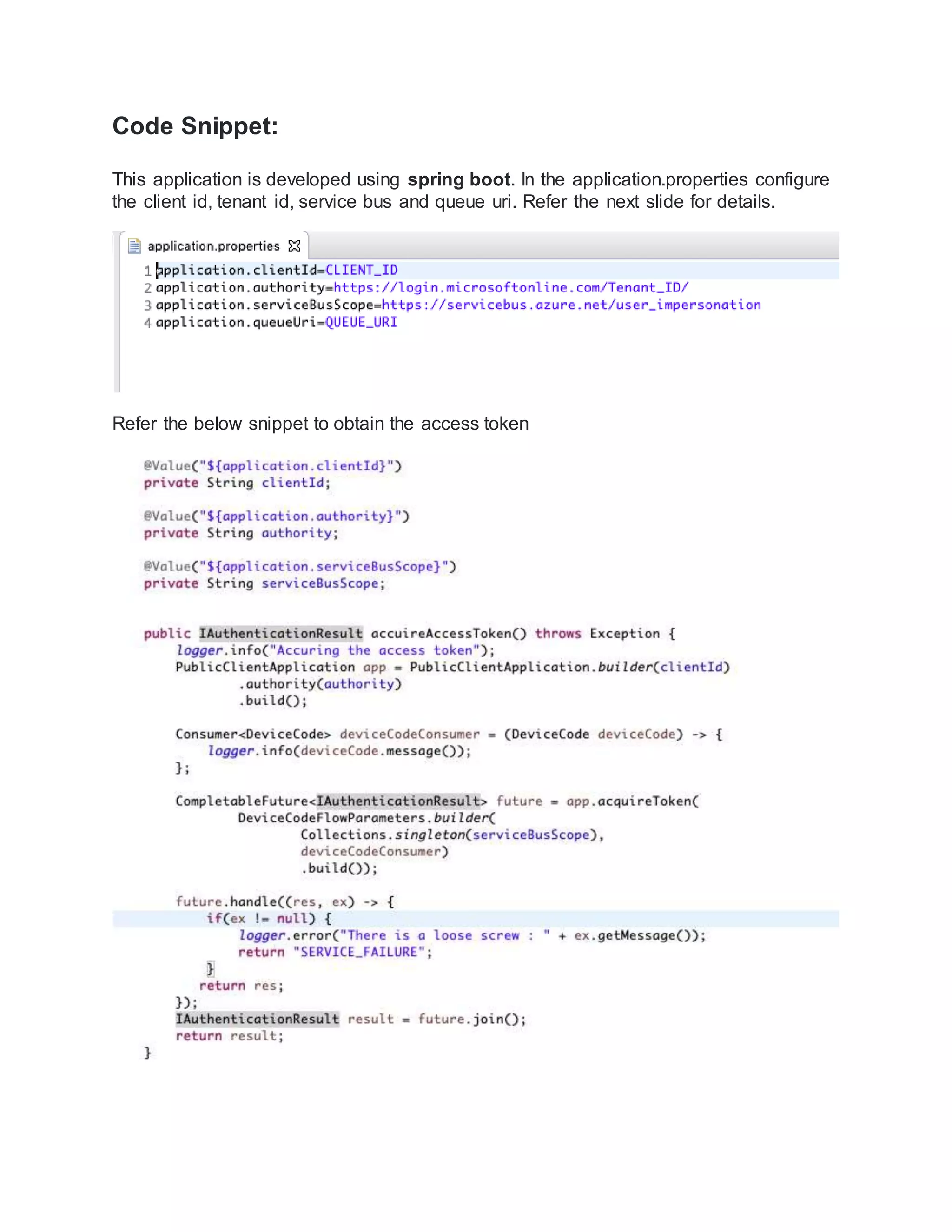
The document outlines the process for using the Microsoft Identity Platform and Device Authorization Flow to access Azure Service Bus from input-constrained devices without an interactive authentication experience. It details the steps for application registration, setting up permissions, creating a Service Bus and queue, and the code required for authentication and publishing messages to Azure Service Bus. Users must follow specific instructions to configure their Azure environment and acquire an access token to publish messages successfully.
