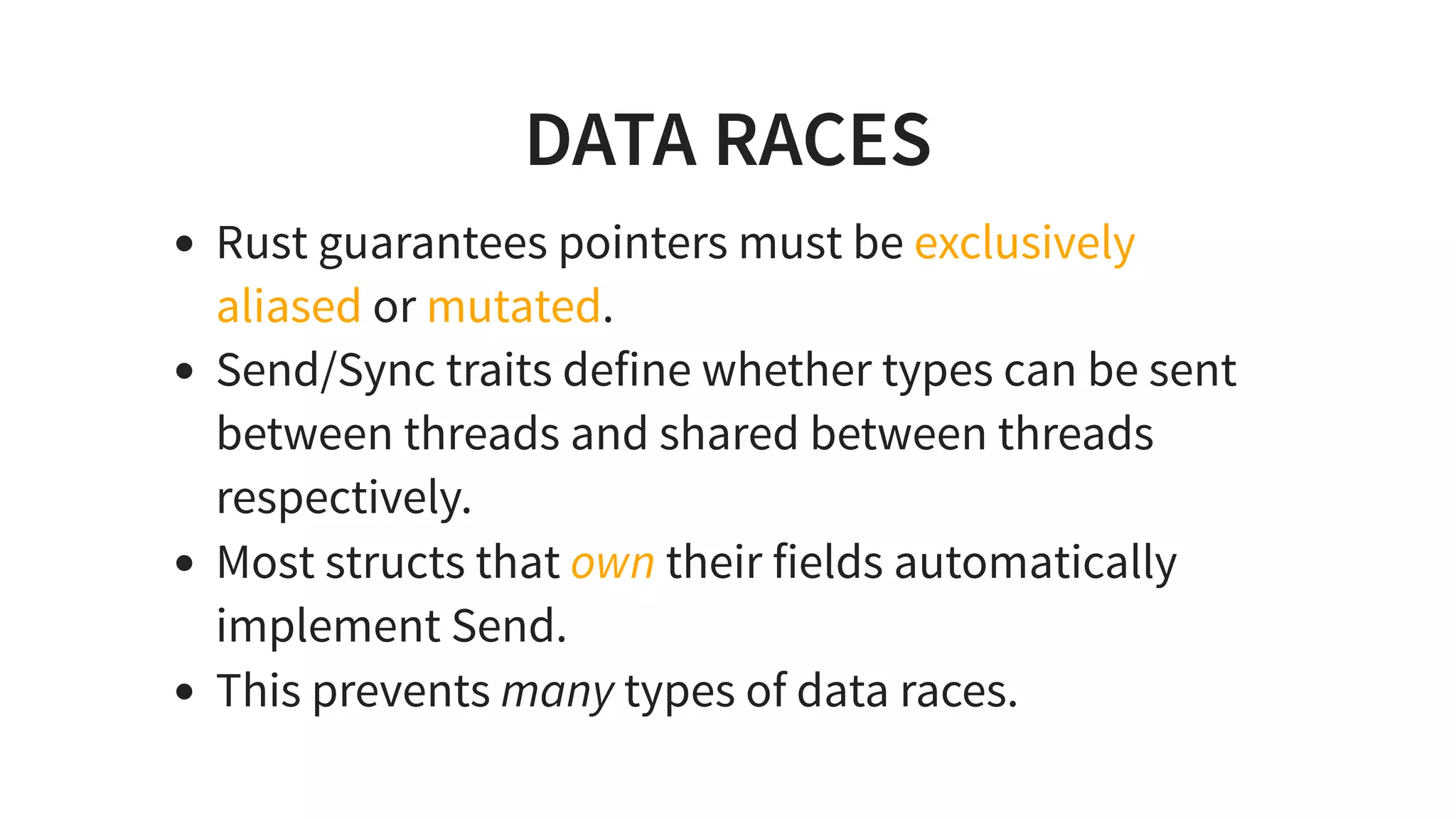
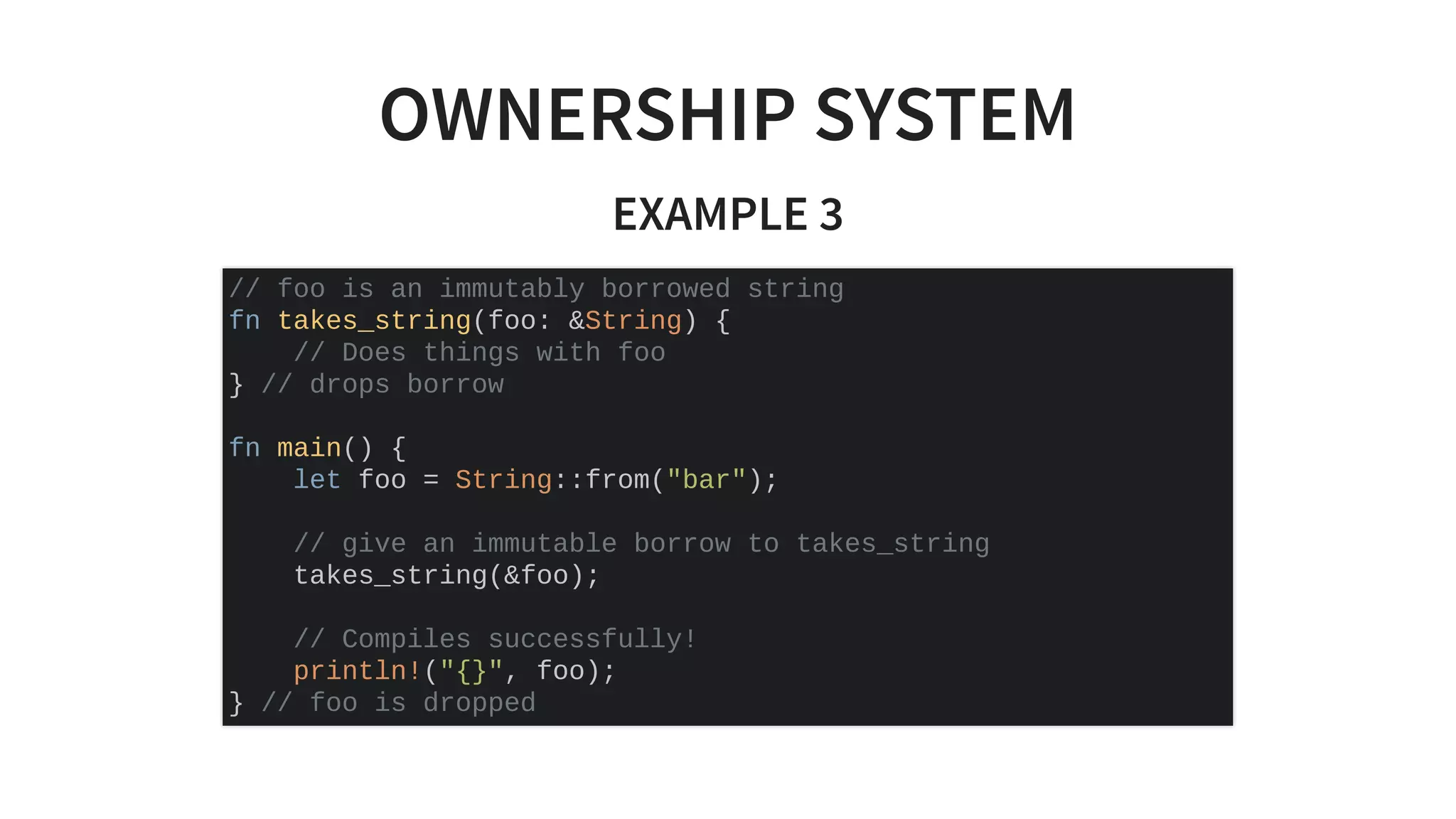
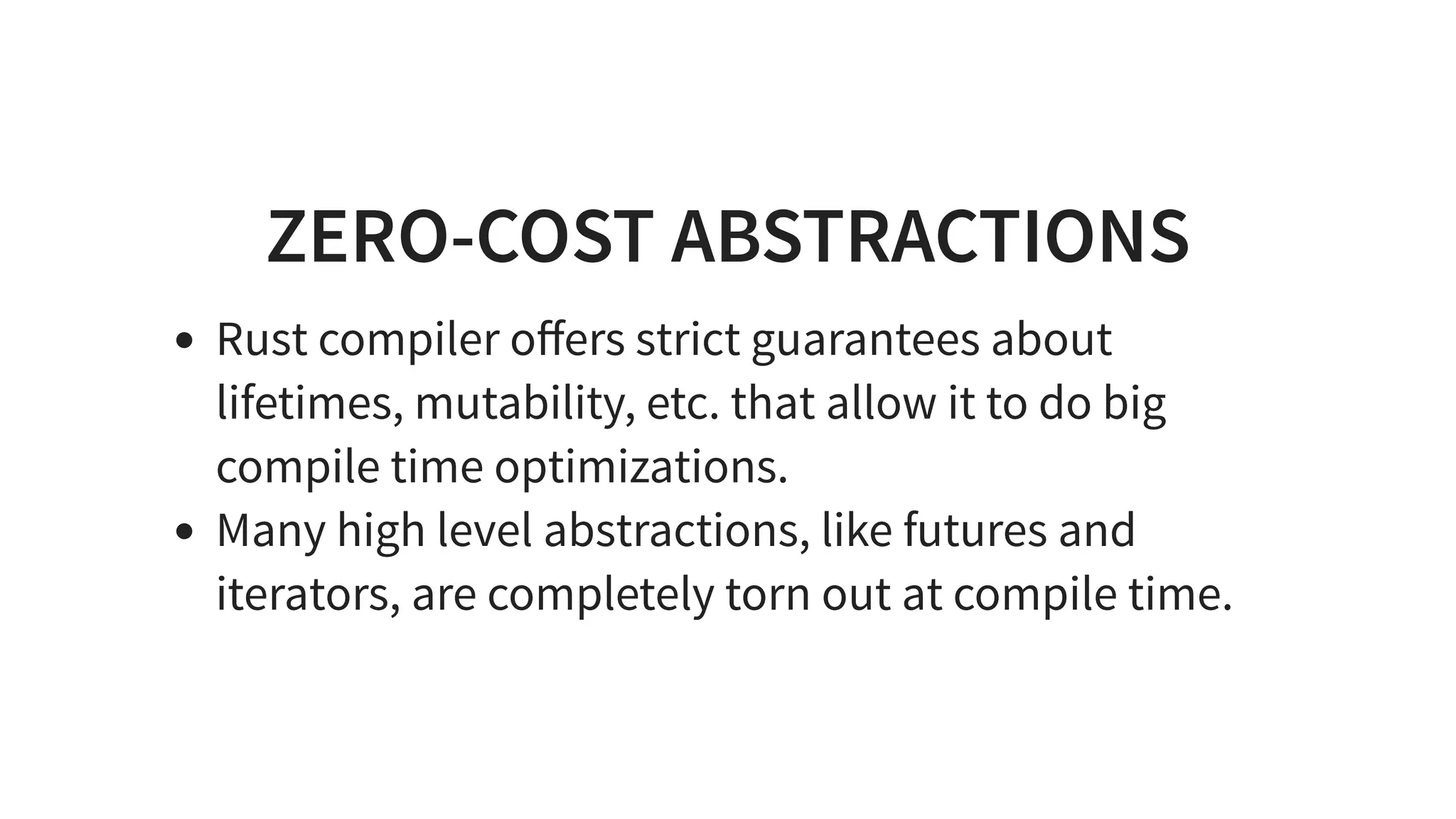
This document introduces Rust by providing a brief history, overview of what Rust is, when it is useful, key features like safety guarantees and the ownership system, and examples of using Rust in different contexts like Python integration. Rust was created at Mozilla in 2006 to improve Firefox performance and safety. It focuses on safety, performance, concurrency through features like eliminating data races and memory safety without garbage collection. Rust is useful when high performance is needed like C but without vulnerabilities, and for applications with high costs of failure.
