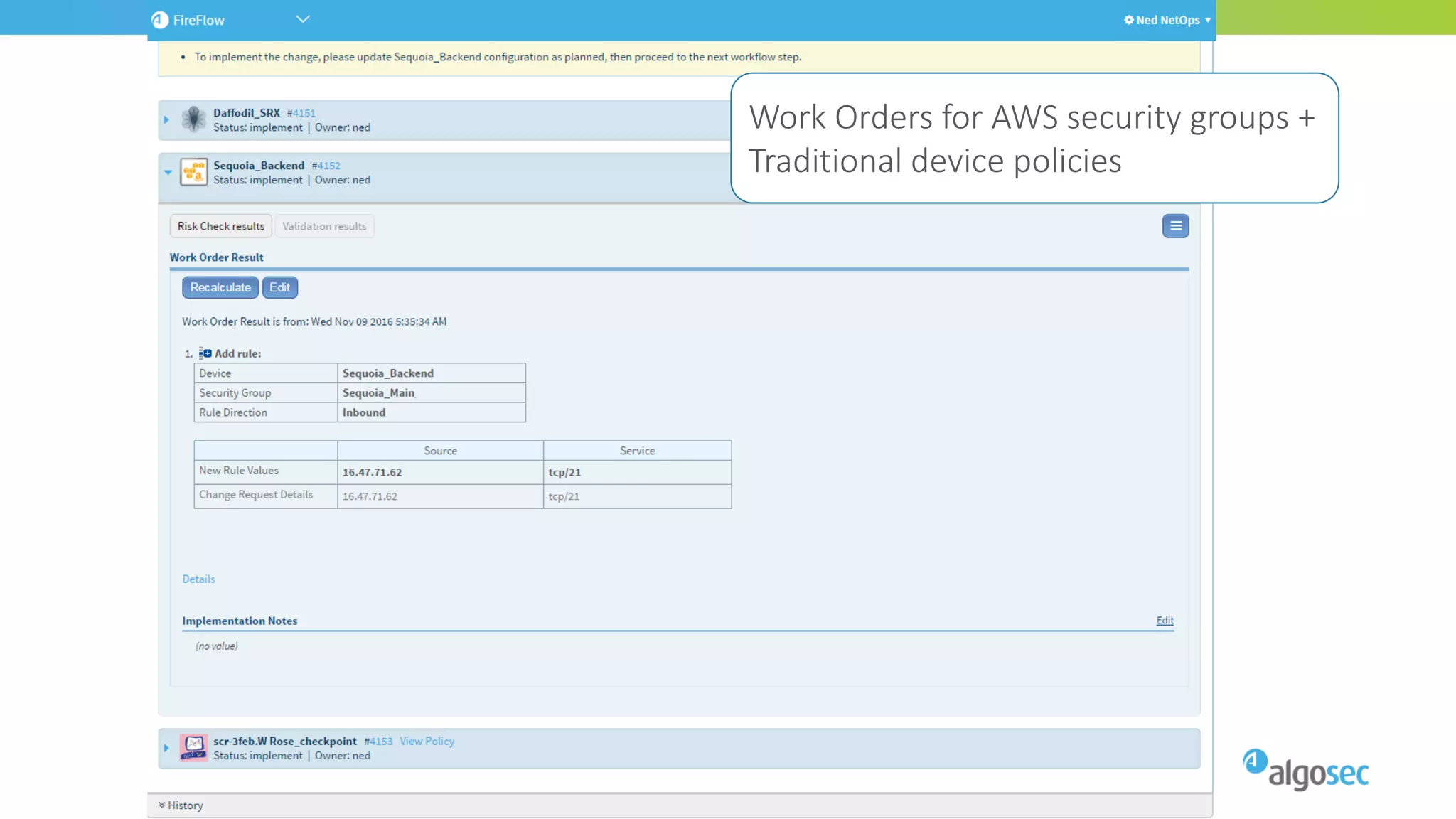
The document discusses best practices for migrating and managing security in an AWS environment, focusing on AWS firewall policies, security groups, and network access control lists (NACLs). It highlights the importance of understanding security configurations, modular policy organization, and achieving visibility in hybrid cloud environments. Additionally, it provides insights on challenges and tips for managing AWS security efficiently while addressing integration with traditional firewalls.