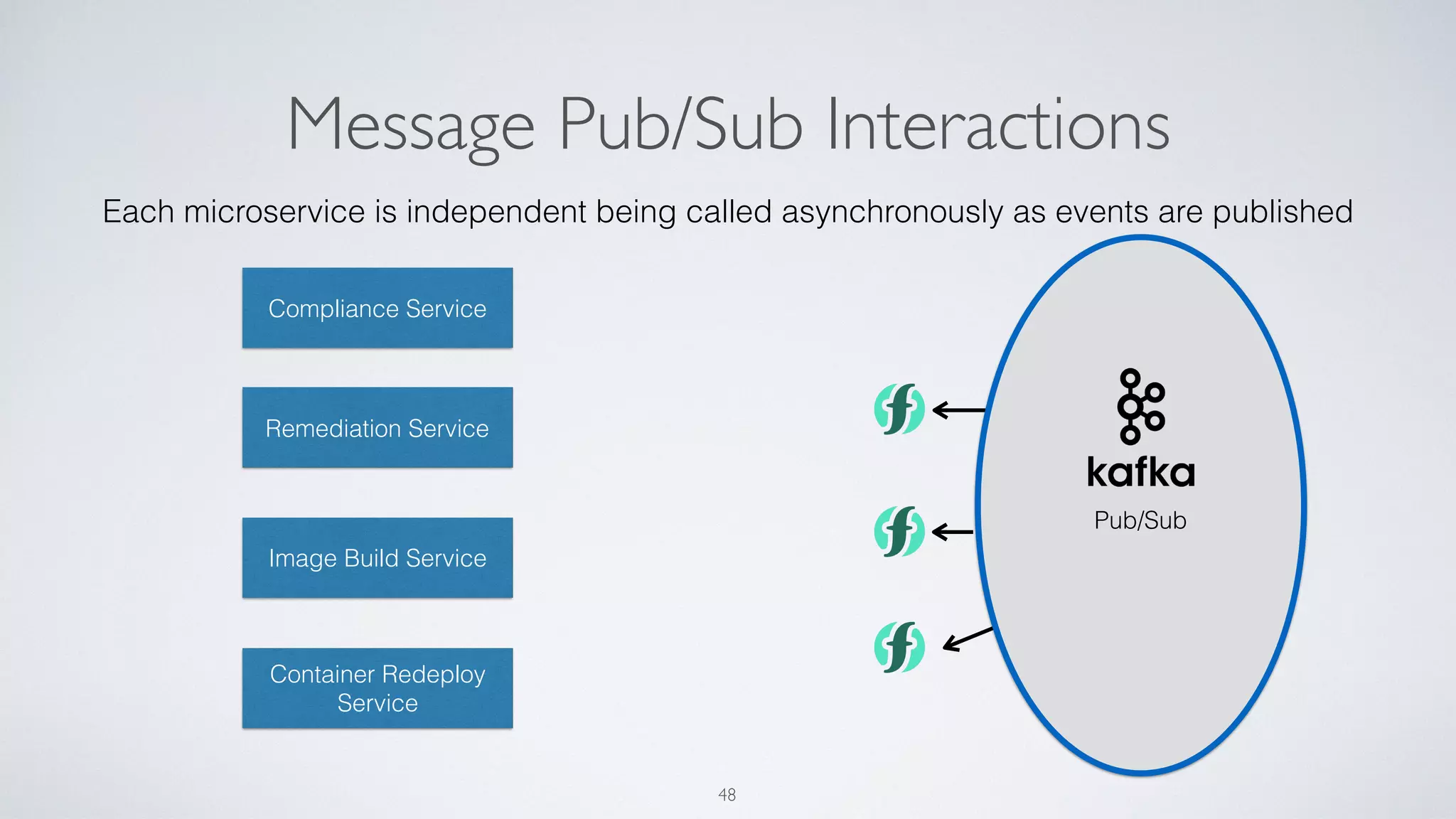
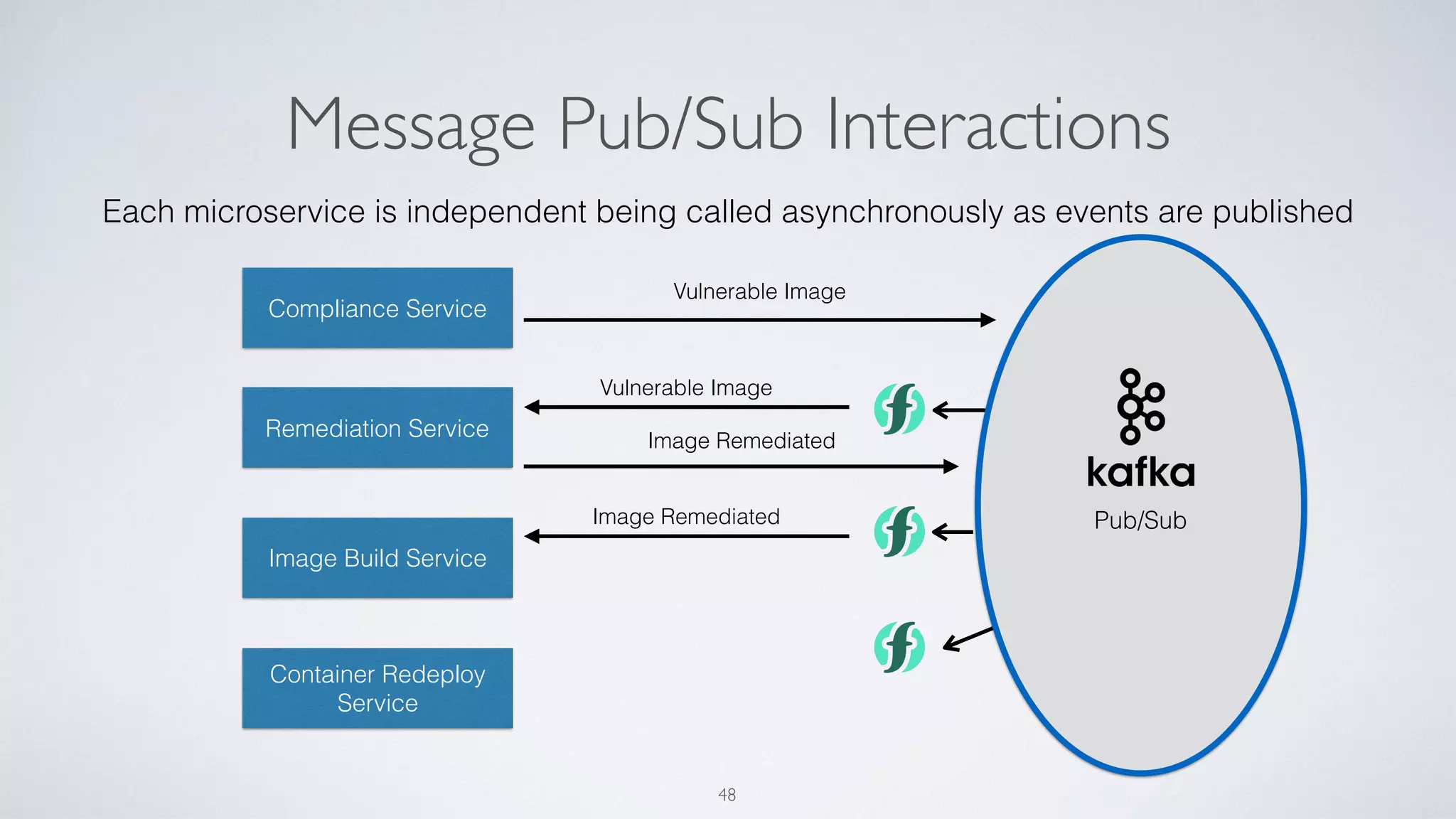
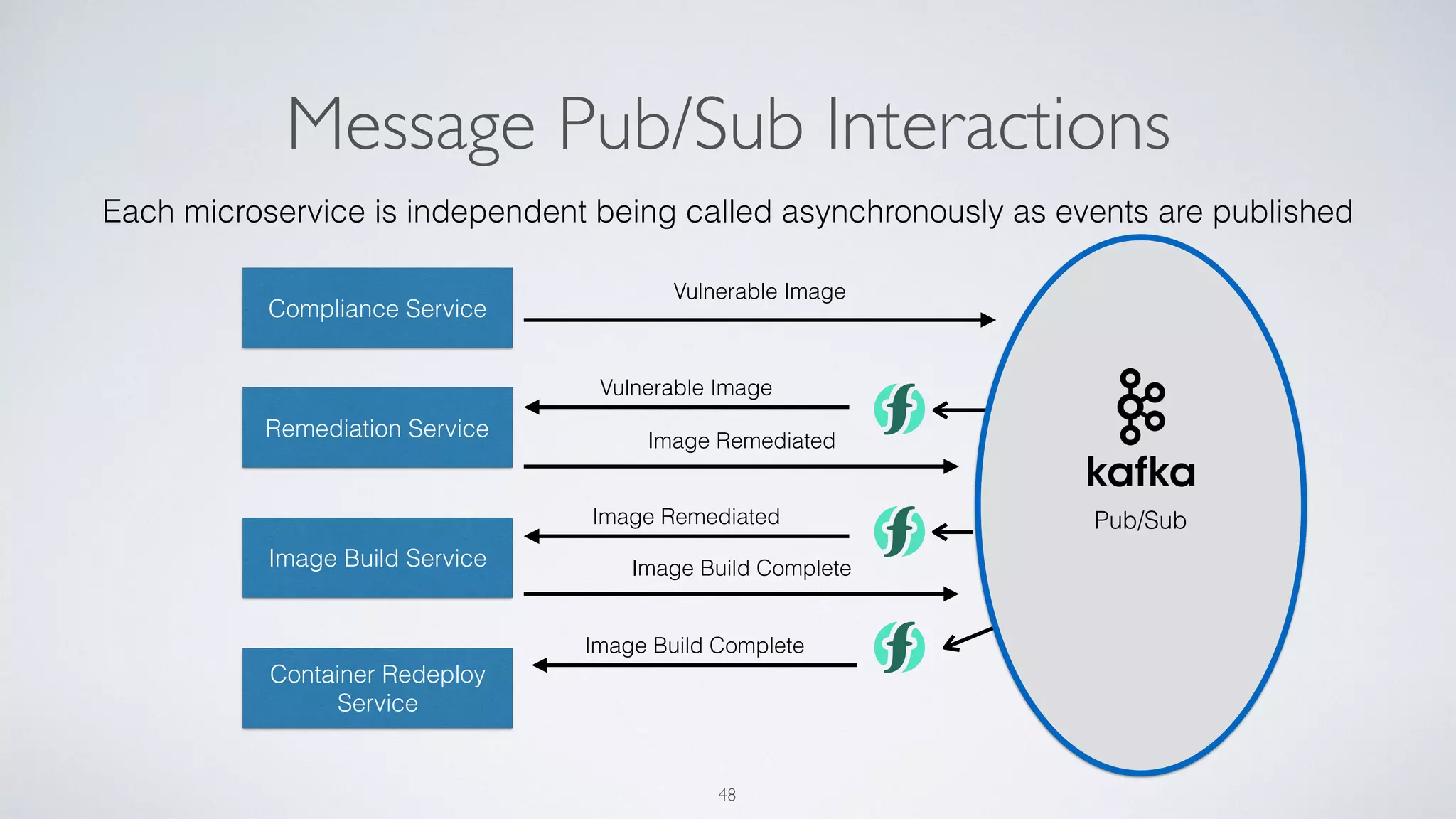
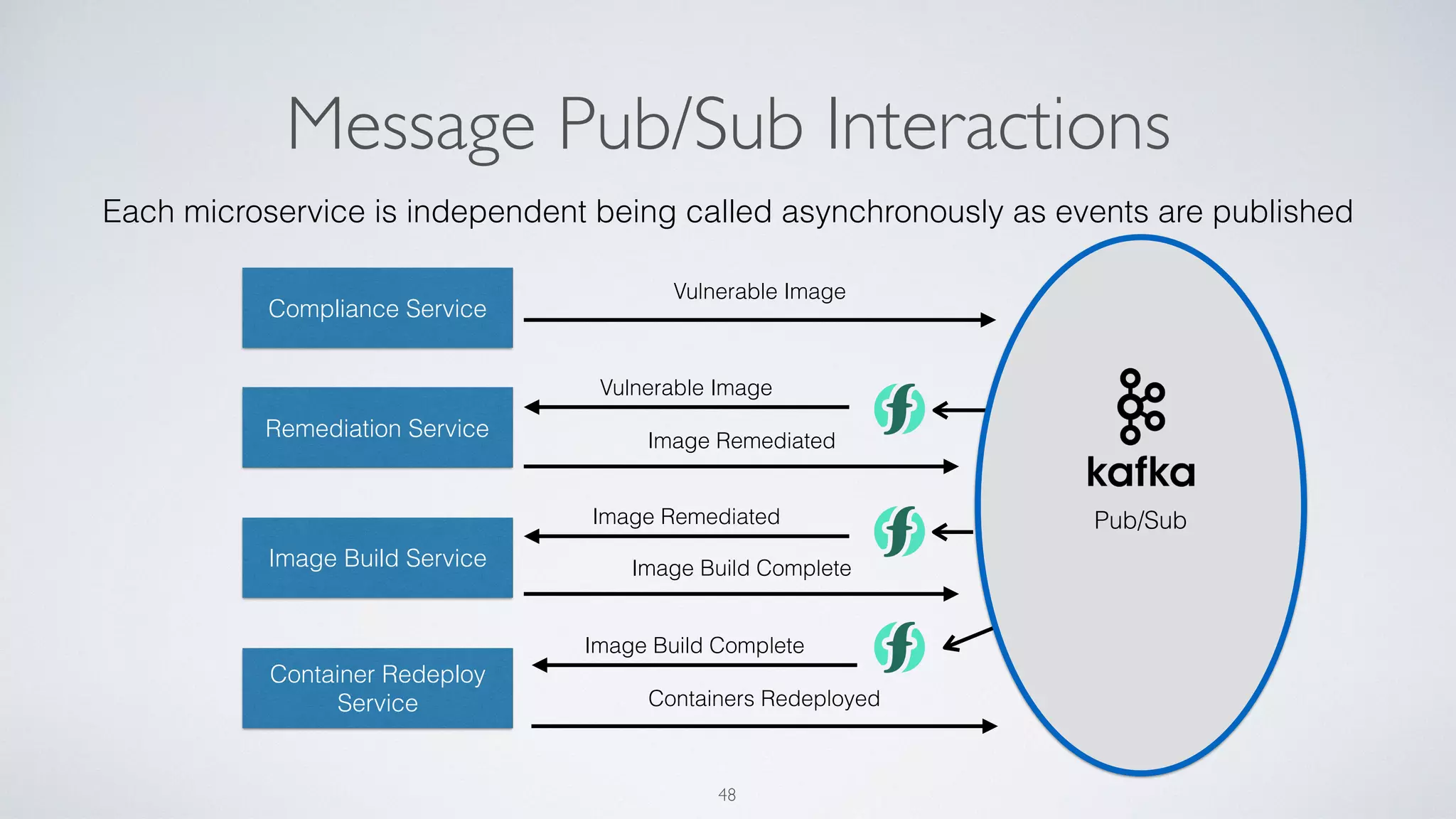
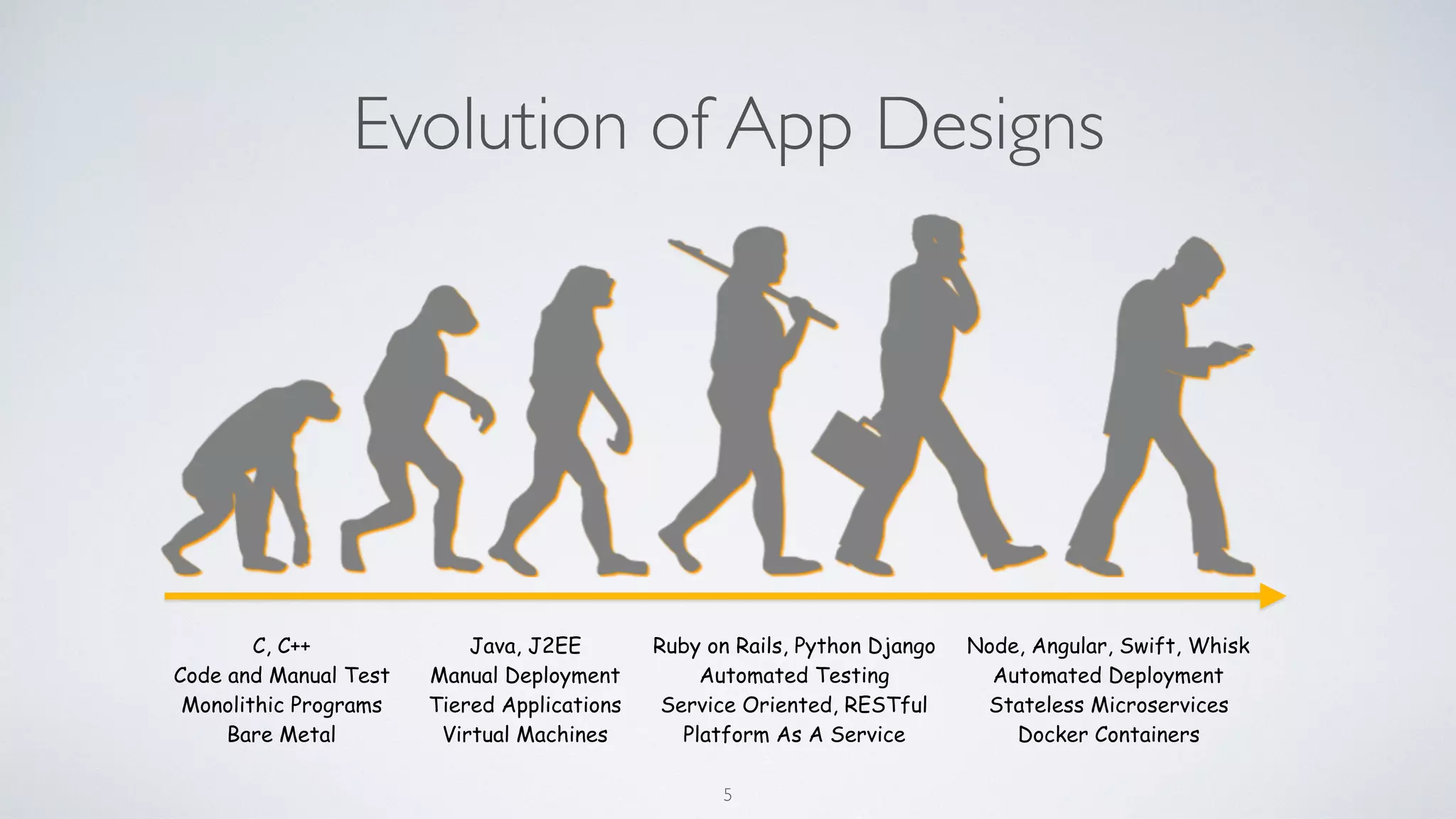