![APP CLIENT ID:
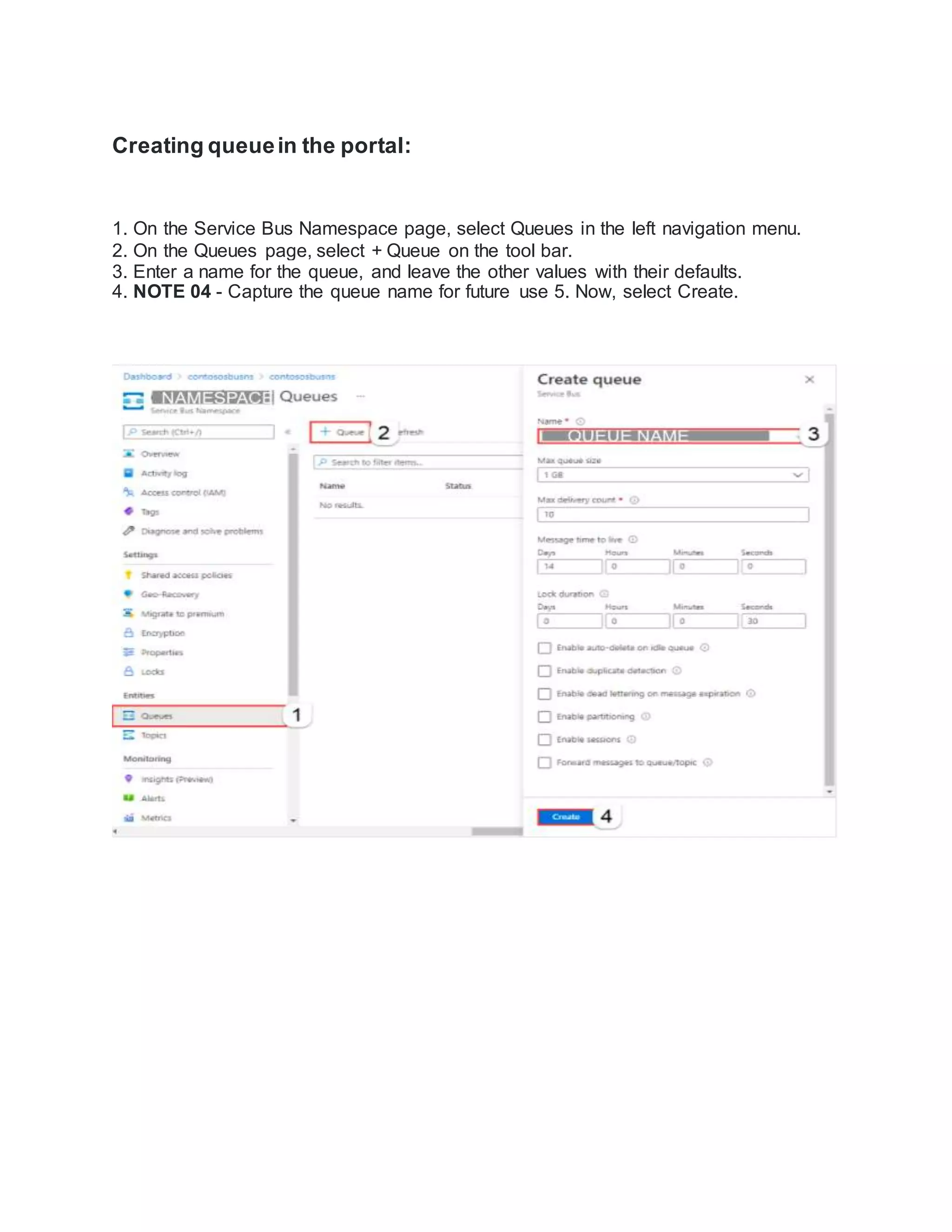
Now go to Azure Home —> Azure Active Directory —> App Registrations. Then under
all applications you can find your application[ad-profile] created in the above step.
