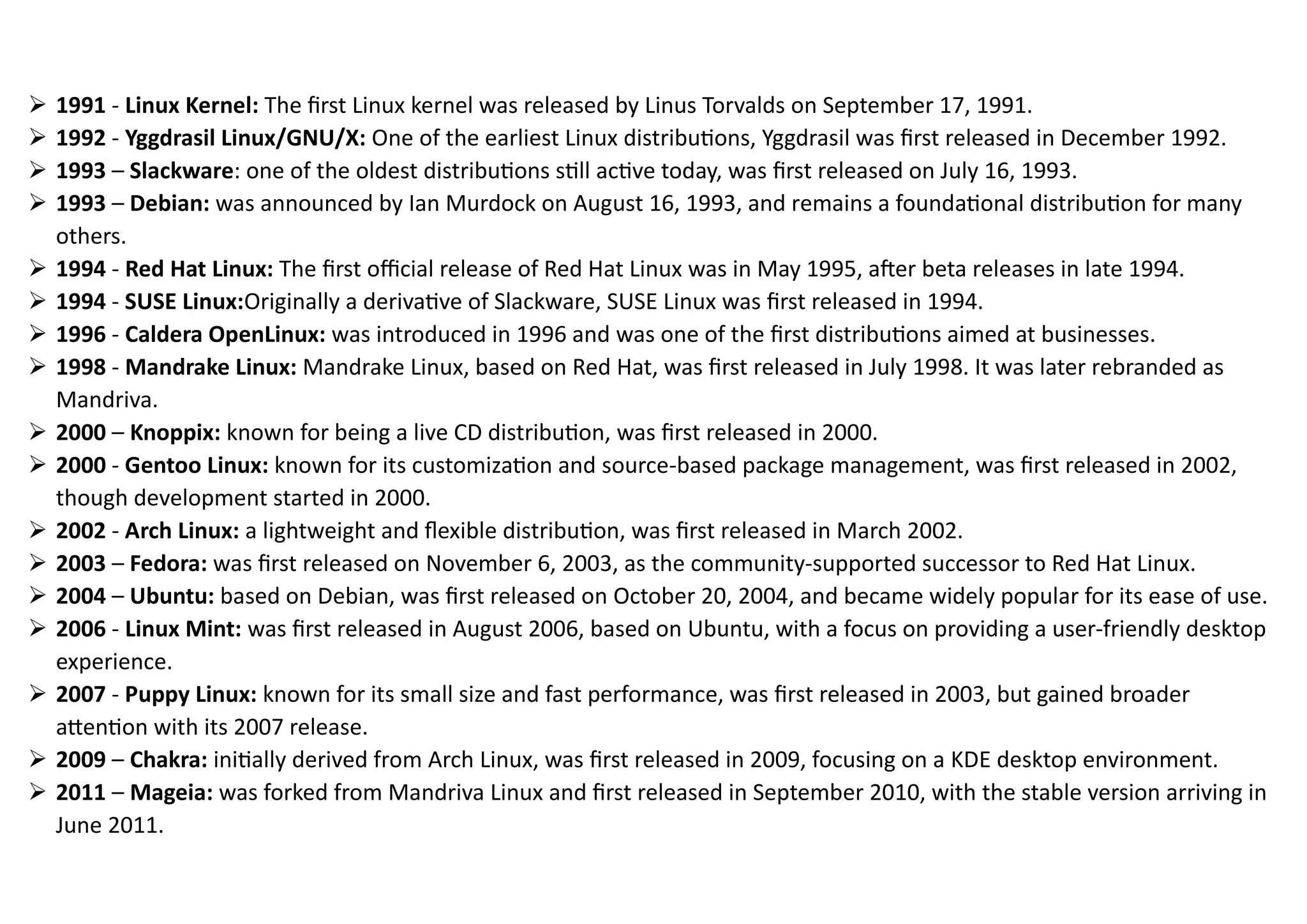
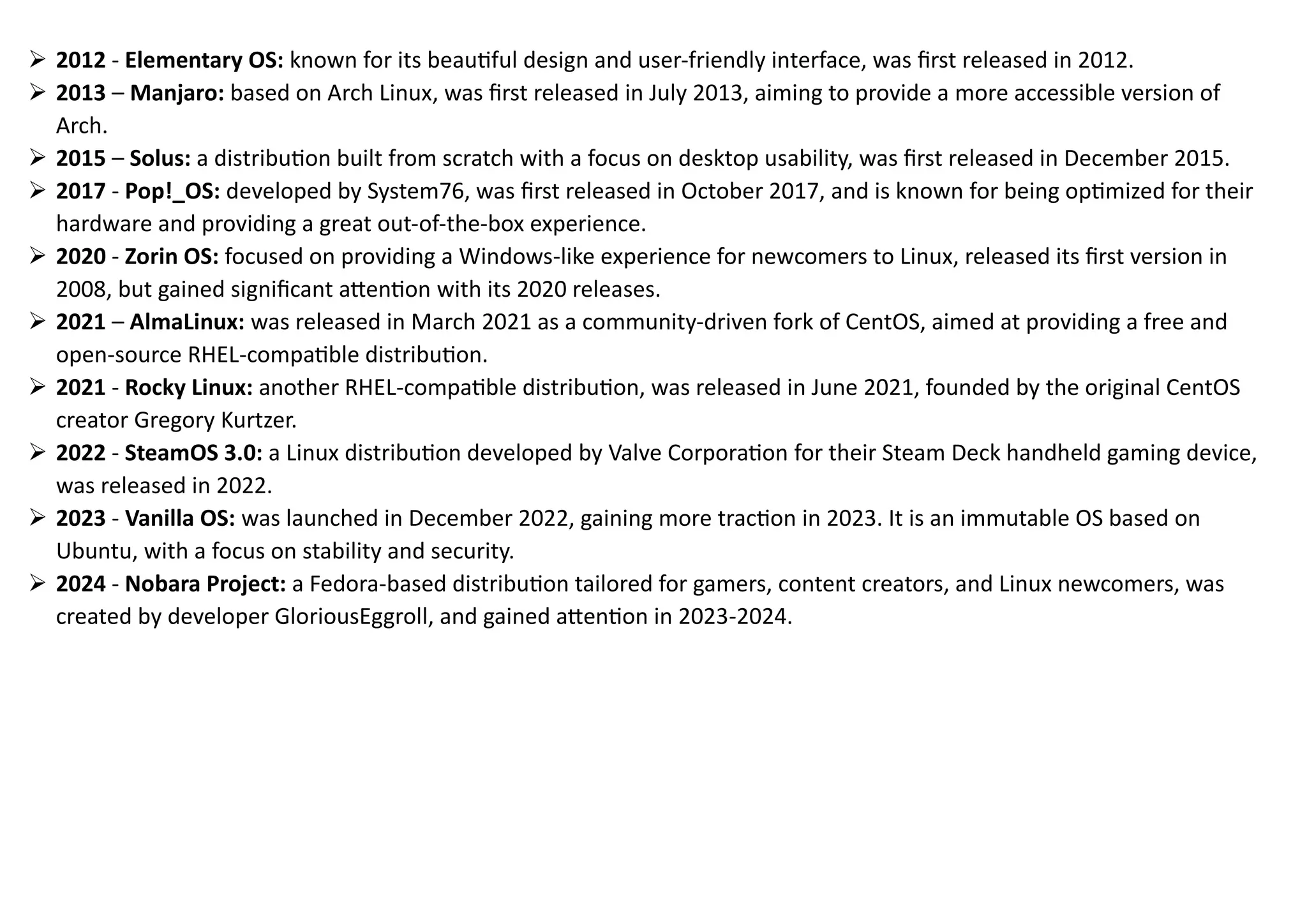
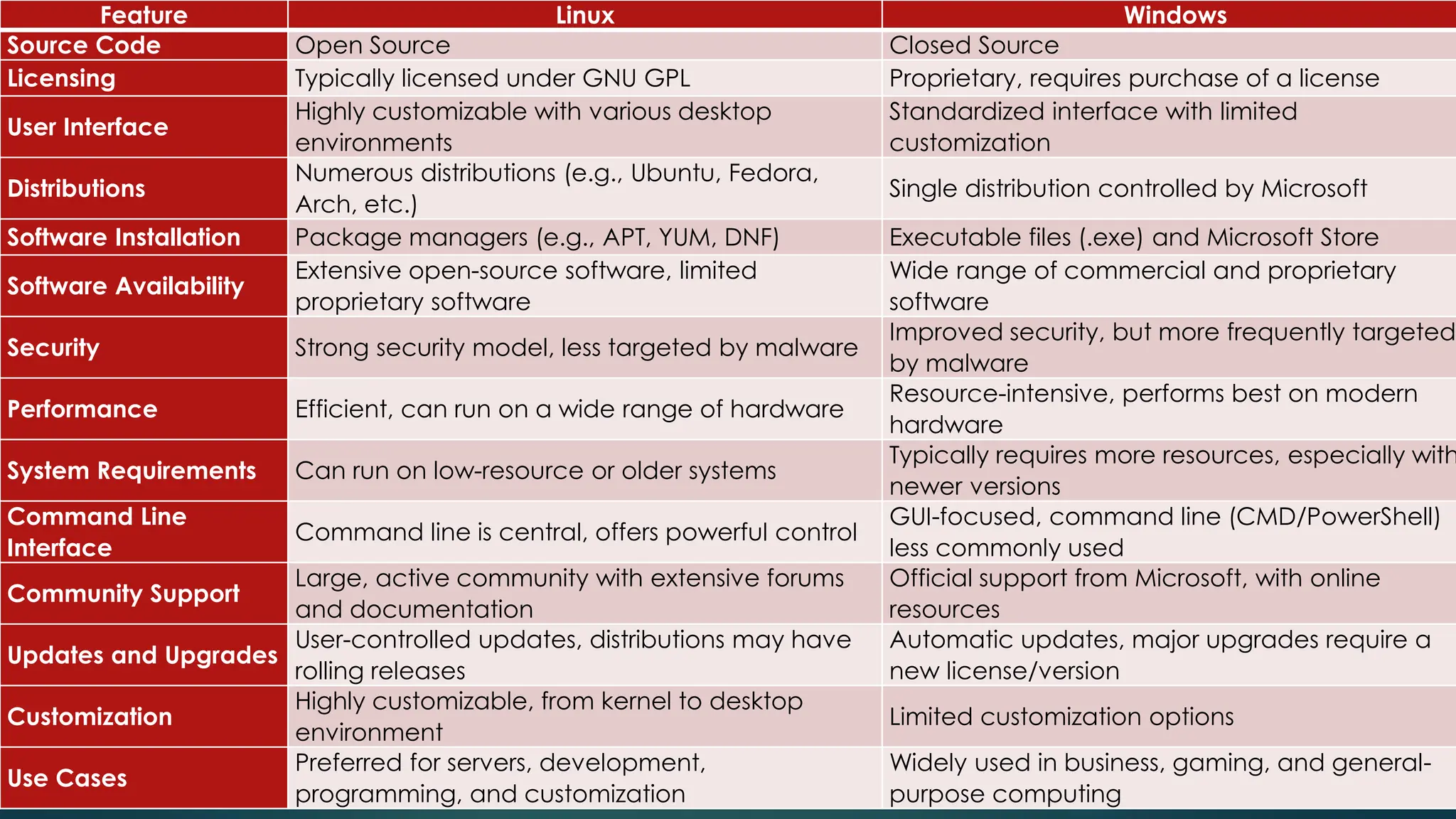
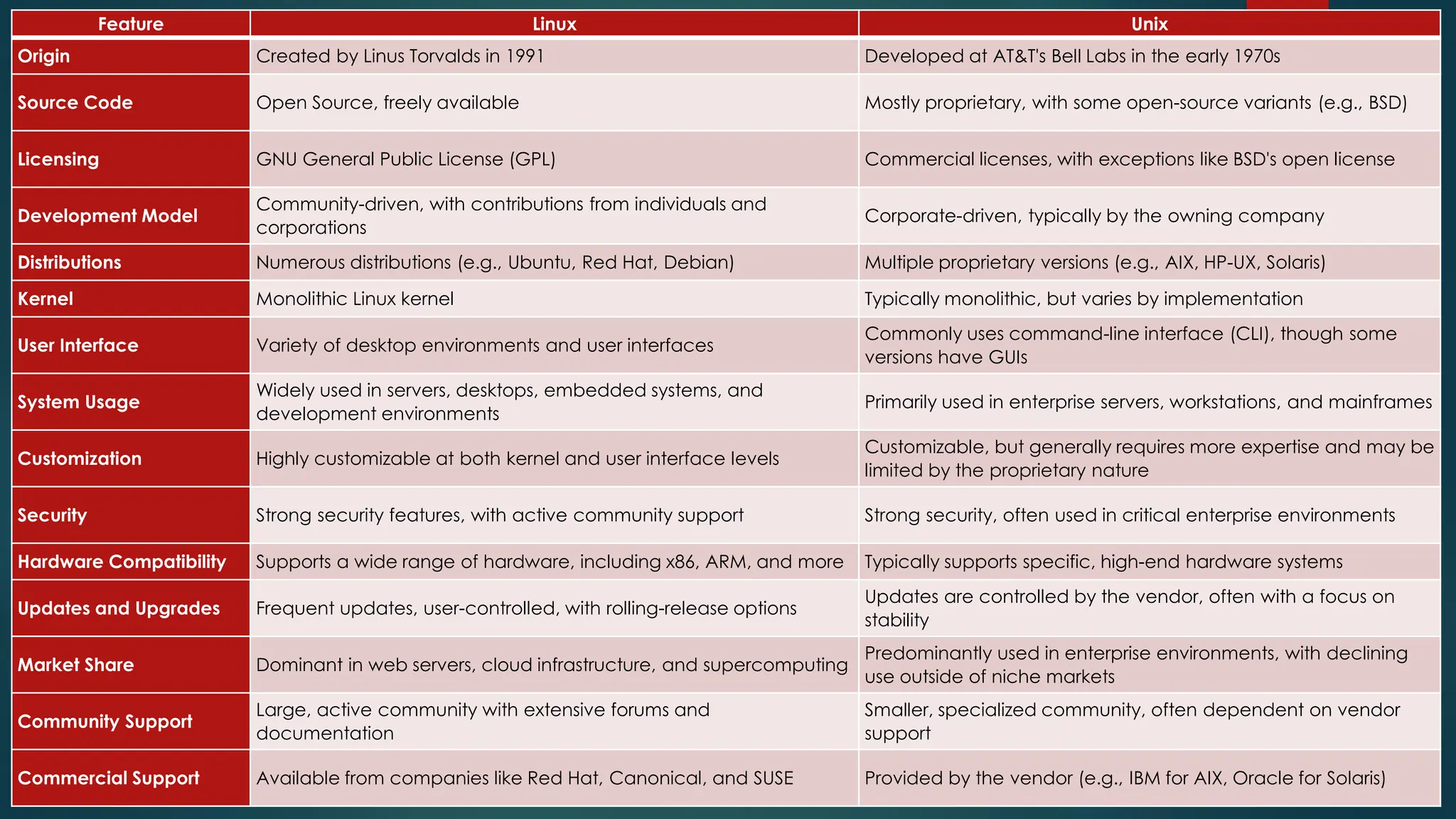
