1. Cyber crimes in India have increased significantly, with a 200% rise in Delhi and various online fraud cases reported.
2. The Information Technology Act, 2000 aims to provide legal recognition for electronic transactions and digital signatures to facilitate electronic governance and commerce.
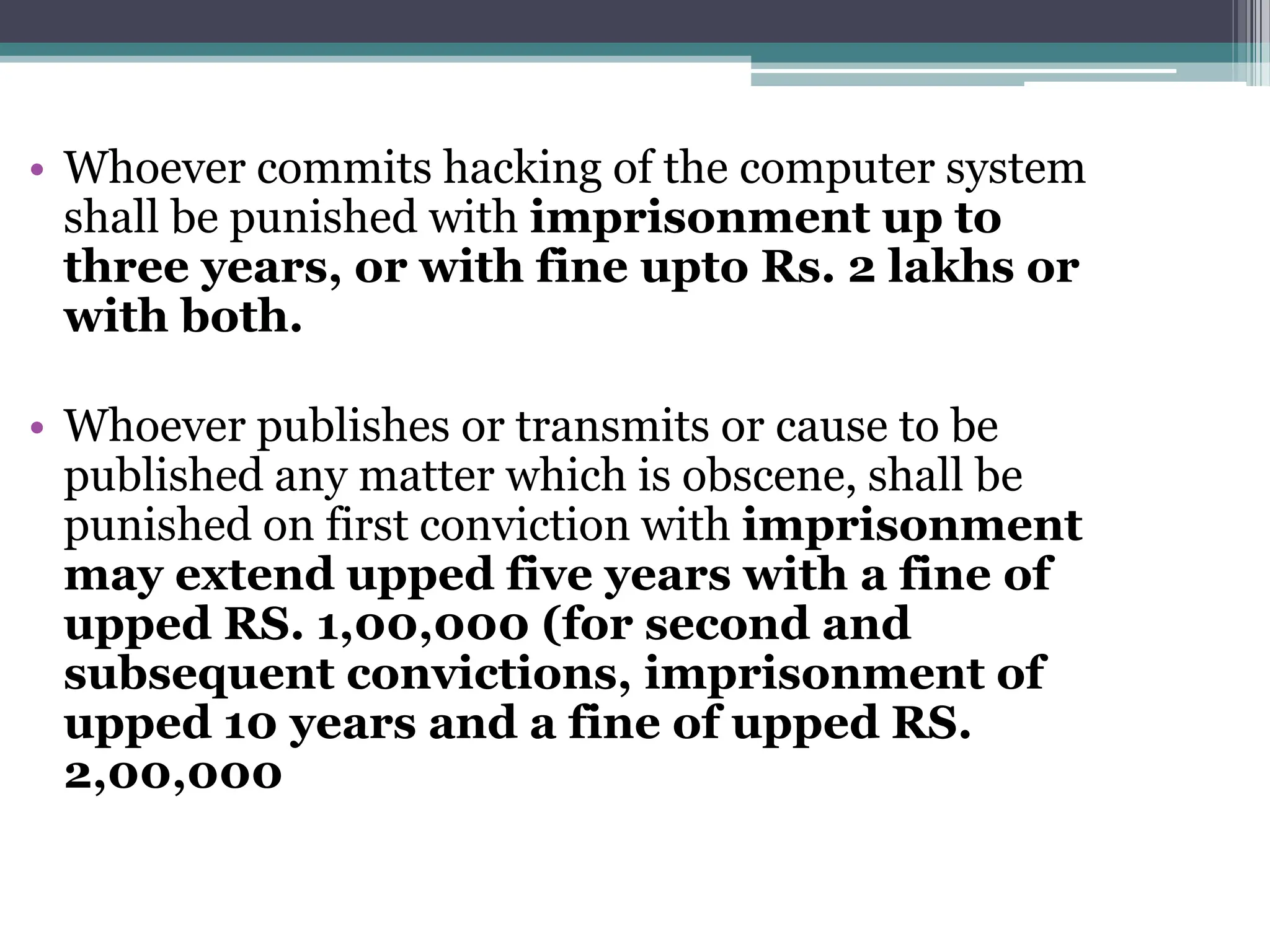
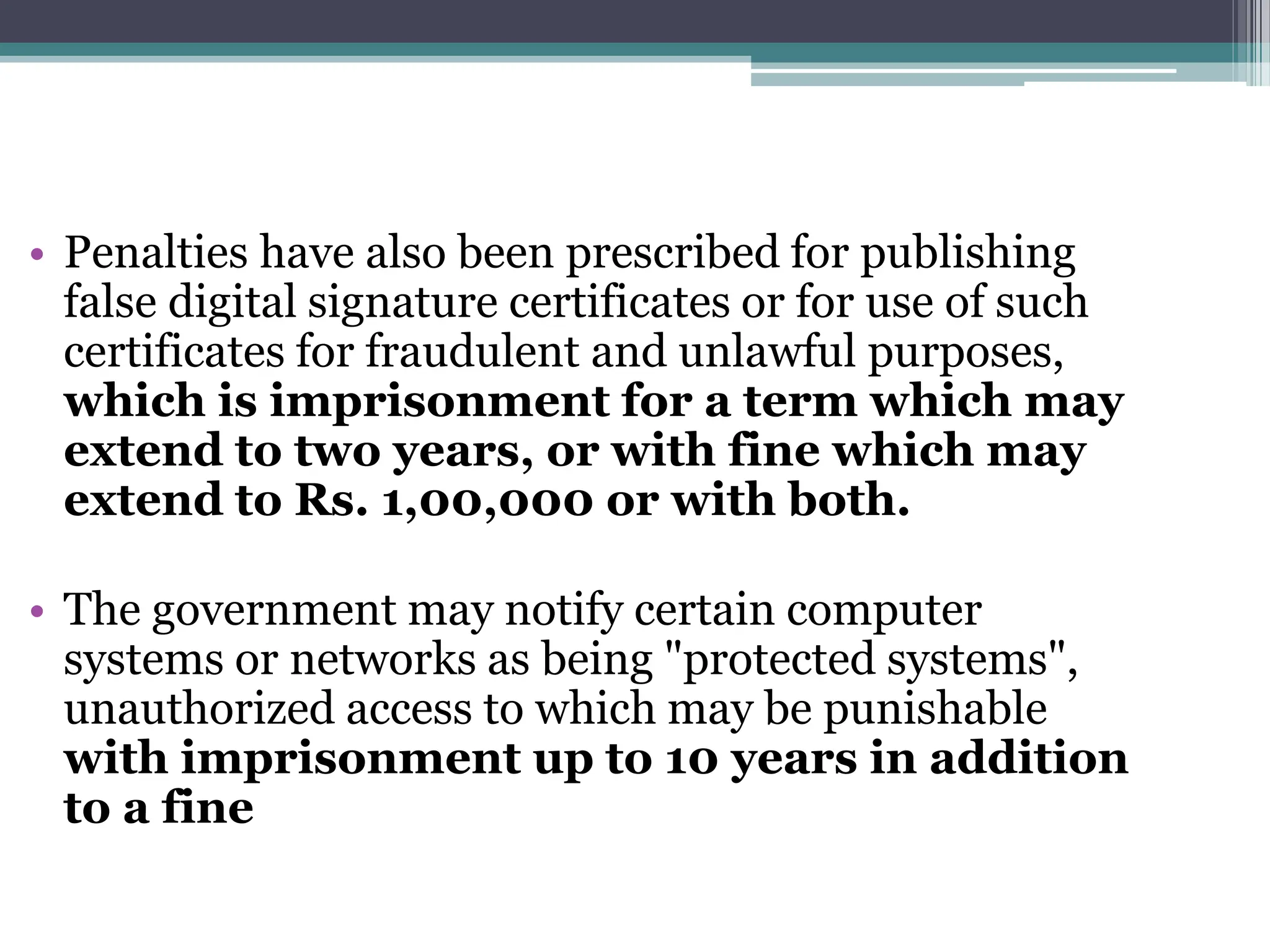
3. The Act defines cyber crimes such as hacking and publishing obscene content online, and prescribes penalties such as imprisonment and fines.