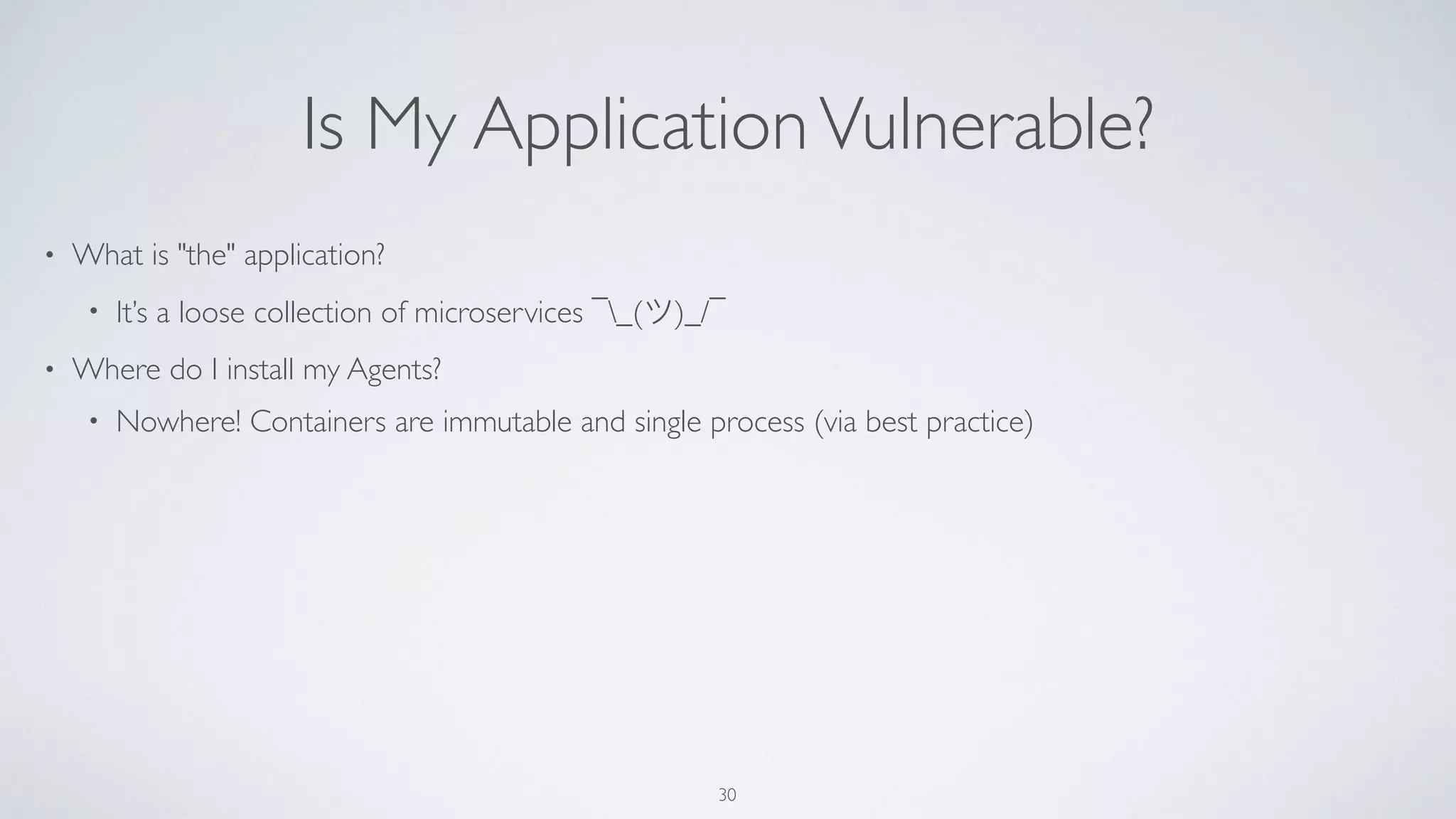
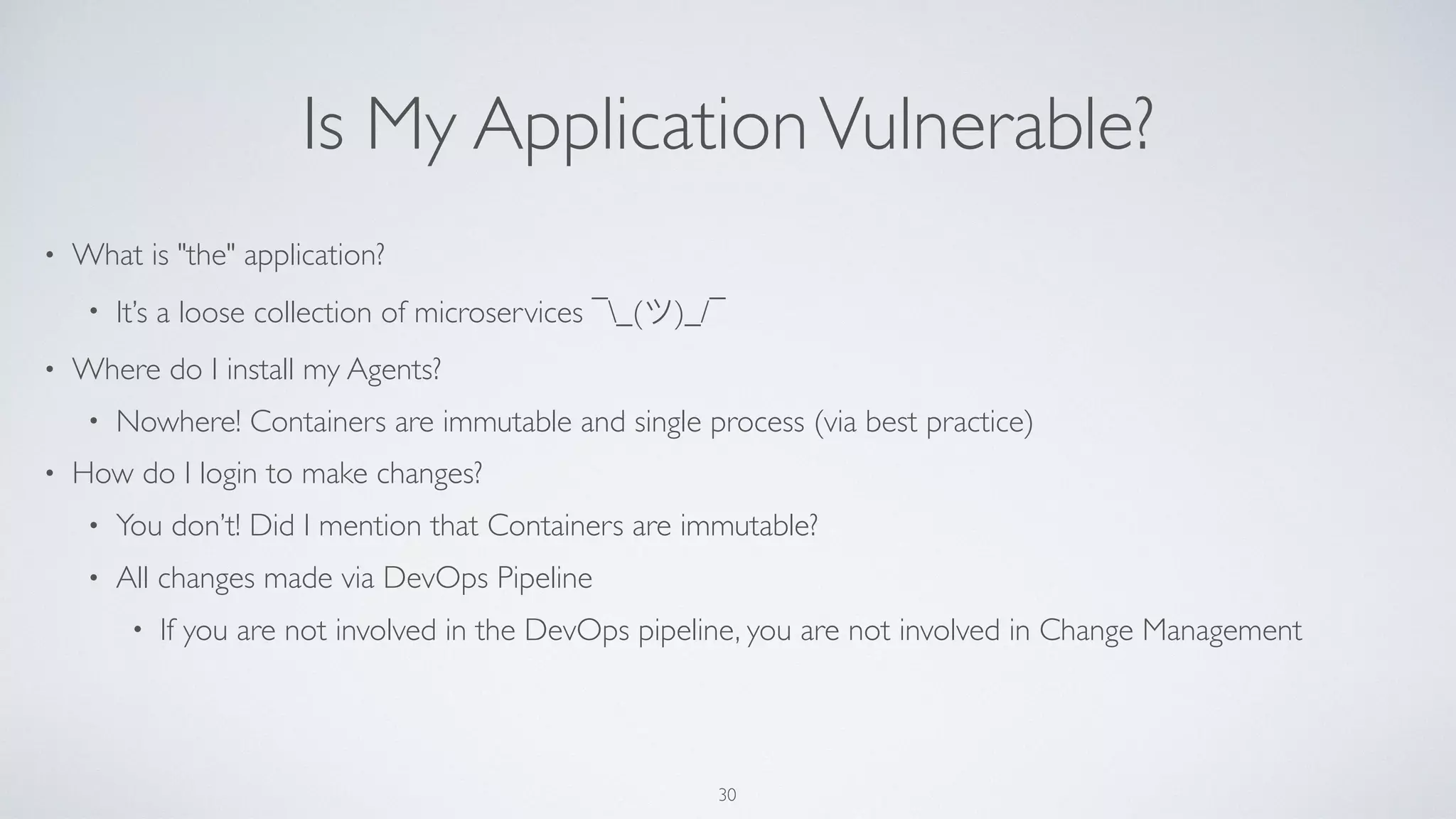
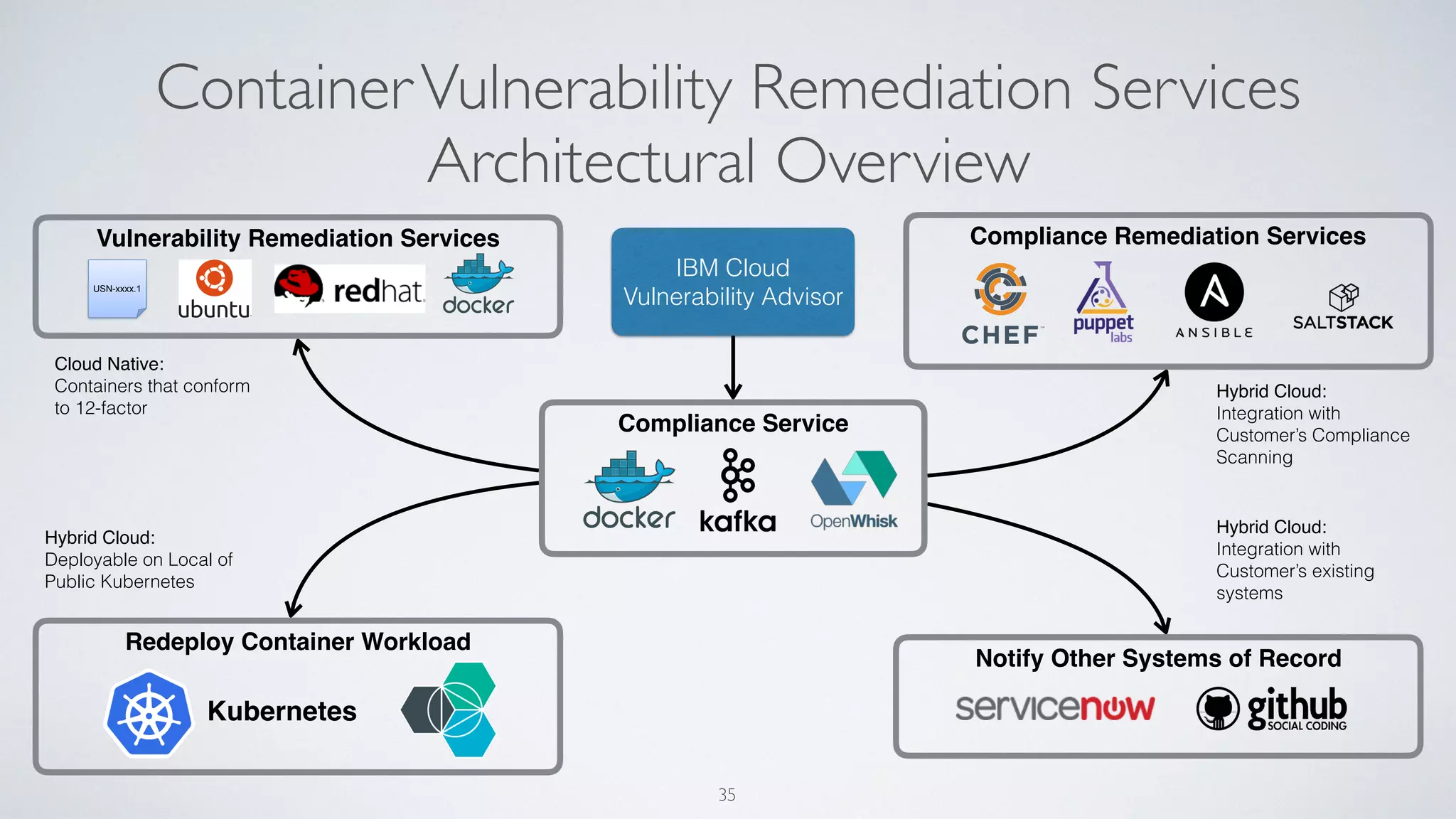
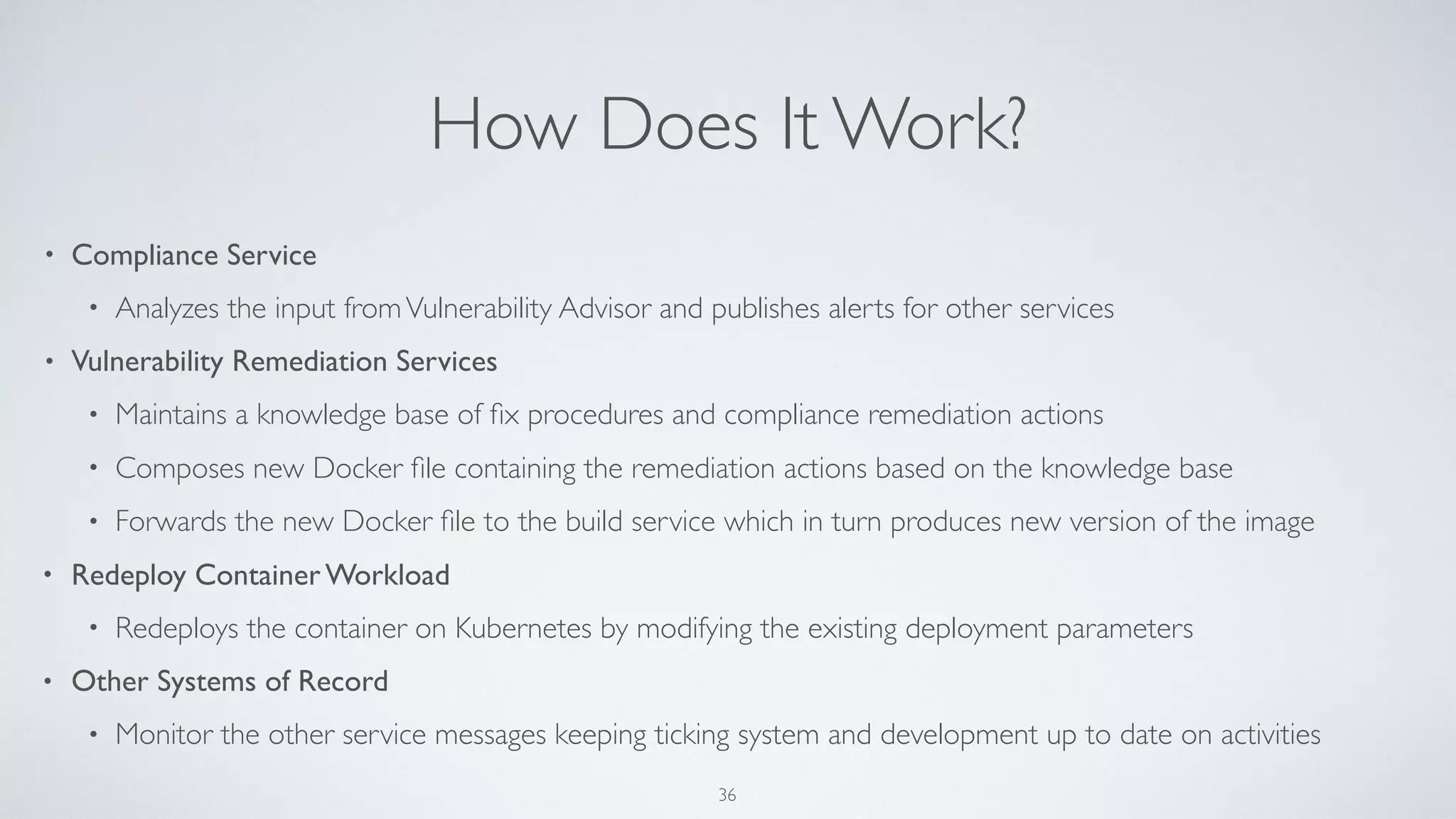