NOTE 01 -Copy the client ID from this screen and keep it for future use. This is unique
identifier is required to access your app. We will be configuring it in the code(GitHub
reference is present ).](https://image.slidesharecdn.com/microsoftidentityplatformanddeviceauthorizationflowtouseazureservicebus-211227145420/75/Microsoft-identity-platform-and-device-authorization-flow-to-use-azure-service-bus-3-2048.jpg)
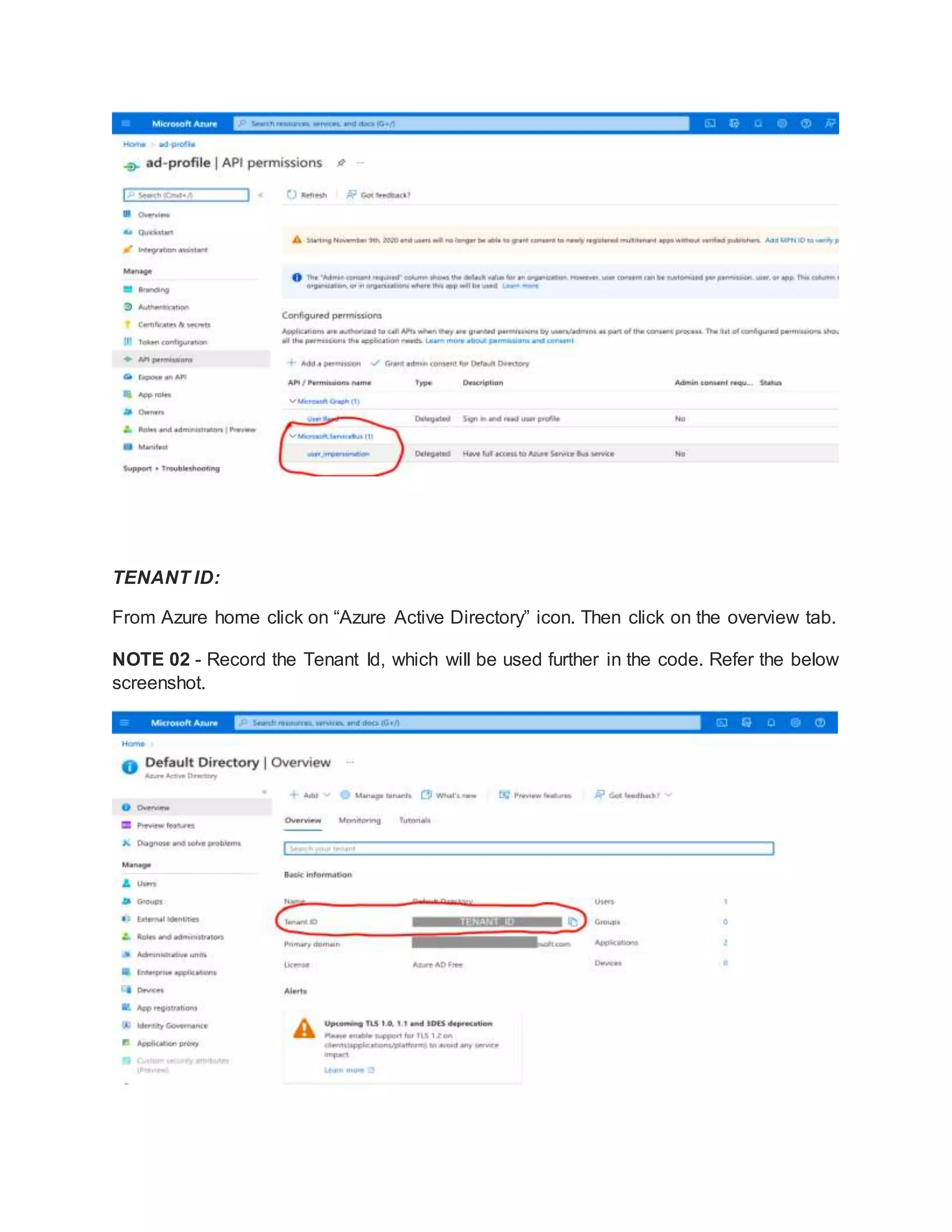
![AUTHENTICATION:
Now click on the authentication section of the App registration screen. Select “Mobile
and desktop application” under “Configure platforms”
Now select the checkbox [https://login.microsoftonline.com/common/oauth2/nativeclient]
and hit configure.](https://image.slidesharecdn.com/microsoftidentityplatformanddeviceauthorizationflowtouseazureservicebus-211227145420/75/Microsoft-identity-platform-and-device-authorization-flow-to-use-azure-service-bus-5-2048.jpg)
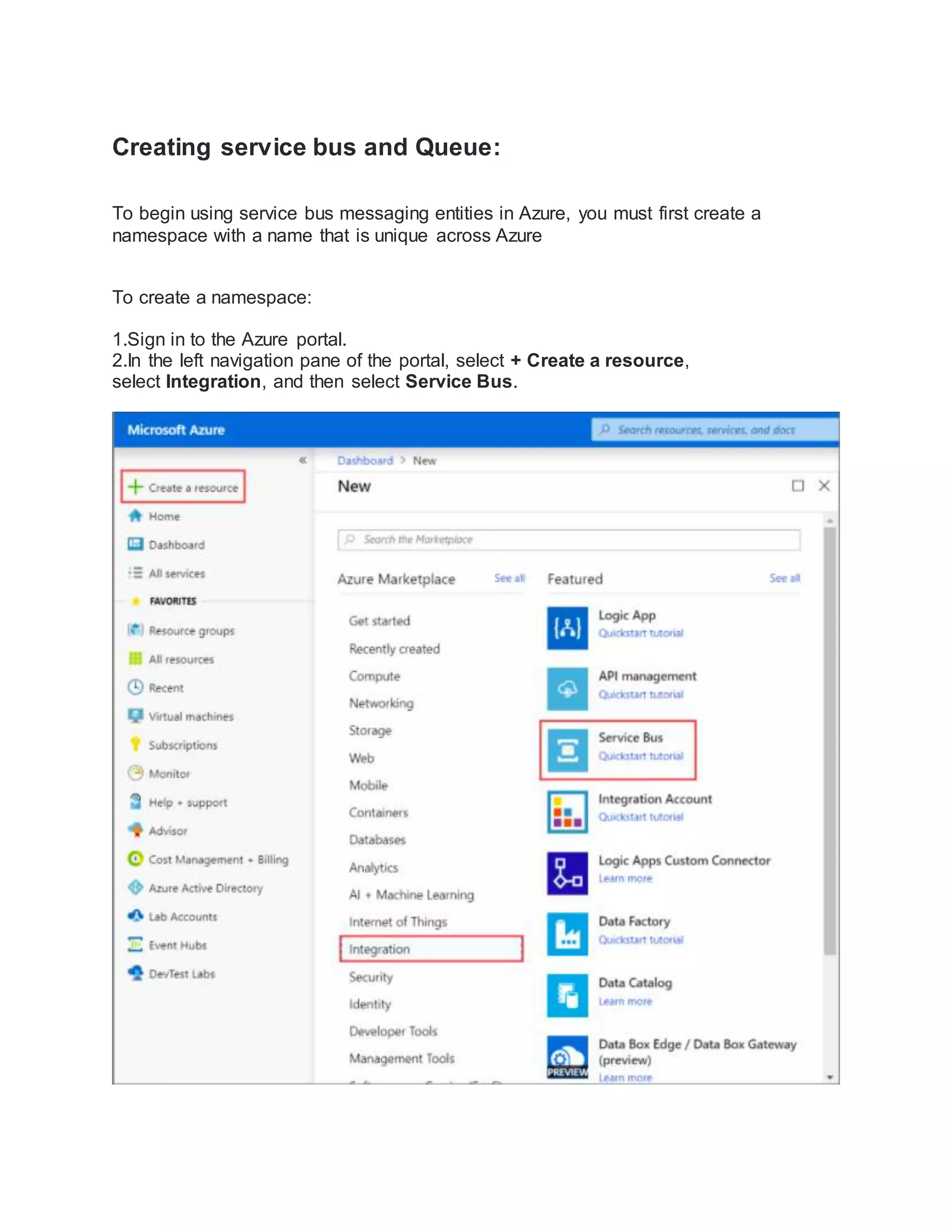
![You see the home page for your service bus namespace.
