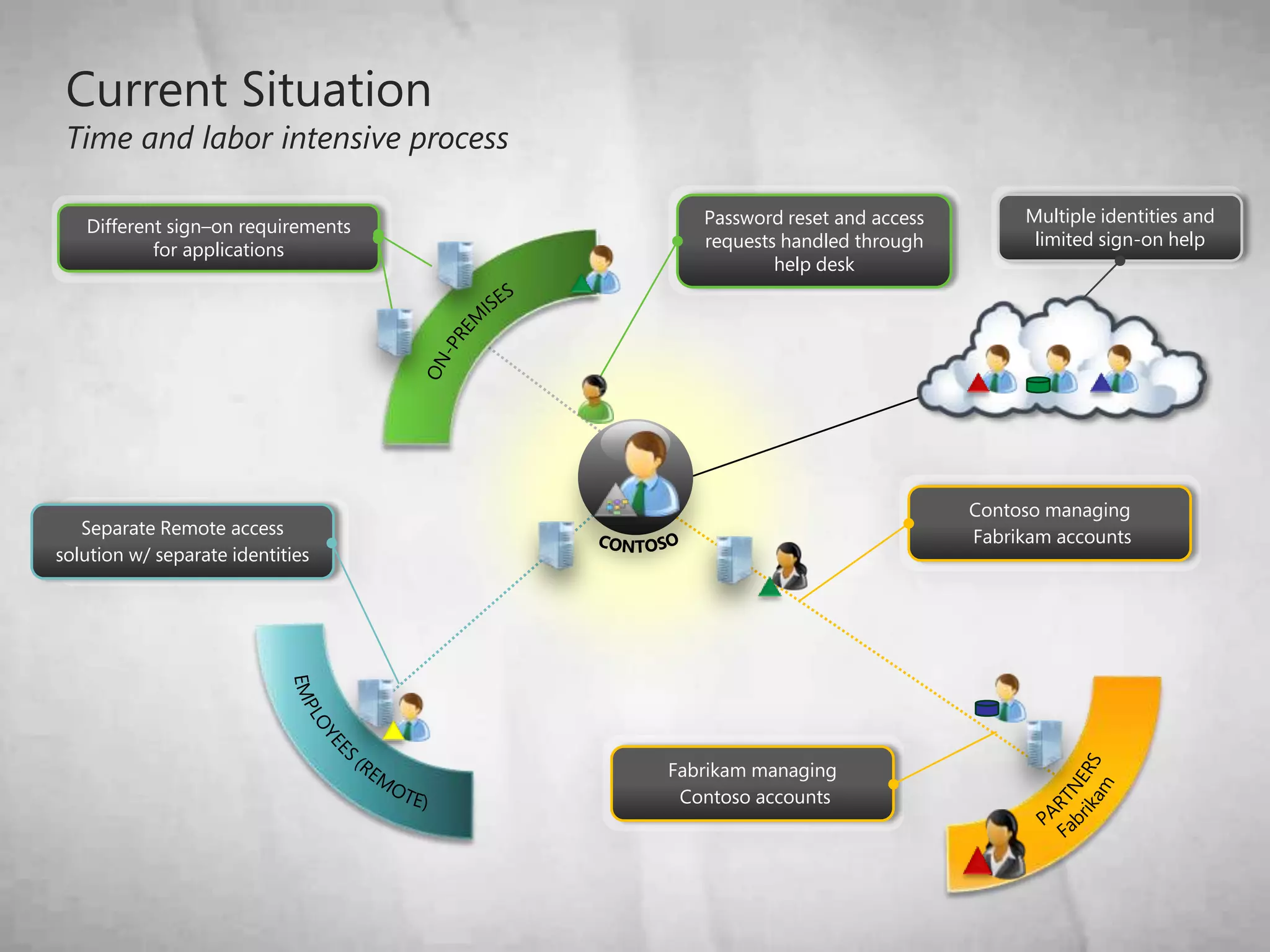
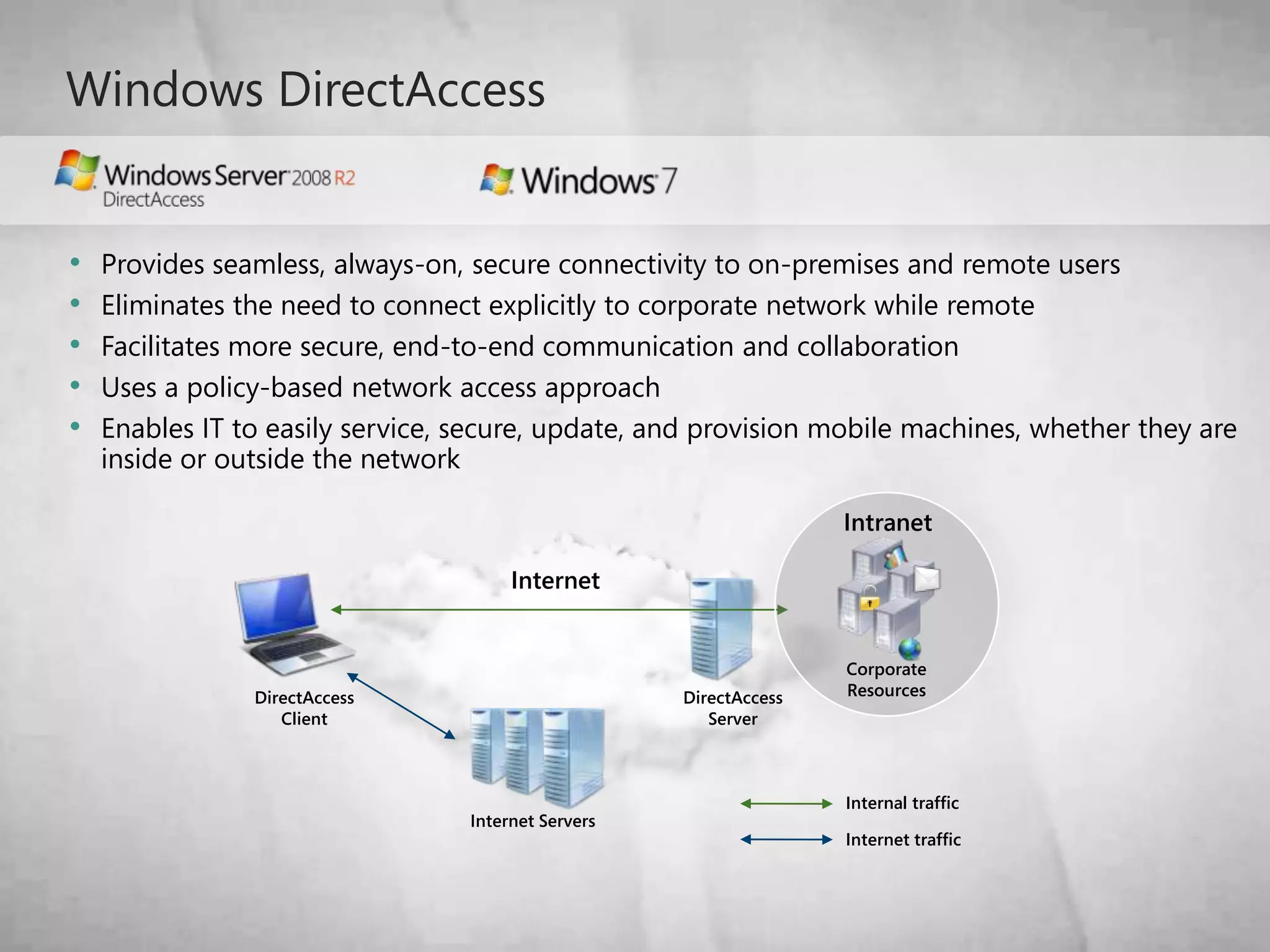
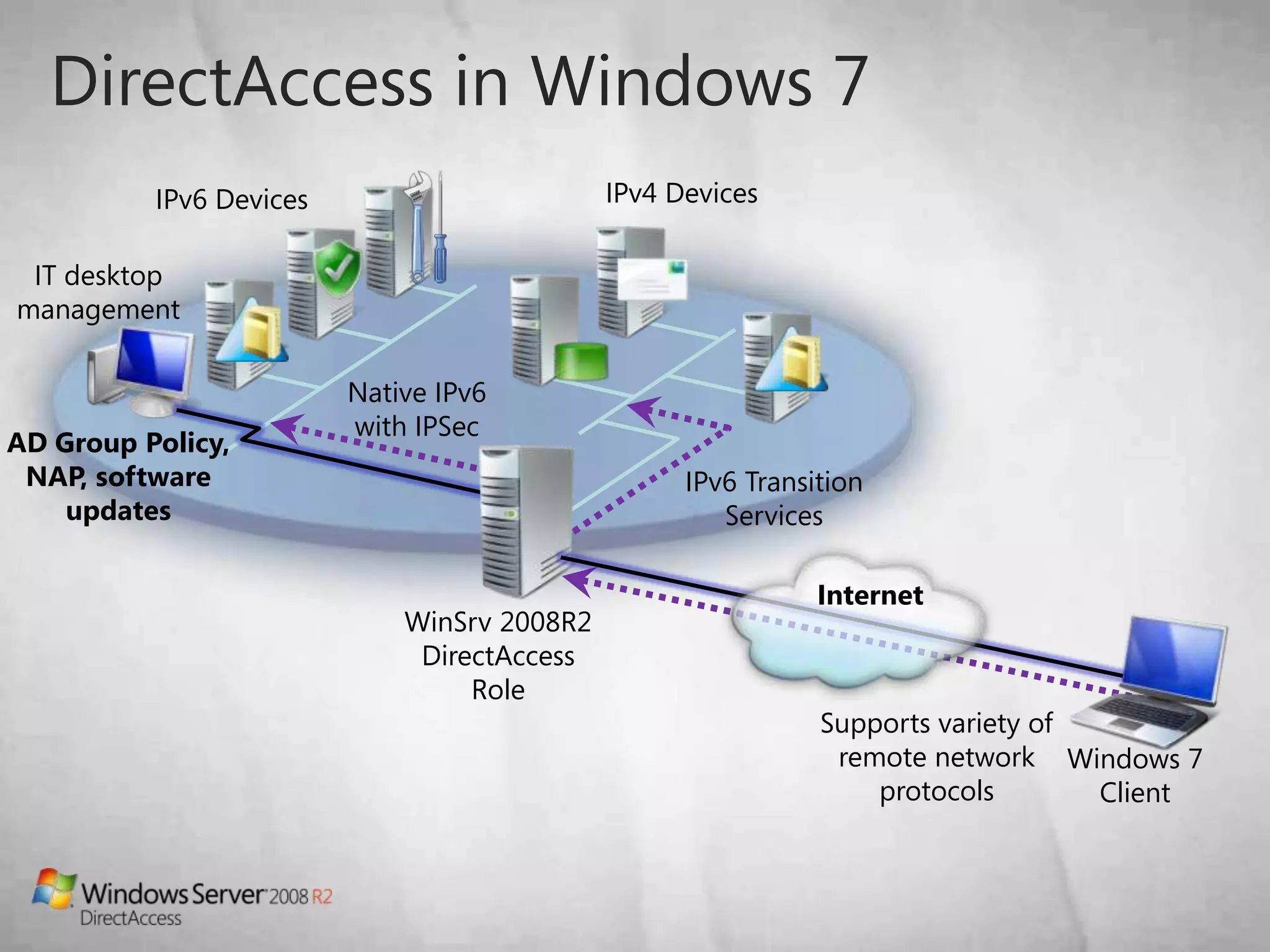
