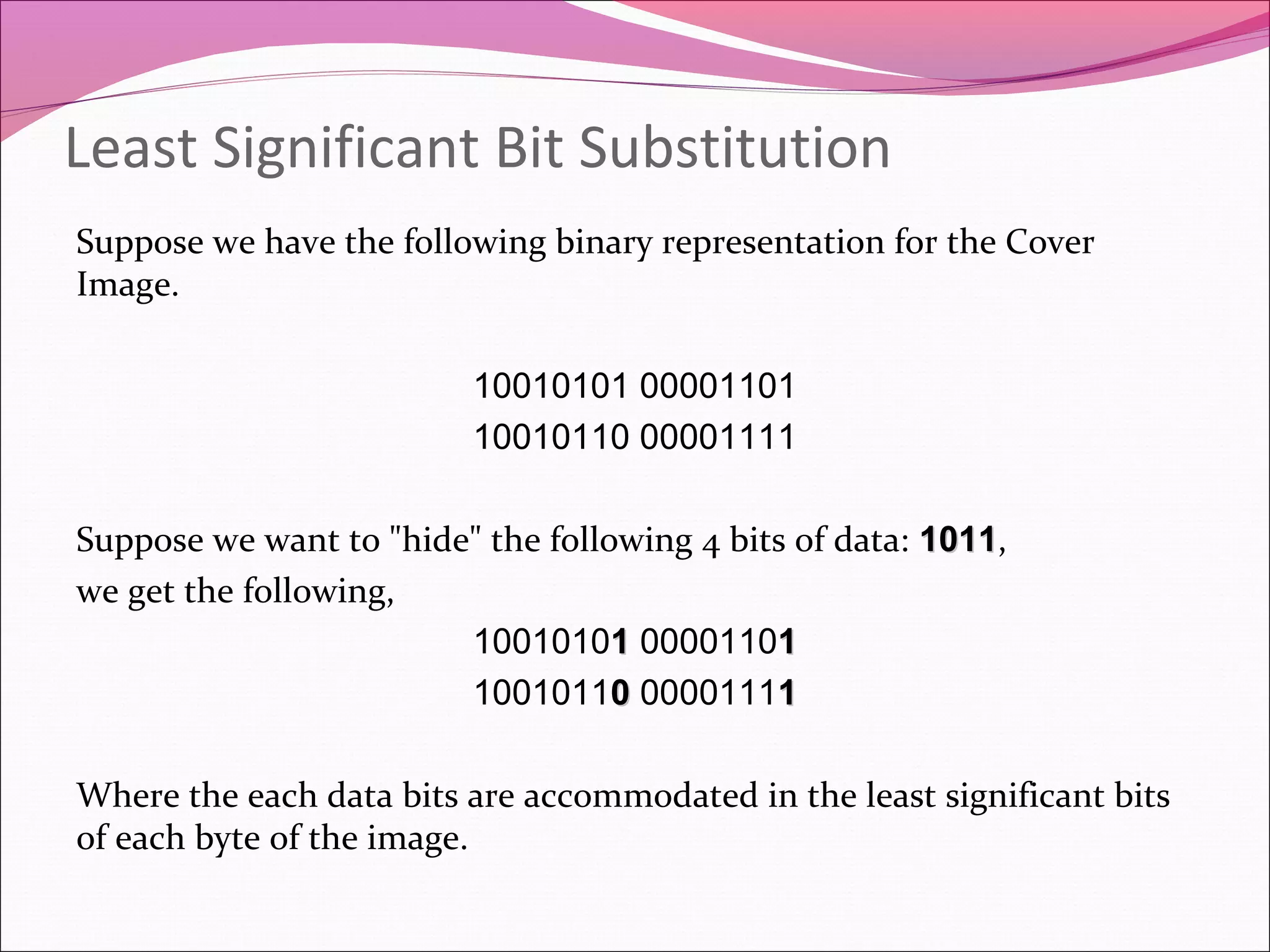
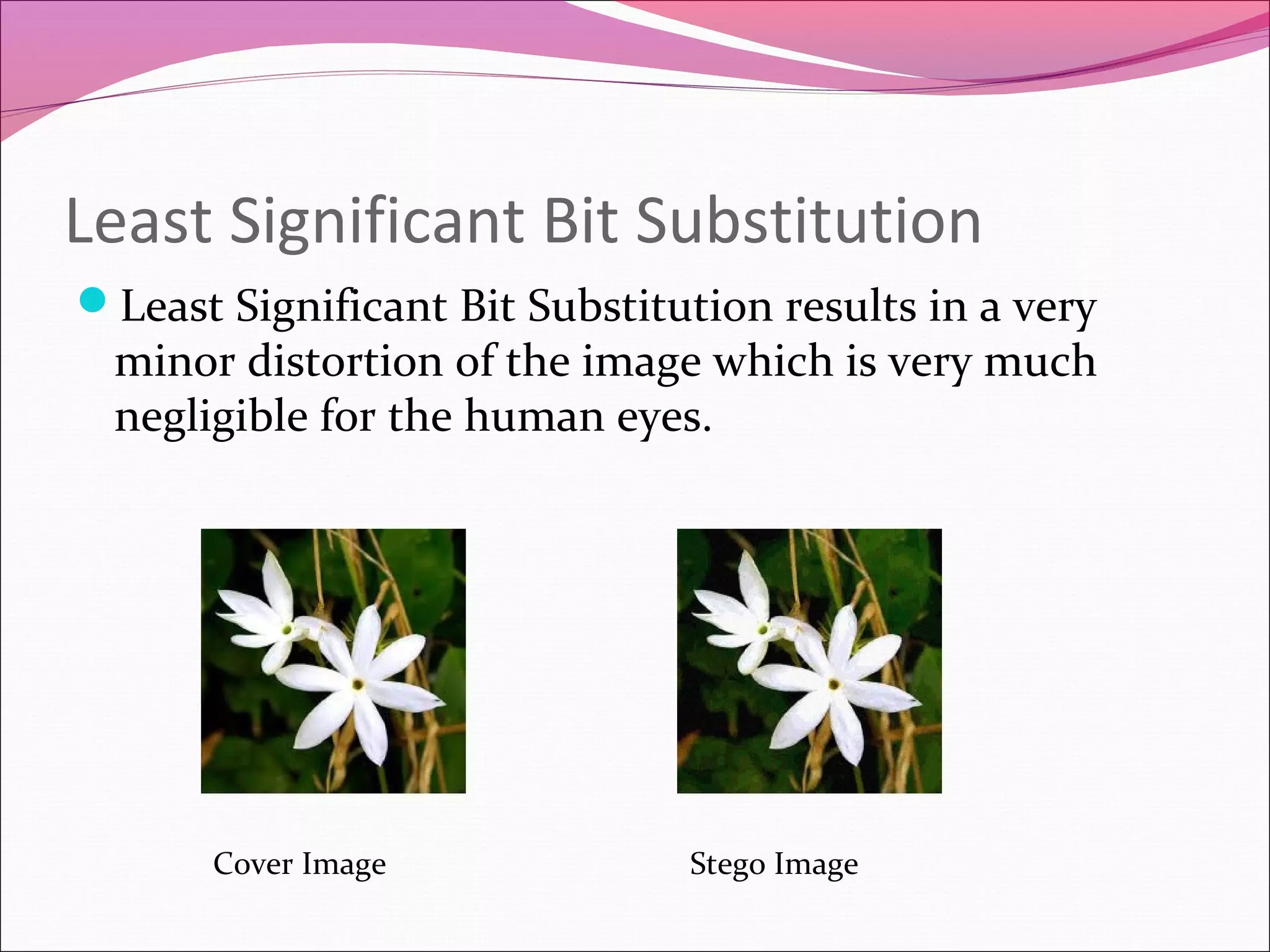
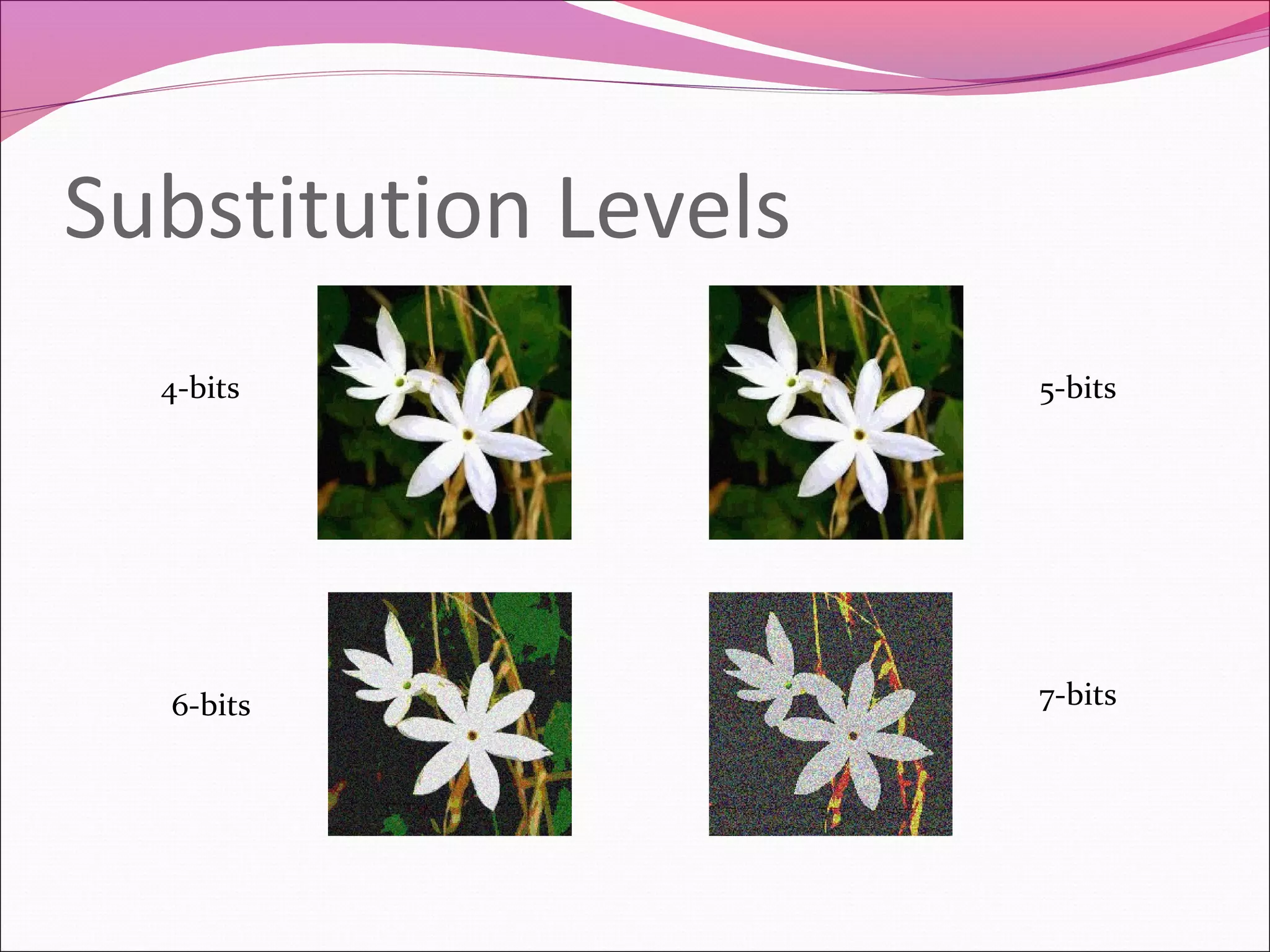
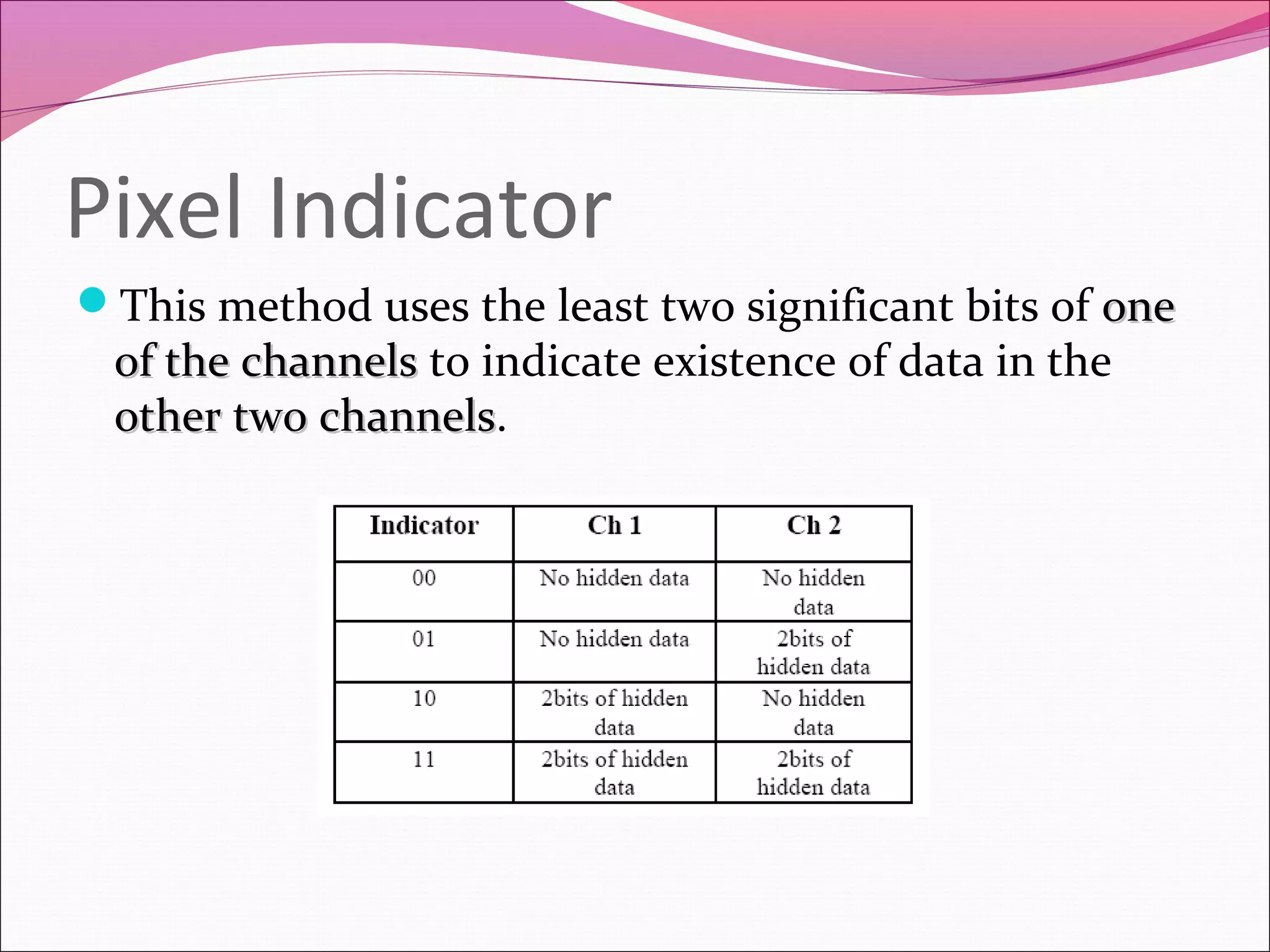
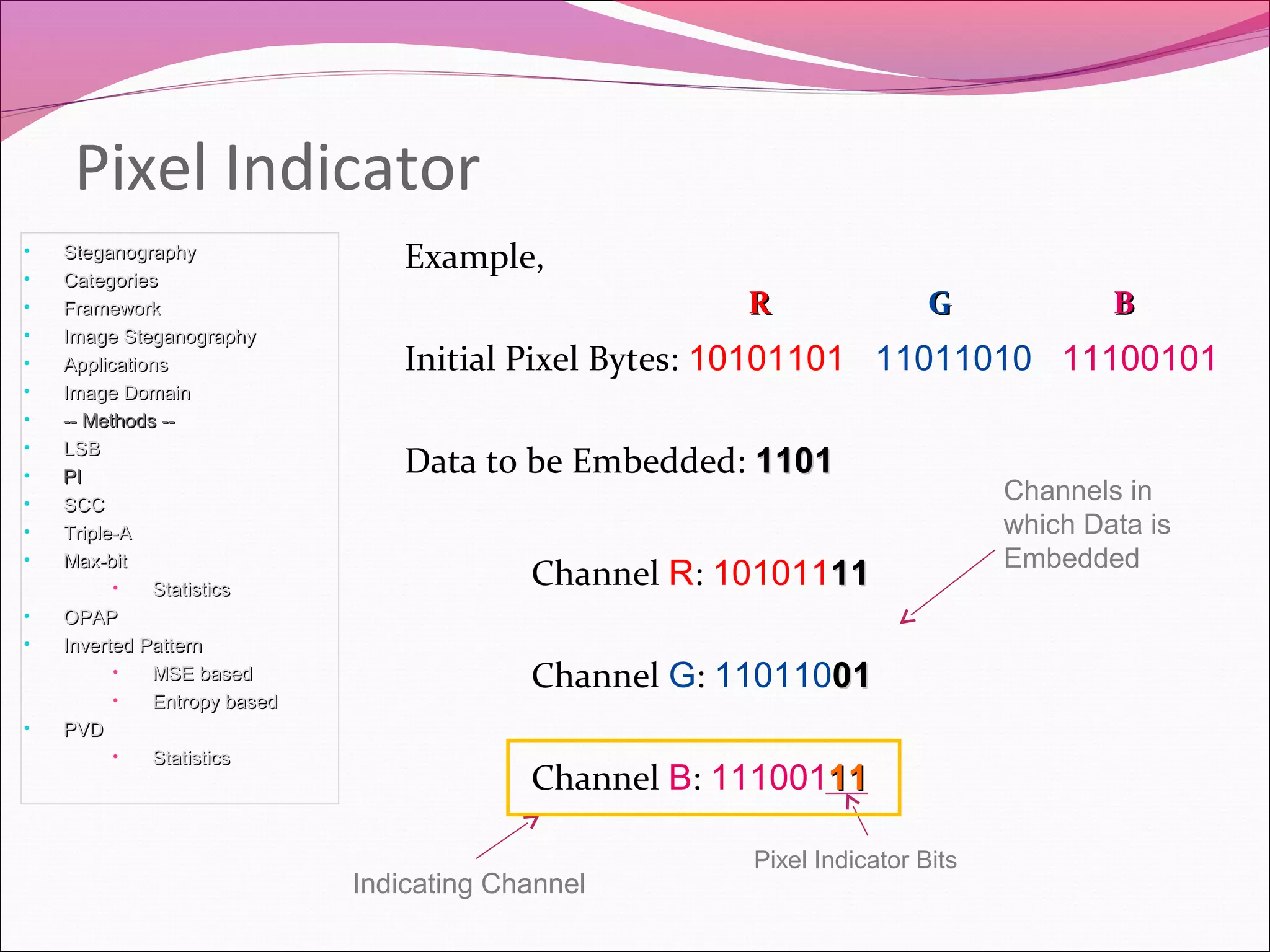
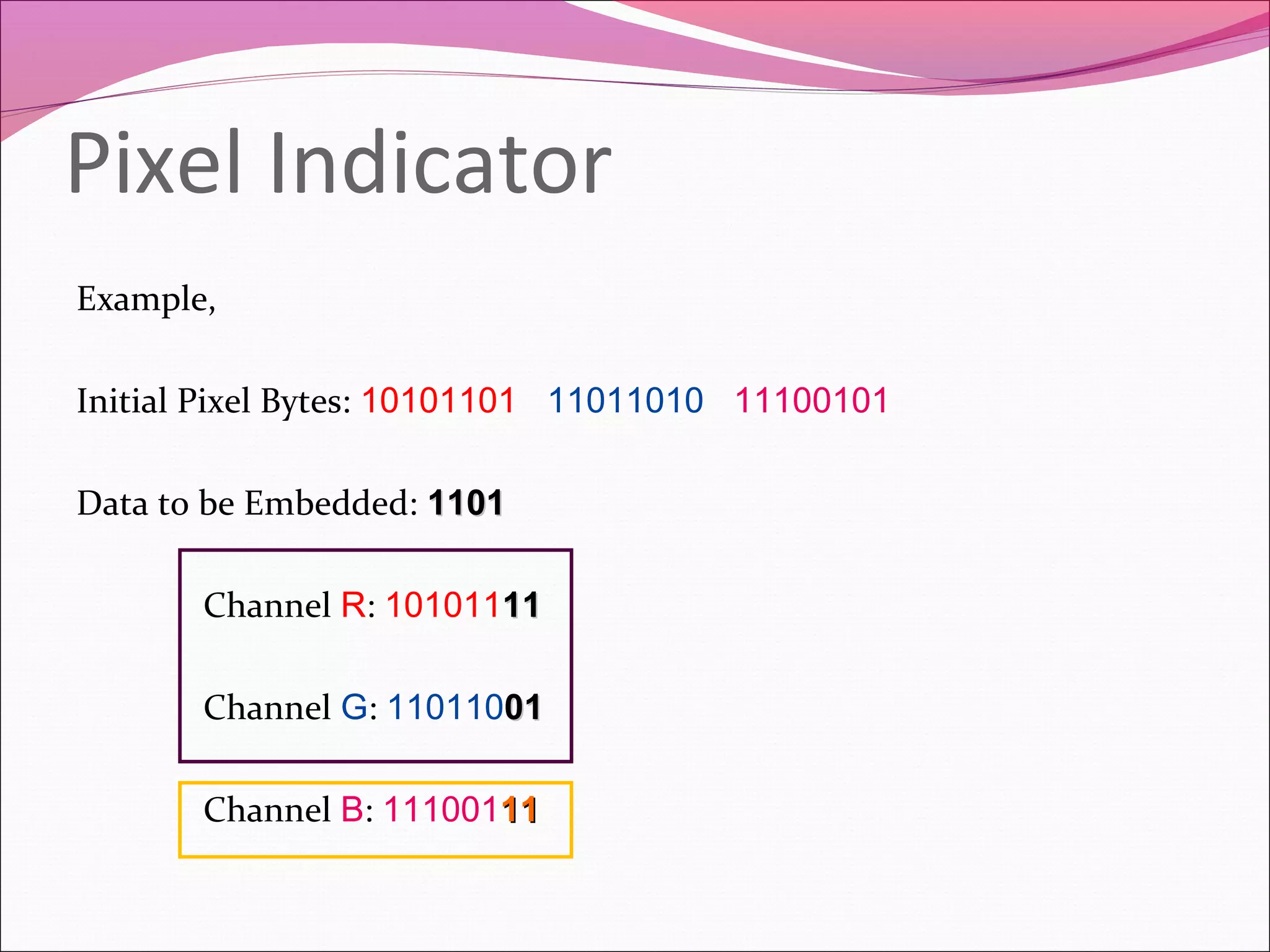
