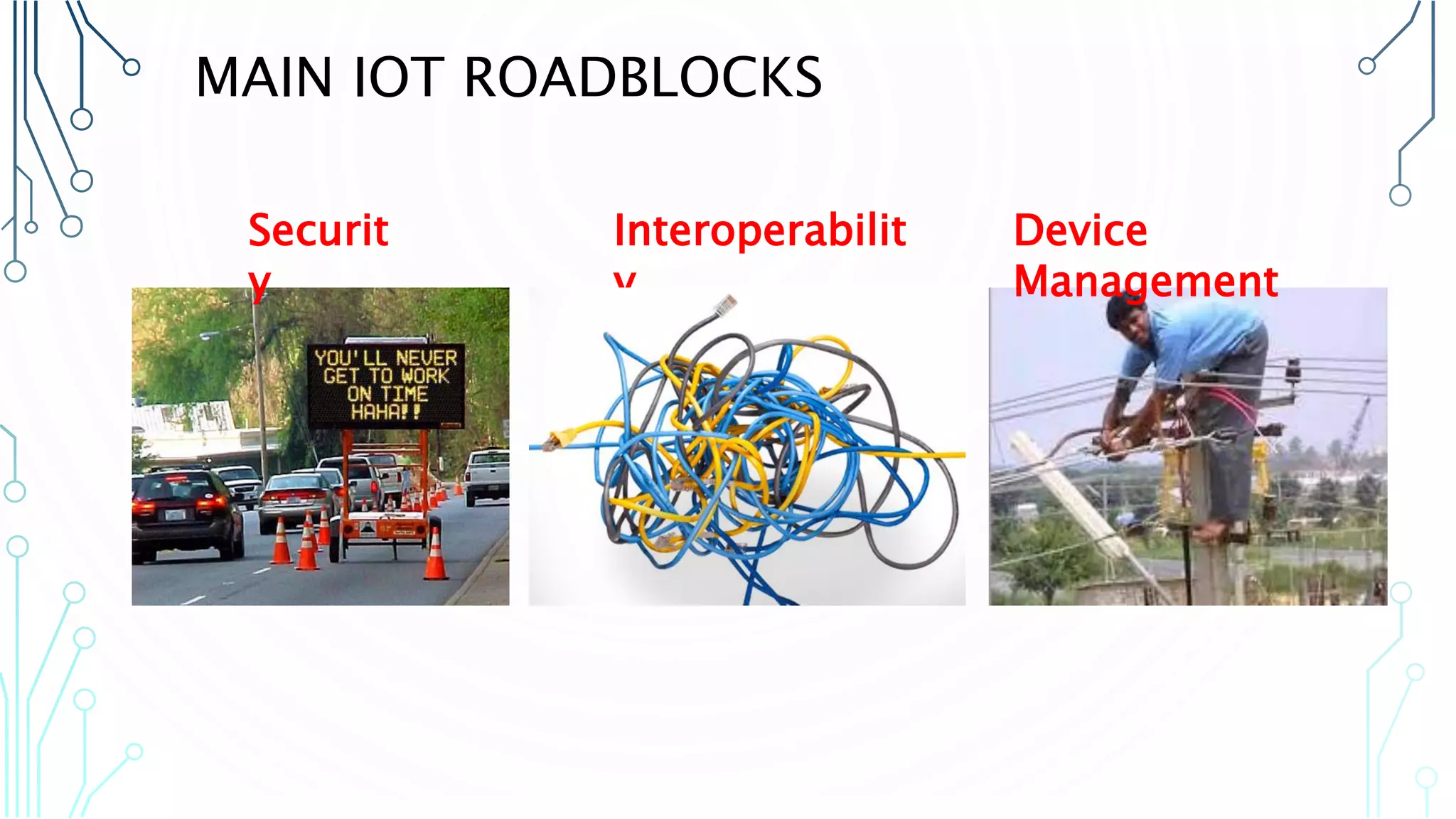
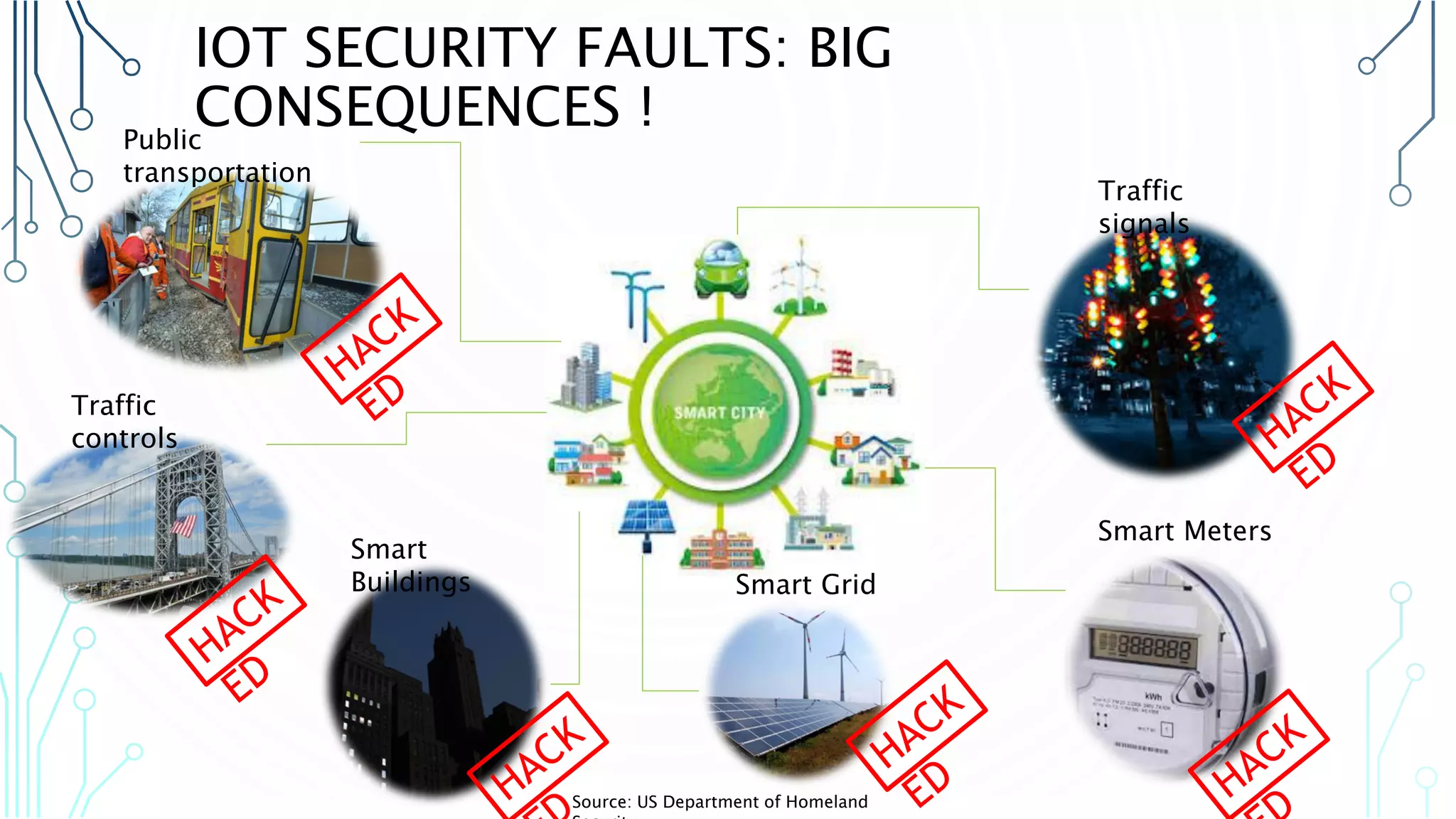
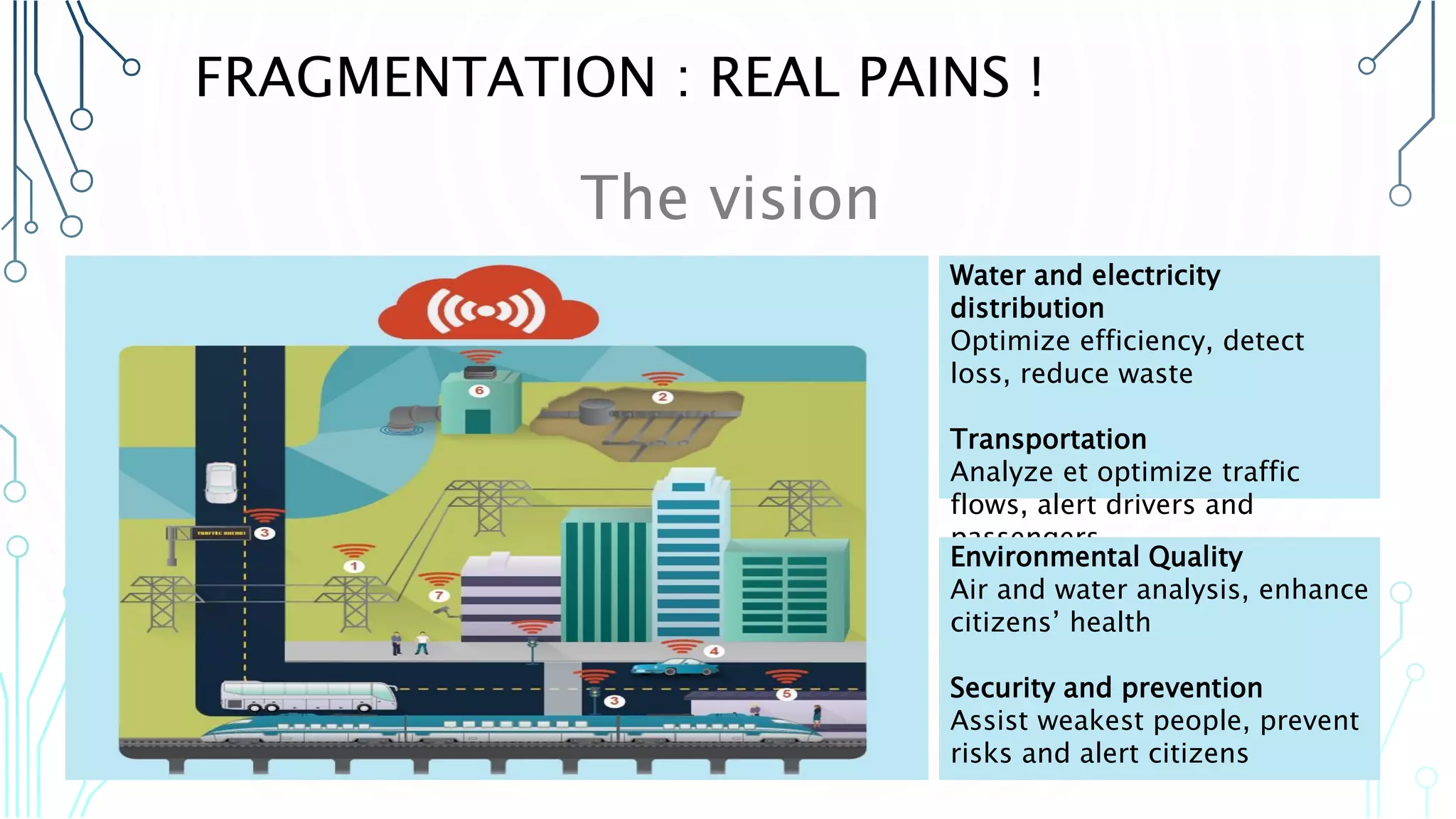