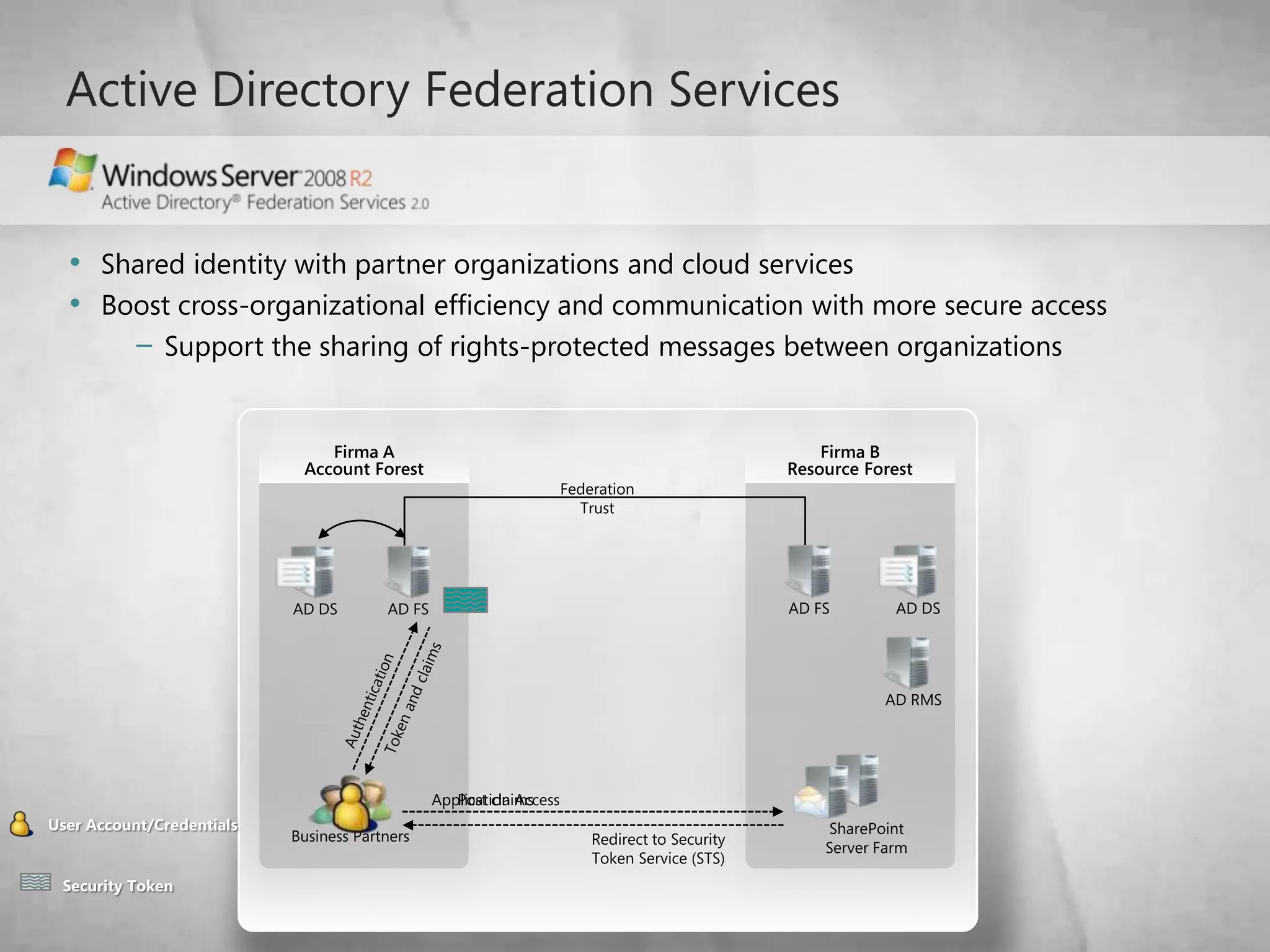
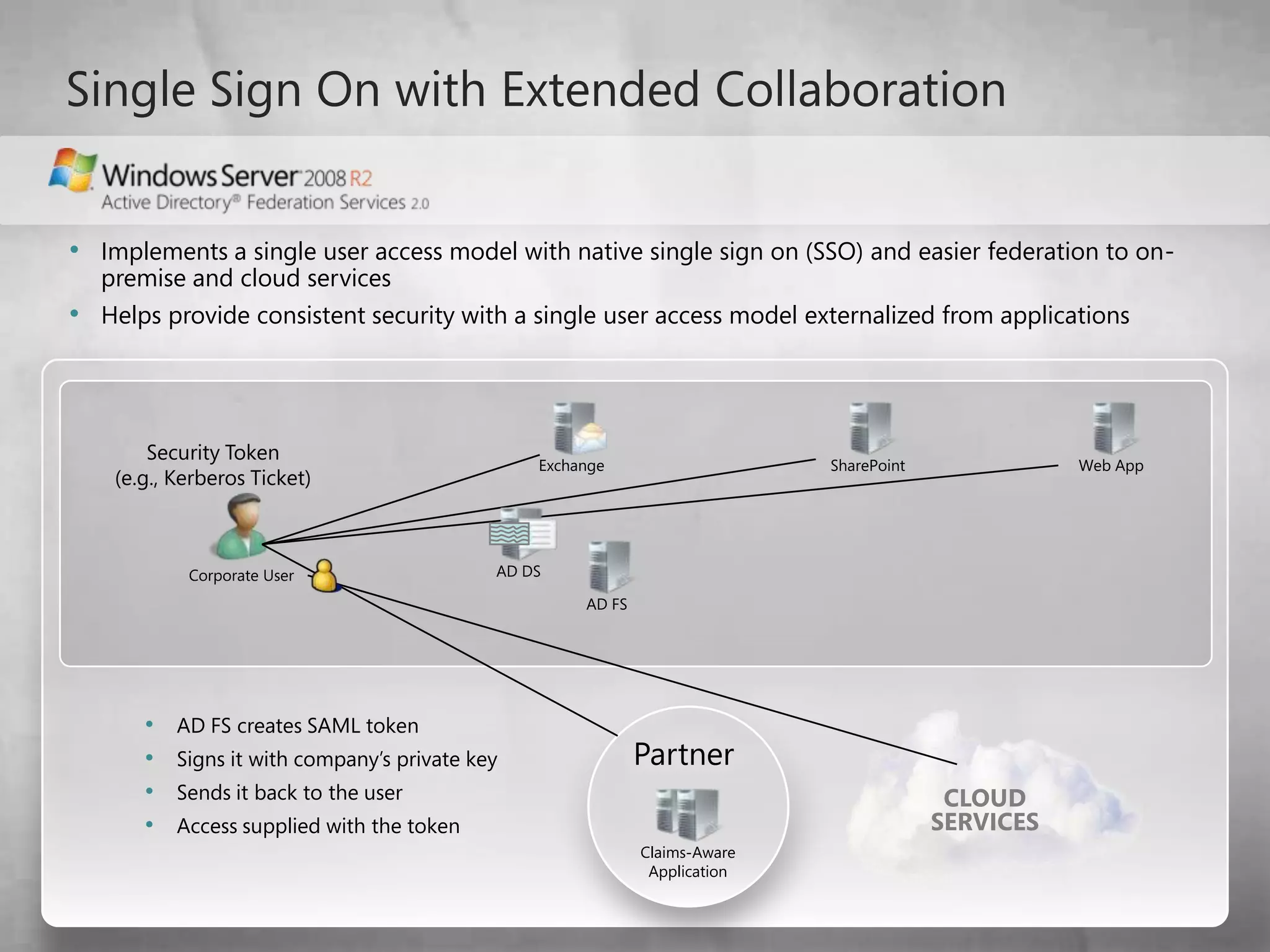
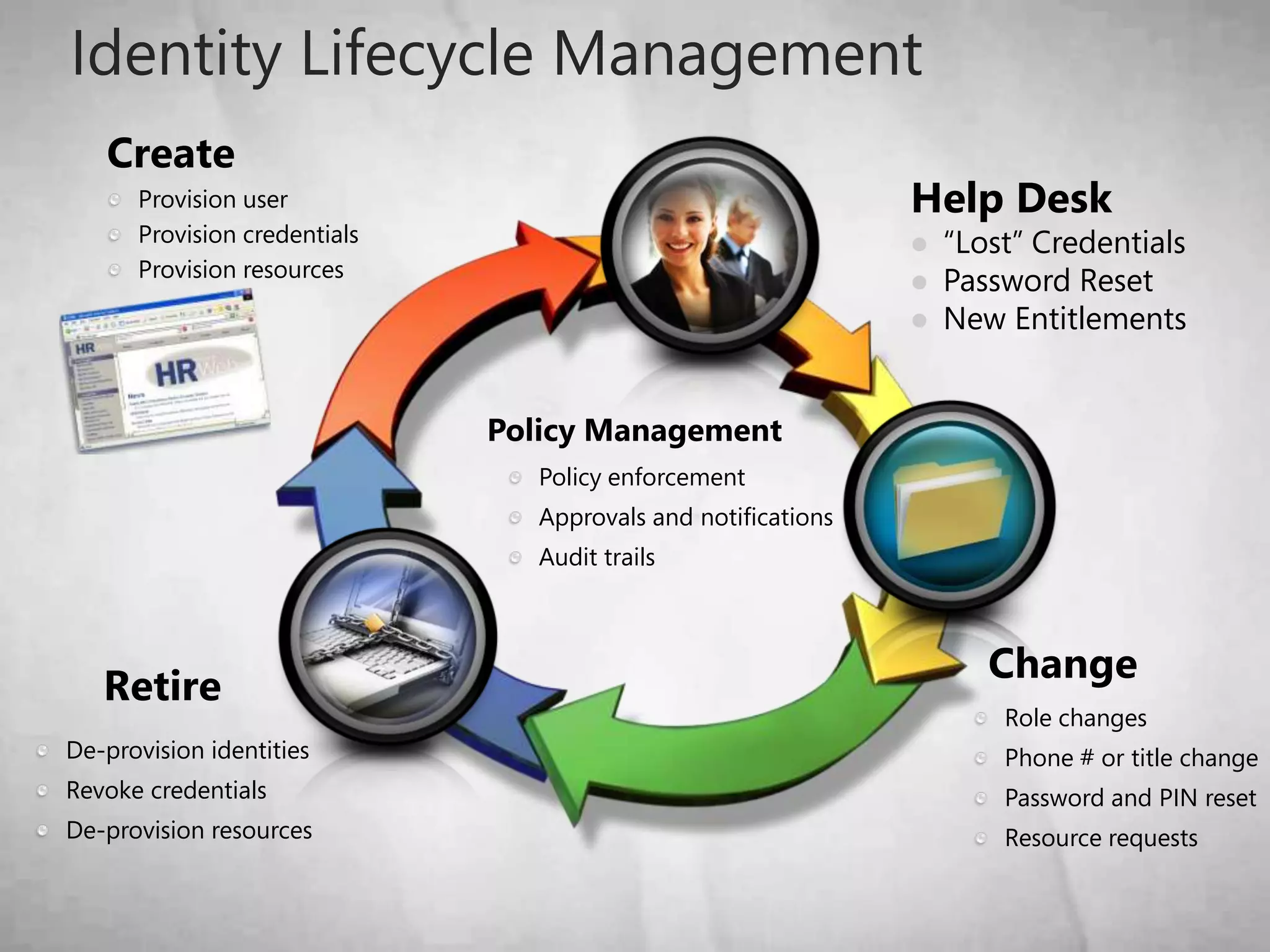