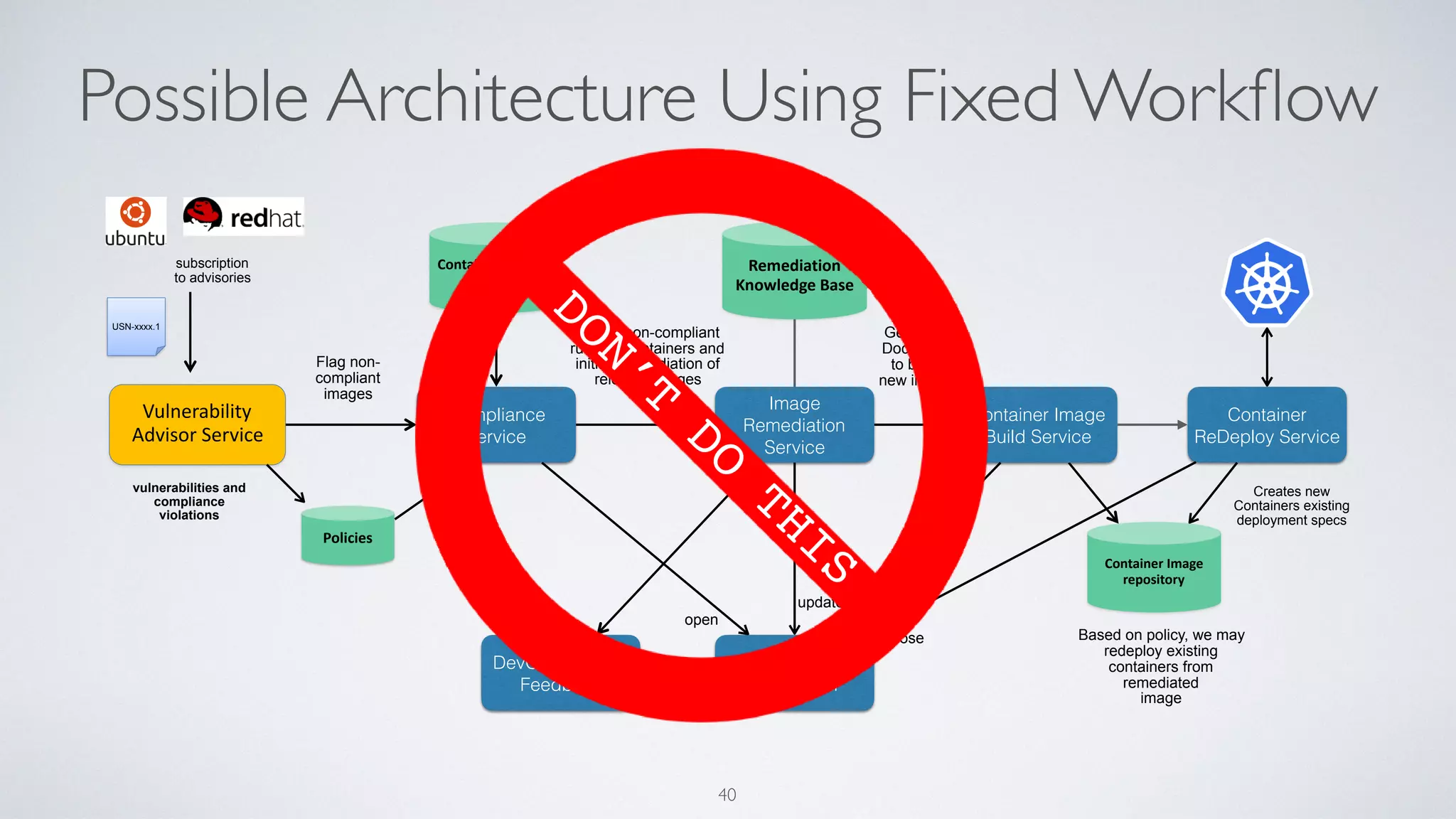
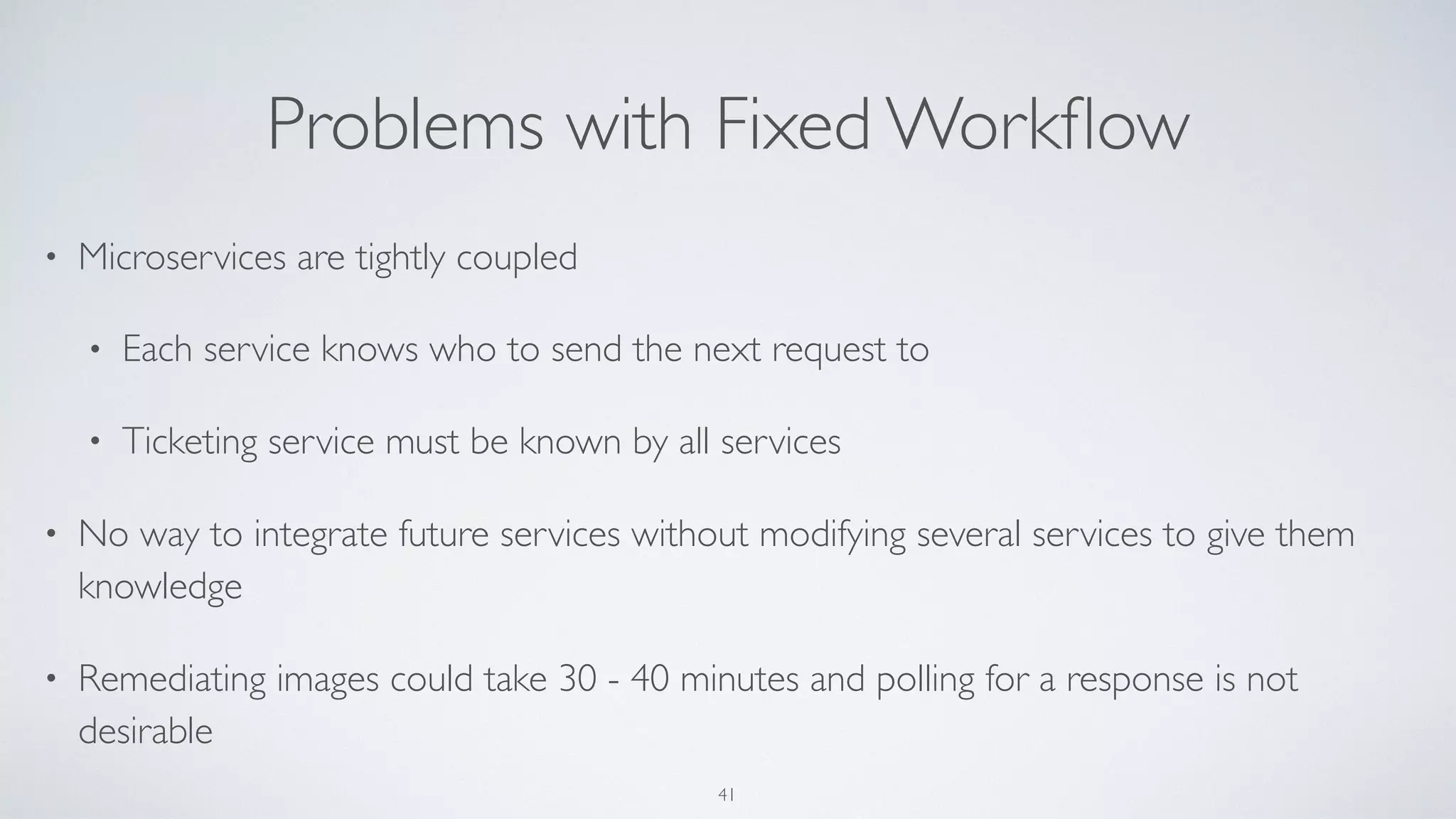
The document discusses the architecture and implementation of microservices, particularly in connection with Docker containers and their vulnerabilities. It emphasizes the benefits of microservices, such as loose coupling and independent deployment, while highlighting the need for continuous management and patching of vulnerabilities in container environments. Additionally, it outlines a solution for automated vulnerability remediation through loosely coupled microservices and DevOps practices.






