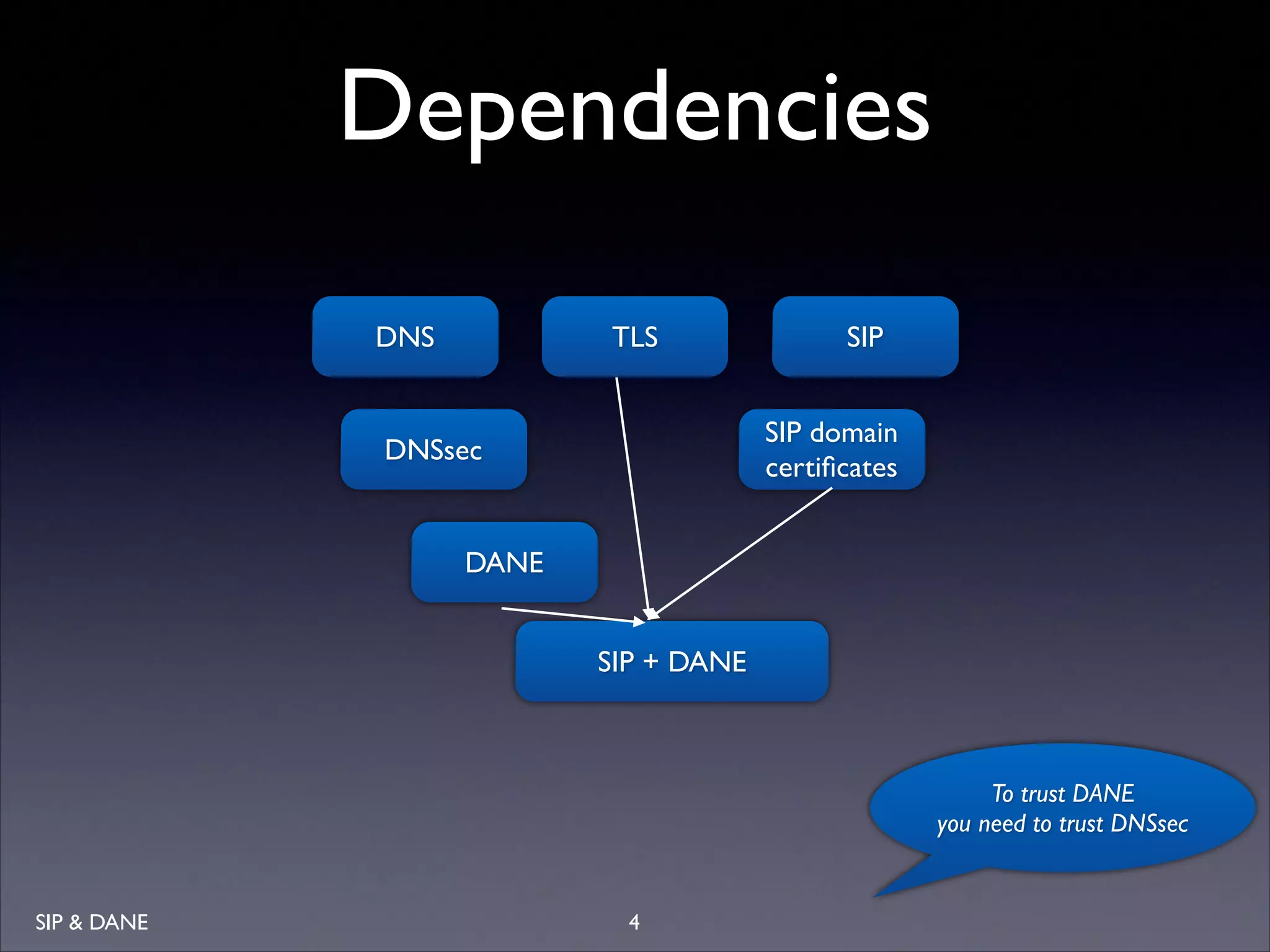
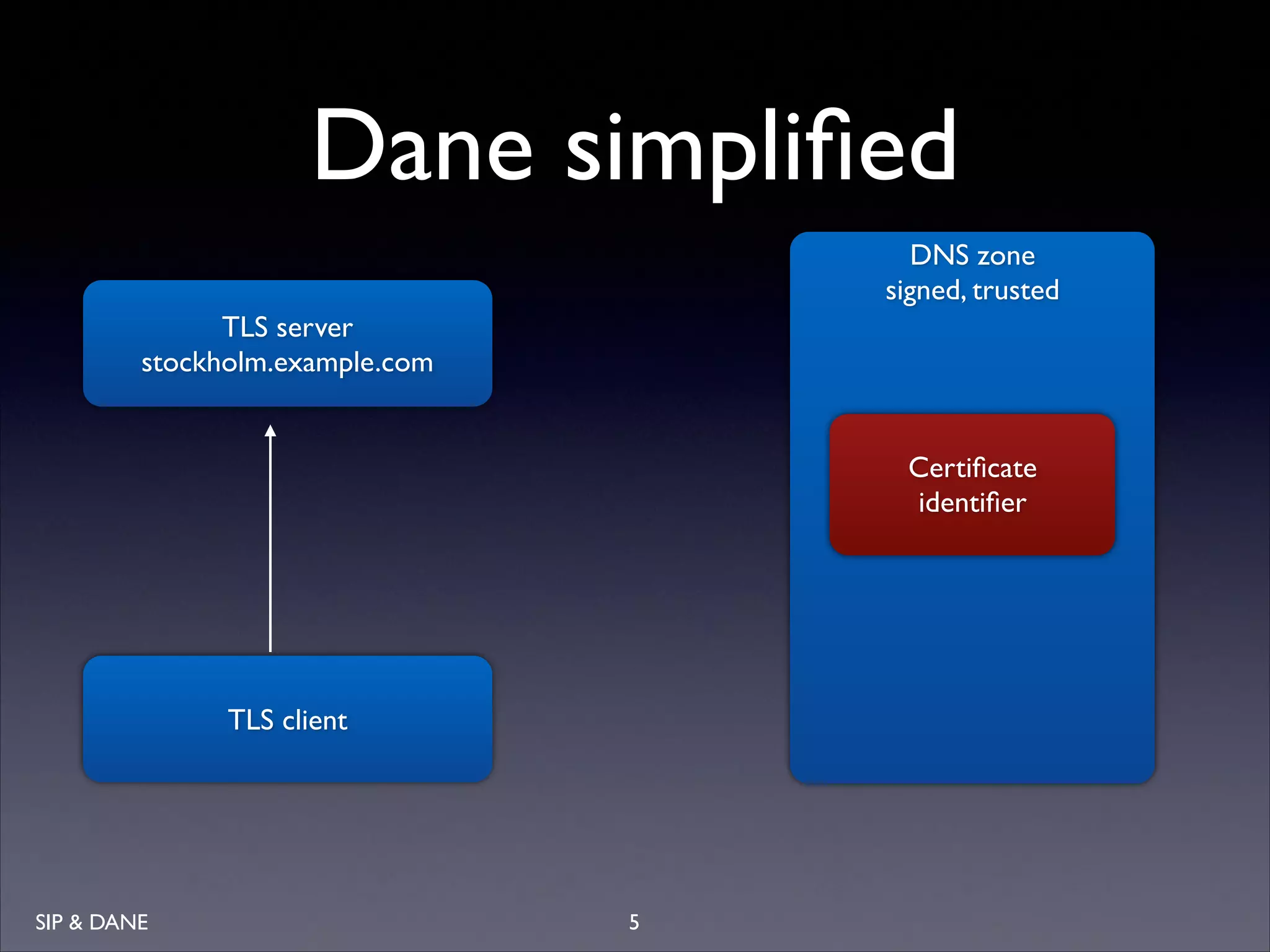
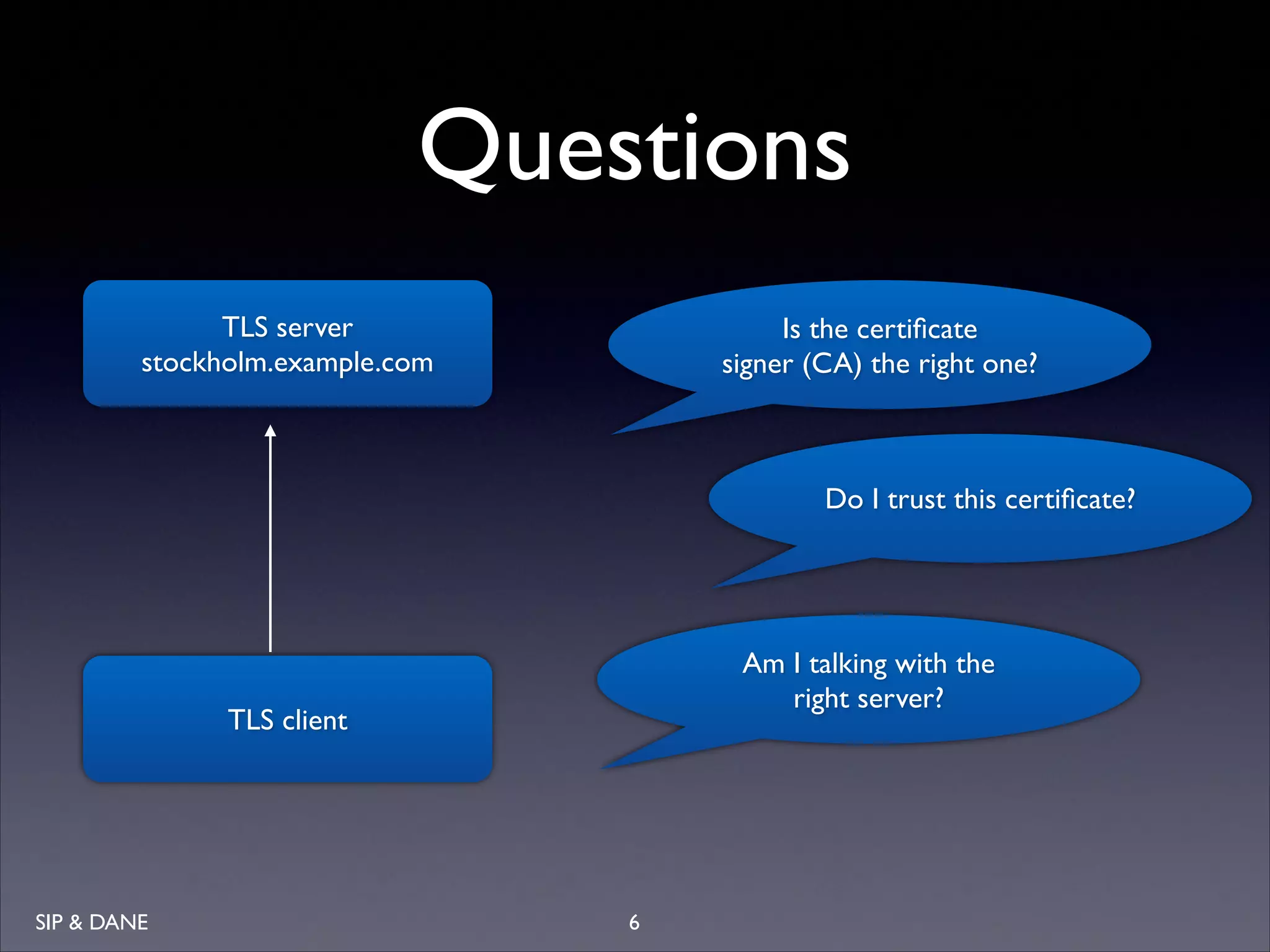
