Report
Share
Download to read offline
Recommended
M.tech.quiz (1)

The document appears to be a practice exam for a higher mathematics course covering topics like propositional logic, logical connectives, and lattices. It contains 20 multiple choice questions testing understanding of concepts like tautologies, partial orders, lattices, logical implications, and relationships between logical statements.
number theory chandramowliswaran theorem

This document proves several theorems regarding positive integers and their properties related to greatest common divisors (GCDs). It first proves that the GCD of (abc, (a+b+c)(a^2 + b^2 + c^2)) is 1 if and only if the GCD of pairs of the integers and their sums is 1. It then extends this to prove a similar property for four integers a, b, c, d and their sums. Finally, it asks if a one-to-one mapping exists between very large odd prime numbers and the vertices of a graph such that the GCD of each prime and the sum of primes mapped to adjacent vertices is 1.
tree-gen-algo

This document presents algorithms for generating all possible tree codes (representations of trees as sequences of integers) for a given number of edges. It establishes several arithmetic properties of tree generation codes, including that adding certain integer sequences to existing tree codes will always produce new valid tree codes. Theorems are provided to construct tree codes by appending, repeating, or transforming parts of existing tree codes in ways that preserve the tree structure. An algorithm is also described for checking if a given graceful graph code represents a tree using the Prüfer code technique.
Passman

The document discusses group rings and zero divisors in group rings. Some key points:
- A group ring K[G] is a vector space over a field K with basis G, where elements are finite formal sums of terms with coefficients in K. Multiplication is defined distributively using the group multiplication in G.
- If G contains an element of finite order, then K[G] will contain zero divisors. However, if G has no elements of finite order, it is not clear if K[G] contains zero divisors.
- The document proves a theorem: K[G] is prime (has no zero divisors) if and only if G has no non-identity finite normal subgroups.
graceful Trees through Graceful codes (1)

This document discusses properties and generation of graceful graphs and trees through graceful codes. Some key points:
- Graceful codes represent graceful graphs through sequences of integers that satisfy certain properties. α-valuable codes and gracious codes are types of graceful codes.
- Properties of graceful/α-valuable codes are discussed, such as how codes can be combined or modified to generate new codes representing larger graphs.
- Theorems show how α-valuable codes of trees can be used to generate codes for larger trees through operations like duplication, insertion, or concatenation of codes. This provides an algorithmic way to systematically generate infinite families of graceful tree codes.
recom

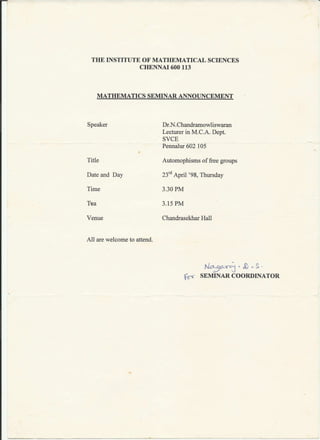
N. Chandramowliswaran was an inspired teacher who made difficult concepts transparent to students and was particularly strong in algebra. His colleague, Dr. K. Balasubramanian, believes Chandramowliswaran will shine as a teacher in any senior position based on the mental acumen and research abilities he demonstrated. Balasubramanian wishes Chandramowliswaran well for his promising future career.
higman

The document summarizes key results about the structure of the unit group of a group ring R(G,K) where G is a finite Abelian group and K is the integer ring of a finite algebraic extension of the rational field.
It shows that R(G,K) decomposes as a direct sum of fields, each isomorphic to an extension of K. It determines a basis for R(G,K) and describes the structure of the unit group of its integer ring. It also proves that elements of finite order in the unit group of R(G,C) are trivial, and the ranks of this unit group and the integer ring unit group are equal.
Recommended
M.tech.quiz (1)

The document appears to be a practice exam for a higher mathematics course covering topics like propositional logic, logical connectives, and lattices. It contains 20 multiple choice questions testing understanding of concepts like tautologies, partial orders, lattices, logical implications, and relationships between logical statements.
number theory chandramowliswaran theorem

This document proves several theorems regarding positive integers and their properties related to greatest common divisors (GCDs). It first proves that the GCD of (abc, (a+b+c)(a^2 + b^2 + c^2)) is 1 if and only if the GCD of pairs of the integers and their sums is 1. It then extends this to prove a similar property for four integers a, b, c, d and their sums. Finally, it asks if a one-to-one mapping exists between very large odd prime numbers and the vertices of a graph such that the GCD of each prime and the sum of primes mapped to adjacent vertices is 1.
tree-gen-algo

