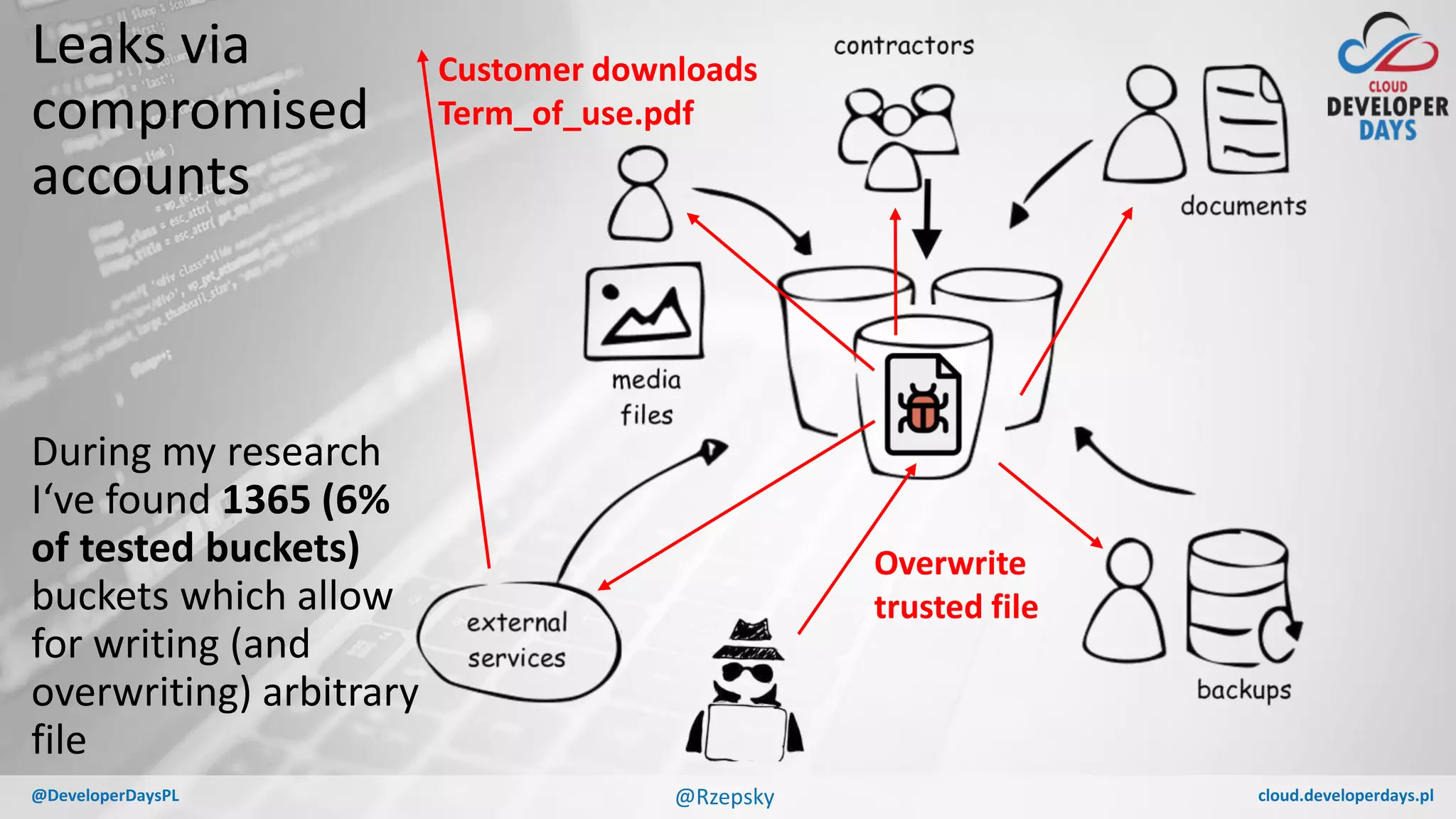
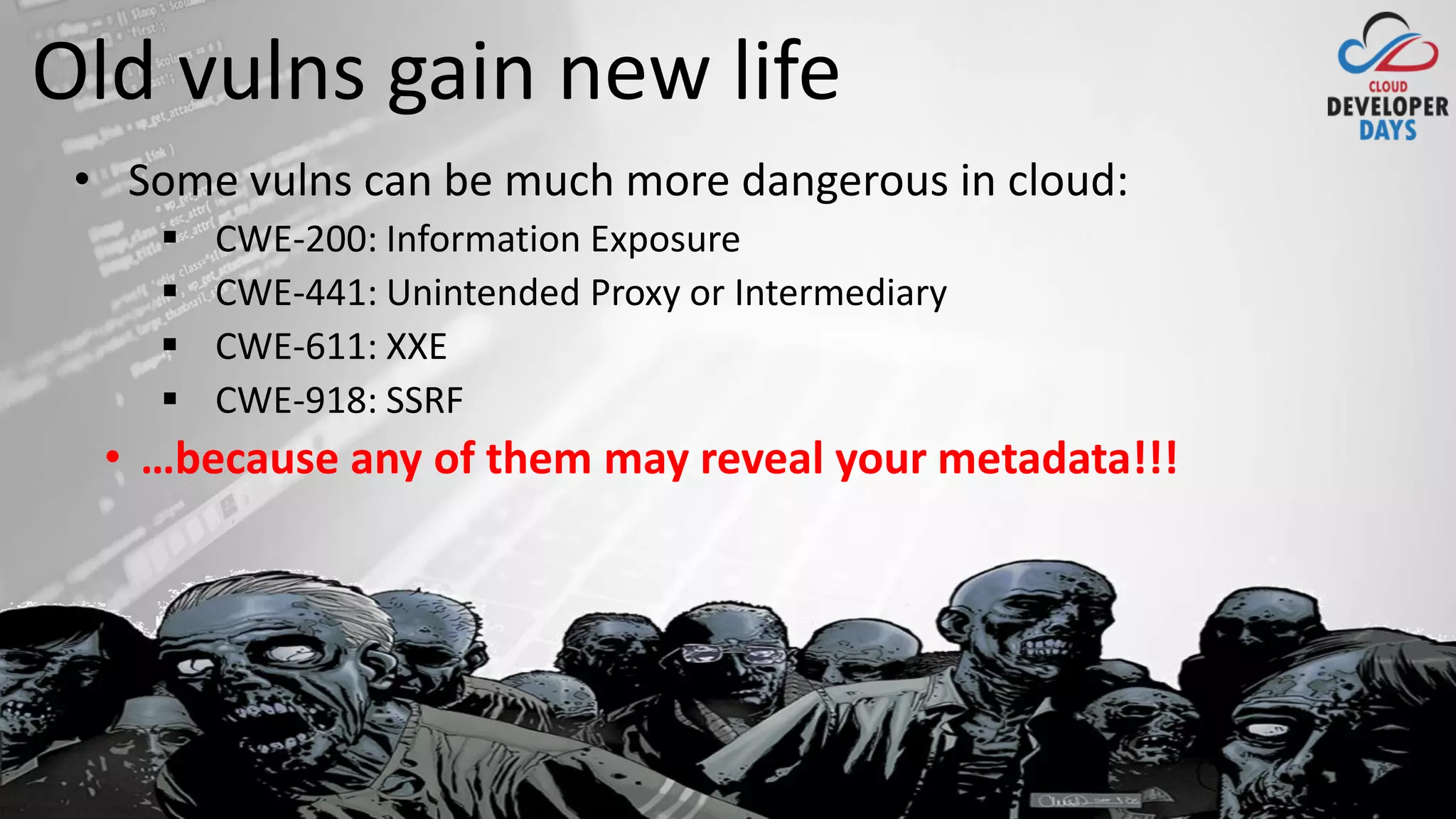
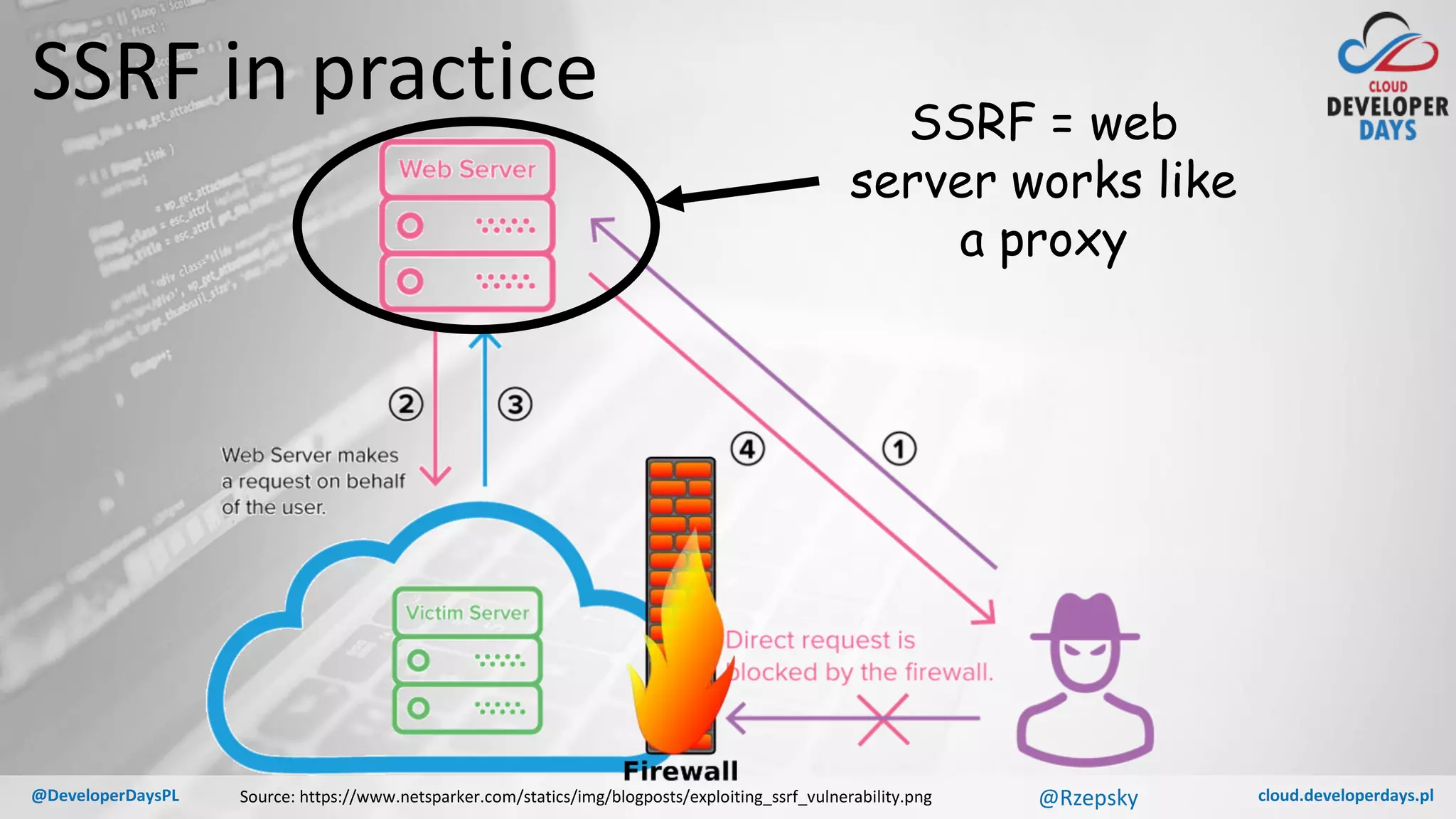