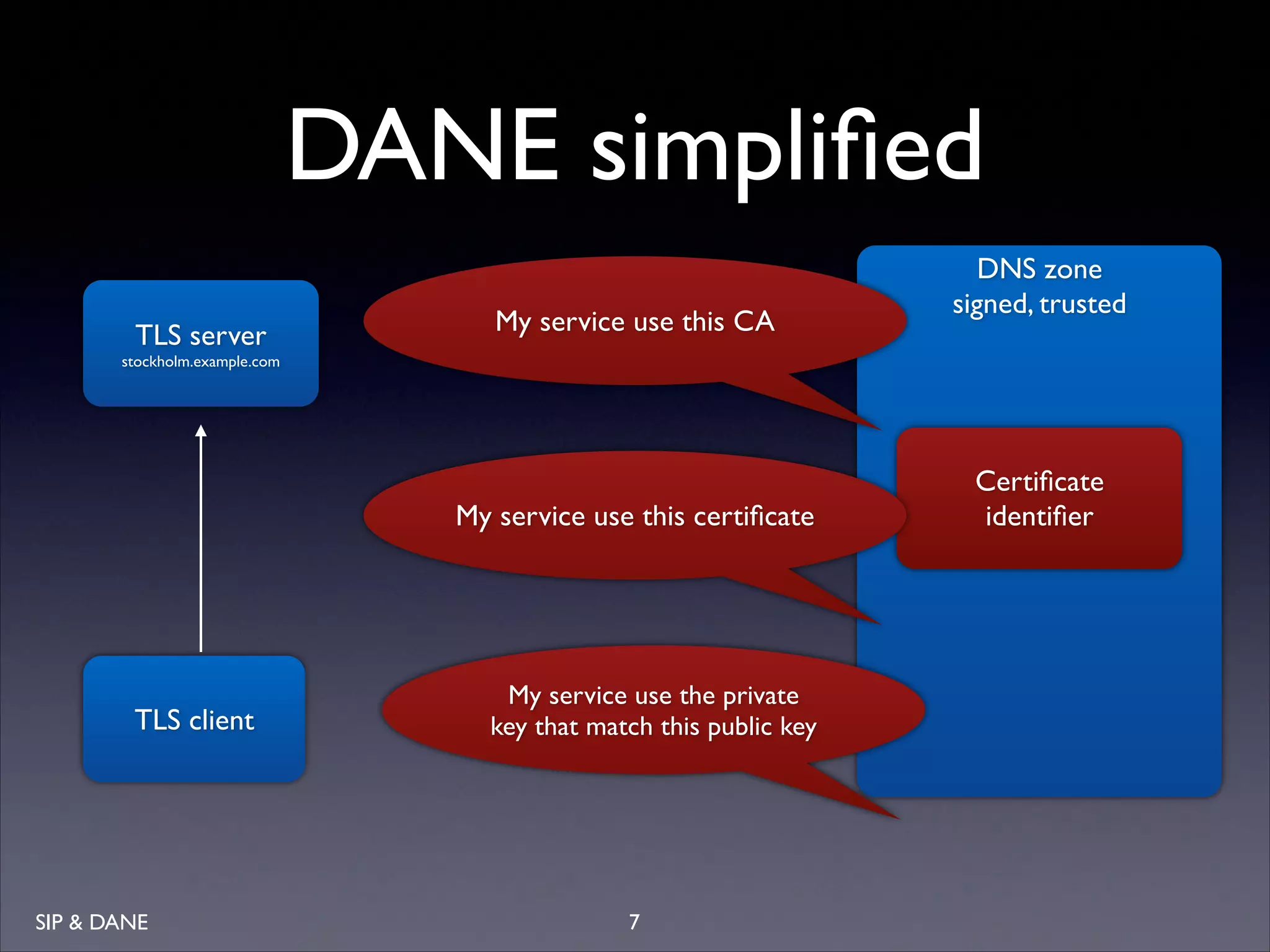
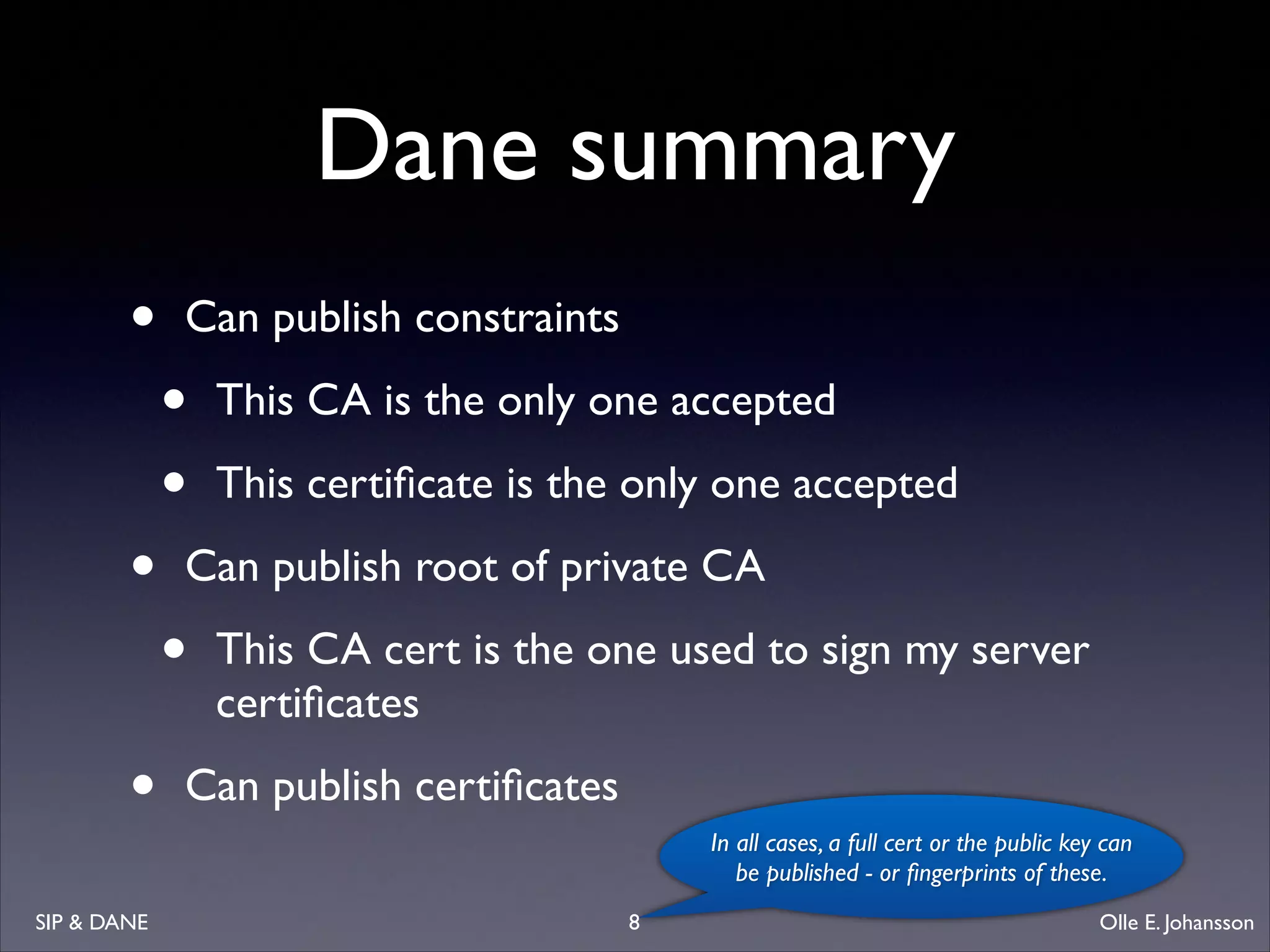
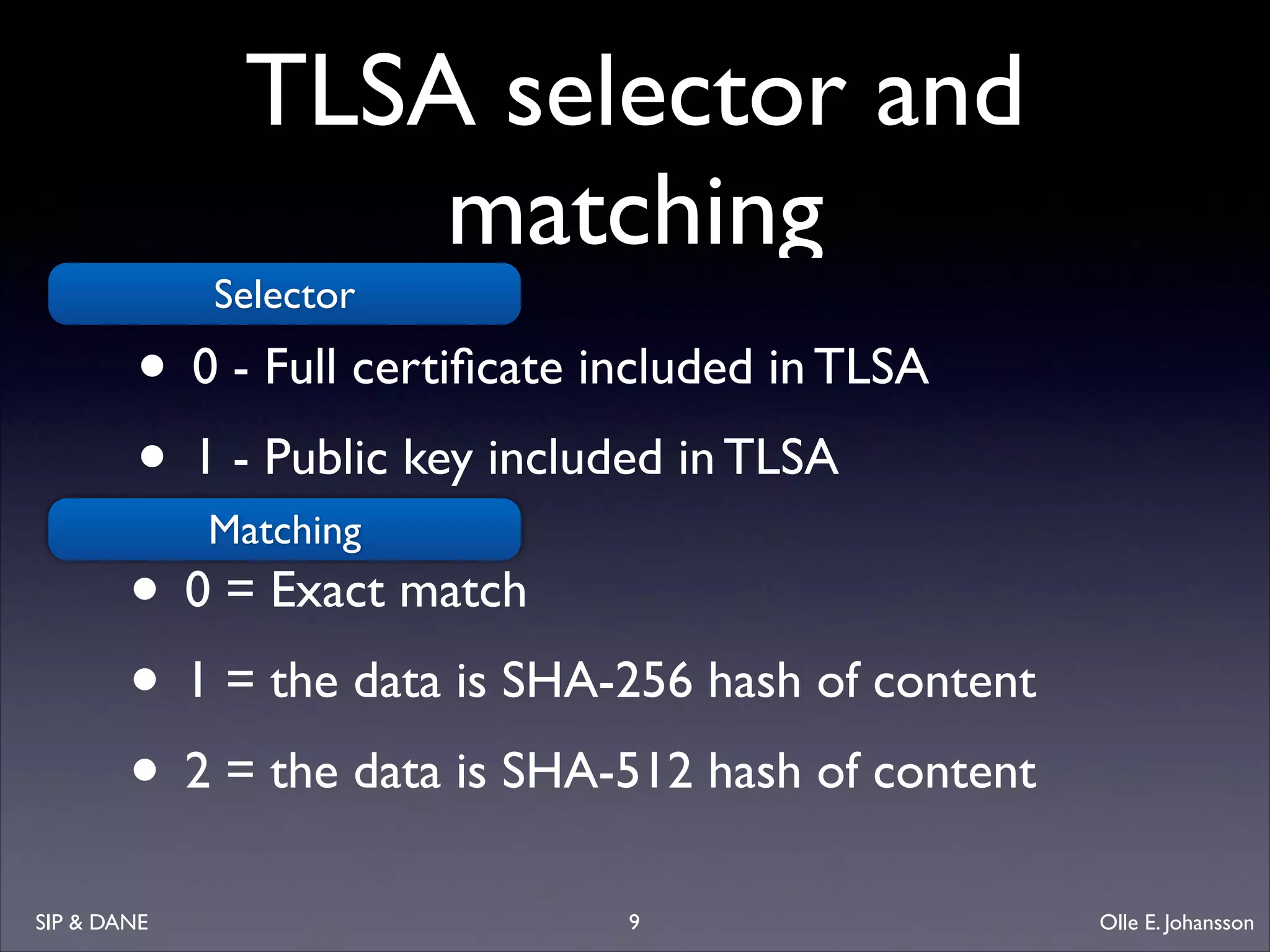
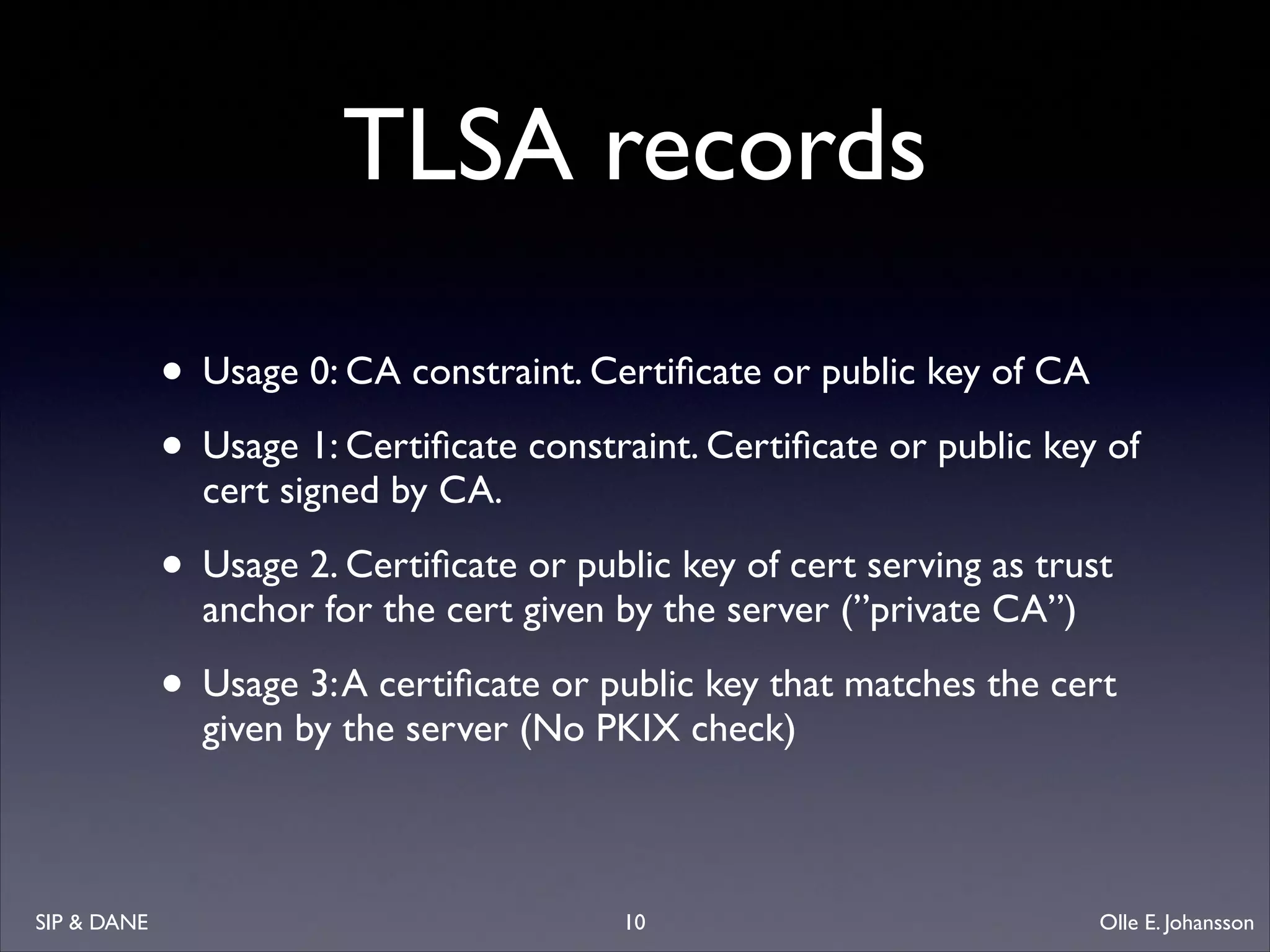
