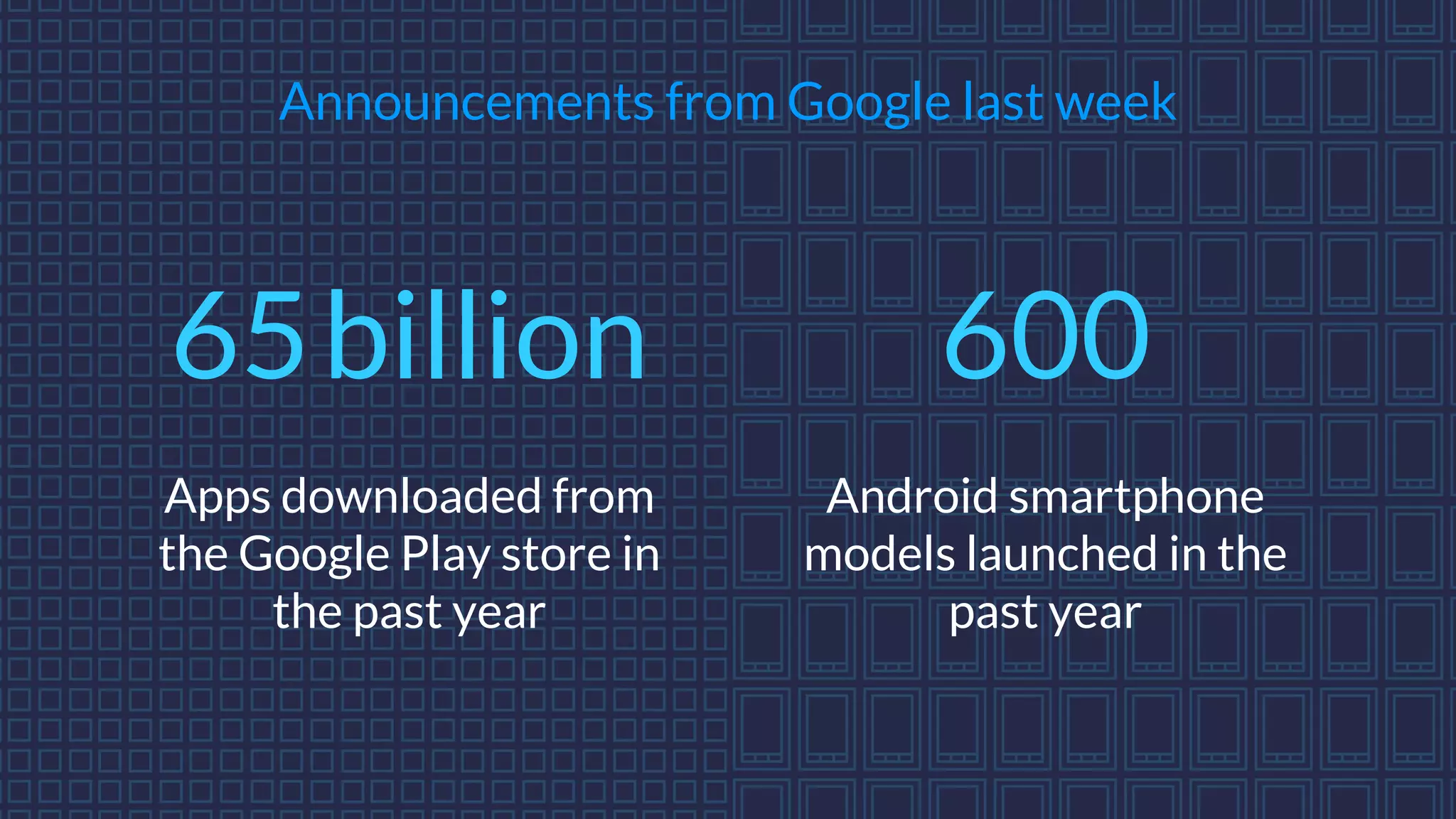
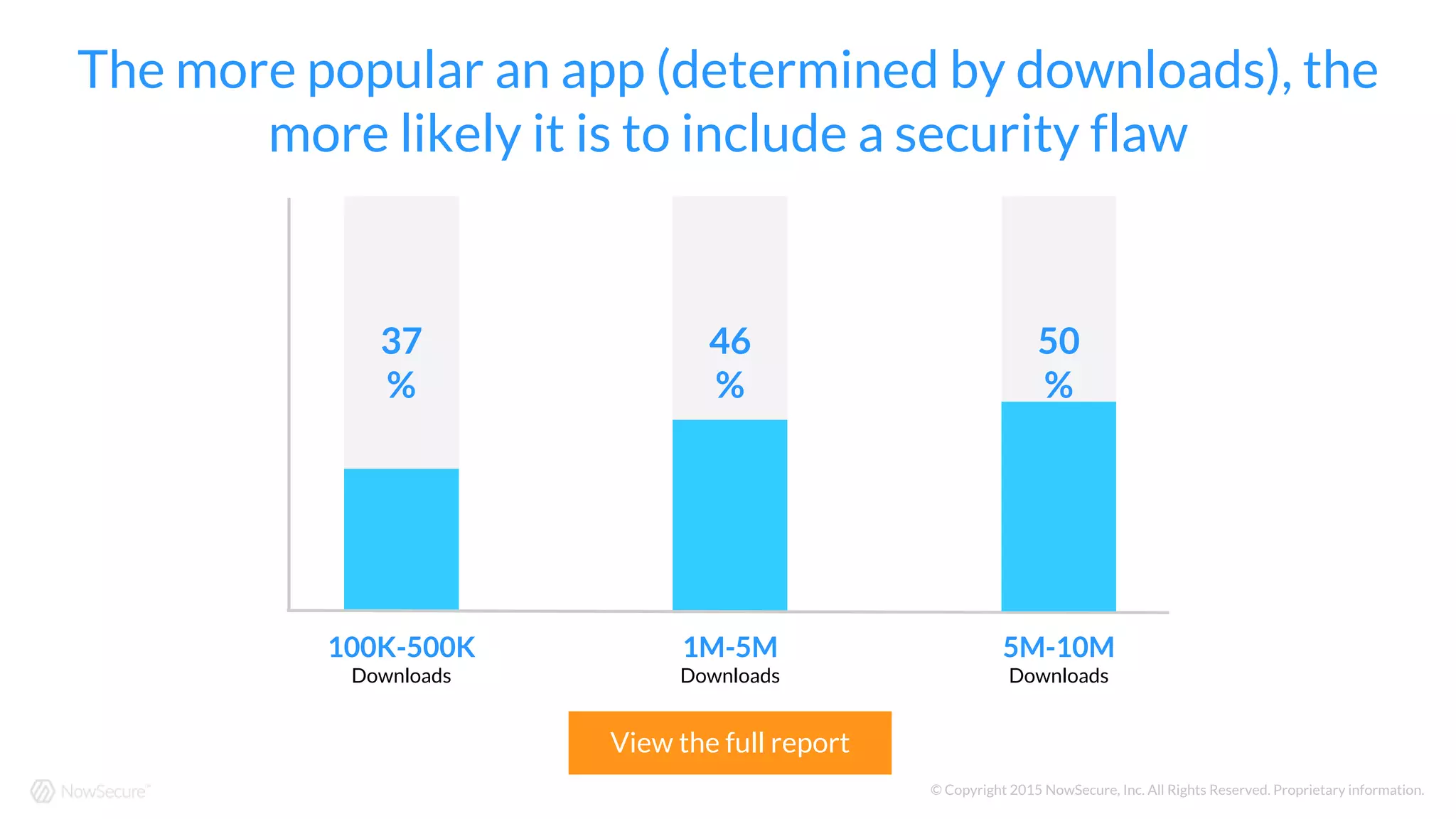
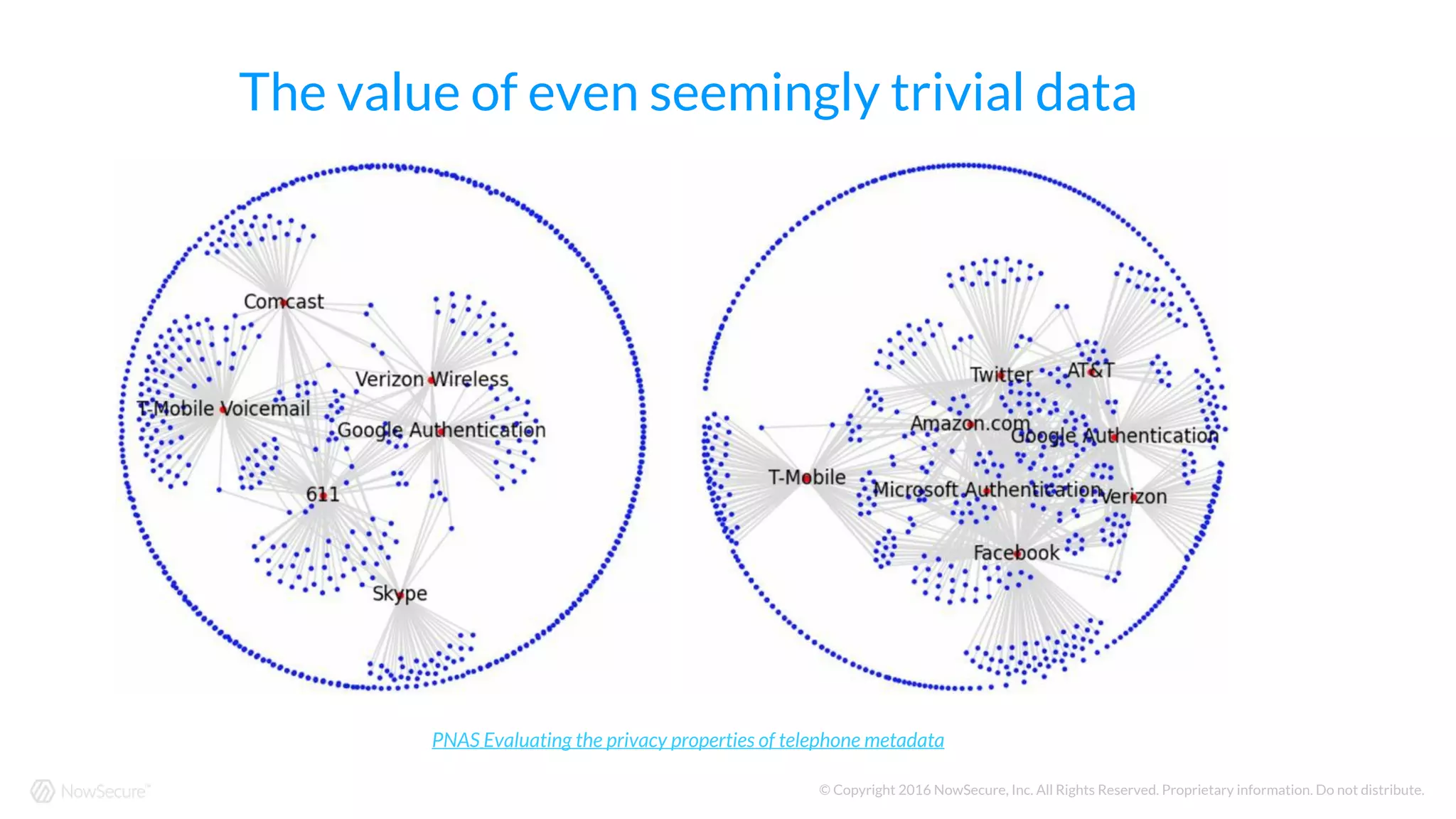