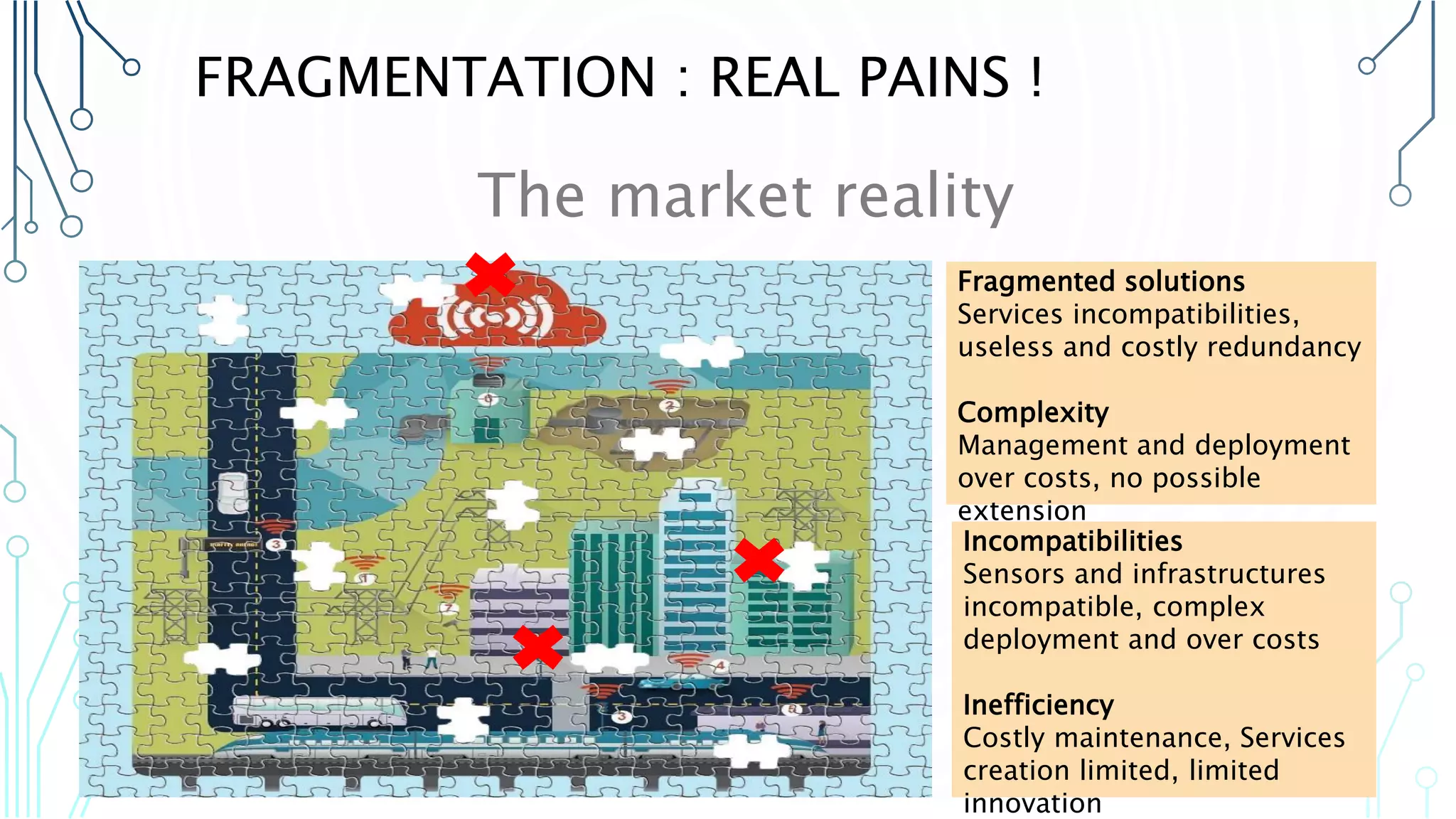
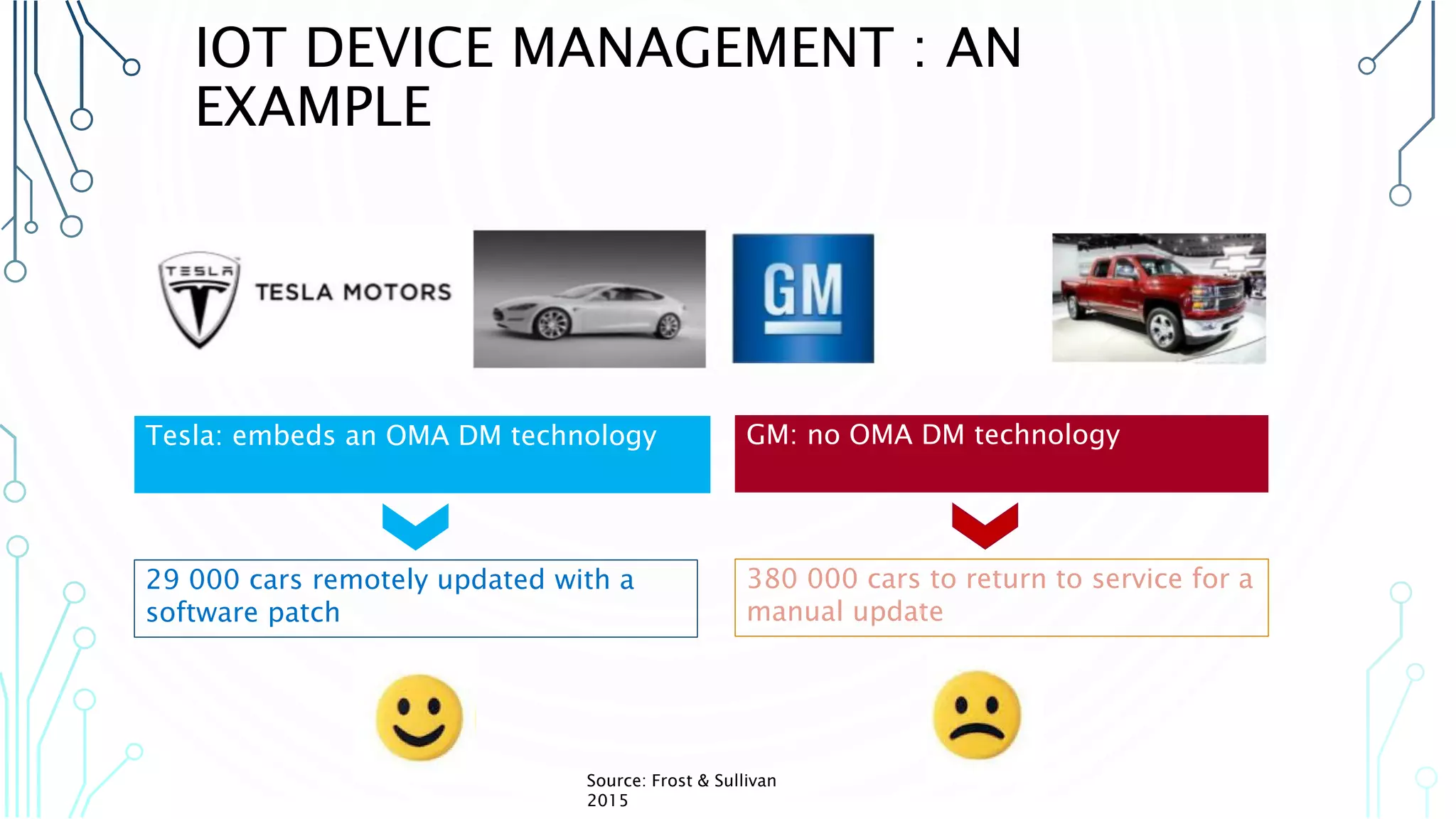