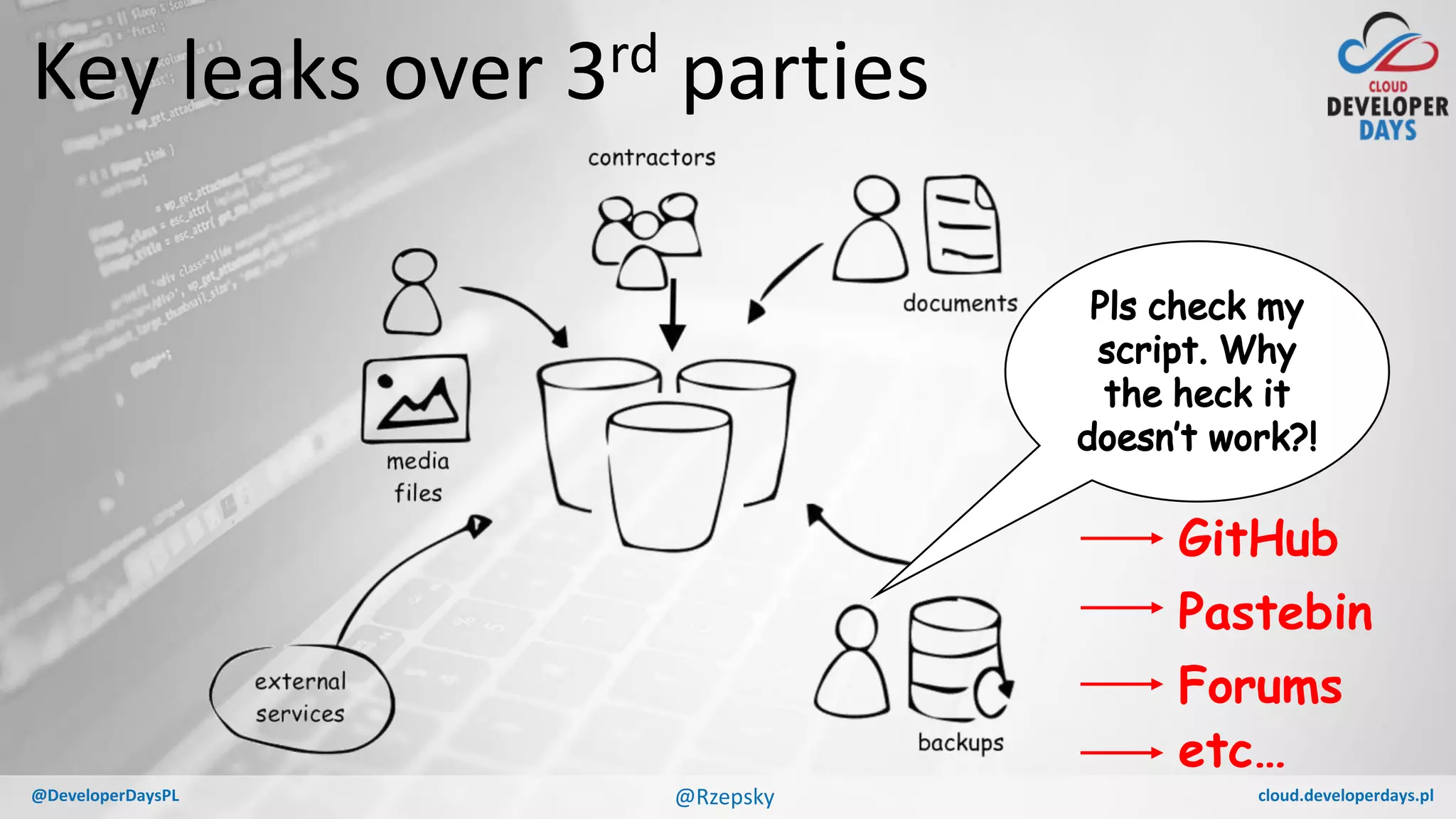
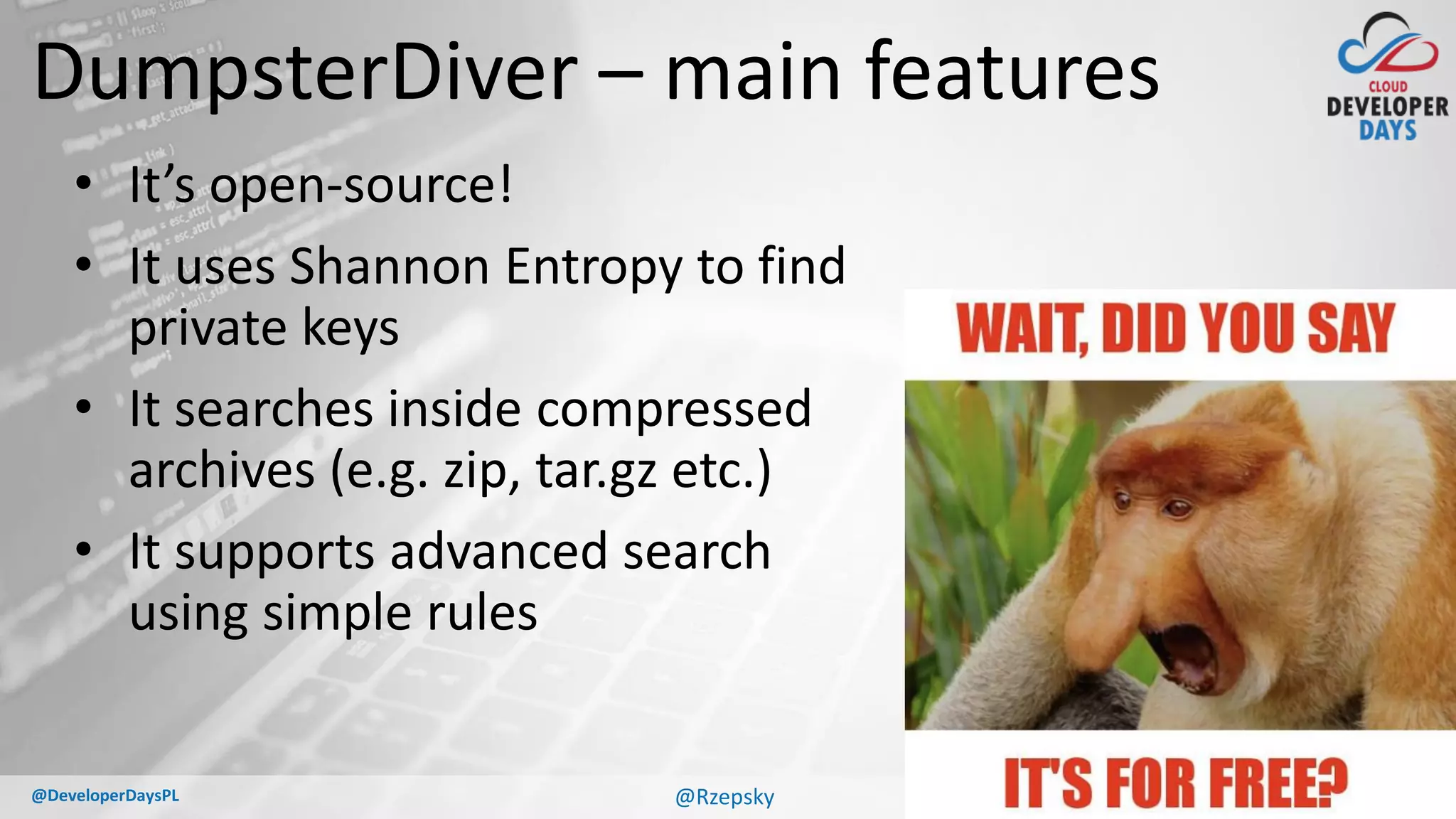
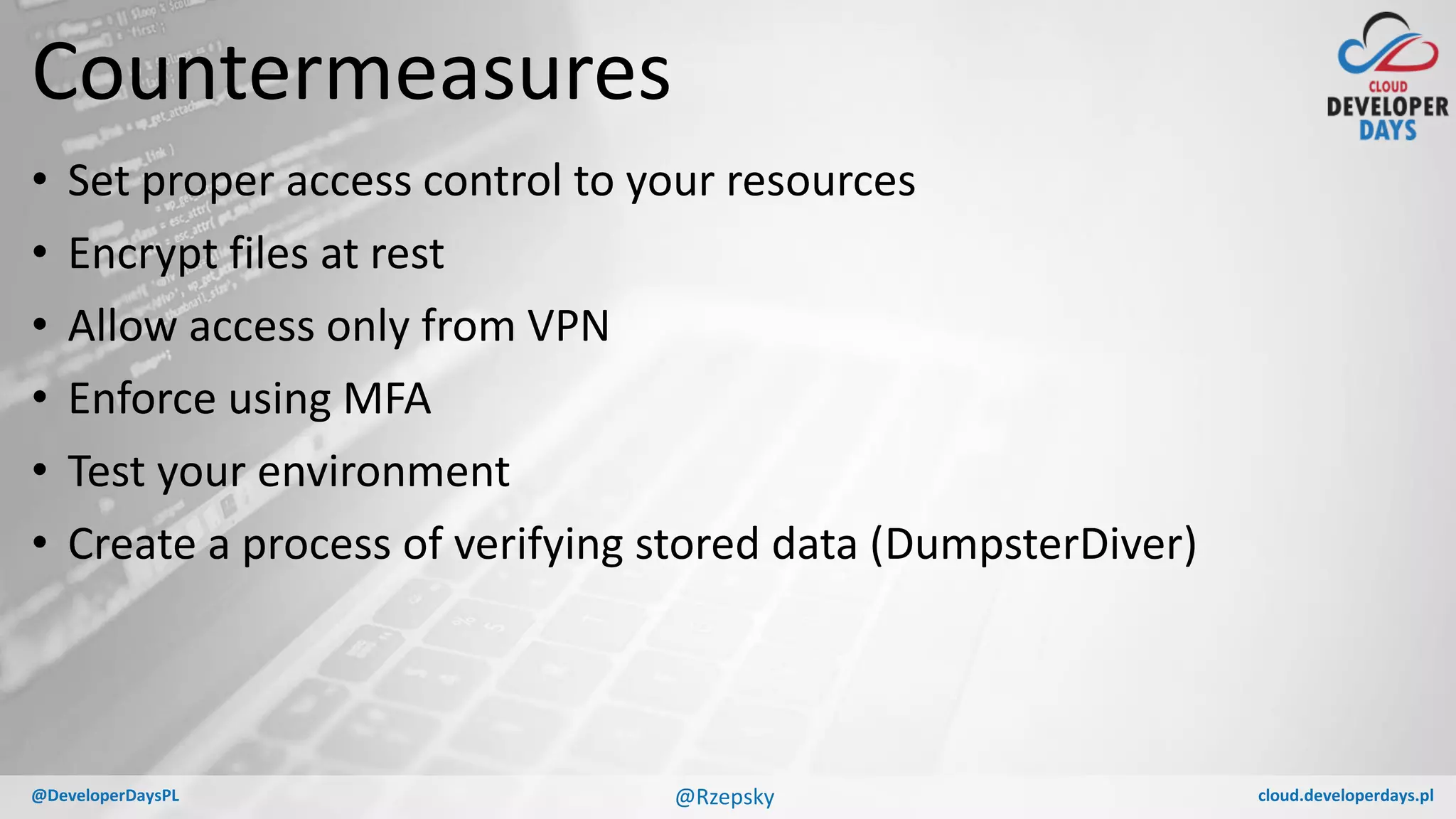