This document presents algorithms for generating all possible tree codes (representations of trees as sequences of integers) for a given number of edges. It establishes several arithmetic properties of tree generation codes, including that adding certain integer sequences to existing tree codes will always produce new valid tree codes. Theorems are provided to construct tree codes by appending, repeating, or transforming parts of existing tree codes in ways that preserve the tree structure. An algorithm is also described for checking if a given graceful graph code represents a tree using the Prüfer code technique.
Passman

The document discusses group rings and zero divisors in group rings. Some key points:
- A group ring K[G] is a vector space over a field K with basis G, where elements are finite formal sums of terms with coefficients in K. Multiplication is defined distributively using the group multiplication in G.
- If G contains an element of finite order, then K[G] will contain zero divisors. However, if G has no elements of finite order, it is not clear if K[G] contains zero divisors.
- The document proves a theorem: K[G] is prime (has no zero divisors) if and only if G has no non-identity finite normal subgroups.
graceful Trees through Graceful codes (1)

This document discusses properties and generation of graceful graphs and trees through graceful codes. Some key points:
- Graceful codes represent graceful graphs through sequences of integers that satisfy certain properties. α-valuable codes and gracious codes are types of graceful codes.
- Properties of graceful/α-valuable codes are discussed, such as how codes can be combined or modified to generate new codes representing larger graphs.
- Theorems show how α-valuable codes of trees can be used to generate codes for larger trees through operations like duplication, insertion, or concatenation of codes. This provides an algorithmic way to systematically generate infinite families of graceful tree codes.
recom

N. Chandramowliswaran was an inspired teacher who made difficult concepts transparent to students and was particularly strong in algebra. His colleague, Dr. K. Balasubramanian, believes Chandramowliswaran will shine as a teacher in any senior position based on the mental acumen and research abilities he demonstrated. Balasubramanian wishes Chandramowliswaran well for his promising future career.
higman

The document summarizes key results about the structure of the unit group of a group ring R(G,K) where G is a finite Abelian group and K is the integer ring of a finite algebraic extension of the rational field.
It shows that R(G,K) decomposes as a direct sum of fields, each isomorphic to an extension of K. It determines a basis for R(G,K) and describes the structure of the unit group of its integer ring. It also proves that elements of finite order in the unit group of R(G,C) are trivial, and the ranks of this unit group and the integer ring unit group are equal.
balakrishnan2004

The document summarizes research on the energy of graphs. It defines the energy of a graph as the sum of the absolute values of its eigenvalues. It shows that for any positive epsilon, there exist infinitely many values of n for which a k-regular graph of order n exists whose energy is arbitrarily close to the known upper bound for k-regular graphs. It also establishes the existence of equienergetic graphs that are not cospectral. Equienergetic graphs have the same energy even if they do not have the same spectrum of eigenvalues.
April2012ART_01(1)

This document summarizes research on algebraic elements in group algebras. It begins by defining a group algebra k[G] over a commutative ring k. An element of k[G] is algebraic if it satisfies a non-constant polynomial. The document discusses tools for studying algebraic elements like partial augmentations corresponding to conjugacy classes. It also summarizes results on idempotents, including Kaplansky's theorem that the trace of an idempotent is real and rational. The author's past work on dimension subgroups is also briefly outlined.
DDDDDDDDDDDDDDDDDD

This document summarizes a paper that proposes novel secret sharing and key distribution schemes based on number theory. It introduces generalized secret sharing schemes and key distribution schemes that are useful for multi-party systems. The paper then presents two main results: 1) A lemma showing that there exist integers that satisfy a particular congruence relation involving three distinct primes. 2) A theorem demonstrating how to generate secret shares of a secret S among three shareholders such that combining the shares recovers S. The scheme is based on the lemma and uses modular arithmetic with a modulus composed of three large primes.
CCCCCCCCCCCCCCCCCC

This document summarizes key concepts in number theory presented in a lecture by Dr. N. Chandramowliswaran including:
- Properties of divisibility, greatest common divisors, prime numbers, and the fundamental theorem of arithmetic.
- Definitions and properties of the Mobius function, Euler's totient function, and congruences.
- Theorems regarding congruences including the Euler-Fermat theorem and the Chinese Remainder Theorem.
BBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBB

