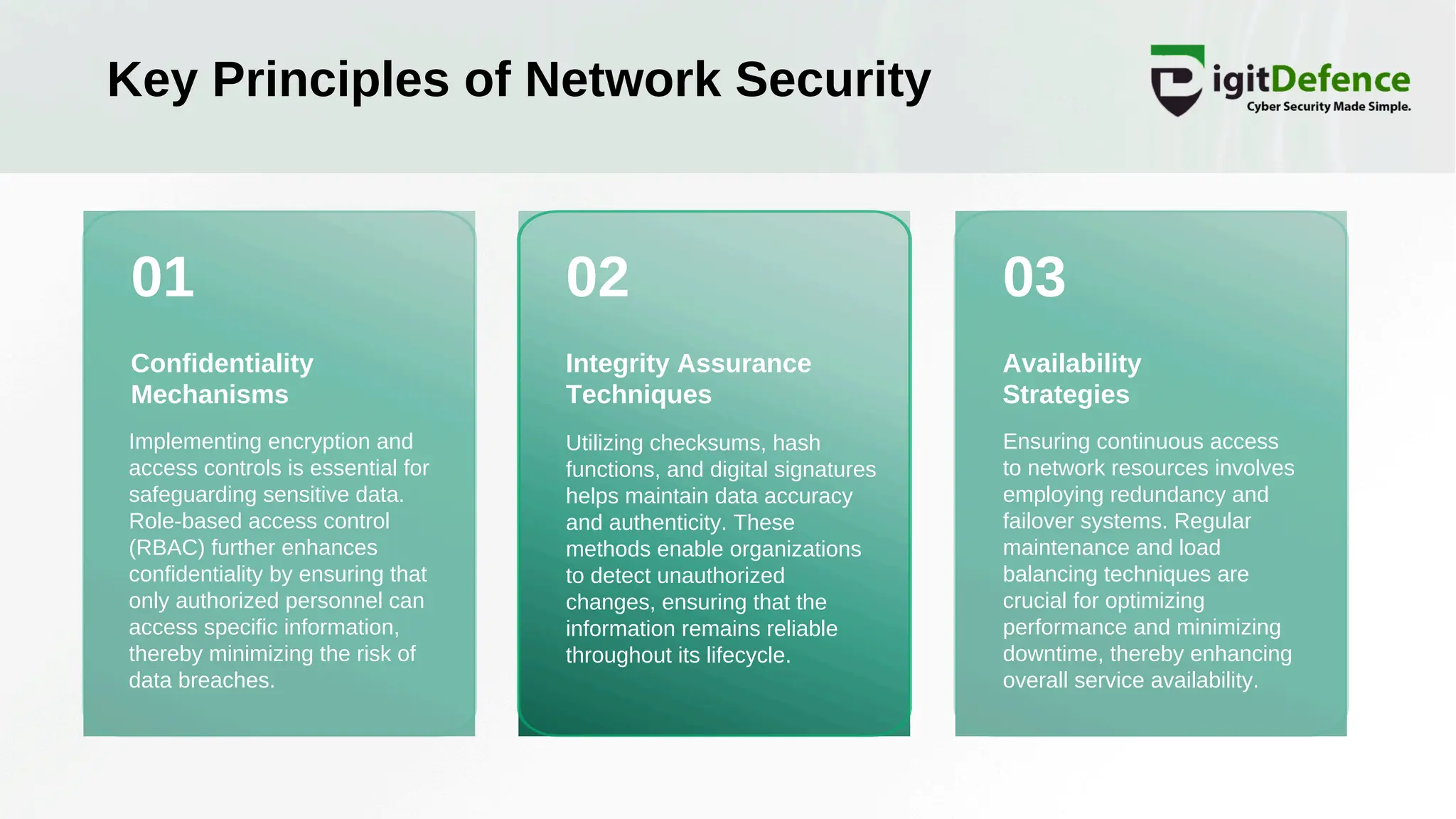
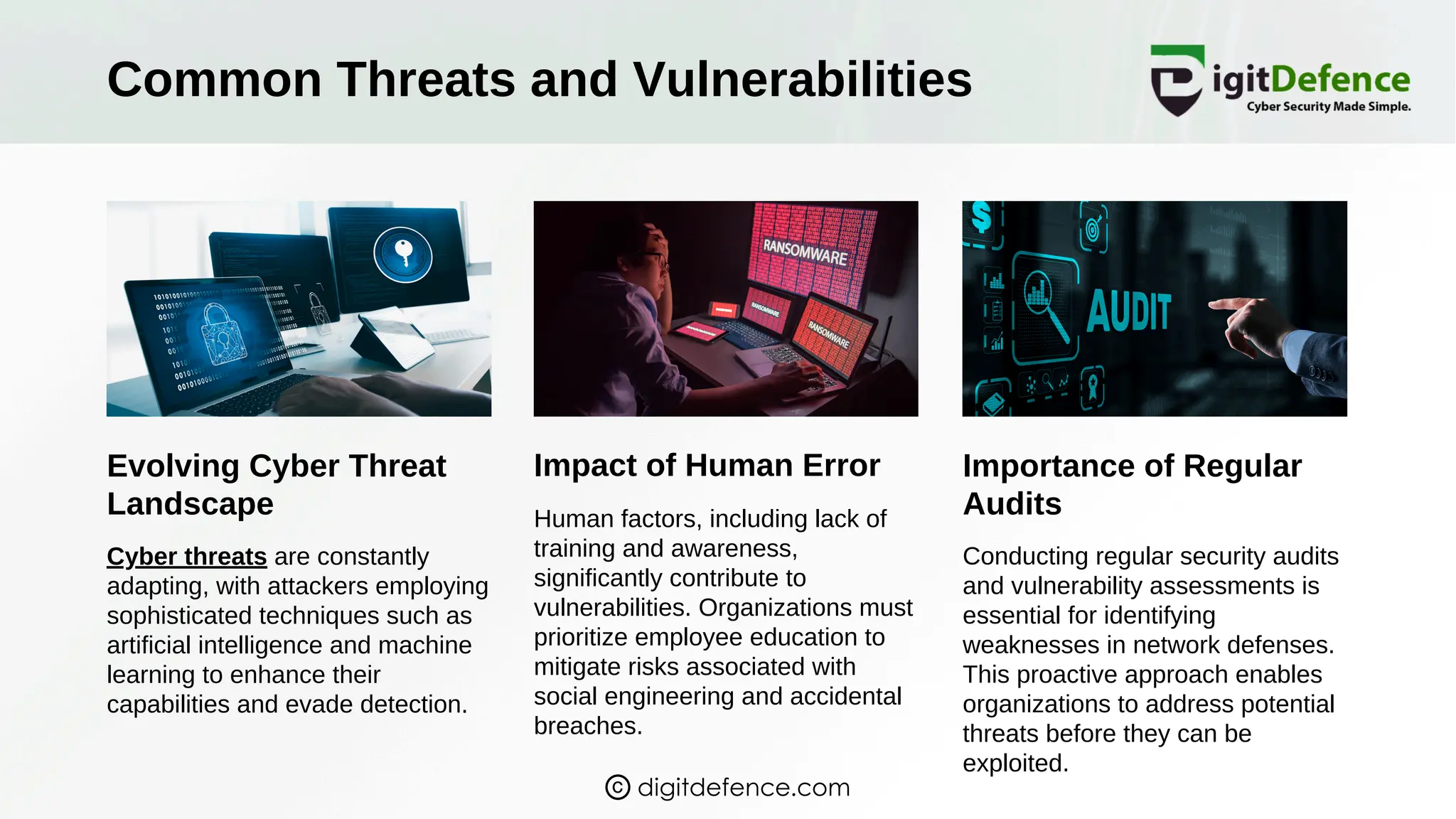
The document discusses the fundamentals of network security, emphasizing its critical role in business operations through a multi-layered defense involving technologies like firewalls and encryption. It highlights the importance of risk assessment, employee education, and proactive measures such as security audits to mitigate evolving cyber threats. Additionally, it explores the integration of emerging technologies such as AI and blockchain in enhancing security and the need for organizations to adopt a holistic security strategy.