NOTE 03 - Record the Host name to use in the code. [refer the below screen shot to
capture host name]](https://image.slidesharecdn.com/microsoftidentityplatformanddeviceauthorizationflowtouseazureservicebus-211227145420/75/Microsoft-identity-platform-and-device-authorization-flow-to-use-azure-service-bus-10-2048.jpg)
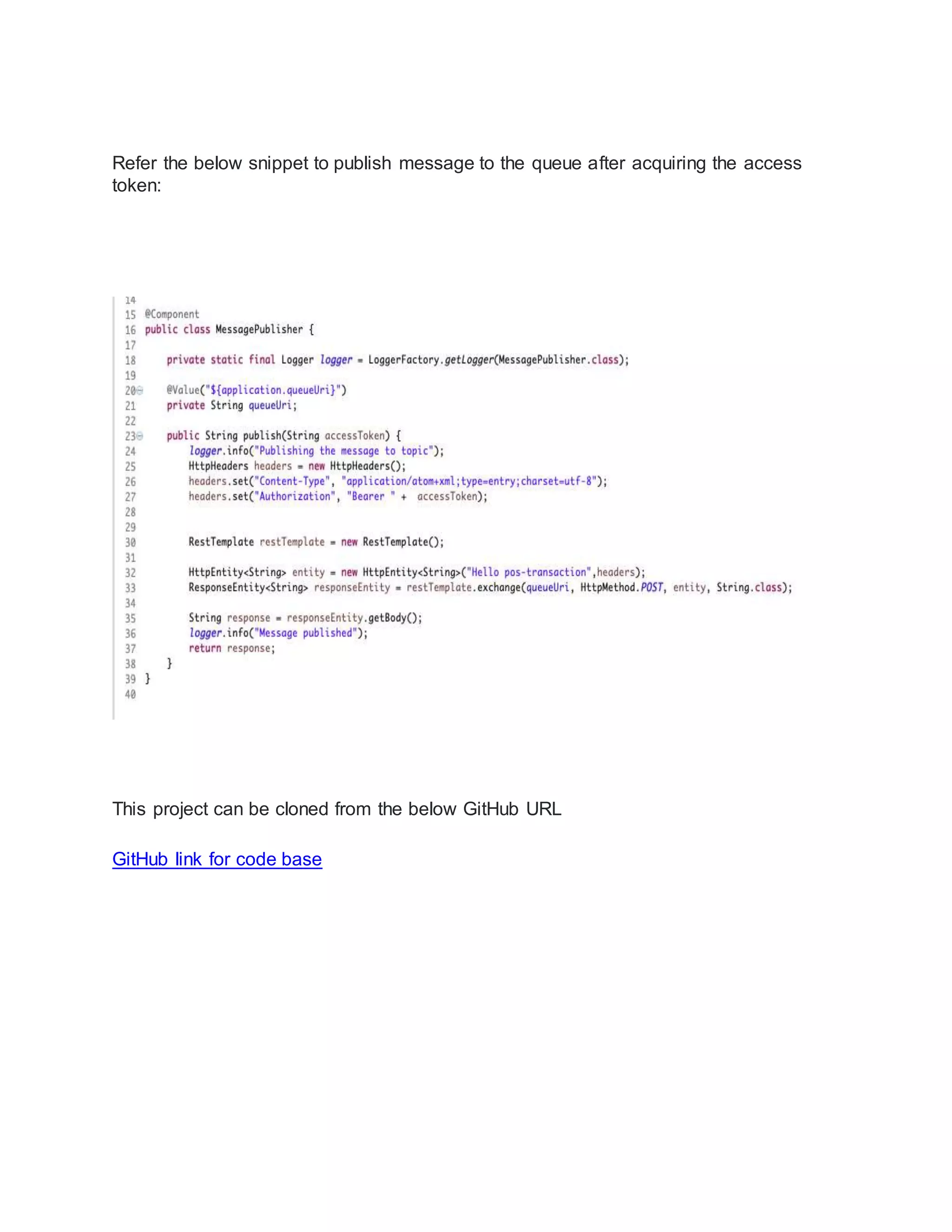
![Running the code:
Clone this code base
Open the application.properties file. Put the value of CLIENT_ID from NOTE
01 and TENAT_ID from NOTE 02 that we have captured in the above steps.
The value of QUEUE_URI is the combination of Host name from NOTE 01 and the
queue name that you have given [refer NOTE 04]
if your namespace id "abc" and queue name is xyz, then
Host name will be : https://abc.servicebus.windows.net
QUEUE_URI will be : https://event-demo.servicebus.windows.net/transactions/messages
Now go to the root of the project and run the below command.
$mvn clean package spring-boot:repackage
A jar file named azure-identity-servicebus-1.0.jar will be generated in the target folder.
Now run the below command
$ java -jar target/azure-identity-servicebus-1.0.jar
The above command will give the response like below:
INFO com.ski.identity.servicebus.ServiceBusManager - To sign in, use a web browser
to open the page https://microsoft.com/devicelogin and enter the code YOURCODE to
authenticate.
Now use the url(https://microsoft.com/devicelogin) and the code from the above
response on a browser. It will ask for the user authentication. This user must present in
the active directory and have the permission to use ServiceBus. Once after successful
authentication, device will able to retrieve access token and publish message.](https://image.slidesharecdn.com/microsoftidentityplatformanddeviceauthorizationflowtouseazureservicebus-211227145420/75/Microsoft-identity-platform-and-device-authorization-flow-to-use-azure-service-bus-14-2048.jpg)