This document summarizes a paper that proposes novel secret sharing and key distribution schemes based on number theory. It introduces generalized secret sharing schemes and key distribution schemes that are useful for multi-party systems. The paper then presents two main results: 1) A lemma showing that there exist integers that satisfy a particular congruence relation involving three distinct primes. 2) A theorem demonstrating how to generate secret shares of a secret S among three shareholders such that combining the shares recovers S. The scheme is based on the lemma and uses modular arithmetic with a modulus composed of three large primes.
PETERSON BERGE

This document summarizes a paper that proposes novel secret sharing and key distribution schemes based on number theory. It introduces generalized secret sharing schemes and key distribution schemes that are useful for multi-party systems. The paper then presents two main results: 1) A lemma showing that there exist integers that satisfy a particular congruence relation involving three distinct primes. 2) A theorem demonstrating how to generate secret shares of a secret S among three shareholders such that combining the shares recovers S. The scheme is based on the lemma and uses modular arithmetic with a modulus composed of three large primes.
FDP SumCourse Schedule July 2009 (1)

This document provides the schedule for a 7-day summer course on basic engineering mathematics, discrete mathematics, and graph theory held from July 6-13, 2009 at VIT University. The course schedule lists the daily topics to be covered from 9:45am-4:15pm, including lectures on graph theory, advanced calculus, formal languages and automata, probability and random processes, mathematical modeling, and programming fundamentals. Various professors from VIT University and other institutions are listed as lecturers for the different topics. The course is coordinated by Dr. N. Chandramowliswaran and overseen by the director Dr. K. Sathiyanarayanan.
R.S.A Encryption

This document describes an RSA encryption method using Pell's equation. It involves:
1) Selecting a secret odd prime integer R and finding the least positive integral solution (Y0, X0) to the Diophantine equation Y^2 - RX^2 = 1.
2) Selecting two large odd primes p and q and defining N = pq.
3) Defining the public key α using Y0, X0, R, and the Euler totient function φ(n).
The encryption of a message m involves computing E ≡ mS (mod n) where S is derived from α, and the decryption recovers m by computing E^d (mod n
ArproTree_journal

The document discusses properties of tree generation codes and algorithms for generating tree codes. It defines graceful labeling and graceful codes for representing graceful graphs. Section 1 defines graceful codes and α-valuable codes. Section 2 presents arithmetic properties of tree generation codes, including theorems for generating tree codes by adding values to existing tree codes. Section 3 describes an algorithm to generate all tree codes for a given number of edges using Prüfer code techniques. The document also provides examples of tree codes.
29-SrinivasanMuralikrishnaChandramowliswaran

This document proposes a secret key distribution technique using number theory. It presents a theorem that for any positive integer k ≥ 2, there exists k + k(k - 1)/2 share holders who can reconstruct a distributed secret. The technique selects secret positive integers and defines variables to distribute shares of the secret to the share holders, ensuring k share holders can reconstruct the secret. It concludes that cryptography has evolved over time into a mathematized discipline combining secret concealment with attack analysis.
11

This document proposes a secure scheme for secret sharing and key distribution using Pell's equation. It begins with an introduction to key distribution problems and secret sharing schemes. It then presents an algorithm that uses Pell's equation to generate a secret exponent S, which is used to distribute shares of a key to users. Each user's share allows them to collectively compute the key when a minimum number of users combine their shares, but individual shares reveal no information about the key. The algorithm provides perfectly secure secret sharing against coalitions of k or fewer users.
15

This document summarizes a research paper that proposes an authenticated multiple key distribution algorithm using simple continued fractions. The algorithm represents two large prime numbers as a simple continued fraction that is then used to construct a non-homogeneous equation with two variables. The secret key is divided into shares distributed to participants in a way that any fewer than a threshold number of shares provides no information about the key. The shares can be used to reconstruct the key and are verified through decrypting an encrypted message.
Final Report-1-(1)

This document is a project report submitted by Shivangi Goel for the degree of Master of Science in Mathematics. The report proposes a secure scheme for secret sharing using graph theory. It involves using a system of linear congruences based on prime numbers to divide a secret into shares and distribute the shares among graph nodes in a way that allows reconstructing the secret using the Chinese Remainder Theorem. The report includes background on secret sharing, linear congruences, and cryptography techniques like RSA. It then describes the proposed scheme which uses specific graph structures like Peterson and Heawood graphs to represent the access structure and distribute shares of the secret.
Aina_final