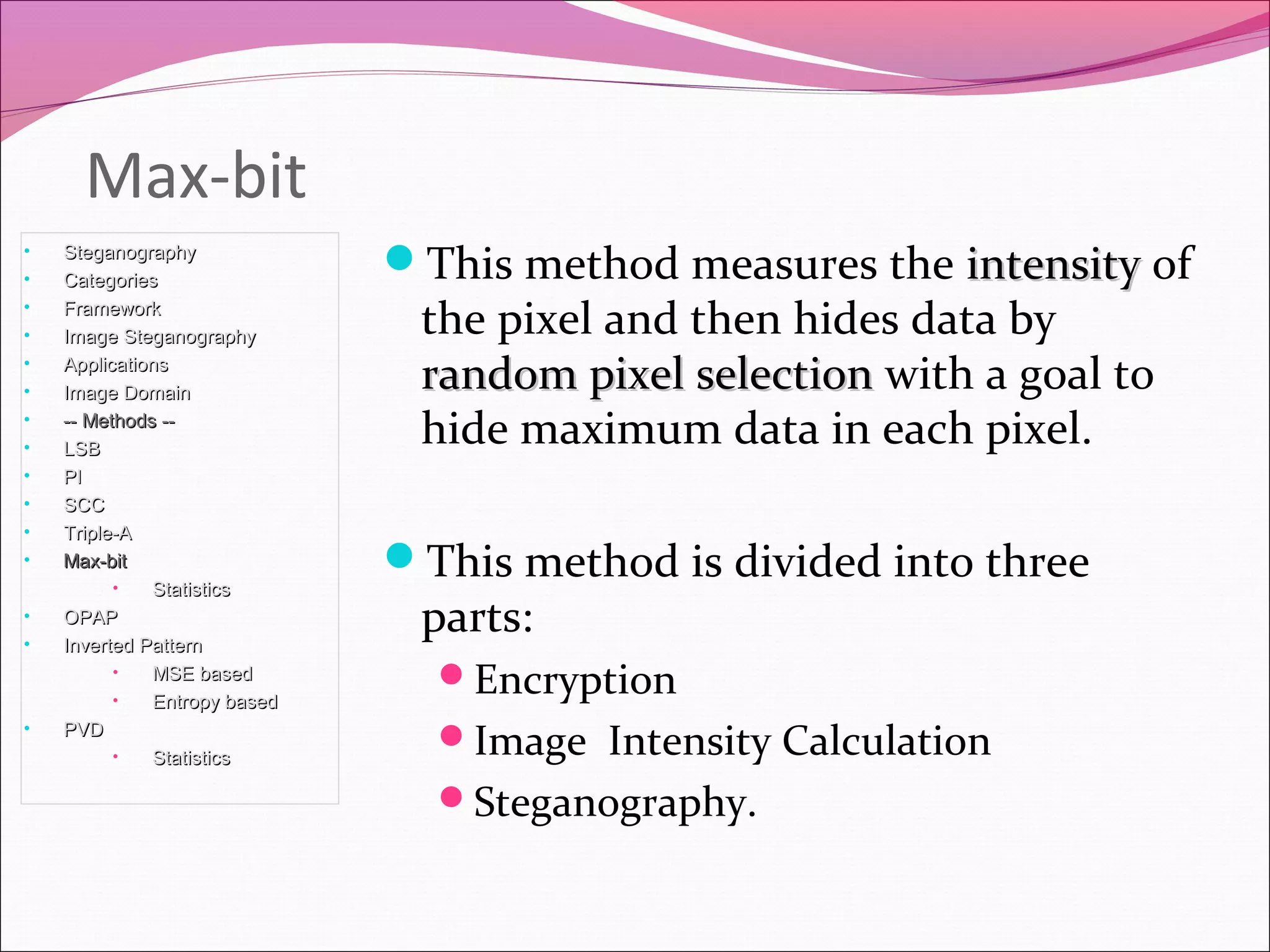
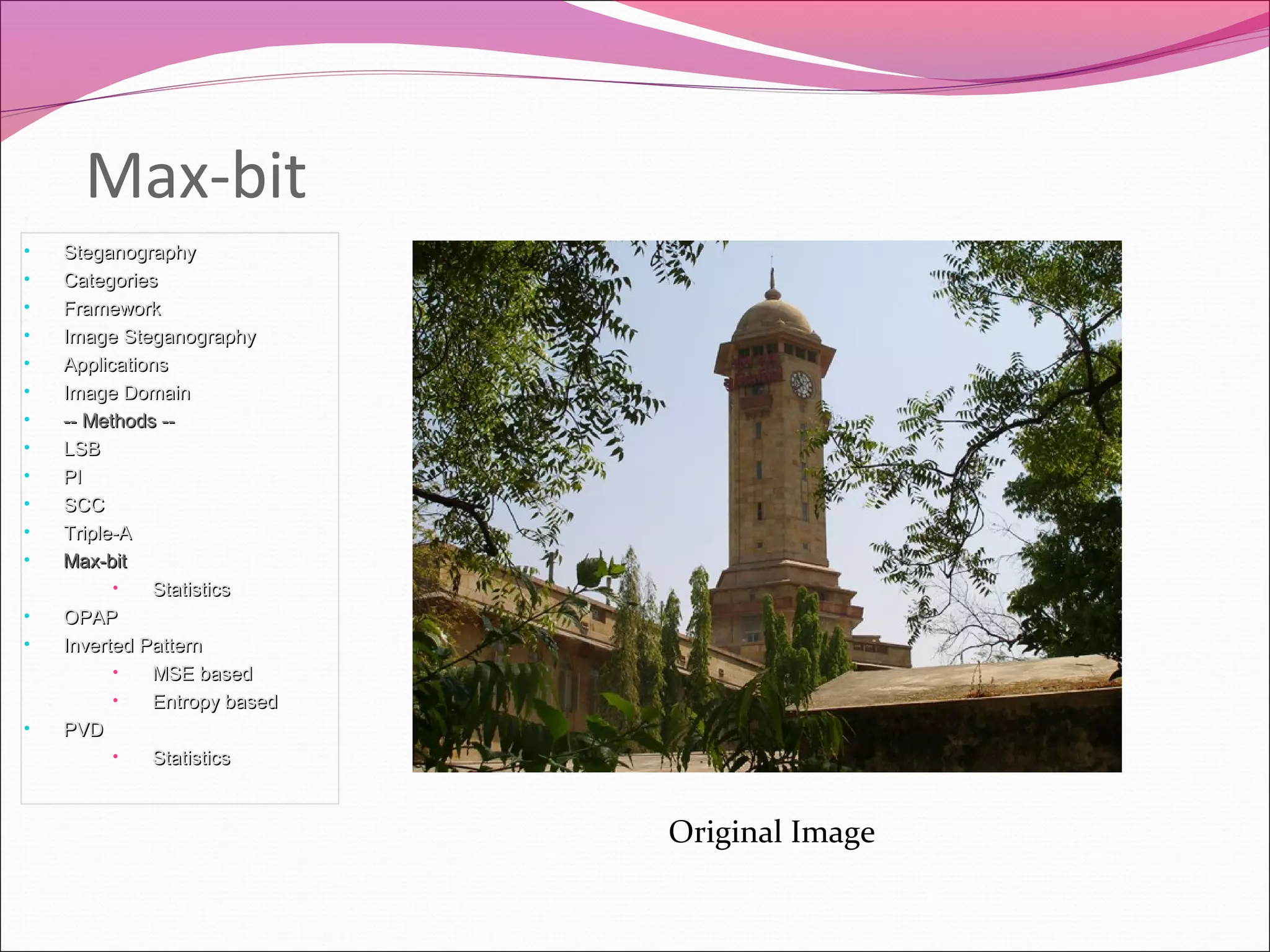
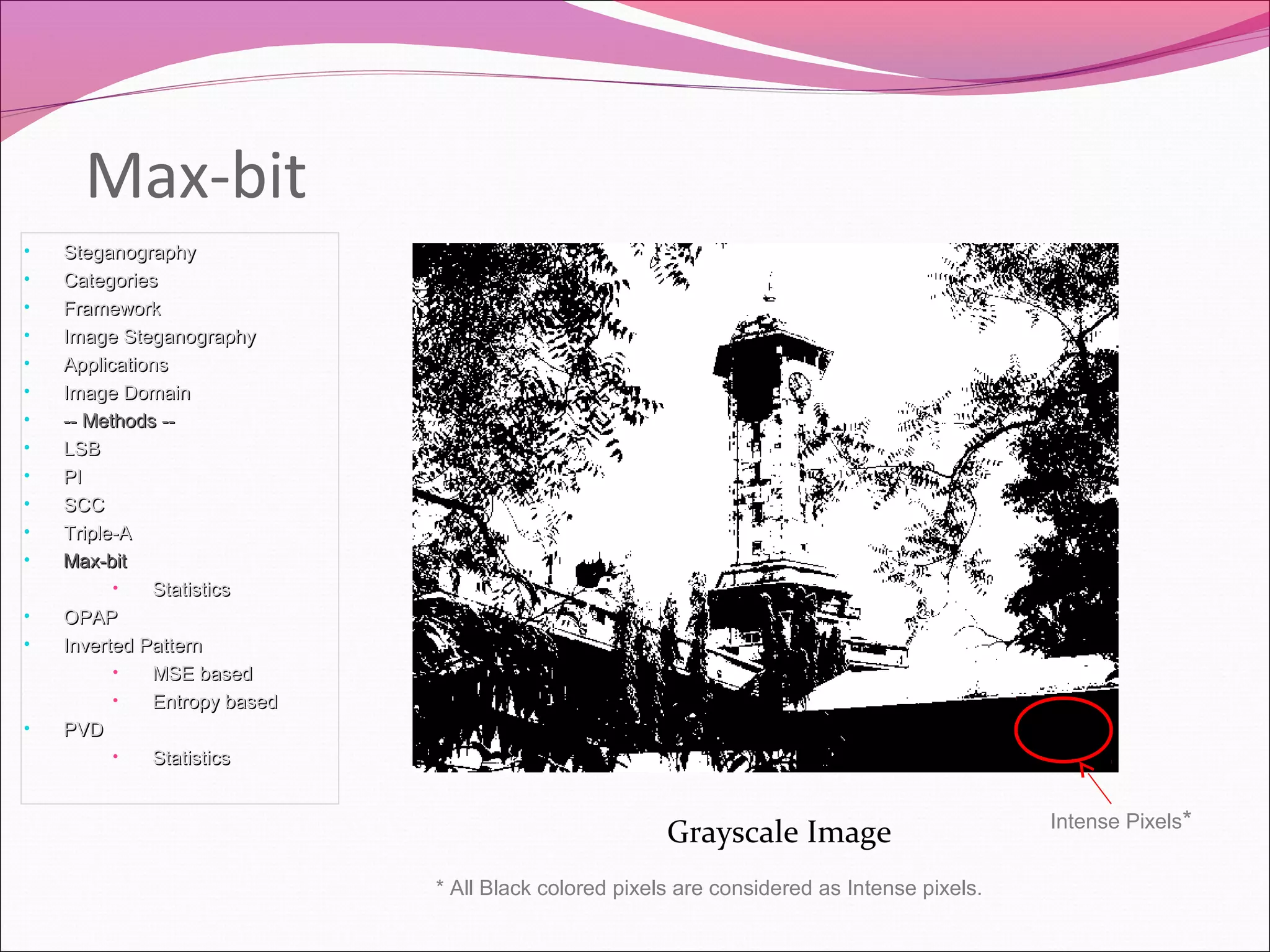
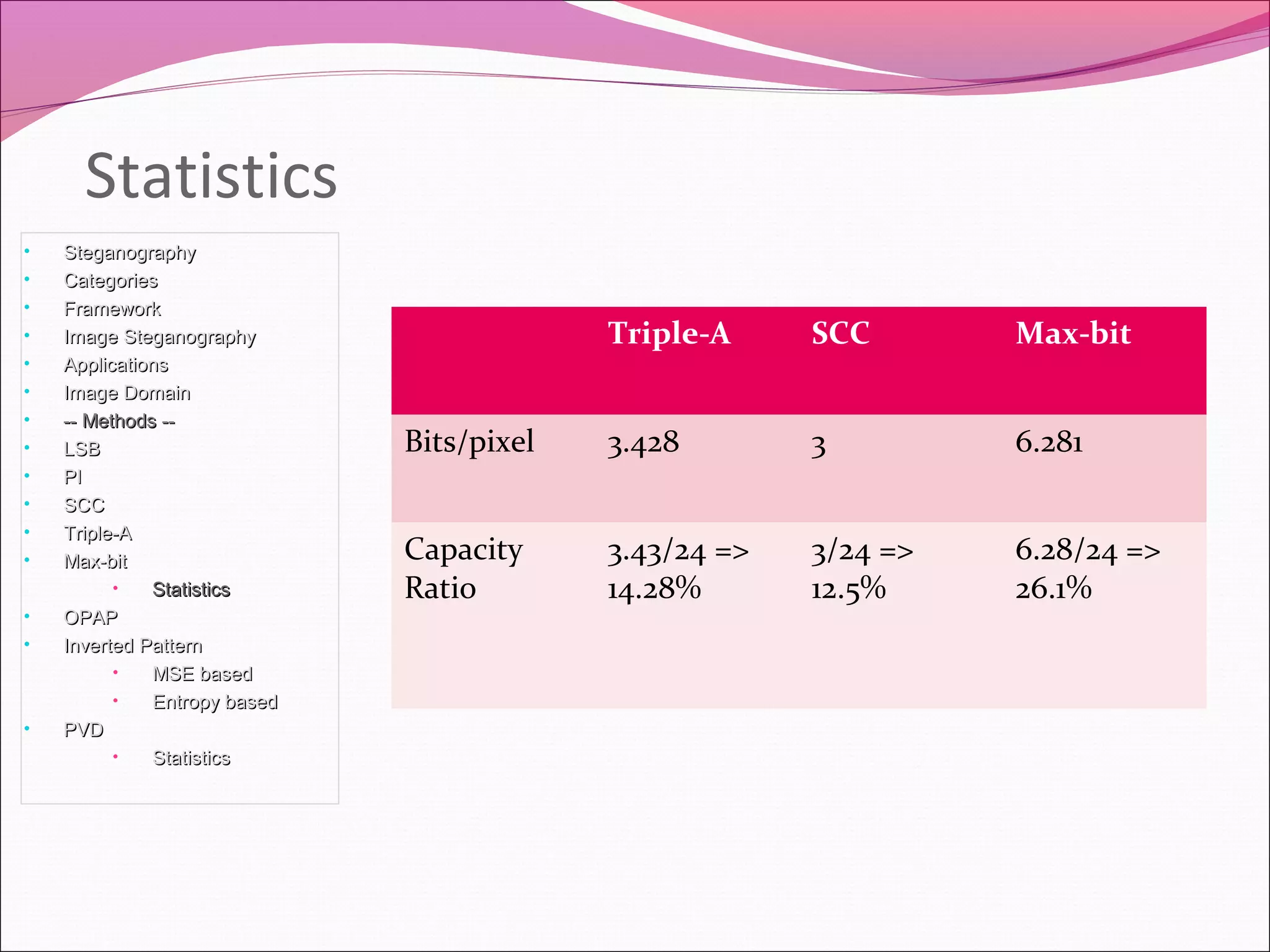
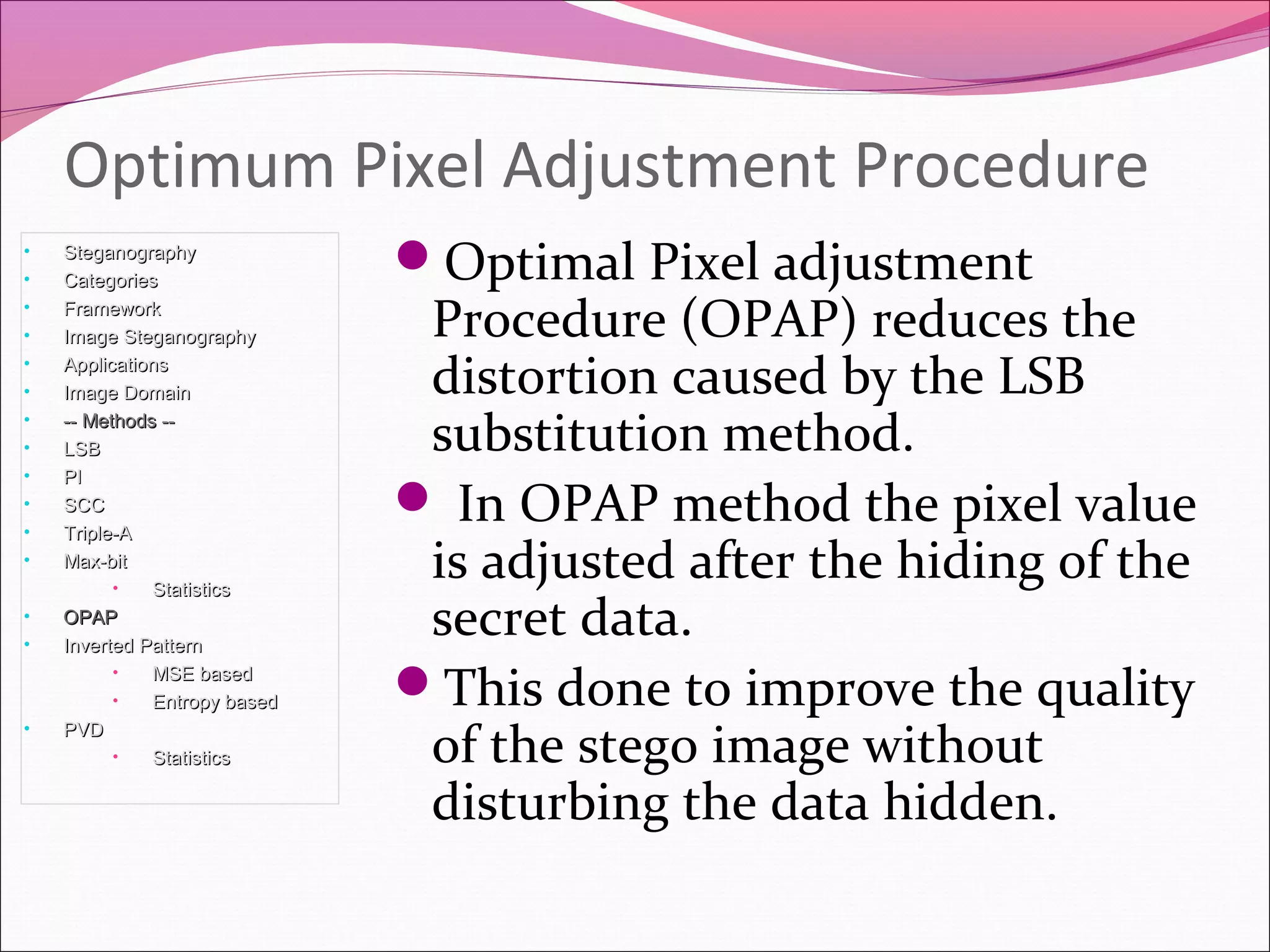
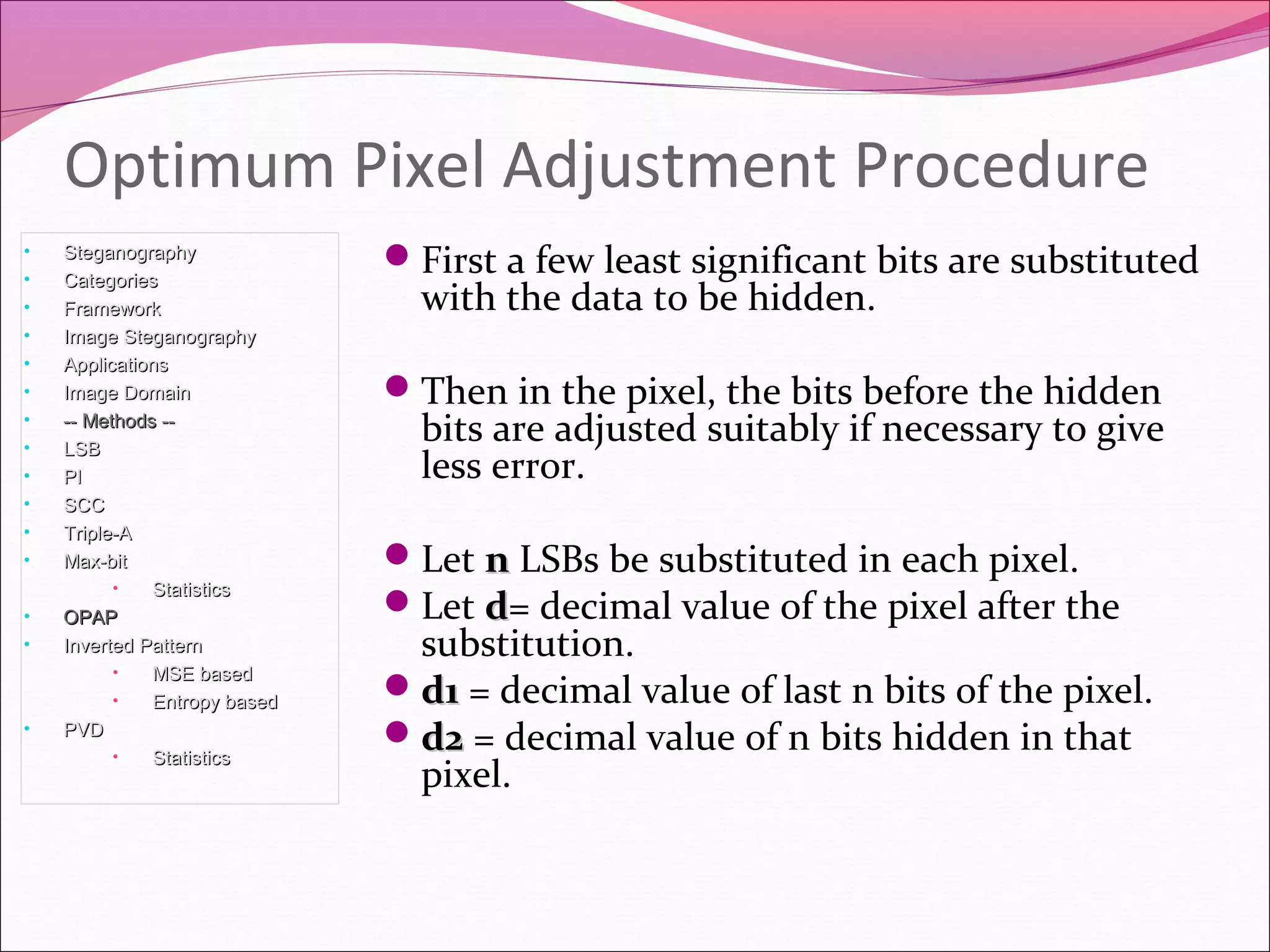
