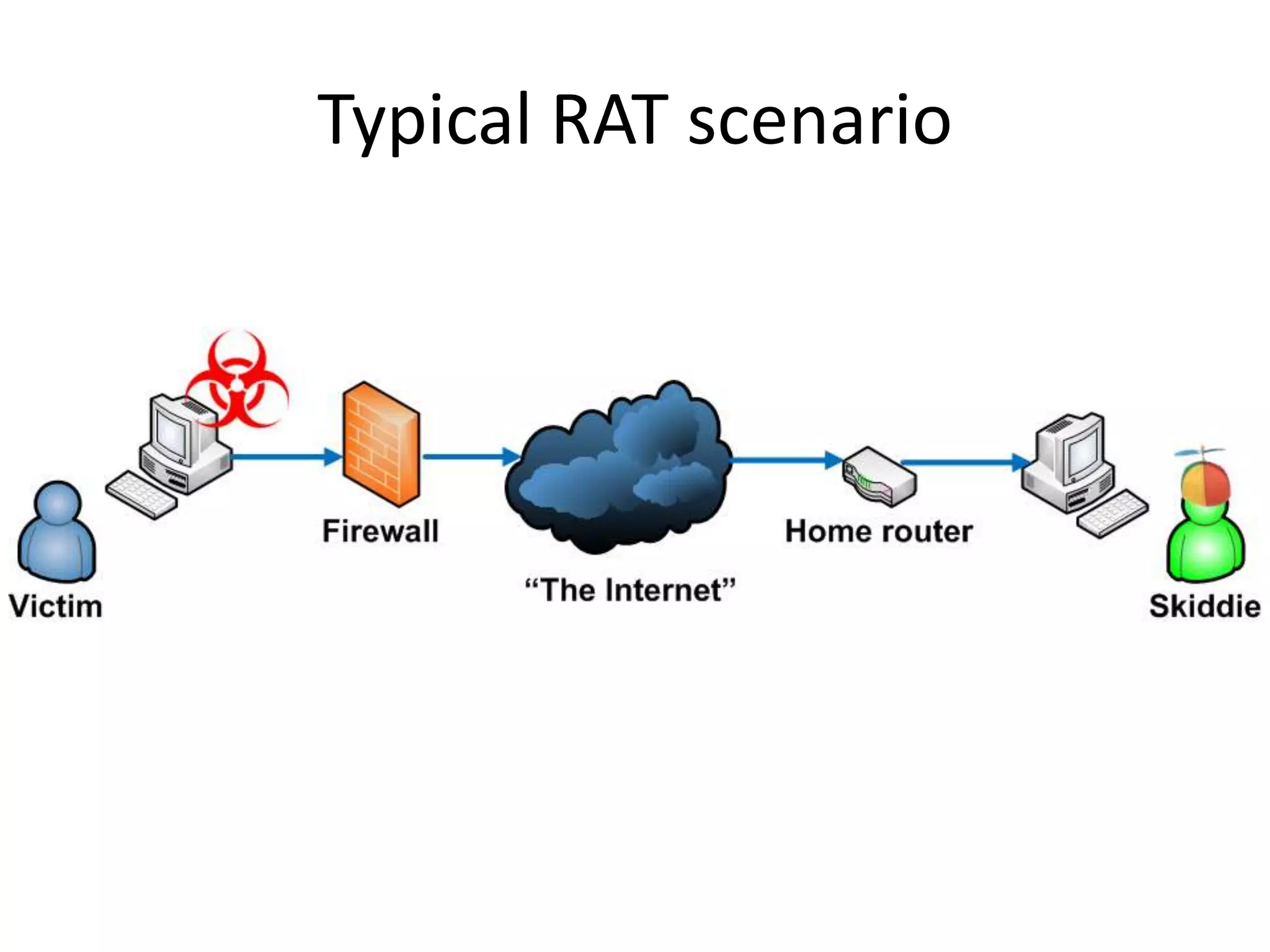
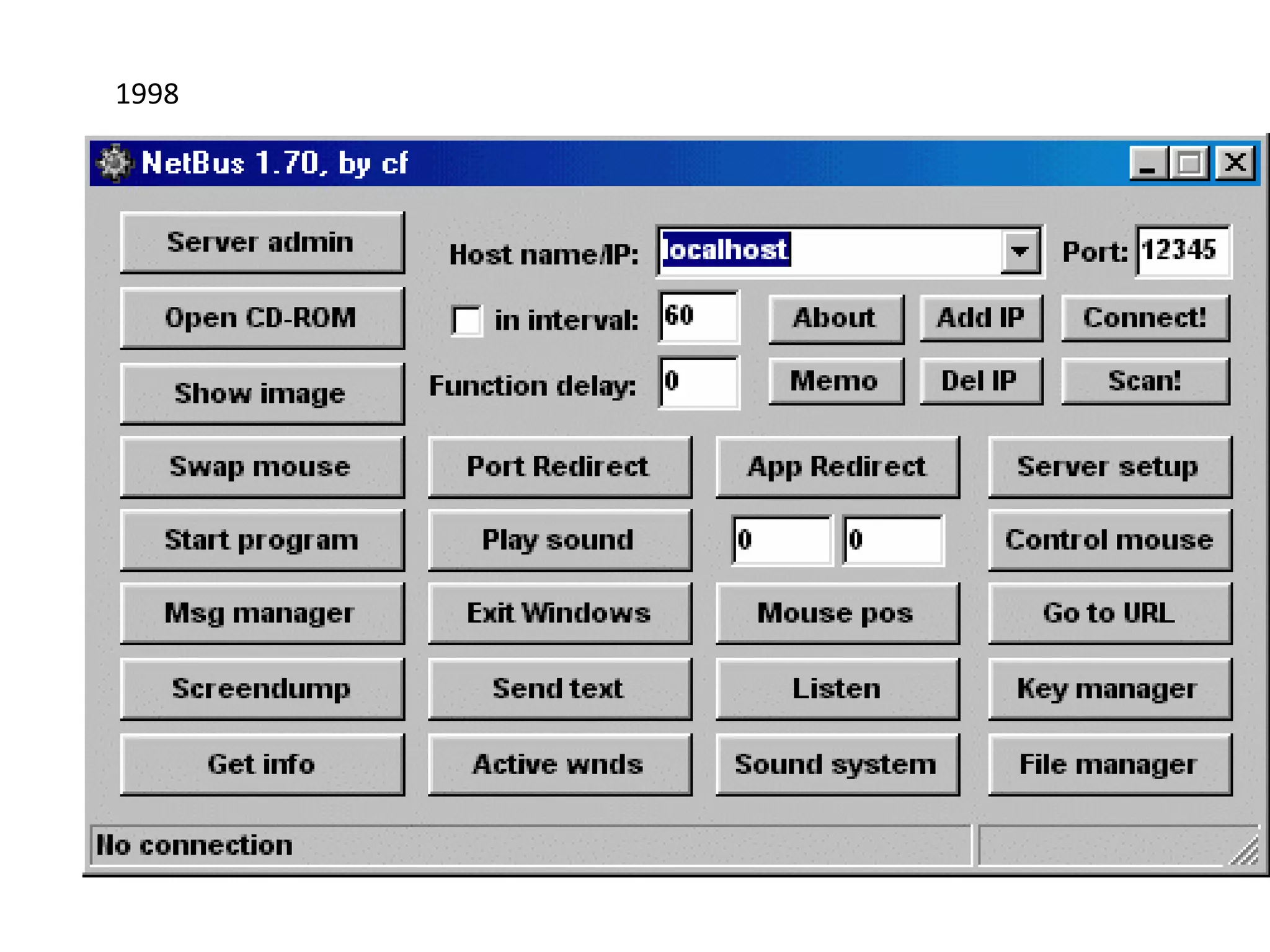
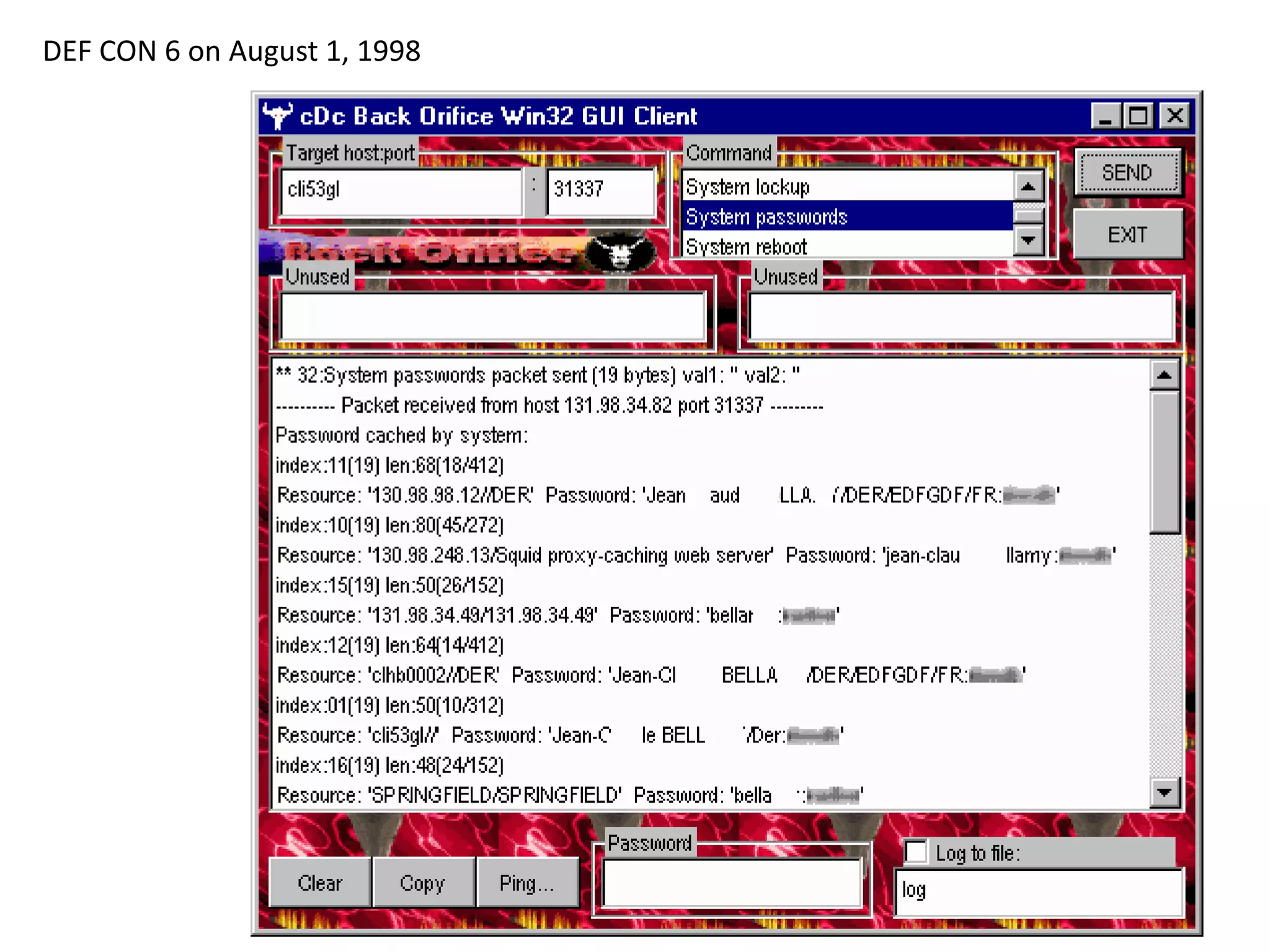
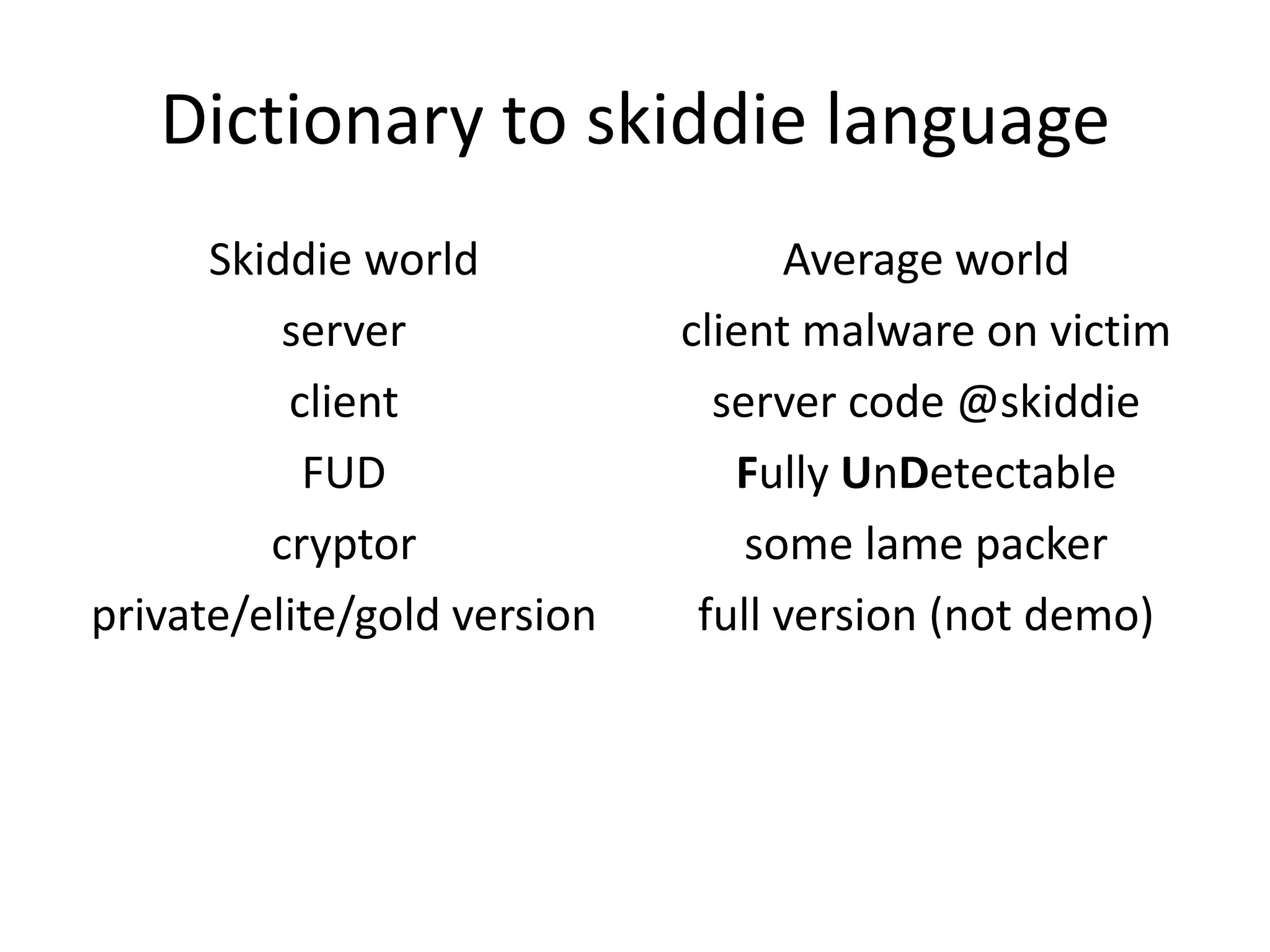
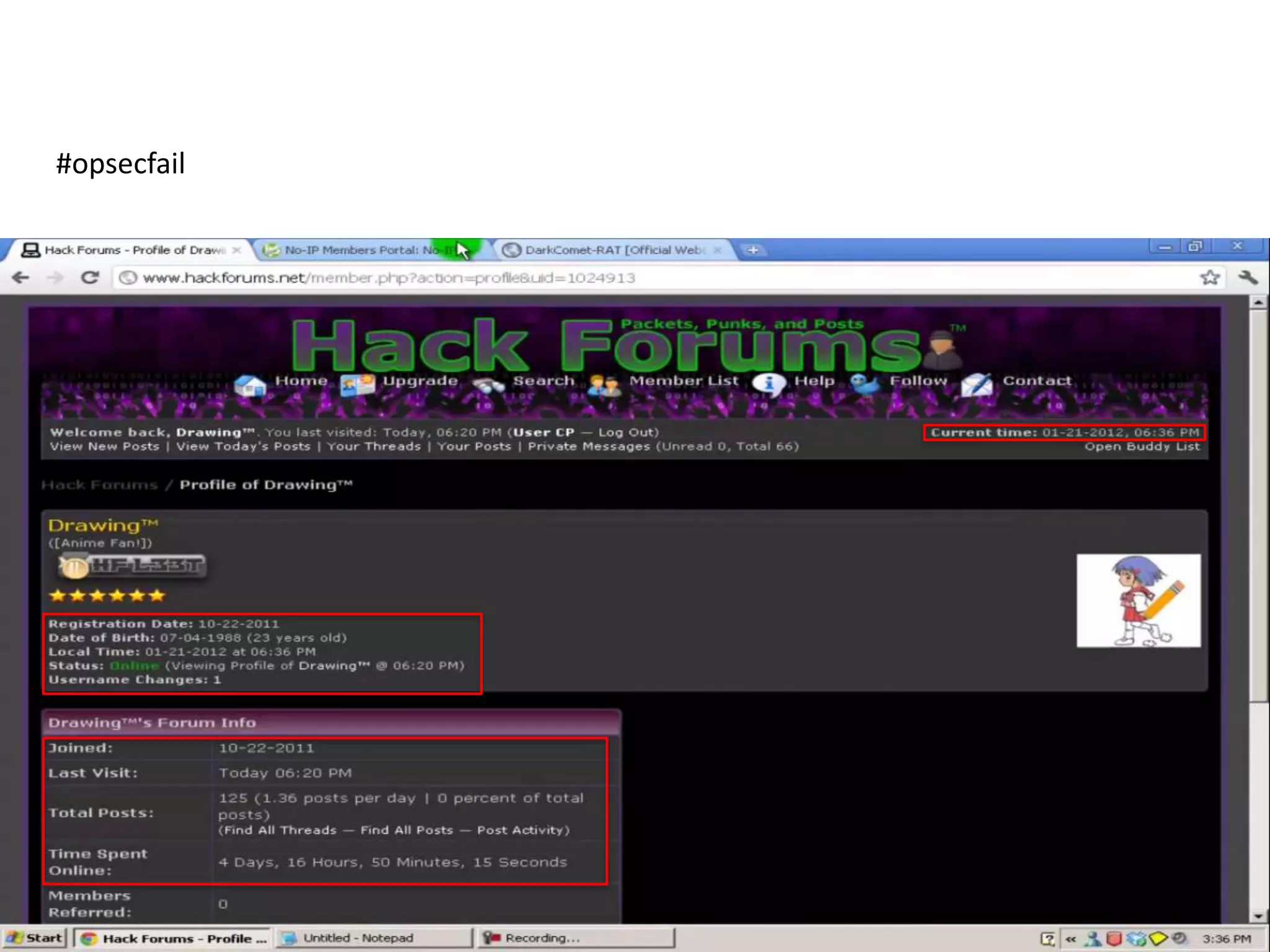