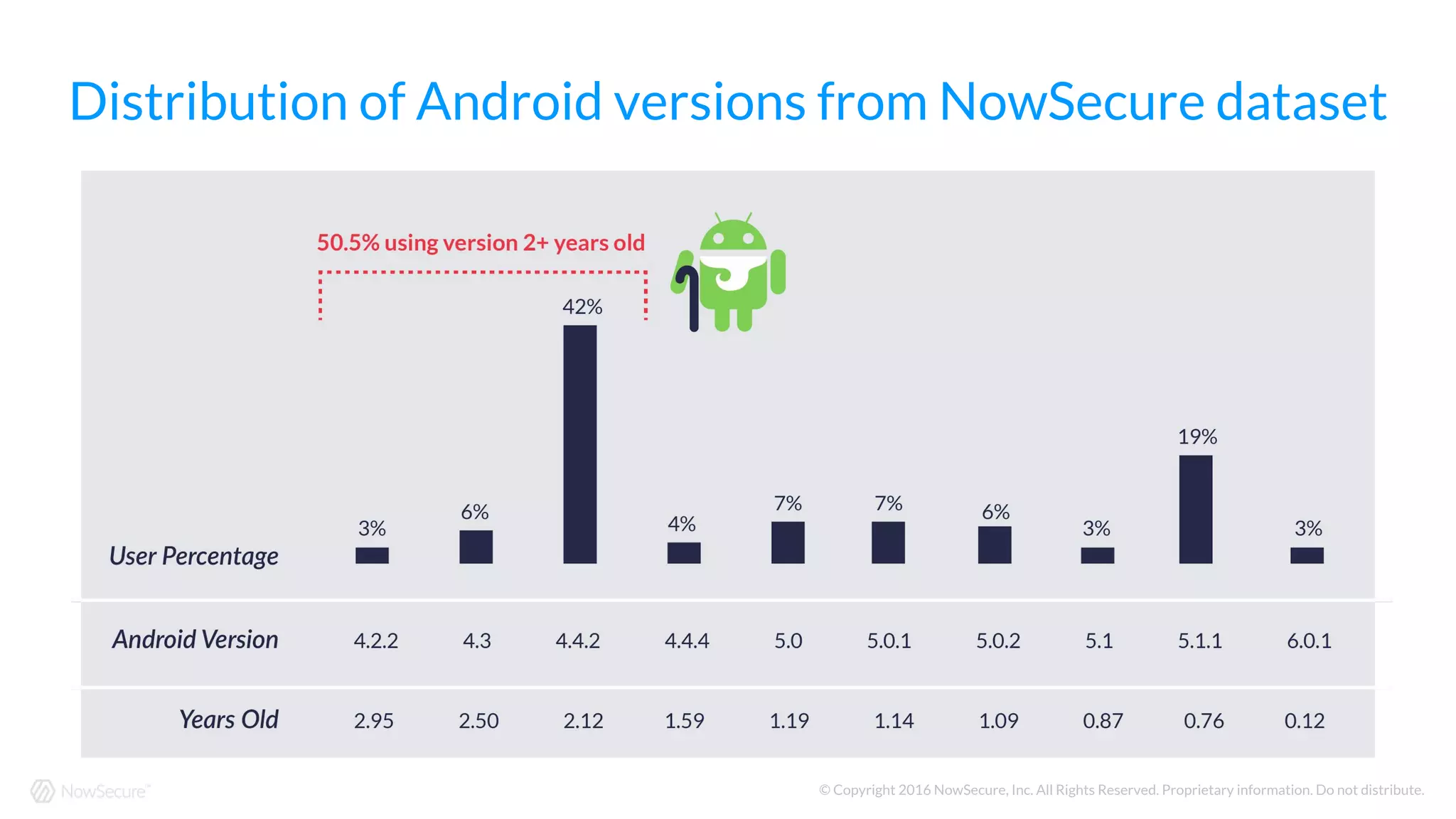
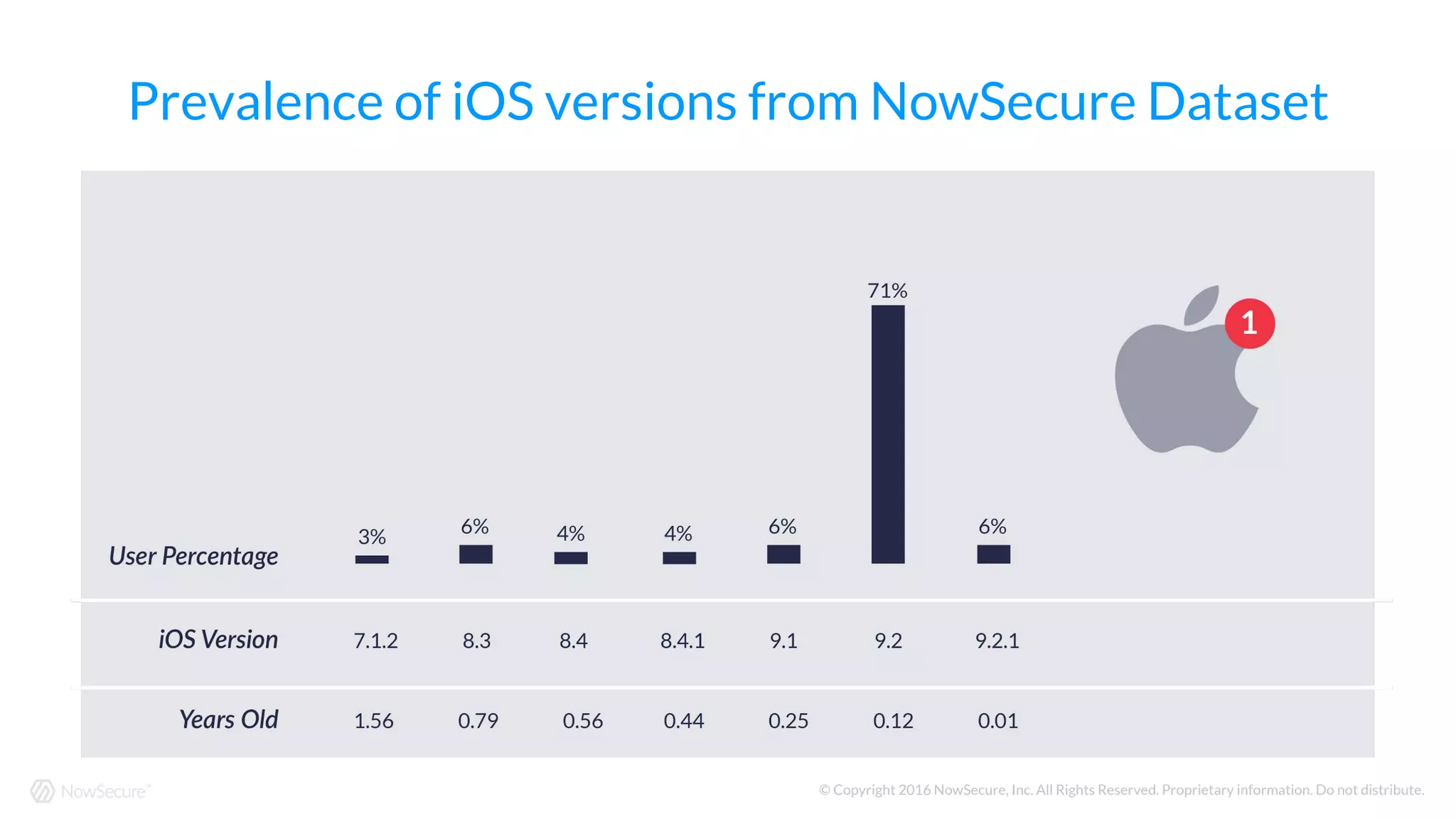
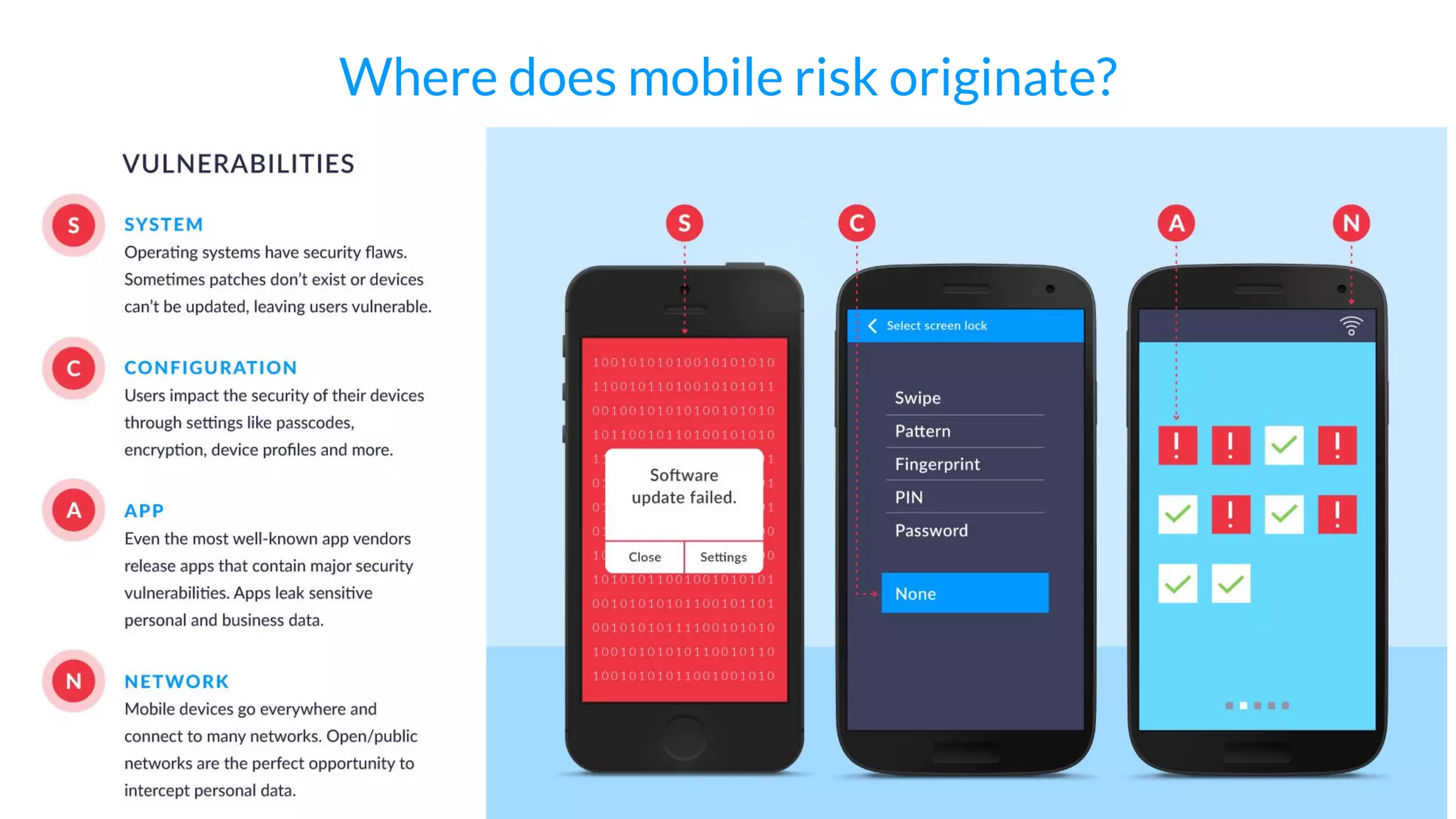
