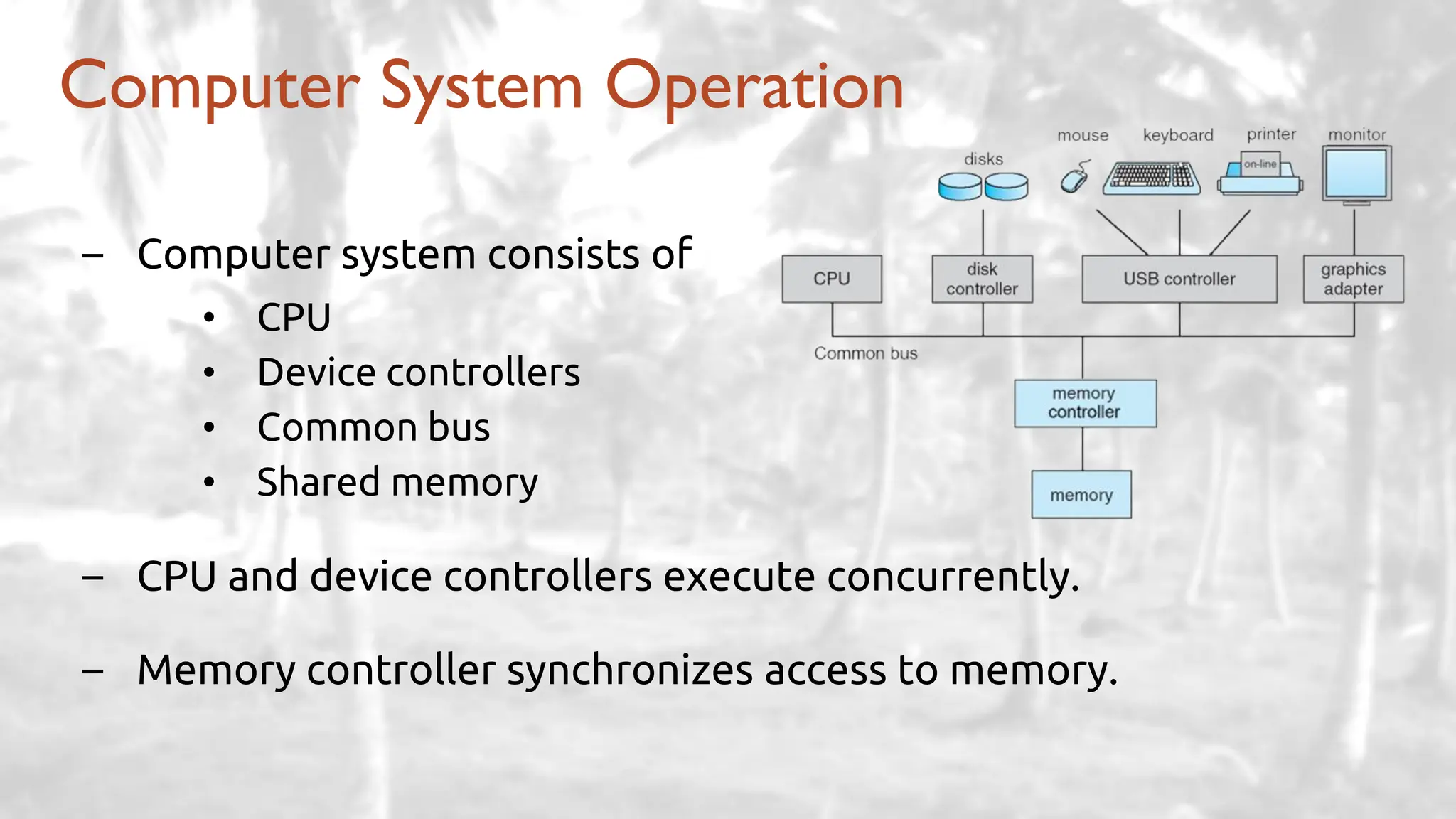
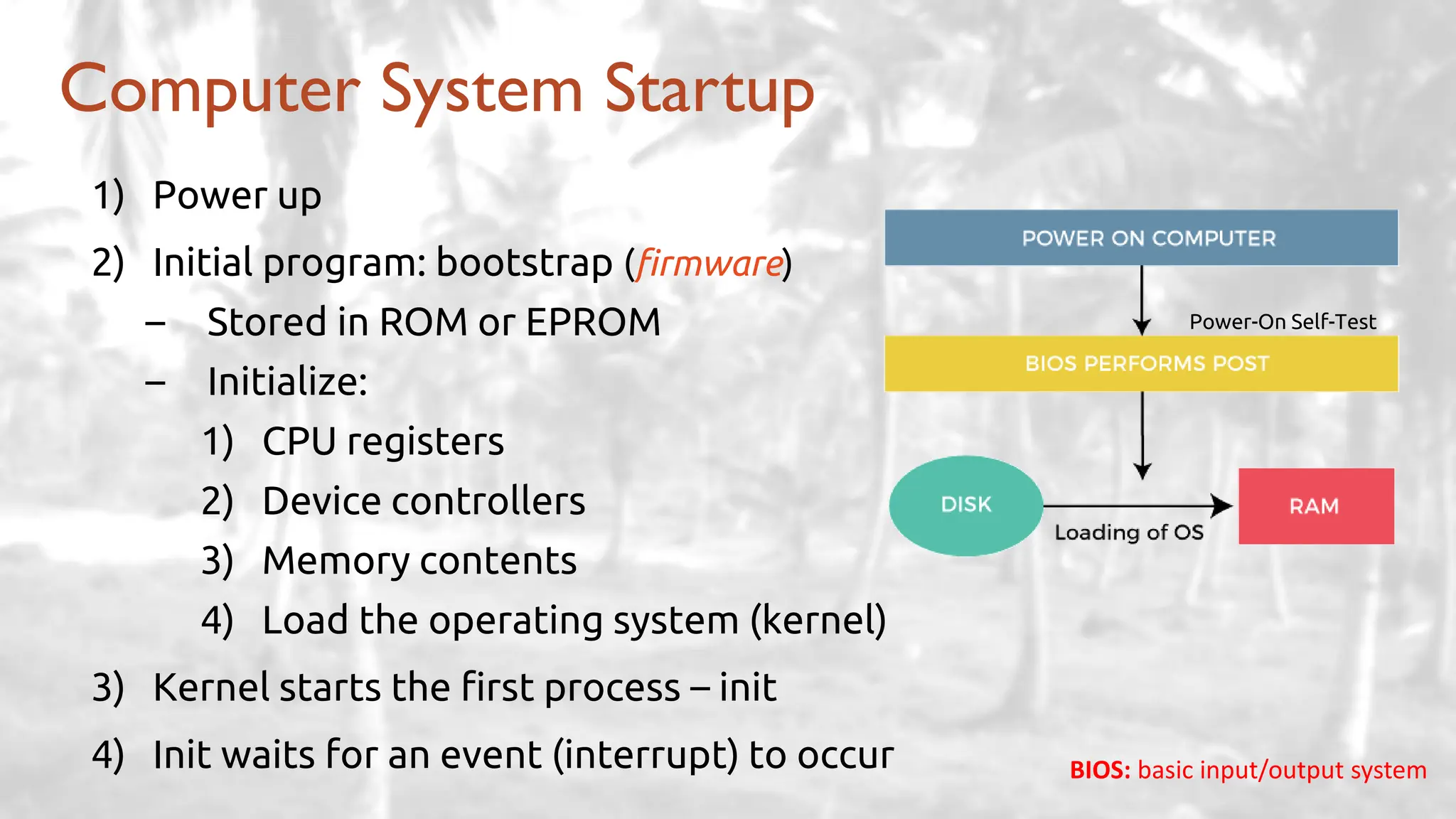
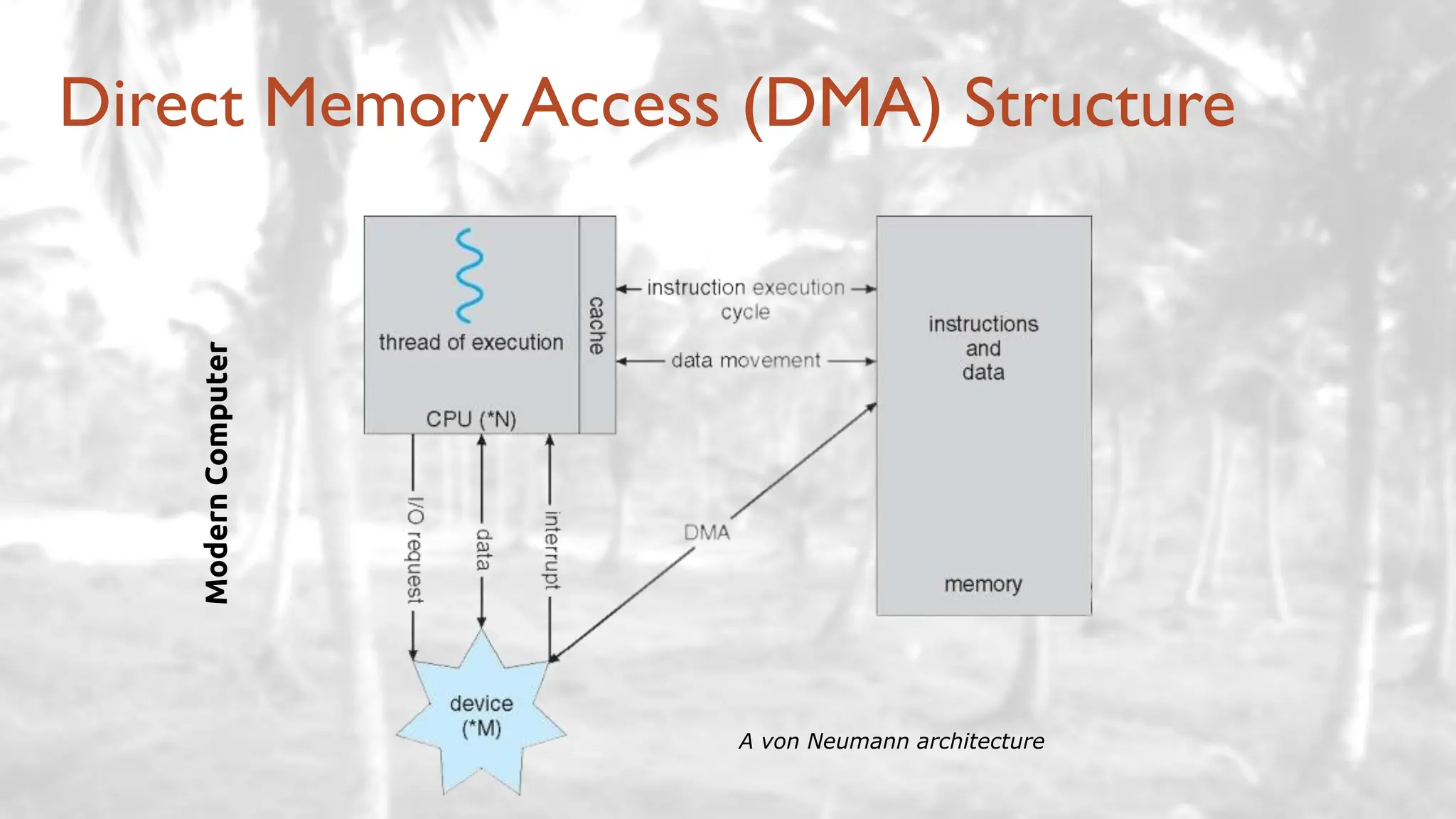
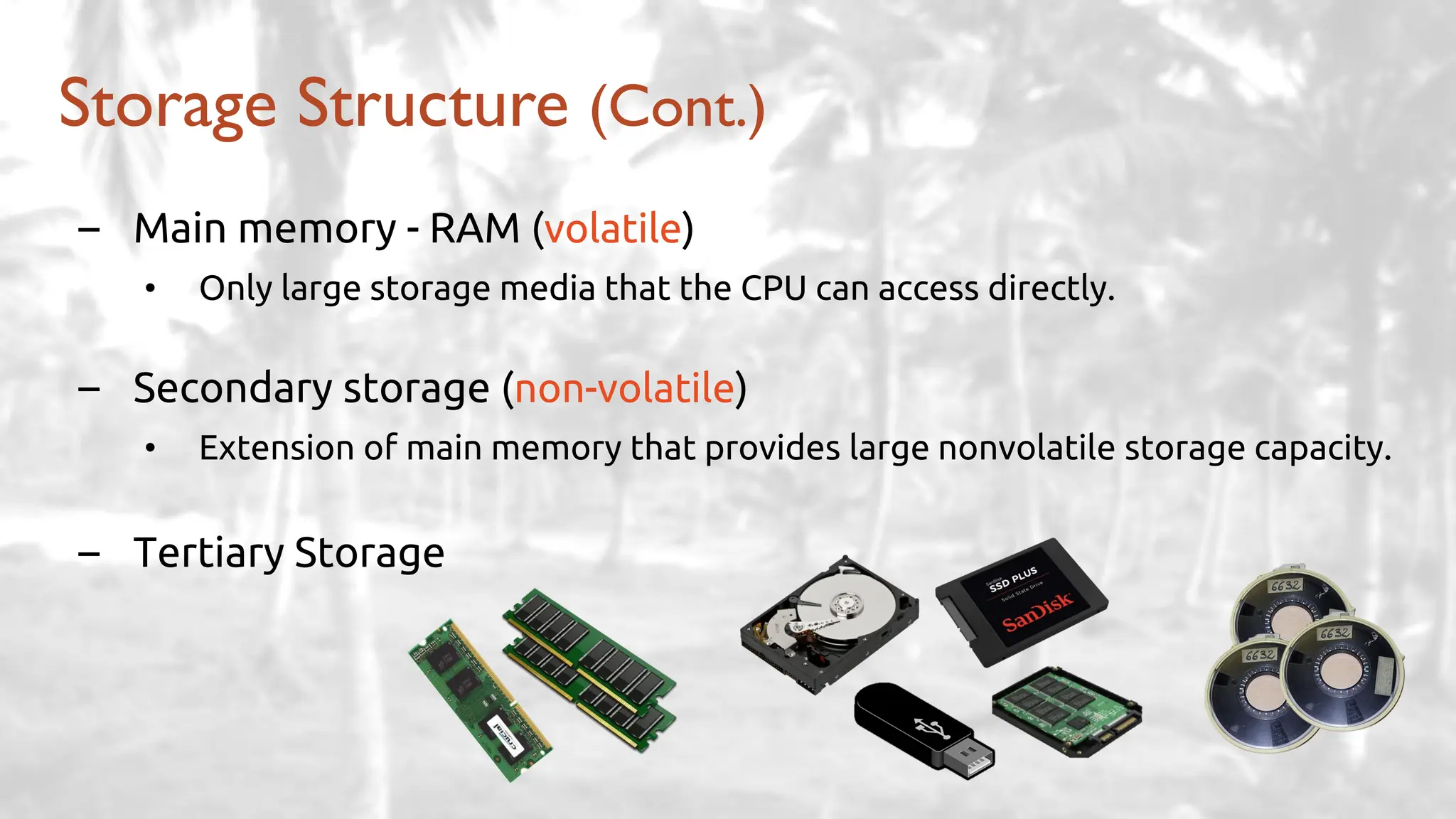
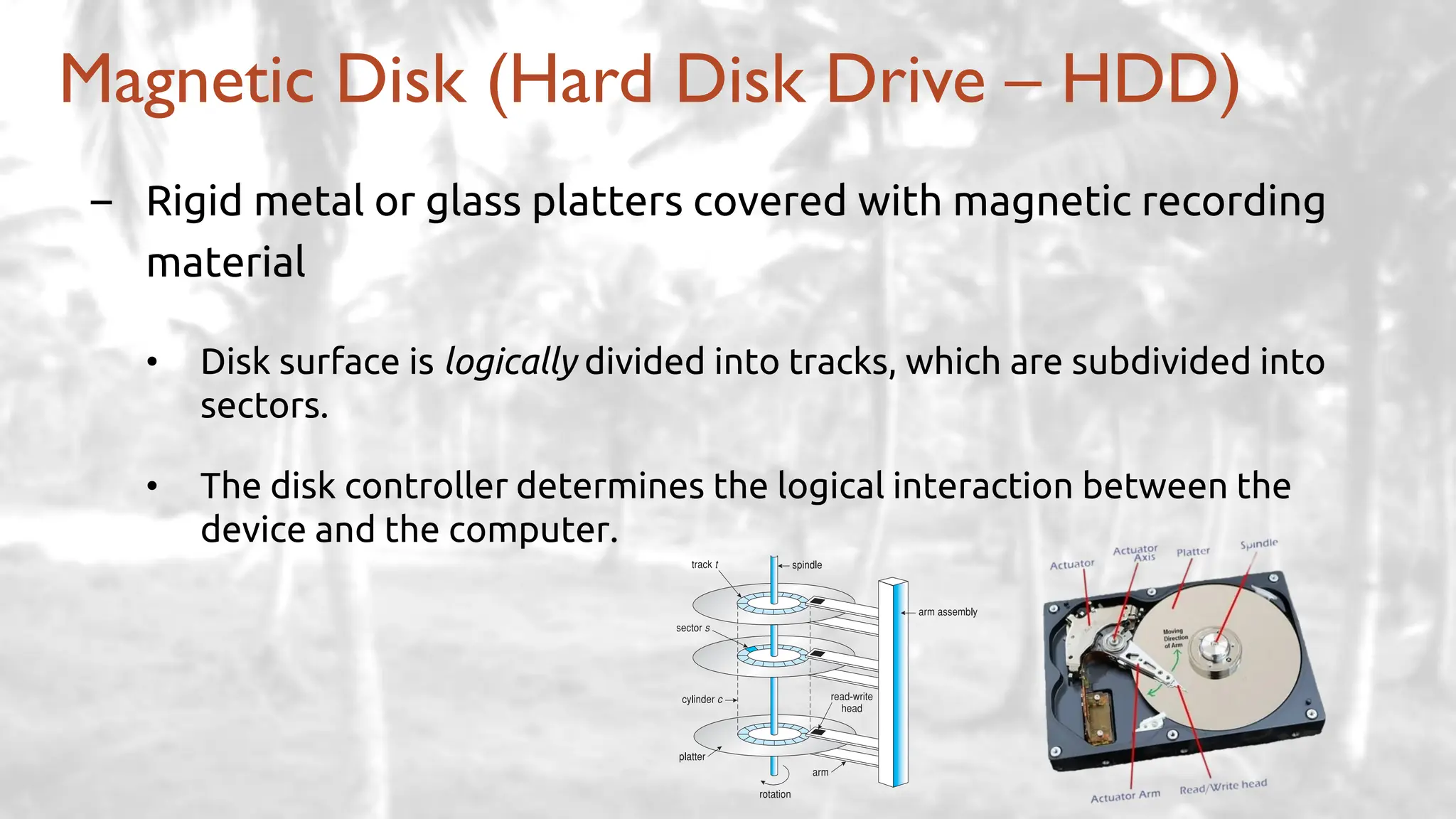