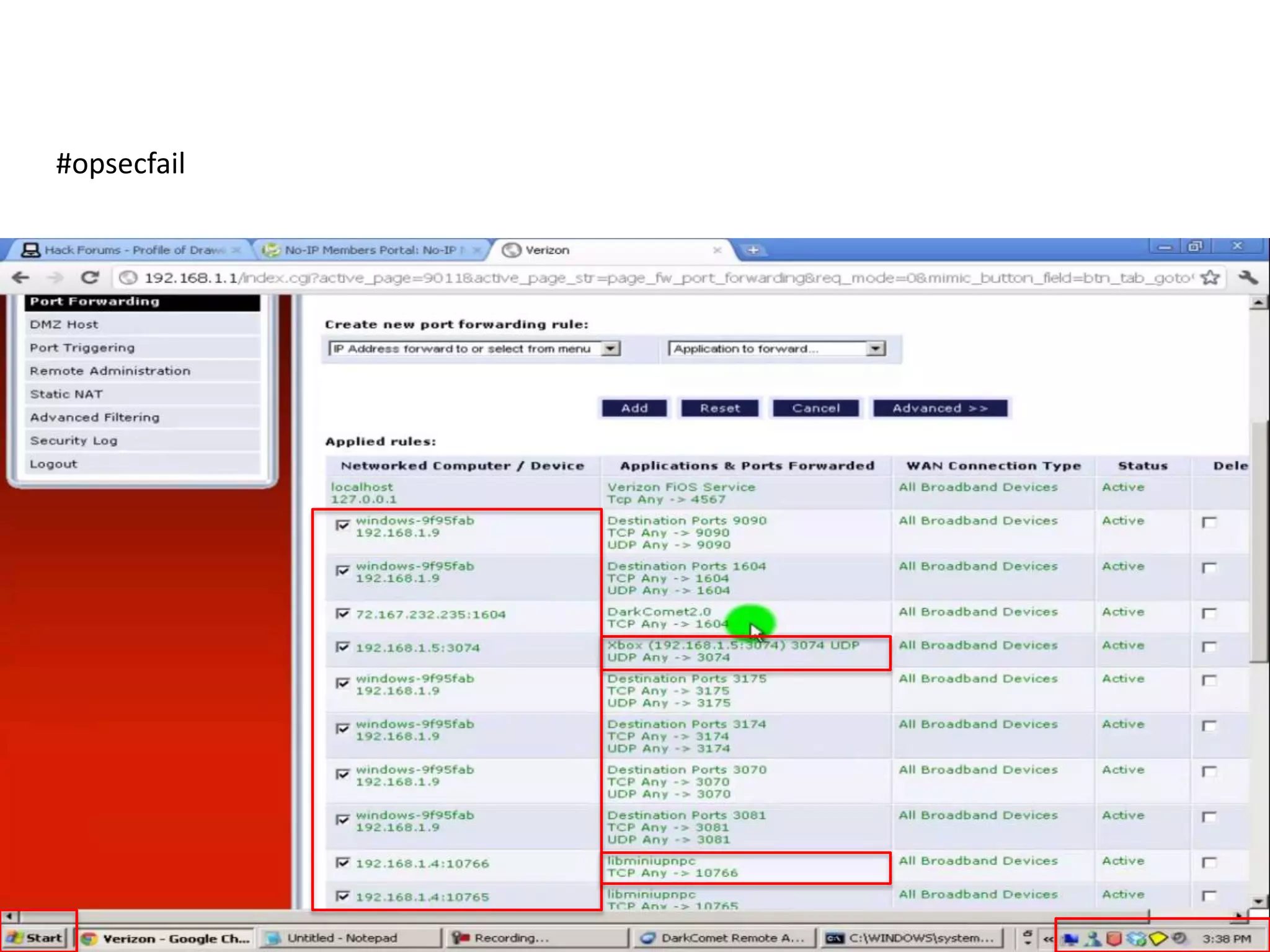
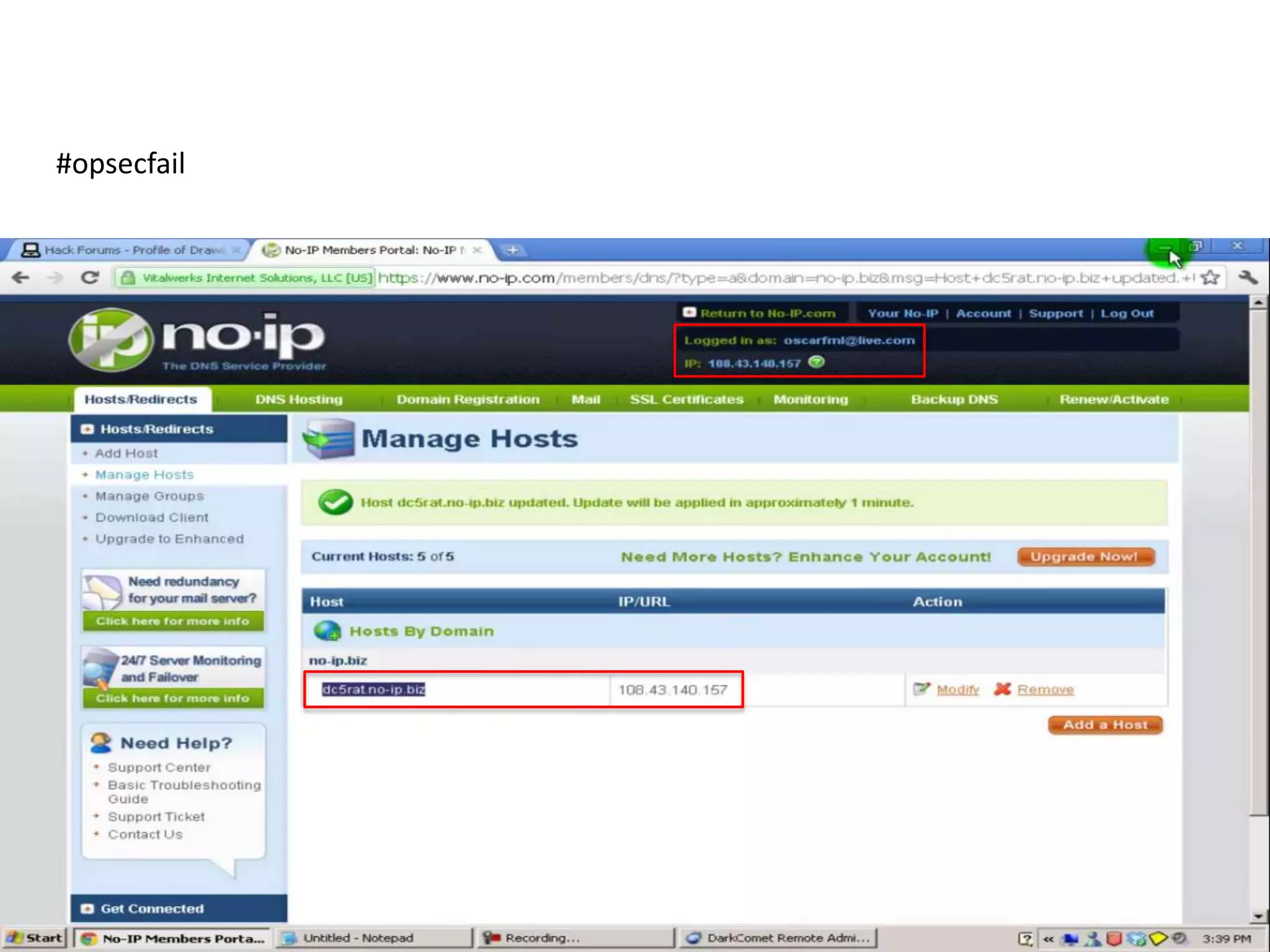
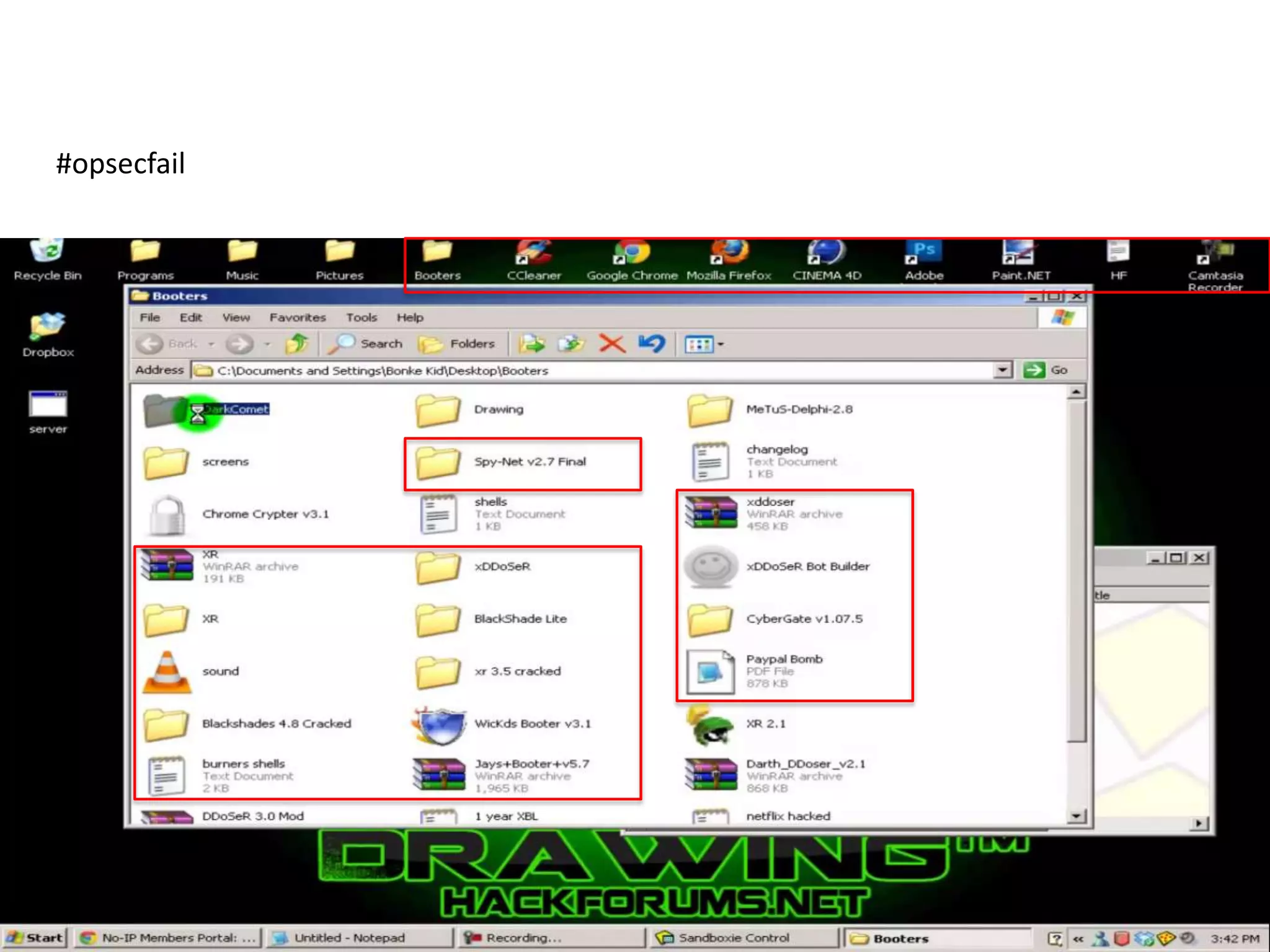
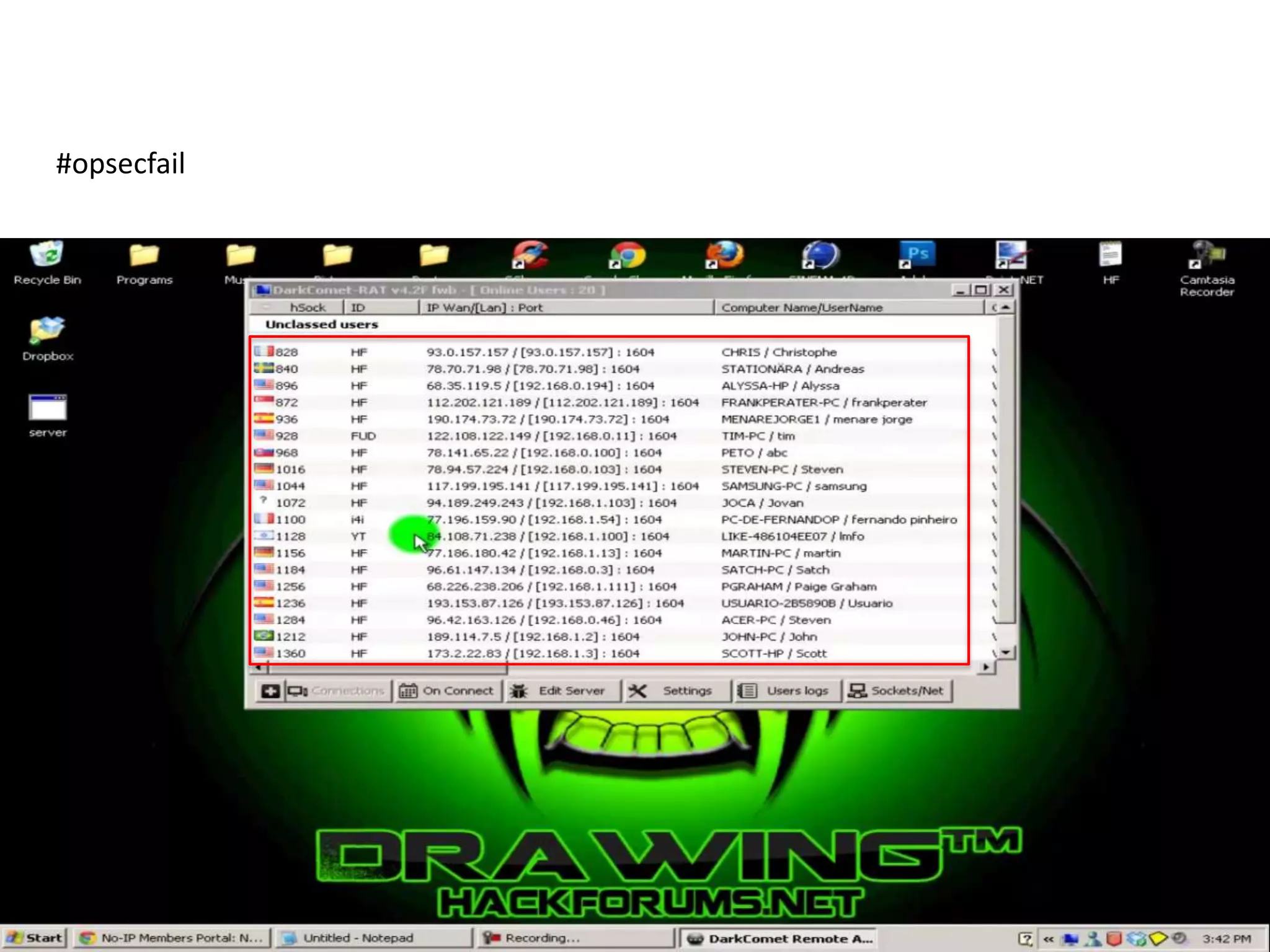
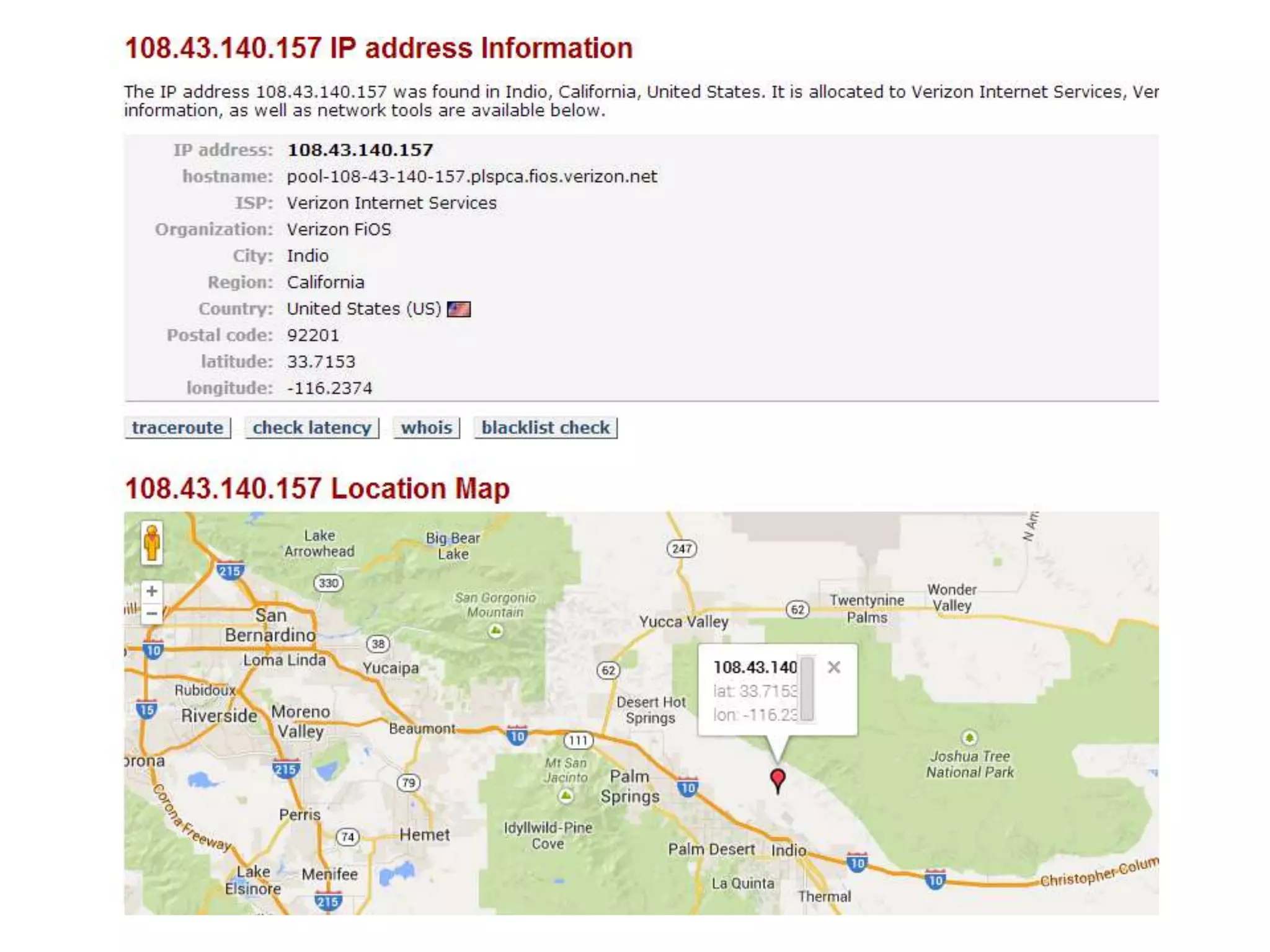
