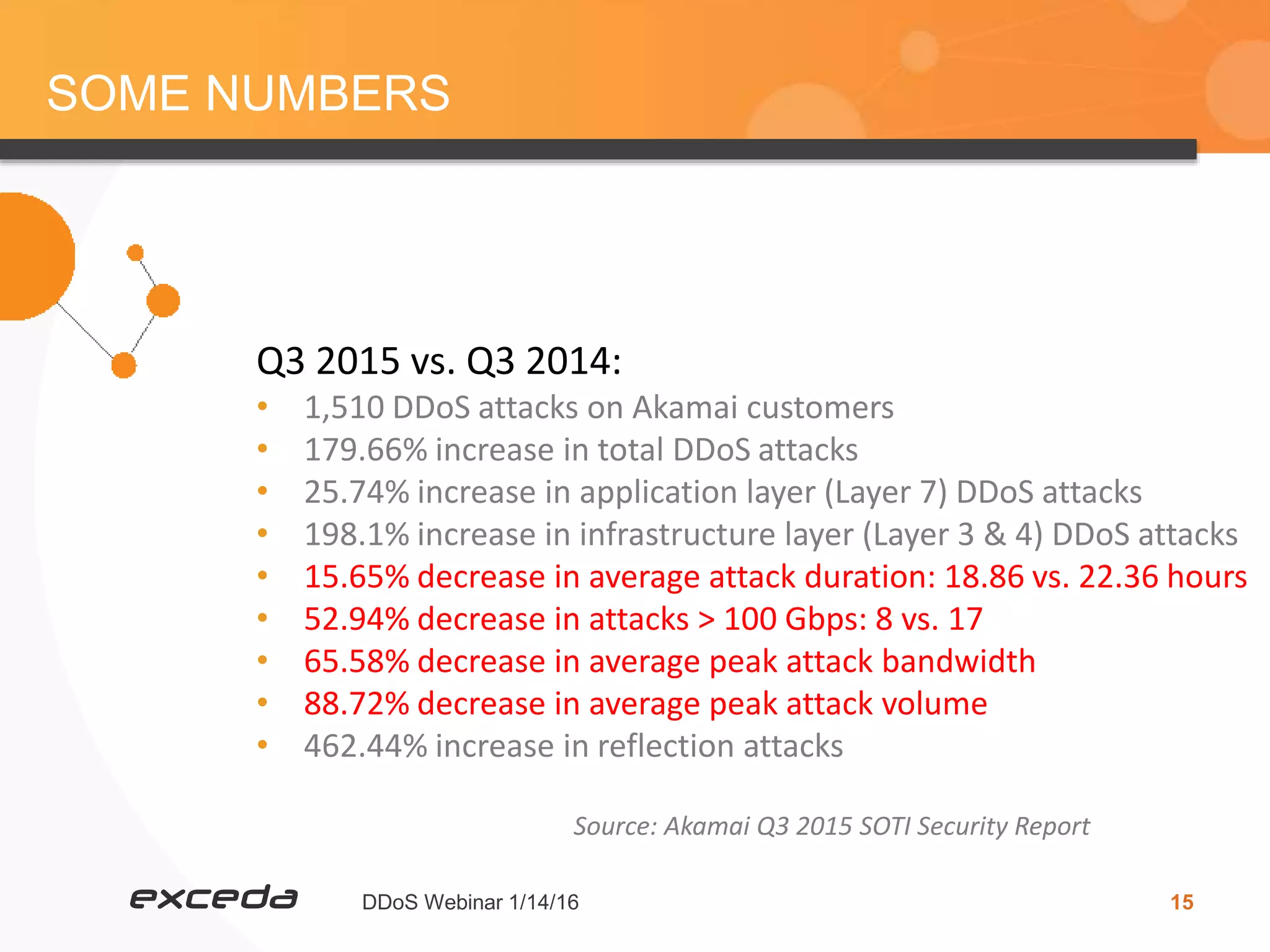
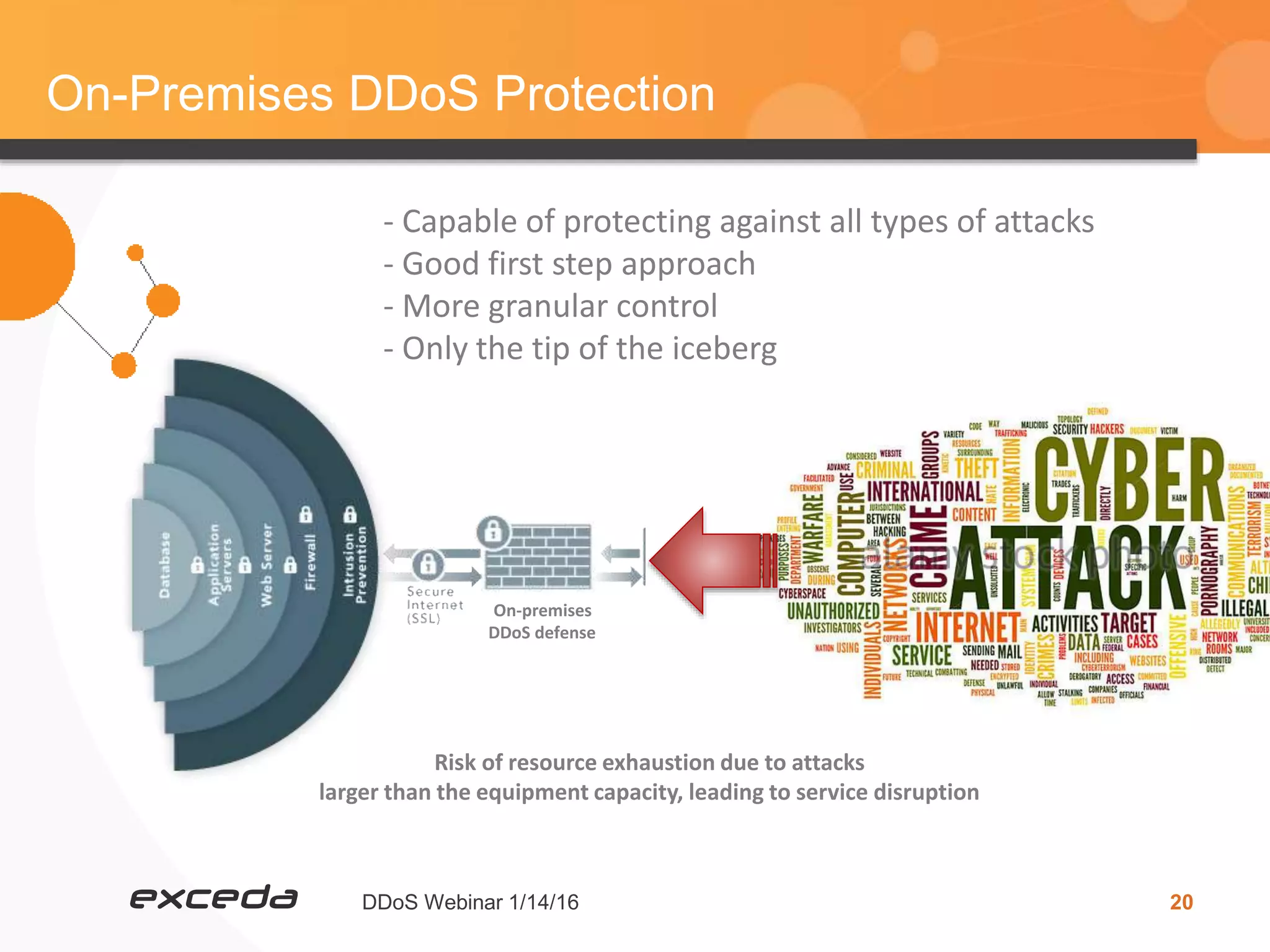
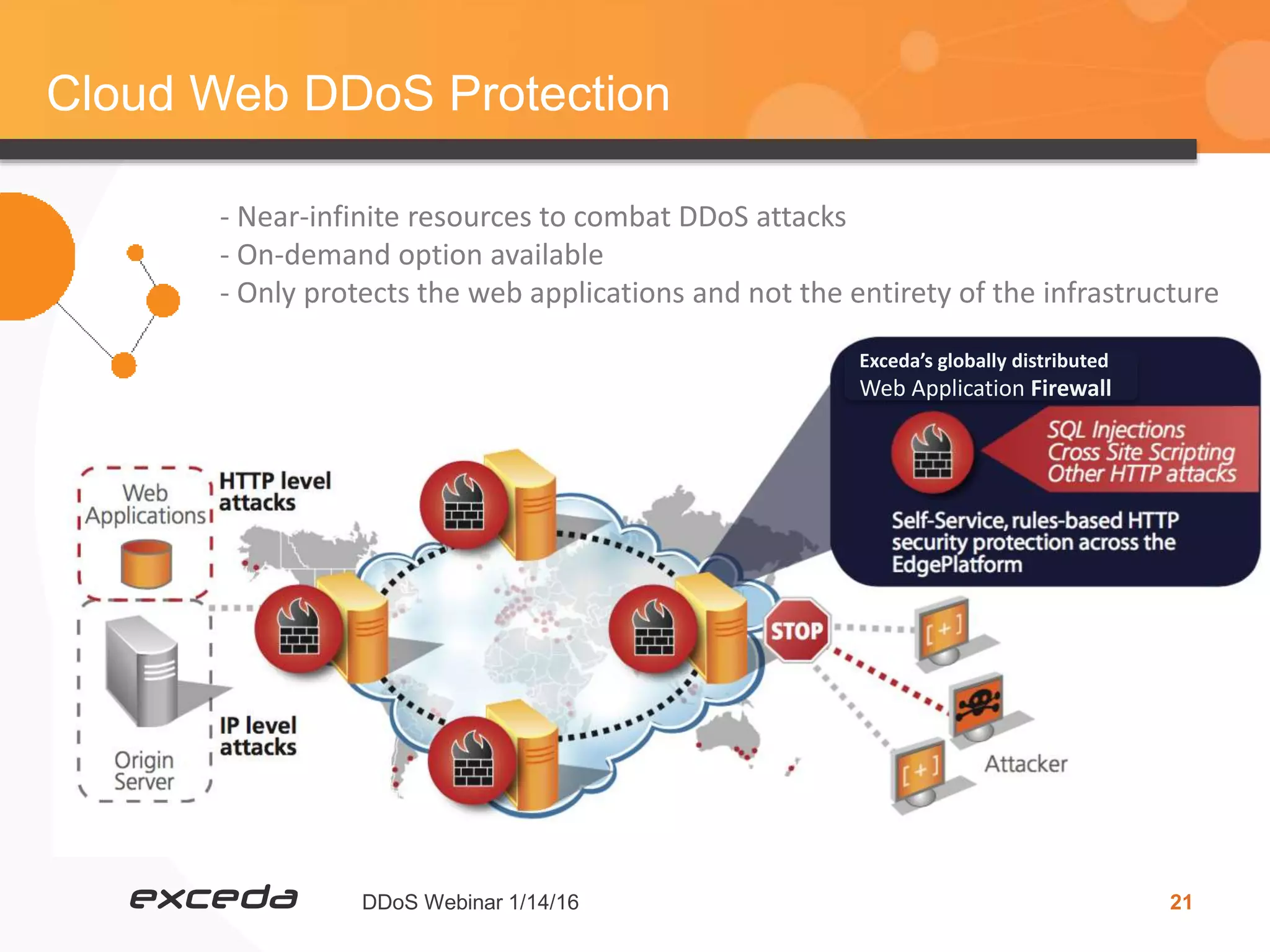
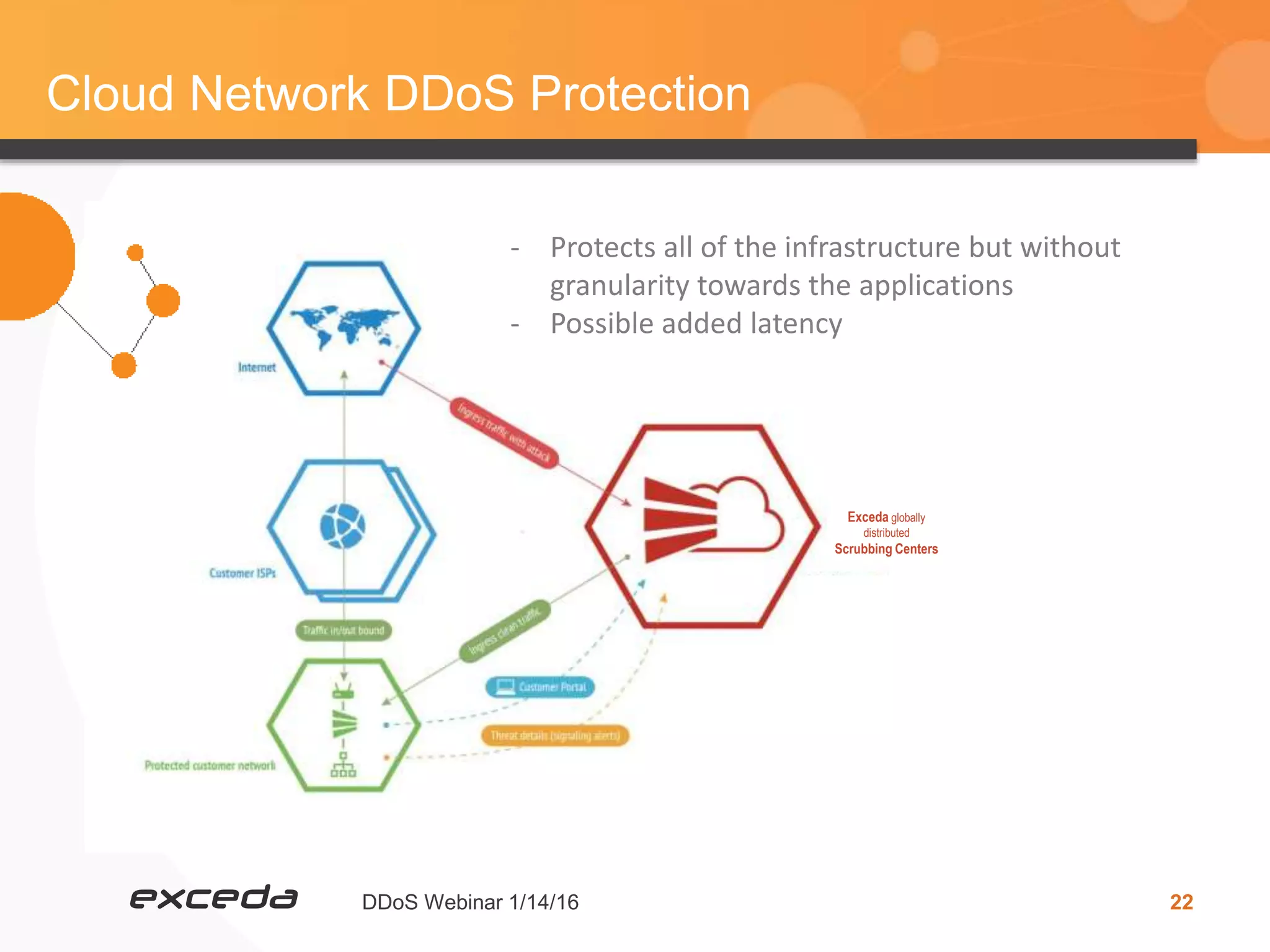
