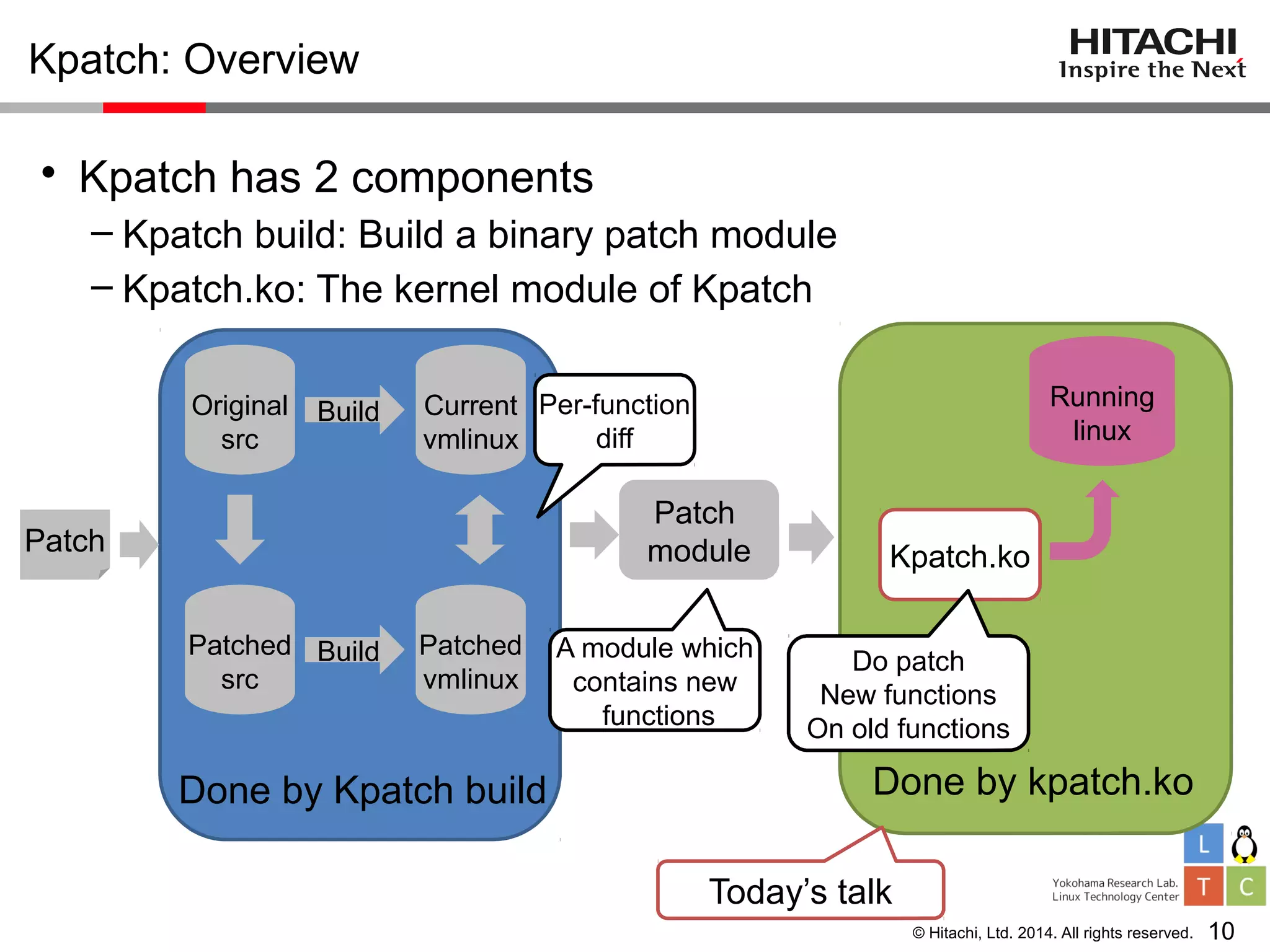
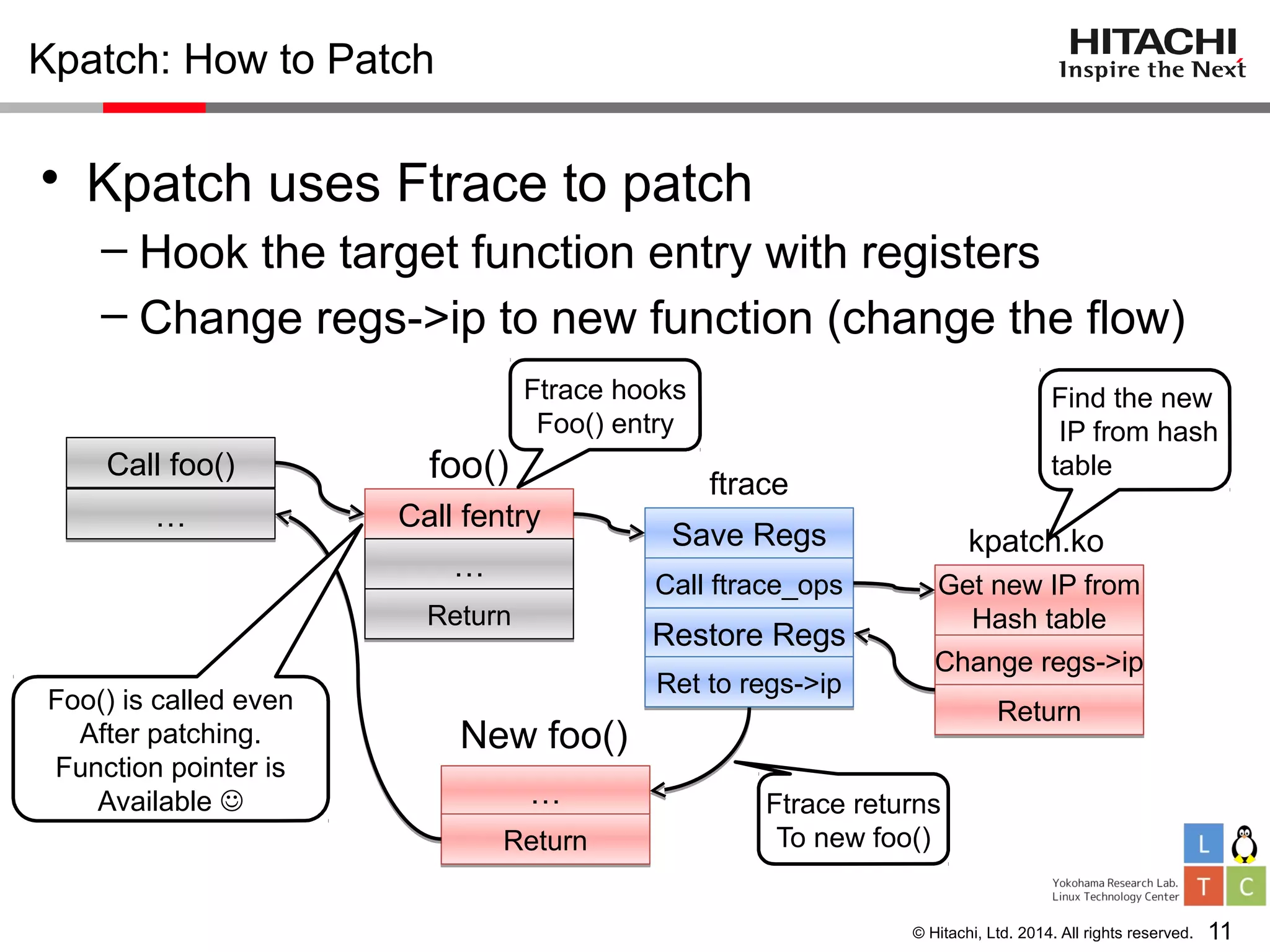
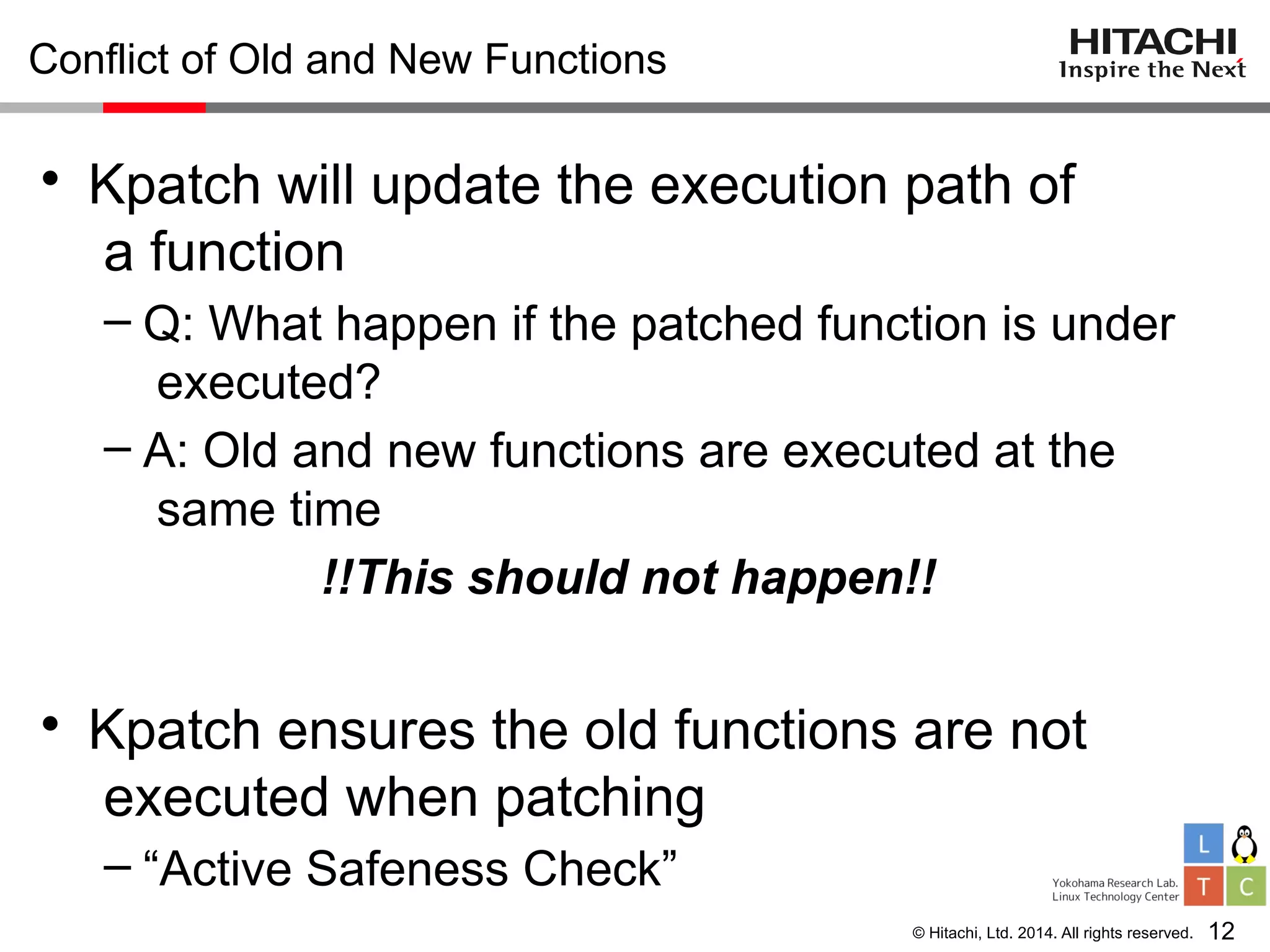
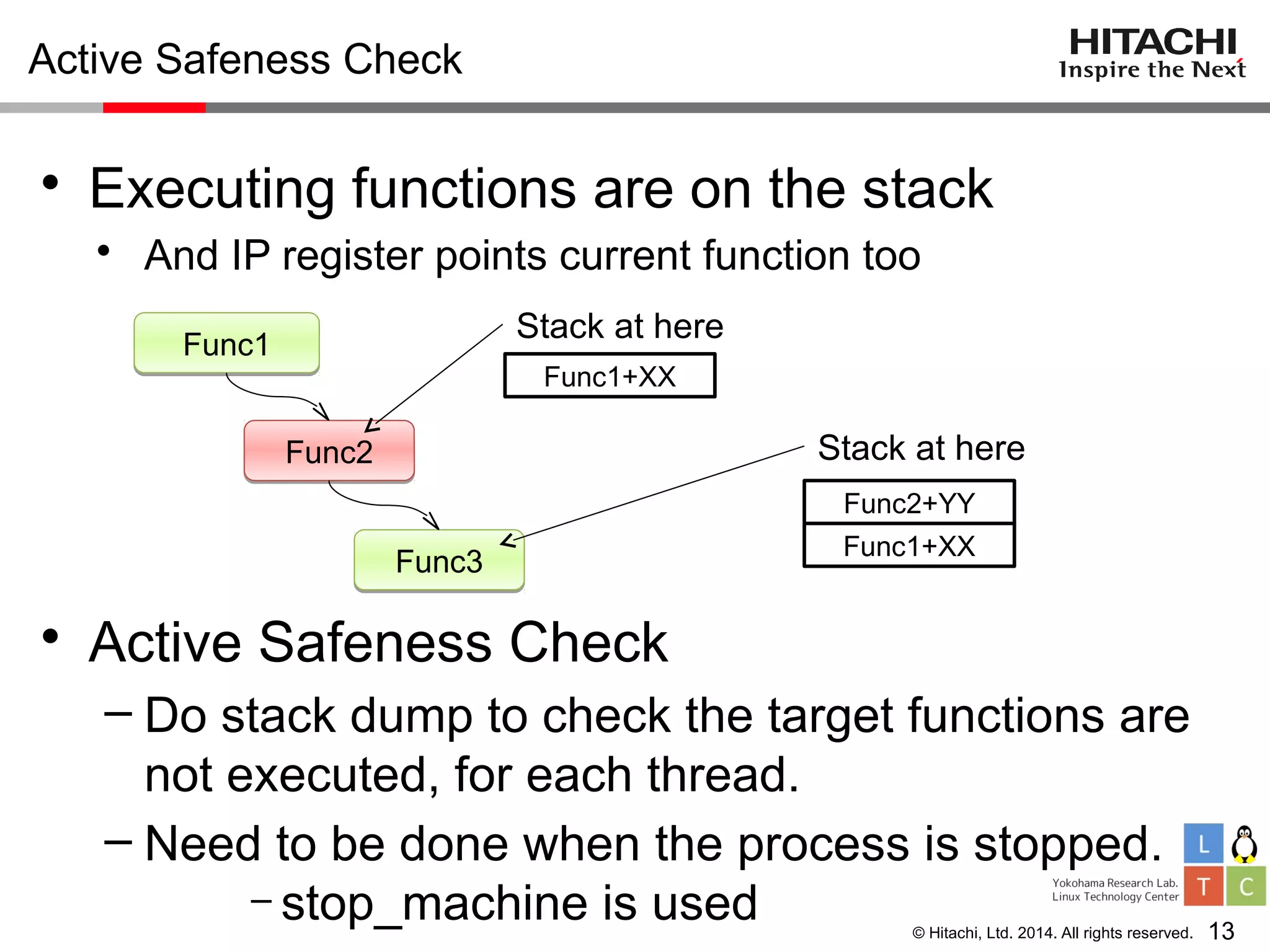