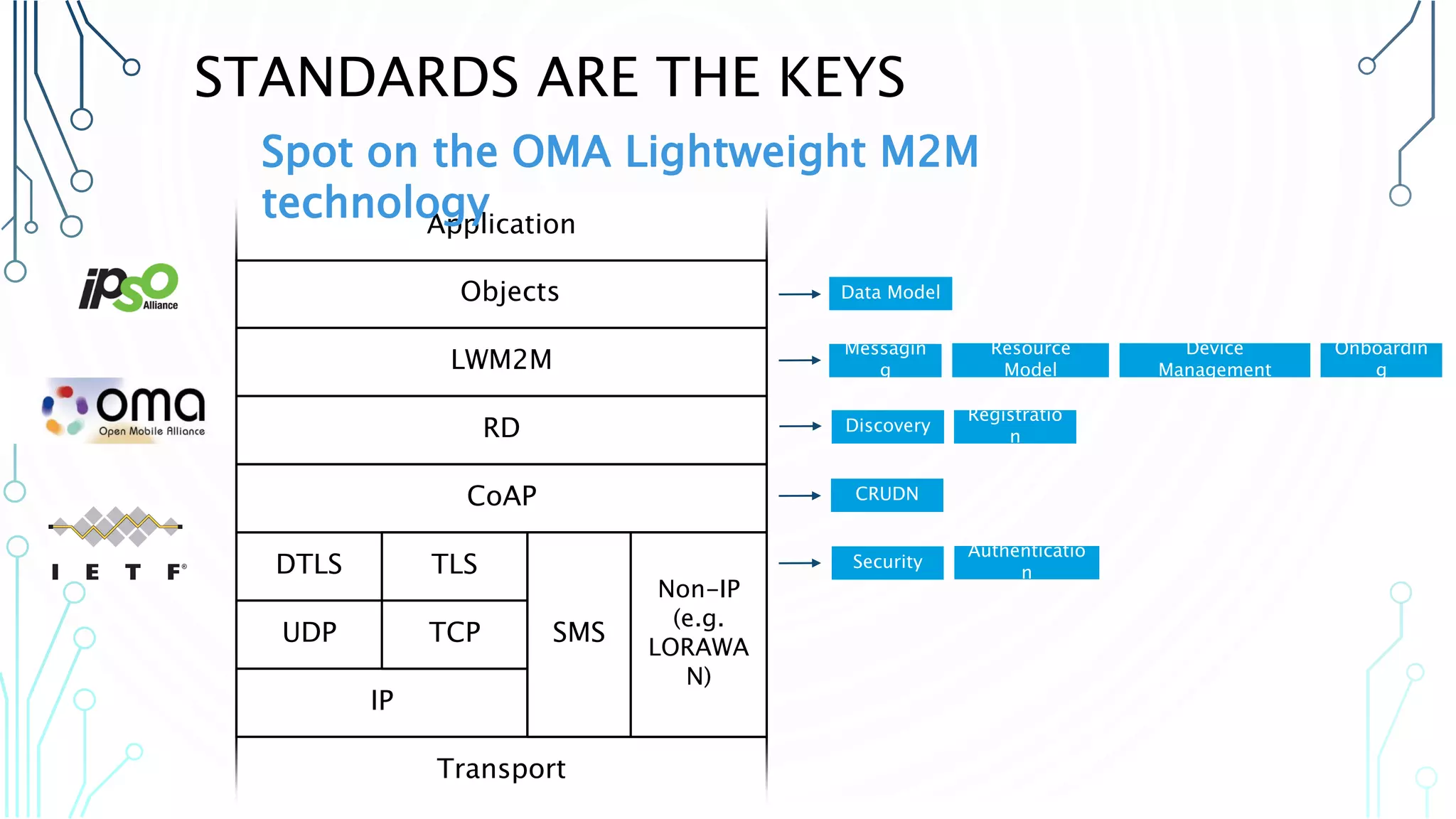
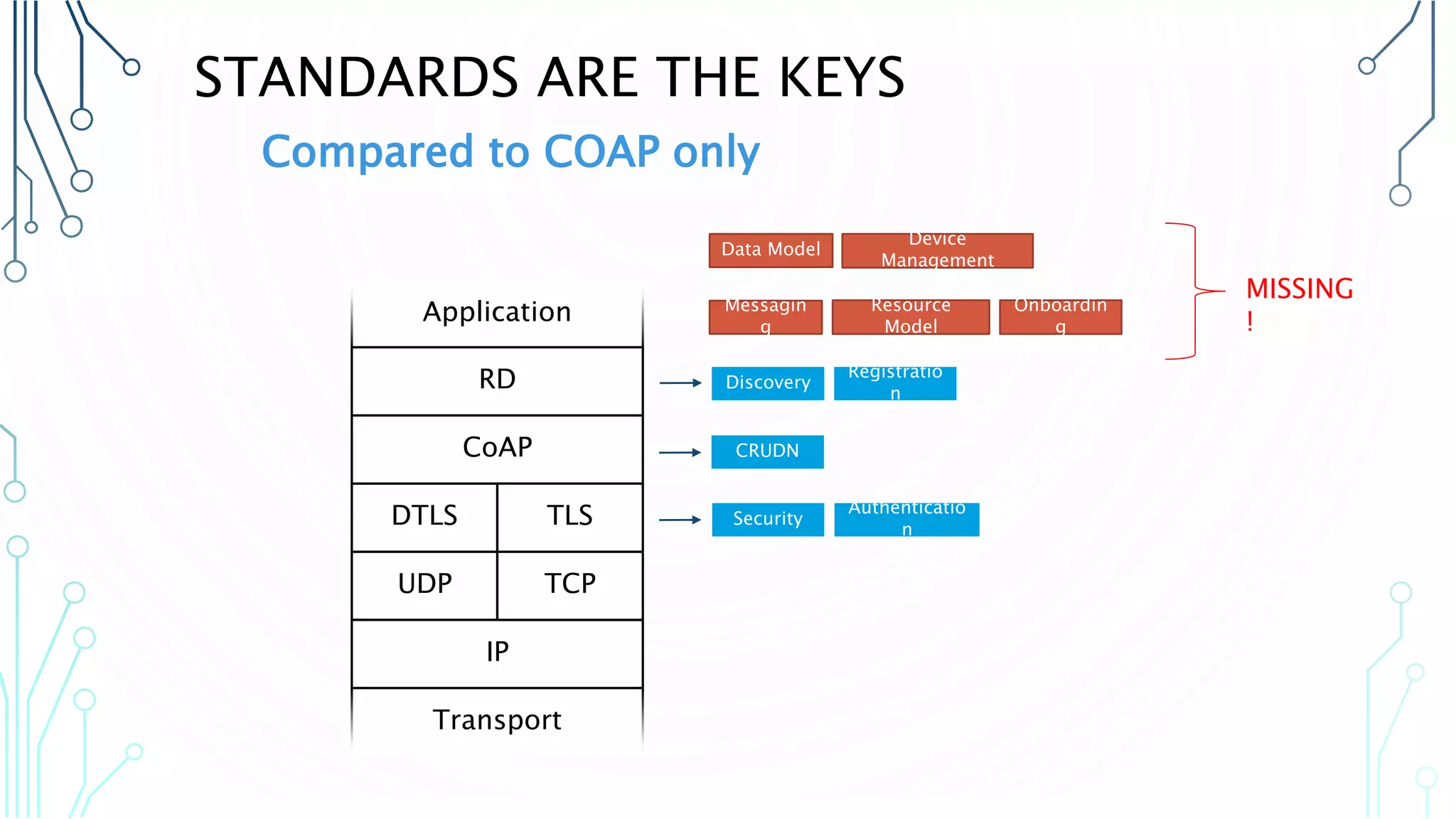
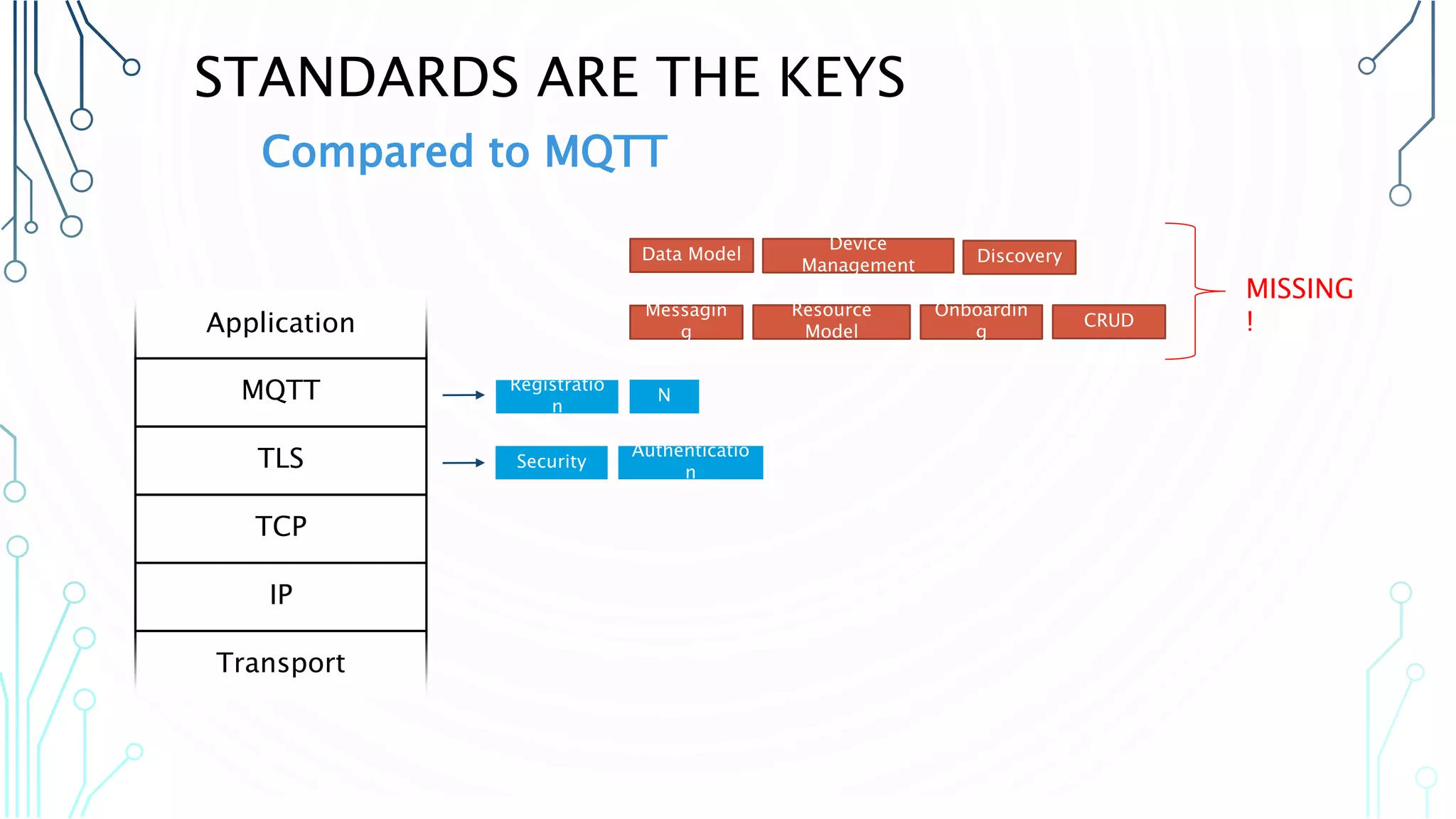
