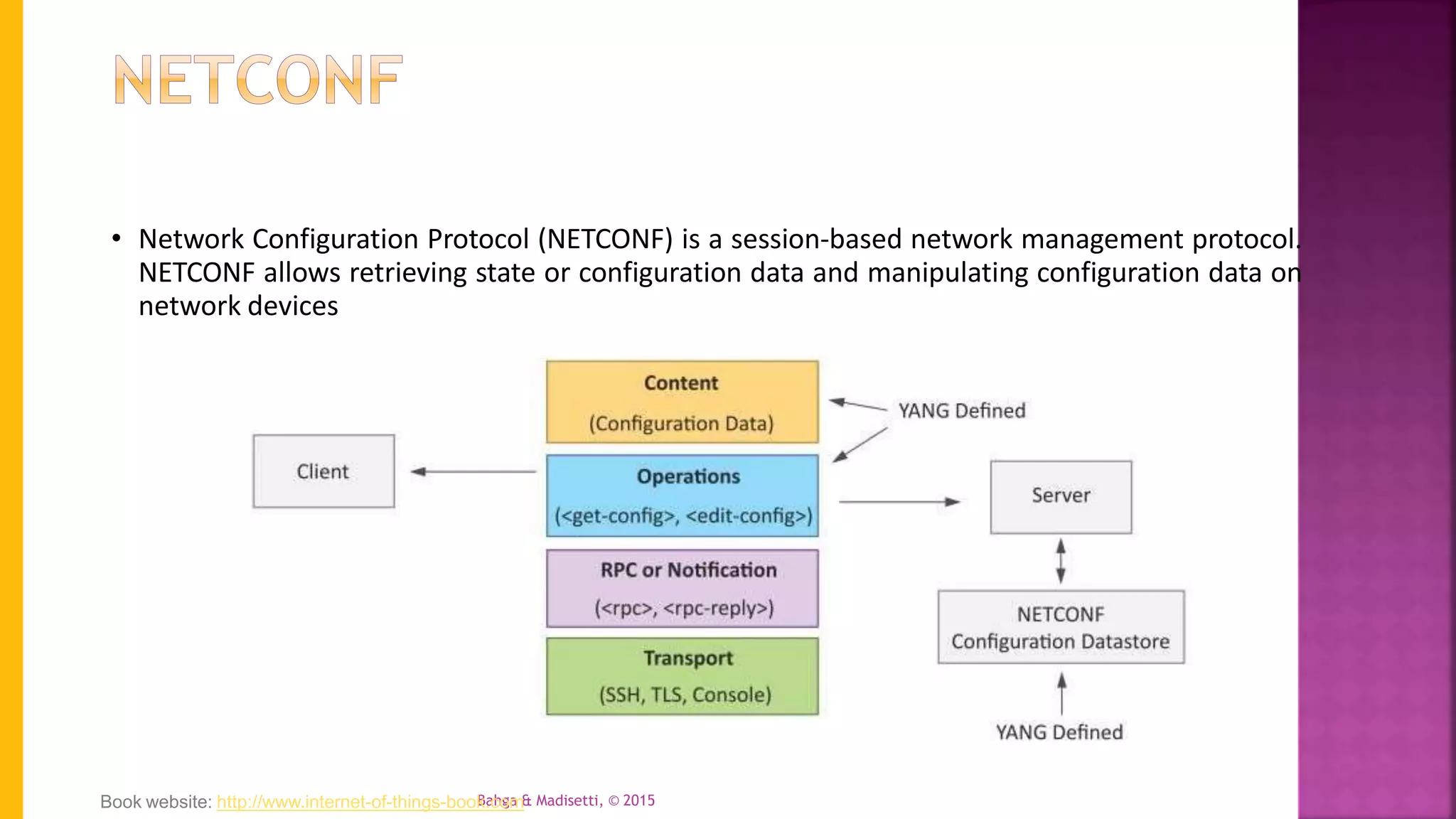
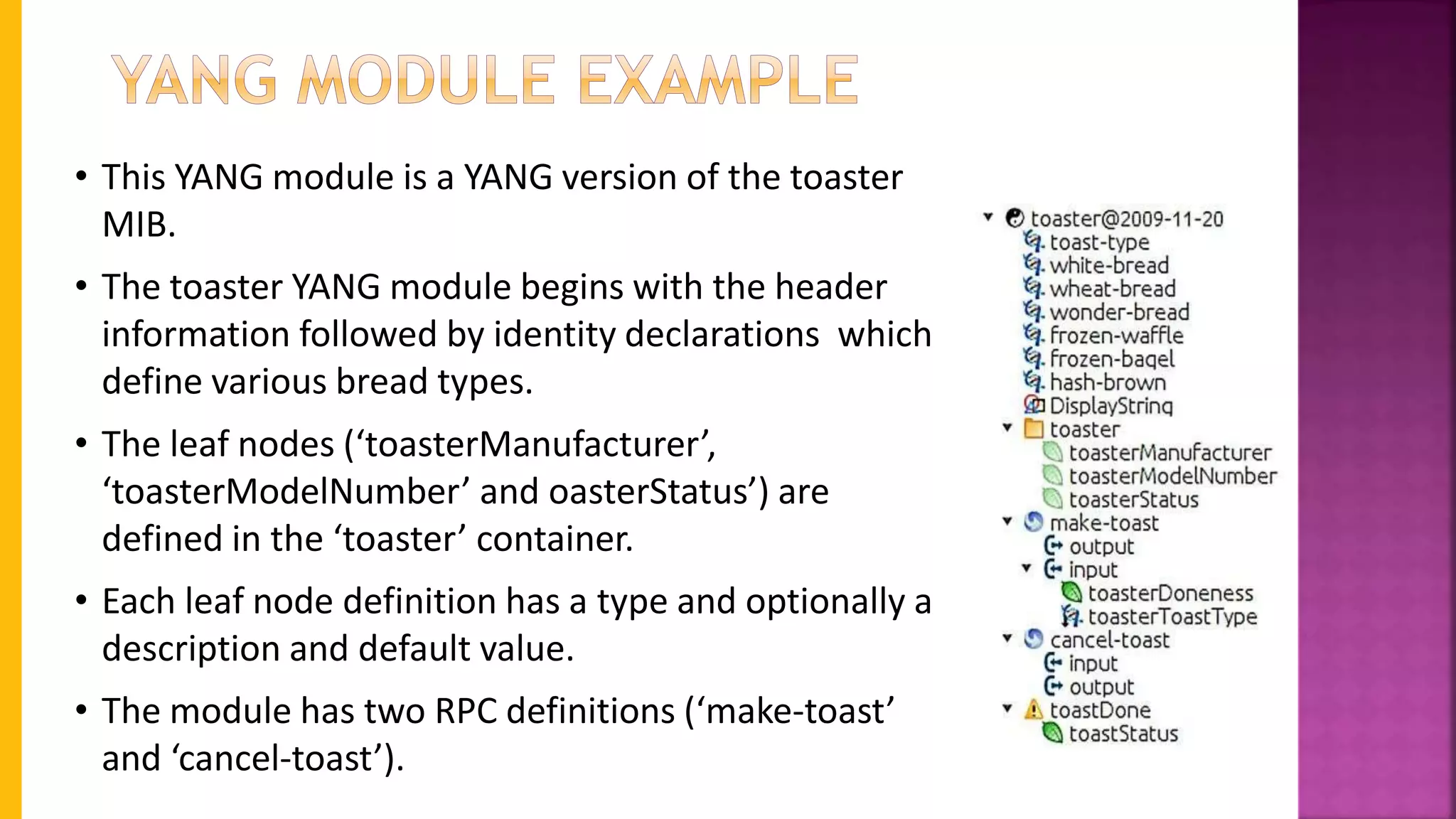
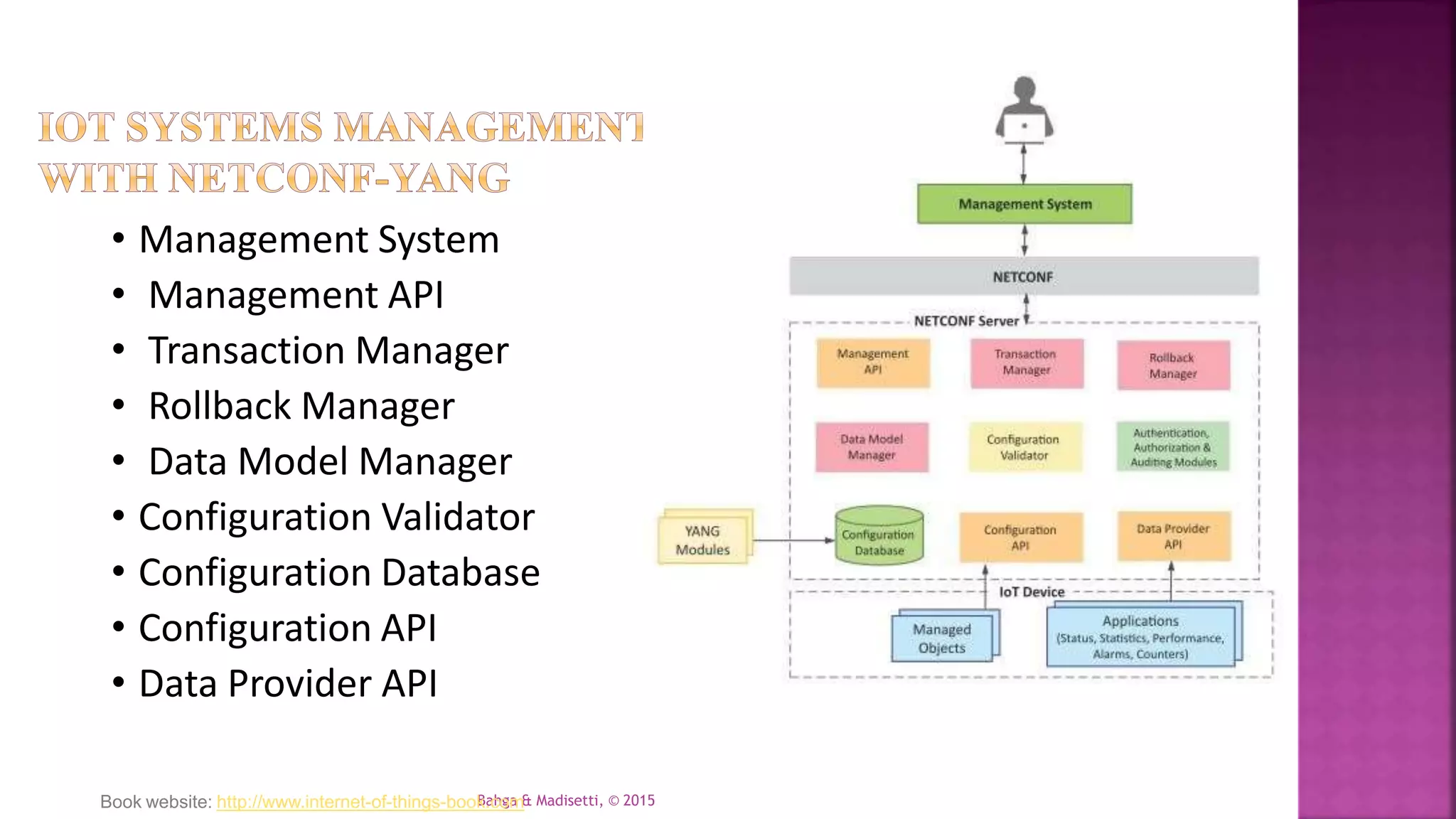
The document discusses using NETCONF and YANG for Internet of Things (IoT) systems management, as NETCONF allows configuring and monitoring network devices through XML-based remote procedure calls and YANG is used to model the configuration and state data. It explains how NETCONF works over SSH for reliable transport, uses XML to encode requests and responses, and provides operations to retrieve and edit device configurations, while YANG is used to define the data models for the configuration and state information exchanged between NETCONF clients and servers. The document also provides an example of a YANG module to model configuration data for a toaster device.