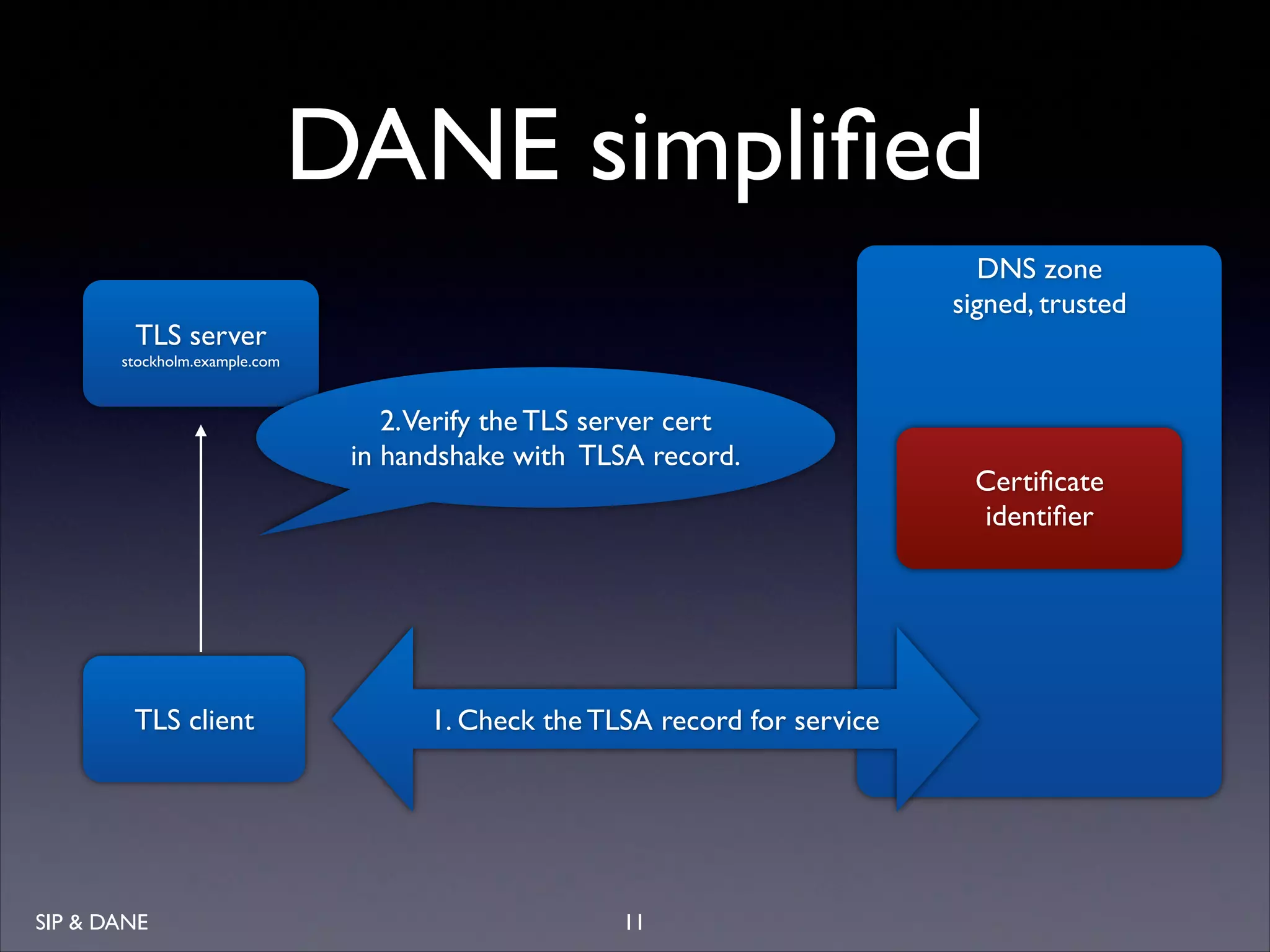
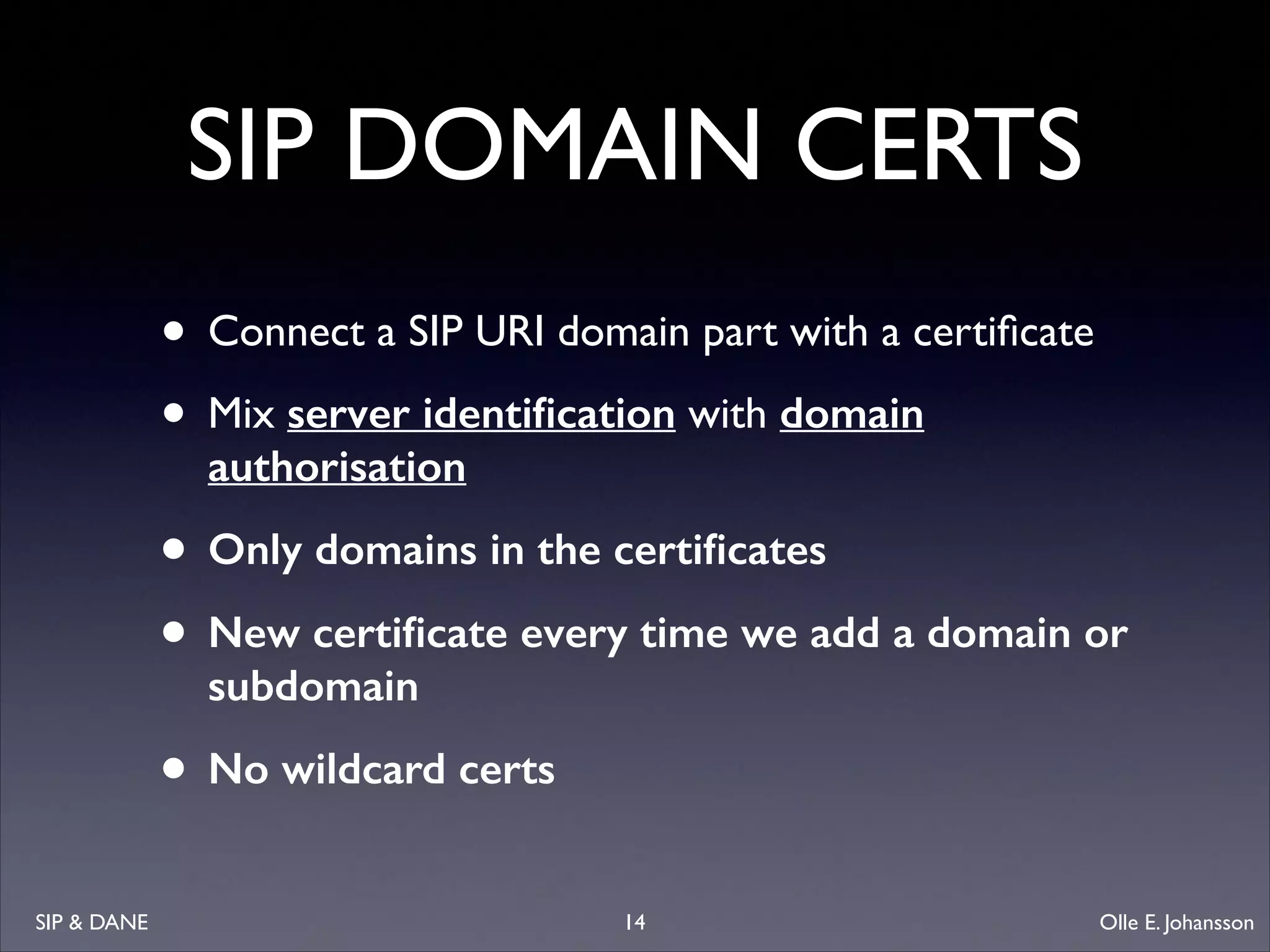
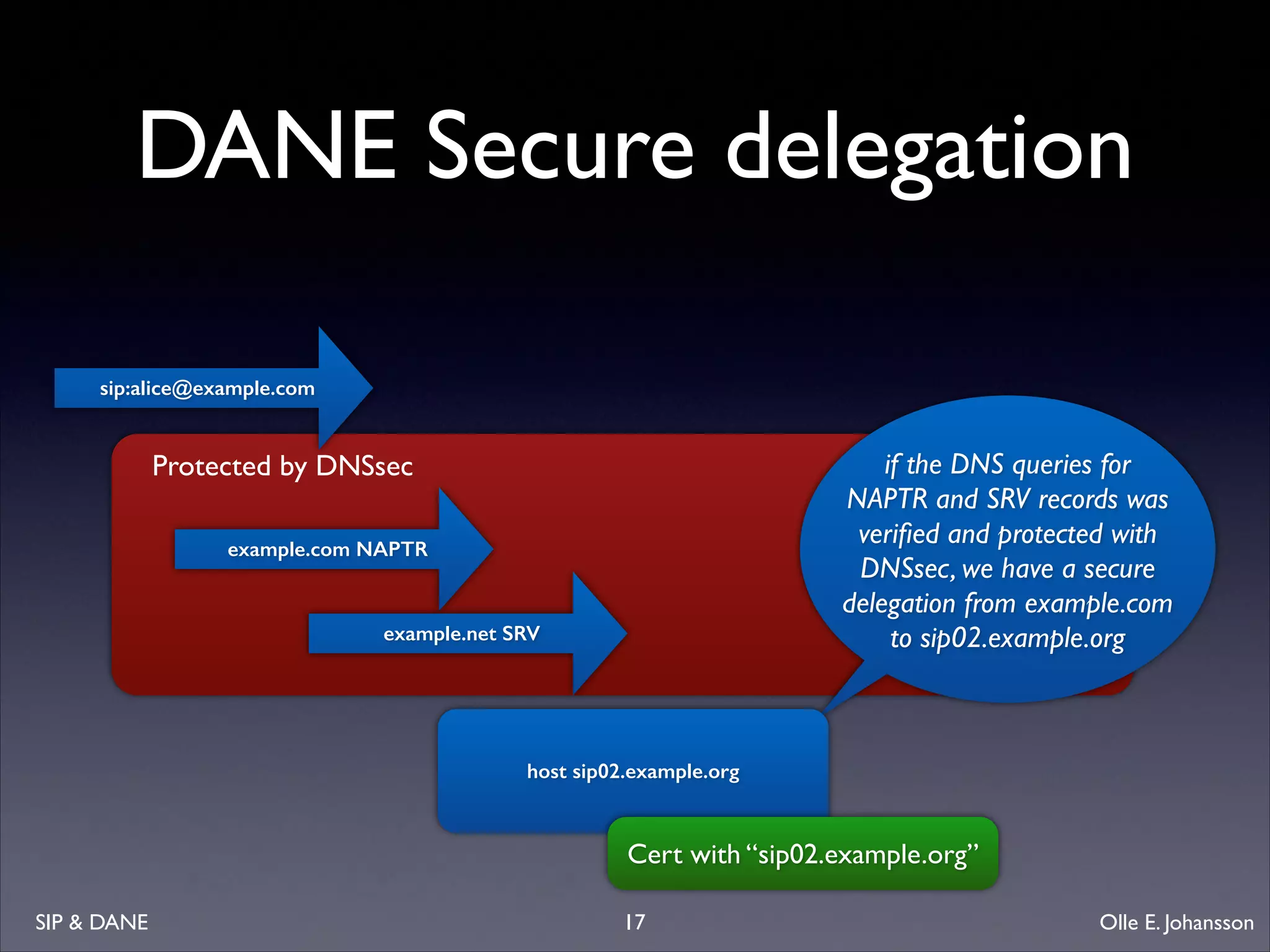