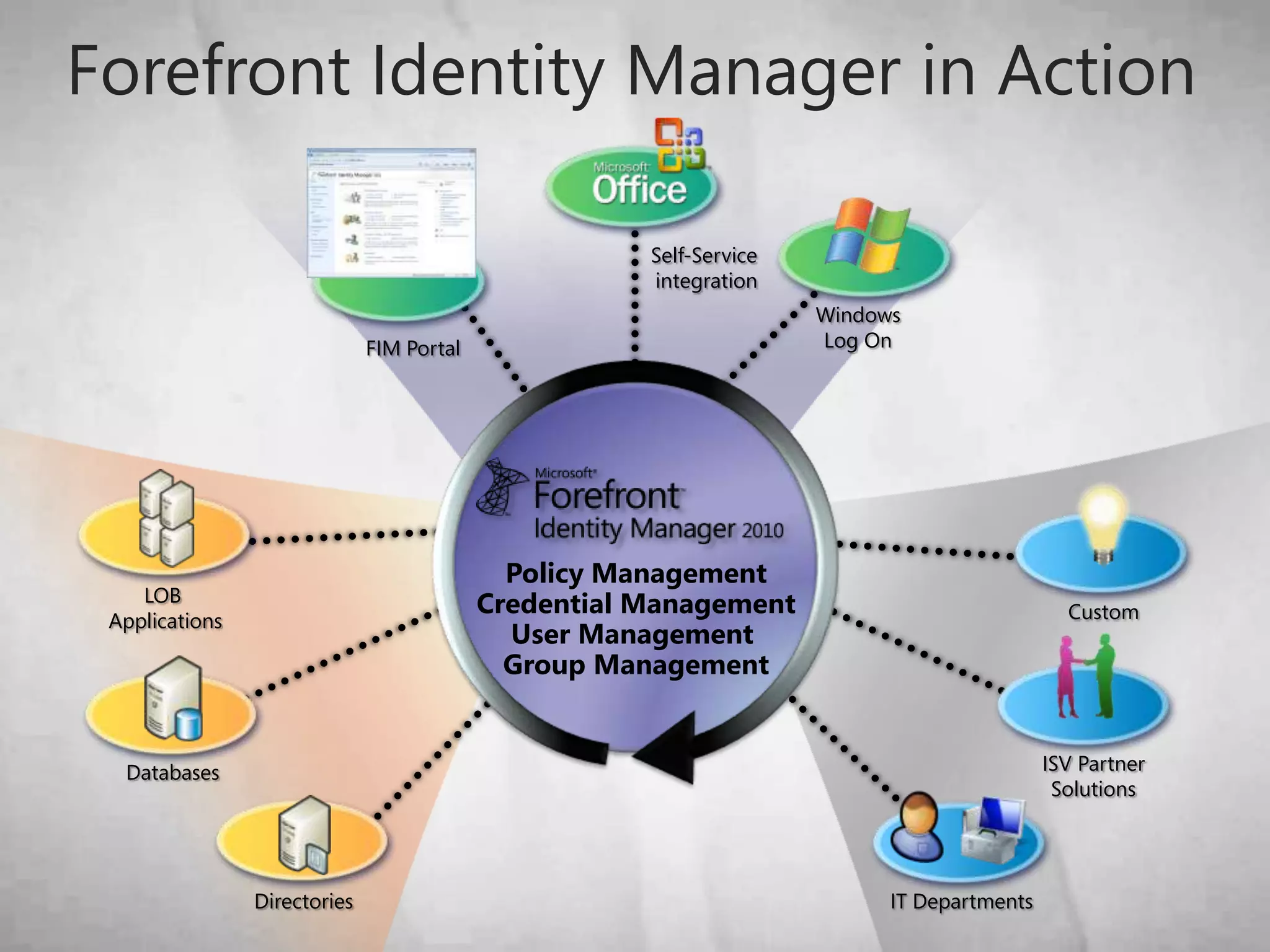
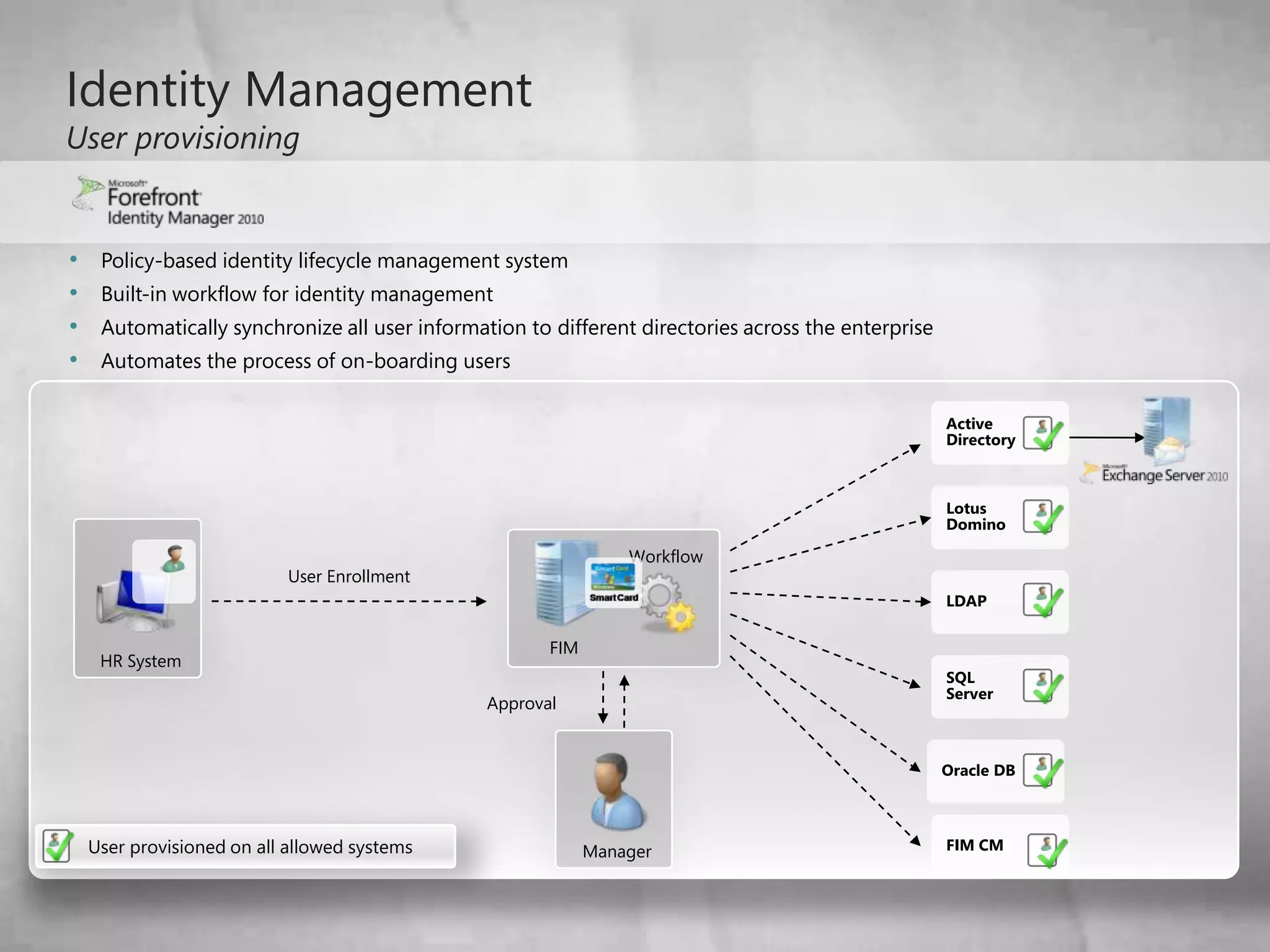
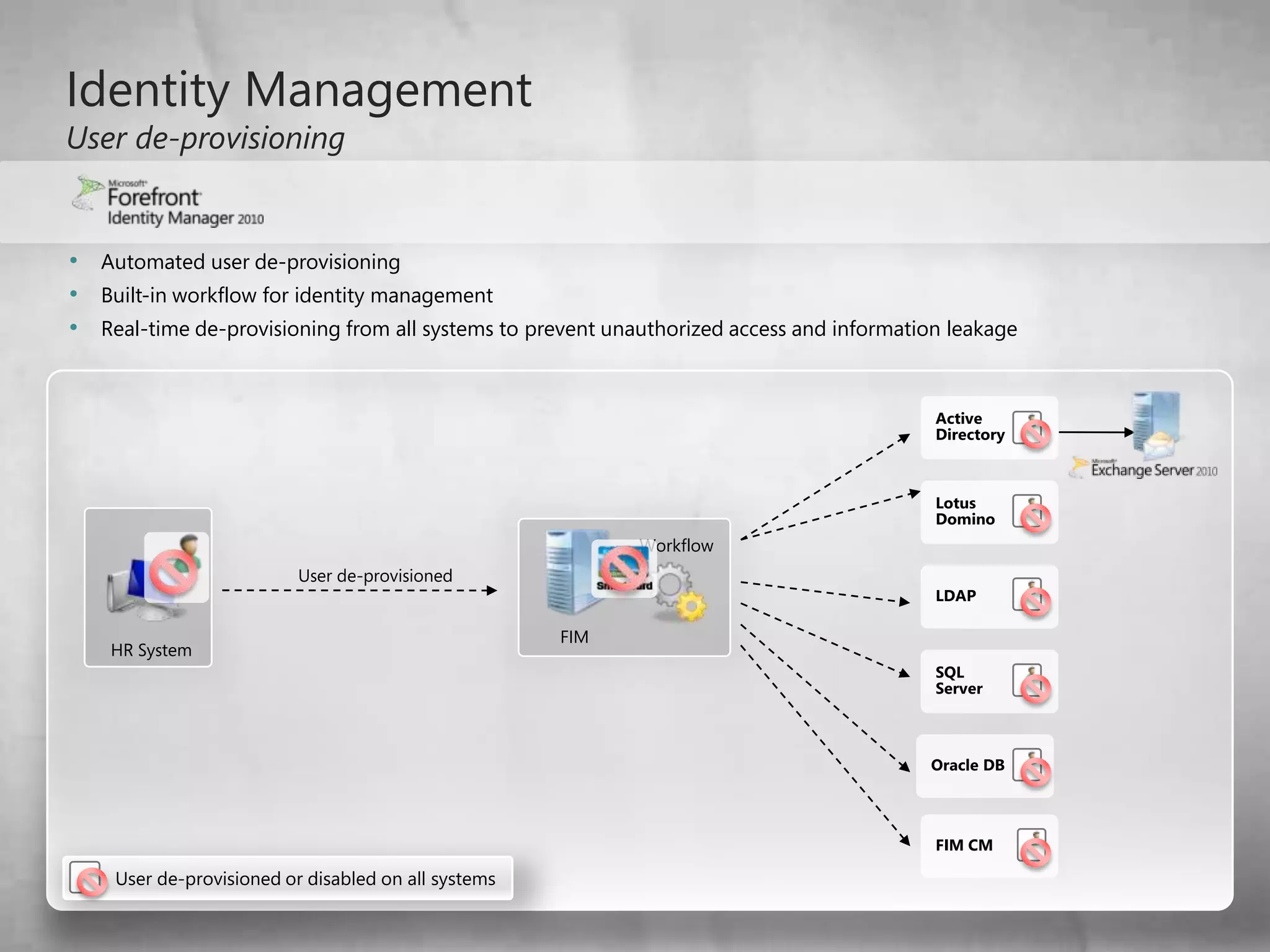
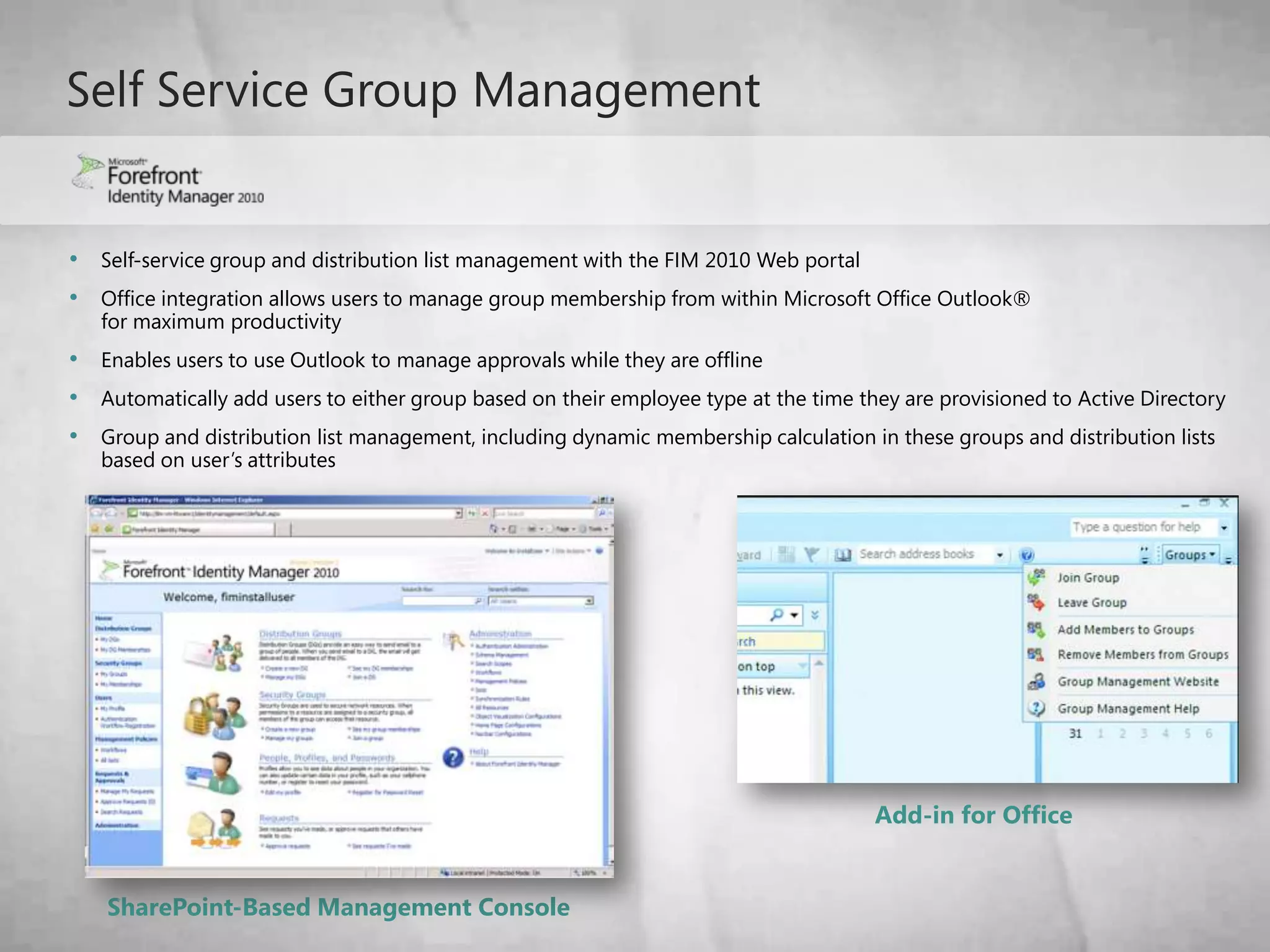