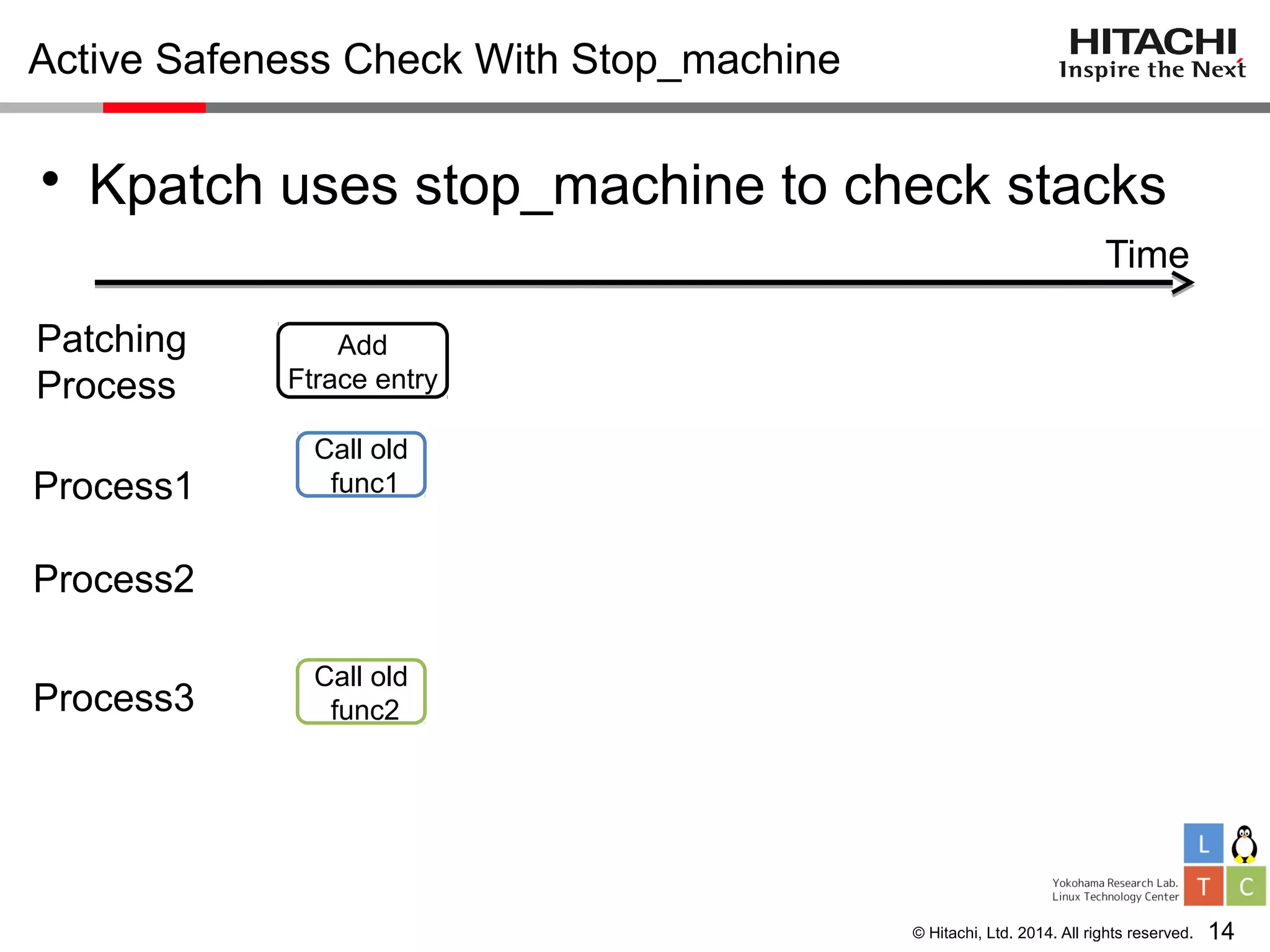
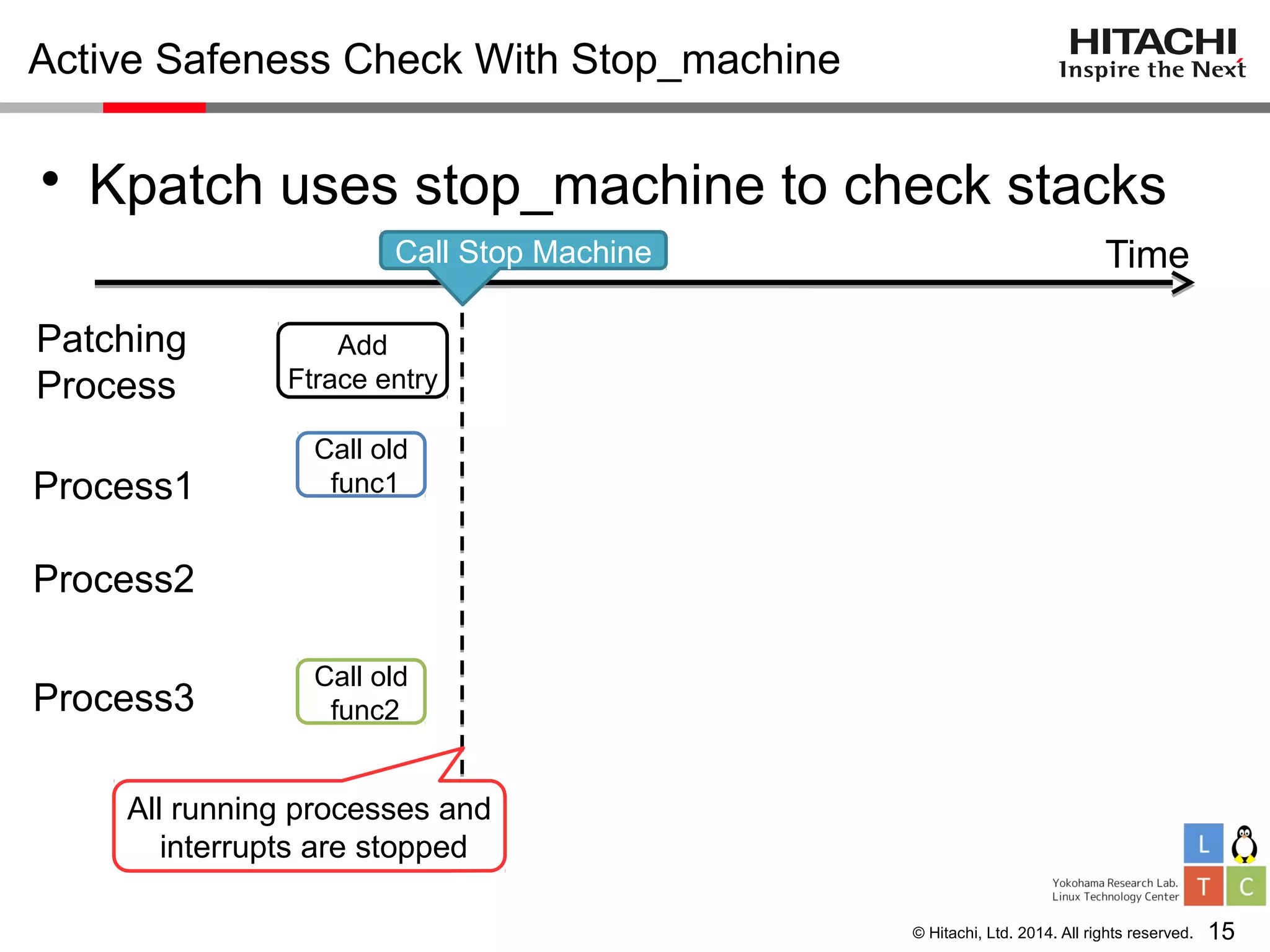
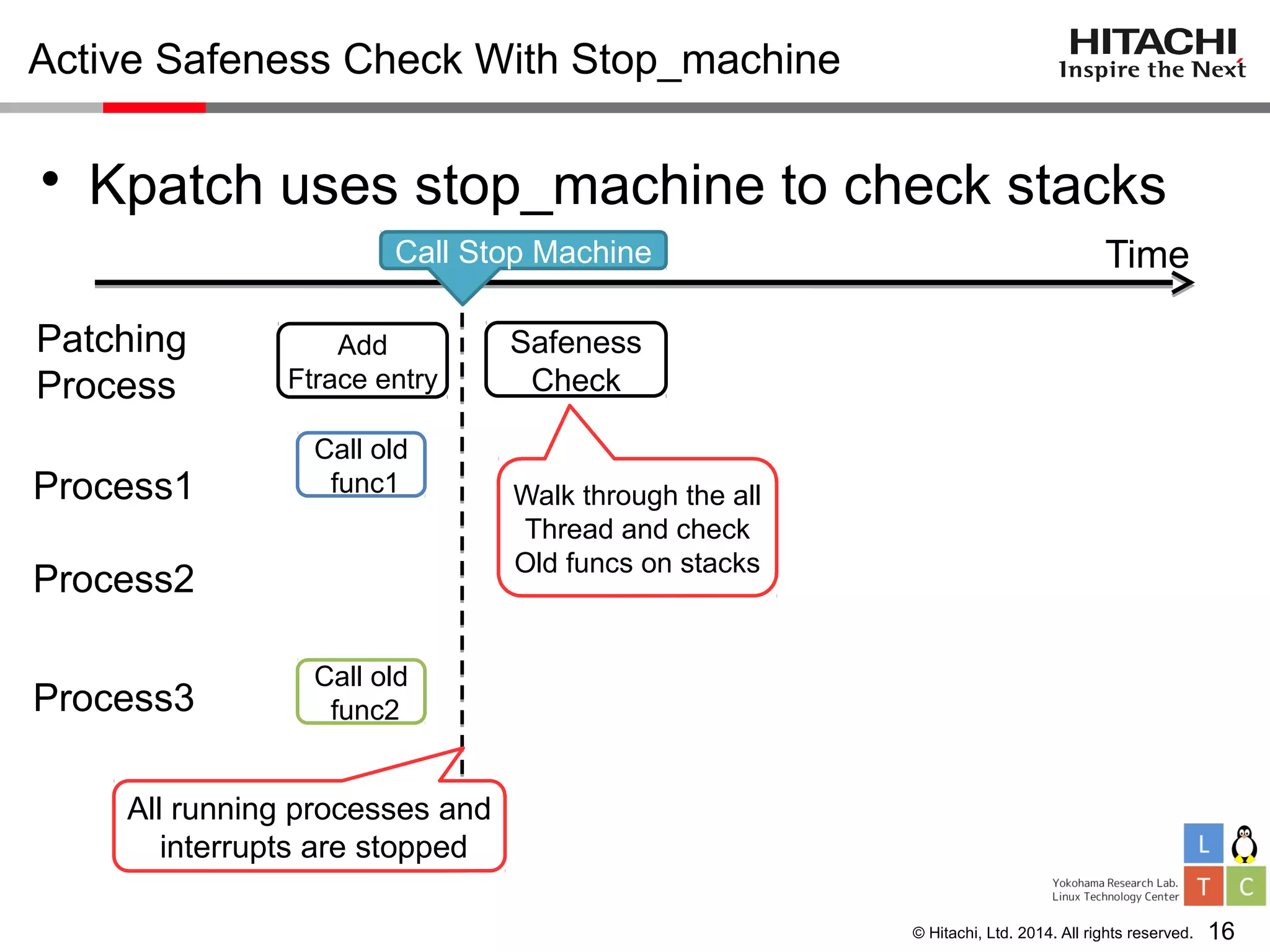
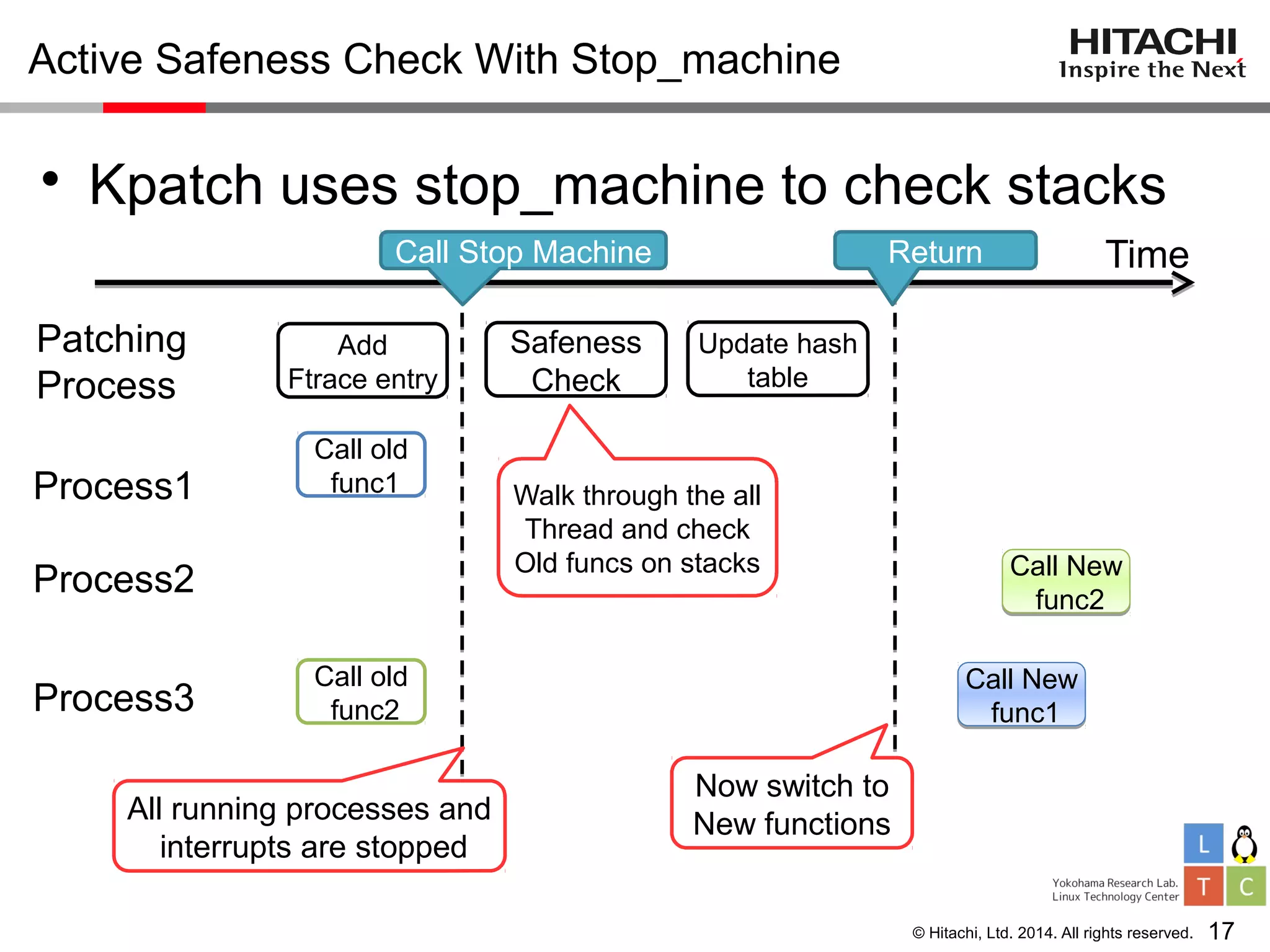
