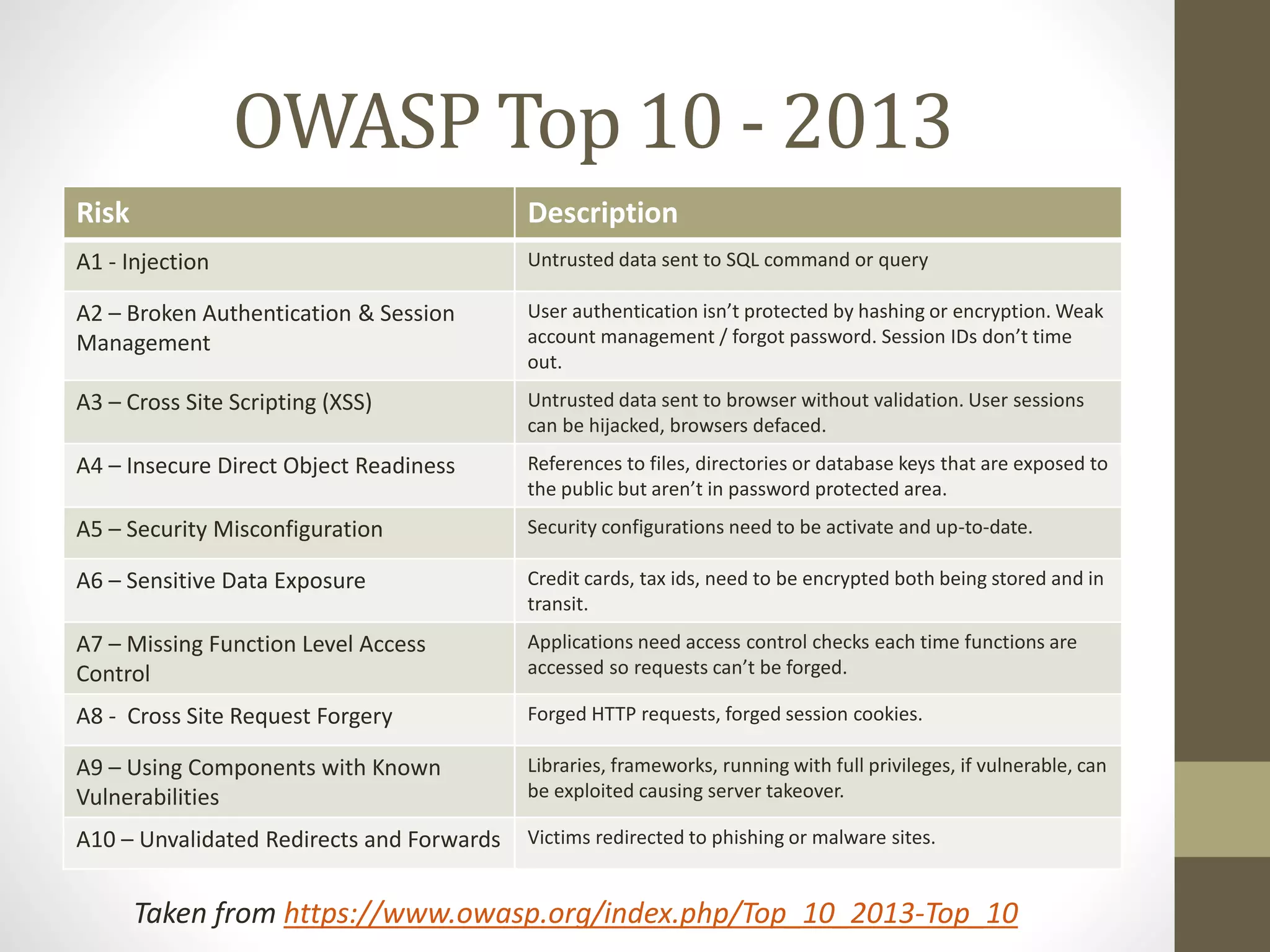
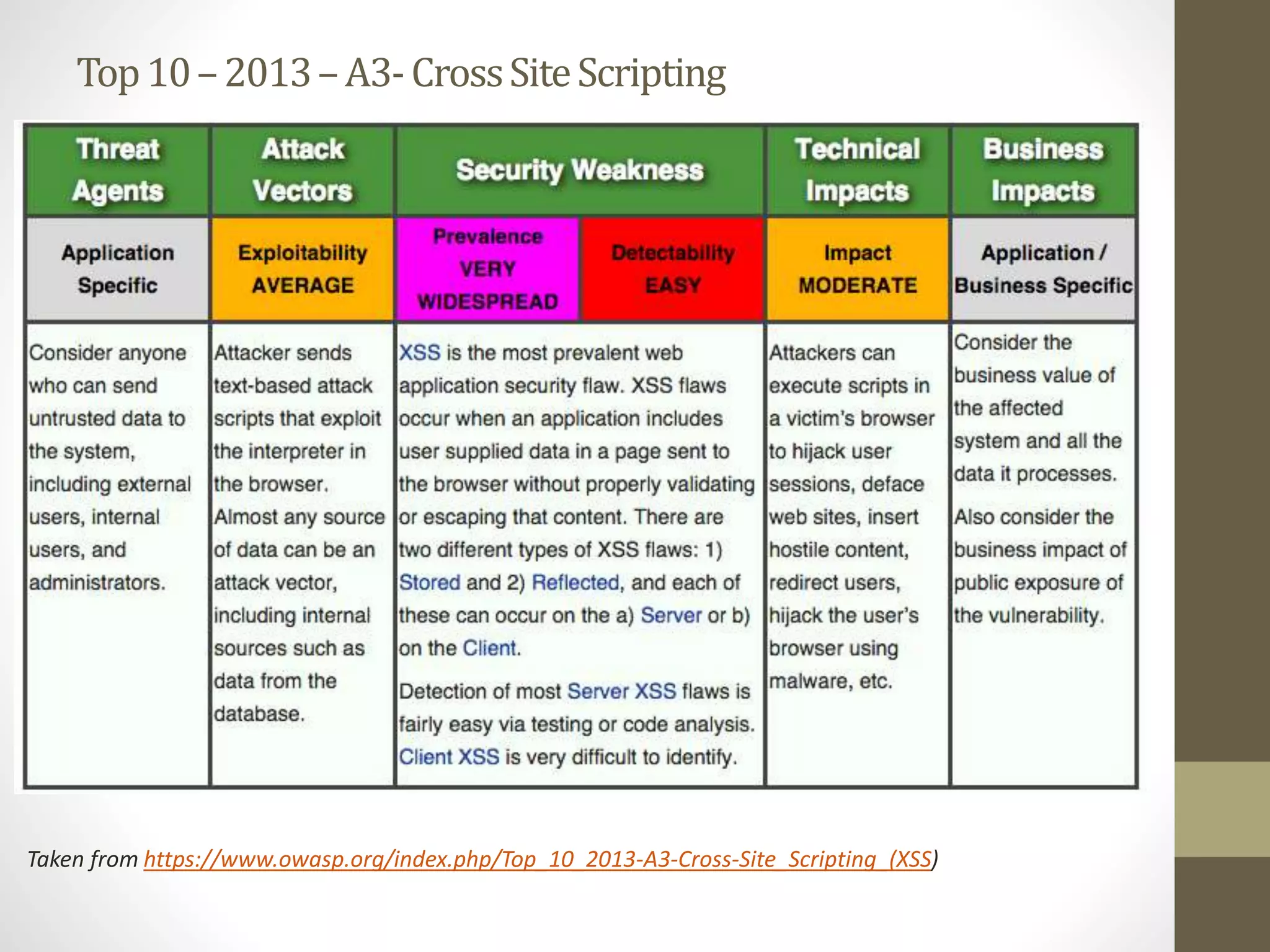
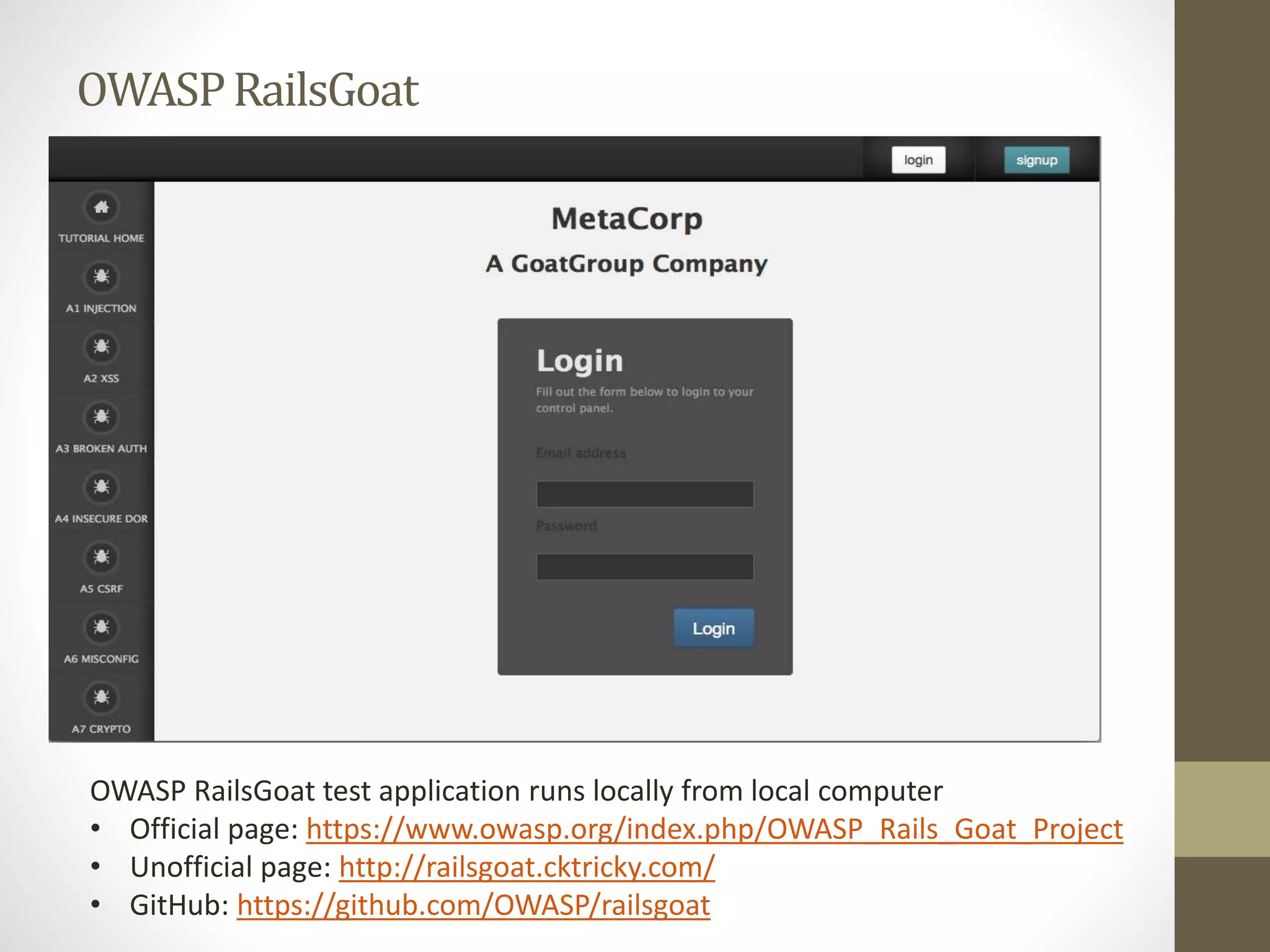
The document introduces the Open Web Application Security Project (OWASP), a resource established to improve security testing in web applications. The top ten vulnerabilities identified by OWASP highlight critical risks such as injection, authentication issues, and insecure data exposure. Additionally, it mentions the effectiveness of crowd-sourced security testing through bug bounty programs involving public participation.