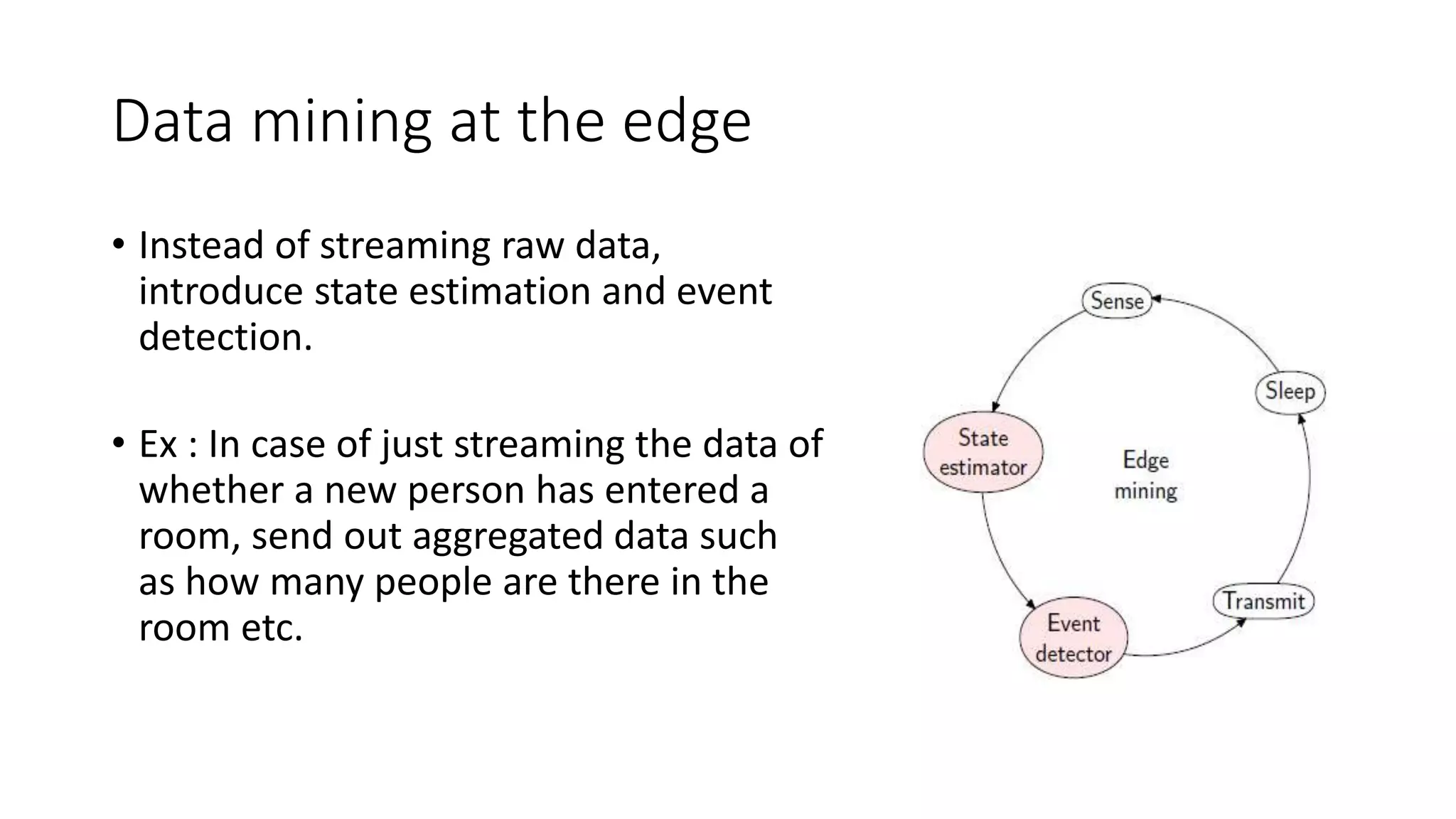
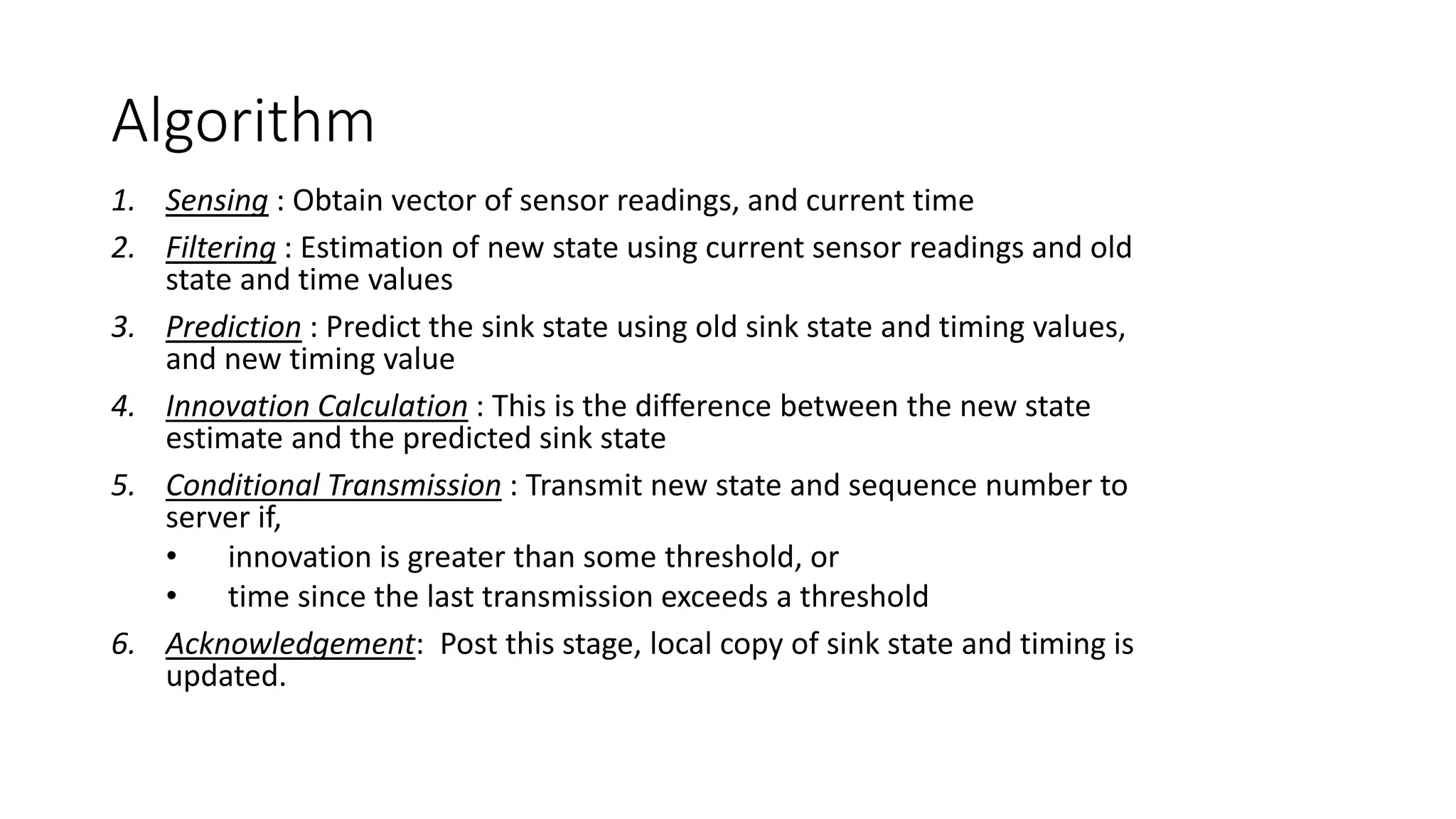
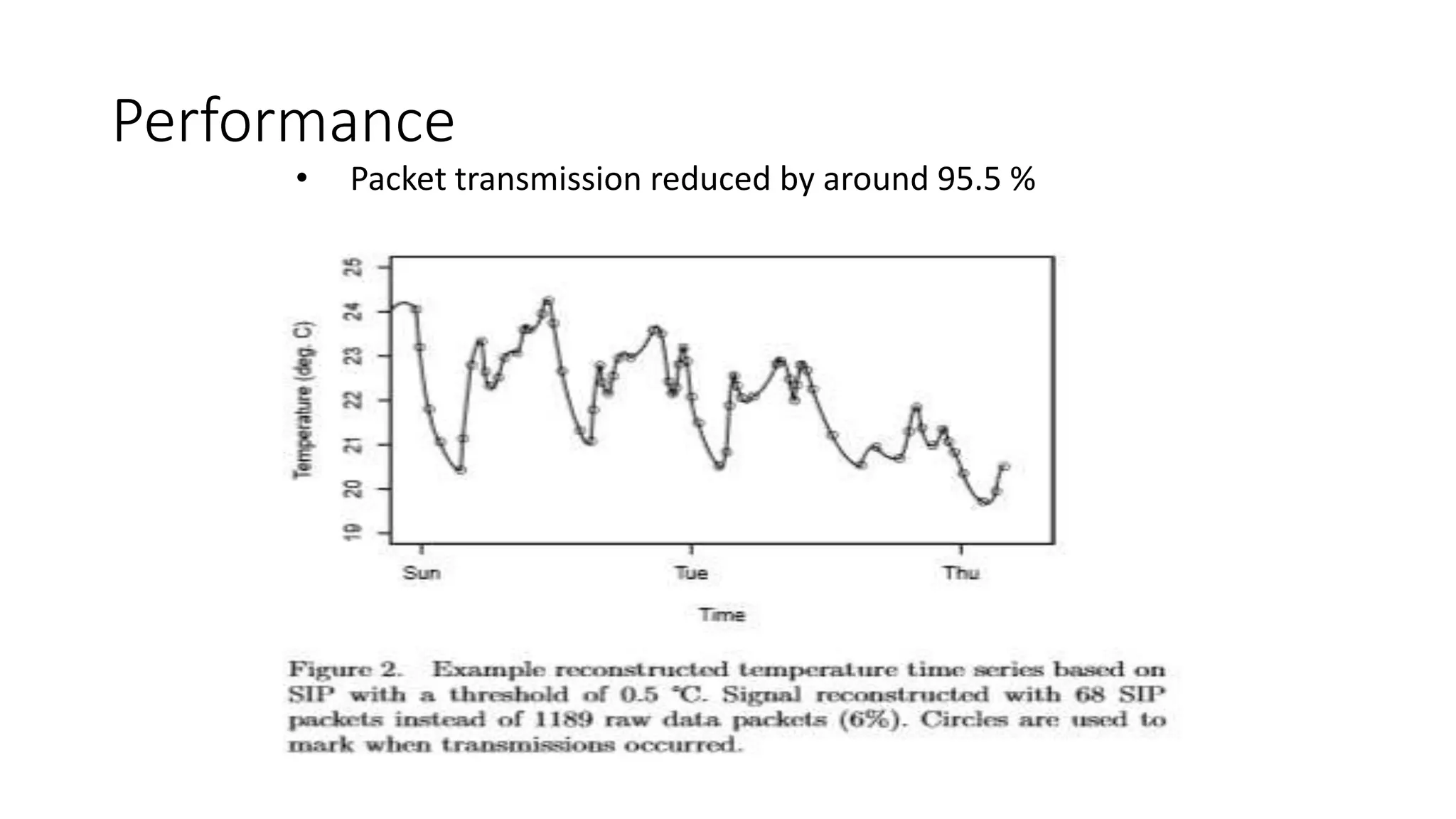
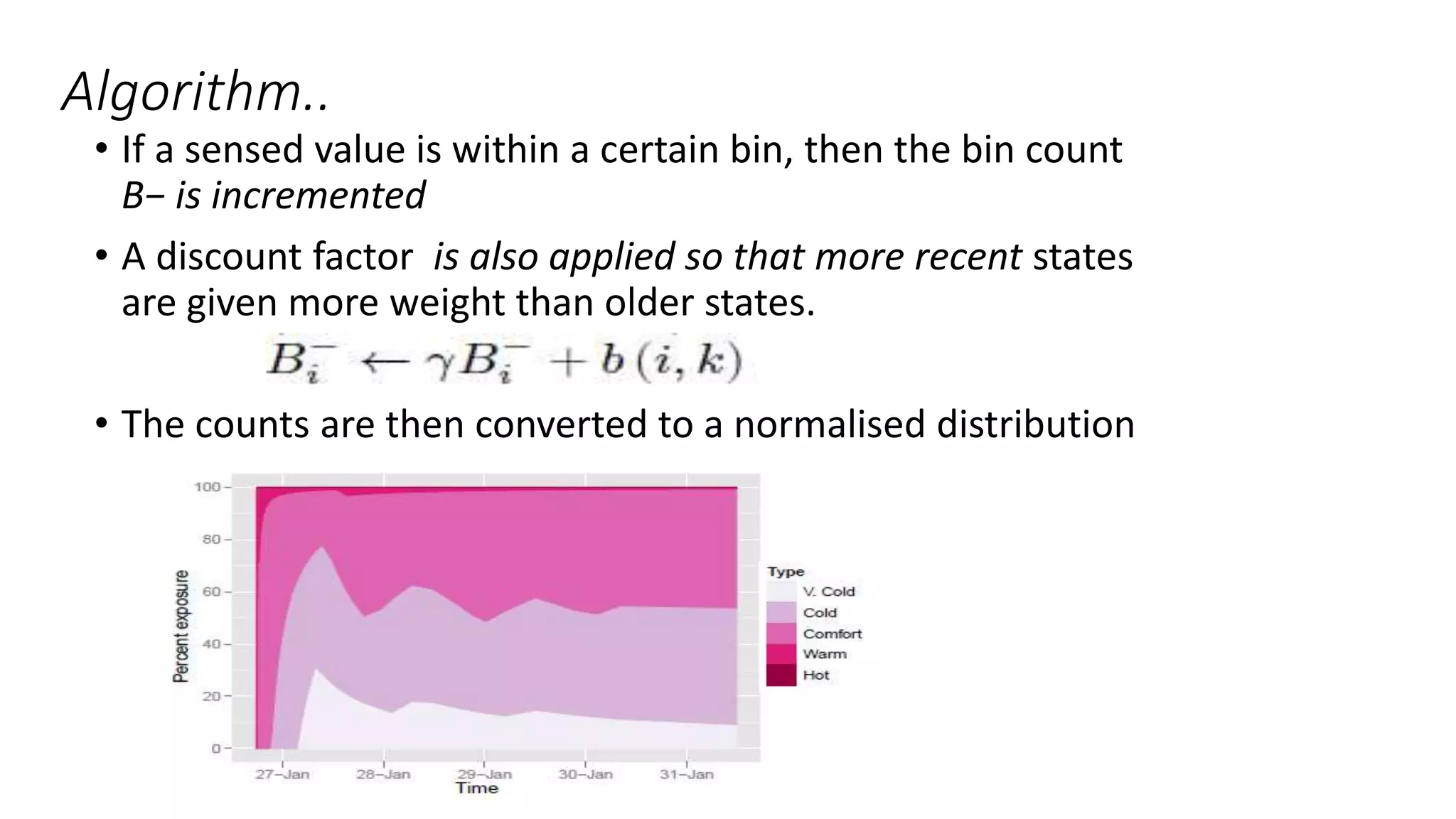