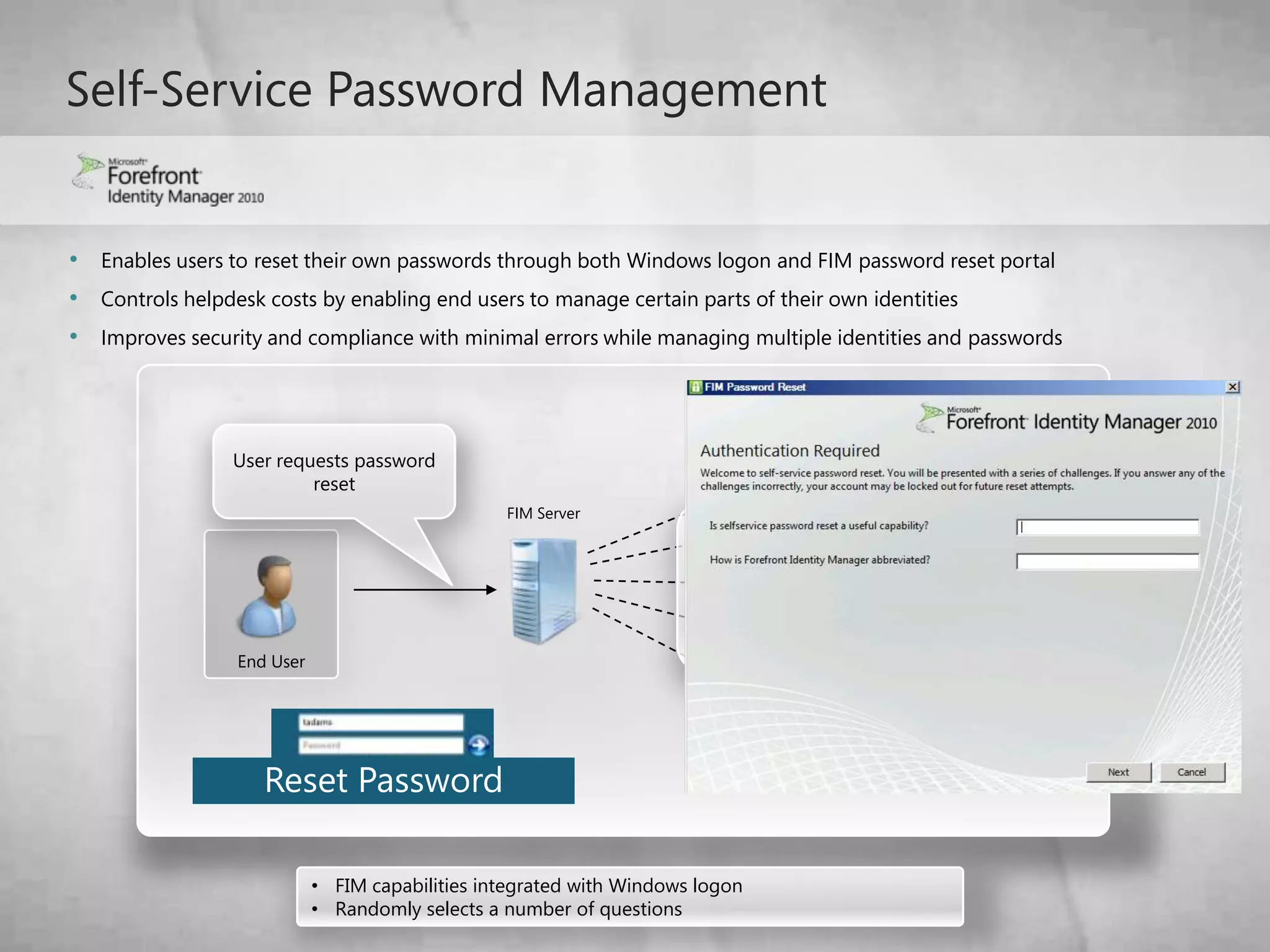
The document discusses Microsoft's Identity and Access Management solutions. It describes challenges with current systems that require time-intensive password resets and separate identities for different applications. The solutions proposed integrate on-premises and cloud-based applications, simplify management through automation and self-service, and provide secure access from any device through single sign-on. Features include direct access for remote users, active directory federation services for partner organizations, and Forefront Identity Manager for automated user lifecycle management.