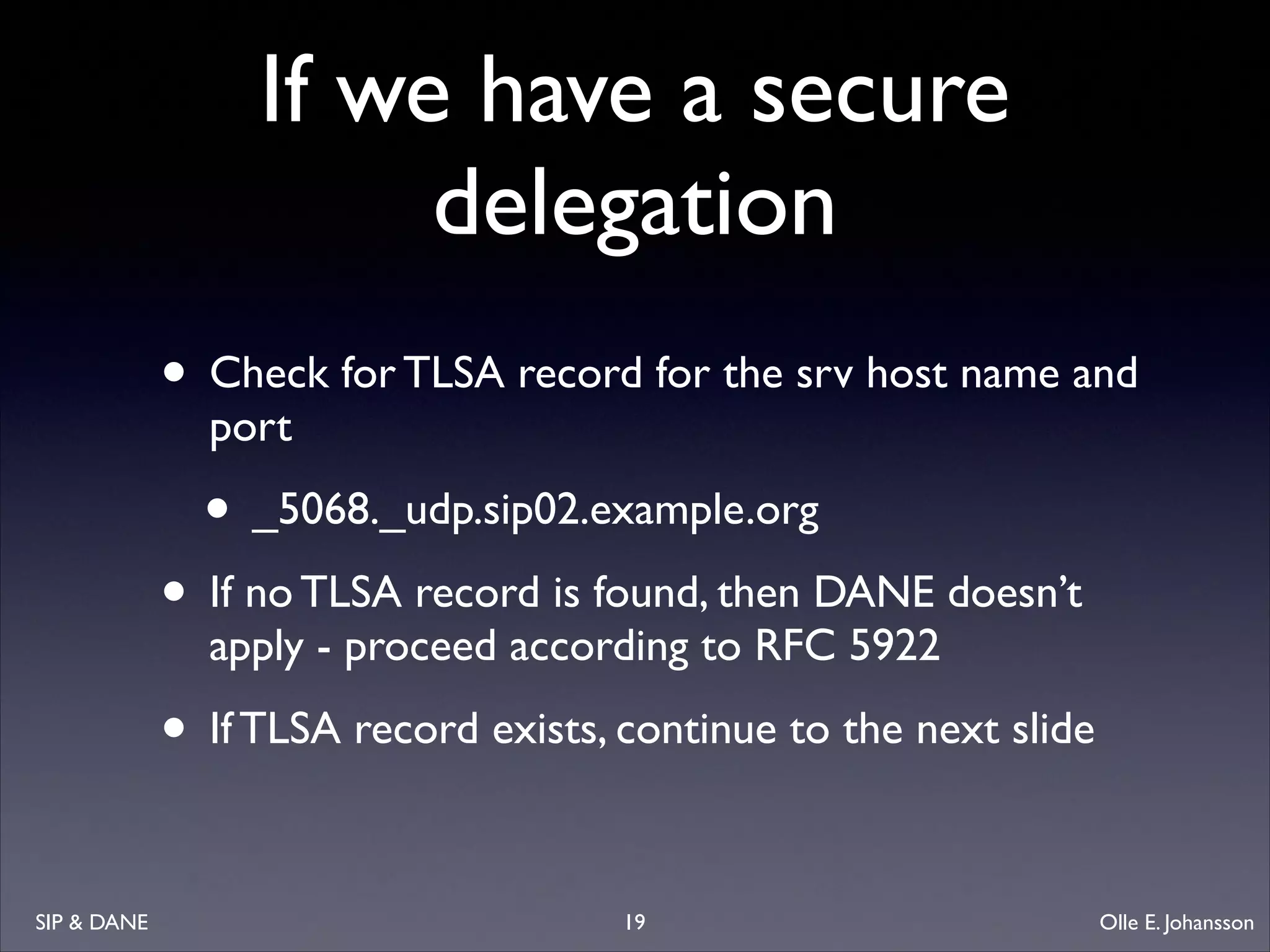
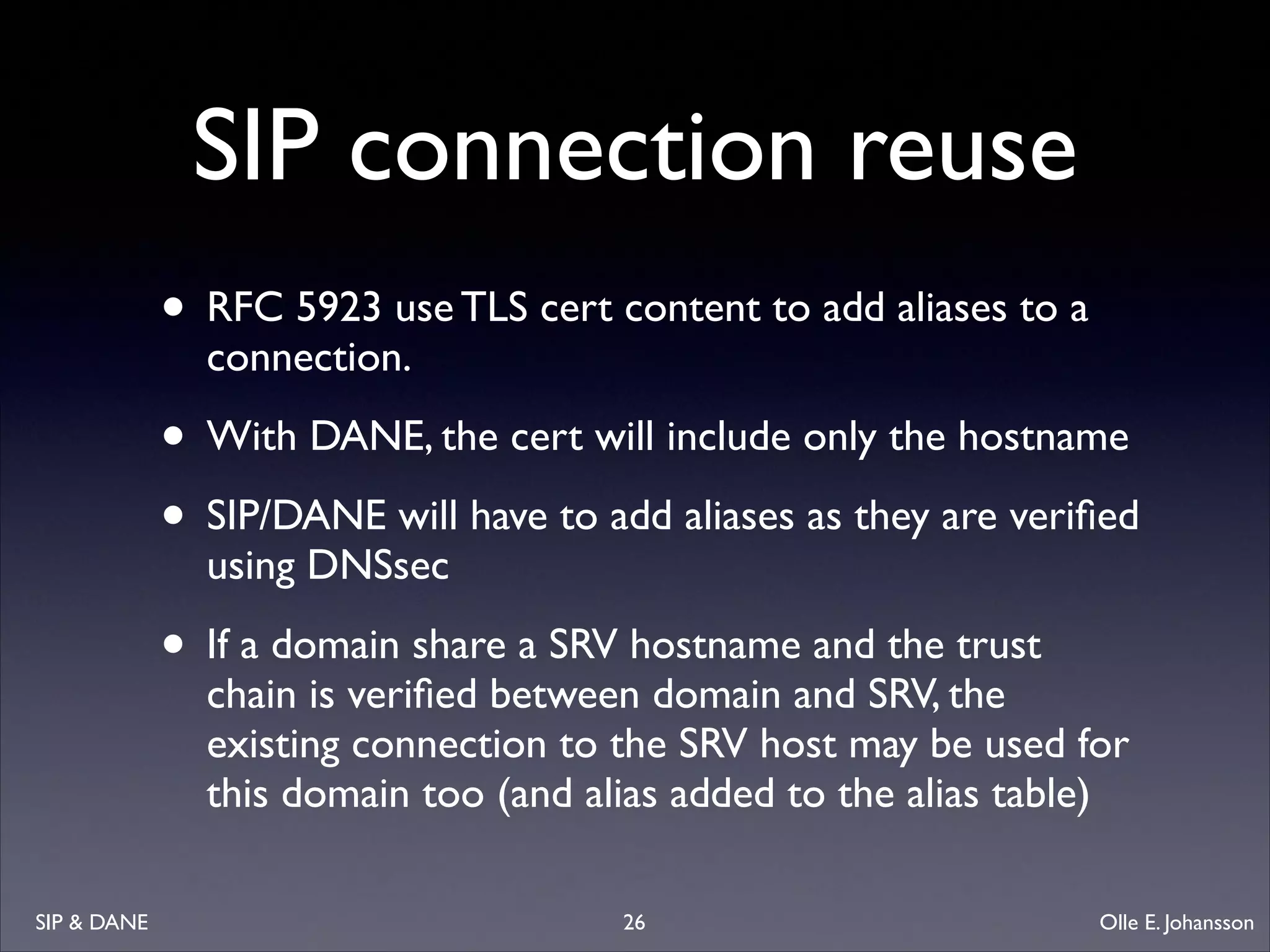
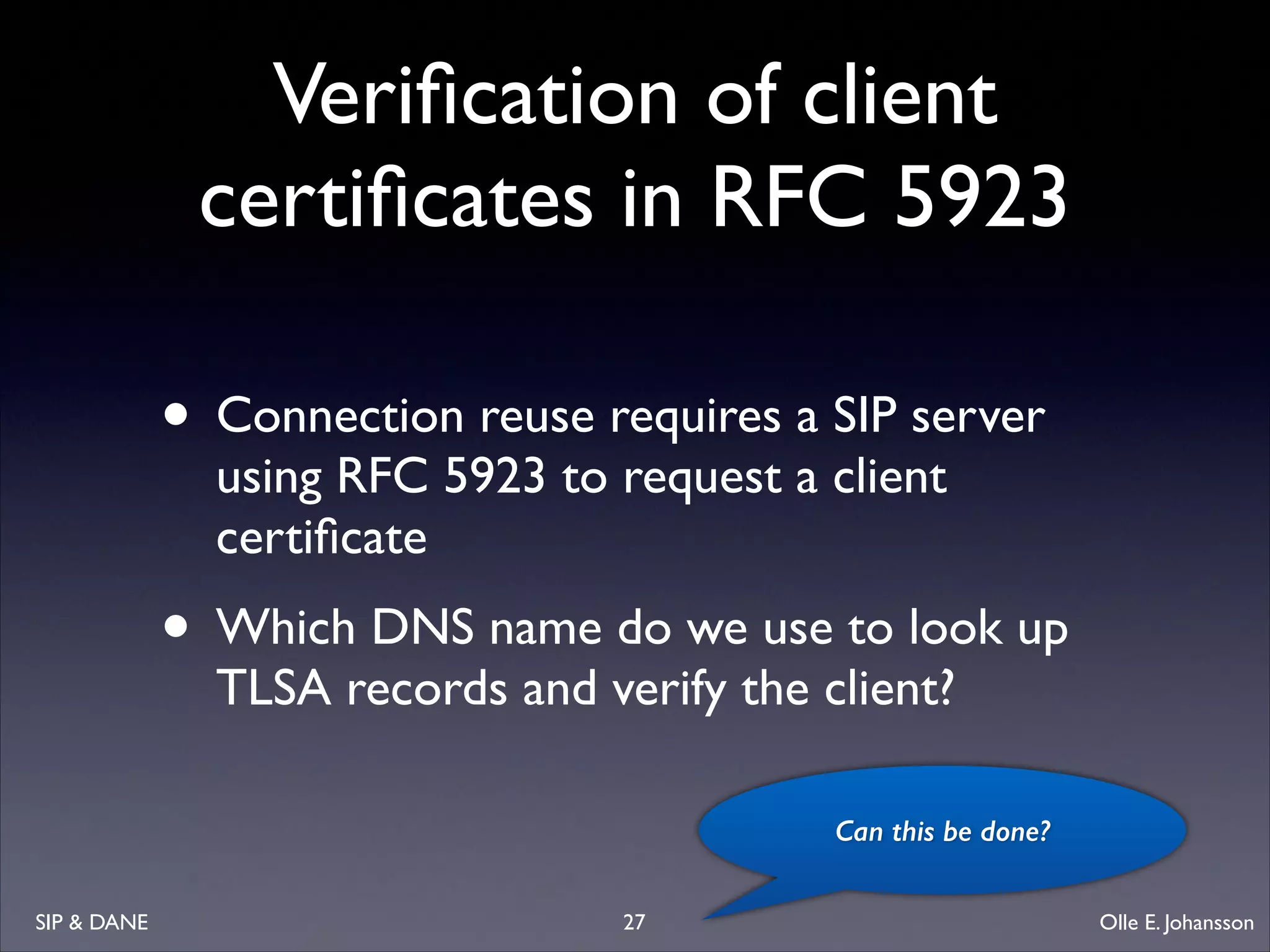