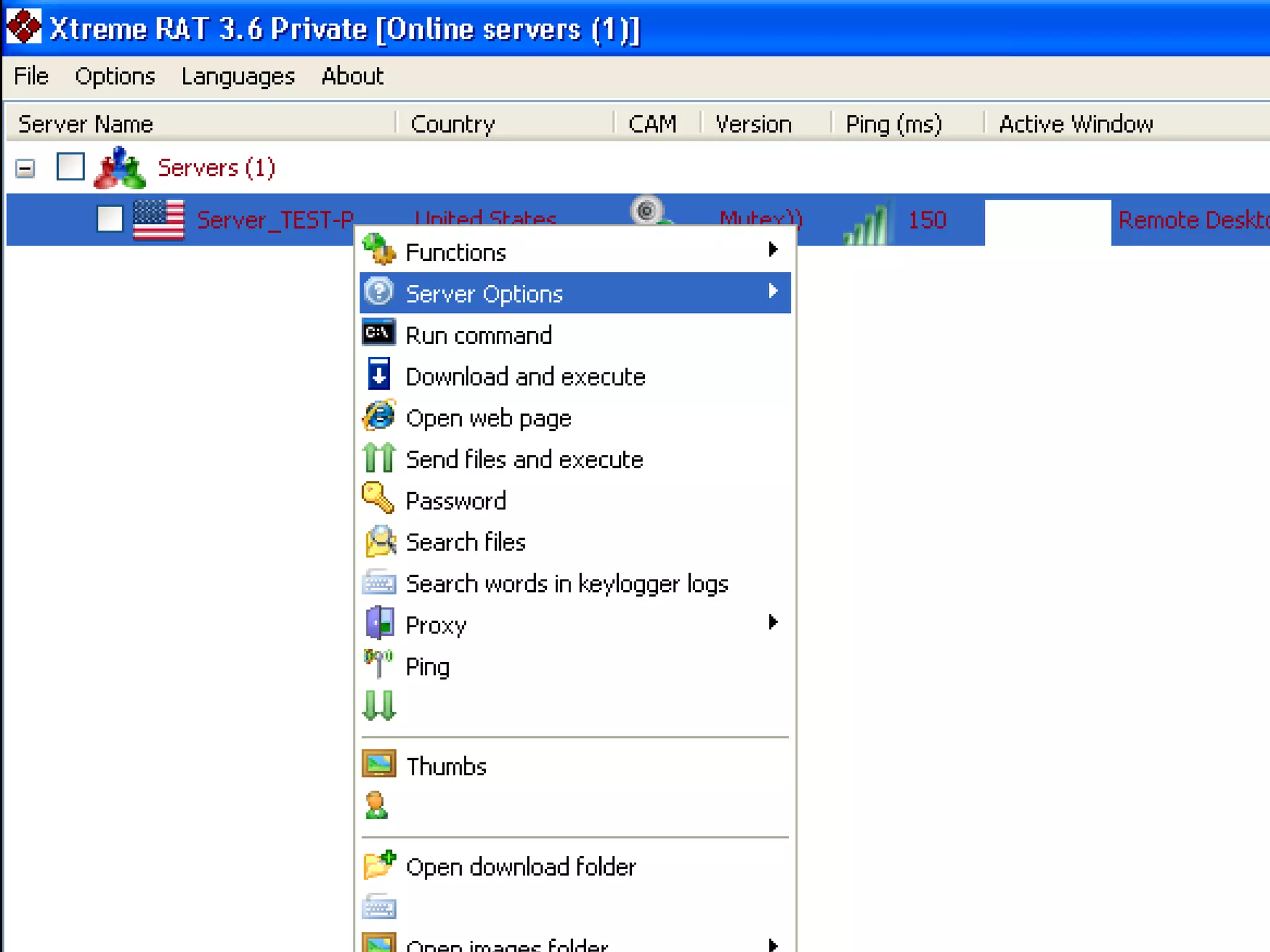
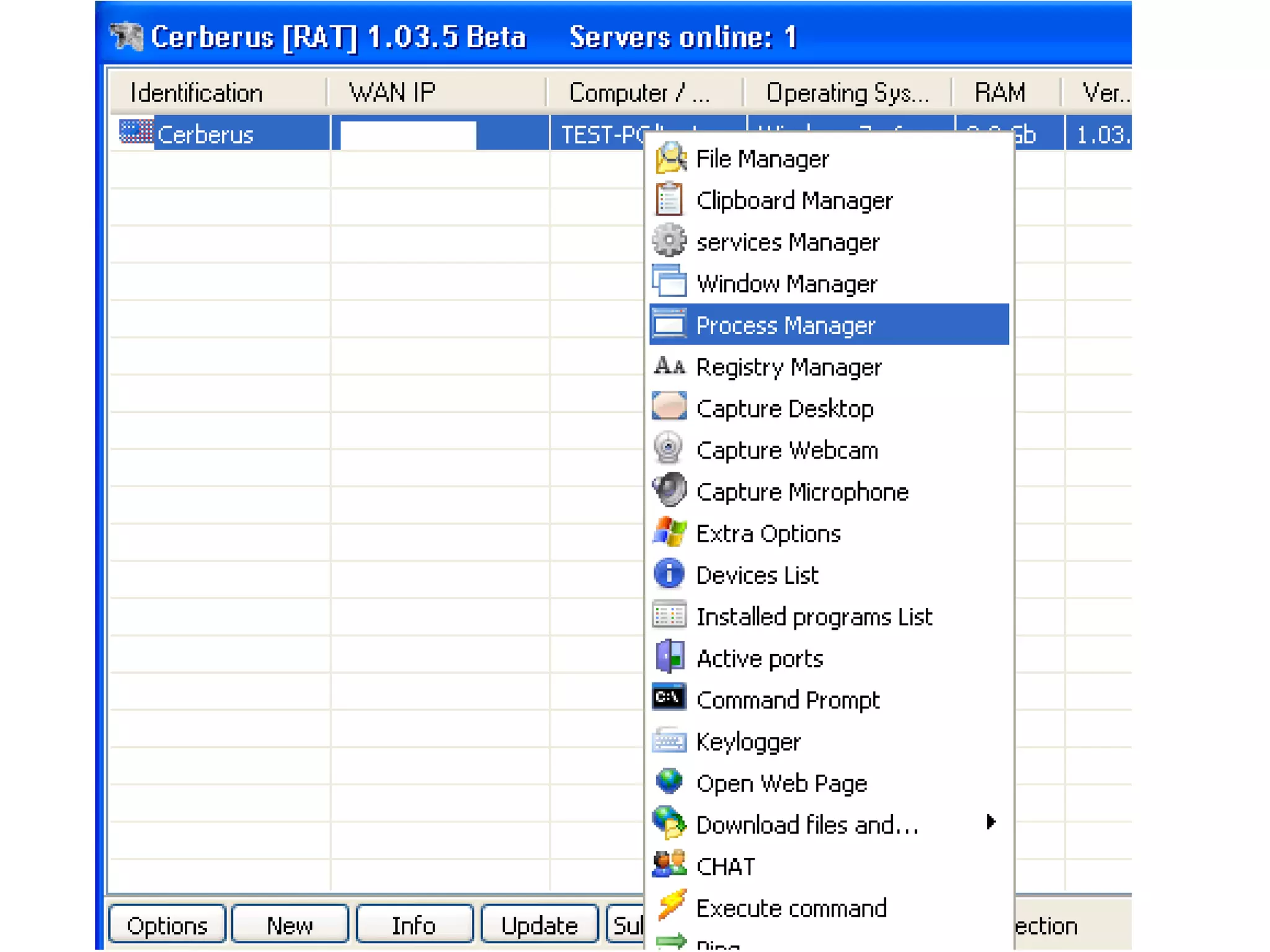
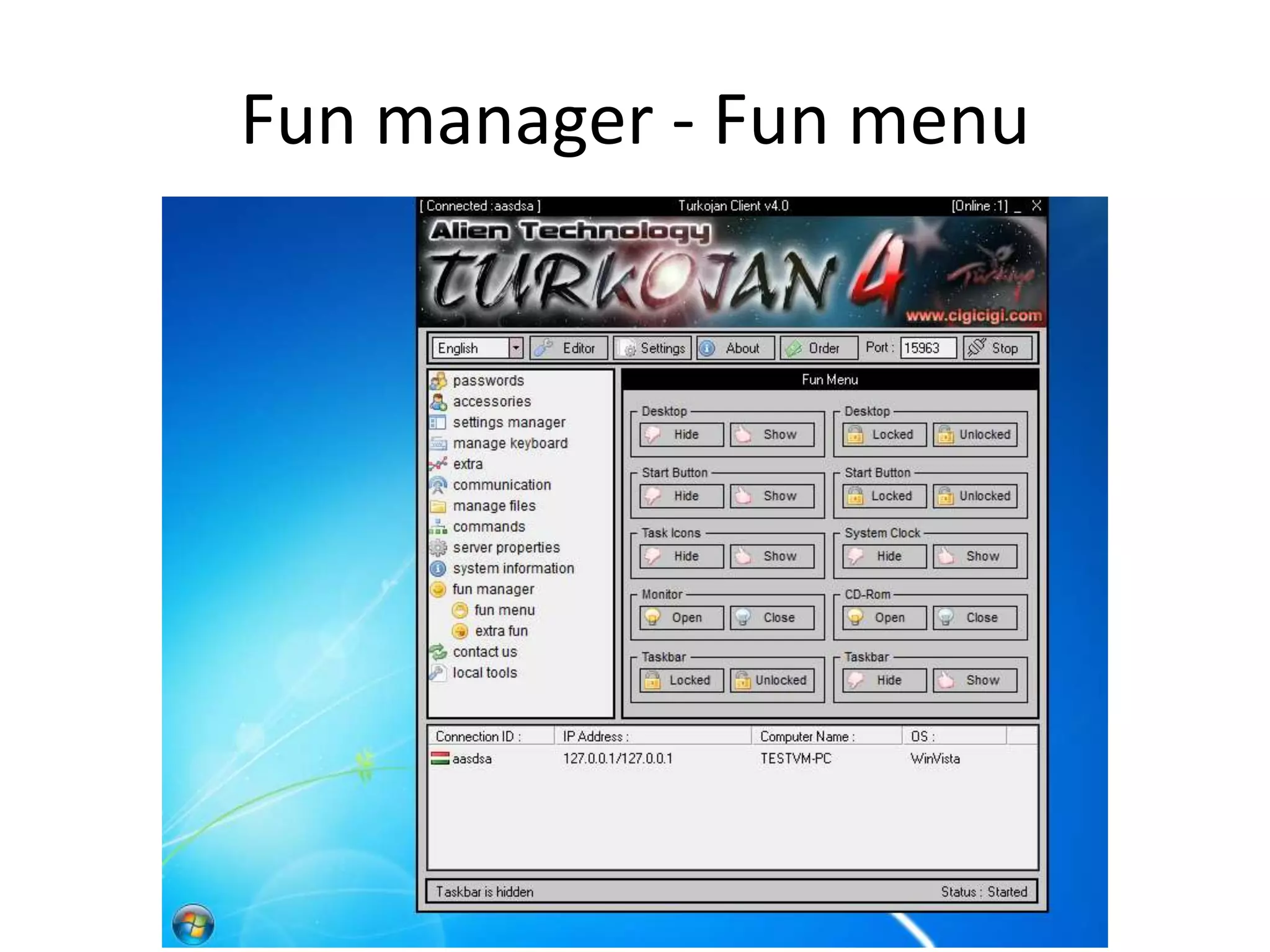
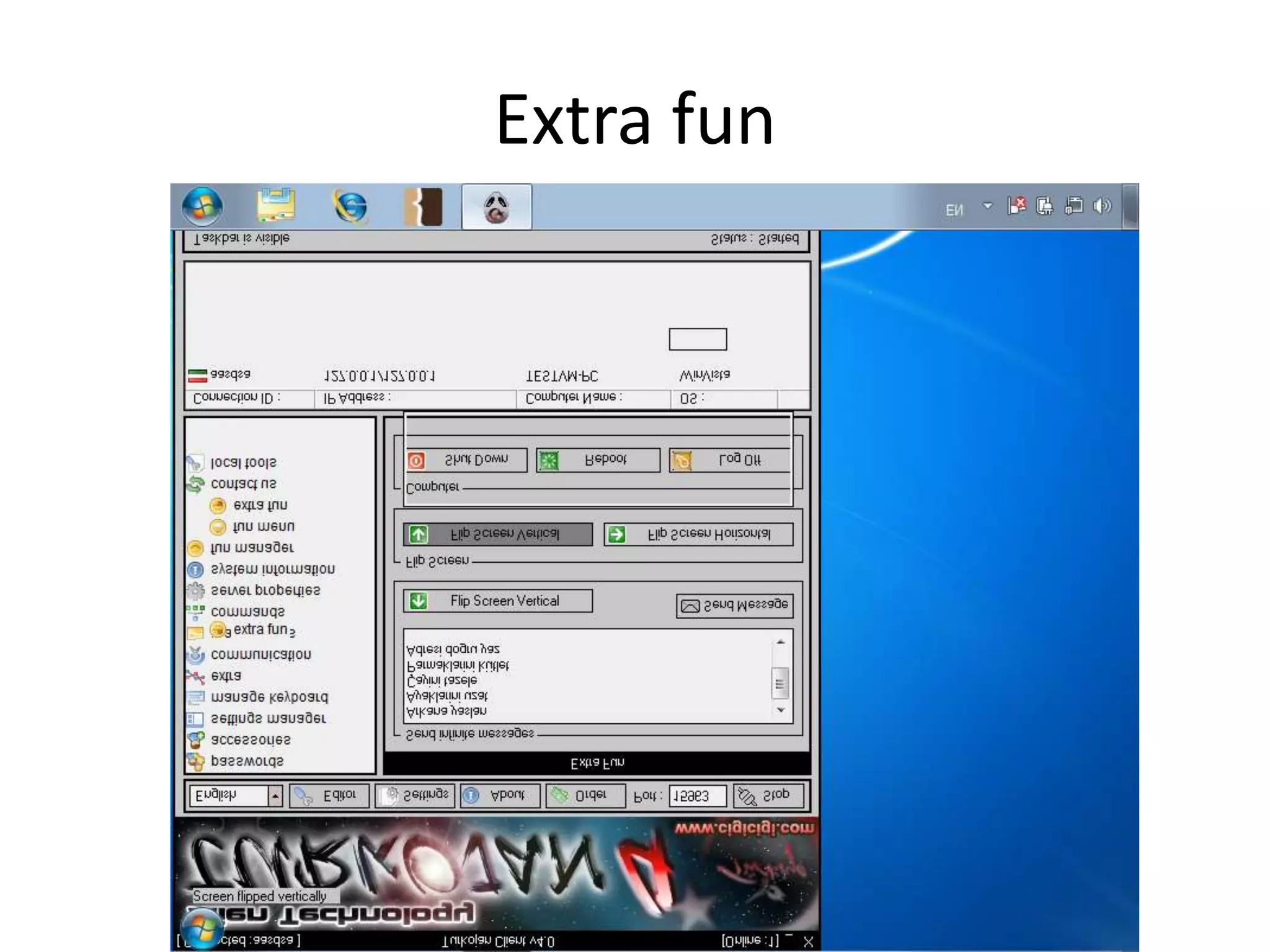
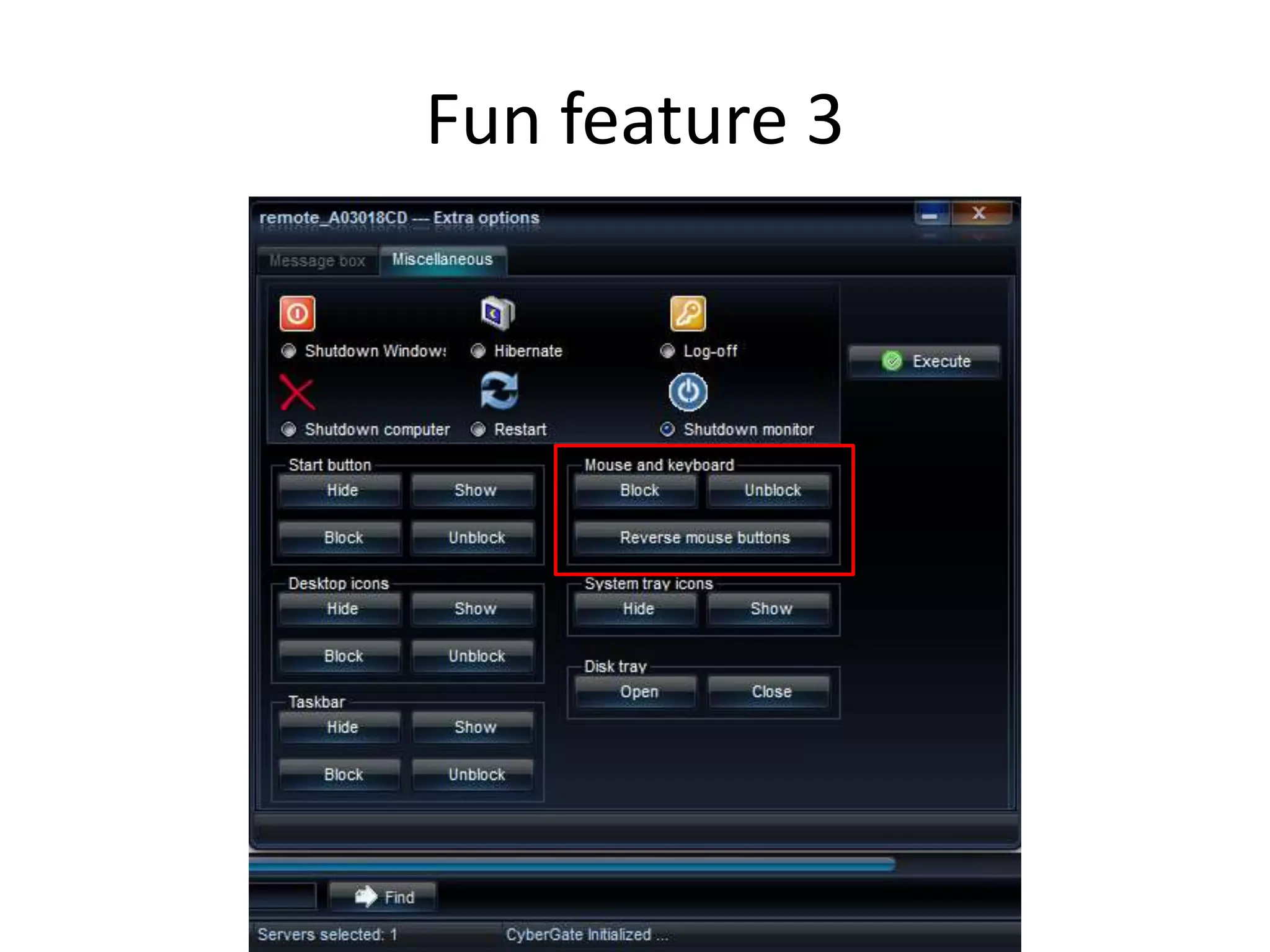