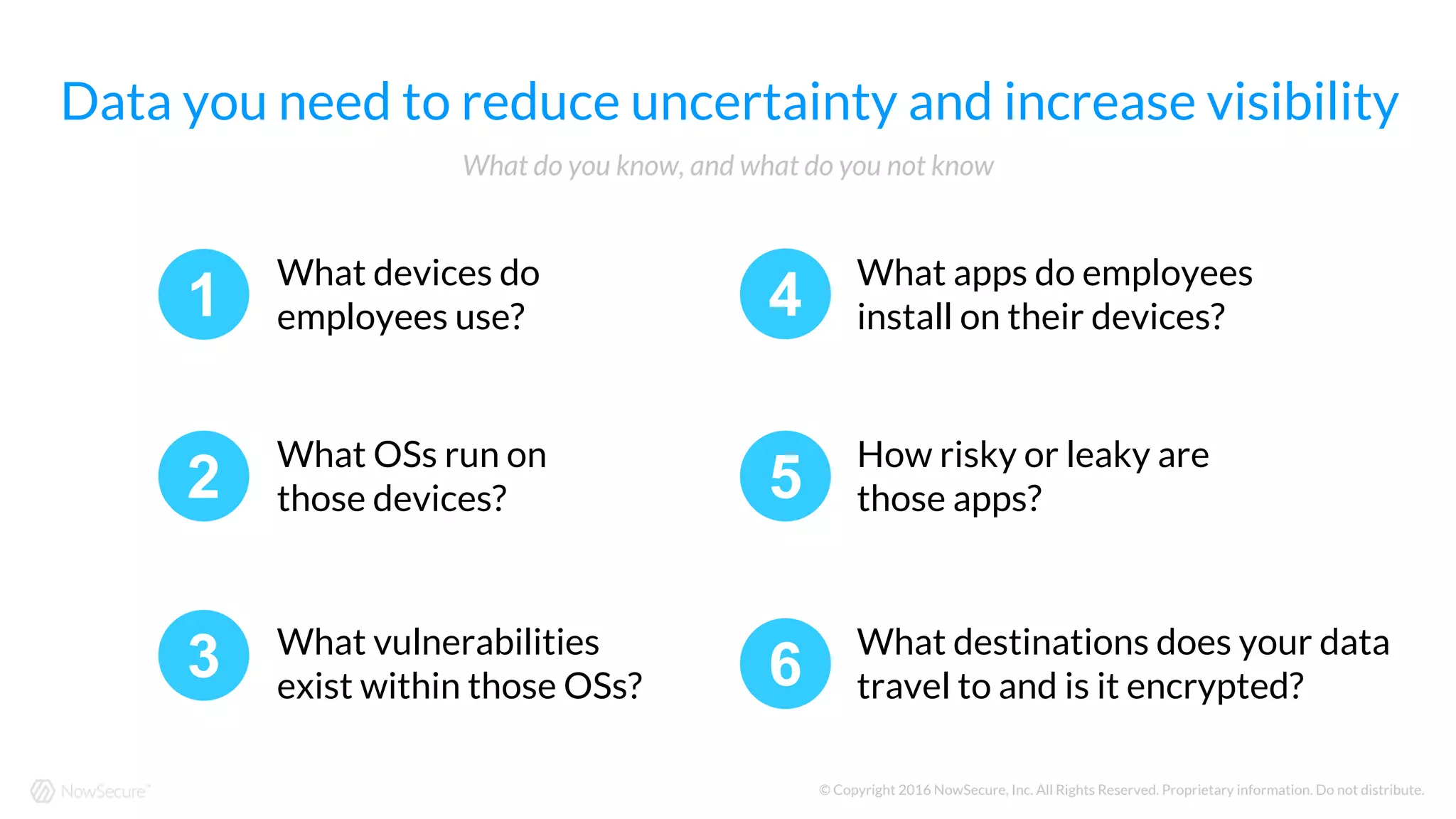
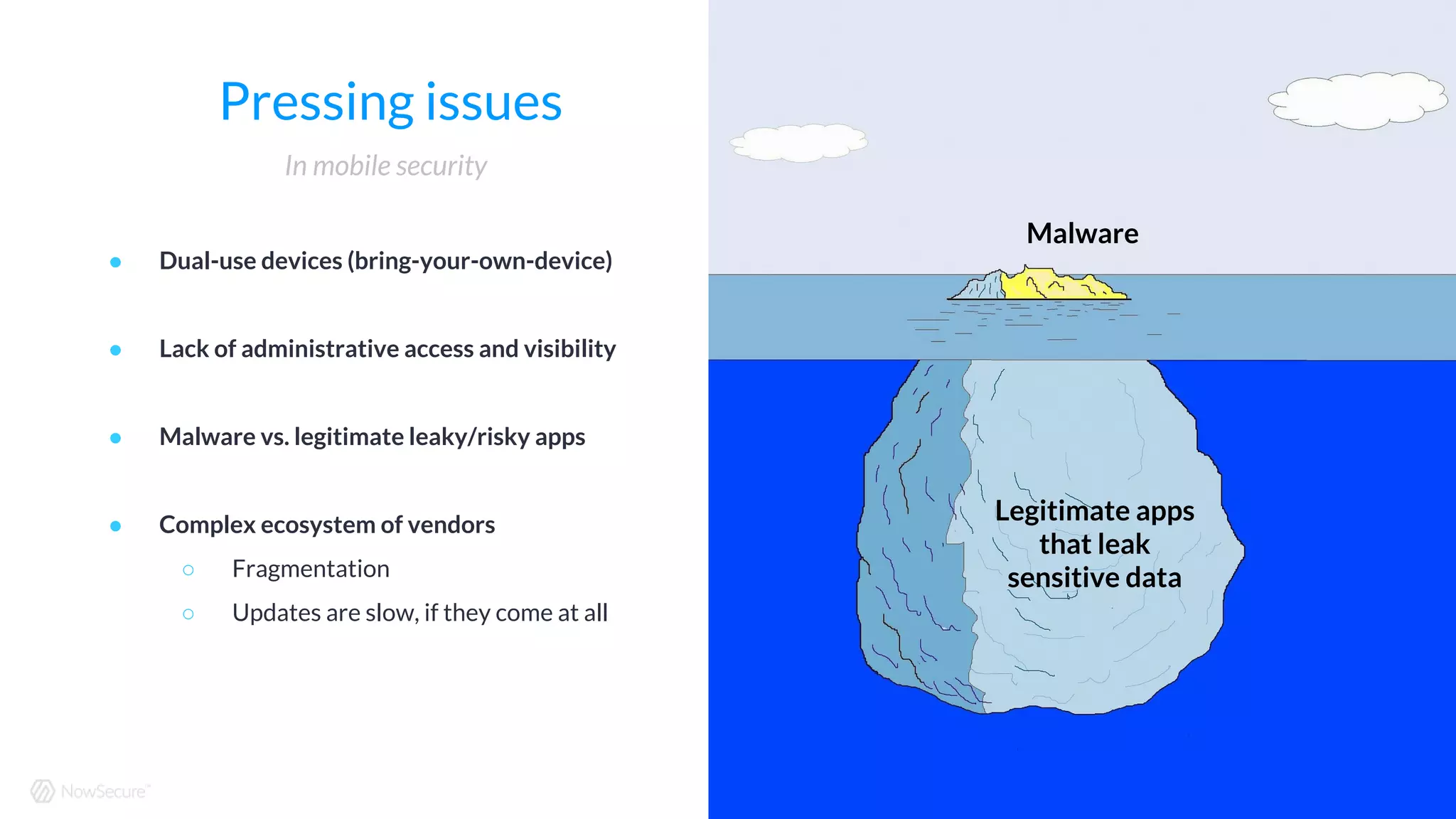
The document discusses the challenges of mobile security in 2016, highlighting issues such as the inadequacy of traditional security defenses, the risks posed by dual-use devices, and the prevalence of leaky apps. It emphasizes the fragmented nature of the mobile ecosystem, where multiple vendors contribute to security without accountability. The document suggests necessary actions, including vetting apps and ensuring installations are on secure endpoints, to mitigate mobile security risks.