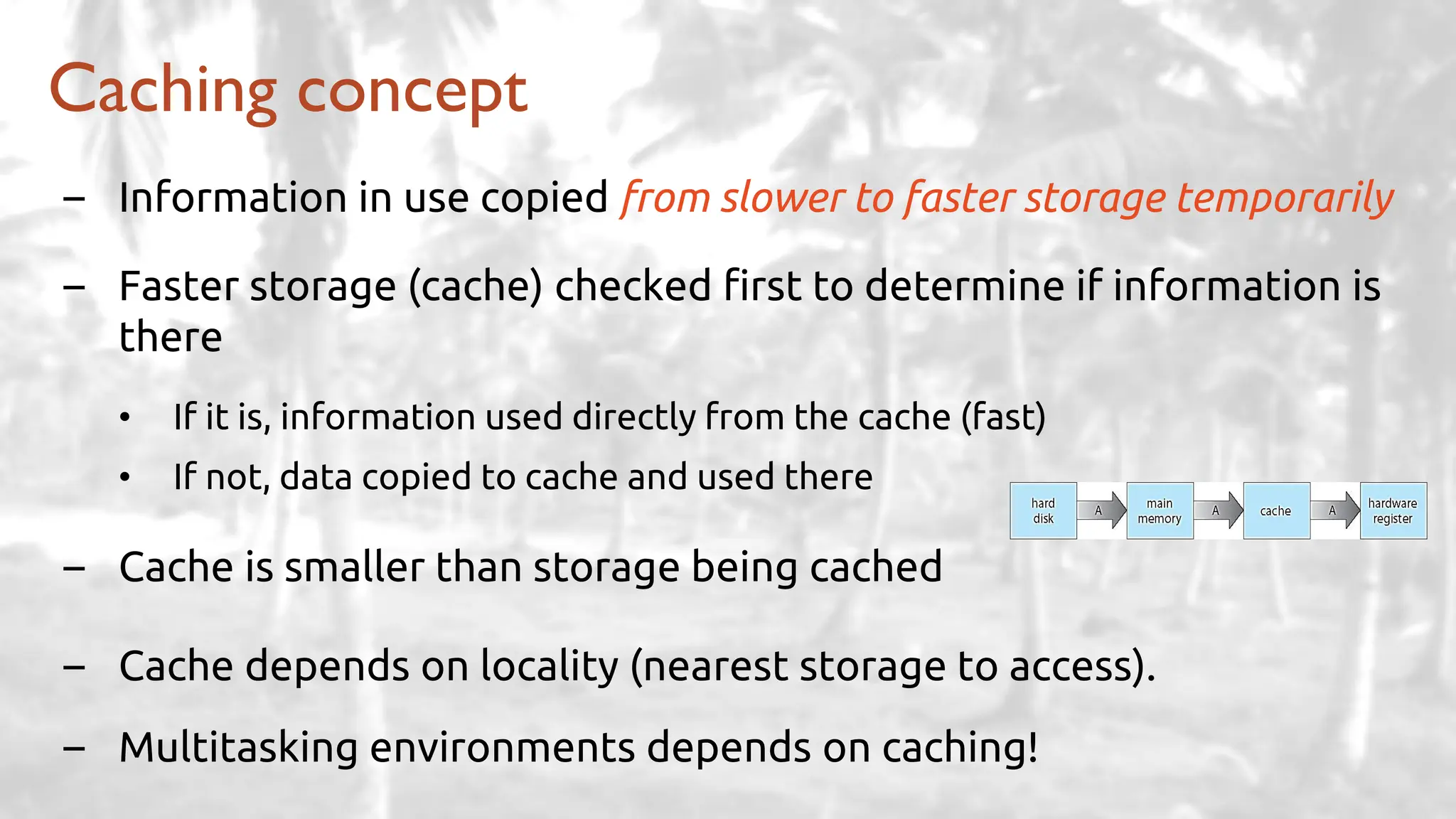
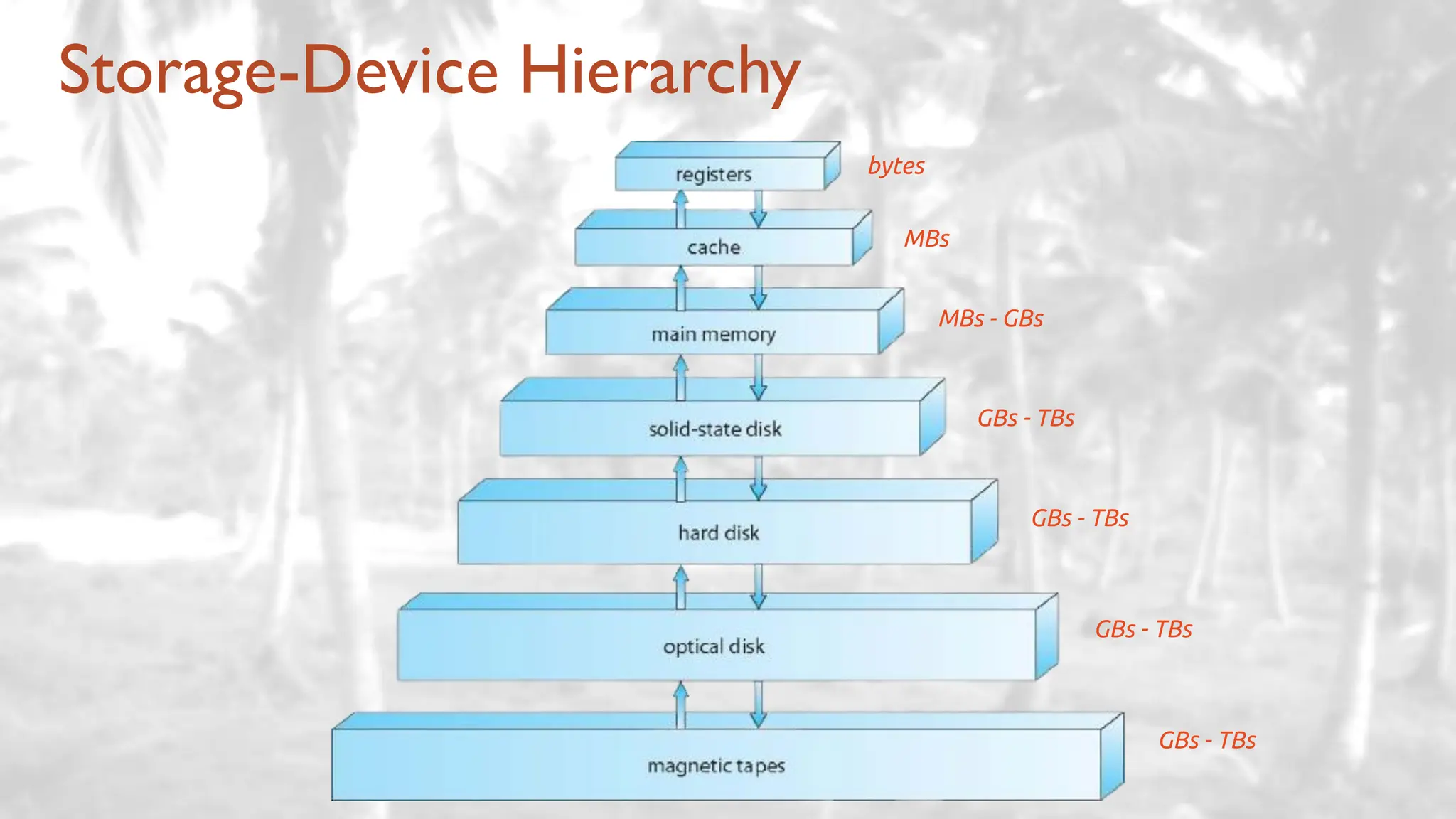
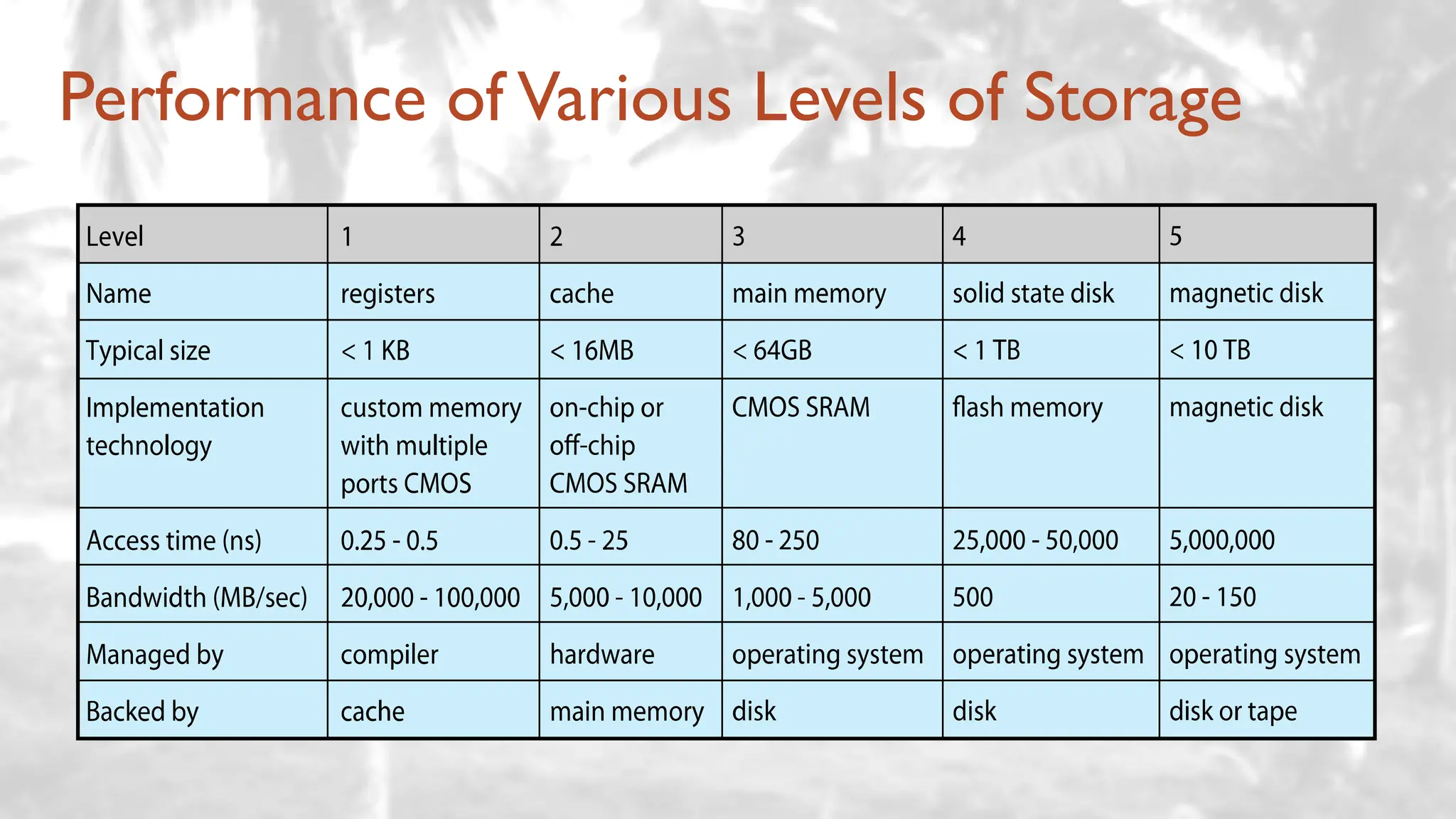
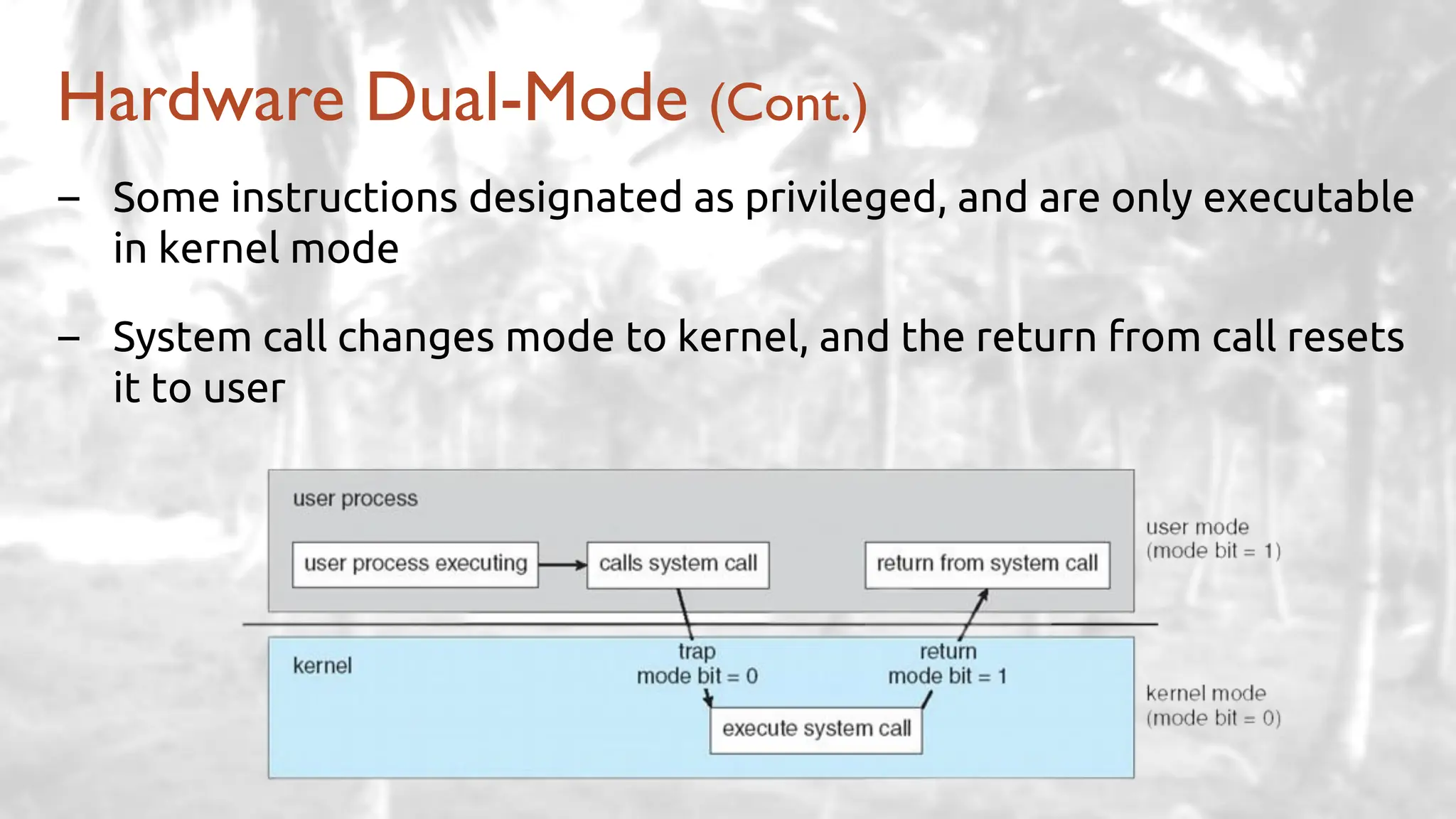
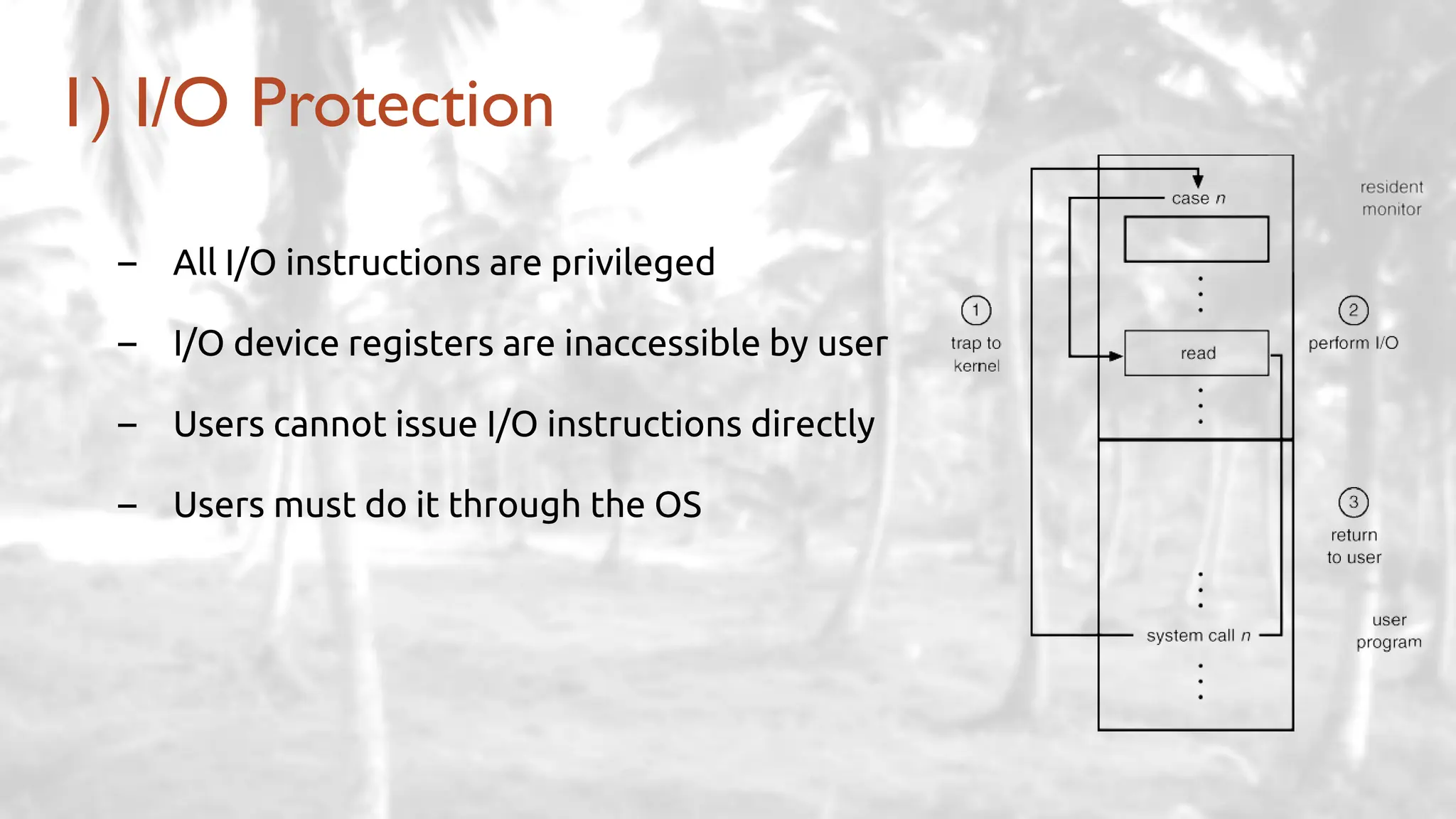