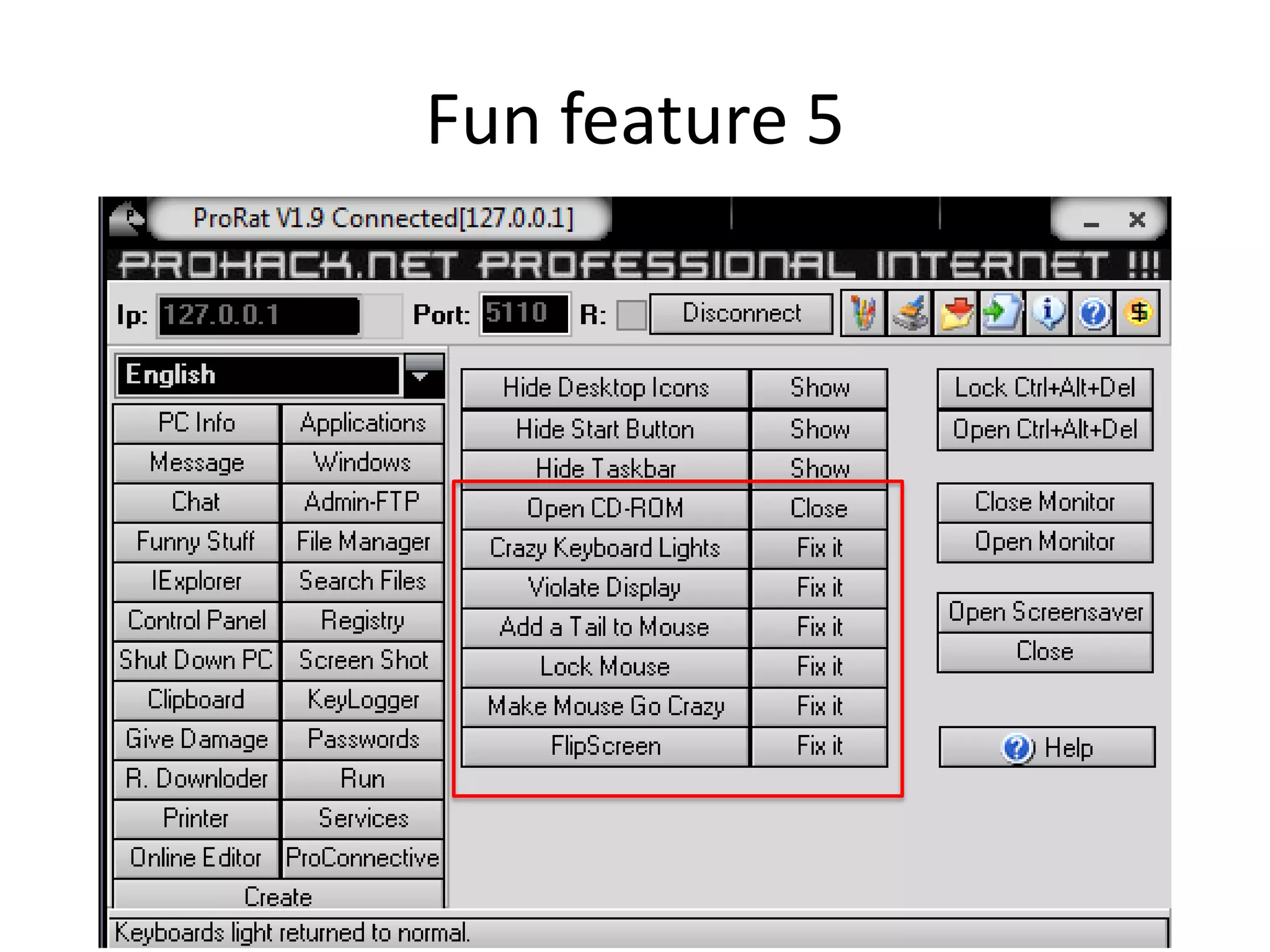
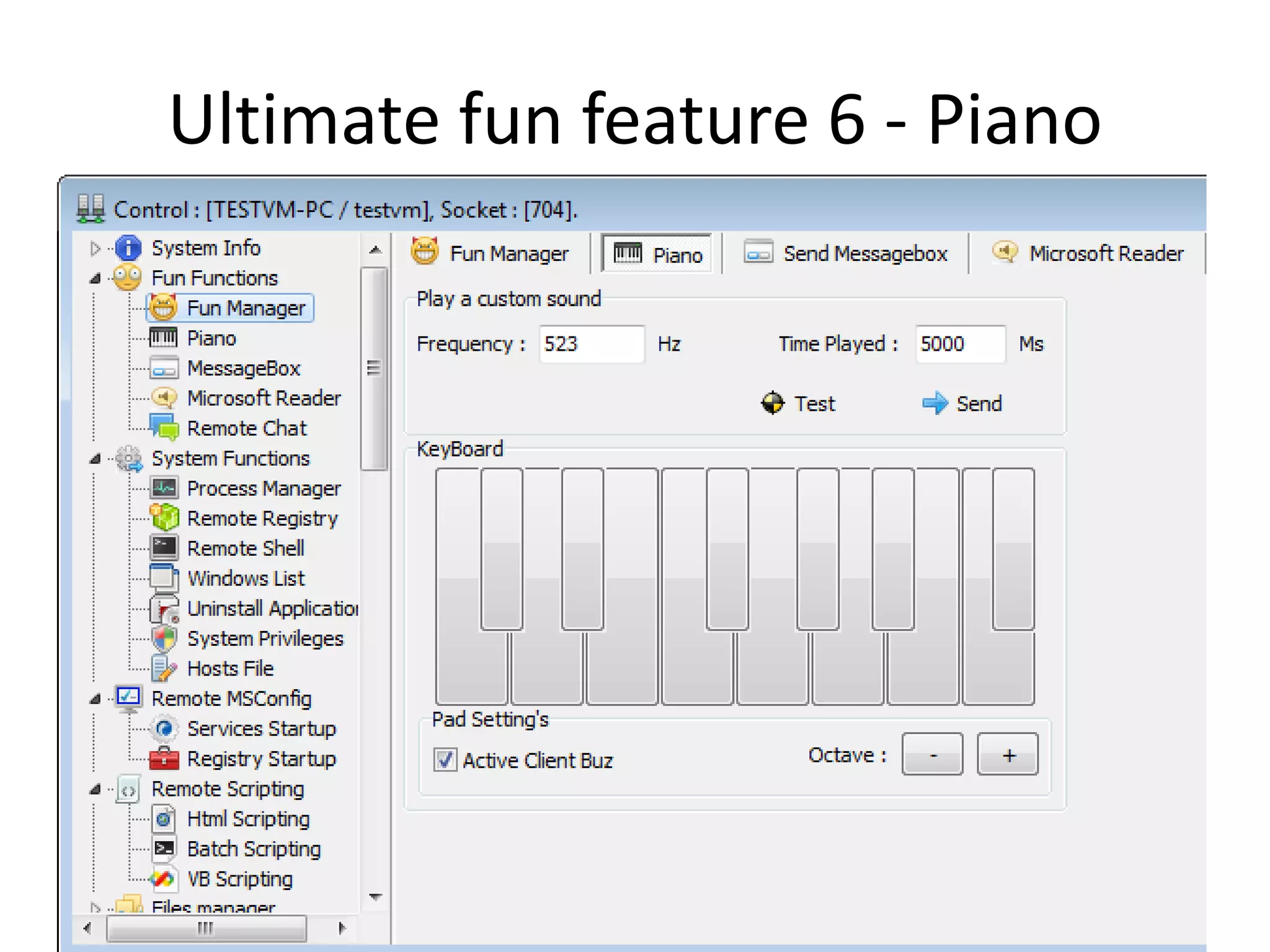
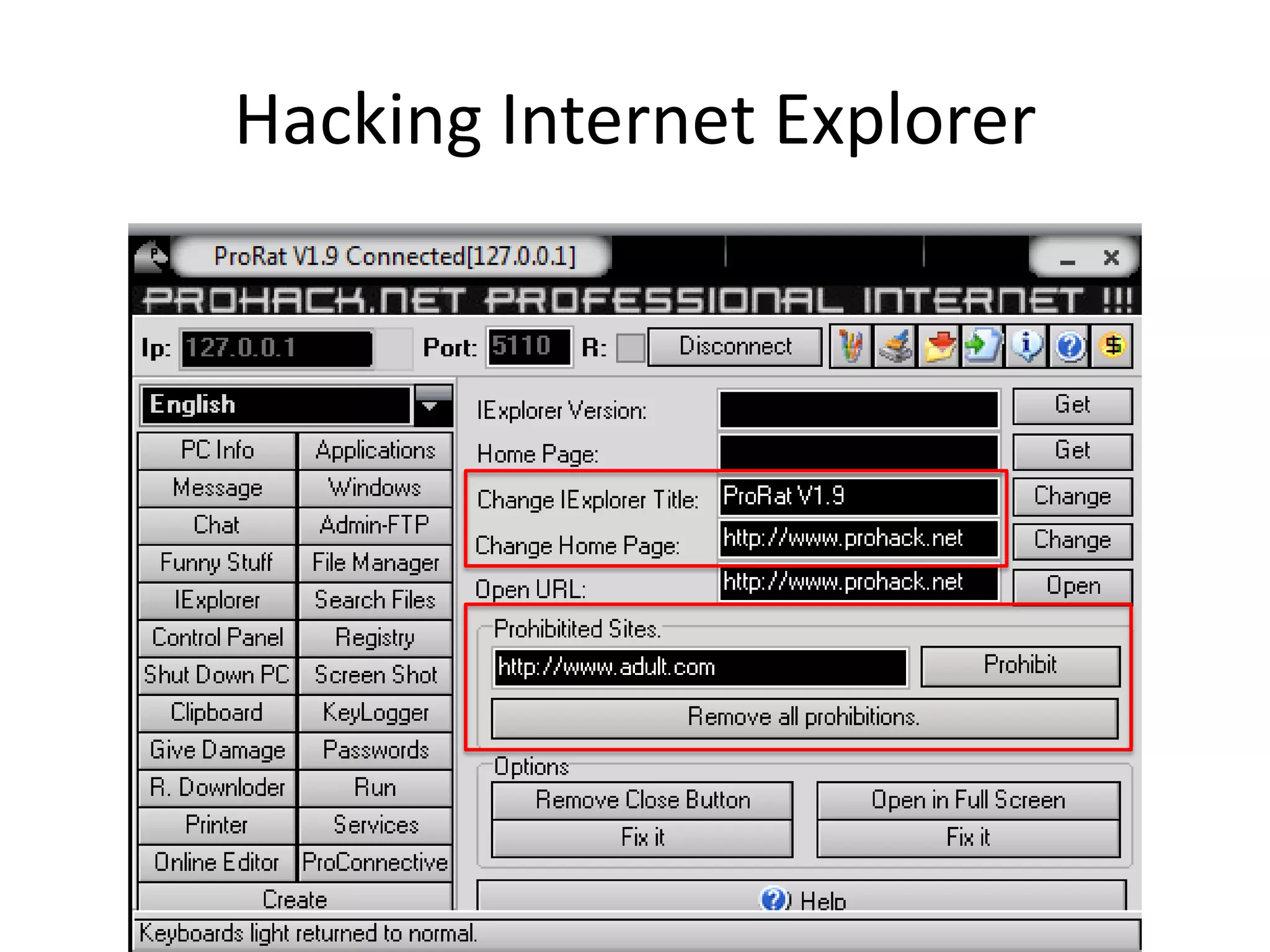
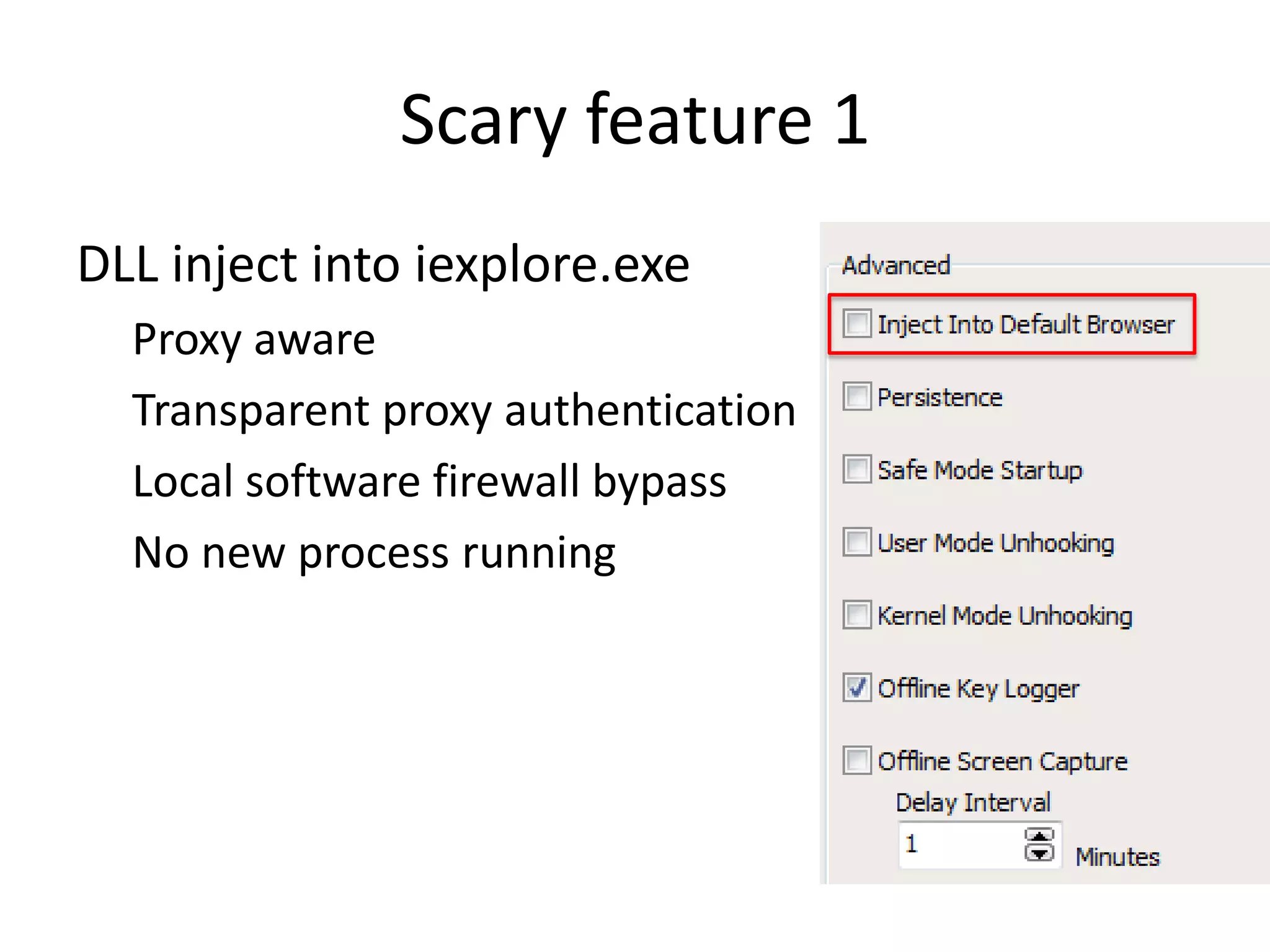
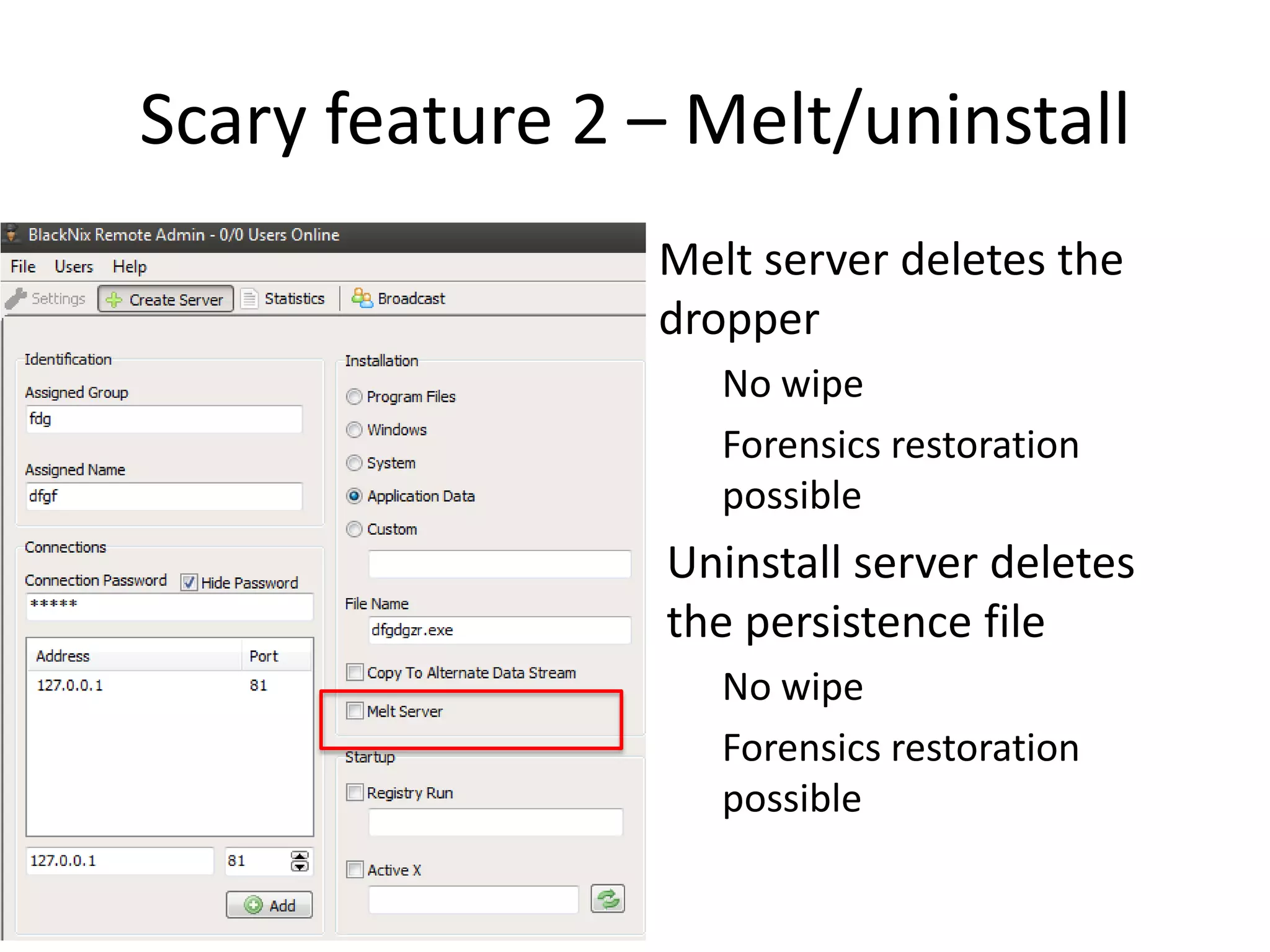