This document is a project report submitted by Aina Gupta to the Department of Applied Sciences at ITM University, Gurgaon, India in partial fulfillment of the requirements for a Master of Science degree in Mathematics. The report explores new encryption and decryption techniques on ZN(3) and ZN(4) under the supervision of Prof. N. Chandramowliswaran and Dr. Gaurav Gupta. The report includes an introduction to cryptography, preliminaries on relevant mathematical concepts, and several sections proposing and analyzing new bijective encryption functions on ZN(3) and ZN(4).
21642583%2E2014%2E985803

This document summarizes an article that proposes three new secret key sharing schemes based on the Chinese Remainder Theorem (CRT). It begins by providing background on CRT and secret sharing schemes. It then presents the main result, which is three theorems and algorithms for authenticated key distribution using a given set of primes. The first theorem describes how to construct three secret shares from a secret S such that combining the shares recovers S. It proves this using a lemma about finding integers that satisfy a system of congruences. The next sections provide examples and algorithms to motivate the secret sharing schemes. In summary, the document presents new methods for secret sharing based on number theory and the CRT.
More Related Content
More from Chandramowliswaran NARAYANASWAMY
balakrishnan2004

The document summarizes research on the energy of graphs. It defines the energy of a graph as the sum of the absolute values of its eigenvalues. It shows that for any positive epsilon, there exist infinitely many values of n for which a k-regular graph of order n exists whose energy is arbitrarily close to the known upper bound for k-regular graphs. It also establishes the existence of equienergetic graphs that are not cospectral. Equienergetic graphs have the same energy even if they do not have the same spectrum of eigenvalues.
April2012ART_01(1)

This document summarizes research on algebraic elements in group algebras. It begins by defining a group algebra k[G] over a commutative ring k. An element of k[G] is algebraic if it satisfies a non-constant polynomial. The document discusses tools for studying algebraic elements like partial augmentations corresponding to conjugacy classes. It also summarizes results on idempotents, including Kaplansky's theorem that the trace of an idempotent is real and rational. The author's past work on dimension subgroups is also briefly outlined.
DDDDDDDDDDDDDDDDDD

This document summarizes a paper that proposes novel secret sharing and key distribution schemes based on number theory. It introduces generalized secret sharing schemes and key distribution schemes that are useful for multi-party systems. The paper then presents two main results: 1) A lemma showing that there exist integers that satisfy a particular congruence relation involving three distinct primes. 2) A theorem demonstrating how to generate secret shares of a secret S among three shareholders such that combining the shares recovers S. The scheme is based on the lemma and uses modular arithmetic with a modulus composed of three large primes.
CCCCCCCCCCCCCCCCCC

This document summarizes key concepts in number theory presented in a lecture by Dr. N. Chandramowliswaran including:
- Properties of divisibility, greatest common divisors, prime numbers, and the fundamental theorem of arithmetic.
- Definitions and properties of the Mobius function, Euler's totient function, and congruences.
- Theorems regarding congruences including the Euler-Fermat theorem and the Chinese Remainder Theorem.
BBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBB

This document summarizes a paper that proposes novel secret sharing and key distribution schemes based on number theory. It introduces generalized secret sharing schemes and key distribution schemes that are useful for multi-party systems. The paper then presents two main results: 1) A lemma showing that there exist integers that satisfy a particular congruence relation involving three distinct primes. 2) A theorem demonstrating how to generate secret shares of a secret S among three shareholders such that combining the shares recovers S. The scheme is based on the lemma and uses modular arithmetic with a modulus composed of three large primes.
PETERSON BERGE

This document summarizes a paper that proposes novel secret sharing and key distribution schemes based on number theory. It introduces generalized secret sharing schemes and key distribution schemes that are useful for multi-party systems. The paper then presents two main results: 1) A lemma showing that there exist integers that satisfy a particular congruence relation involving three distinct primes. 2) A theorem demonstrating how to generate secret shares of a secret S among three shareholders such that combining the shares recovers S. The scheme is based on the lemma and uses modular arithmetic with a modulus composed of three large primes.
FDP SumCourse Schedule July 2009 (1)

