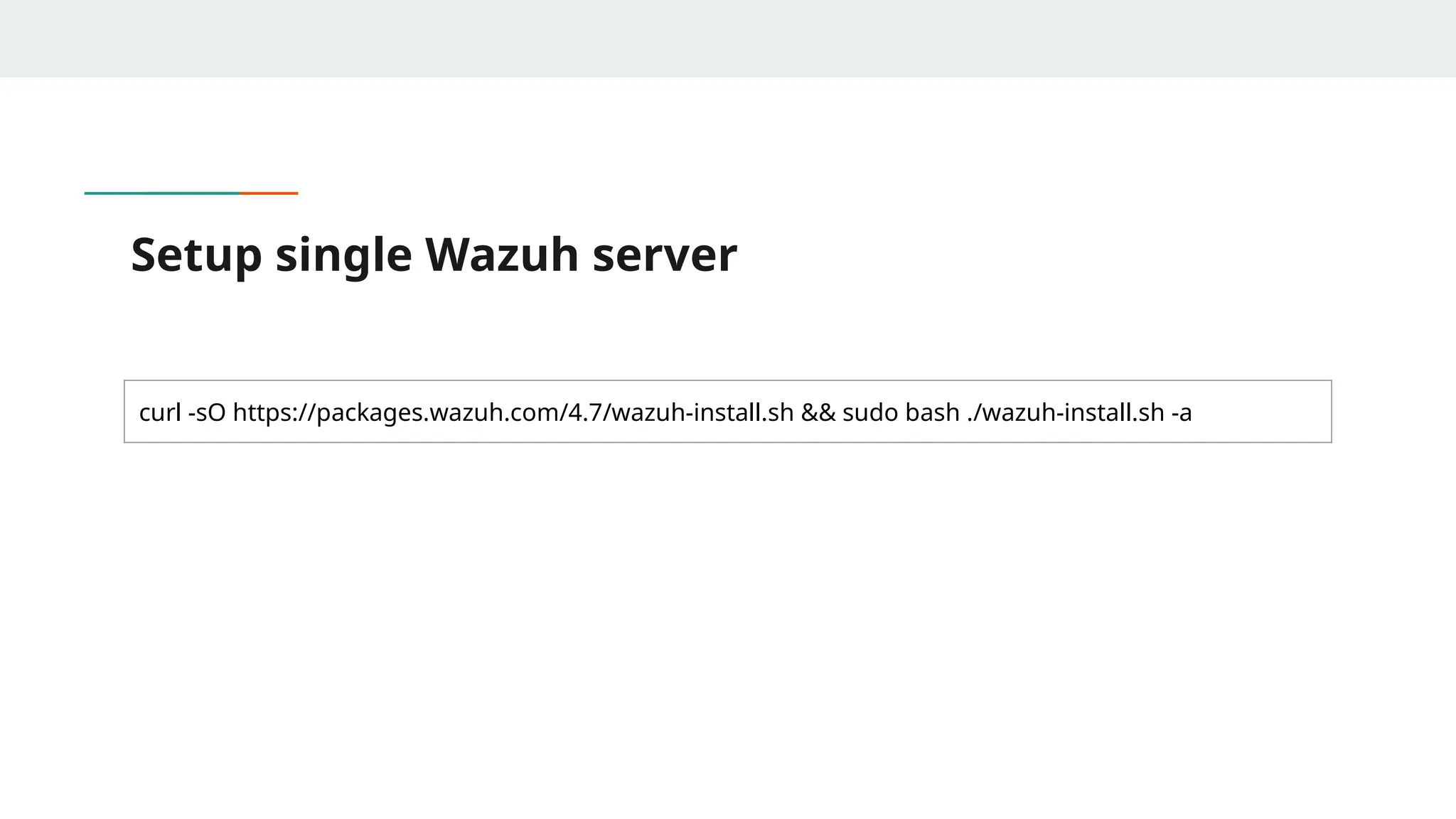
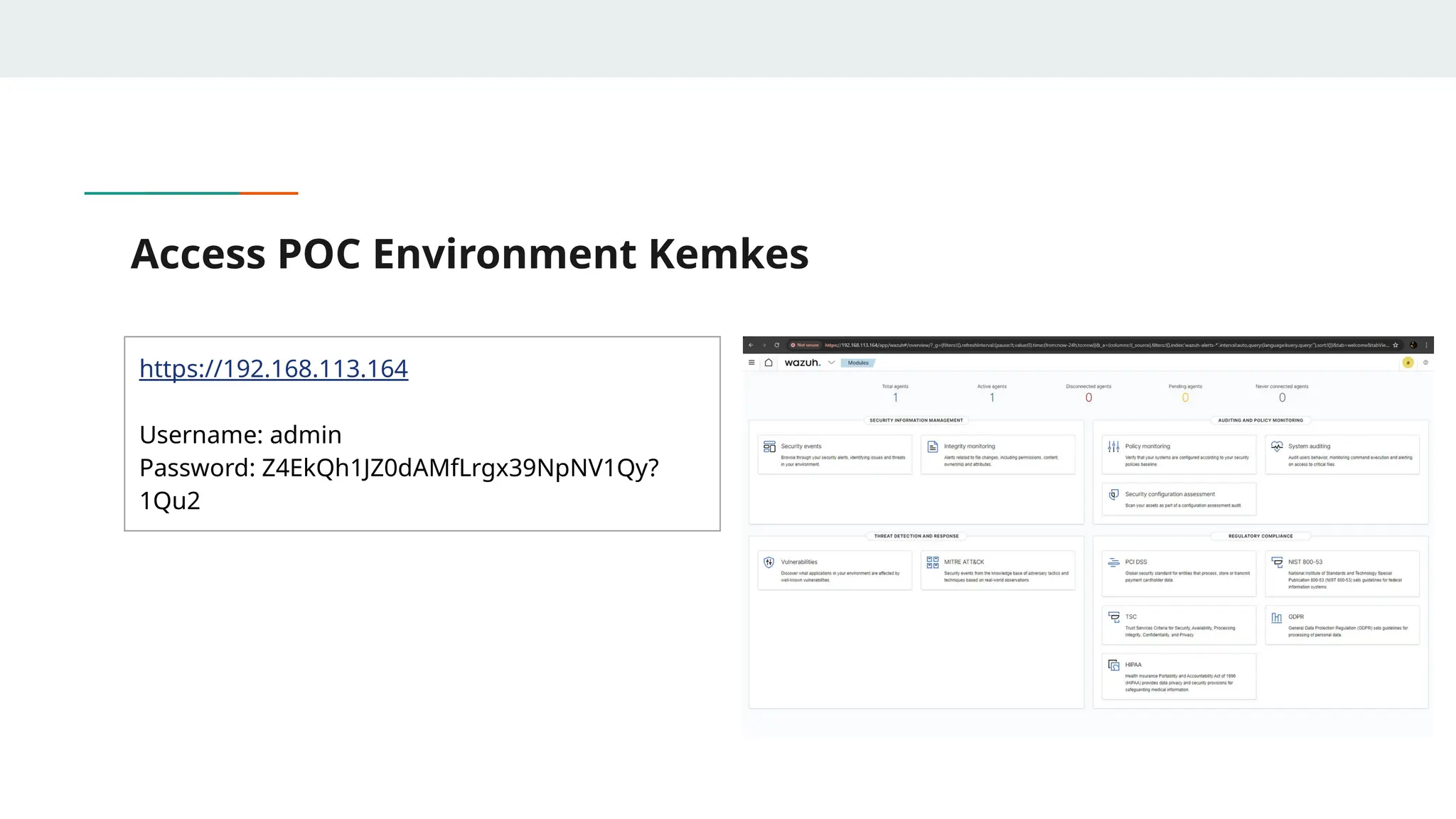
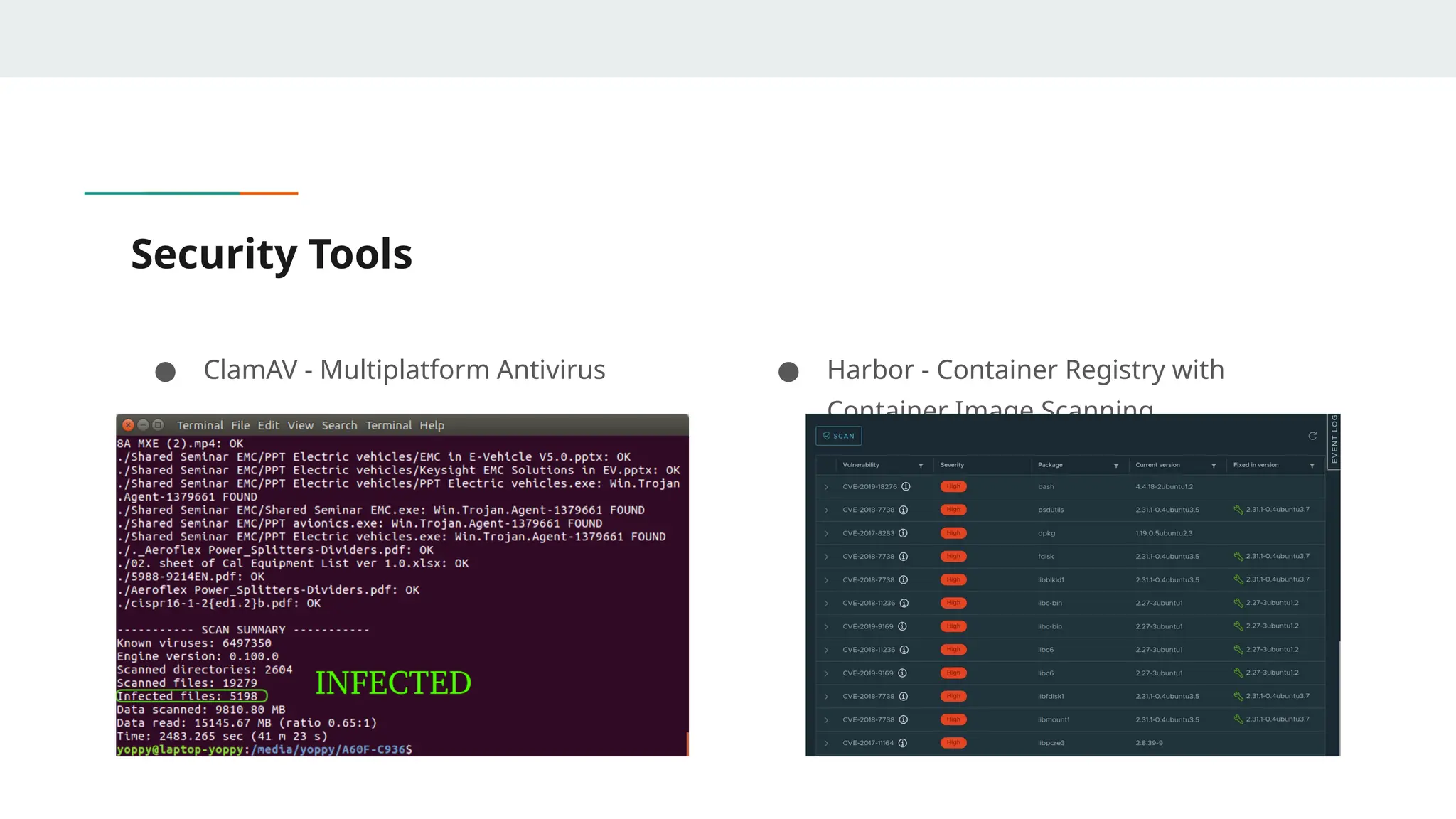
The document provides an overview of Security Information and Event Management (SIEM) and its importance in cybersecurity, outlining the roles of red teams and blue teams in managing security threats. It describes various security standards organizations can adopt and emphasizes the benefits of using SIEM tools, such as real-time threat detection and regulatory compliance. The document also introduces the Wazuh SIEM tool, detailing setup instructions and additional security tools relevant to maintaining cybersecurity.