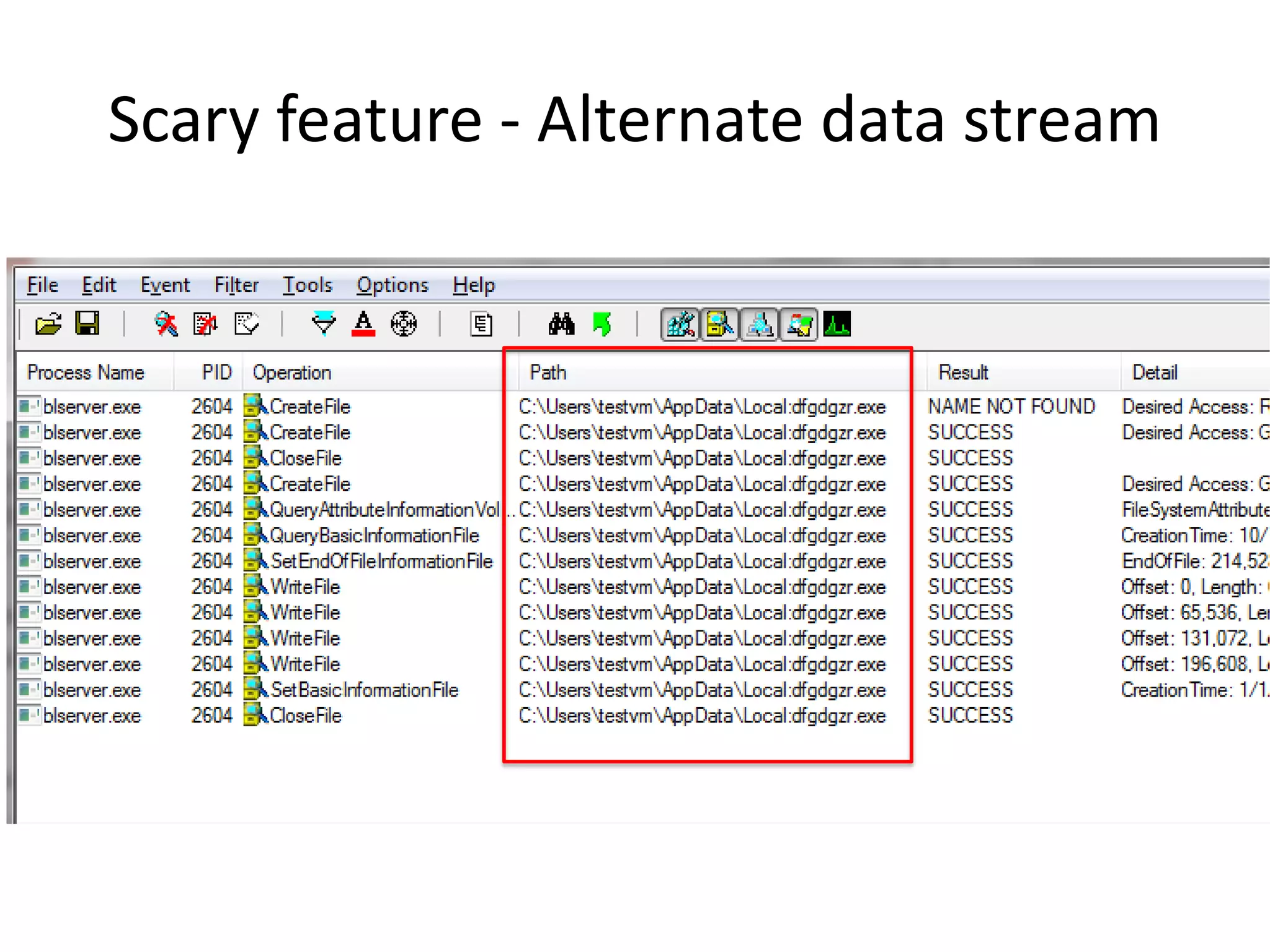
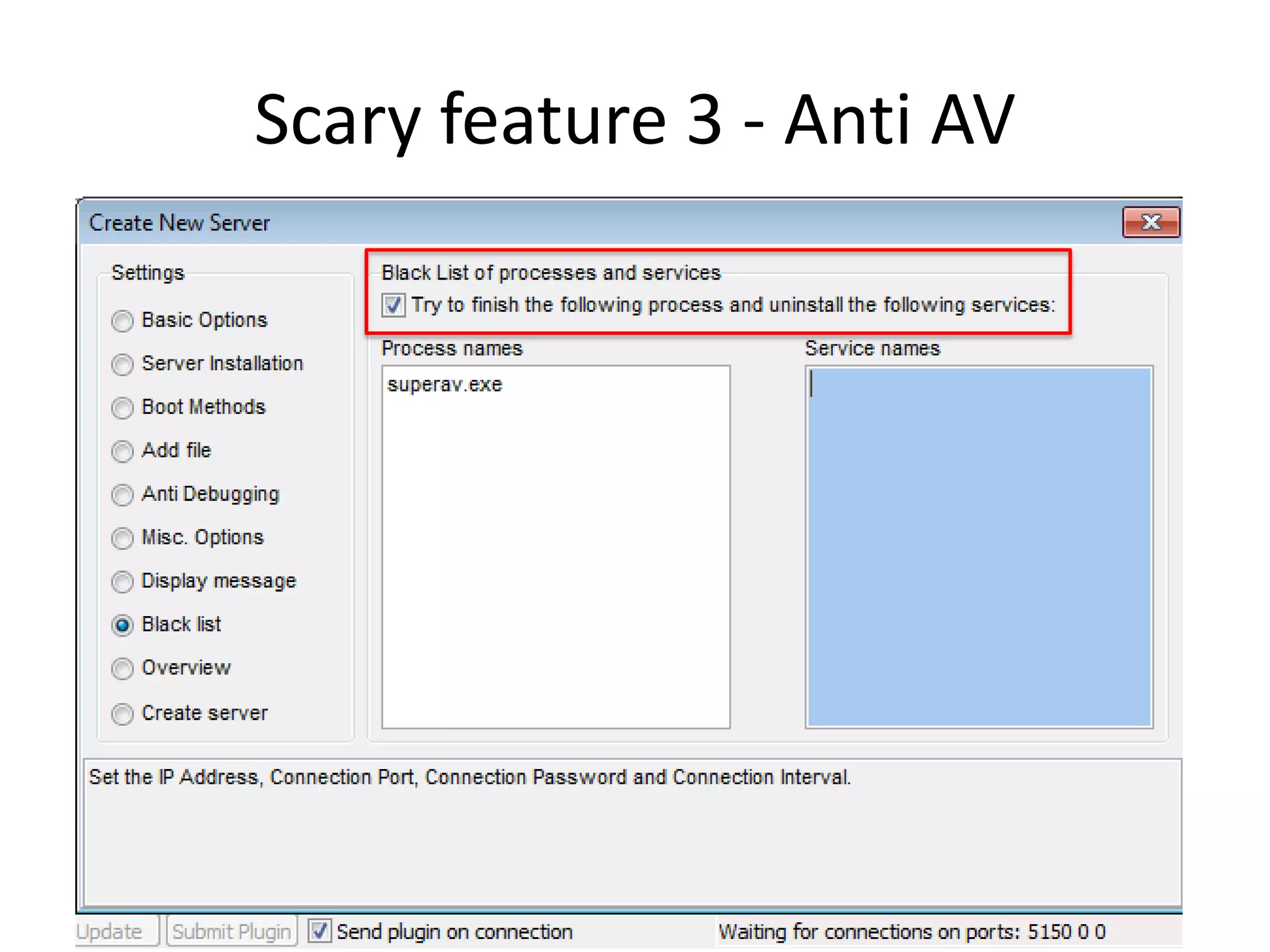
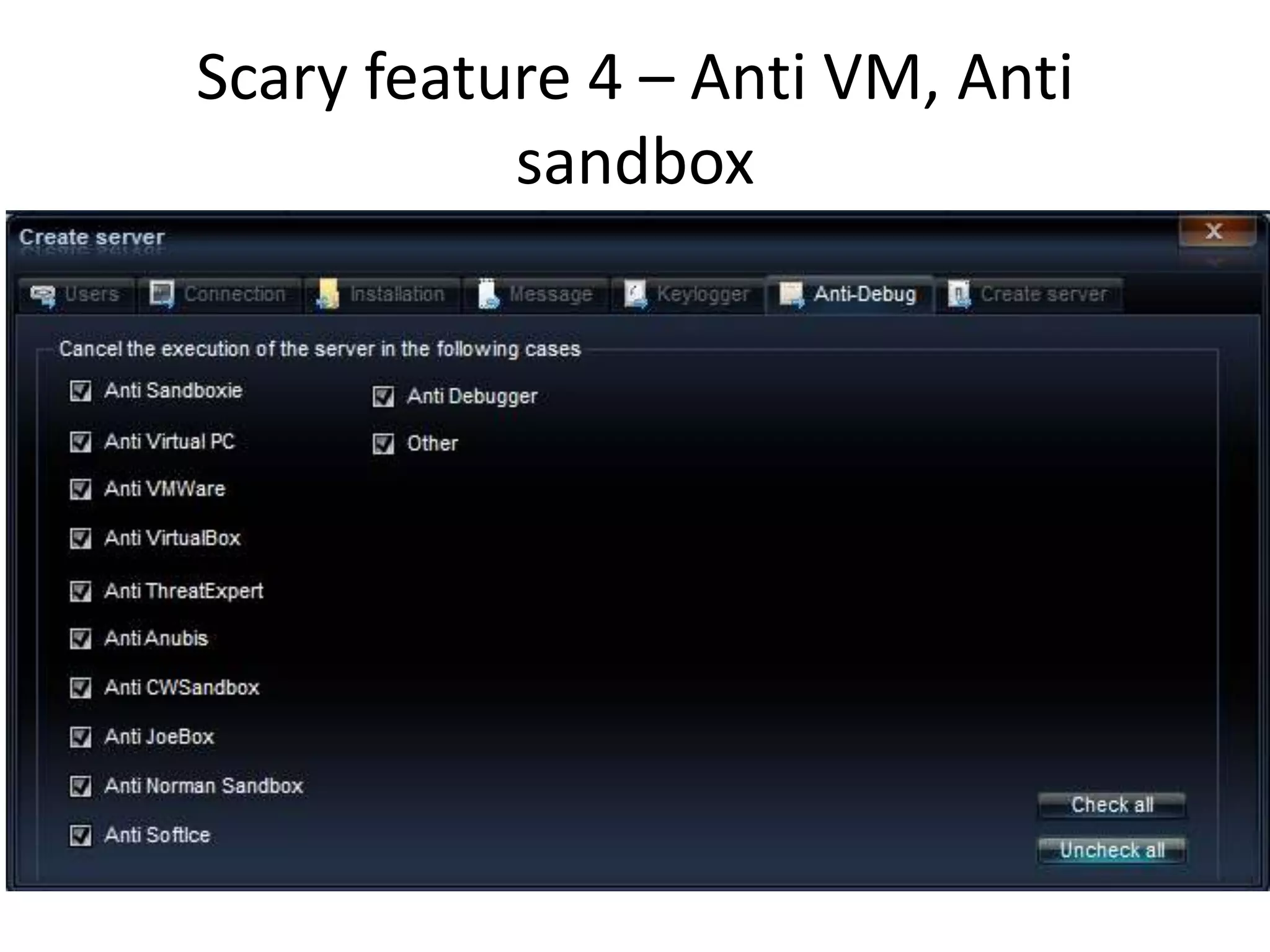
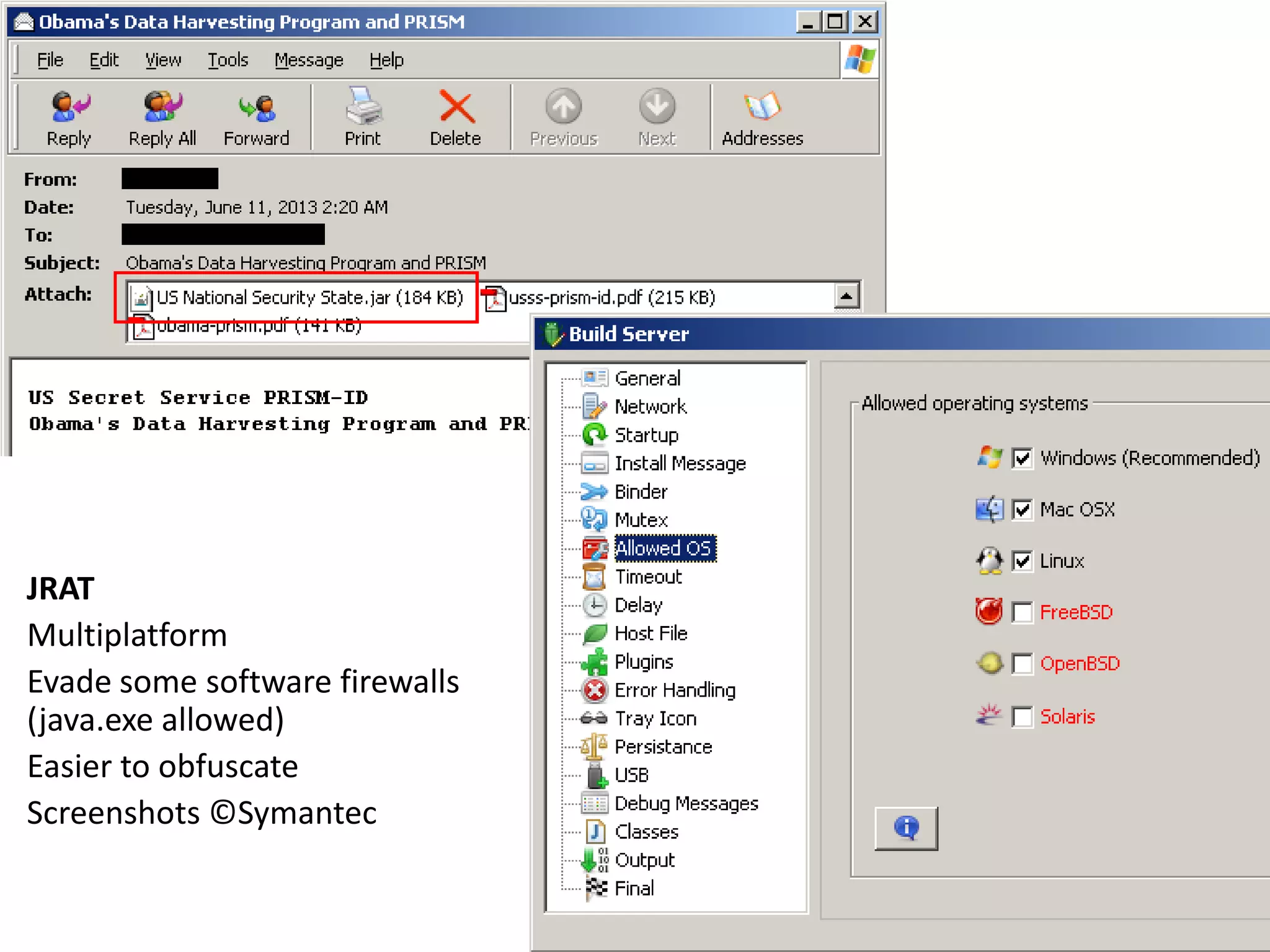
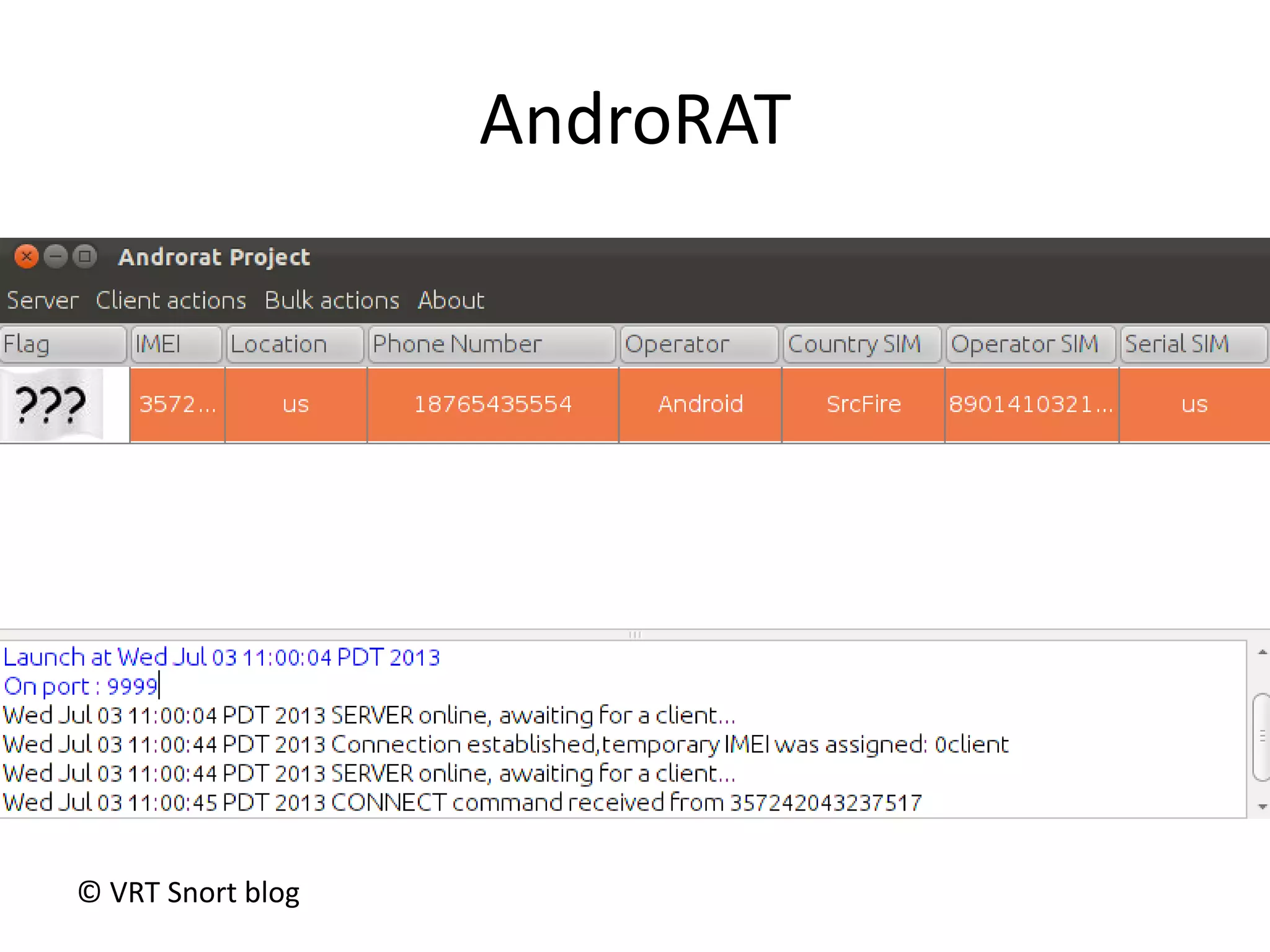