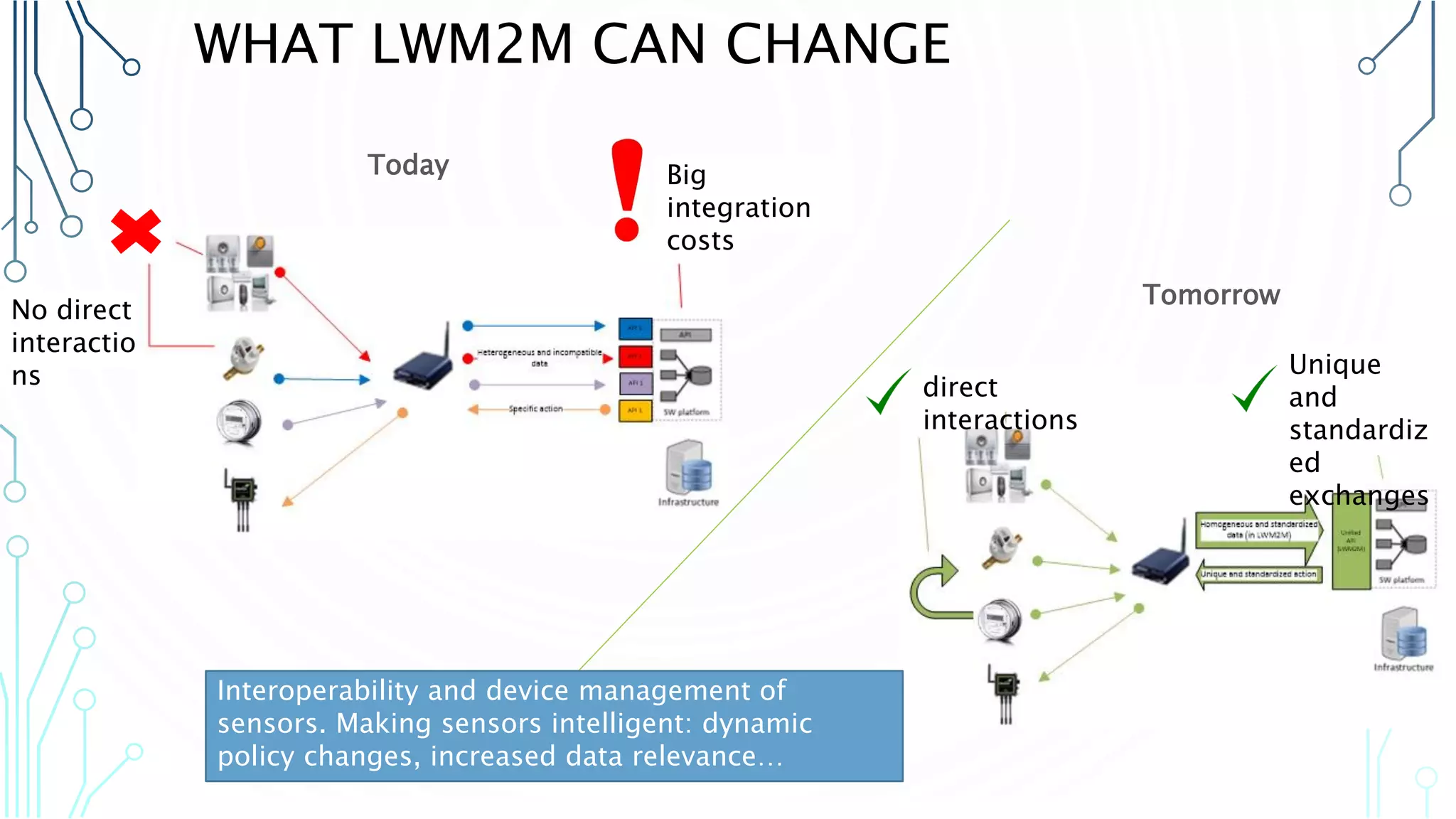
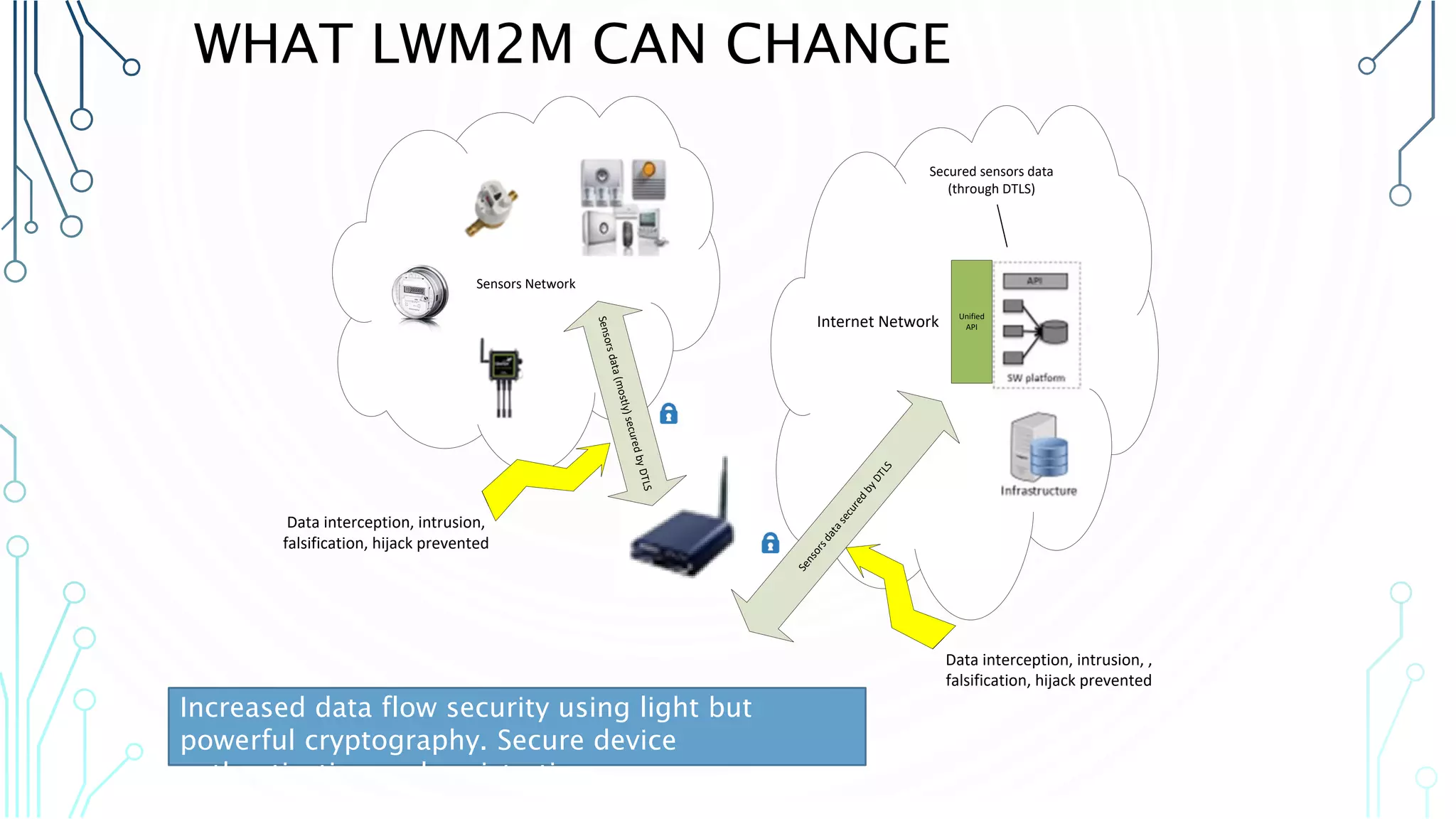
The document discusses the challenges and solutions related to interoperability, security, and device management in the Internet of Things (IoT). It highlights significant issues such as security vulnerabilities in various smart systems and the fragmentation of solutions leading to inefficiencies. The document also emphasizes the importance of standards like LwM2M for enhancing device management and interoperability among IoT devices.