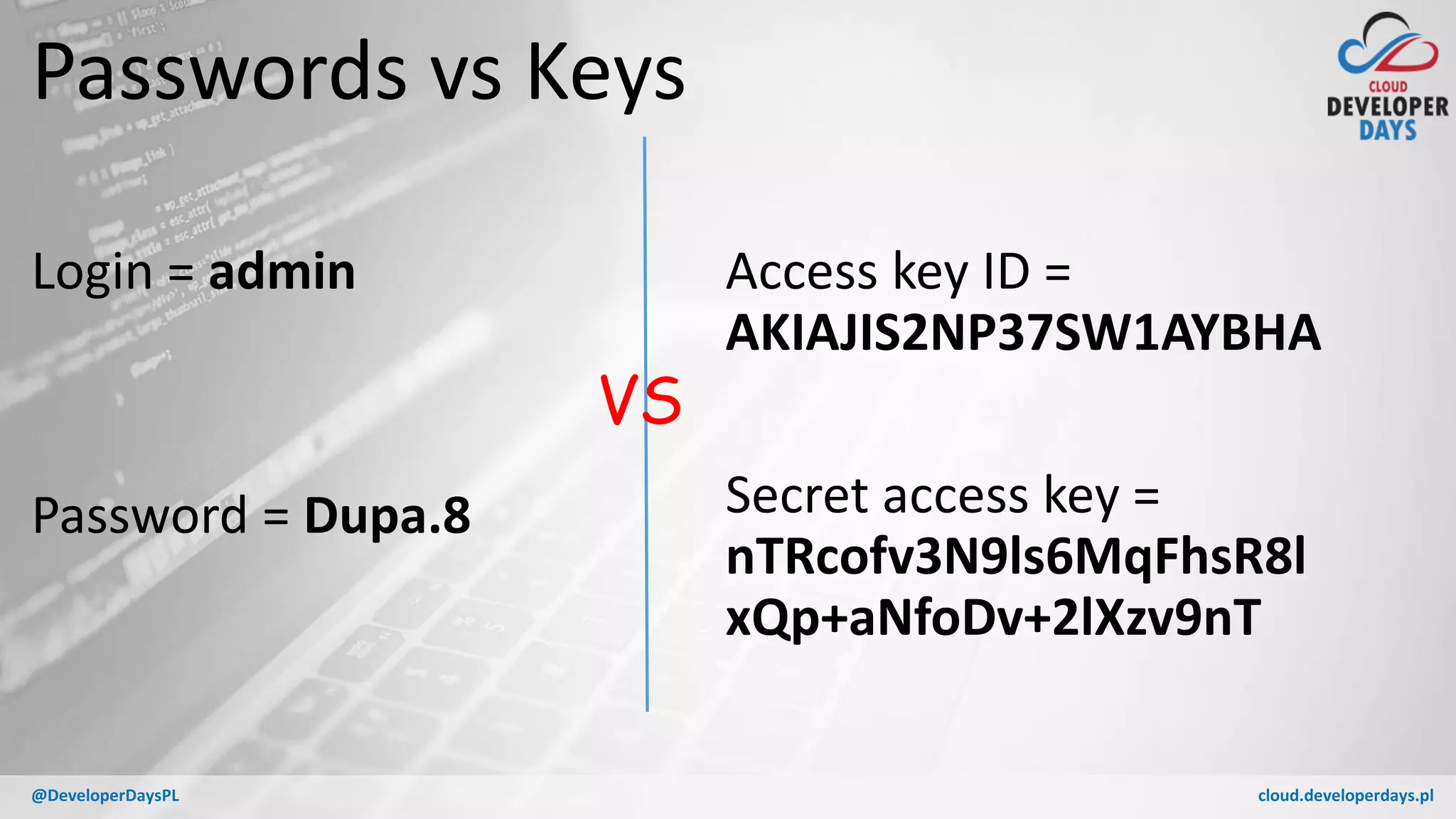
The presentation focuses on the potential leakage of access keys across various cloud service providers (AWS, Azure, GCP) and discusses effective countermeasures to prevent these leaks. It outlines different types of leaks, including those from storage containers, compromised accounts, web apps, and third-party services, while emphasizing the importance of secure coding practices and multi-factor authentication (MFA). Tools like 'dumpsterdiver' are introduced to help identify and audit these vulnerabilities in cloud environments.