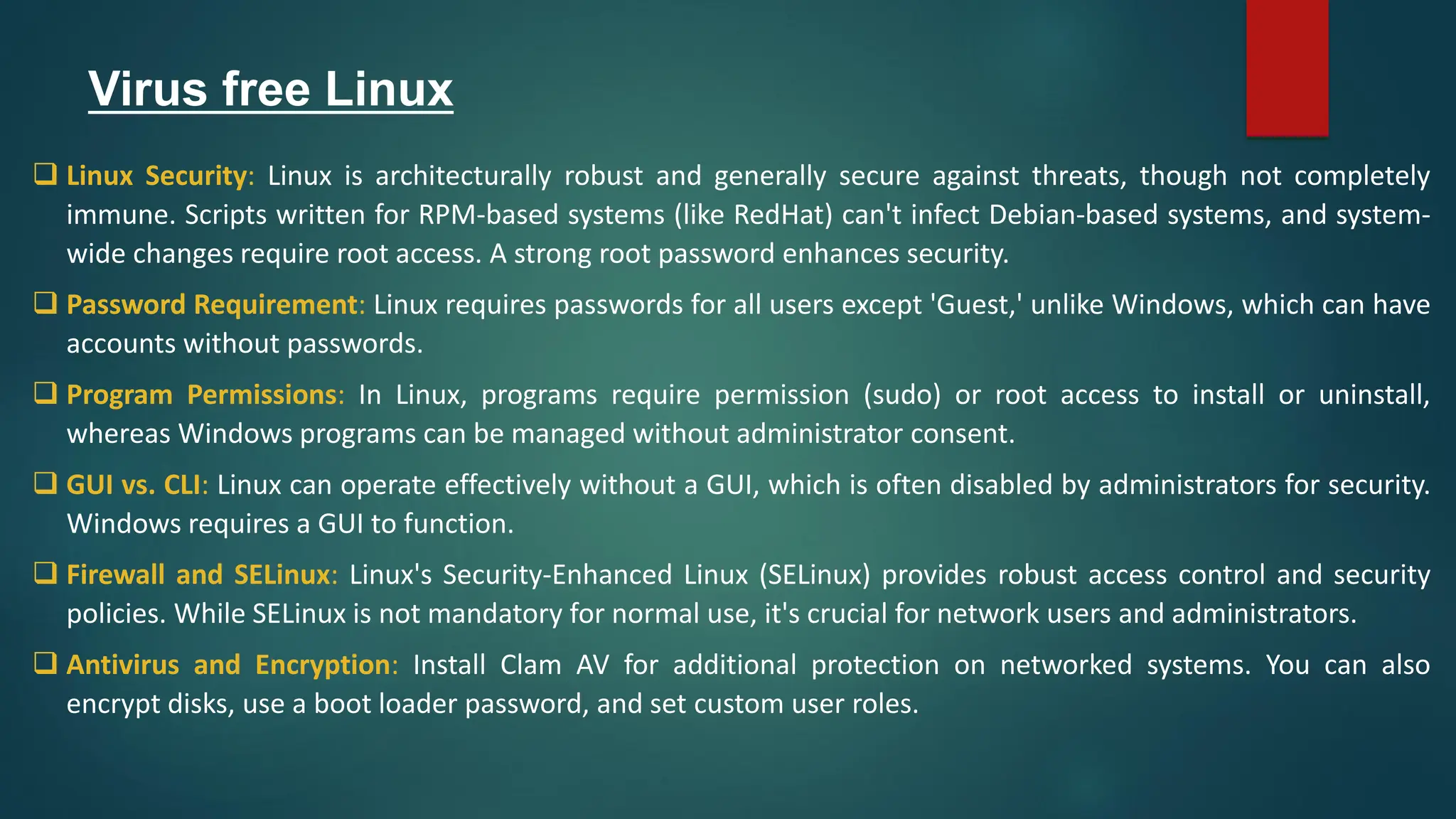
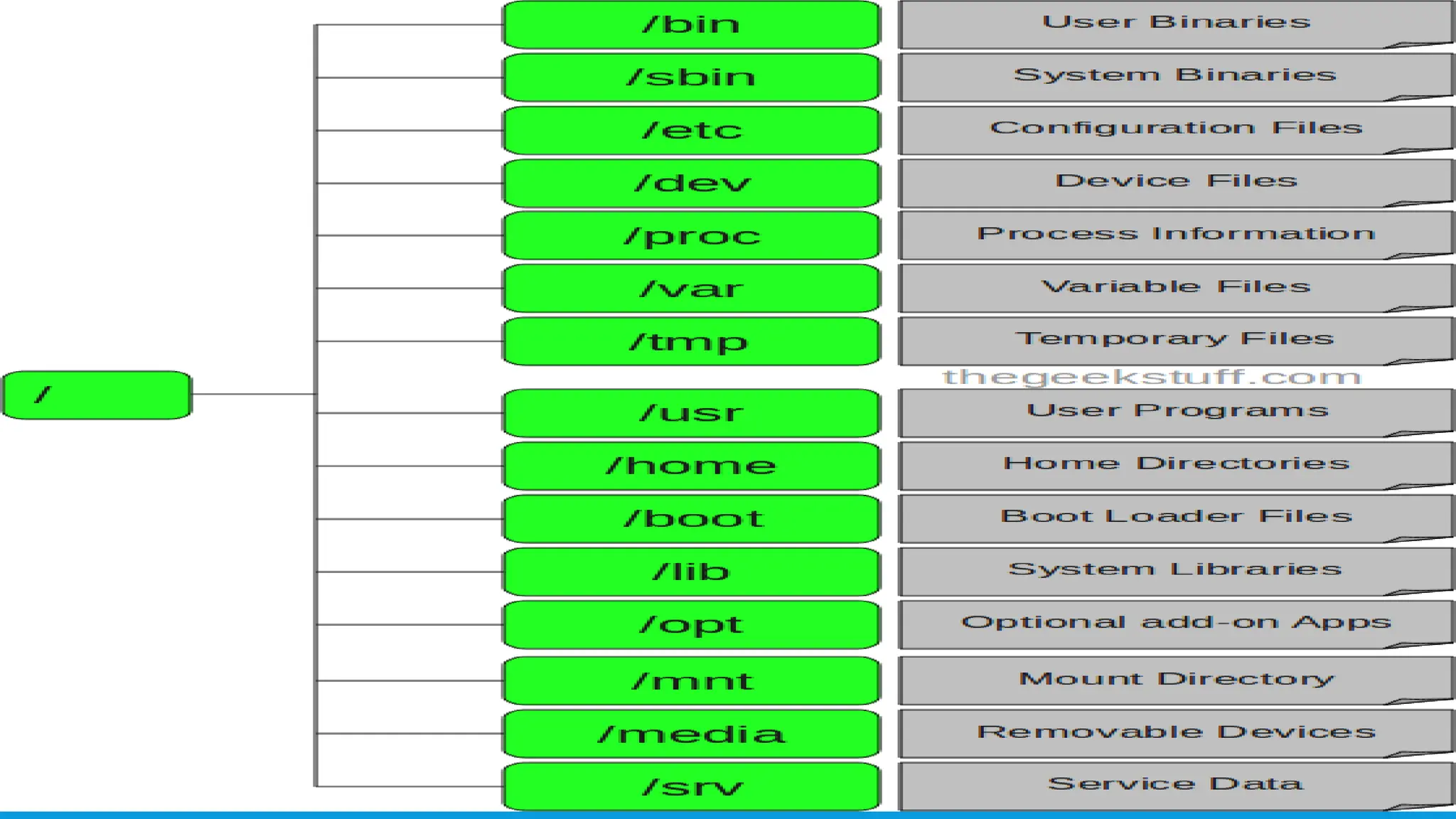
The document outlines the history and development of various Linux distributions from 1991 to 2024, highlighting key releases and features of each distribution. It also compares Linux to Windows and Unix regarding source code, licensing, user interface, and system usage, while discussing pros and cons of Linux. Additionally, the document details the Linux directory structure and its significant features, emphasizing Linux's open-source nature, security, and extensive community support.