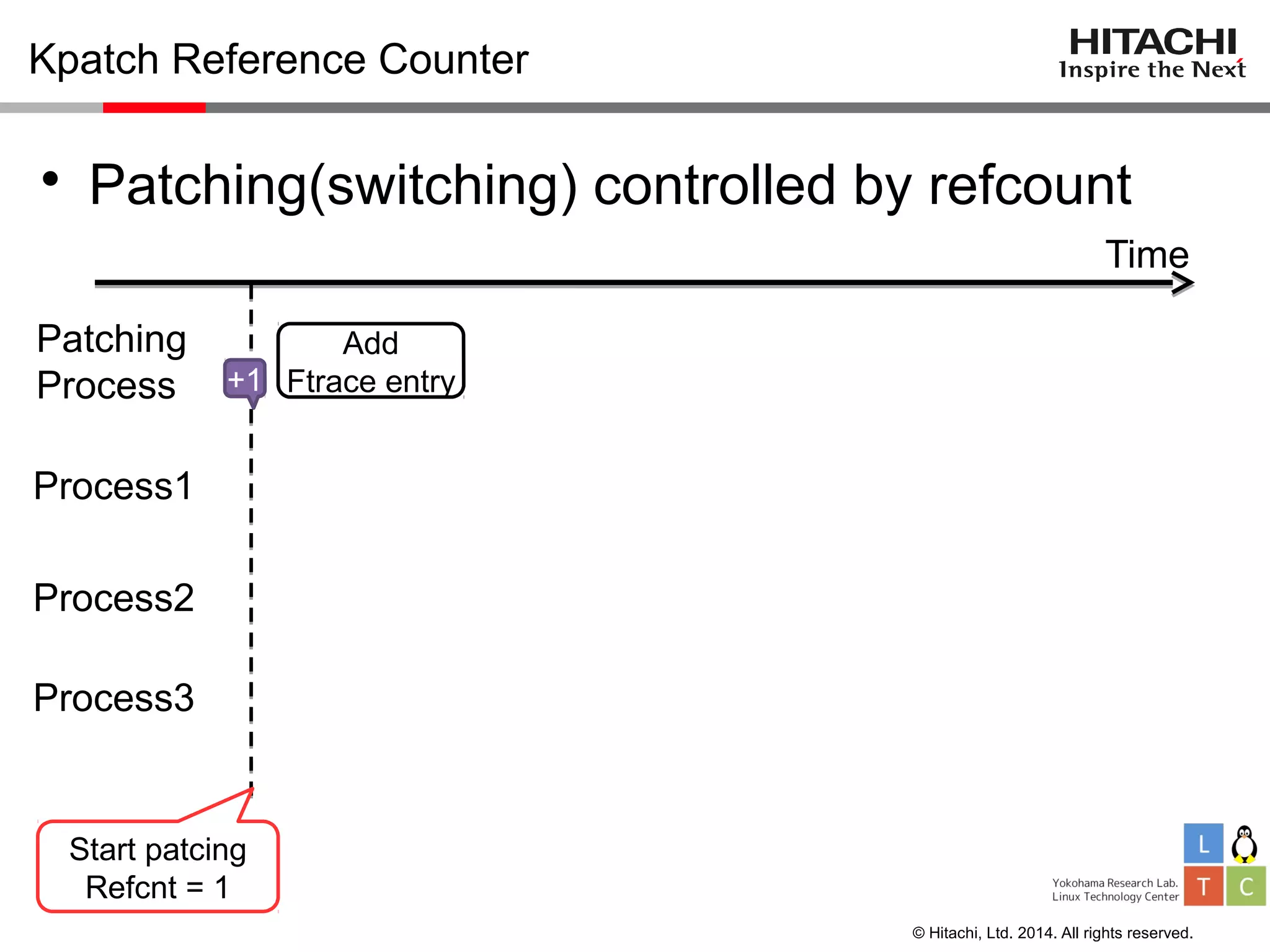
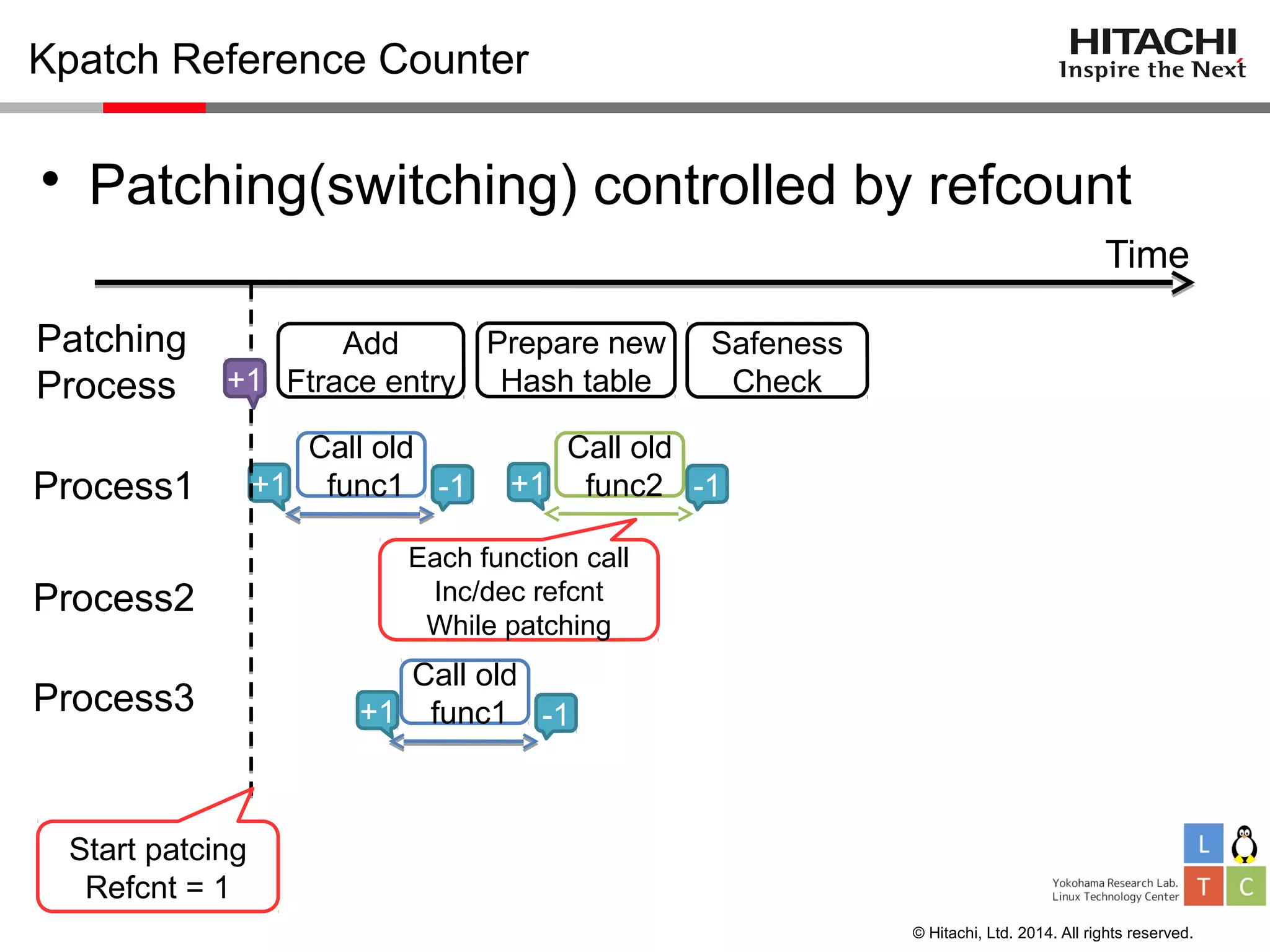
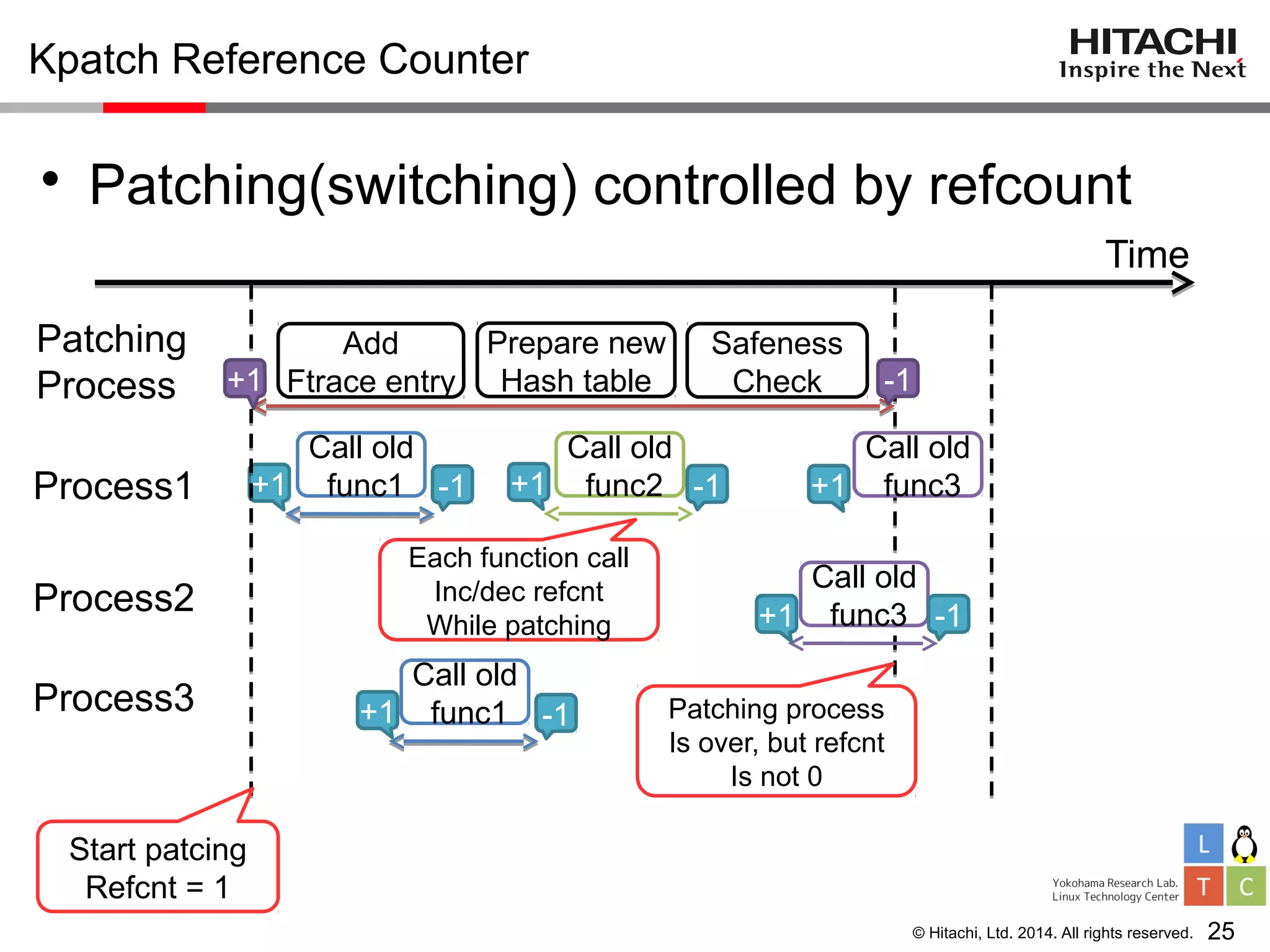
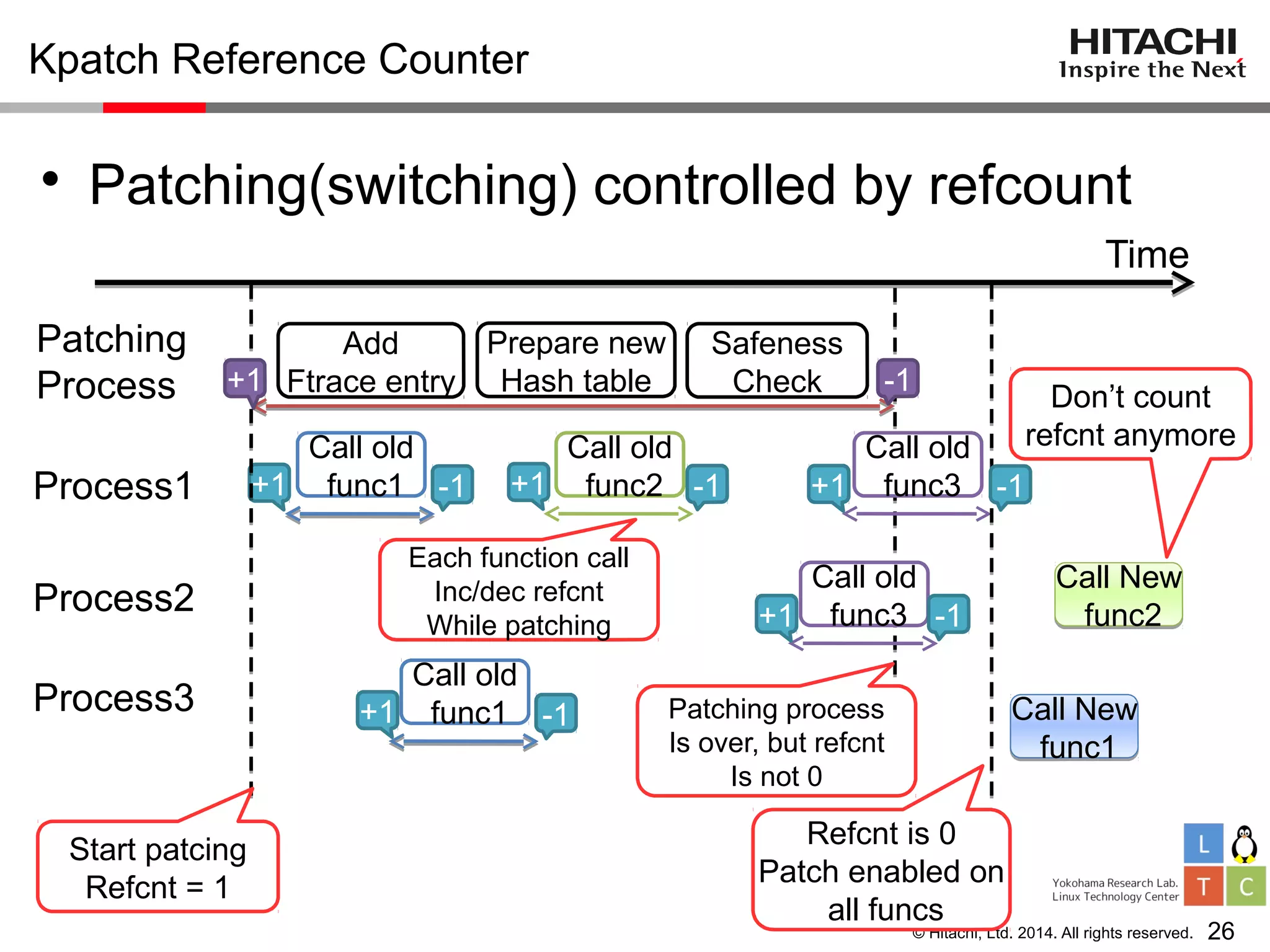