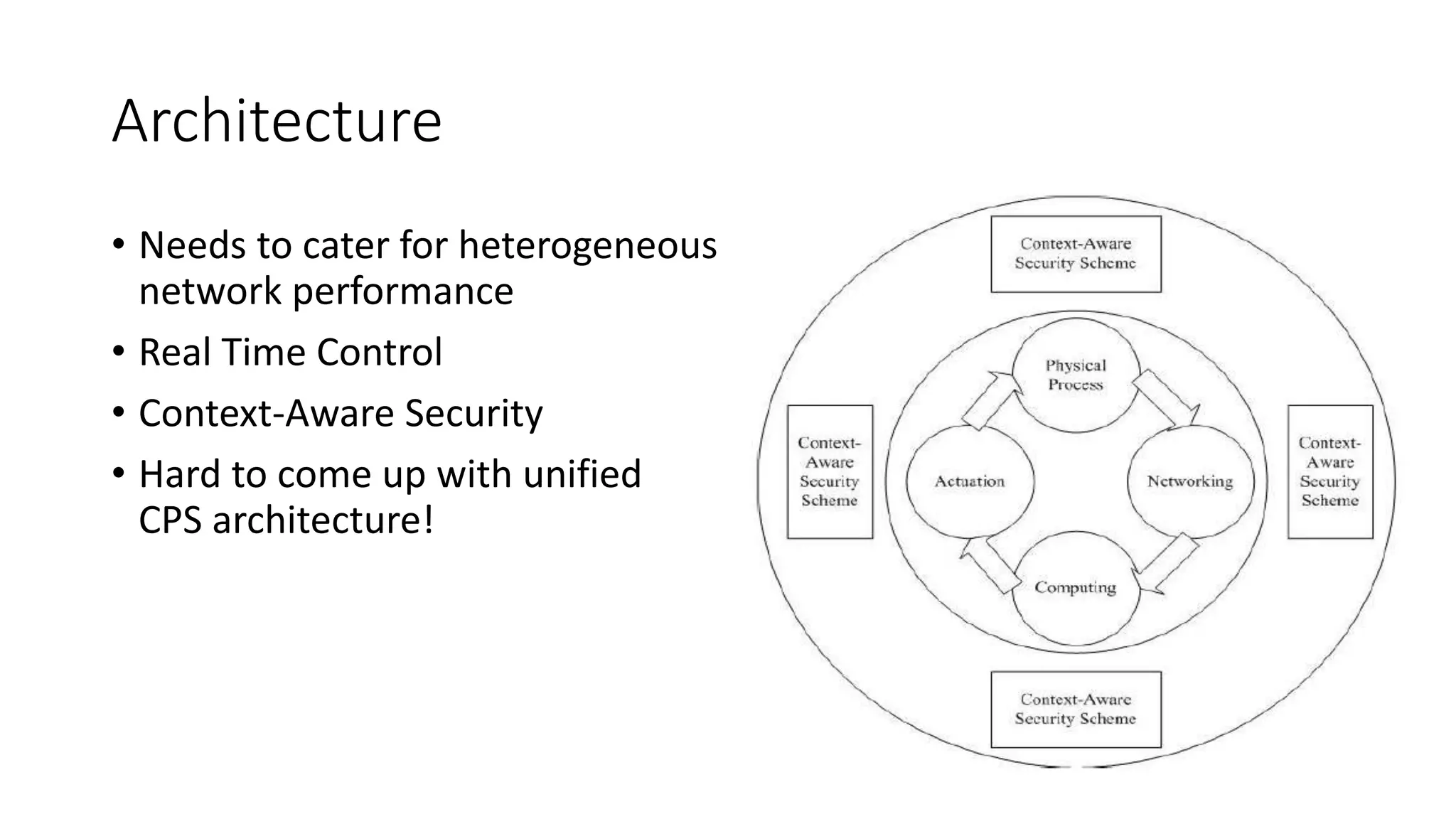
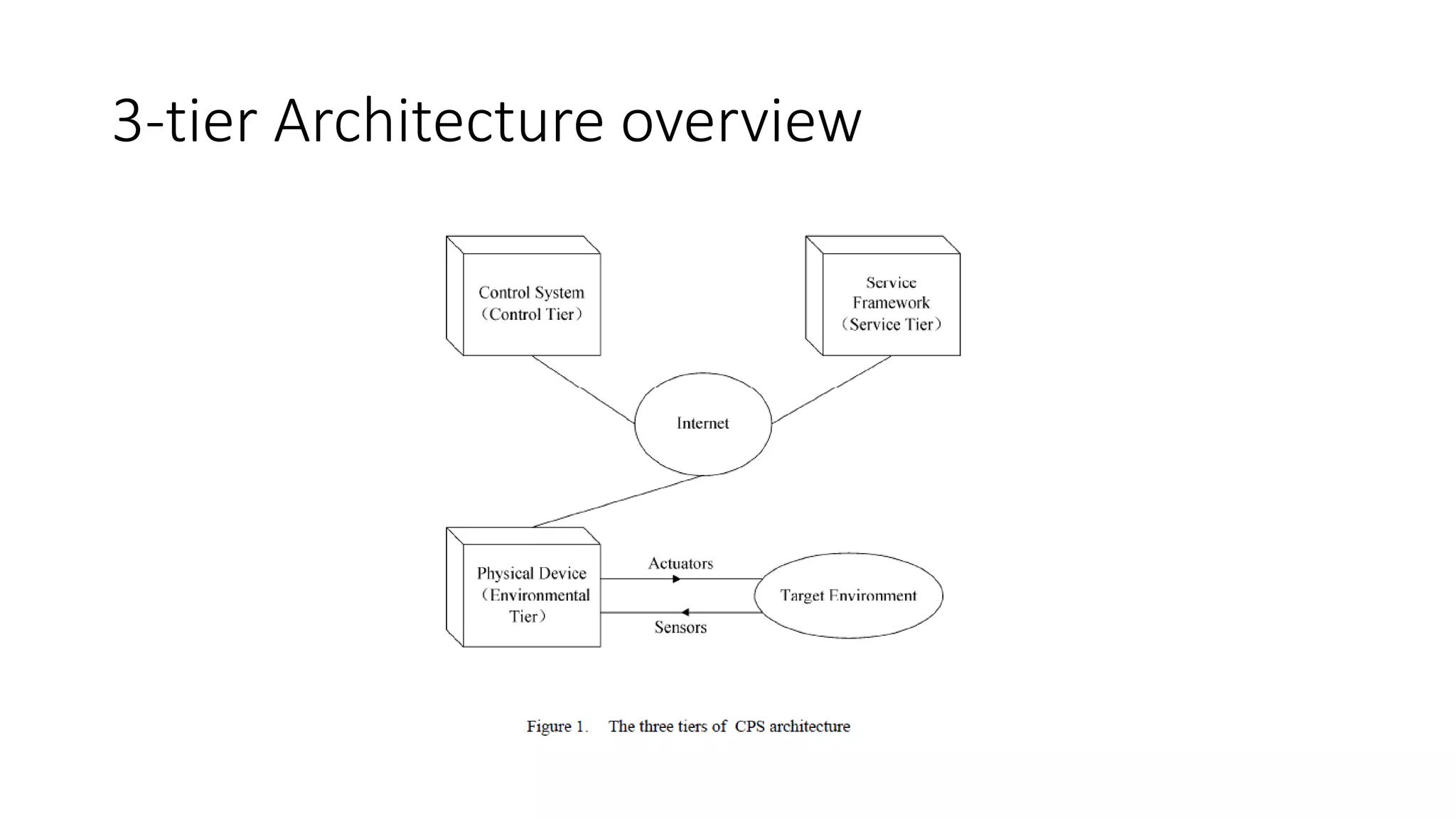
This document discusses design challenges and solutions for energy efficiency in cyber-physical systems (CPS). It outlines key CPS challenges such as timing issues, miniaturization, and energy efficiency. It then describes approaches to optimize low power design at various layers, including low-energy VLSI techniques and low power communication methods. Two edge mining techniques called the Spanish Inquisition Protocol and Bare Necessities are introduced to reduce the number of sensing messages and achieve lower energy consumption. These techniques introduce state estimation and event detection at edge nodes to send aggregated data instead of raw sensor readings. This helps improve privacy by making it impossible to use the data for unintended purposes. Both techniques significantly reduce the number of data transmissions needed. The document