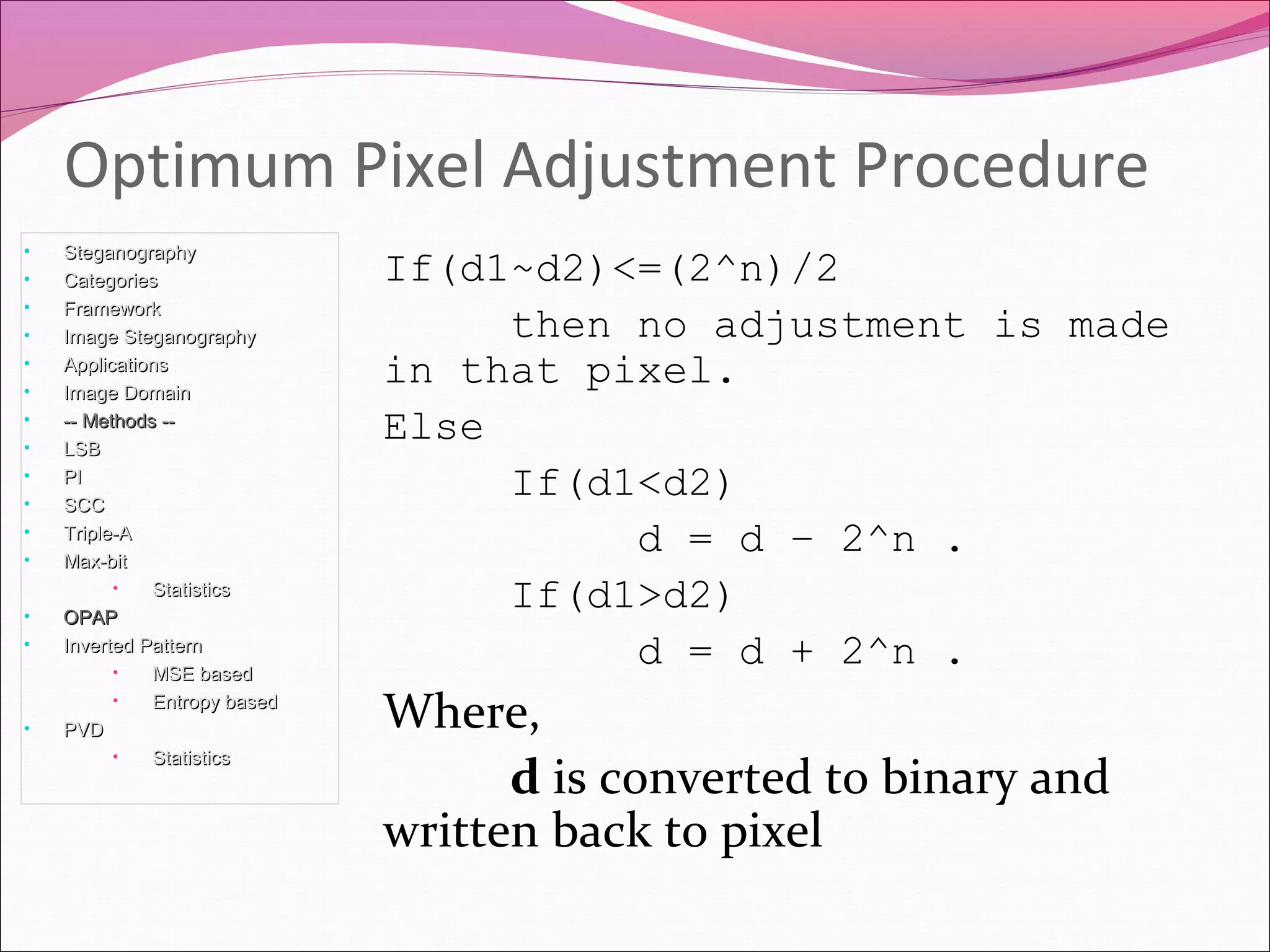
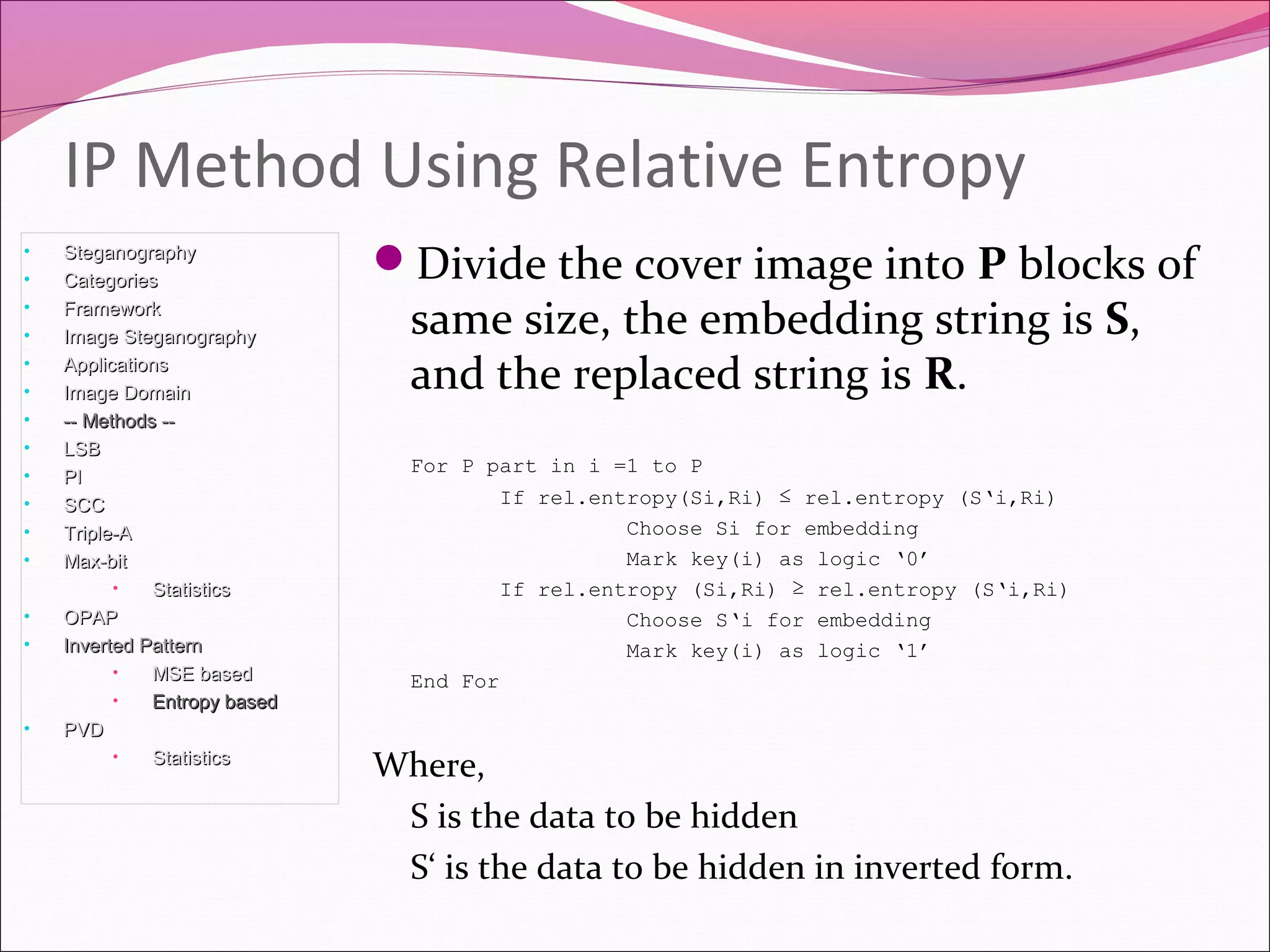
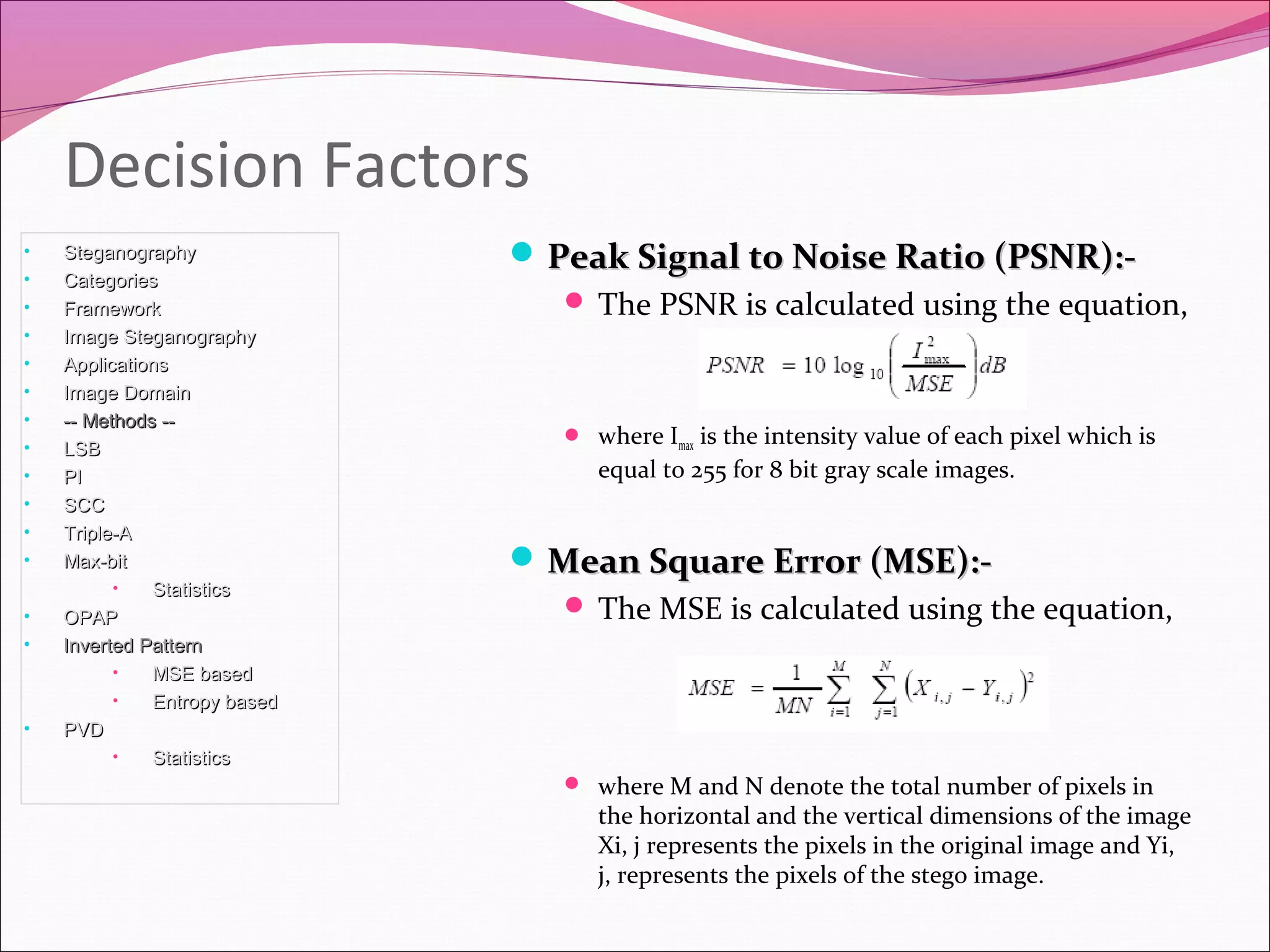
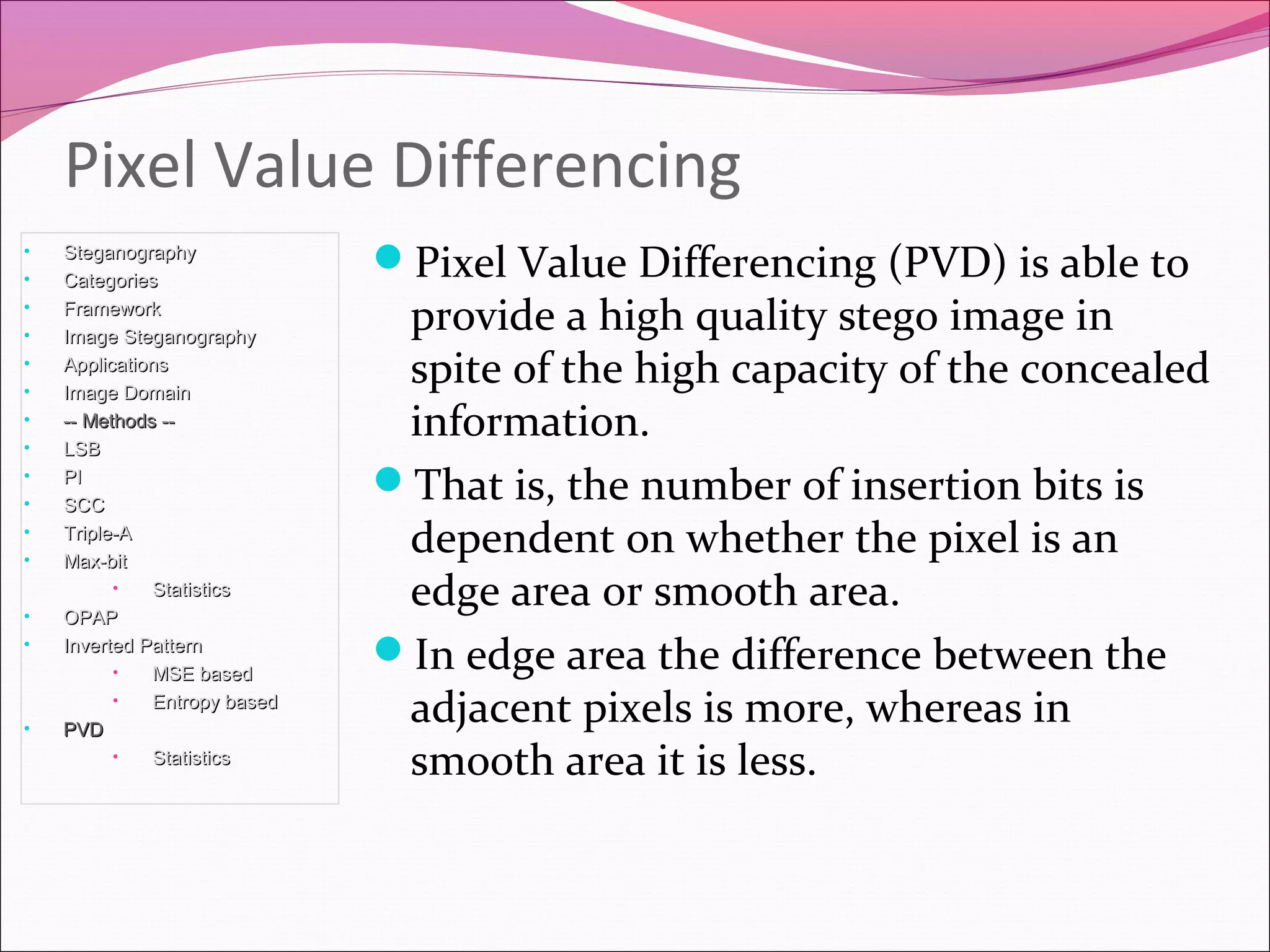
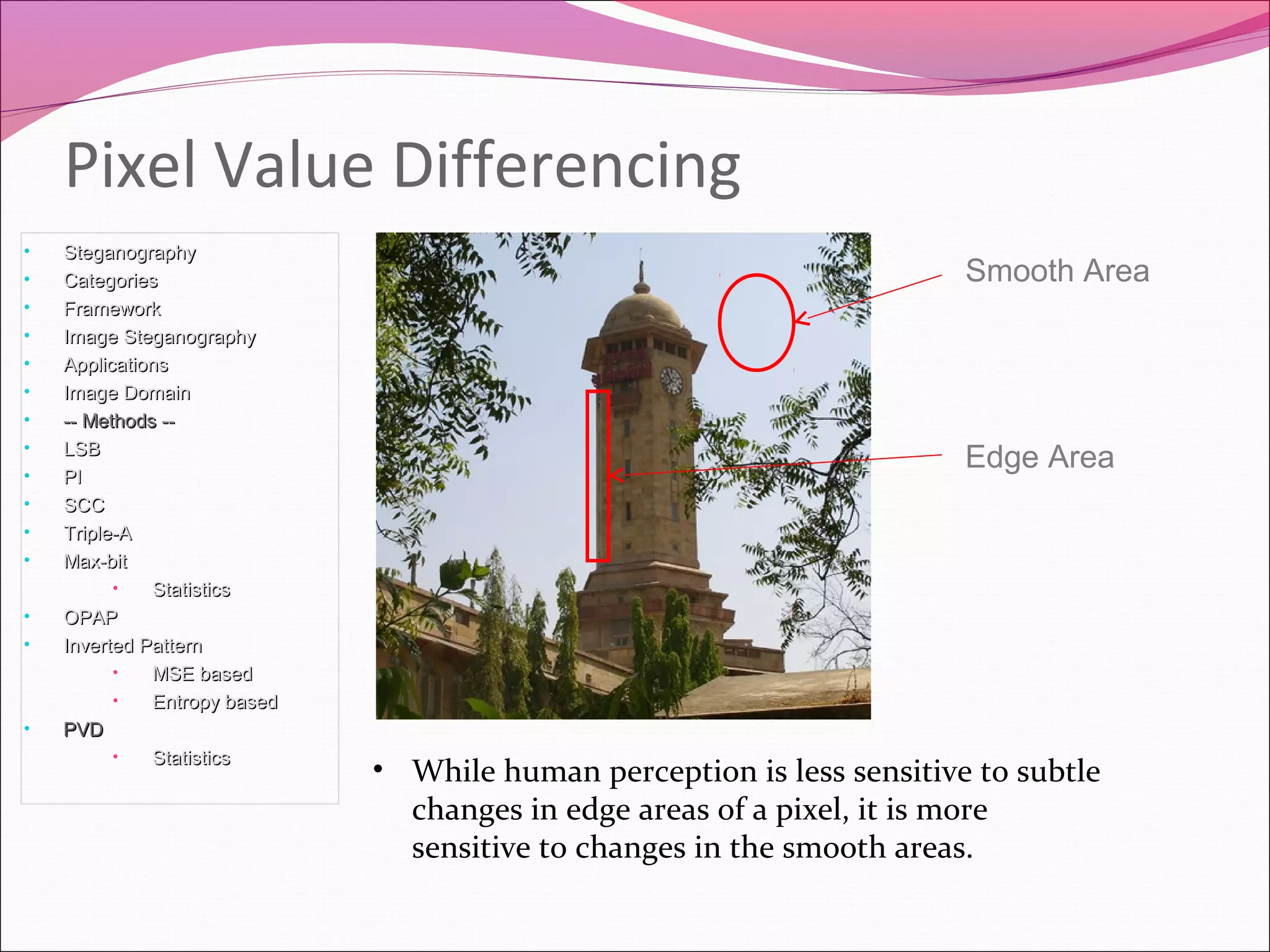