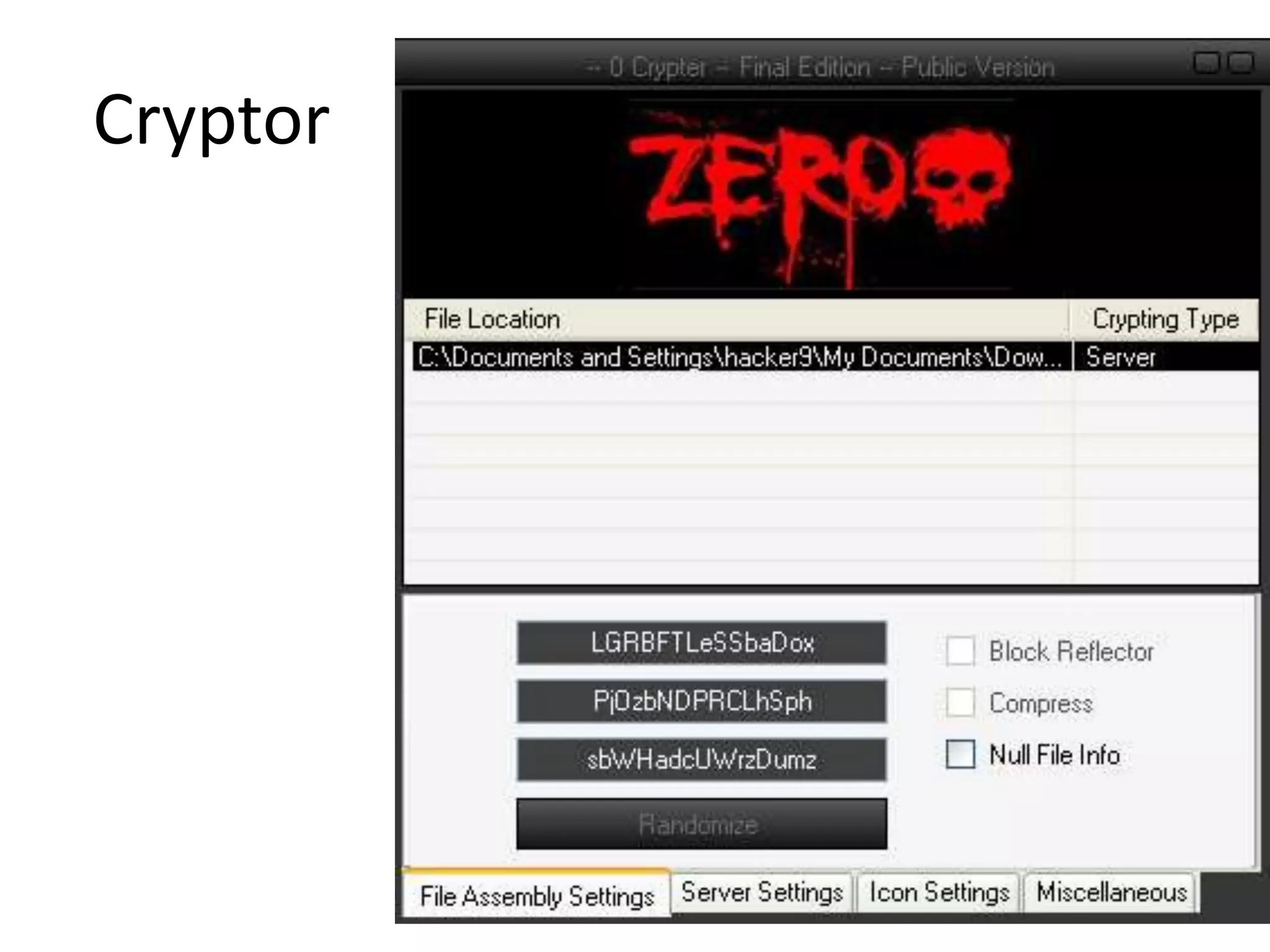
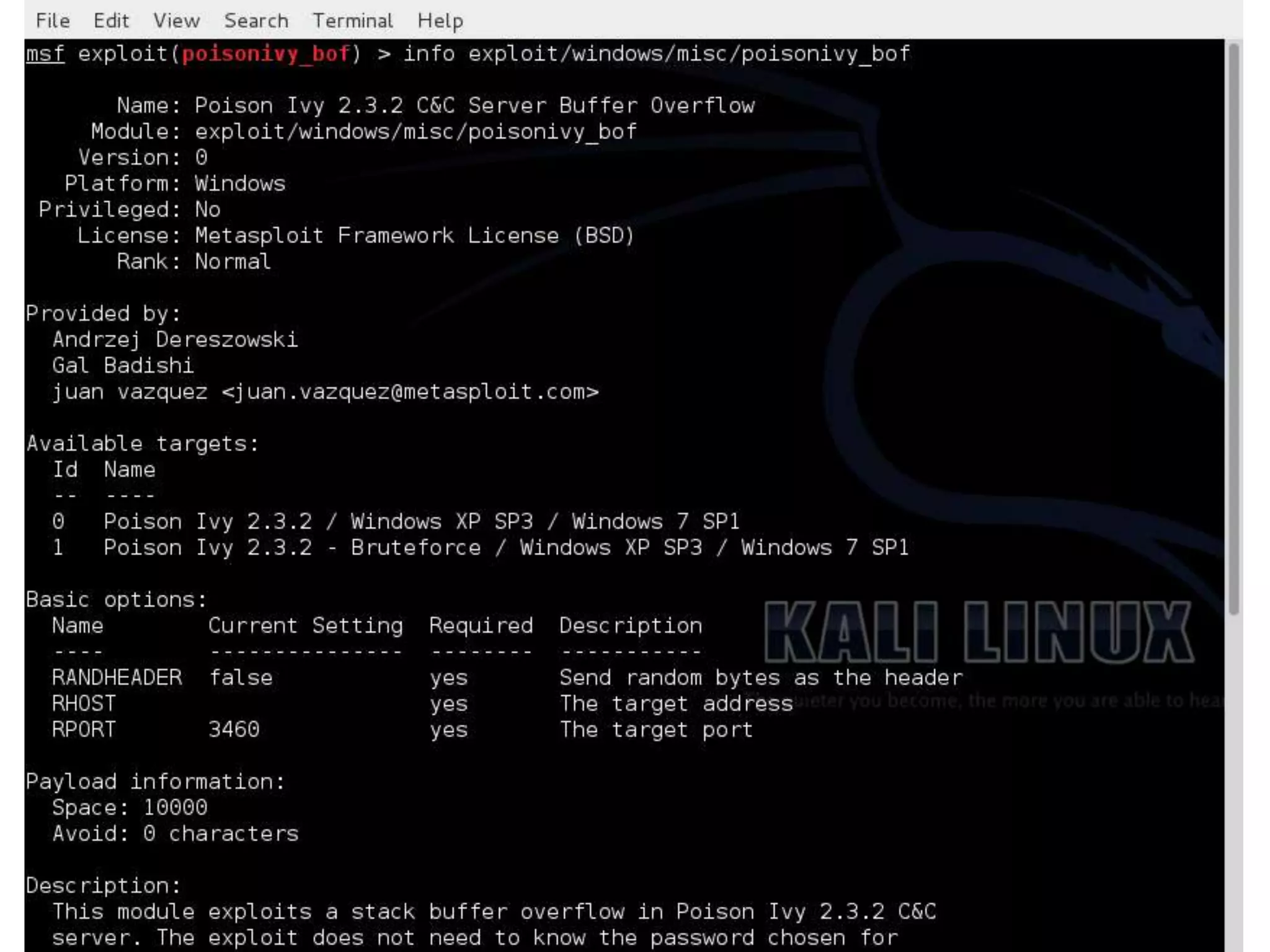
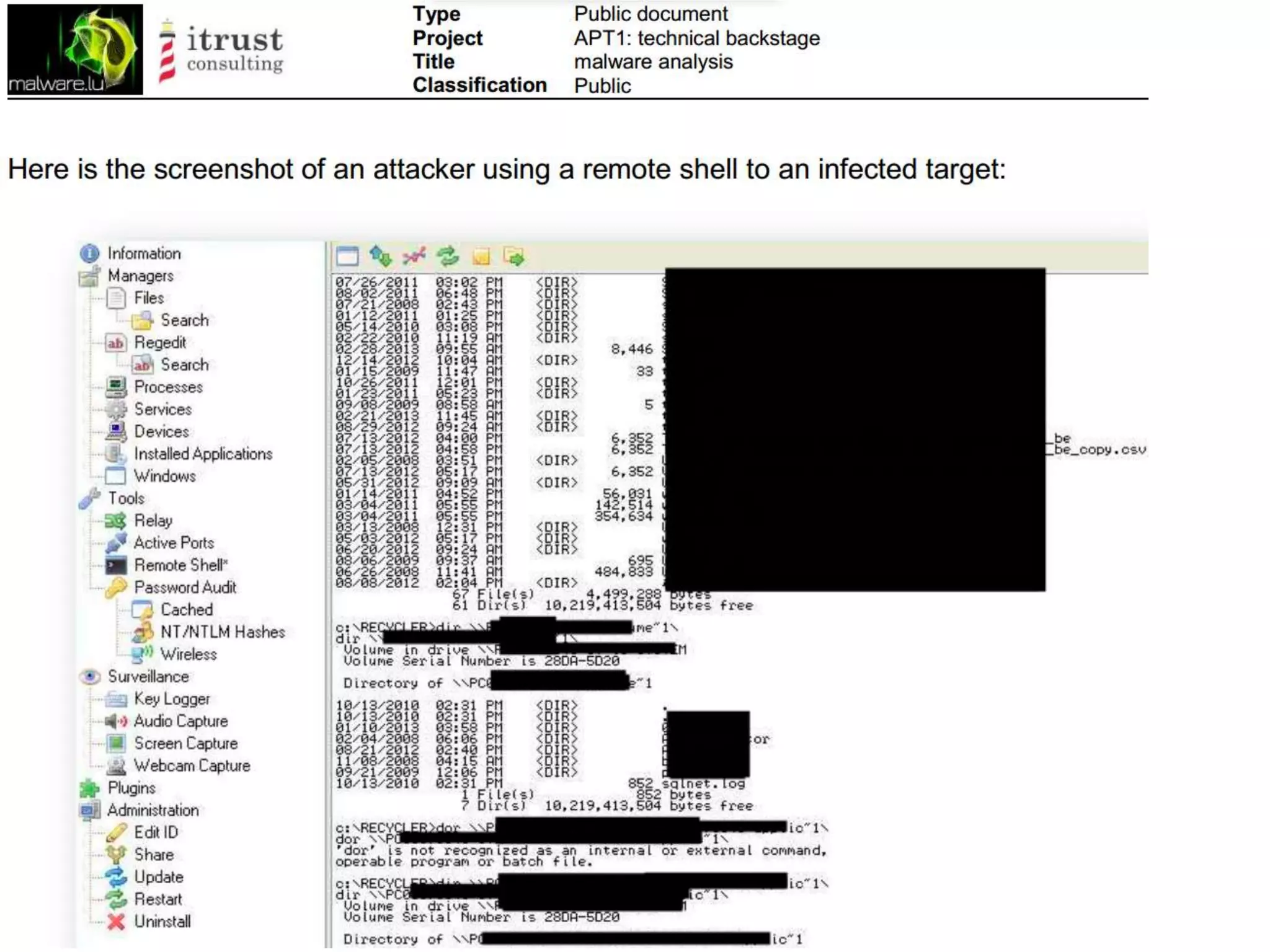
The document discusses the use of Remote Admin Tools (RATs) in cyber security, highlighting their legitimate applications as well as potential misuse in illegal activities. It emphasizes the importance of understanding these tools for penetration testing and malware response, while warning against their malicious use by various actors, including script kiddies. Additionally, it outlines various features of RATs and the associated risks, including evasion tactics against security measures.