![FROM alpine:3.3
# Install just the Python runtime (no dev)
RUN apk add --update
python
py-pip
&& rm -rf /var/cache/apk/*
ENV PORT 5000
EXPOSE $PORT
# Set up a working folder and install the pre-reqs
WORKDIR /app
ADD requirements.txt /app
RUN pip install -r requirements.txt
# Add the code as the last Docker layer because it changes the most
ADD static /app/static
ADD service.py /app
# Run the service
CMD [ "python", "service.py" ]
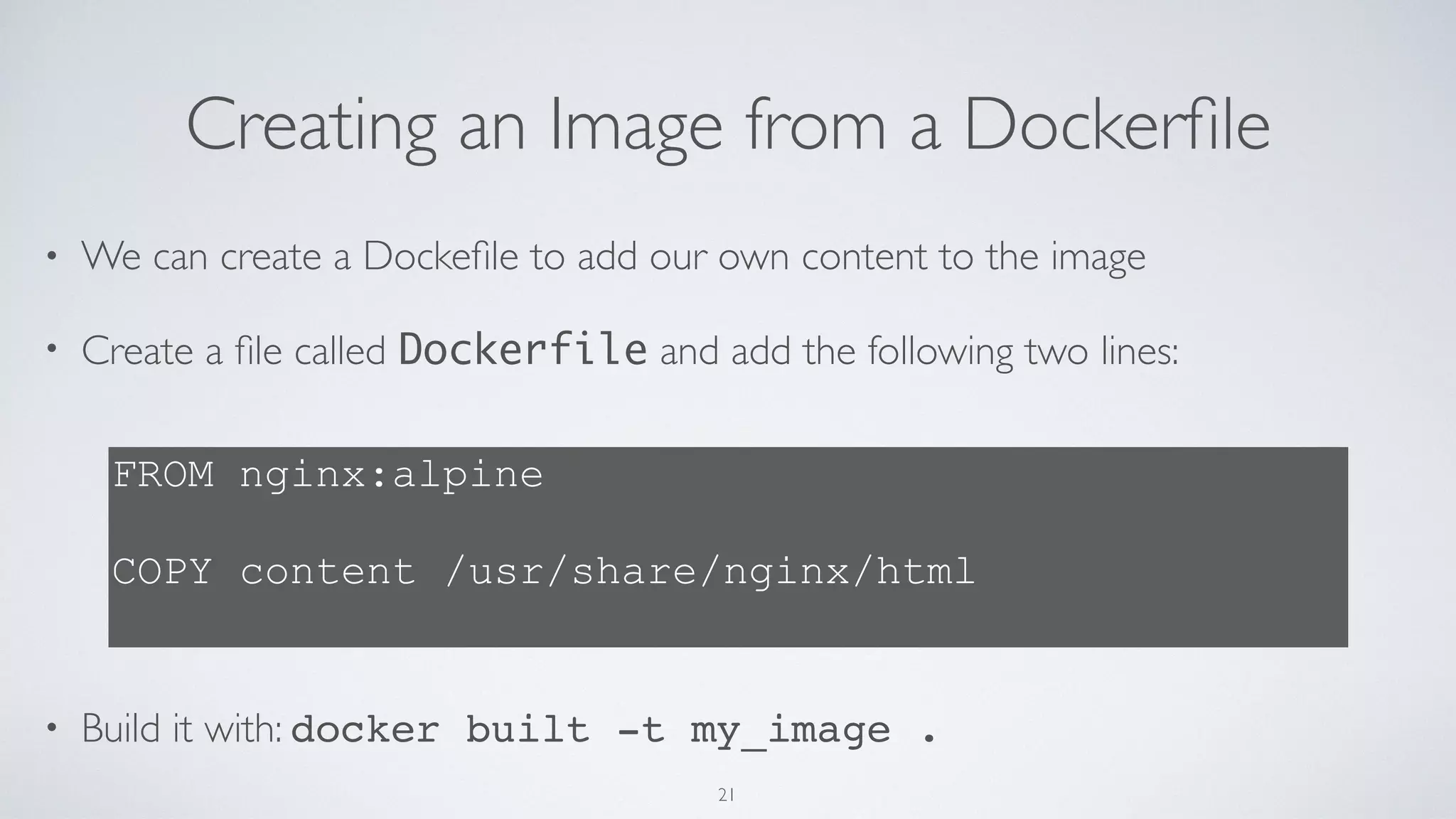
More Advanced Dockerfile
22](https://image.slidesharecdn.com/ieee-microservices-rofrano-180709160548/75/Microservices-How-loose-is-loosely-coupled-25-2048.jpg)



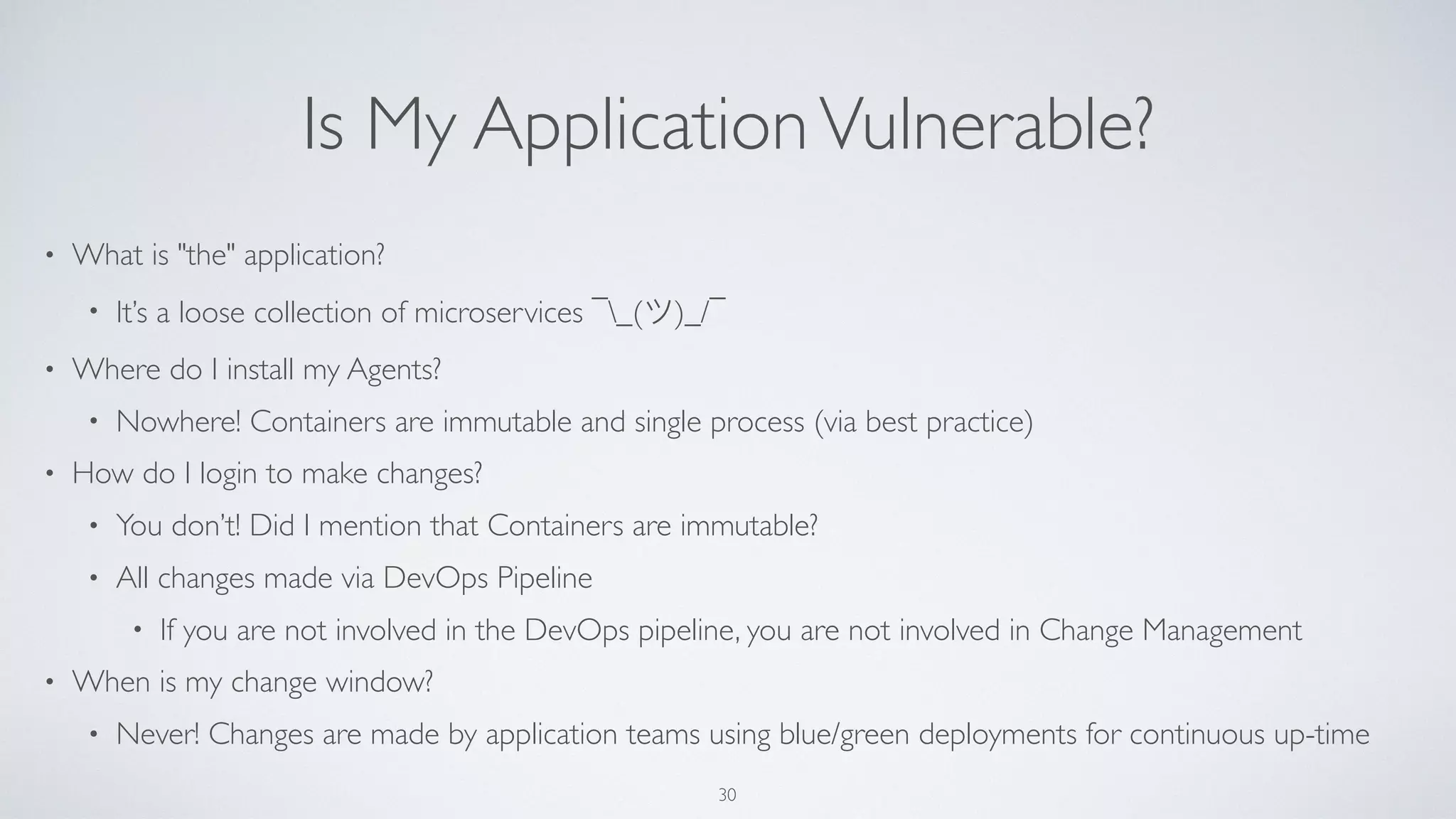



![What’s in a CVE?