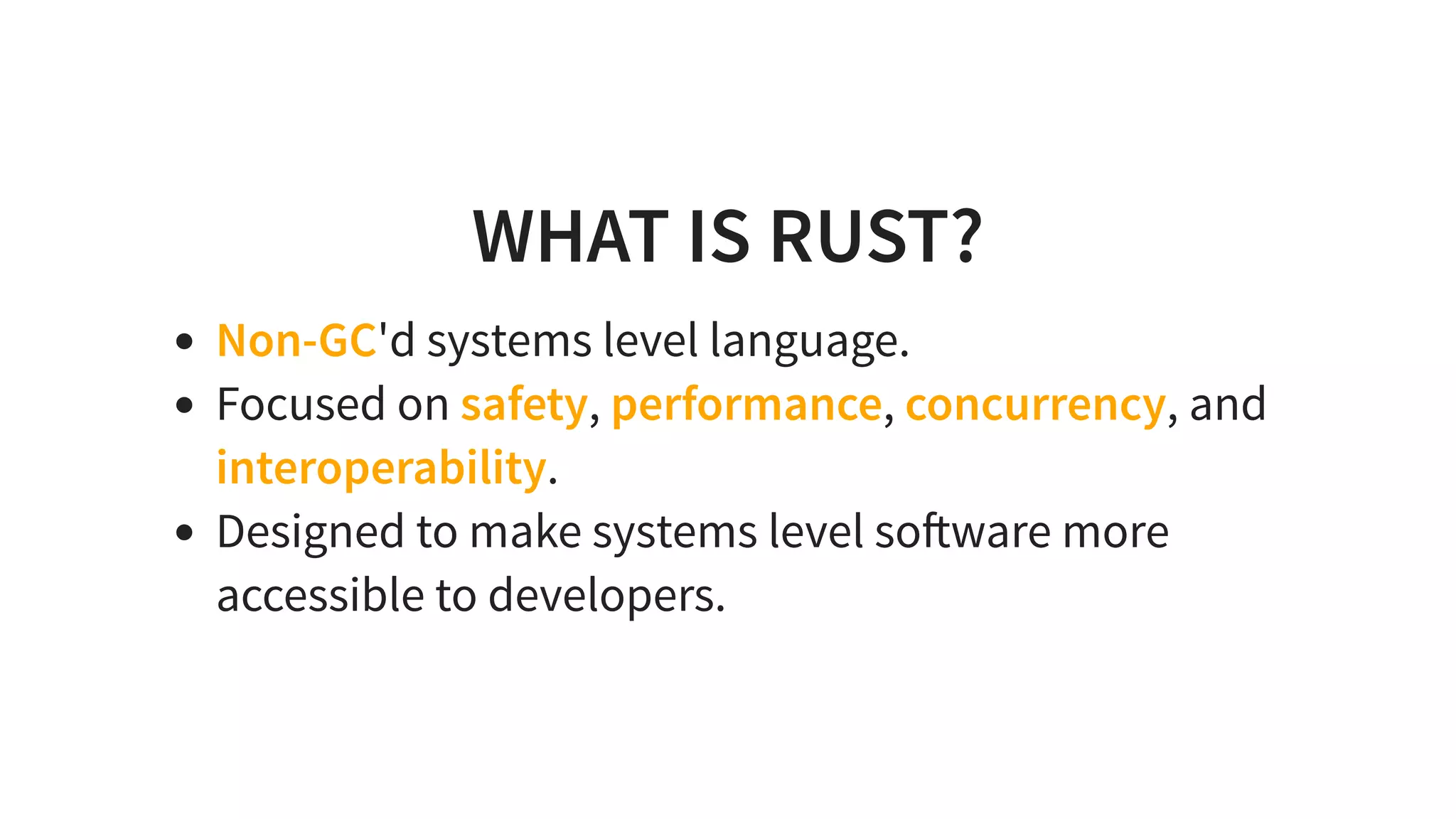
![ZERO-COST ABSTRACTIONS
EXAMPLE 1
trait Animal {
fn speak(&self) -> String;
}
struct Dog;
struct Cat;
impl Animal for Dog {
fn speak(&self) -> String { "Woof".to_string() }
}
impl Animal for Cat {
fn speak(&self) -> String { "Meow".to_string() }
}
fn main() {
let animals: Vec<&dyn Animal> = vec![&Dog, &Cat];
println!("{:?}", animals.iter().map(|x| x.speak())
.collect::<Vec<String>>());
}](https://image.slidesharecdn.com/pitchme-190206164557/75/Intro-to-Rust-2019-17-2048.jpg)