This document provides the schedule for a 7-day summer course on basic engineering mathematics, discrete mathematics, and graph theory held from July 6-13, 2009 at VIT University. The course schedule lists the daily topics to be covered from 9:45am-4:15pm, including lectures on graph theory, advanced calculus, formal languages and automata, probability and random processes, mathematical modeling, and programming fundamentals. Various professors from VIT University and other institutions are listed as lecturers for the different topics. The course is coordinated by Dr. N. Chandramowliswaran and overseen by the director Dr. K. Sathiyanarayanan.
R.S.A Encryption

This document describes an RSA encryption method using Pell's equation. It involves:
1) Selecting a secret odd prime integer R and finding the least positive integral solution (Y0, X0) to the Diophantine equation Y^2 - RX^2 = 1.
2) Selecting two large odd primes p and q and defining N = pq.
3) Defining the public key α using Y0, X0, R, and the Euler totient function φ(n).
The encryption of a message m involves computing E ≡ mS (mod n) where S is derived from α, and the decryption recovers m by computing E^d (mod n
ArproTree_journal

The document discusses properties of tree generation codes and algorithms for generating tree codes. It defines graceful labeling and graceful codes for representing graceful graphs. Section 1 defines graceful codes and α-valuable codes. Section 2 presents arithmetic properties of tree generation codes, including theorems for generating tree codes by adding values to existing tree codes. Section 3 describes an algorithm to generate all tree codes for a given number of edges using Prüfer code techniques. The document also provides examples of tree codes.
29-SrinivasanMuralikrishnaChandramowliswaran

This document proposes a secret key distribution technique using number theory. It presents a theorem that for any positive integer k ≥ 2, there exists k + k(k - 1)/2 share holders who can reconstruct a distributed secret. The technique selects secret positive integers and defines variables to distribute shares of the secret to the share holders, ensuring k share holders can reconstruct the secret. It concludes that cryptography has evolved over time into a mathematized discipline combining secret concealment with attack analysis.
11

This document proposes a secure scheme for secret sharing and key distribution using Pell's equation. It begins with an introduction to key distribution problems and secret sharing schemes. It then presents an algorithm that uses Pell's equation to generate a secret exponent S, which is used to distribute shares of a key to users. Each user's share allows them to collectively compute the key when a minimum number of users combine their shares, but individual shares reveal no information about the key. The algorithm provides perfectly secure secret sharing against coalitions of k or fewer users.
15

This document summarizes a research paper that proposes an authenticated multiple key distribution algorithm using simple continued fractions. The algorithm represents two large prime numbers as a simple continued fraction that is then used to construct a non-homogeneous equation with two variables. The secret key is divided into shares distributed to participants in a way that any fewer than a threshold number of shares provides no information about the key. The shares can be used to reconstruct the key and are verified through decrypting an encrypted message.
Final Report-1-(1)

This document is a project report submitted by Shivangi Goel for the degree of Master of Science in Mathematics. The report proposes a secure scheme for secret sharing using graph theory. It involves using a system of linear congruences based on prime numbers to divide a secret into shares and distribute the shares among graph nodes in a way that allows reconstructing the secret using the Chinese Remainder Theorem. The report includes background on secret sharing, linear congruences, and cryptography techniques like RSA. It then describes the proposed scheme which uses specific graph structures like Peterson and Heawood graphs to represent the access structure and distribute shares of the secret.
Aina_final

This document is a project report submitted by Aina Gupta to the Department of Applied Sciences at ITM University, Gurgaon, India in partial fulfillment of the requirements for a Master of Science degree in Mathematics. The report explores new encryption and decryption techniques on ZN(3) and ZN(4) under the supervision of Prof. N. Chandramowliswaran and Dr. Gaurav Gupta. The report includes an introduction to cryptography, preliminaries on relevant mathematical concepts, and several sections proposing and analyzing new bijective encryption functions on ZN(3) and ZN(4).
21642583%2E2014%2E985803

This document summarizes an article that proposes three new secret key sharing schemes based on the Chinese Remainder Theorem (CRT). It begins by providing background on CRT and secret sharing schemes. It then presents the main result, which is three theorems and algorithms for authenticated key distribution using a given set of primes. The first theorem describes how to construct three secret shares from a secret S such that combining the shares recovers S. It proves this using a lemma about finding integers that satisfy a system of congruences. The next sections provide examples and algorithms to motivate the secret sharing schemes. In summary, the document presents new methods for secret sharing based on number theory and the CRT.