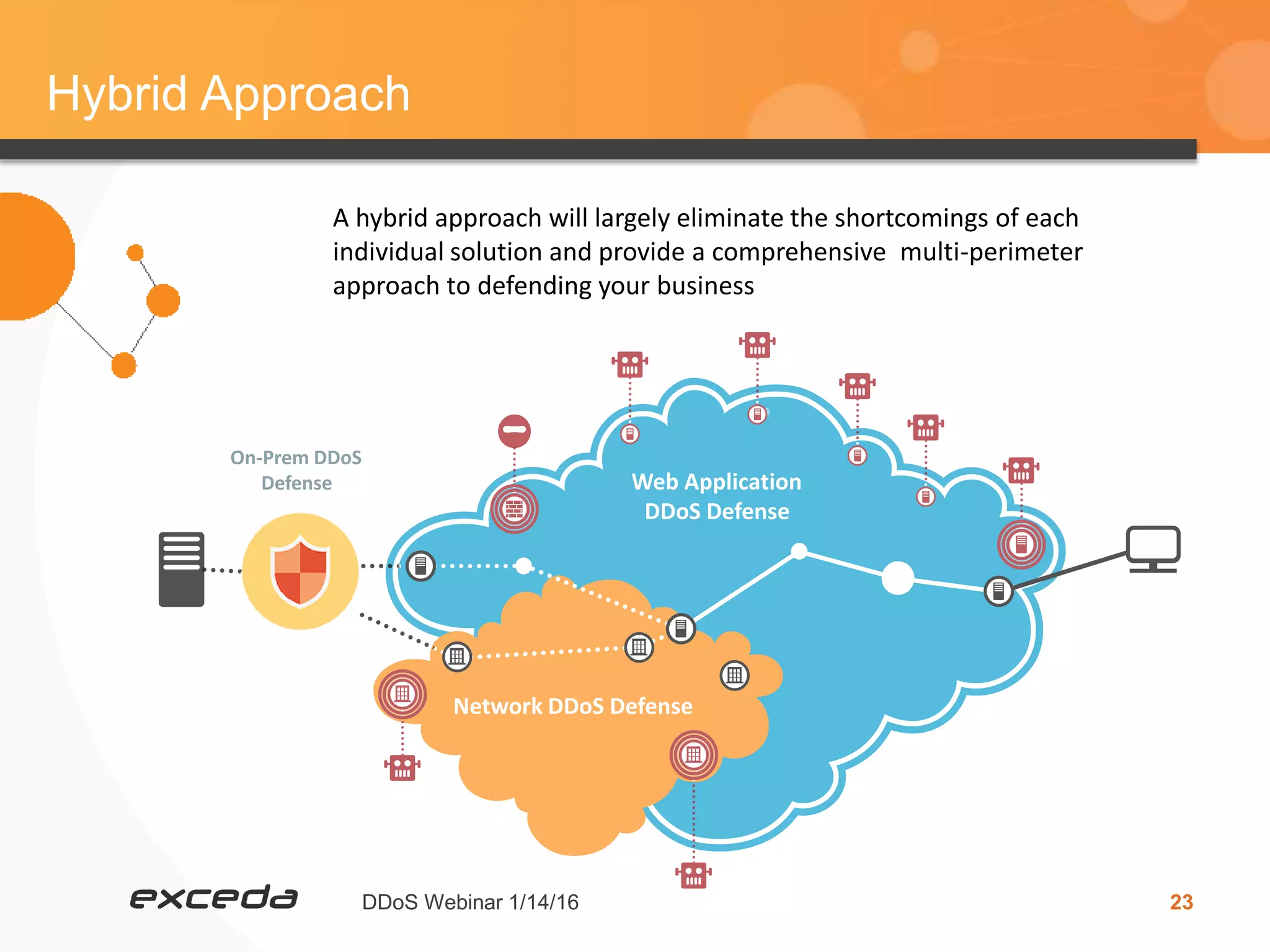
The document discusses mitigating DDoS attacks. It provides an overview of DDoS attacks including some history and context, current observations and statistics showing a large increase in attacks, the visible and invisible costs of attacks, and strategies for protection including using on-premises appliances, cloud-based solutions, or a hybrid approach. It also covers some challenges in protecting applications and infrastructure layers and looks ahead to threats in 2016 as barriers to DDoS attacks are lowered. The presentation aims to help organizations understand the risks and have the right tools and configurations to defend against attacks.