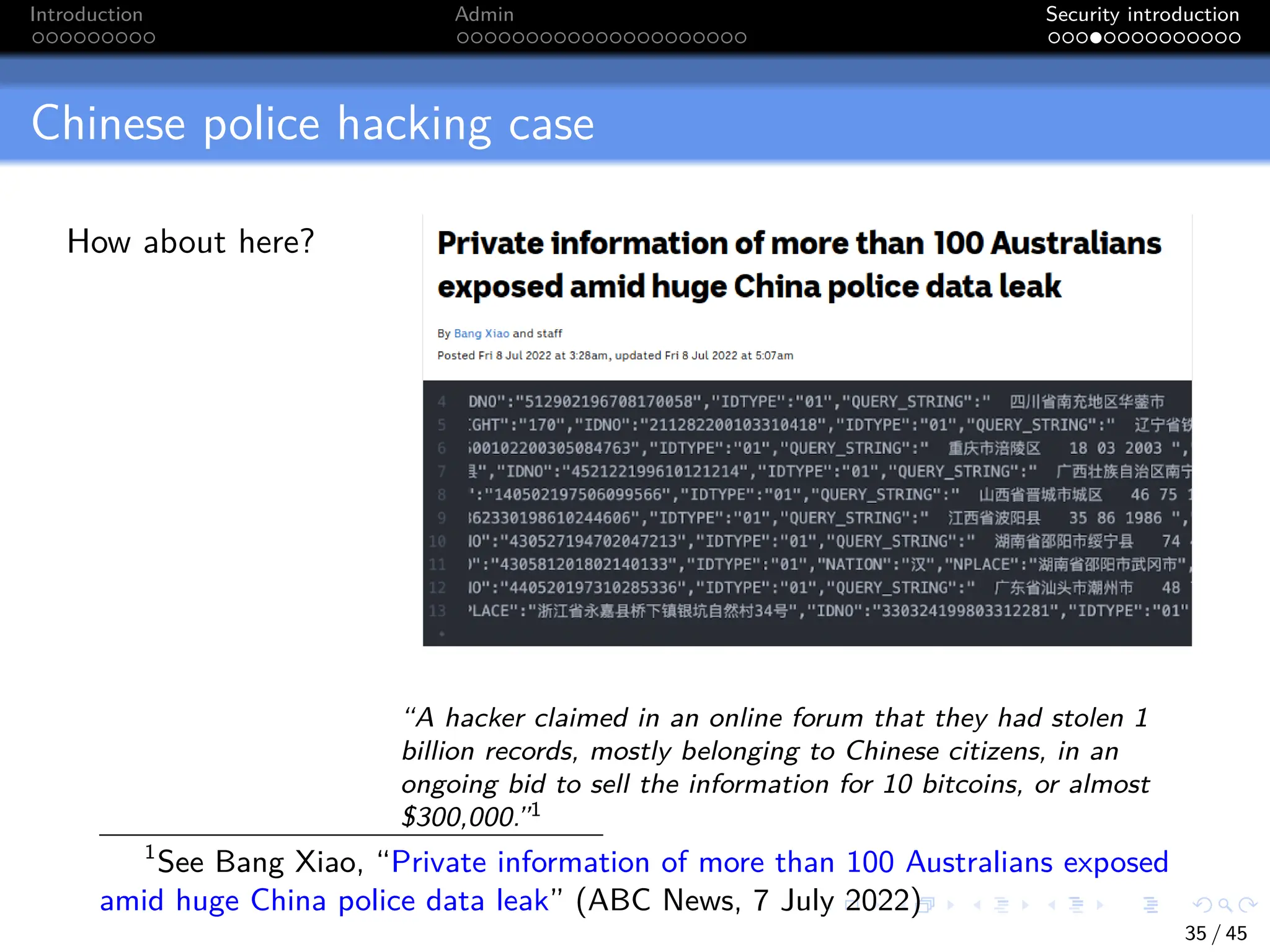
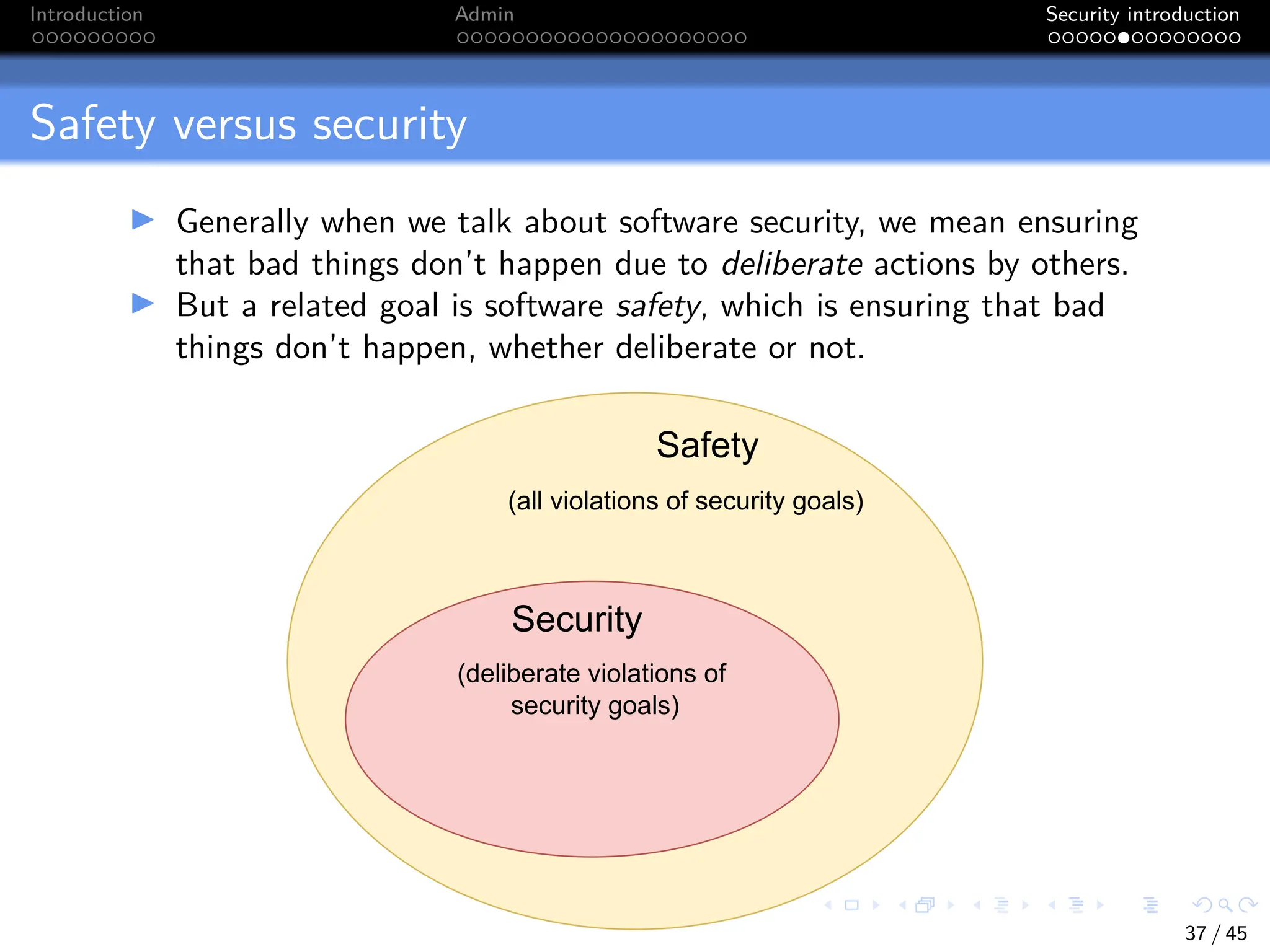
This document provides an introduction to the CITS3007 Secure Coding unit. It outlines the unit goals, content, assessment, and prerequisites. It also introduces key concepts in software security including the goals of confidentiality, integrity and availability. Examples are given of how each of these goals could be compromised. The distinction between security and safety is discussed, and an example email is analyzed to determine its authenticity.










![Introduction Admin Security introduction
Purdue University case
Which security goal
was compromised
here?
“During his senior year, Sun missed all of his classes but
one. However, with the help of [an accomplice’s] scheme, he
was still able to receive straight A’s.”1
1
See Treye Green, “Who Is Roy Sun? Purdue Graduate Sentenced To Jail For
Changing Grades To Straight A’s” (International Business Times, 2014)
34 / 45](https://image.slidesharecdn.com/lect01-intro-240103153616-68267332/75/lect01-intro-pdf-35-2048.jpg)