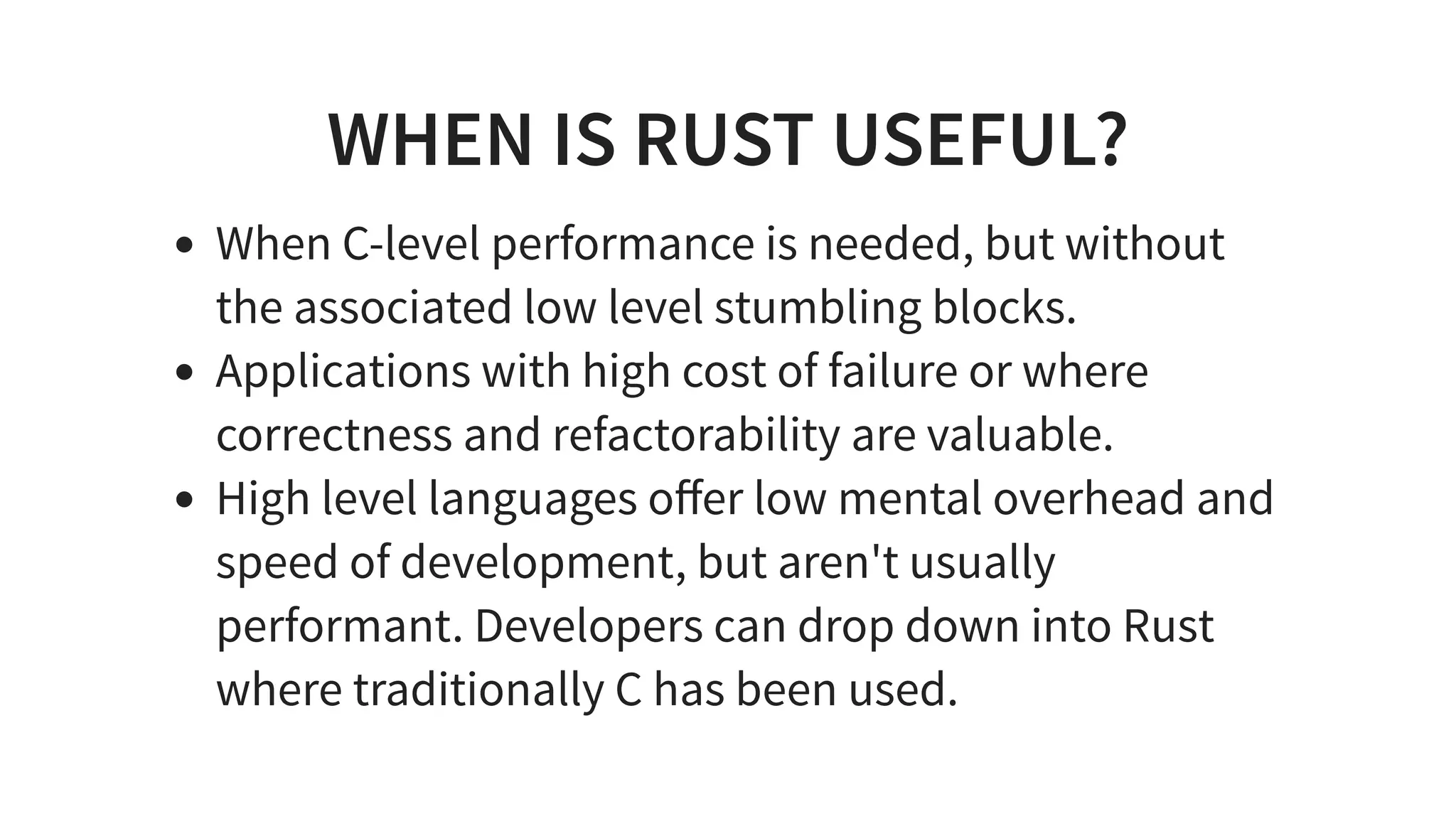
![ZERO-COST ABSTRACTIONS
EXAMPLE 2
enum Animal { Dog, Cat }
impl Animal {
fn speak(&self) -> String {
match self {
Animal::Dog => "Woof".to_string(),
Animal::Cat => "Meow".to_string()
}
}
}
fn main() {
use Animal::*;
let animals: Vec<Animal> = vec![Dog, Cat];
println!("{:?}", animals.iter().map(|x| x.speak())
.collect::<Vec<String>>());
}](https://image.slidesharecdn.com/pitchme-190206164557/75/Intro-to-Rust-2019-18-2048.jpg)
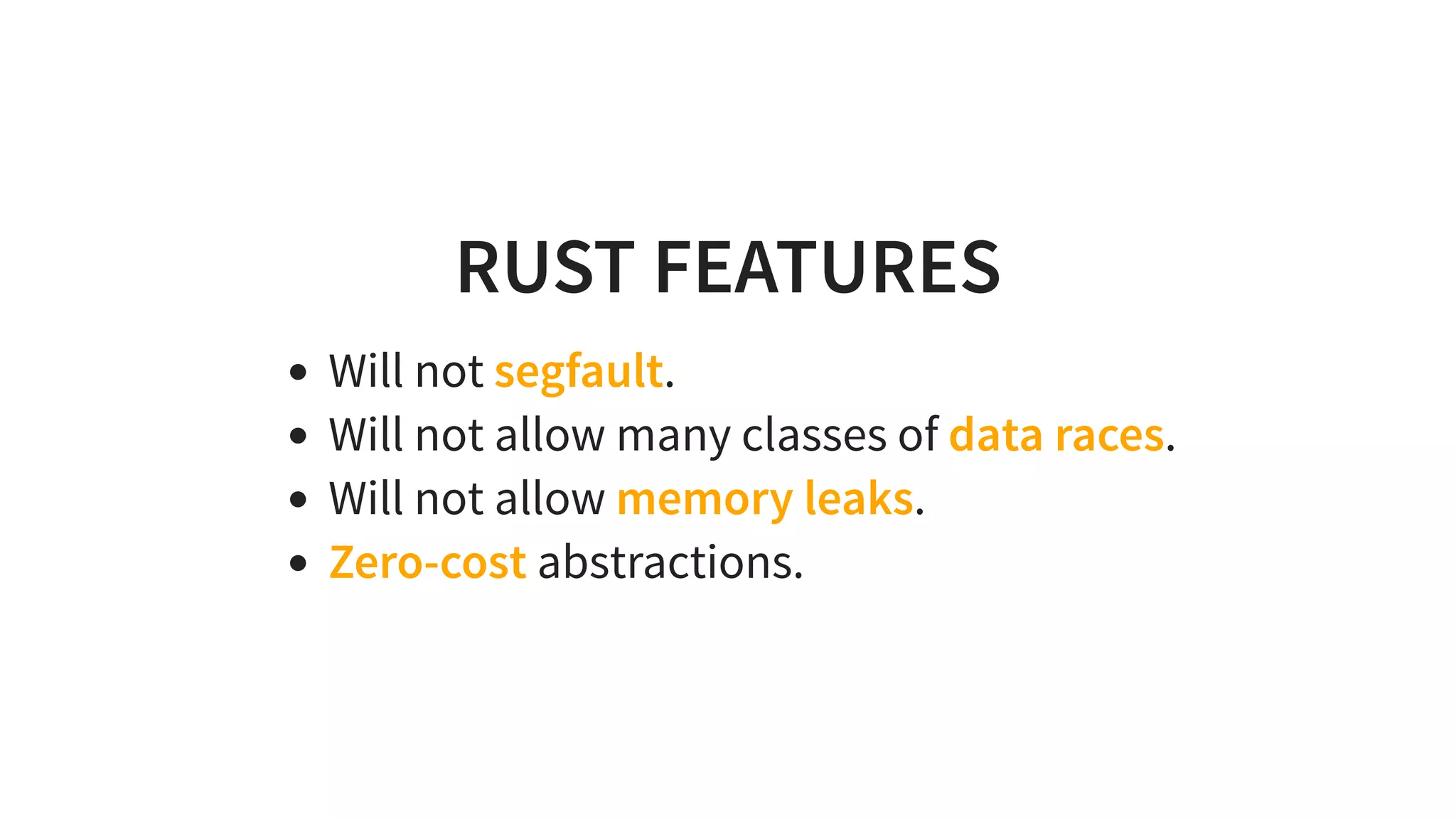
![ZERO-COST ABSTRACTIONS
EXAMPLE 3
use std::fmt::Debug;
fn debug_string<T: Debug>(obj: T) -> String {
format!("{:?}", obj)
}
fn debug_string_dynamic(obj: &dyn Debug) -> String {
format!("{:?}", obj)
}
fn main() {
println!("{}", debug_string(vec![1, 2, 3]));
println!("{}", debug_string("foobar"));
println!("{}", debug_string_dynamic(&vec![1, 2, 3]));
println!("{}", debug_string_dynamic(&"foobar"));
}](https://image.slidesharecdn.com/pitchme-190206164557/75/Intro-to-Rust-2019-19-2048.jpg)