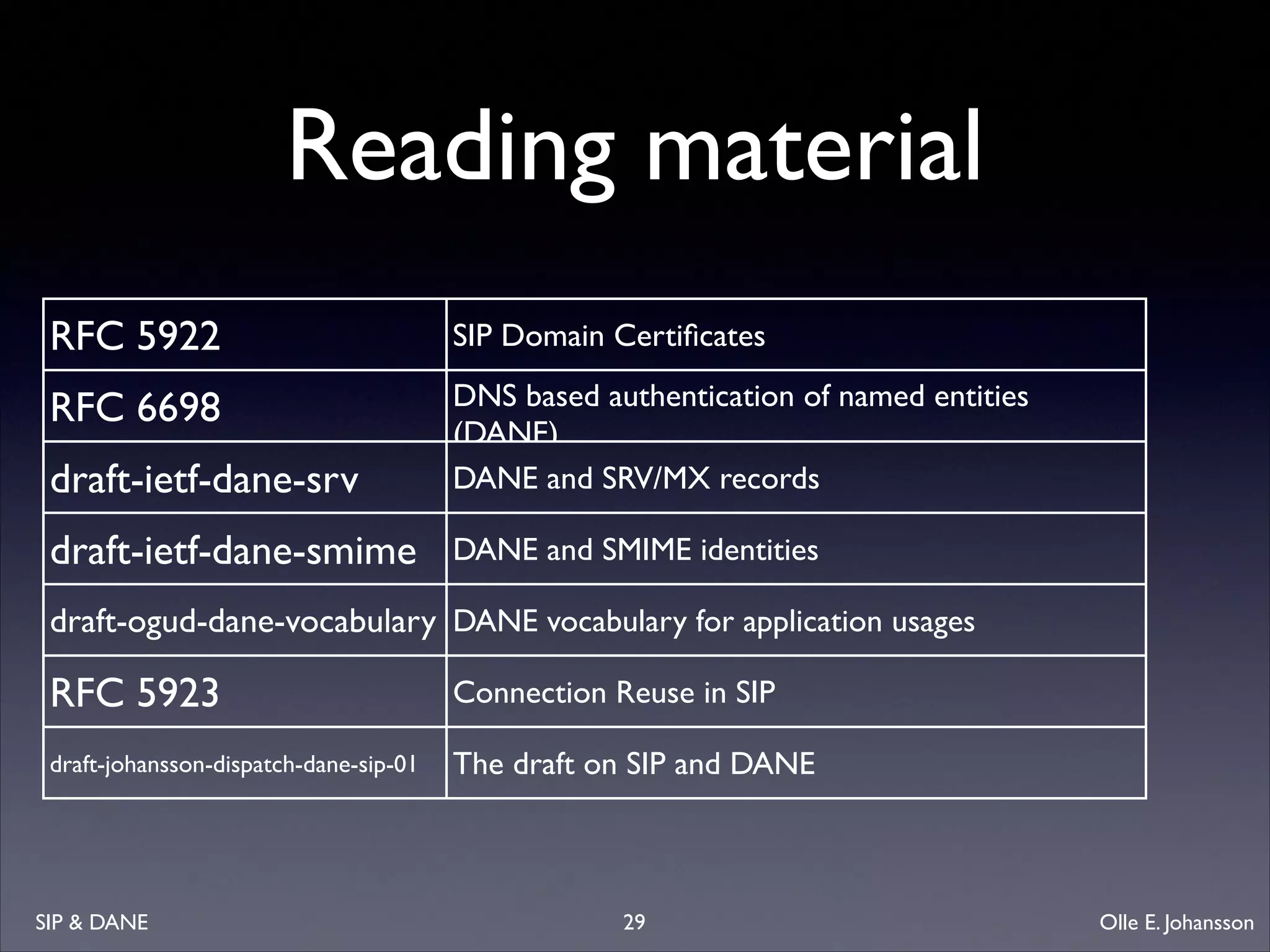
This document discusses the integration of SIP (Session Initiation Protocol) and DANE (DNS-Based Authentication of Named Entities) to enhance security by using DNSSEC for certificate validation. It outlines the approach for utilizing TLS (Transport Layer Security) certificates, DANE constraints, and the importance of secure delegation in DNS lookups for SIP communications. The author, Olle E. Johansson, emphasizes the need for proper validation to ensure secure connections between SIP clients and servers.