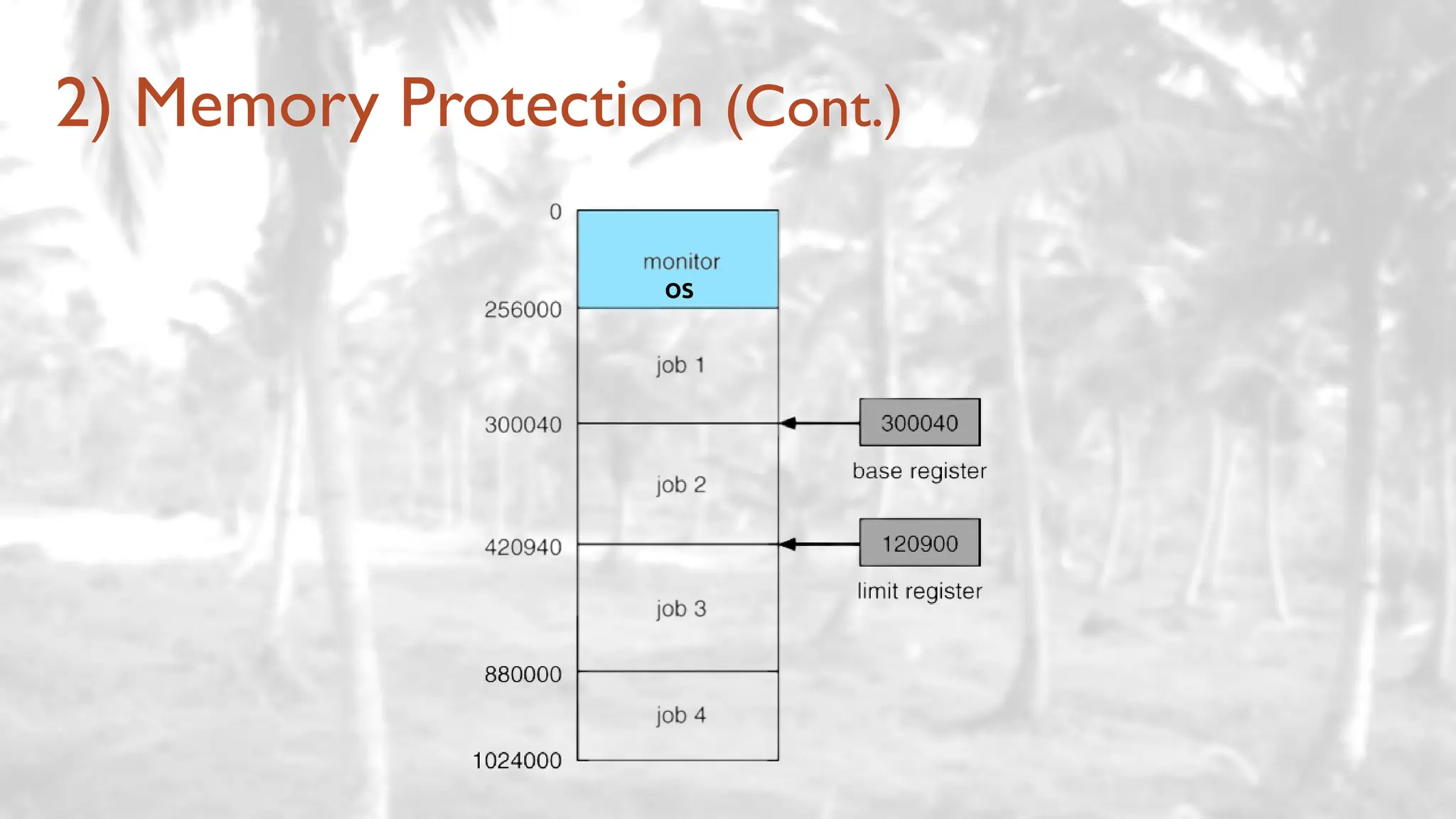
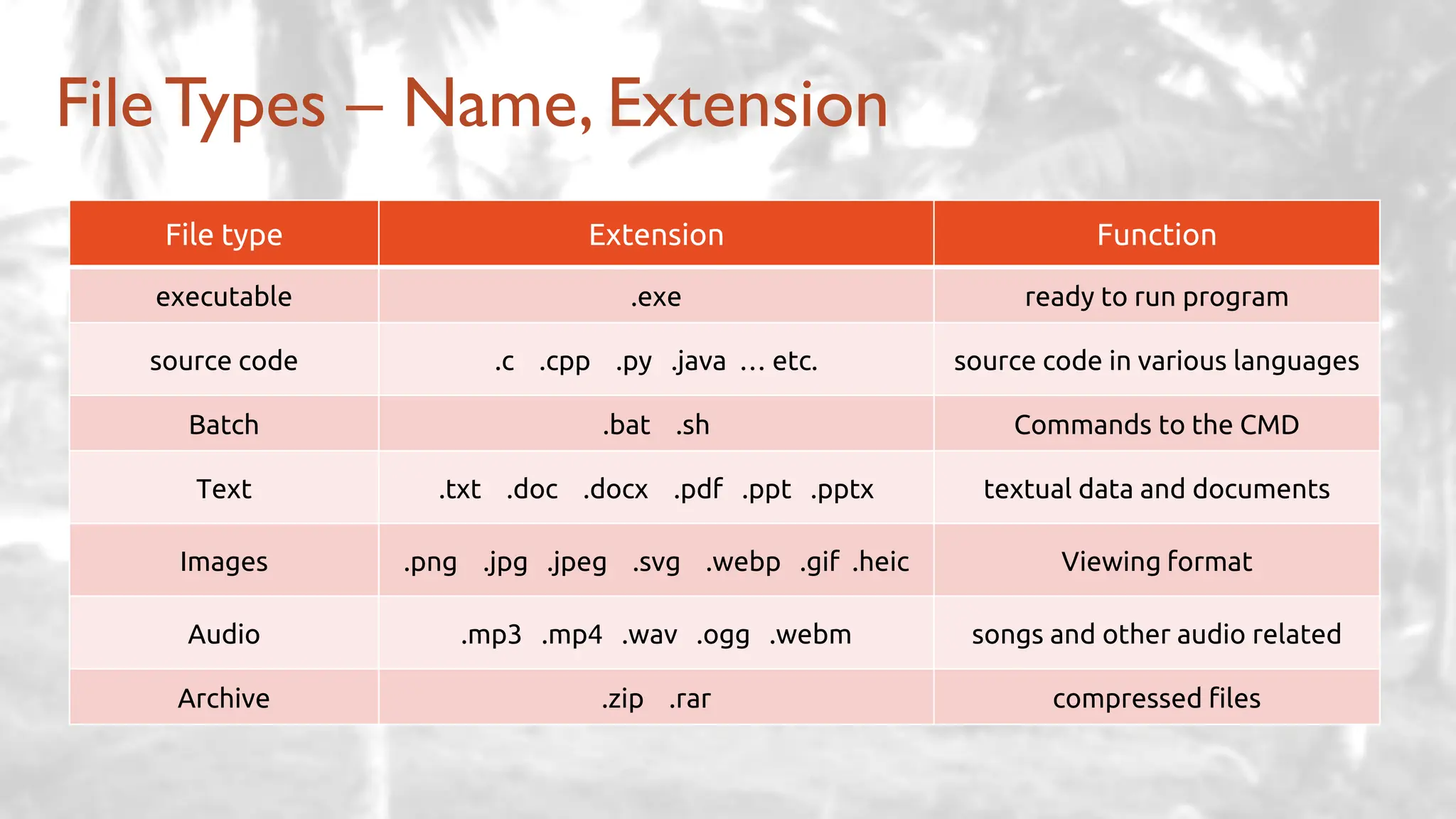
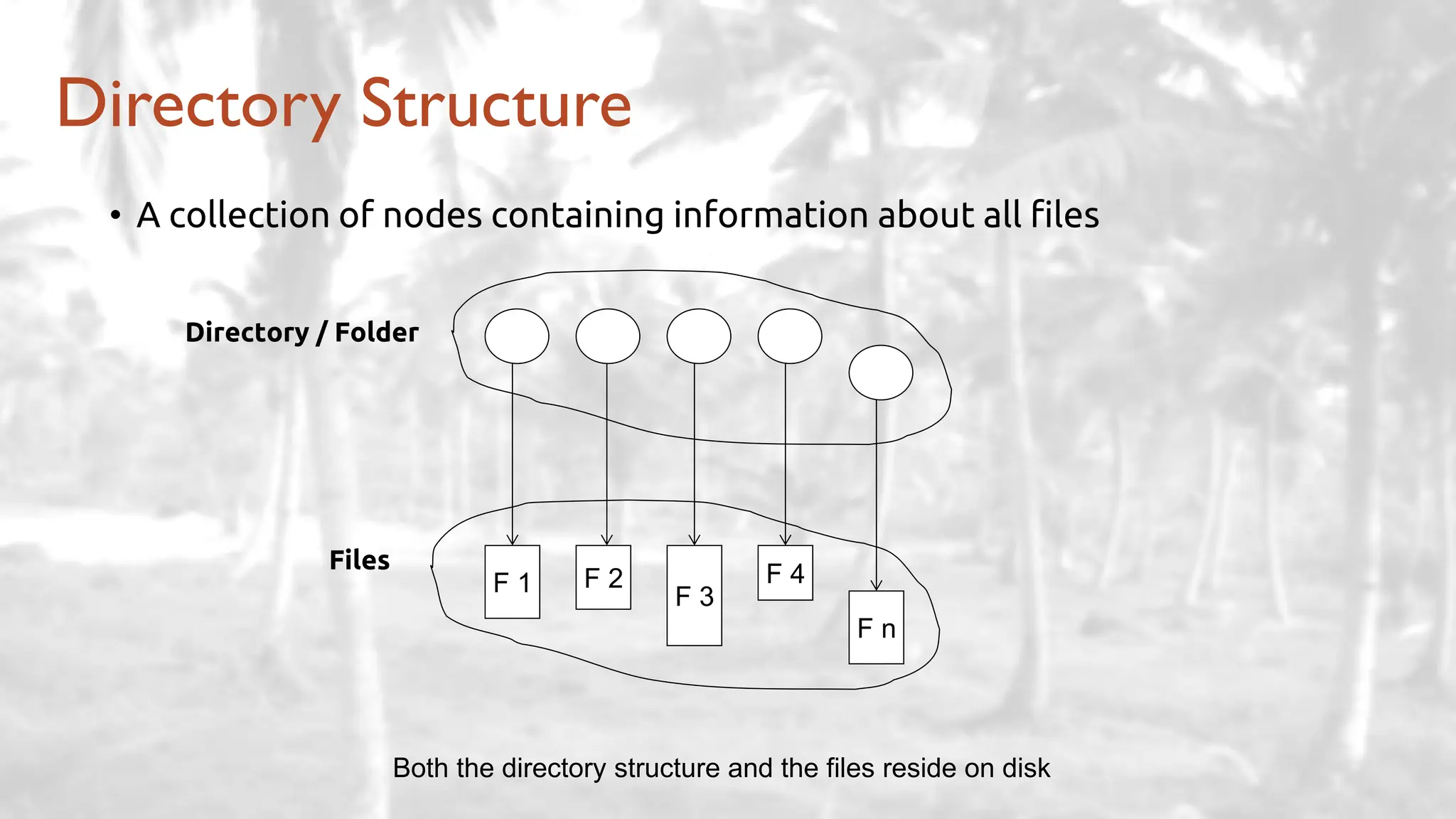
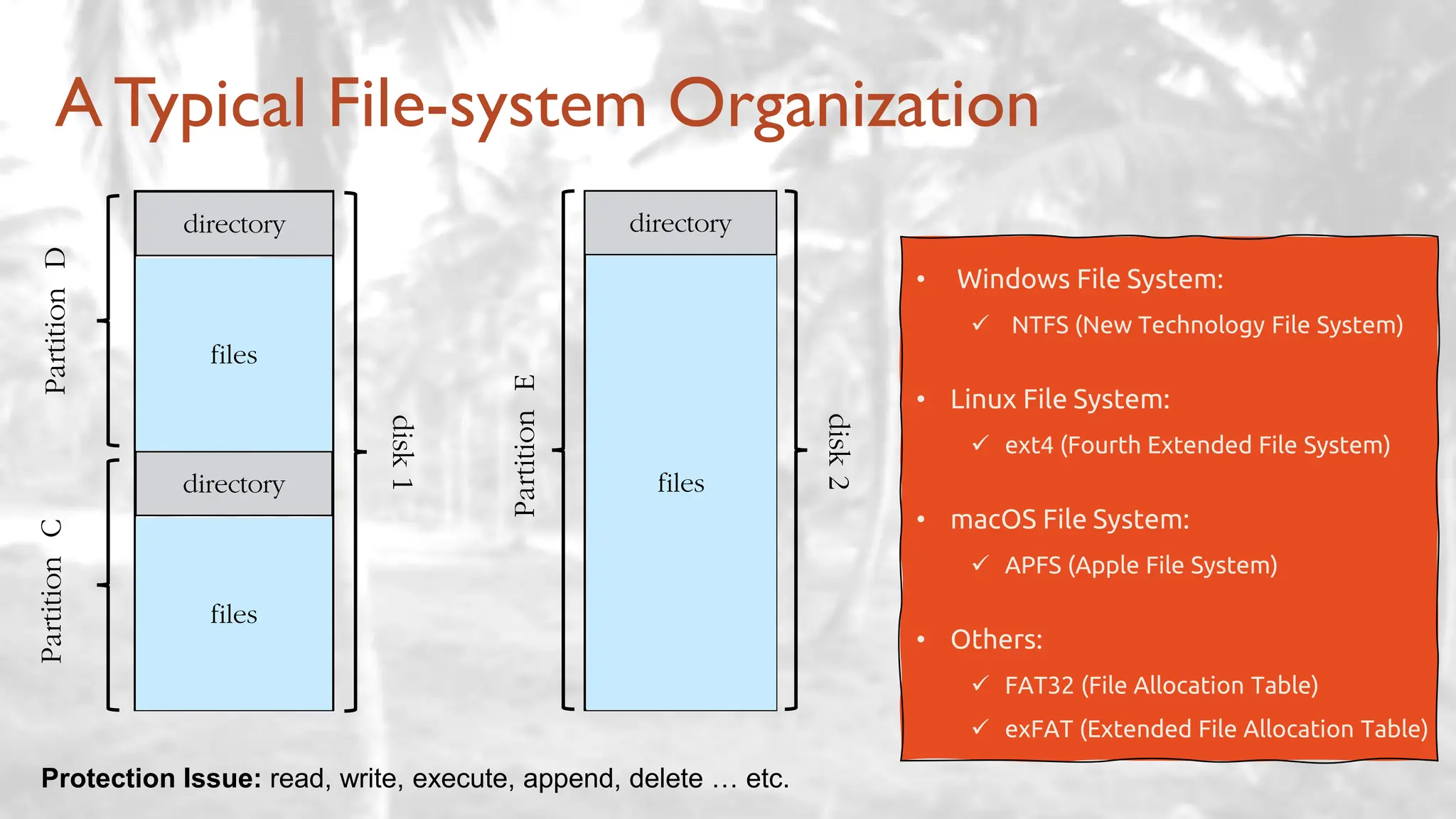
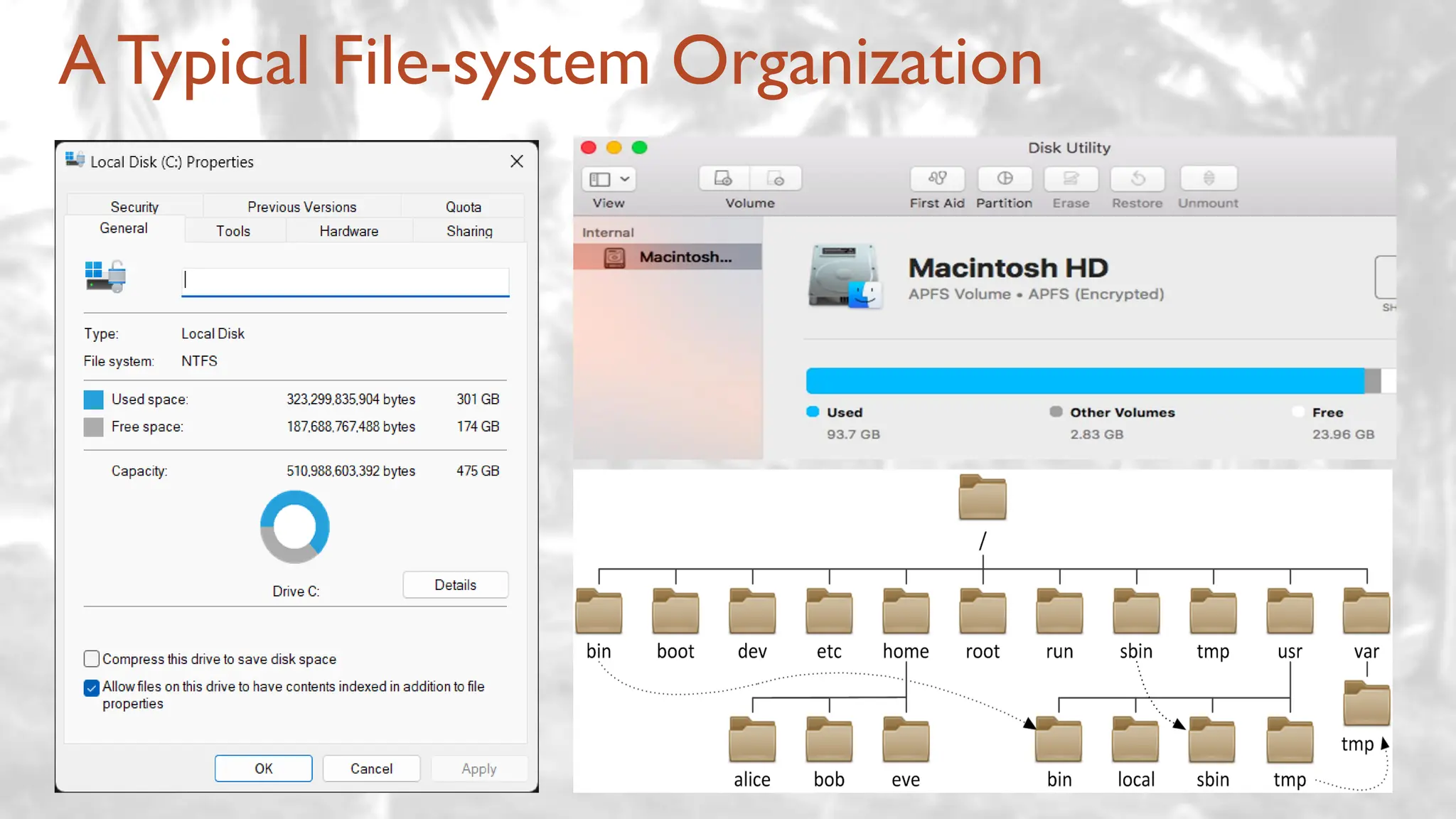
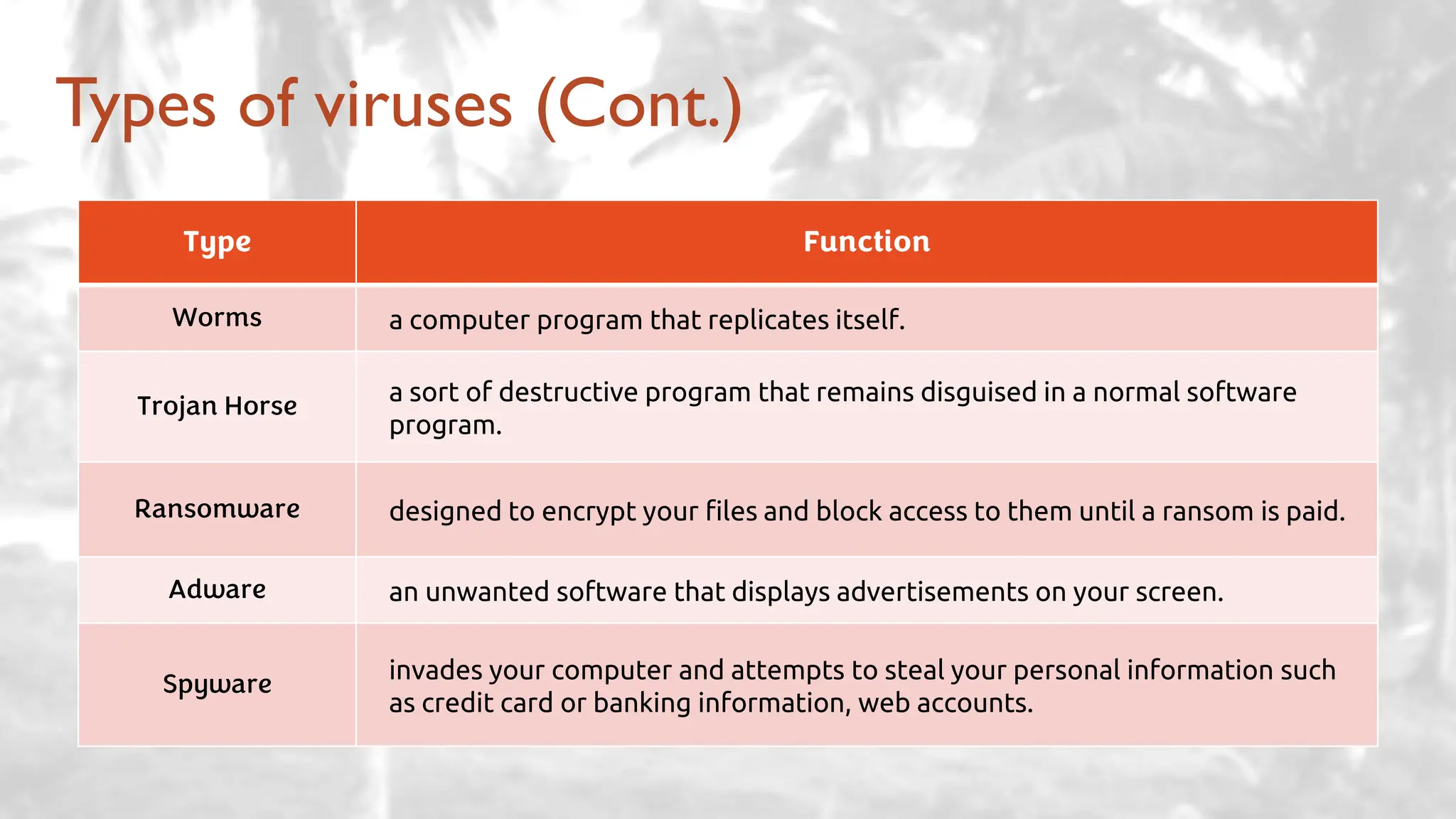