37
{
"id": "78de8449-313e-44c9-90b1-ae8277b12f95",
"scan_time": 1510759001,
"status": "WARN",
"vulnerabilities": [
{
"type": "vulnerable_package",
"description": "busybox 1.24.1-r7 has vulnerabilities",
"corrective_action": "Upgrade to busybox 1.24.2-r1",
"fixes": [
{
"cve_ids": "CVE-2016-6301",
"summary": "The recv_and_process_client_pkt function in networking/ntpd.c in busybox allows remote attackers to
cause a denial of service (CPU and bandwidth consumption) via a forged NTP packet, which triggers a communication loop.",
"notice": "",
"meta": {
"usn_id": ""
}
}
],
"meta": {
"package_name": "busybox"
"fix_version": "1.24.2-r1",
"installed_version": "1.24.1-r7",
}
},](https://image.slidesharecdn.com/ieee-microservices-rofrano-180709160548/75/Microservices-How-loose-is-loosely-coupled-44-2048.jpg)
![What’s in a CVE?
37
{
"id": "78de8449-313e-44c9-90b1-ae8277b12f95",
"scan_time": 1510759001,
"status": "WARN",
"vulnerabilities": [
{
"type": "vulnerable_package",
"description": "busybox 1.24.1-r7 has vulnerabilities",
"corrective_action": "Upgrade to busybox 1.24.2-r1",
"fixes": [
{
"cve_ids": "CVE-2016-6301",
"summary": "The recv_and_process_client_pkt function in networking/ntpd.c in busybox allows remote attackers to
cause a denial of service (CPU and bandwidth consumption) via a forged NTP packet, which triggers a communication loop.",
"notice": "",
"meta": {
"usn_id": ""
}
}
],
"meta": {
"package_name": "busybox"
"fix_version": "1.24.2-r1",
"installed_version": "1.24.1-r7",
}
},
This is how we know what to patch](https://image.slidesharecdn.com/ieee-microservices-rofrano-180709160548/75/Microservices-How-loose-is-loosely-coupled-45-2048.jpg)
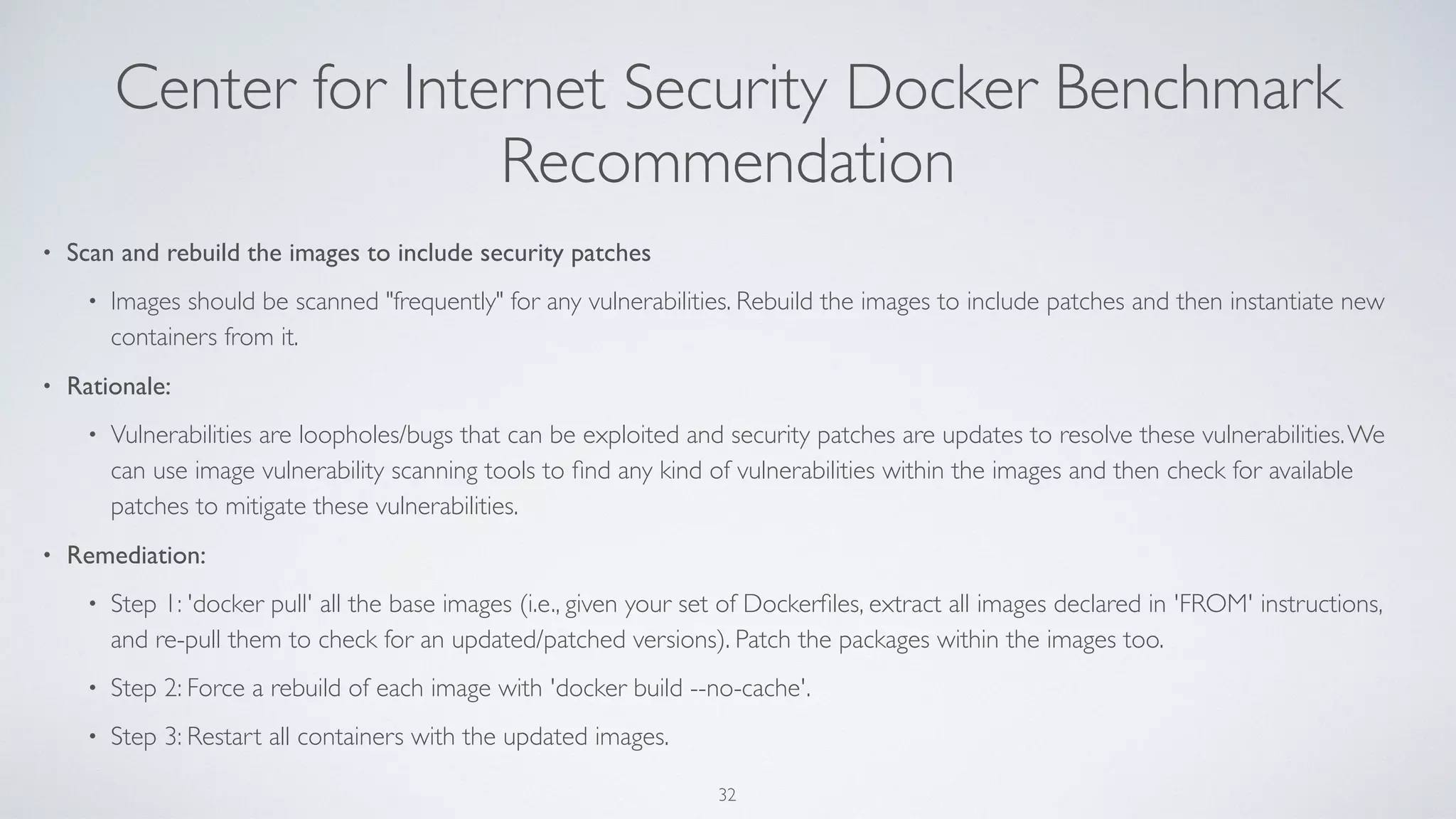
![Generated Dockerfile for Alpine
38
#
# Remediation Service
#
FROM registry.ng.bluemix.net/cloud_service_mgmt/comp-srv:2.1
#
# Patching Vulnerabilities
#
RUN apk add --no-cache busybox=1.24.2-r1;if [ $? -ne 0 ]; then apk add --no-cache busybox; fi;
RUN apk add --no-cache zlib=1.2.11-r0;if [ $? -ne 0 ]; then apk add --no-cache zlib; fi;
#
# Fixing Compliance Issues
#
RUN if [ -e /etc/login.defs ]; then sed -i '/^#/! s/^.*PASS_MAX_DAYS.*$/PASS_MAX_DAYSt90/g' /etc/login.defs; fi;
# NO FIX FOR: Linux.2-1-d - Minimum days that must elapse between user-initiated password changes should be 1.](https://image.slidesharecdn.com/ieee-microservices-rofrano-180709160548/75/Microservices-How-loose-is-loosely-coupled-46-2048.jpg)
![Generated Dockerfile for Alpine
38
#
# Remediation Service
#
FROM registry.ng.bluemix.net/cloud_service_mgmt/comp-srv:2.1
#
# Patching Vulnerabilities
#
RUN apk add --no-cache busybox=1.24.2-r1;if [ $? -ne 0 ]; then apk add --no-cache busybox; fi;
RUN apk add --no-cache zlib=1.2.11-r0;if [ $? -ne 0 ]; then apk add --no-cache zlib; fi;
#
# Fixing Compliance Issues
#
RUN if [ -e /etc/login.defs ]; then sed -i '/^#/! s/^.*PASS_MAX_DAYS.*$/PASS_MAX_DAYSt90/g' /etc/login.defs; fi;
# NO FIX FOR: Linux.2-1-d - Minimum days that must elapse between user-initiated password changes should be 1.
References the original image](https://image.slidesharecdn.com/ieee-microservices-rofrano-180709160548/75/Microservices-How-loose-is-loosely-coupled-47-2048.jpg)
![Generated Dockerfile for Alpine
38
#
# Remediation Service
#
FROM registry.ng.bluemix.net/cloud_service_mgmt/comp-srv:2.1
#
# Patching Vulnerabilities
#
RUN apk add --no-cache busybox=1.24.2-r1;if [ $? -ne 0 ]; then apk add --no-cache busybox; fi;
RUN apk add --no-cache zlib=1.2.11-r0;if [ $? -ne 0 ]; then apk add --no-cache zlib; fi;
#
# Fixing Compliance Issues
#
RUN if [ -e /etc/login.defs ]; then sed -i '/^#/! s/^.*PASS_MAX_DAYS.*$/PASS_MAX_DAYSt90/g' /etc/login.defs; fi;