This document discusses various image steganography techniques. It begins by introducing image steganography and its applications, such as hiding passwords and encrypting private files. It then covers several embedding and extraction methods, including least significant bit substitution, pixel indicator, stego color cycle, triple-A, Max-bit, optimal pixel adjustment procedure, and inverted pattern approaches. For each method, it provides a brief overview of the technique and how it works to hide information in the image in an imperceptible way.
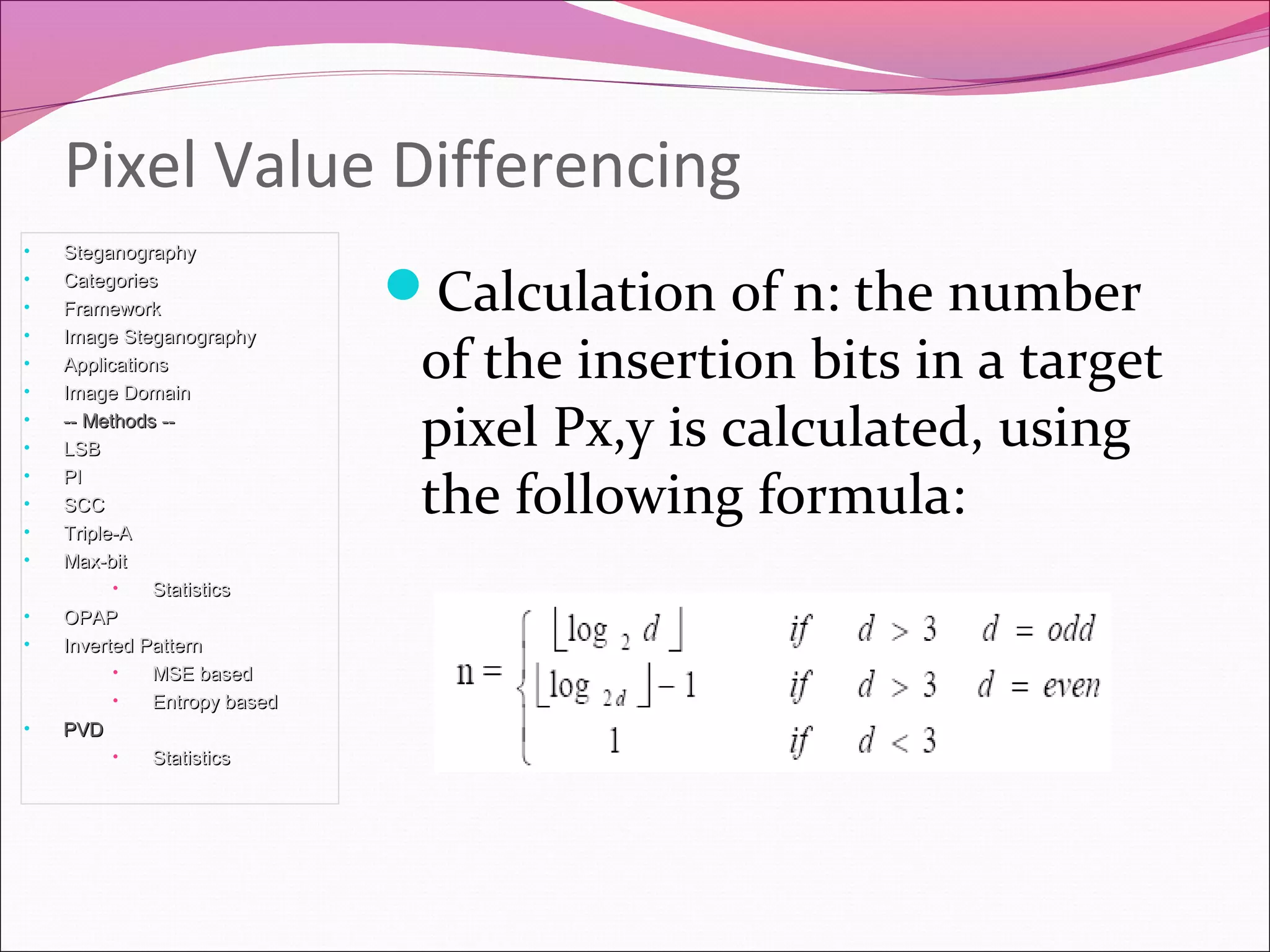
![Select the maximum and the minimum
values(g) among the three pixel values that
have already finished the embedding process.
Consider upper pixel (g1), left pixel (g2) and
the upper left pixel (g3) in a given target pixel
g(x,y)
Calculate d using following:
d= [max (g1, g2, g3) – min (g1, g2, g3)]
Using d , we get an idea as to whether the
target pixel is included in an edge area or in
smooth area.