![cloud.developerdays.pl@DeveloperDaysPL
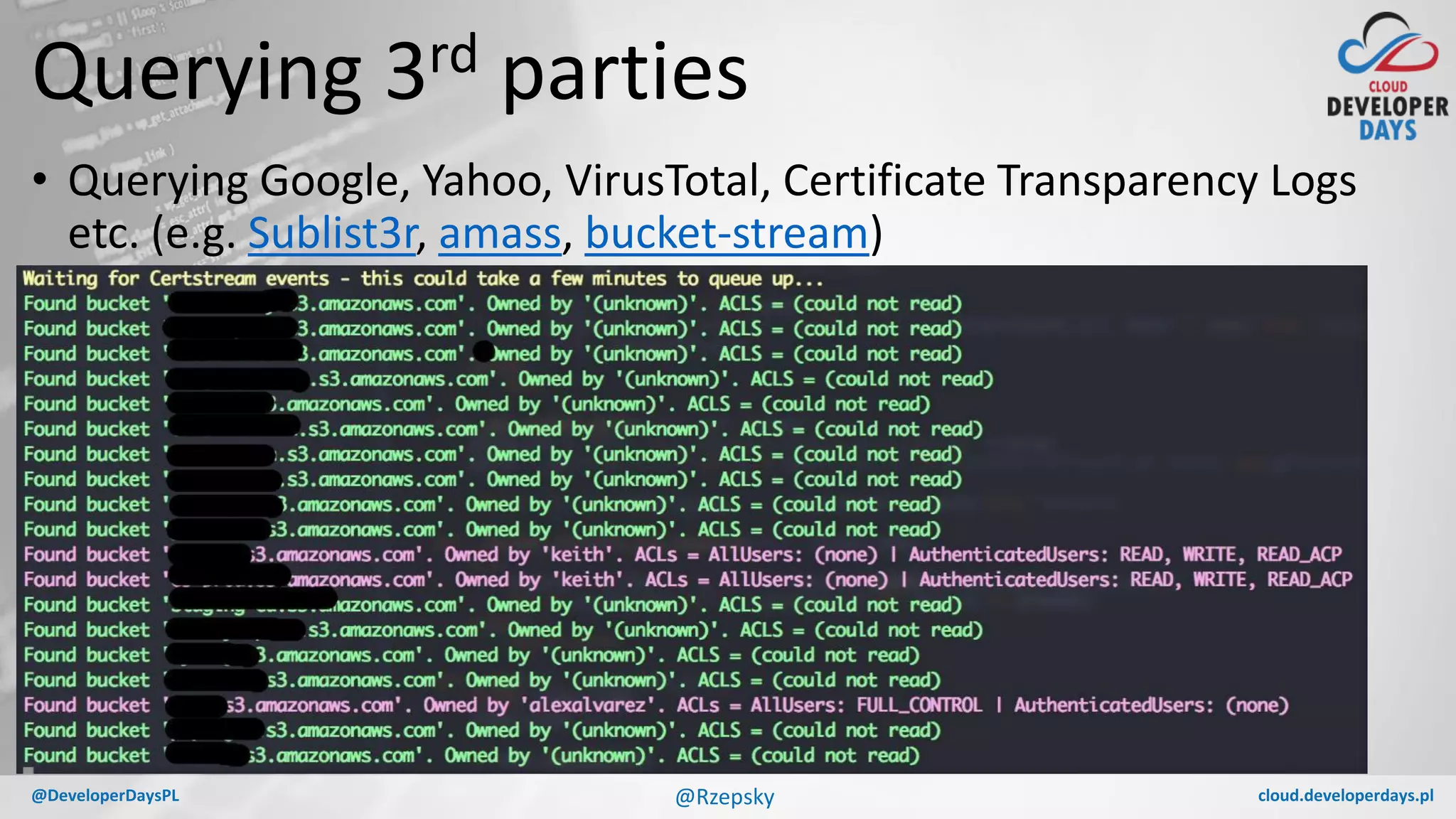
Let’s find open buckets
https://[bucketname].s3.amazonaws.com
https://[aws_endpoint].amazonaws.com/[bucket_name]/
For example: https://chicagodb.s3.amazonaws.com/
Source: https://www.upguard.com/breaches/cloud-leak-chicago-voters
@Rzepsky](https://image.slidesharecdn.com/huntingforthesecretsinacloudforest-180529140243/75/Hunting-for-the-secrets-in-a-cloud-forest-11-2048.jpg)
![cloud.developerdays.pl@DeveloperDaysPL
What about Azure?
• There is no groups like “Any authenticated Azure user” (thanks
Microsoft!)
• You have to discover 2 variables instead of 1 (consider only Full
public read access):
http://[storage account name].blob.core.windows.net/[container
name]?restype=container&comp=list](https://image.slidesharecdn.com/huntingforthesecretsinacloudforest-180529140243/75/Hunting-for-the-secrets-in-a-cloud-forest-18-2048.jpg)