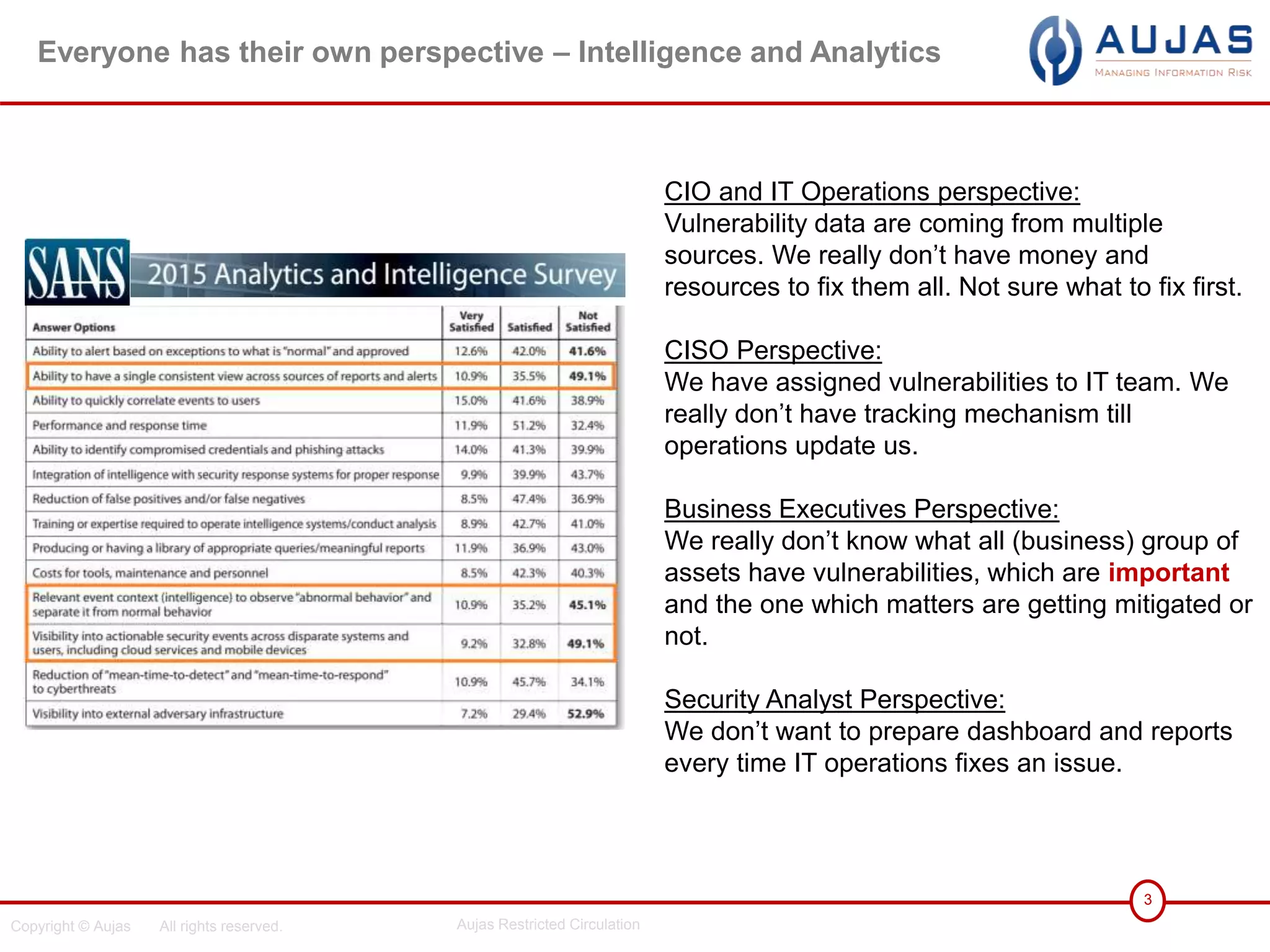
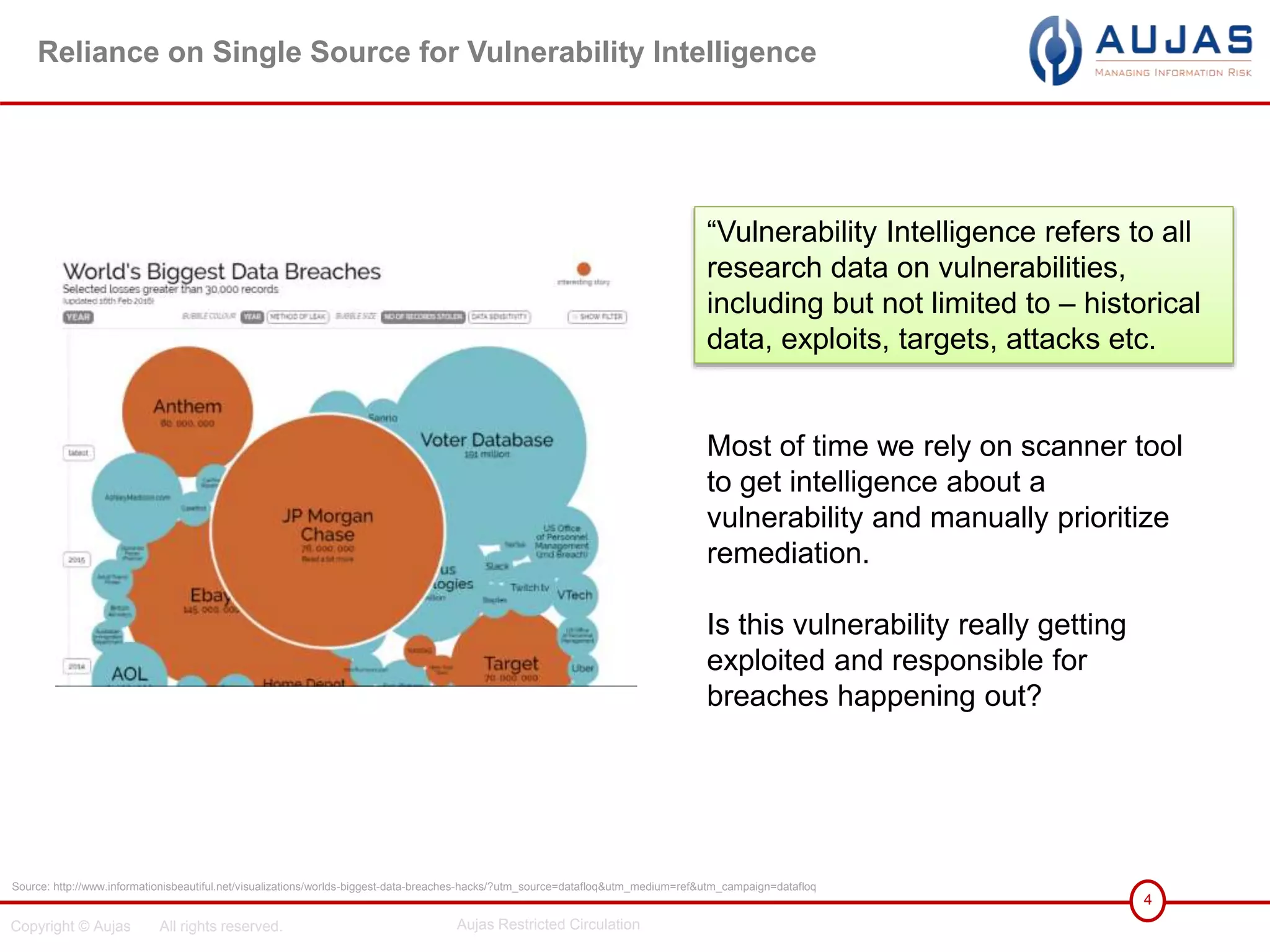
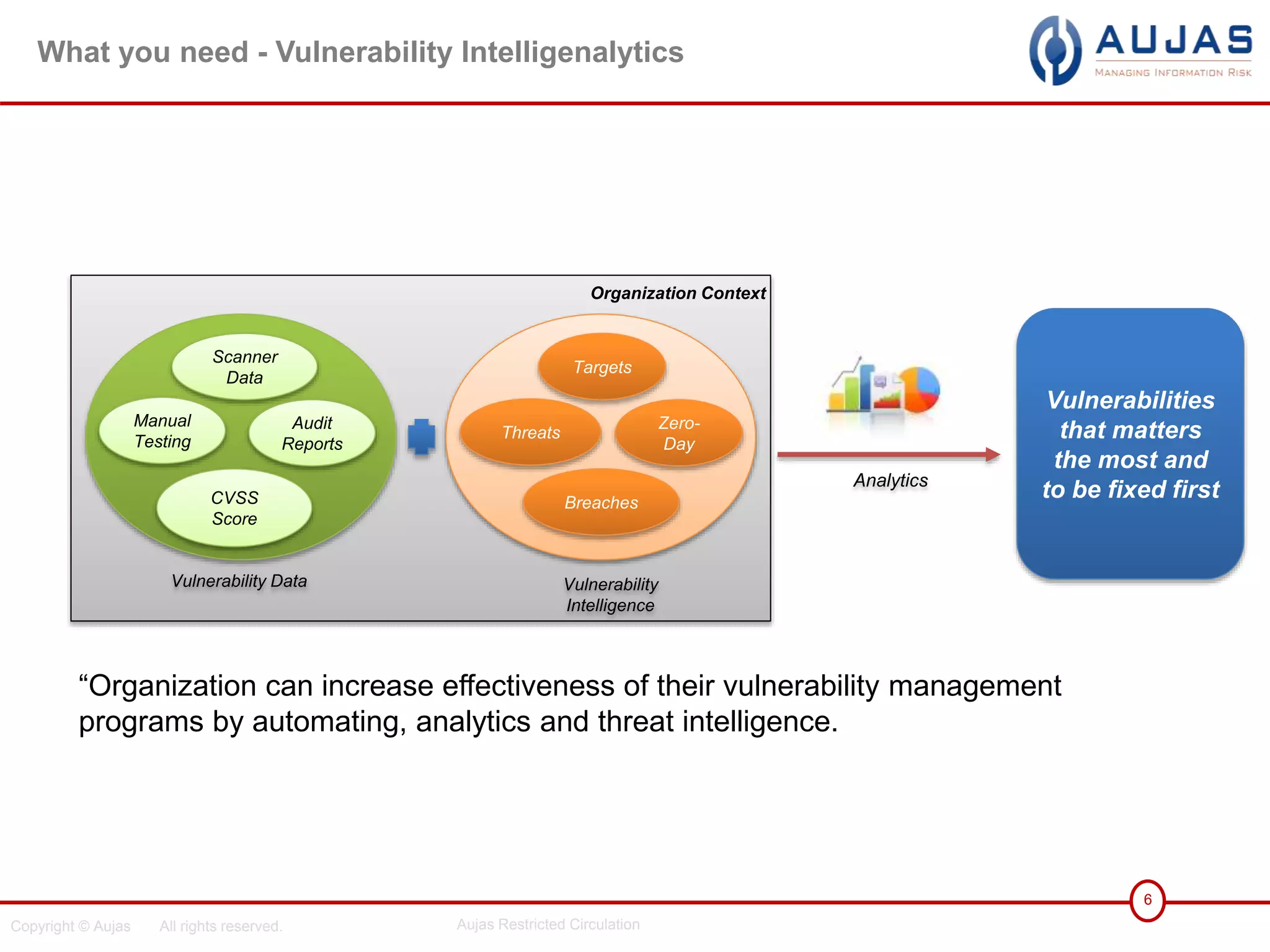
The document discusses the need for organizations to contextualize vulnerability data and prioritize remediation based on risk rather than relying solely on vulnerability scanner data. It advocates using vulnerability intelligence feeds incorporating threat data, breaches, exploits and targets to understand external attacks and their relevance to the organization. The document recommends automating these processes to effectively track the vulnerabilities that matter most and need to be fixed first given organizational context and asset criticality.