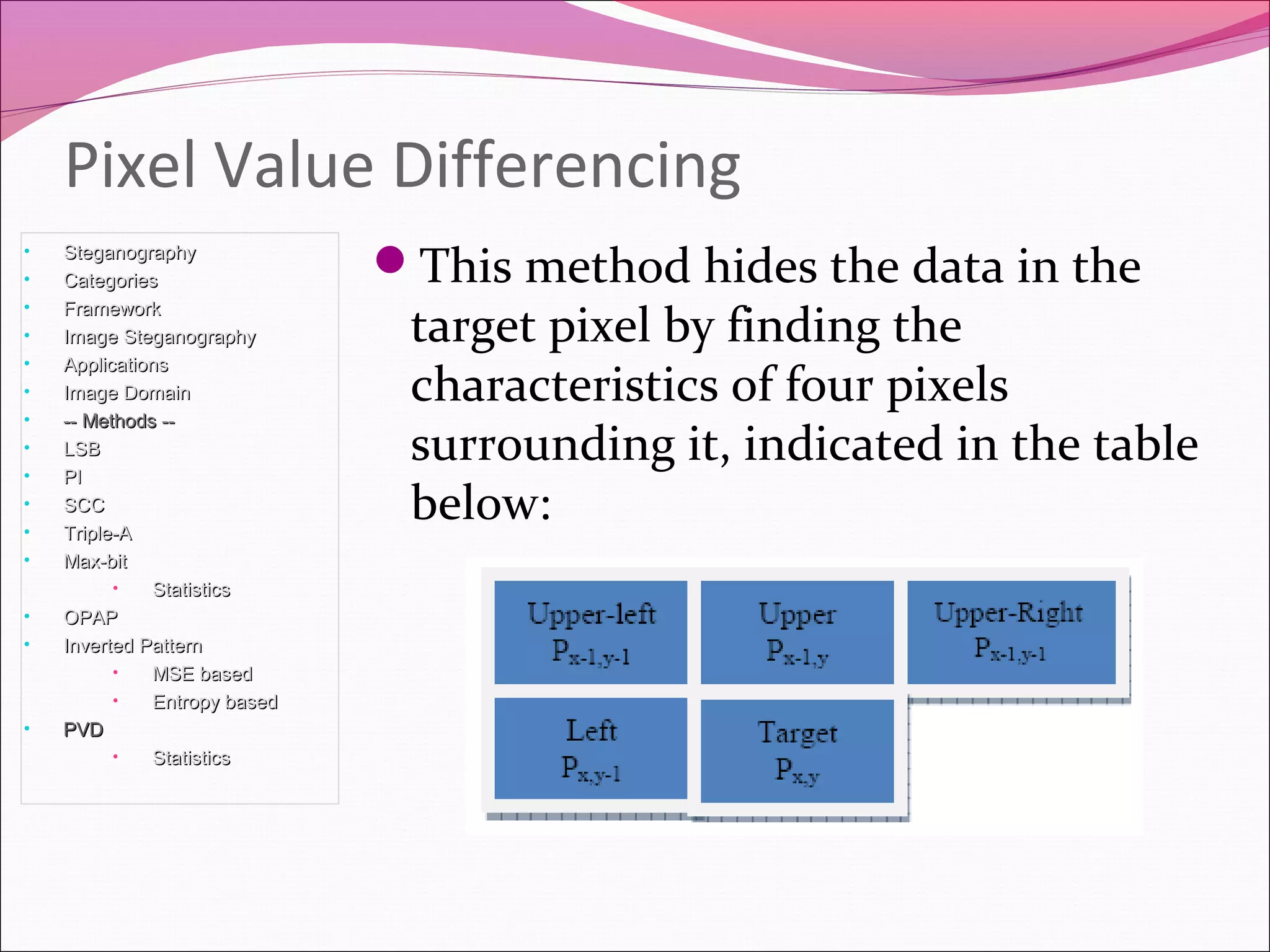
Pixel Value Differencing
• SteganographySteganography
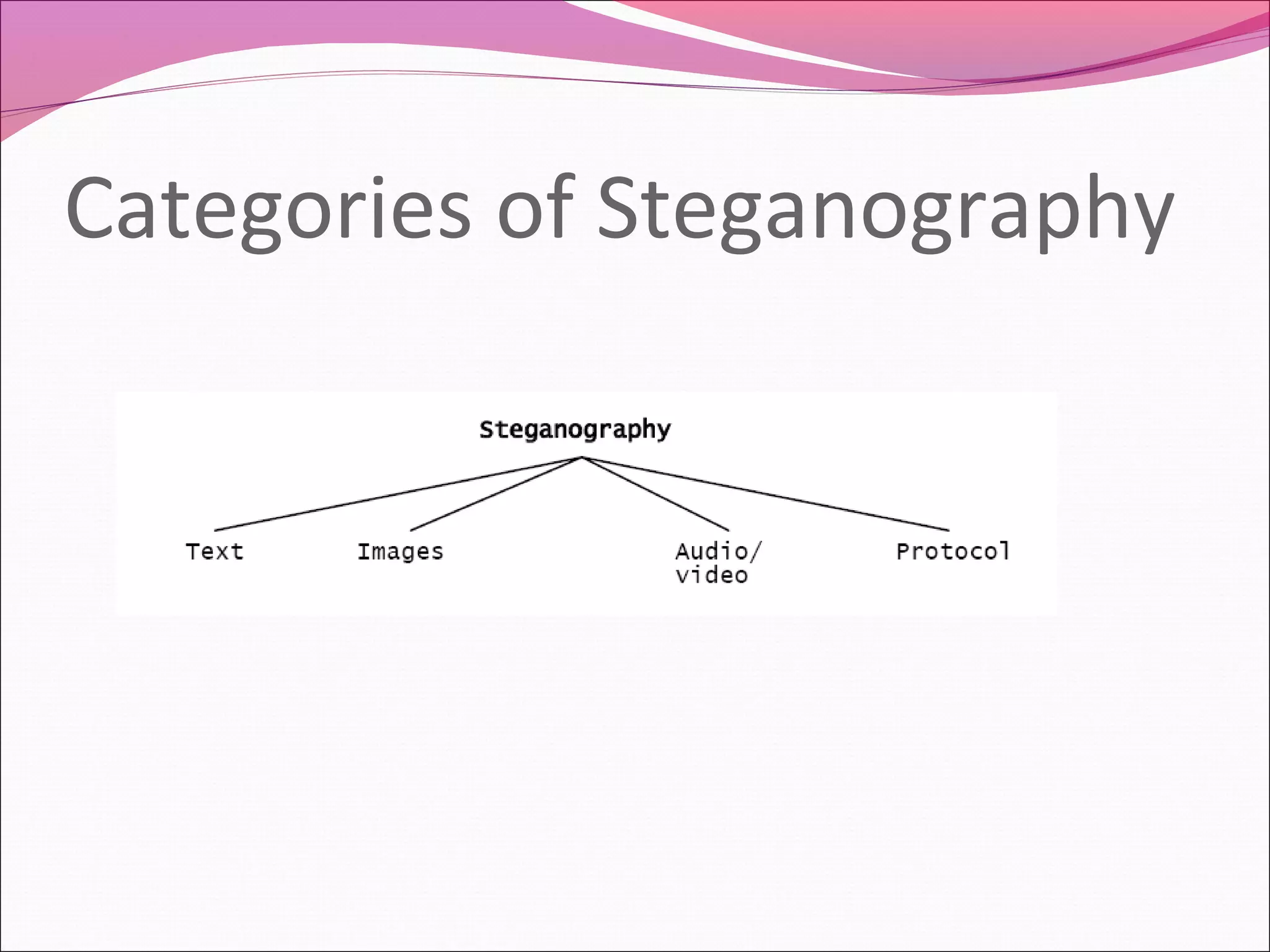
• CategoriesCategories
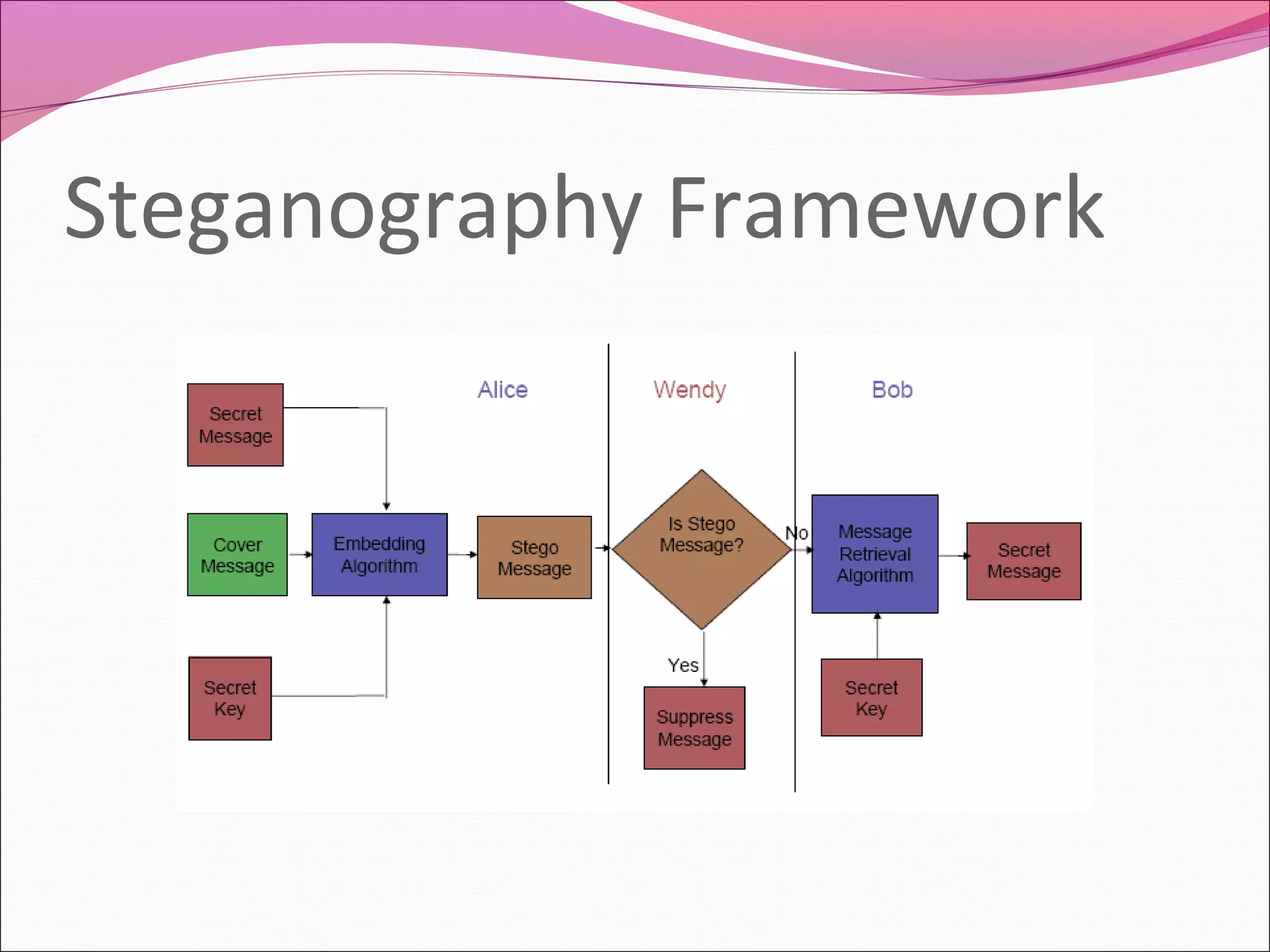
• FrameworkFramework
• Image SteganographyImage Steganography
• ApplicationsApplications
• Image DomainImage Domain
• -- Methods ---- Methods --
• LSBLSB
• PIPI
• SCCSCC
• Triple-ATriple-A
• Max-bitMax-bit
• StatisticsStatistics
• OPAPOPAP
• Inverted PatternInverted Pattern
• MSE basedMSE based
• Entropy basedEntropy based
• PVDPVD
• StatisticsStatistics](https://image.slidesharecdn.com/imagestegnogrpahy-161212063812/75/Image-stegnogrpahy-muqeed-35-2048.jpg)