![Cybersecurity and Cyberwar: What Everyone Needs to Know
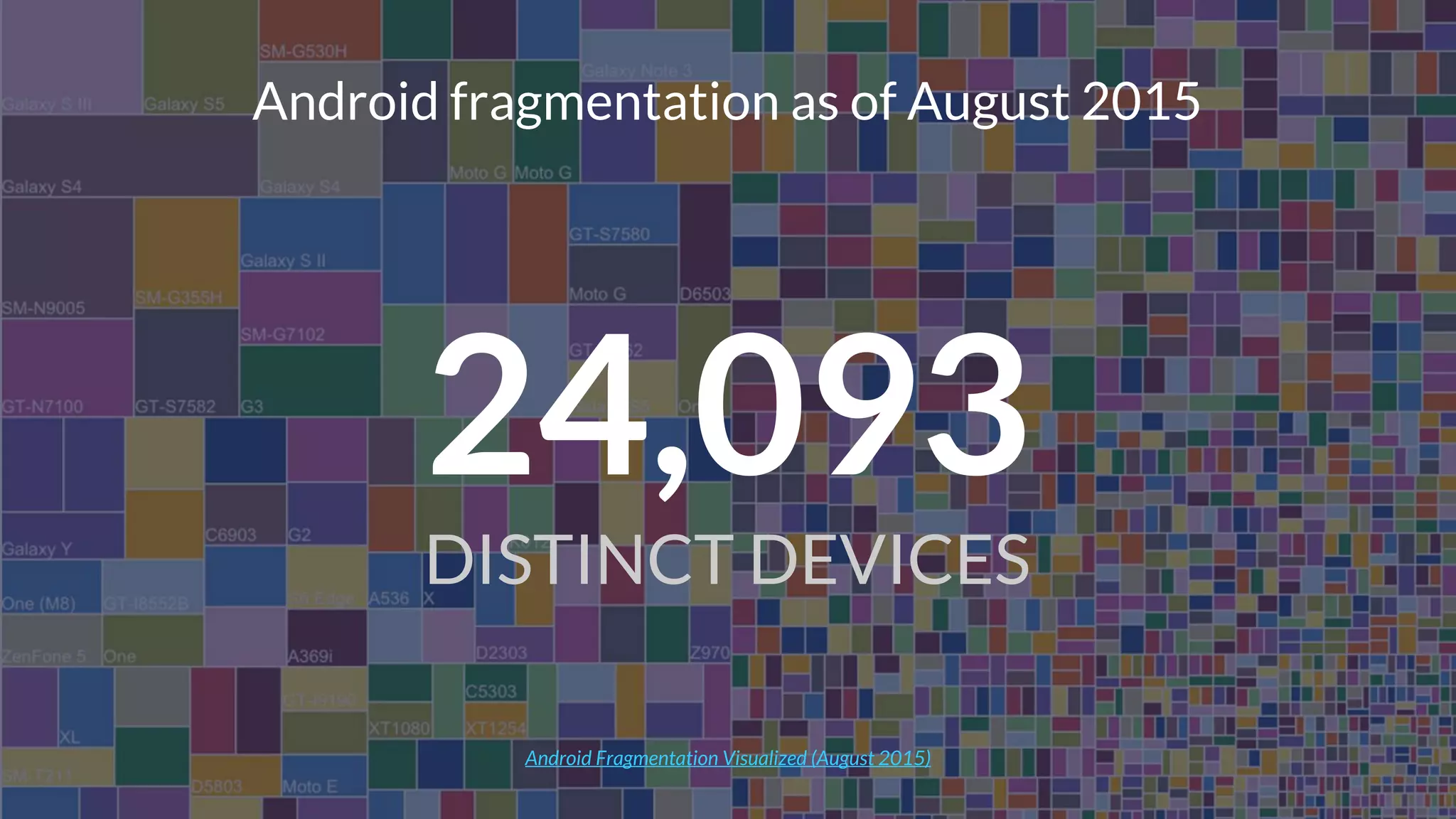
[The] market is fragmented, with multiple makers…
each with a role in security but often lacking any
sense of responsibility for it.
“
”](https://image.slidesharecdn.com/slideshareitsnotaboutyou-mobilesecurityin2016-160527155018/75/It-s-not-about-you-Mobile-security-in-2016-9-2048.jpg)