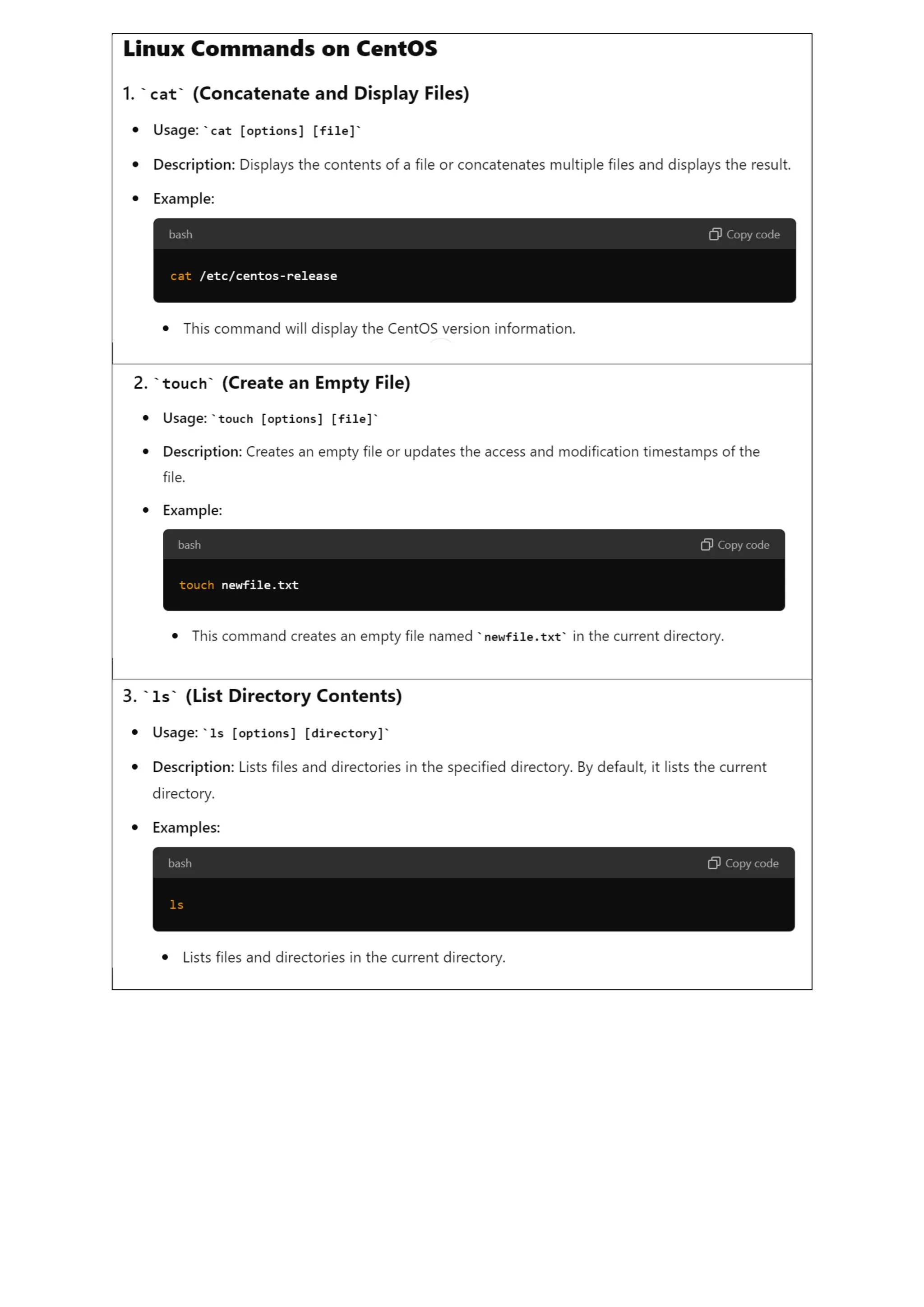
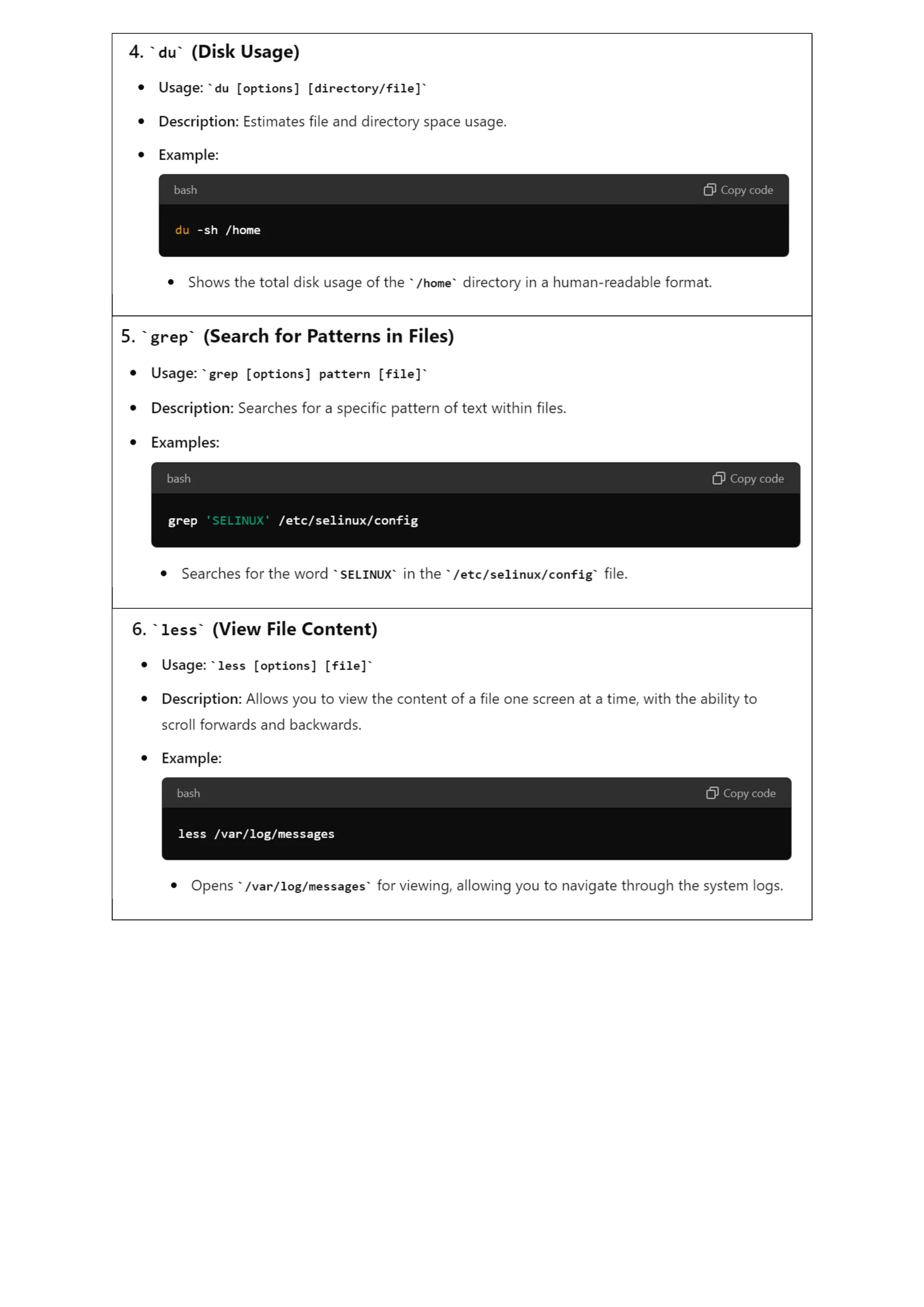

![File and Directory Management
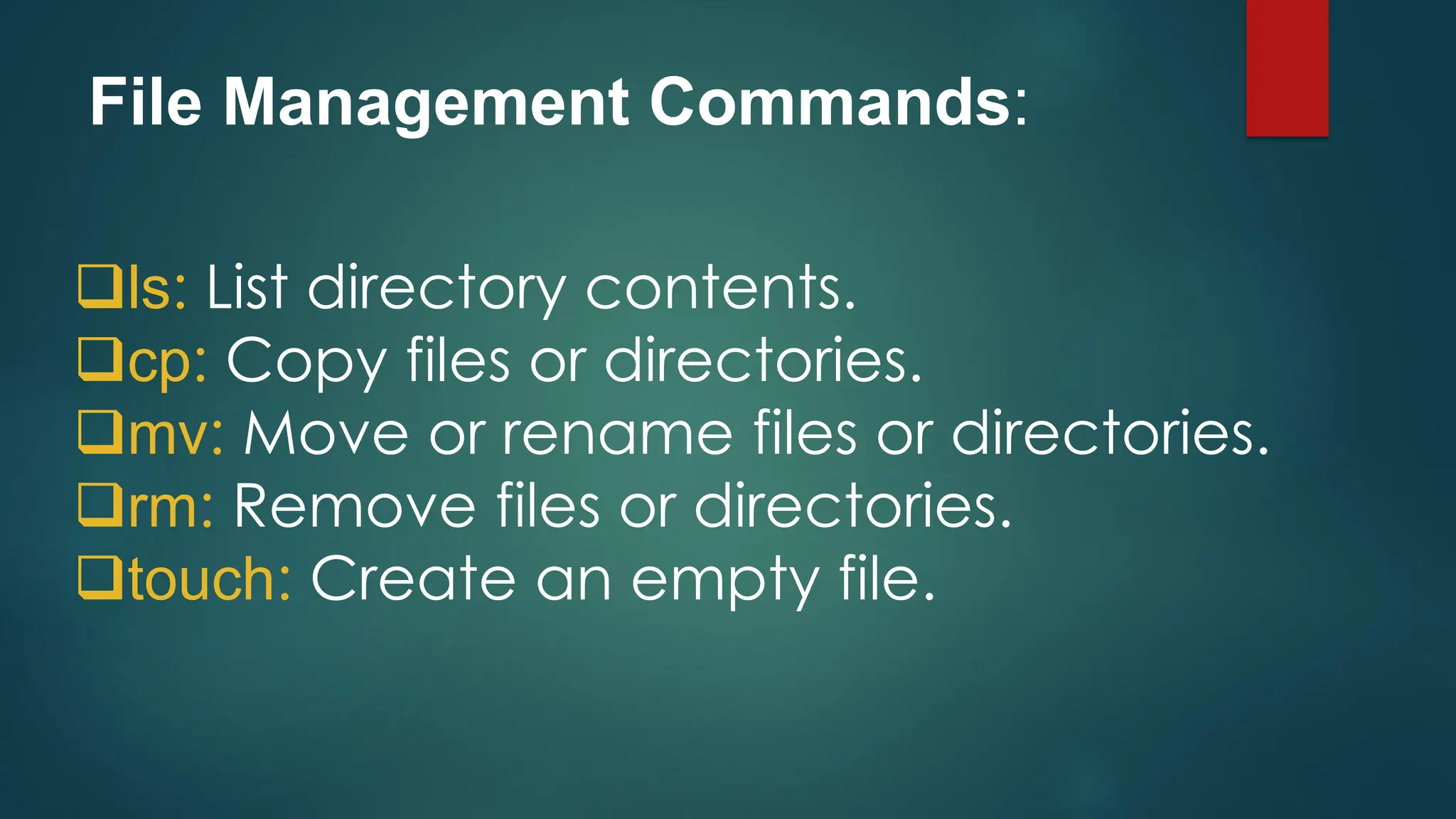
• ls: Lists files and directories in the current directory.
• cd [directory]: Changes the current directory to the specified directory.
• pwd: Displays the current working directory.
• mkdir [directory]: Creates a new directory.
• rmdir [directory]: Removes an empty directory.
• rm [file]: Removes a file.
• rm -r [directory]: Removes a directory and its contents recursively.
• cp [source] [destination]: Copies files or directories from the source to the destination.
• mv [source] [destination]: Moves or renames files or directories.
• touch [file]: Creates an empty file or updates the timestamp of an existing file.](https://image.slidesharecdn.com/lfsallinone-241007183446-3171c039/75/LFS-all-in-one123456789012334455678-pdf-40-2048.jpg)