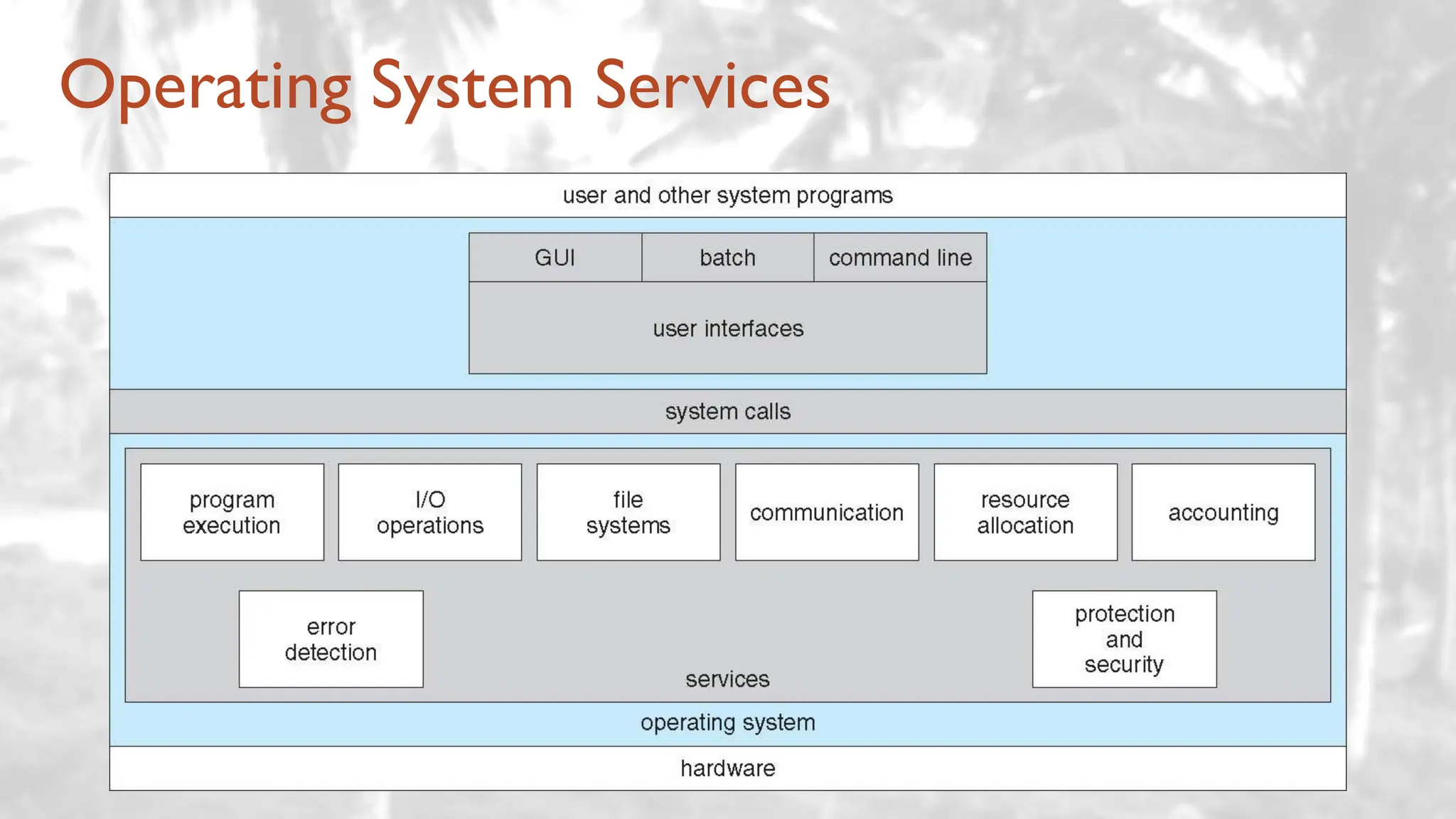
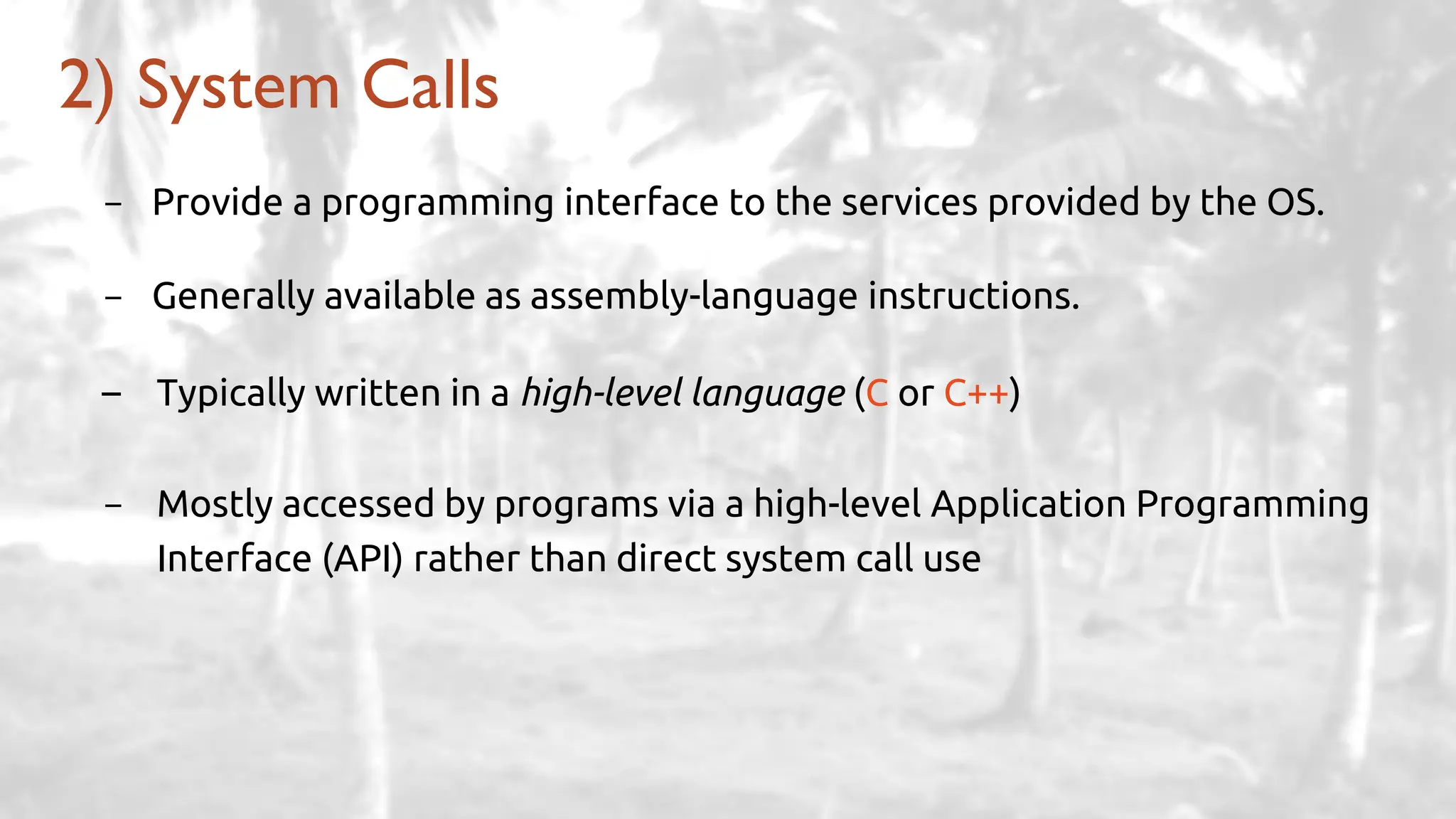
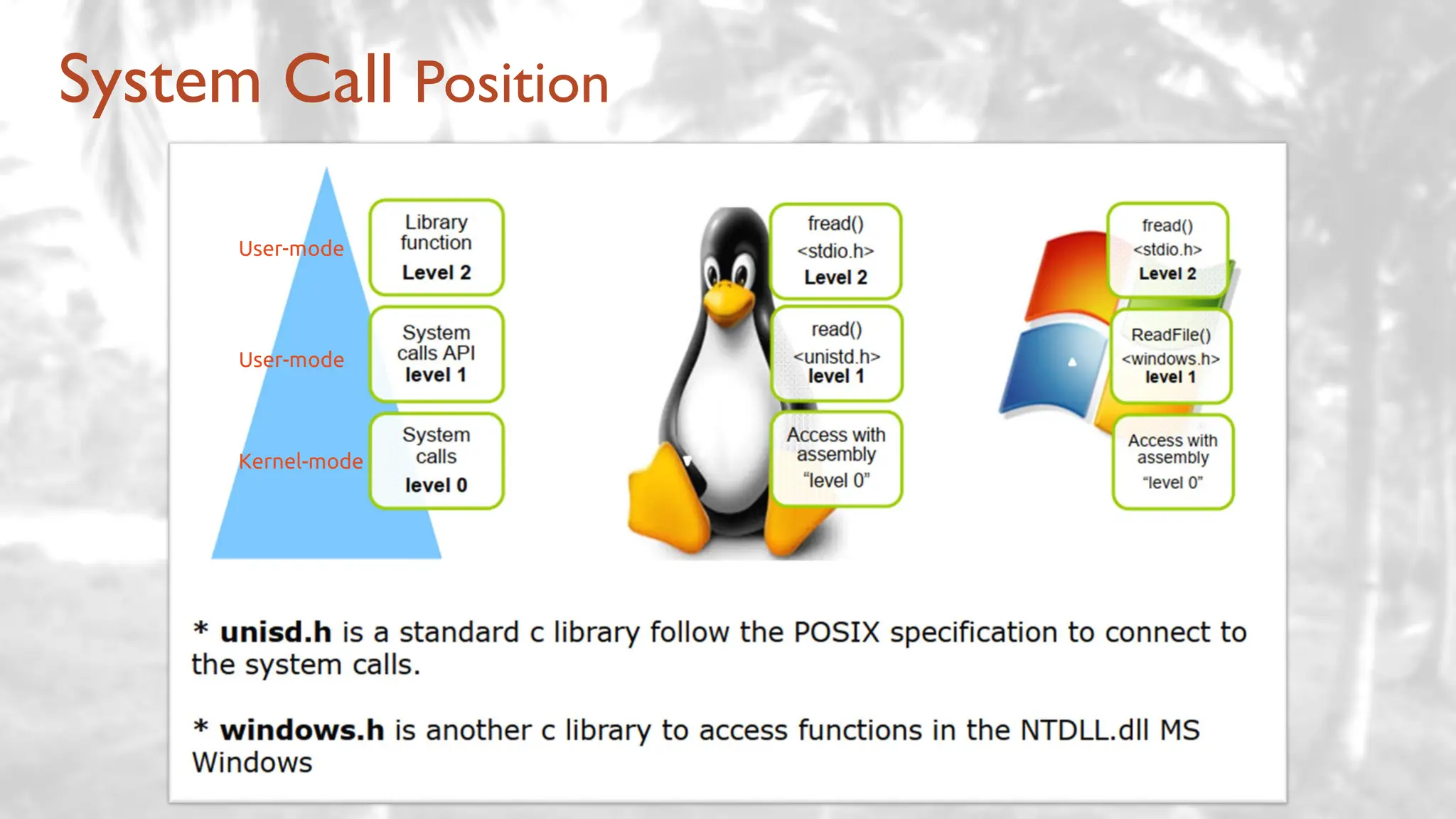
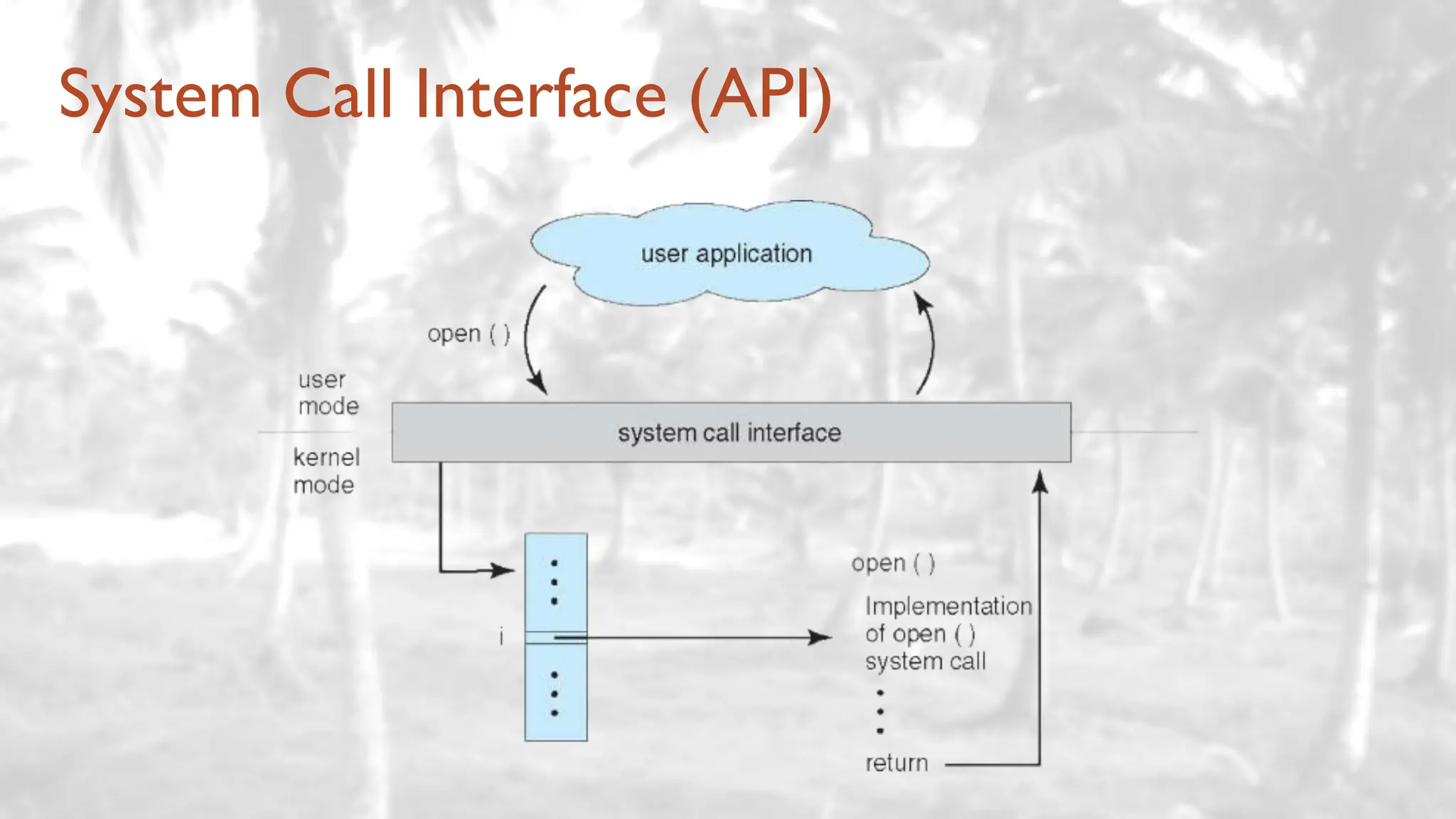
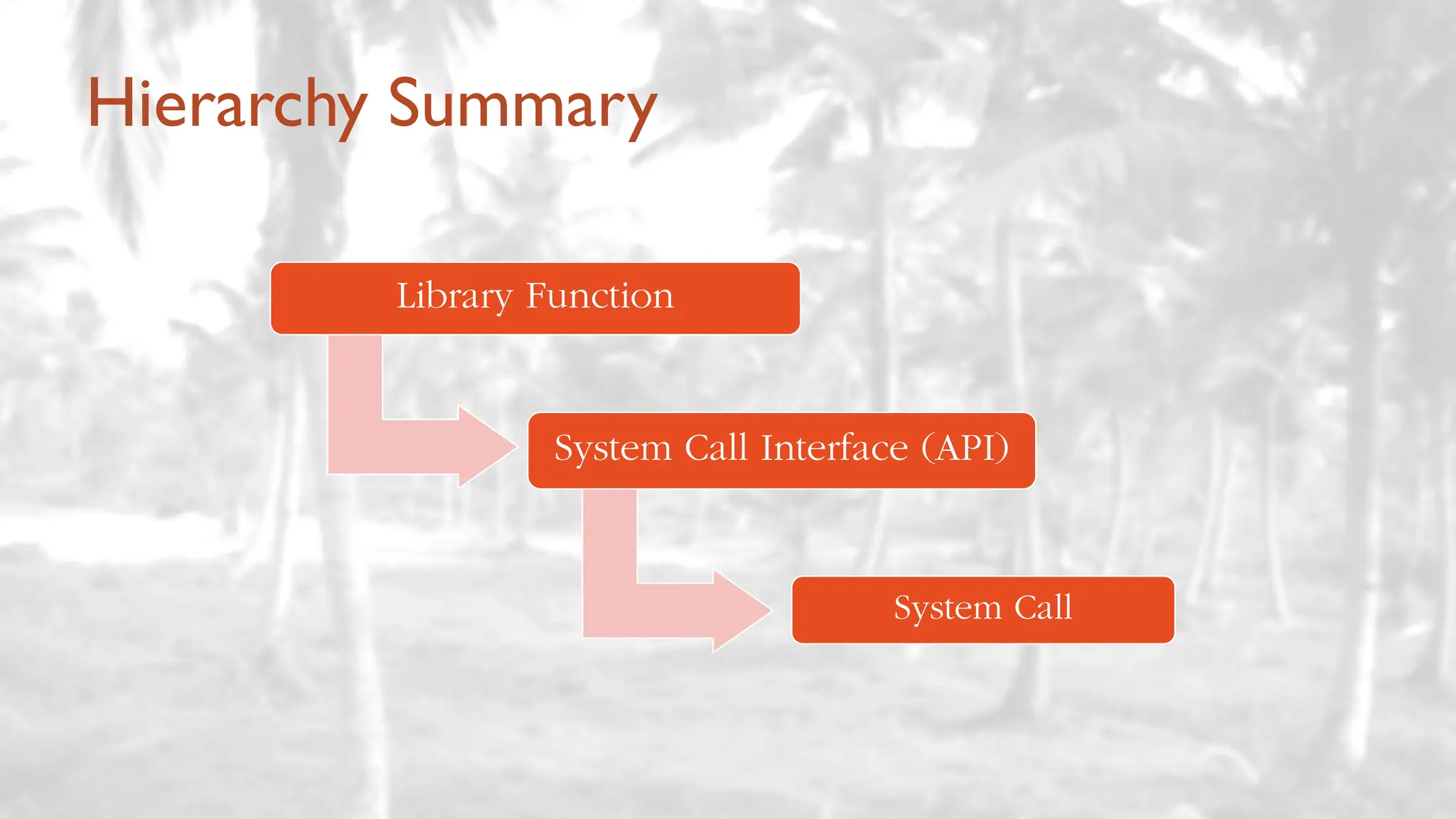