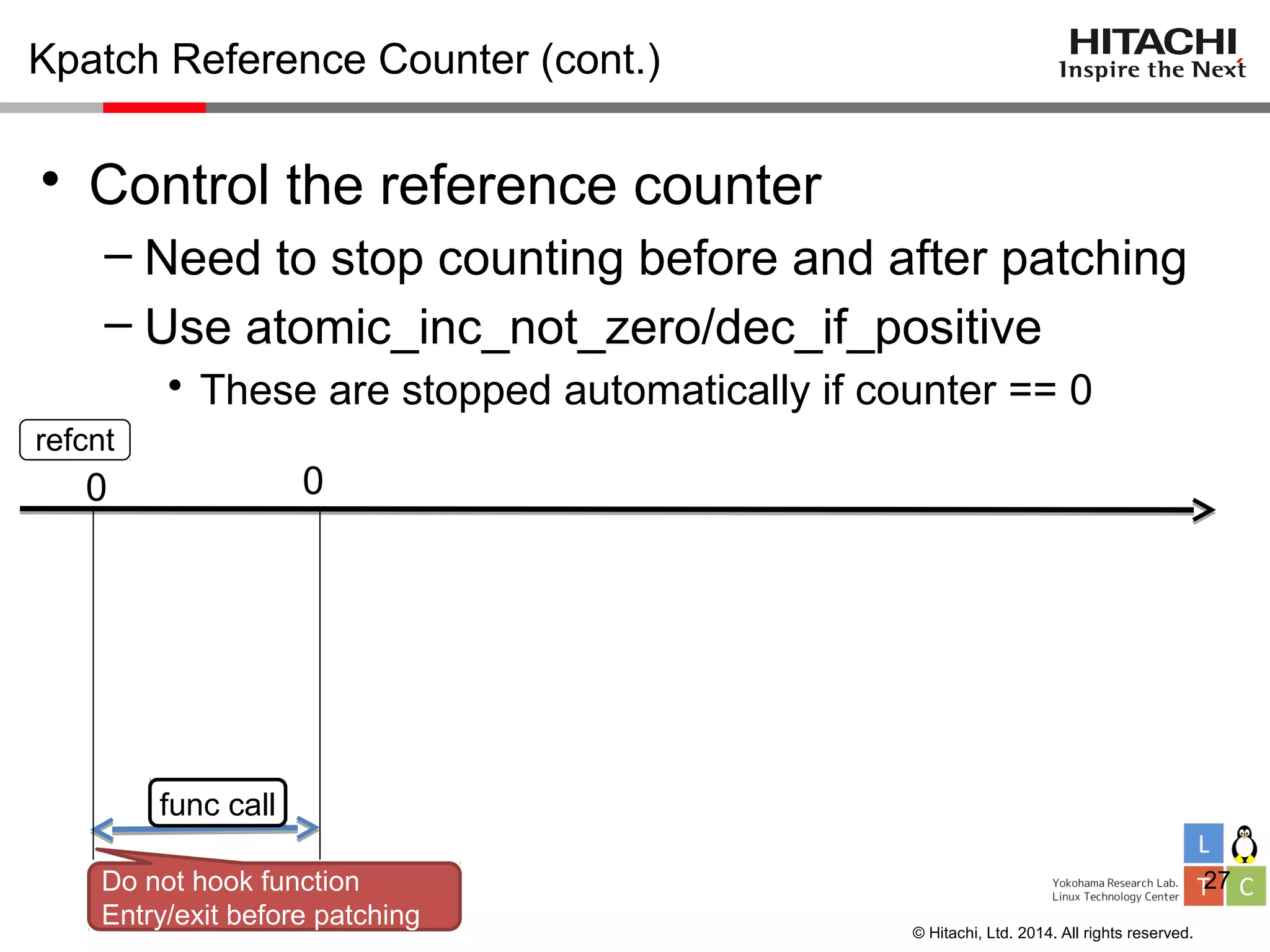
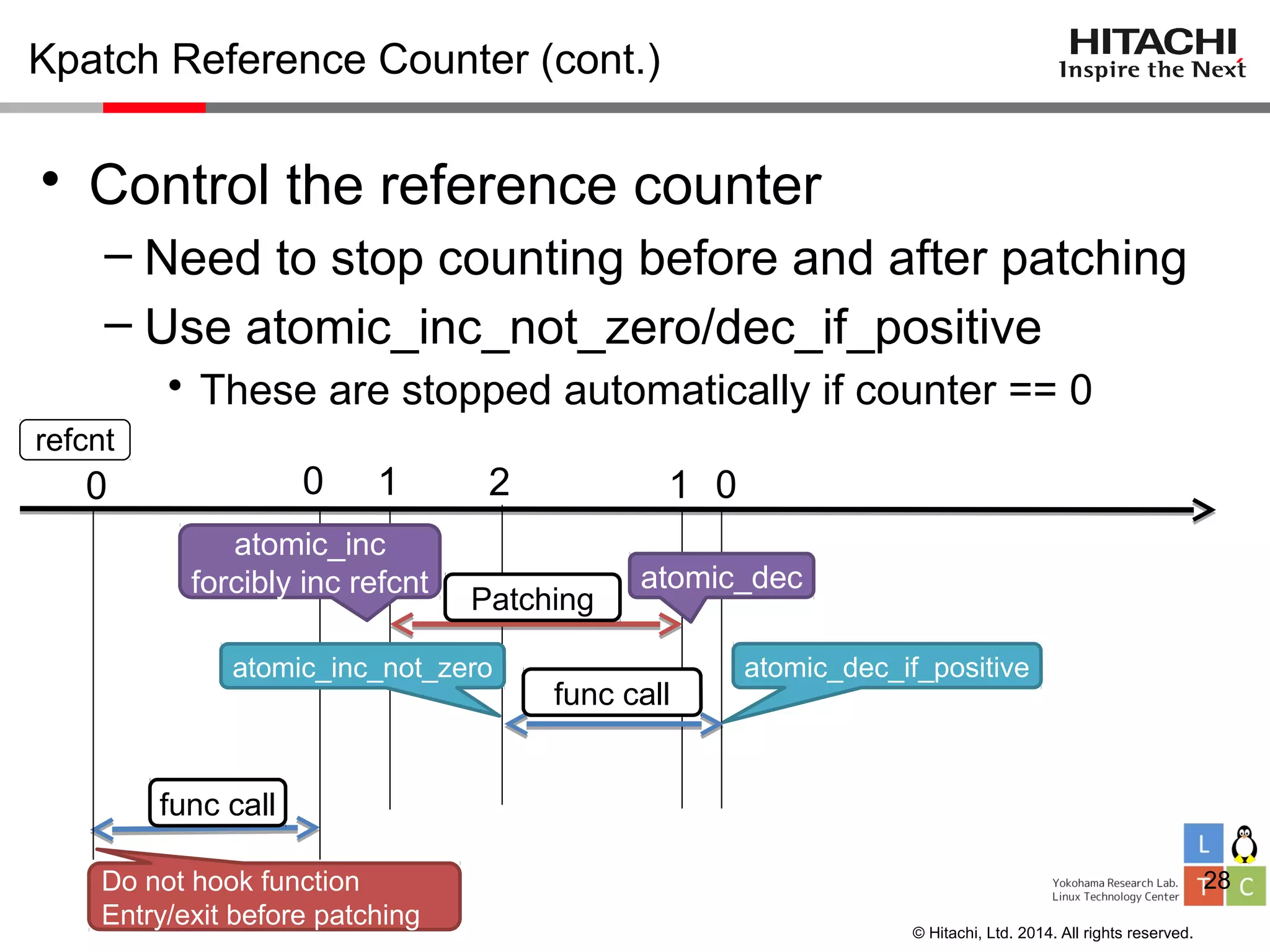
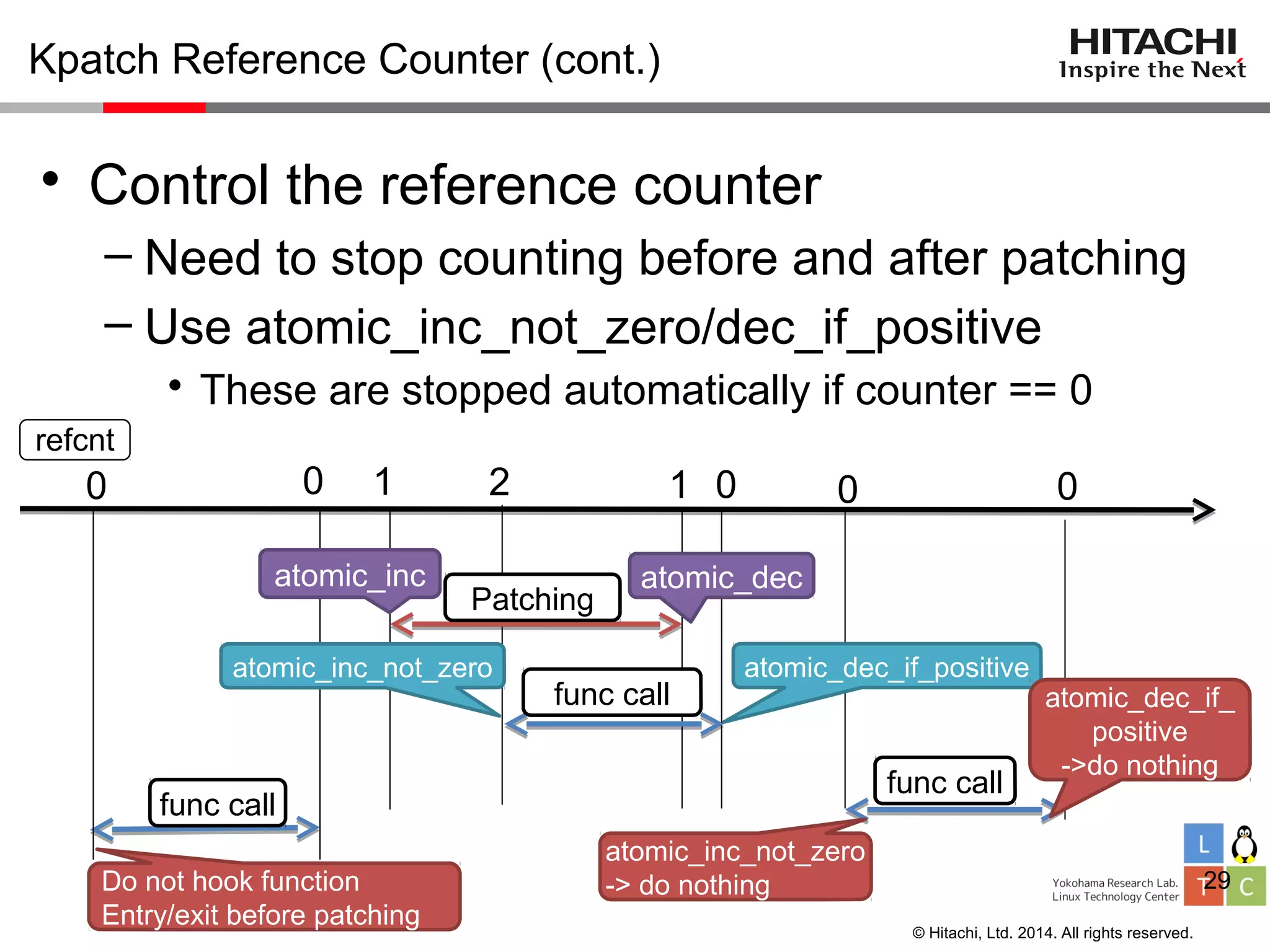
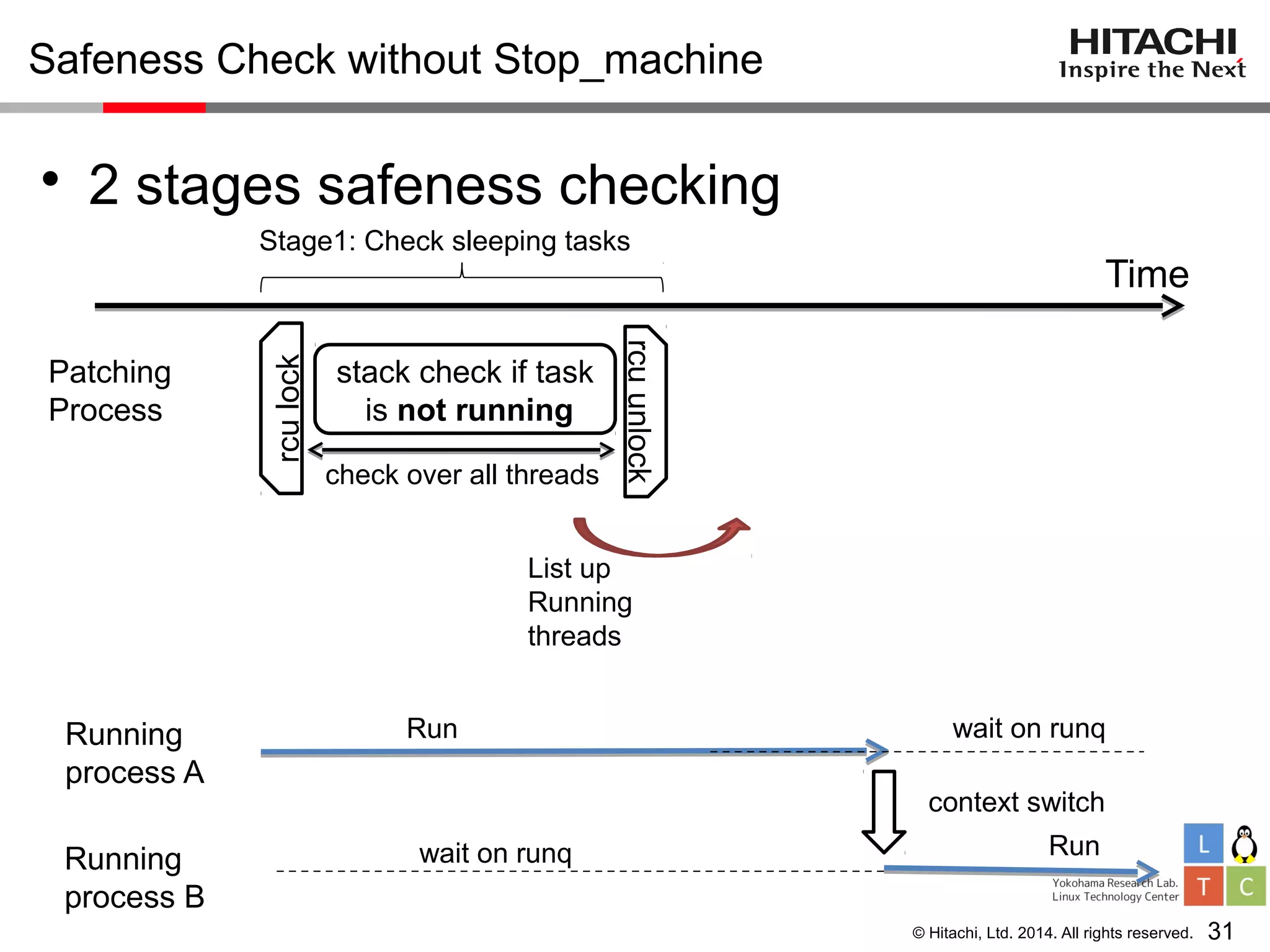