# NO FIX FOR: Linux.2-1-d - Minimum days that must elapse between user-initiated password changes should be 1.
References the original image
Updates the libraries that are vulnerable](https://image.slidesharecdn.com/ieee-microservices-rofrano-180709160548/75/Microservices-How-loose-is-loosely-coupled-48-2048.jpg)
![Generated Dockerfile for Alpine
38
#
# Remediation Service
#
FROM registry.ng.bluemix.net/cloud_service_mgmt/comp-srv:2.1
#
# Patching Vulnerabilities
#
RUN apk add --no-cache busybox=1.24.2-r1;if [ $? -ne 0 ]; then apk add --no-cache busybox; fi;
RUN apk add --no-cache zlib=1.2.11-r0;if [ $? -ne 0 ]; then apk add --no-cache zlib; fi;
#
# Fixing Compliance Issues
#
RUN if [ -e /etc/login.defs ]; then sed -i '/^#/! s/^.*PASS_MAX_DAYS.*$/PASS_MAX_DAYSt90/g' /etc/login.defs; fi;
# NO FIX FOR: Linux.2-1-d - Minimum days that must elapse between user-initiated password changes should be 1.
References the original image
Updates the libraries that are vulnerable
Fixes known compliance issues](https://image.slidesharecdn.com/ieee-microservices-rofrano-180709160548/75/Microservices-How-loose-is-loosely-coupled-49-2048.jpg)
![Generated Dockerfile for Ubuntu
39
#
# Remediation Service
#
FROM registry.ng.bluemix.net/rofrano/counter:latest
MAINTAINER Vulnerability Remediator 1.0
#
# Patching Vulnerabilities
#
RUN apt-get install -y bash=4.3-7ubuntu1.7;if [ $? -ne 0 ]; then apt-get install -y bash; fi;
RUN apt-get install -y libexpat1=2.1.0-4ubuntu1.4;if [ $? -ne 0 ]; then apt-get install -y libexpat1; fi;
RUN apt-get install -y libffi6=3.1~rc1+r3.0.13-12ubuntu0.2;if [ $? -ne 0 ]; then apt-get install -y libffi6; fi;
RUN apt-get install -y libgcrypt11=1.5.3-2ubuntu4.5;if [ $? -ne 0 ]; then apt-get install -y libgcrypt11; fi;
RUN apt-get install -y libgnutls26=2.12.23-12ubuntu2.8;if [ $? -ne 0 ]; then apt-get install -y libgnutls26; fi;
RUN apt-get install -y libssl1.0.0=1.0.1f-1ubuntu2.23;if [ $? -ne 0 ]; then apt-get install -y libssl1.0.0; fi;
RUN apt-get install -y libtasn1-6=3.4-3ubuntu0.5;if [ $? -ne 0 ]; then apt-get install -y libtasn1-6; fi;
RUN apt-get install -y login=1:4.1.5.1-1ubuntu9.5;if [ $? -ne 0 ]; then apt-get install -y login; fi;
RUN apt-get install -y passwd=1:4.1.5.1-1ubuntu9.5;if [ $? -ne 0 ]; then apt-get install -y passwd; fi;
RUN apt-get install -y sudo=1.8.9p5-1ubuntu1.4;if [ $? -ne 0 ]; then apt-get install -y sudo; fi;](https://image.slidesharecdn.com/ieee-microservices-rofrano-180709160548/75/Microservices-How-loose-is-loosely-coupled-50-2048.jpg)


![Example Python Cloud Function
47
def main(params):
""" Container Redeploy Function """
# Get the API key and use it in the headers
headers = get_headers(params)
api_endpoint = params.get('API_ENDPOINT')
value = params['messages'][0]['value'] # process messages
namespace = value.get('namespace', 'default') # check parameters
# create the message body
body = {
'namespace': namespace,
'old_image': value['old_image'],
'new_image': value['new_image']
}
logging.info('Redeploying: %s', value['old_image'])
result = requests.post(api_endpoint,
data=json.dumps(body),
headers=headers)
message = result.json()
return {'result': message}](https://image.slidesharecdn.com/ieee-microservices-rofrano-180709160548/75/Microservices-How-loose-is-loosely-coupled-59-2048.jpg)
![Example Python Cloud Function
47
def main(params):
""" Container Redeploy Function """
# Get the API key and use it in the headers
headers = get_headers(params)
api_endpoint = params.get('API_ENDPOINT')
value = params['messages'][0]['value'] # process messages
namespace = value.get('namespace', 'default') # check parameters
# create the message body
body = {
'namespace': namespace,
'old_image': value['old_image'],
'new_image': value['new_image']
}
logging.info('Redeploying: %s', value['old_image'])
result = requests.post(api_endpoint,
data=json.dumps(body),
headers=headers)
message = result.json()
return {'result': message}
Get the endpoint to be called](https://image.slidesharecdn.com/ieee-microservices-rofrano-180709160548/75/Microservices-How-loose-is-loosely-coupled-60-2048.jpg)
![Example Python Cloud Function
47
def main(params):
""" Container Redeploy Function """
# Get the API key and use it in the headers
headers = get_headers(params)
api_endpoint = params.get('API_ENDPOINT')
value = params['messages'][0]['value'] # process messages
namespace = value.get('namespace', 'default') # check parameters
# create the message body
body = {
'namespace': namespace,
'old_image': value['old_image'],
'new_image': value['new_image']
}
logging.info('Redeploying: %s', value['old_image'])
result = requests.post(api_endpoint,
data=json.dumps(body),
headers=headers)
message = result.json()
return {'result': message}
Get the endpoint to be called
Get parameters passed in](https://image.slidesharecdn.com/ieee-microservices-rofrano-180709160548/75/Microservices-How-loose-is-loosely-coupled-61-2048.jpg)
![Example Python Cloud Function
47
def main(params):
""" Container Redeploy Function """
# Get the API key and use it in the headers
headers = get_headers(params)
api_endpoint = params.get('API_ENDPOINT')
value = params['messages'][0]['value'] # process messages
namespace = value.get('namespace', 'default') # check parameters
# create the message body
body = {
'namespace': namespace,
'old_image': value['old_image'],
'new_image': value['new_image']
}
logging.info('Redeploying: %s', value['old_image'])
result = requests.post(api_endpoint,
data=json.dumps(body),
headers=headers)
message = result.json()
return {'result': message}
Get the endpoint to be called
Get parameters passed in
Construct body of request
for microservice to call](https://image.slidesharecdn.com/ieee-microservices-rofrano-180709160548/75/Microservices-How-loose-is-loosely-coupled-62-2048.jpg)
![Example Python Cloud Function
47
def main(params):
""" Container Redeploy Function """
# Get the API key and use it in the headers
headers = get_headers(params)
api_endpoint = params.get('API_ENDPOINT')
value = params['messages'][0]['value'] # process messages
namespace = value.get('namespace', 'default') # check parameters
# create the message body
body = {
'namespace': namespace,
'old_image': value['old_image'],
'new_image': value['new_image']
}
logging.info('Redeploying: %s', value['old_image'])
result = requests.post(api_endpoint,
data=json.dumps(body),
headers=headers)
message = result.json()
return {'result': message}
Get the endpoint to be called
Get parameters passed in
Construct body of request
for microservice to call
Make the call to fire off the microservice](https://image.slidesharecdn.com/ieee-microservices-rofrano-180709160548/75/Microservices-How-loose-is-loosely-coupled-63-2048.jpg)
![Example Python Cloud Function
47
def main(params):
""" Container Redeploy Function """
# Get the API key and use it in the headers
headers = get_headers(params)
api_endpoint = params.get('API_ENDPOINT')
value = params['messages'][0]['value'] # process messages
namespace = value.get('namespace', 'default') # check parameters
# create the message body
body = {
'namespace': namespace,
'old_image': value['old_image'],
'new_image': value['new_image']
}
logging.info('Redeploying: %s', value['old_image'])
result = requests.post(api_endpoint,
data=json.dumps(body),
headers=headers)
message = result.json()
return {'result': message}
Get the endpoint to be called
Get parameters passed in
Construct body of request
for microservice to call
Make the call to fire off the microservice
Return the microservice output](https://image.slidesharecdn.com/ieee-microservices-rofrano-180709160548/75/Microservices-How-loose-is-loosely-coupled-64-2048.jpg)