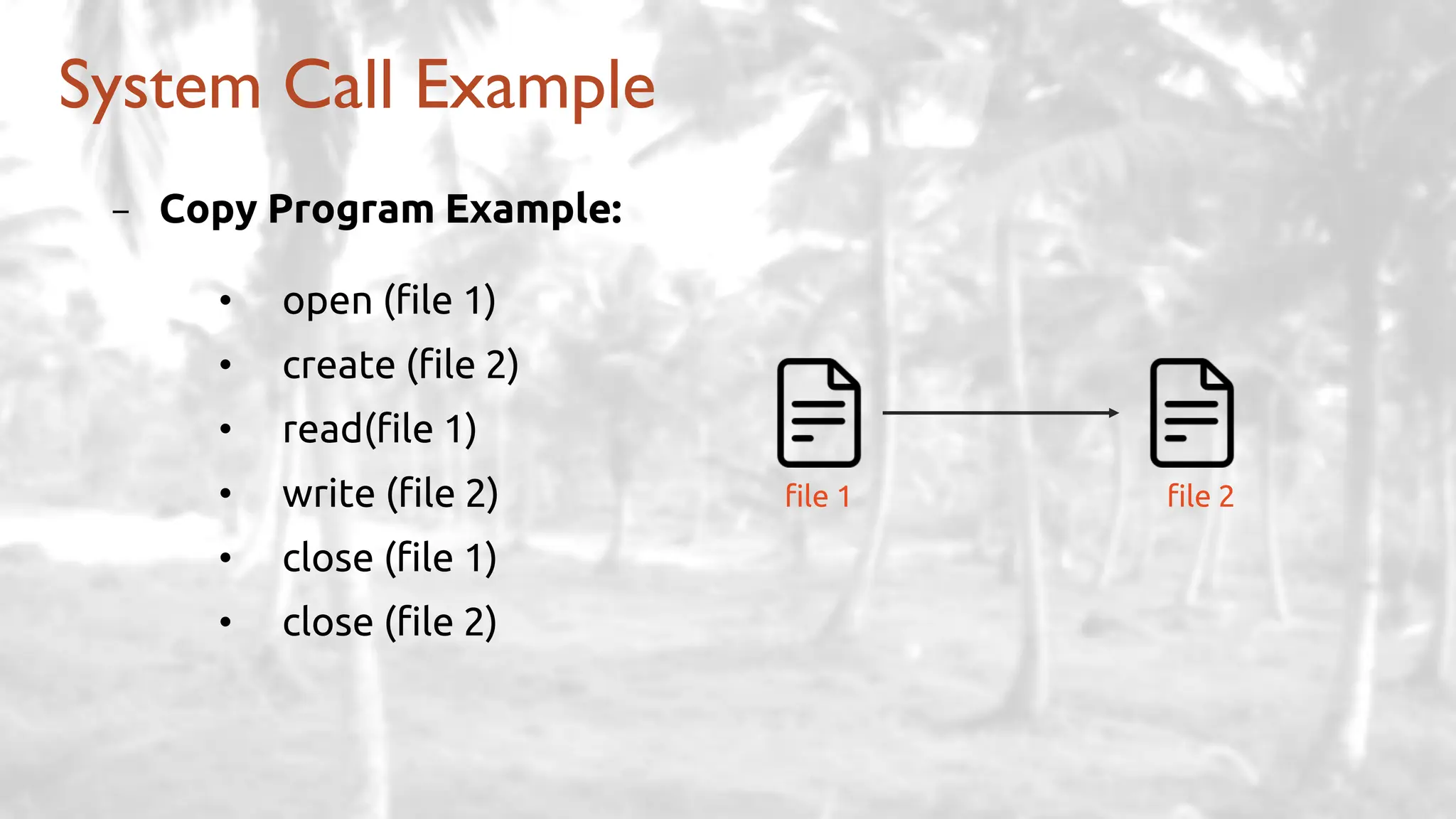
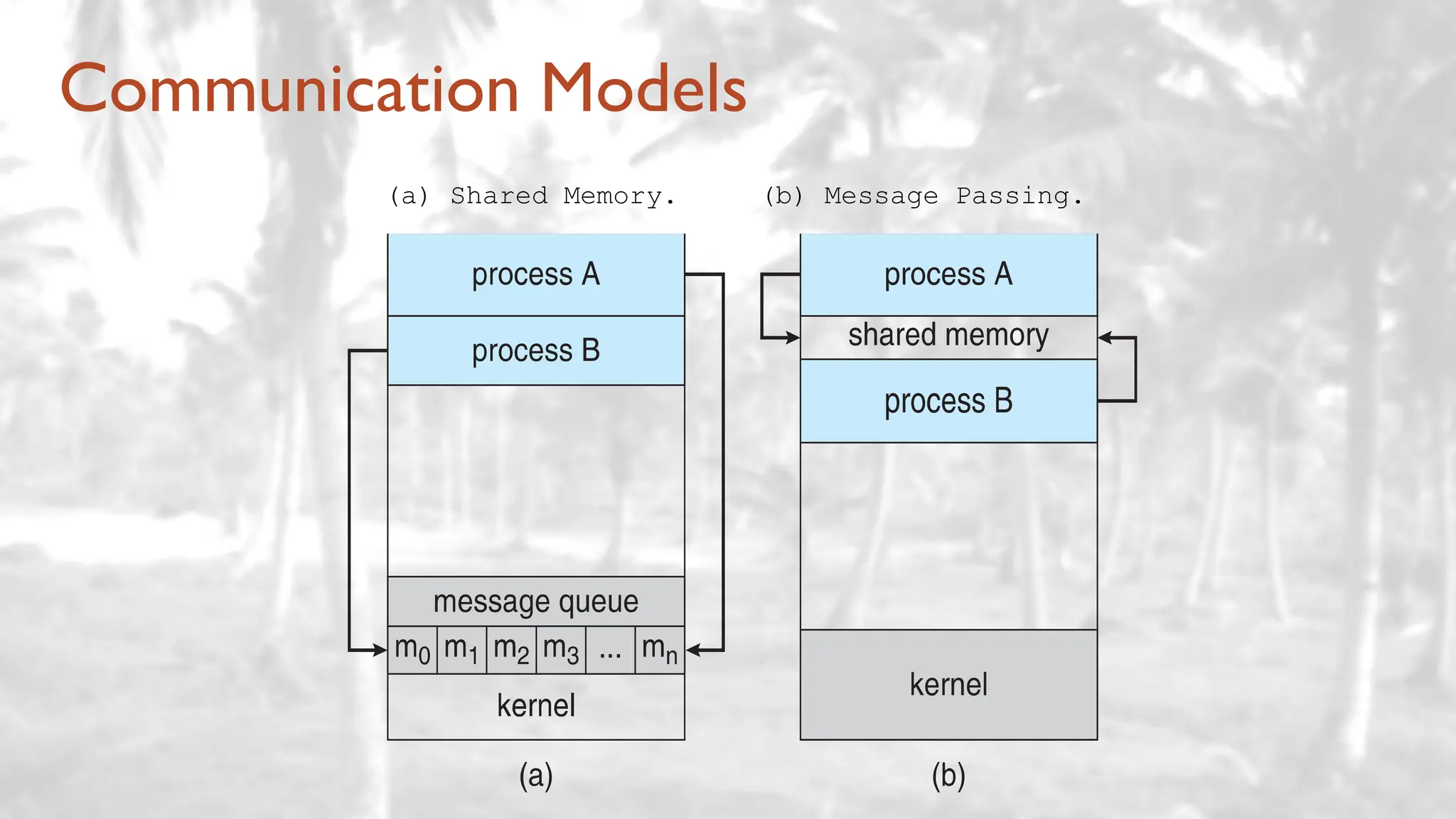
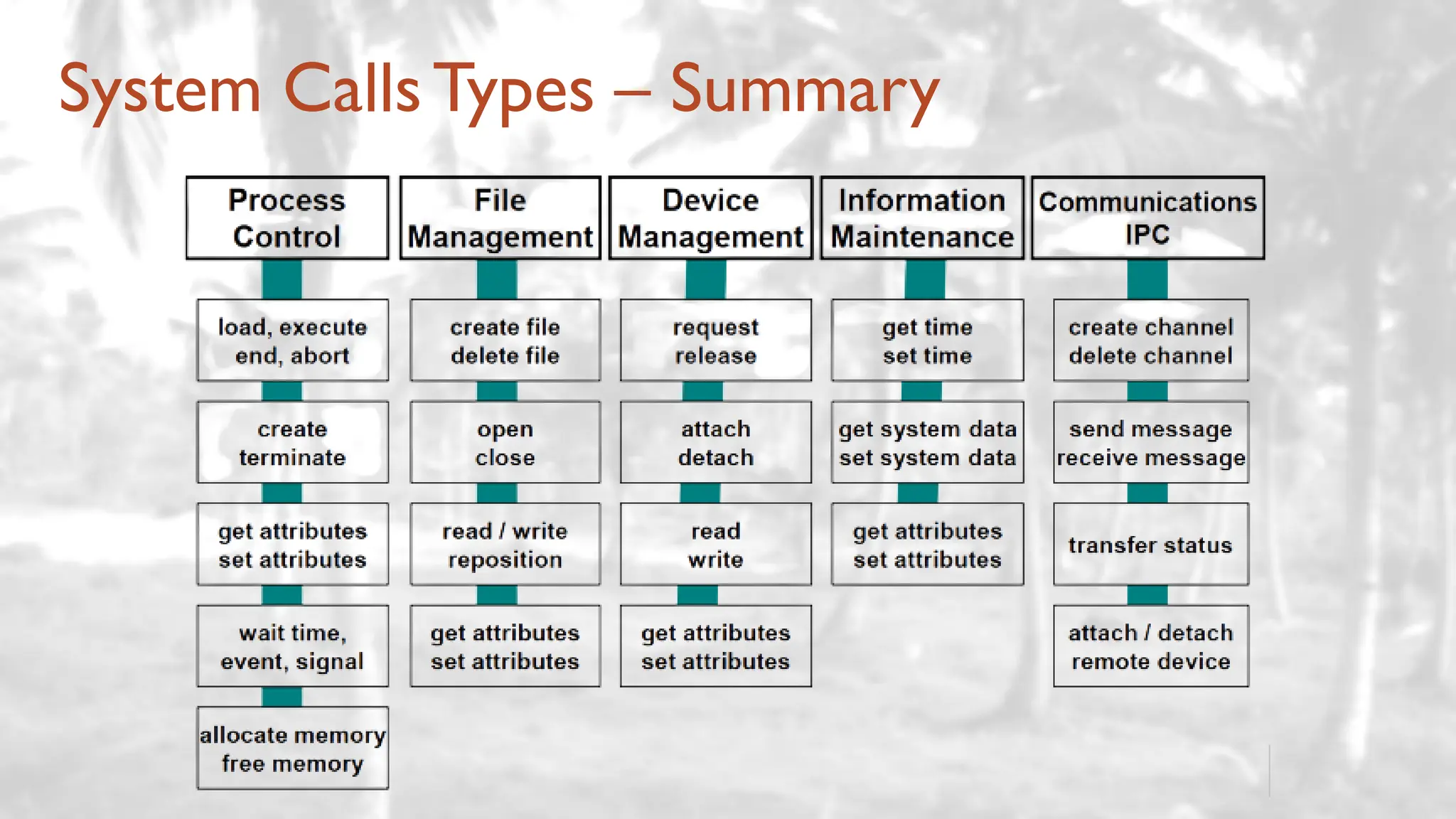
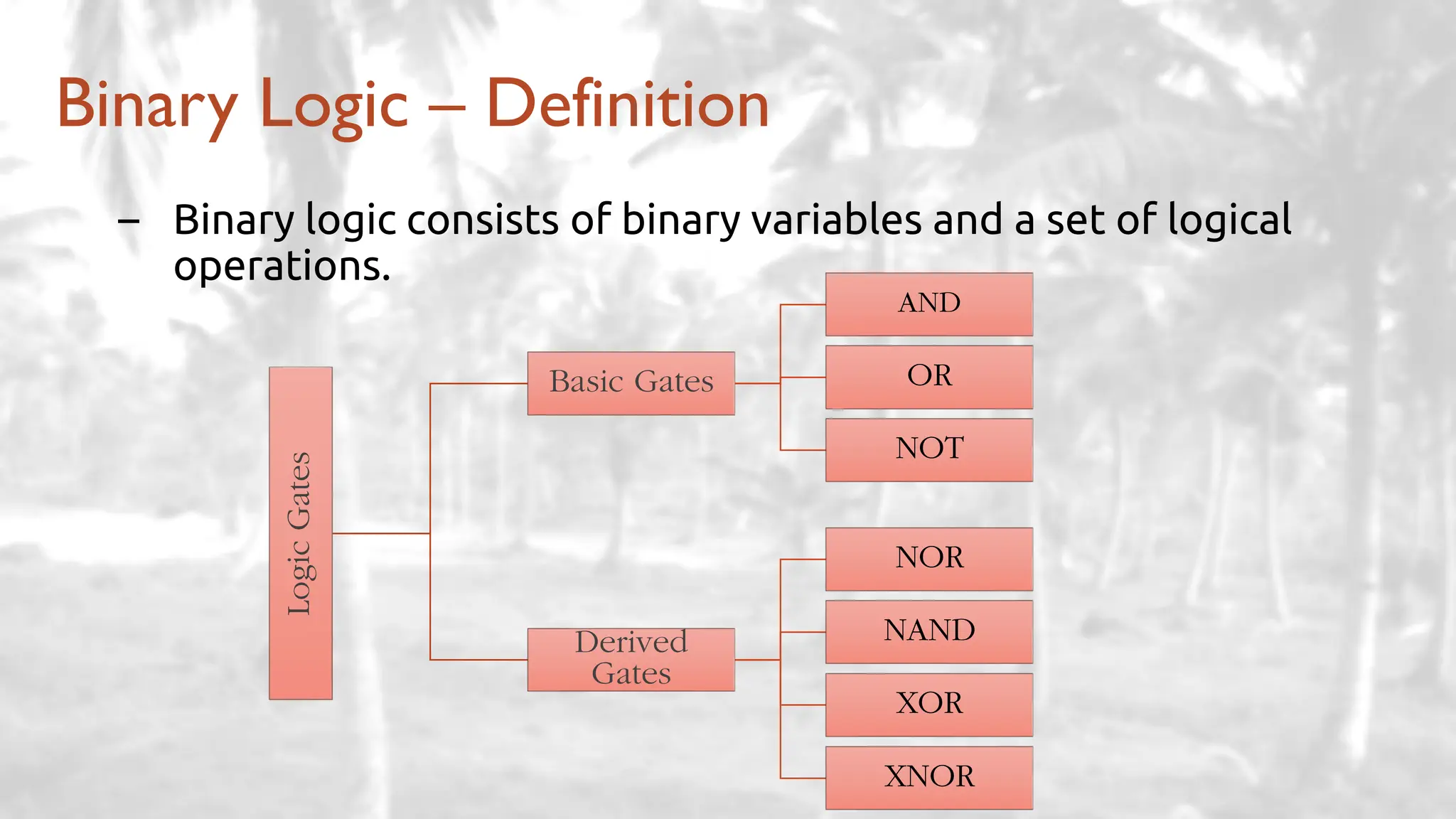
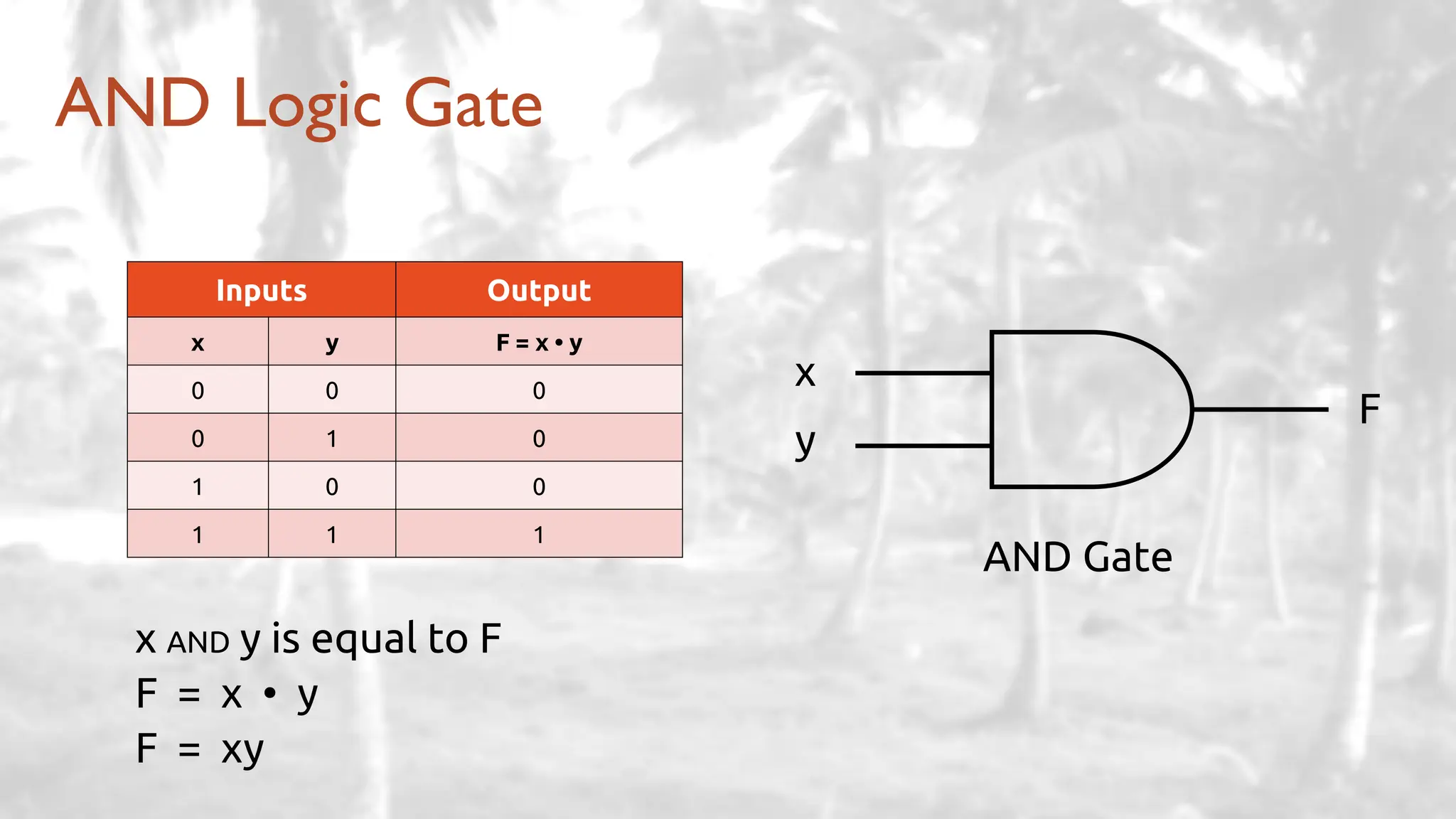