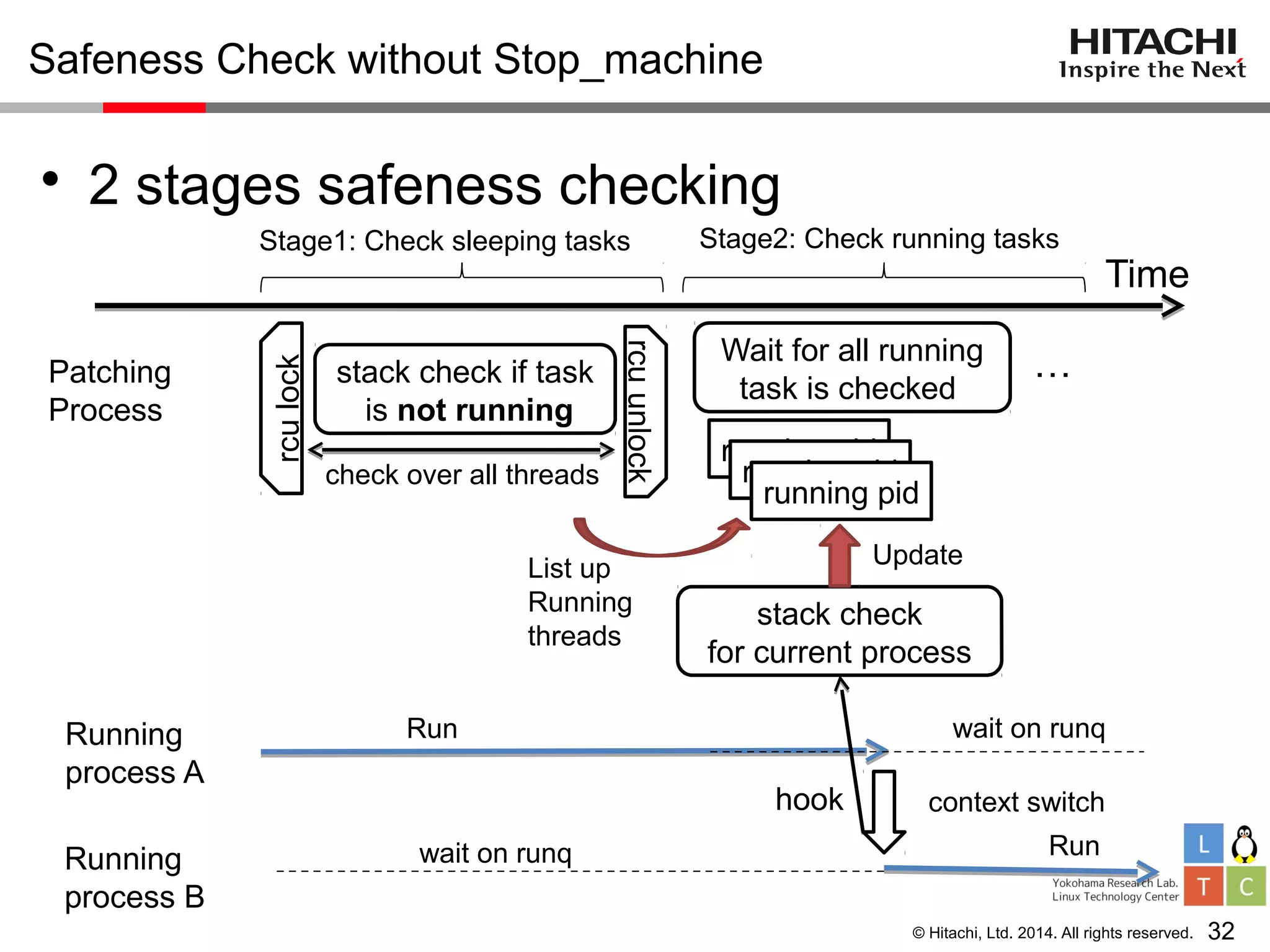
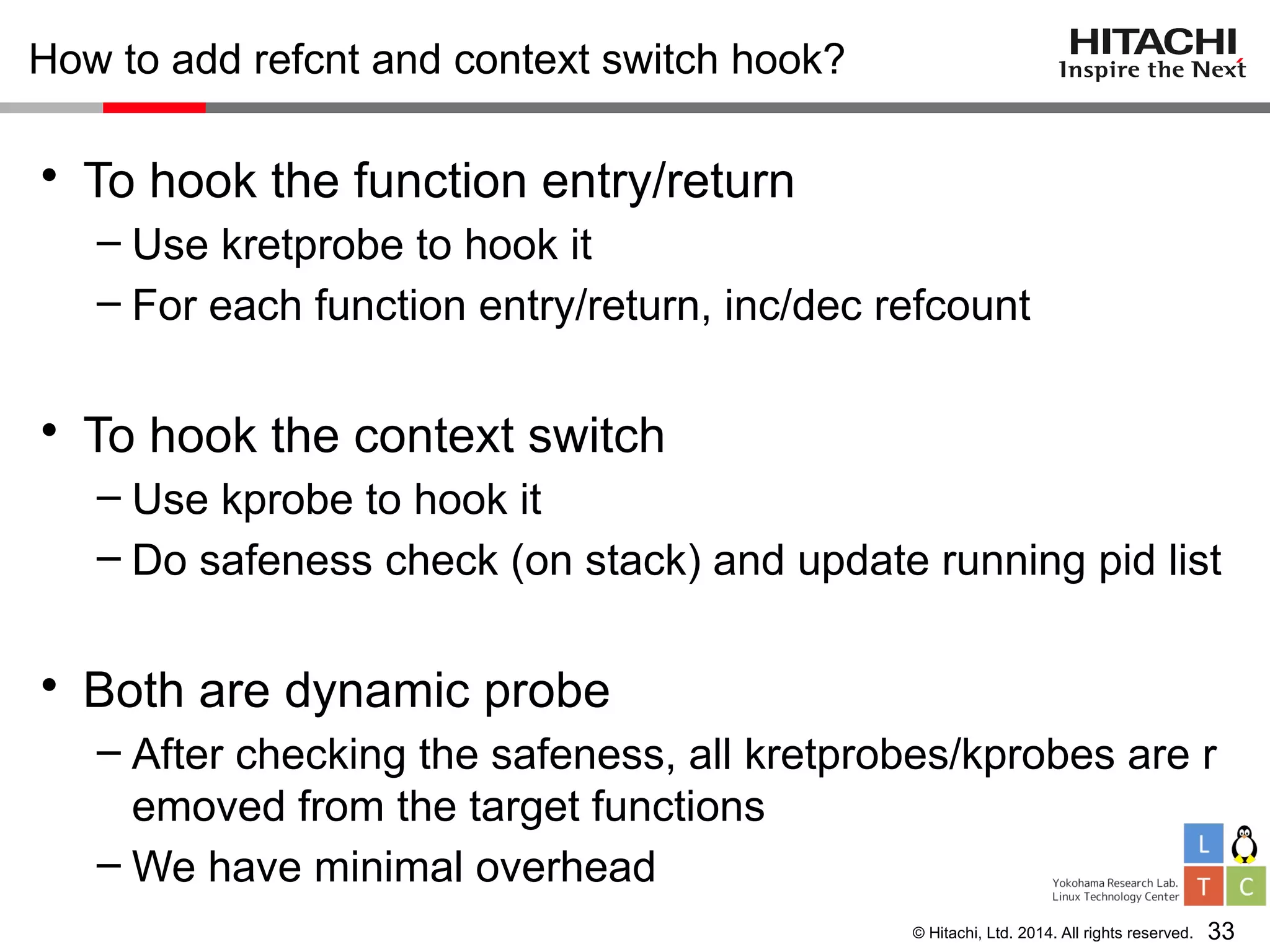
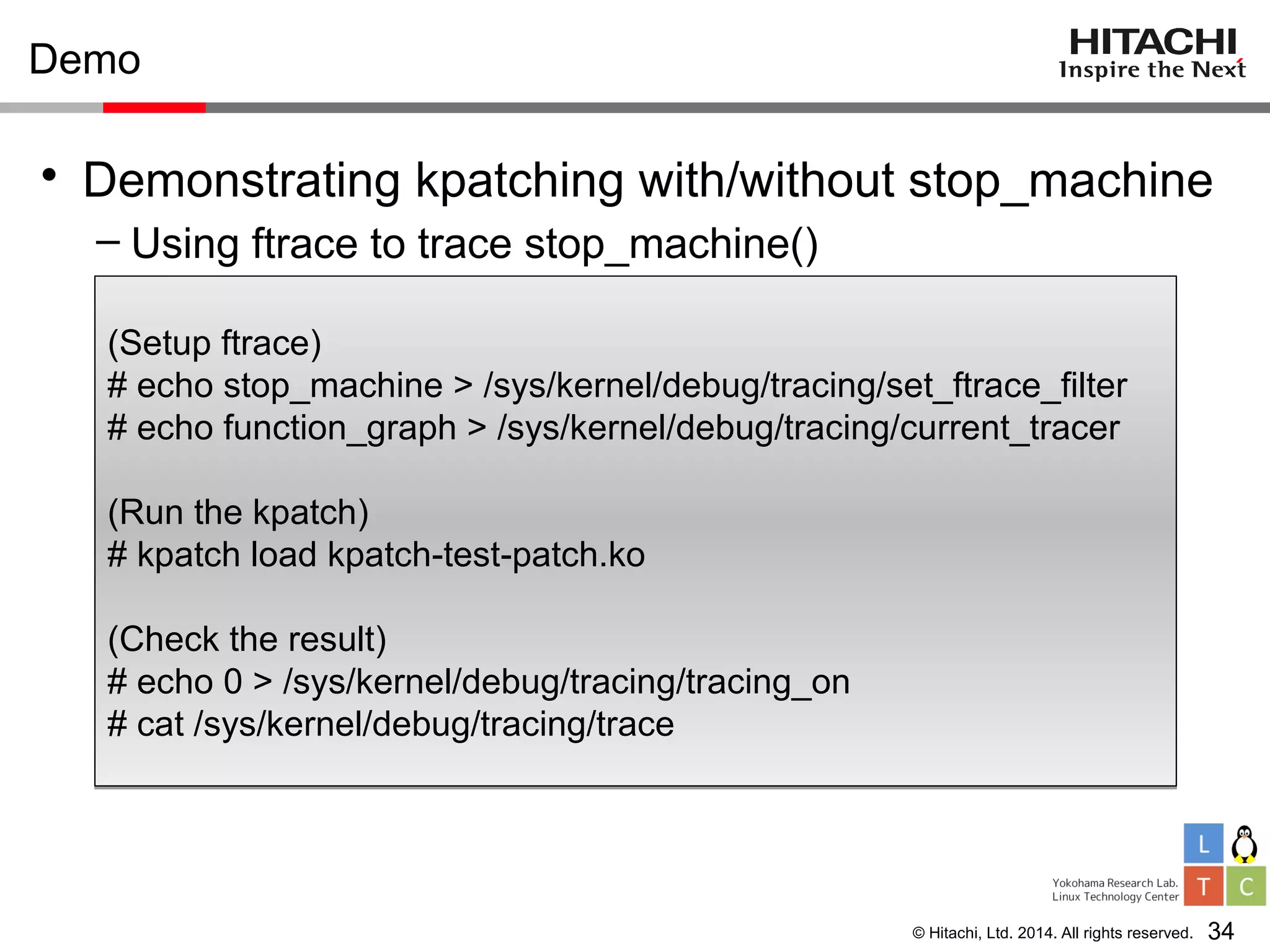
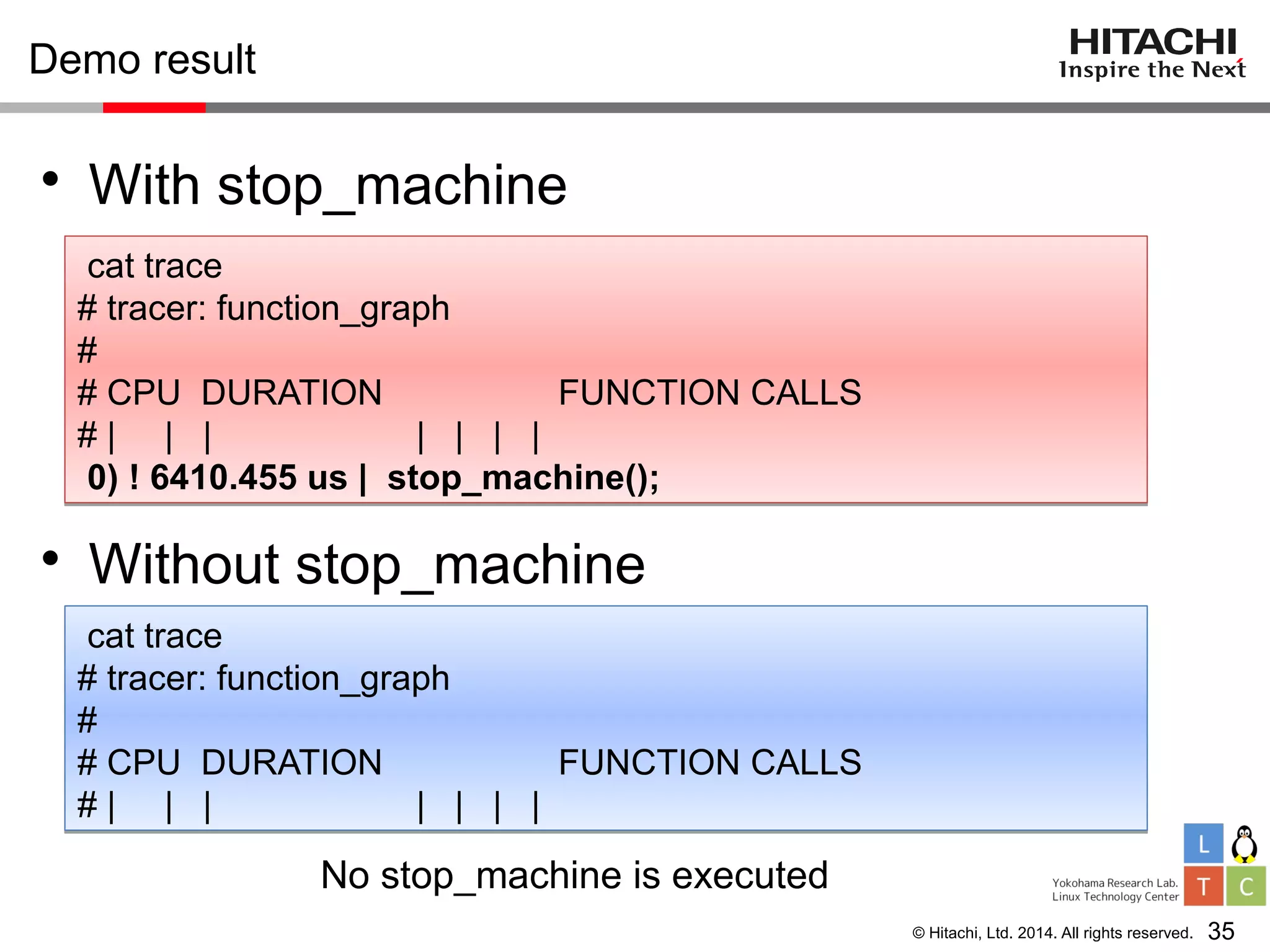
This document summarizes a presentation about kpatch without stopping machines. Kpatch is a live patching tool that applies binary patches to the kernel without requiring a reboot. Originally, kpatch used stop_machine to safely check for active functions during patching. The presentation introduces improvements that allow kpatch to patch without stopping all processes. This is done by using an atomic reference counter and hooking context switches to safely check stacks while processes continue running.