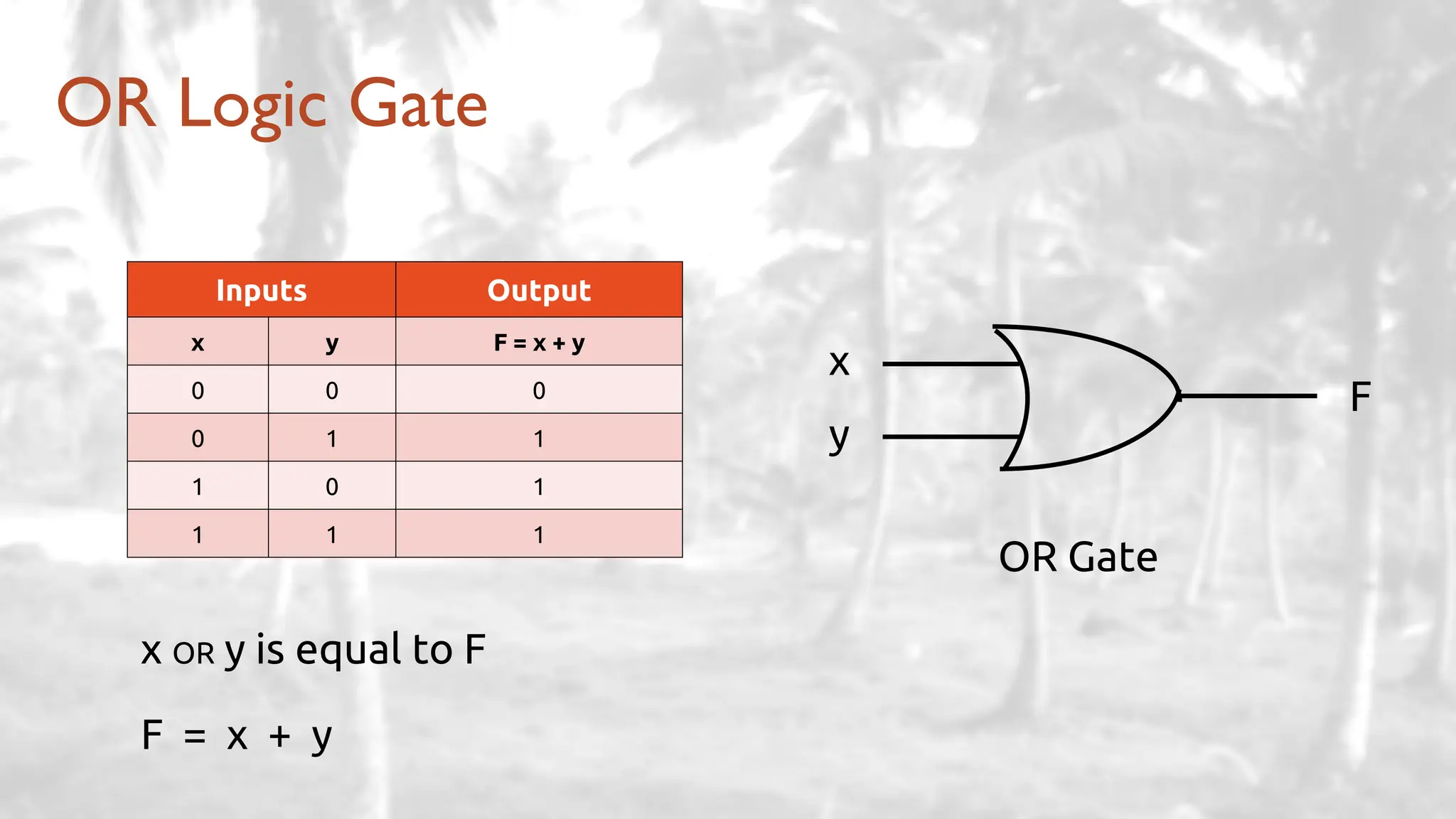
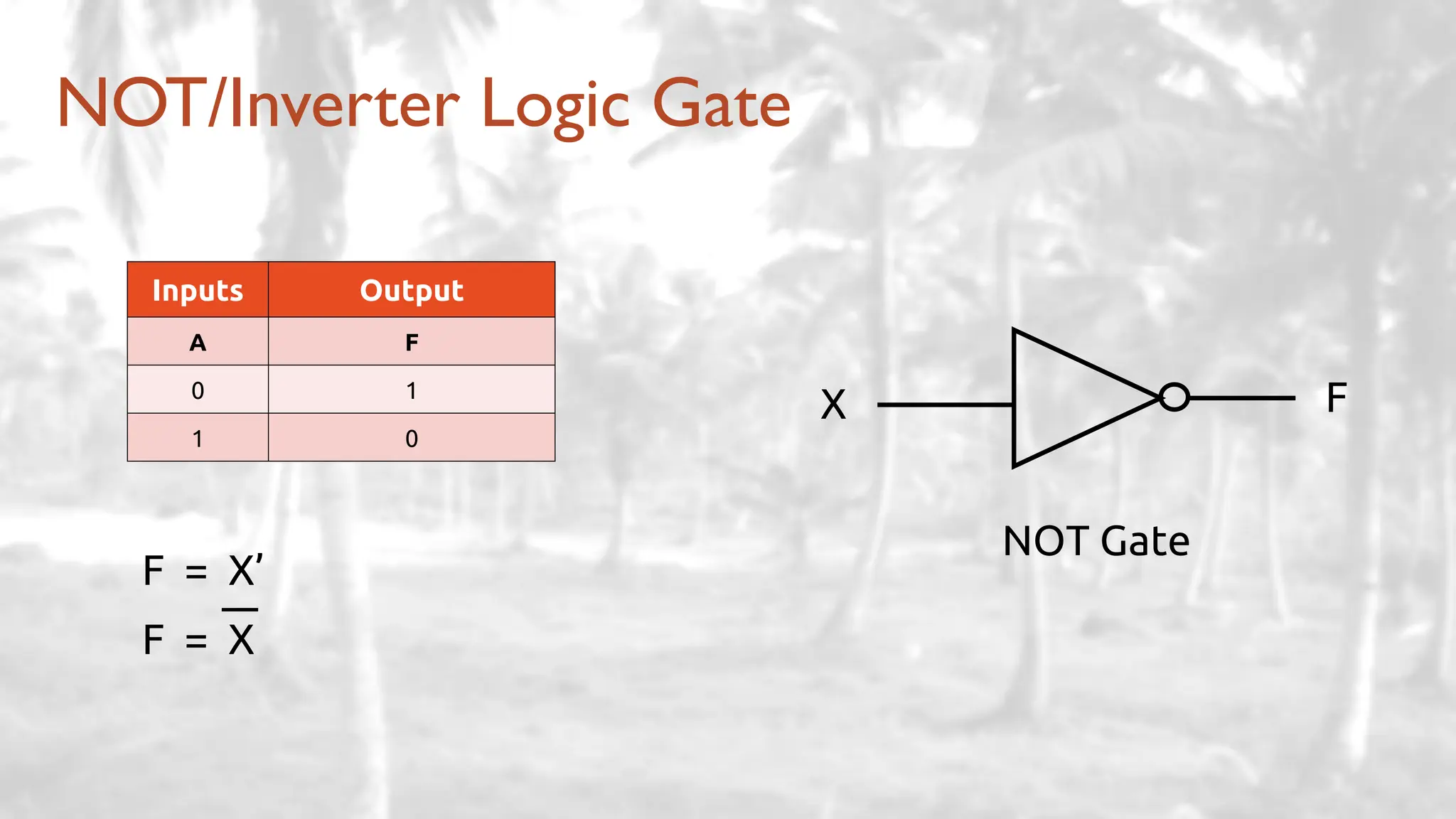
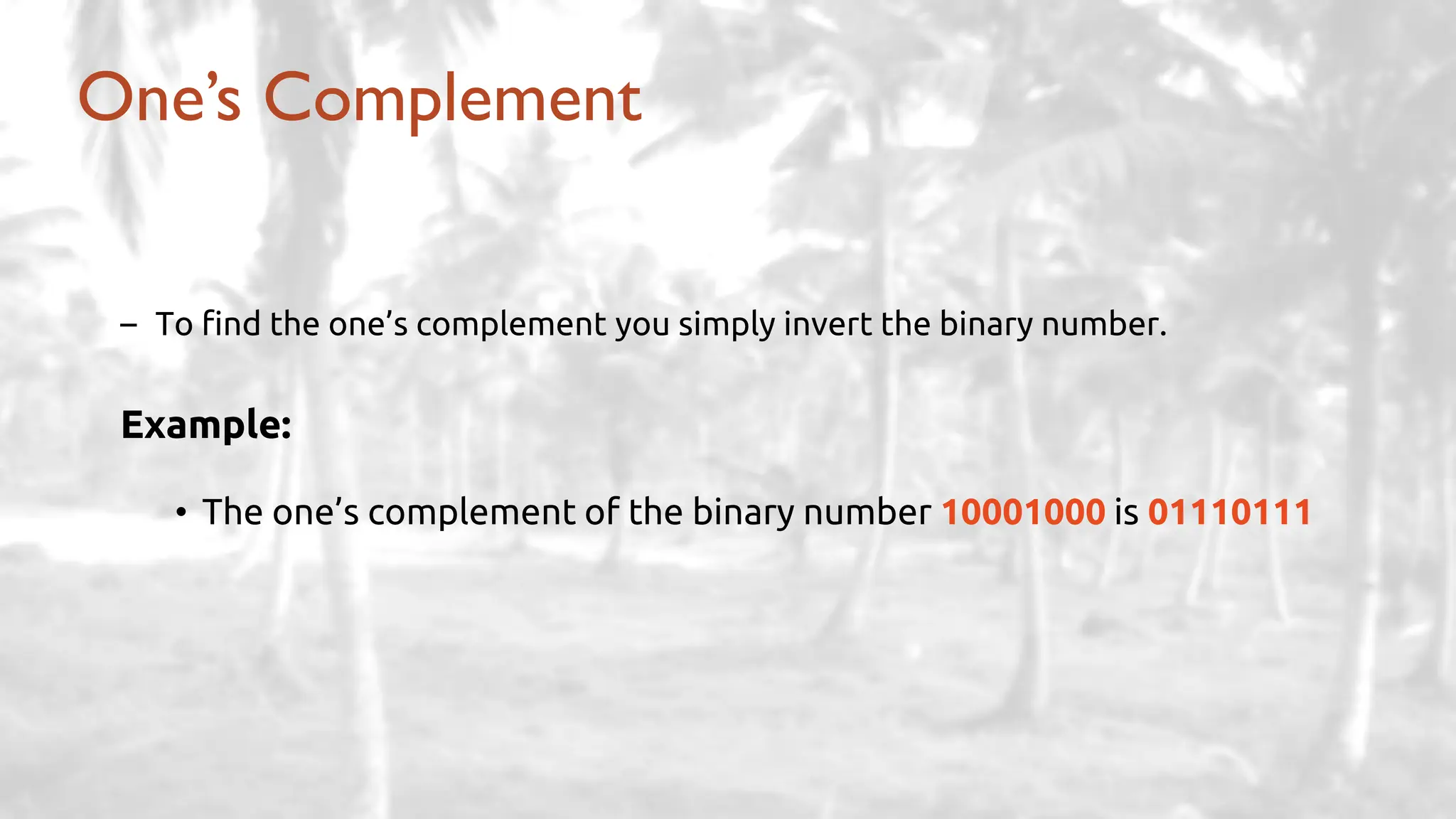
The document presents a comprehensive overview of computer system structure, detailing the role and functions of operating systems and their components, as well as the interaction between CPU, memory, and I/O devices. It covers topics such as interrupts, multi-tasking, various storage types, memory protection, and system calls, alongside file management and user interfaces. Additionally, it introduces binary logic concepts and provides an introduction to types of system files and viruses, alongside their protective measures.